| File name: | a1.exe |
| Full analysis: | https://app.any.run/tasks/4381b7ad-4f3e-4fba-b100-958e1ce998d3 |
| Verdict: | Suspicious activity |
| Analysis date: | June 26, 2019, 03:15:33 |
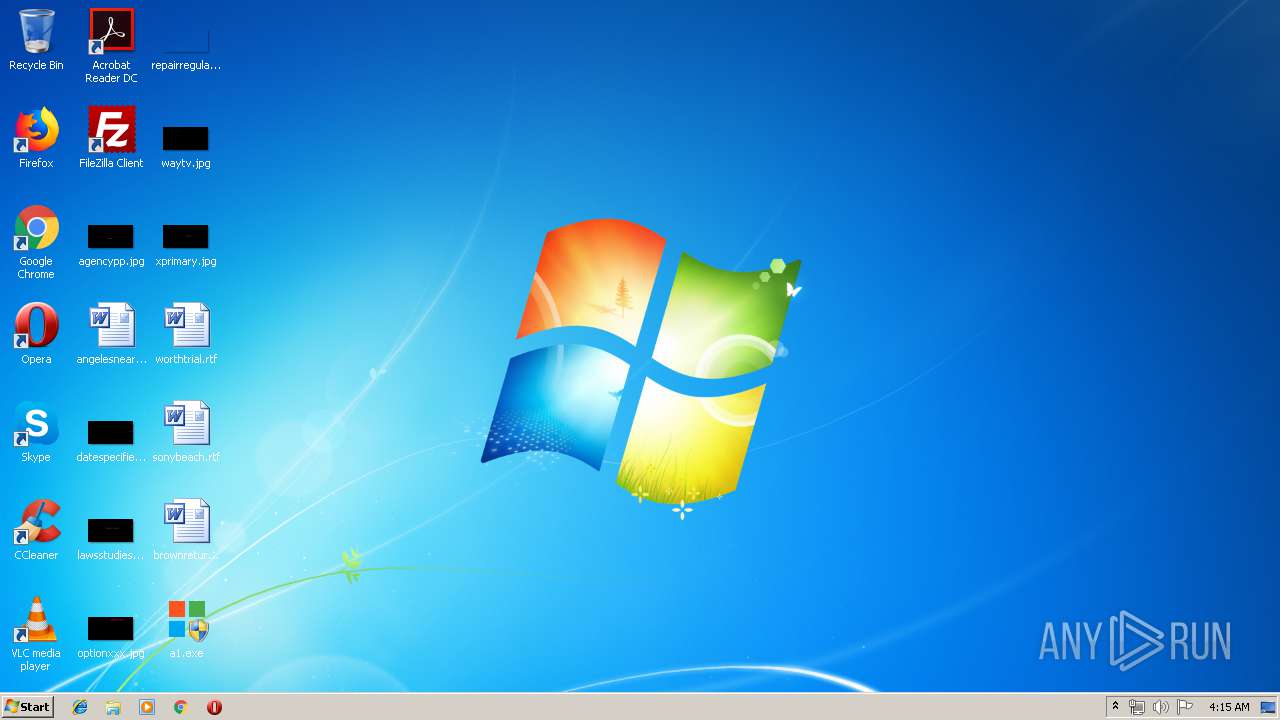
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | B352847C806E3B7F73AFF3FC4E1026C4 |
| SHA1: | 1B7818578BB031BB1E051B1C8C701414E2EF1DB4 |
| SHA256: | FE9FA1D187C038686D4951349A663B9EFDB71E927567889C7095261FA78B3431 |
| SSDEEP: | 768:bZCZtZ188np9auyiXZWgyvcPpRsX5d6O7fuadb340nbcuyD7Uv:bg8SM+7P/sb6OzVdL40nouy8 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts CMD.EXE for commands execution
- a1.exe (PID: 3468)
- cmd.exe (PID: 1208)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3348)
- cmd.exe (PID: 1208)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:01:18 11:10:35+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 36864 |
| InitializedDataSize: | 430080 |
| UninitializedDataSize: | 487424 |
| EntryPoint: | 0x7fae0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Jan-2017 10:10:35 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 18-Jan-2017 10:10:35 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00077000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00078000 | 0x00009000 | 0x00008800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.94147 |
.rsrc | 0x00081000 | 0x00069000 | 0x00069000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.95356 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.08821 | 672 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 2.73134 | 270376 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 2.47494 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 2.77792 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 2.71659 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 3.32768 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
E48EB3C39403C2A59635DBF3C54139B7 | 7.86824 | 1447 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
E5030BA8DC51CC1431F1764662CCD7B1 | 2.58496 | 6 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
F0696CA8F837048E22CB1F69D8424C8A | 3.6645 | 14 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.DLL |
MSVCRT.dll |
OLE32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
USER32.DLL |
WINMM.DLL |
Total processes
46
Monitored processes
10
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 416 | Reg.exe add "HKLM\SOFTWARE\ACD Systems\ACDSee Professional\110\LClient" /v "pid2" /t REG_BINARY /d "be9825649d98333533a59b230ae7f16b121784d43d89865f" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 900 | Reg.exe add "HKLM\SOFTWARE\ACD Systems\ACDSee Professional\110\LClient" /v "iid" /t REG_DWORD /d "317555" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1208 | "C:\Windows\system32\cmd.exe" /c "C:\Users\admin\AppData\Local\Temp\F2B.tmp\F2C.bat C:\Users\admin\Desktop\a1.exe" | C:\Windows\system32\cmd.exe | — | a1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1476 | xcopy /s /e /r /y /k "Data\C_Crack\C3\*.*" "" | C:\Windows\system32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extended Copy Utility Exit code: 4 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1568 | Reg.exe add "HKLM\SOFTWARE\ACD Systems\ACDSee Professional\110\LClient" /v "md" /t REG_BINARY /d "fa2e1a67279e0ffa8dc9c6a627a7f3cdb425a03038e326e810e4bba01d1f6411cdb5a3195c8f2aaebc5e75a48d982fb67930f458bc0232abf88e37fdb3df155787386d1253bddb48f62e50bdc973d43db756d78fb94637039b984b48161f075dbd82f7944402d39b790b705fe48d368c1ddd835b77246e386b9910b01f15e9f7c207b5de5944953190abdf62c41320dcf6949a2f45453117e7d9b7cf89500178ae48ebc1ac8520c54c9e196f14a4d5978ee641e678a6042f21d4c725bd9d6f3954441999f3ea3c105b750cdd7acc6ea91bf4ade11c2f39e40a789d37769e423f4e1be46b322b3ad2454c9e5aad5a9da208f8662756ffa04dc79275bfab96040359d3b7b9e4de48edc831d44bd662084548009c72e9942678109fdd3132320de371dc947bf2352ce3bc12992336bc820e85782774b785f72b239bcc27496161d4bf5028f498945fc5ec1d5d1b7015a991e5bcfd6e29cef428accc6e933784c4faacc3f8b646465da8878769eddc256f2a635b78ec922b9e42aa49ddbe966a70b0" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1740 | Reg.exe add "HKLM\SOFTWARE\ACD Systems\RBC" /v "MachineGuid" /t REG_SZ /d "7c1042f8-b0fd-4755-80be-a7d3d0bd30d2" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1824 | "C:\Users\admin\Desktop\a1.exe" | C:\Users\admin\Desktop\a1.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2132 | reg query "HKLM\SOFTWARE\ACD Systems\ACDSee Professional\110" /v InstallDir | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3348 | C:\Windows\system32\cmd.exe /c reg query "HKLM\SOFTWARE\ACD Systems\ACDSee Professional\110" /v InstallDir 2>nul | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3468 | "C:\Users\admin\Desktop\a1.exe" | C:\Users\admin\Desktop\a1.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
46
Read events
38
Write events
8
Delete events
0
Modification events
| (PID) Process: | (3468) a1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3468) a1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (900) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ACD Systems\ACDSee Professional\110\LClient |
| Operation: | write | Name: | iid |
Value: 317555 | |||
| (PID) Process: | (416) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ACD Systems\ACDSee Professional\110\LClient |
| Operation: | write | Name: | pid2 |
Value: BE9825649D98333533A59B230AE7F16B121784D43D89865F | |||
| (PID) Process: | (1568) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ACD Systems\ACDSee Professional\110\LClient |
| Operation: | write | Name: | md |
Value: FA2E1A67279E0FFA8DC9C6A627A7F3CDB425A03038E326E810E4BBA01D1F6411CDB5A3195C8F2AAEBC5E75A48D982FB67930F458BC0232ABF88E37FDB3DF155787386D1253BDDB48F62E50BDC973D43DB756D78FB94637039B984B48161F075DBD82F7944402D39B790B705FE48D368C1DDD835B77246E386B9910B01F15E9F7C207B5DE5944953190ABDF62C41320DCF6949A2F45453117E7D9B7CF89500178AE48EBC1AC8520C54C9E196F14A4D5978EE641E678A6042F21D4C725BD9D6F3954441999F3EA3C105B750CDD7ACC6EA91BF4ADE11C2F39E40A789D37769E423F4E1BE46B322B3AD2454C9E5AAD5A9DA208F8662756FFA04DC79275BFAB96040359D3B7B9E4DE48EDC831D44BD662084548009C72E9942678109FDD3132320DE371DC947BF2352CE3BC12992336BC820E85782774B785F72B239BCC27496161D4BF5028F498945FC5EC1D5D1B7015A991E5BCFD6E29CEF428ACCC6E933784C4FAACC3F8B646465DA8878769EDDC256F2A635B78EC922B9E42AA49DDBE966A70B0 | |||
| (PID) Process: | (1740) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ACD Systems\RBC |
| Operation: | write | Name: | MachineGuid |
Value: 7c1042f8-b0fd-4755-80be-a7d3d0bd30d2 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3468 | a1.exe | C:\Users\admin\AppData\Local\Temp\F2B.tmp\F2C.bat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report