| File name: | HorrorTrojan.exe |
| Full analysis: | https://app.any.run/tasks/09eb8bcd-2d62-44e6-938c-748cb8bbb4ba |
| Verdict: | Malicious activity |
| Analysis date: | August 05, 2023, 14:42:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 88501D015F58AB6C33B32F78324DE059 |
| SHA1: | 83BF9BEF17B44940710A32939BFF0E10E7D83F9A |
| SHA256: | FE8D19B219E7EA3CF17D747932ECBA2A45CA5FE0573870F7F0FE31C7726B074C |
| SSDEEP: | 49152:bKyhZJirb8GVjdY1F9xFgGlFmFMUbhNVM5pEEuk32SEnsPf:blBQb8YZ0F/FgGlK5b0uBkPf |
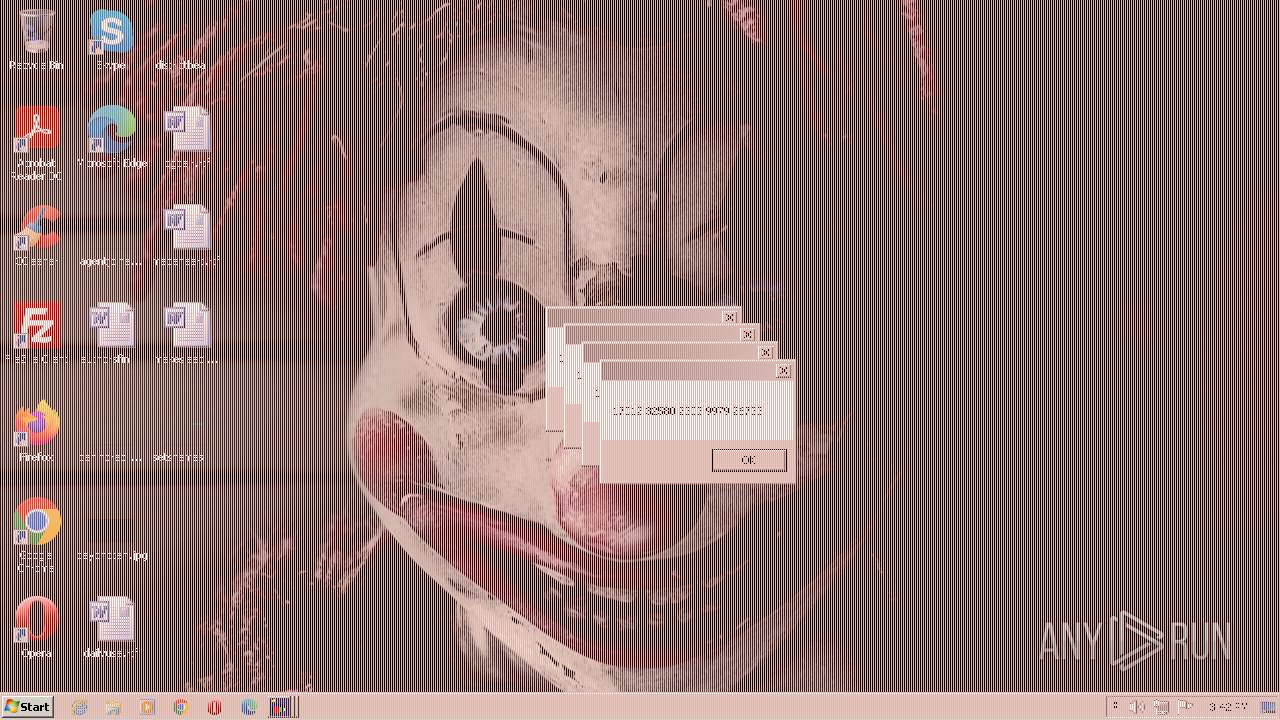
MALICIOUS
Application was dropped or rewritten from another process
- CLWCP.exe (PID: 792)
- flasher.exe (PID: 2420)
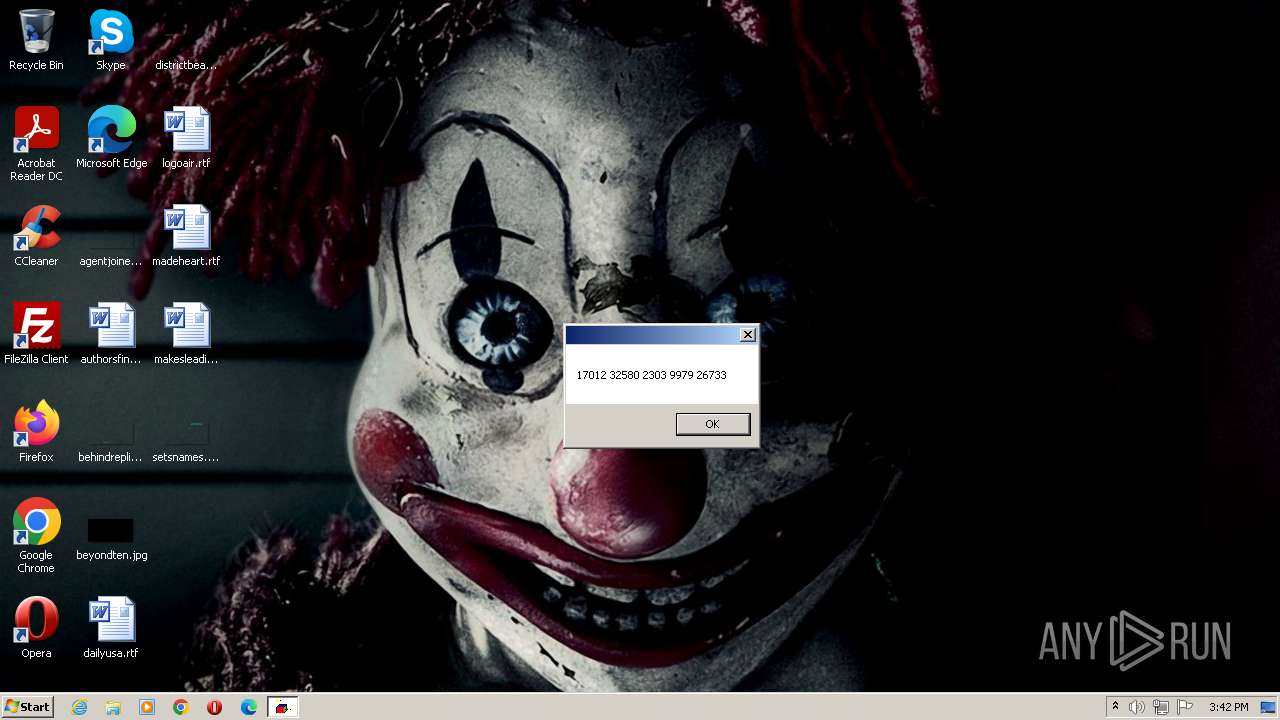
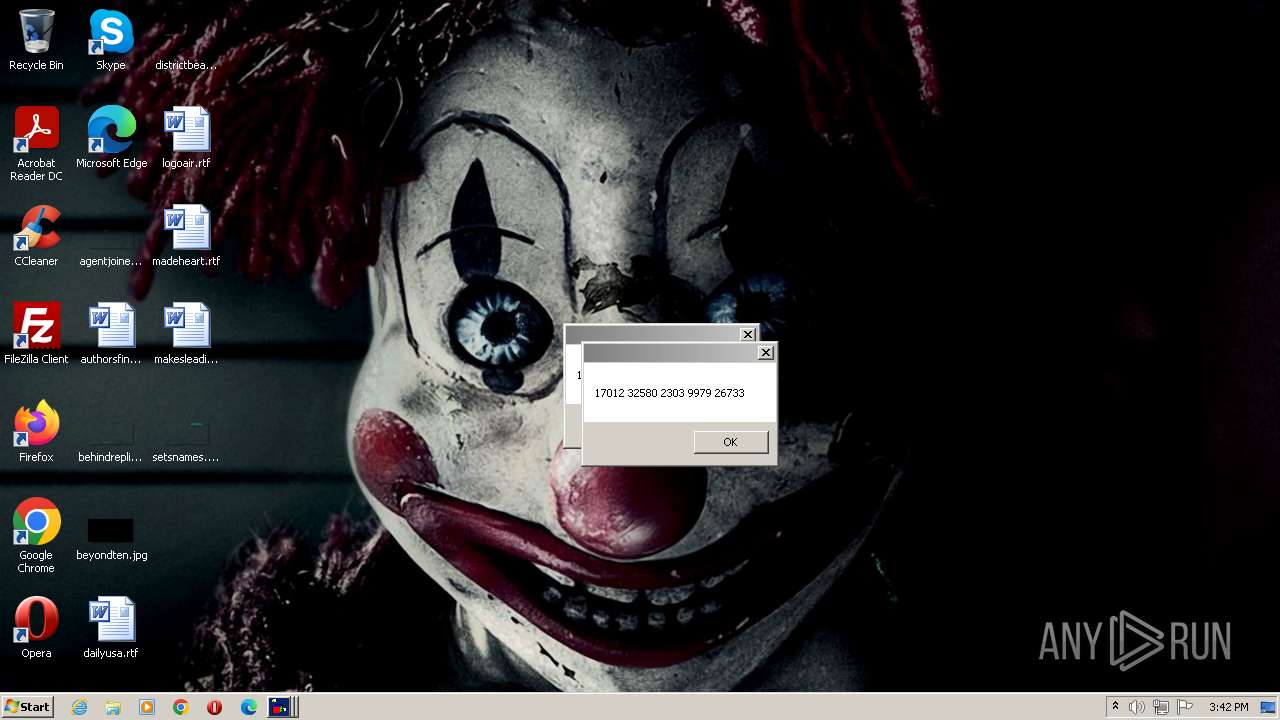
- screenscrew.exe (PID: 1996)
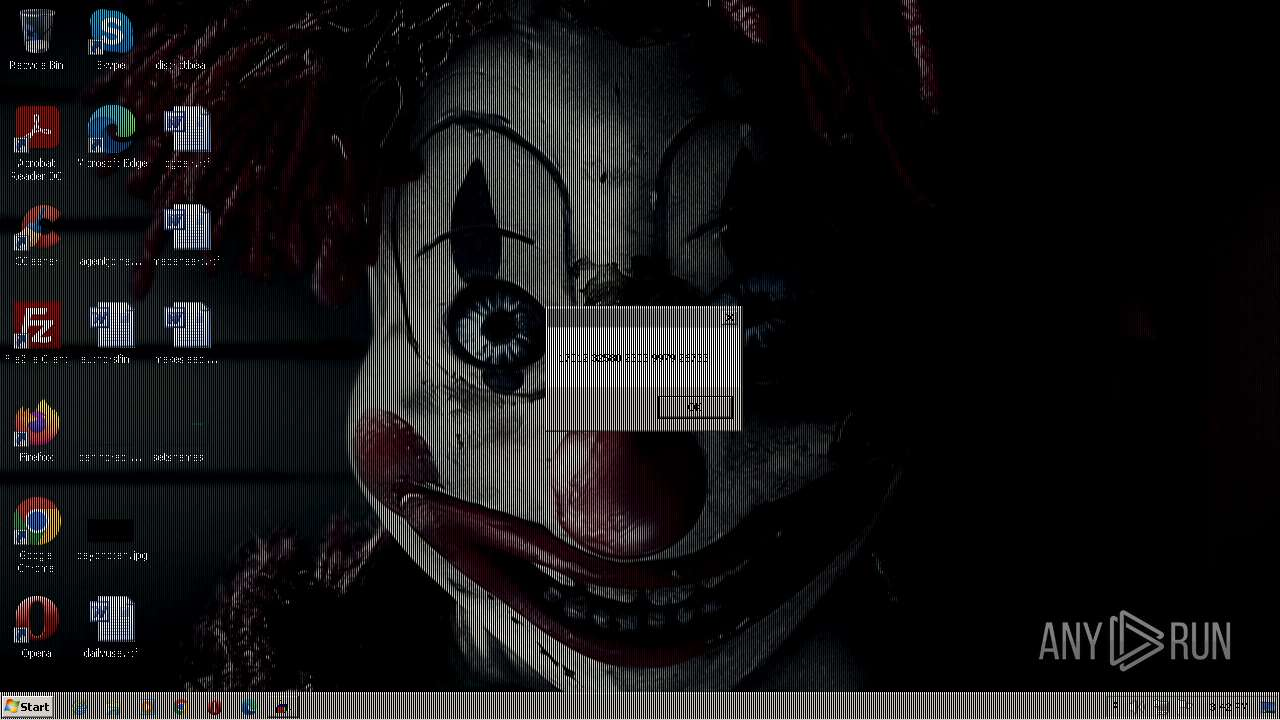
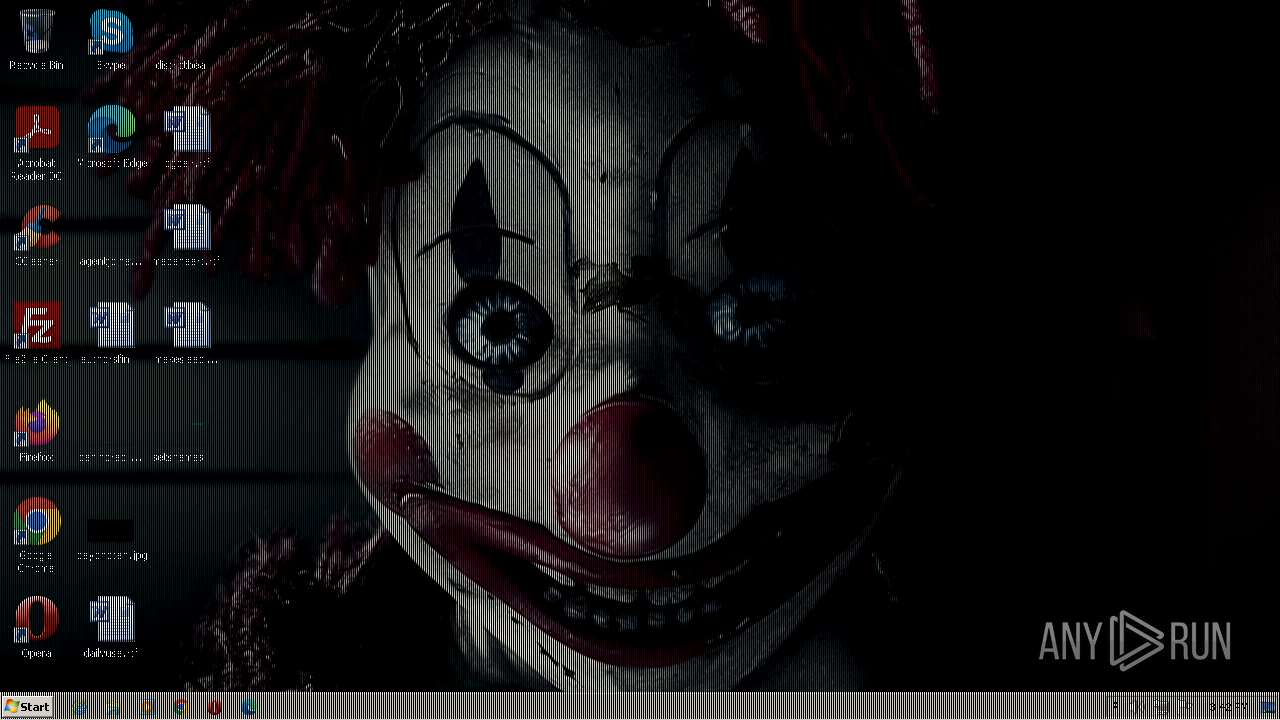
- melter.exe (PID: 1896)
SUSPICIOUS
Executing commands from a ".bat" file
- HorrorTrojan.exe (PID: 2848)
Executable content was dropped or overwritten
- HorrorTrojan.exe (PID: 2848)
Reads the Internet Settings
- HorrorTrojan.exe (PID: 2848)
- cmd.exe (PID: 3172)
Starts CMD.EXE for commands execution
- HorrorTrojan.exe (PID: 2848)
The process executes VB scripts
- cmd.exe (PID: 3172)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 3172)
INFO
Checks supported languages
- HorrorTrojan.exe (PID: 2848)
- CLWCP.exe (PID: 792)
- flasher.exe (PID: 2420)
- screenscrew.exe (PID: 1996)
- melter.exe (PID: 1896)
The process checks LSA protection
- HorrorTrojan.exe (PID: 2848)
Reads the computer name
- HorrorTrojan.exe (PID: 2848)
The executable file from the user directory is run by the CMD process
- flasher.exe (PID: 2420)
- CLWCP.exe (PID: 792)
- screenscrew.exe (PID: 1996)
- melter.exe (PID: 1896)
Create files in a temporary directory
- HorrorTrojan.exe (PID: 2848)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x83dbd0 |
| UninitializedDataSize: | 6328320 |
| InitializedDataSize: | 4096 |
| CodeSize: | 2314240 |
| LinkerVersion: | 2.5 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2010:11:08 13:12:07+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Nov-2010 13:12:07 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 08-Nov-2010 13:12:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00609000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0060A000 | 0x00235000 | 0x00234800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99991 |
.rsrc | 0x0083F000 | 0x00001000 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.85565 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.92322 | 611 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
B | 7.79257 | 896 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
F | 0 | 8581332 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
I | 6.32896 | 108 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
N | 3.32193 | 10 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
O | 2.58496 | 6 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
MSVCRT.dll |
OLE32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
169
Monitored processes
135
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | timeout 1 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 448 | timeout 1 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 588 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\6E17.tmp\x.vbs" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 620 | timeout 1 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 740 | timeout 1 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 744 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\6E17.tmp\x.vbs" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 744 | timeout 1 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 768 | timeout 1 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 768 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\6E17.tmp\x.vbs" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 792 | clwcp c:\horror\bg.bmp | C:\Users\admin\AppData\Local\Temp\6E17.tmp\CLWCP.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
7 317
Read events
6 797
Write events
520
Delete events
0
Modification events
| (PID) Process: | (2848) HorrorTrojan.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2848) HorrorTrojan.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2848) HorrorTrojan.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2848) HorrorTrojan.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3172) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3172) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3172) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3172) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
4
Suspicious files
0
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2848 | HorrorTrojan.exe | C:\Users\admin\AppData\Local\Temp\6E17.tmp\bg.bmp | — | |
MD5:— | SHA256:— | |||
| 3172 | cmd.exe | C:\horror\bg.bmp | — | |
MD5:— | SHA256:— | |||
| 2848 | HorrorTrojan.exe | C:\Users\admin\AppData\Local\Temp\6E17.tmp\screenscrew.exe | executable | |
MD5:E87A04C270F98BB6B5677CC789D1AD1D | SHA256:E03520794F00FB39EF3CFFF012F72A5D03C60F89DE28DBE69016F6ED151B5338 | |||
| 2848 | HorrorTrojan.exe | C:\Users\admin\AppData\Local\Temp\6E17.tmp\horror.bat | text | |
MD5:3255E8BCD675D756D558DC26BB82620C | SHA256:10470BE0FD23195DD21893584409DFF05F6F58F48AF5FF7106368CA12AA9E591 | |||
| 2848 | HorrorTrojan.exe | C:\Users\admin\AppData\Local\Temp\6E17.tmp\scream.bmp | image | |
MD5:71DA1EAE2BE419D58F50B9A4EDECD9A5 | SHA256:FA03CBB06CD0A6C4875F5CB770476EBC6947B0FD366FD779BFD4C9F8B0899536 | |||
| 2848 | HorrorTrojan.exe | C:\Users\admin\AppData\Local\Temp\6E17.tmp\melter.exe | executable | |
MD5:D9BAAC374CC96E41C9F86C669E53F61C | SHA256:A1D883577BCB6C4F9DE47B06FE97C370C09BDDFFB6569B6CF93576371BDBC412 | |||
| 3172 | cmd.exe | C:\horror\scream.bmp | image | |
MD5:71DA1EAE2BE419D58F50B9A4EDECD9A5 | SHA256:FA03CBB06CD0A6C4875F5CB770476EBC6947B0FD366FD779BFD4C9F8B0899536 | |||
| 2848 | HorrorTrojan.exe | C:\Users\admin\AppData\Local\Temp\6E17.tmp\flasher.exe | executable | |
MD5:9254CA1DA9FF8AD492CA5FA06CA181C6 | SHA256:30676AD5DC94C3FEC3D77D87439B2BF0A1AAA7F01900B68002A06F11CAEE9CE6 | |||
| 3172 | cmd.exe | C:\Users\admin\AppData\Local\Temp\6E17.tmp\x.vbs | text | |
MD5:0F320E5C2A87D656A7D7439FA8E83DEE | SHA256:EE7FDAEE23205B431FA7032EF0800CBEEE8B60DACC23278B1953EA1A6B850B90 | |||
| 2848 | HorrorTrojan.exe | C:\Users\admin\AppData\Local\Temp\6E17.tmp\CLWCP.exe | executable | |
MD5:E62EE6F1EFC85CB36D62AB779DB6E4EC | SHA256:13B4EC59785A1B367EFB691A3D5C86EB5AAF1CA0062521C4782E1BAAC6633F8A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2640 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |