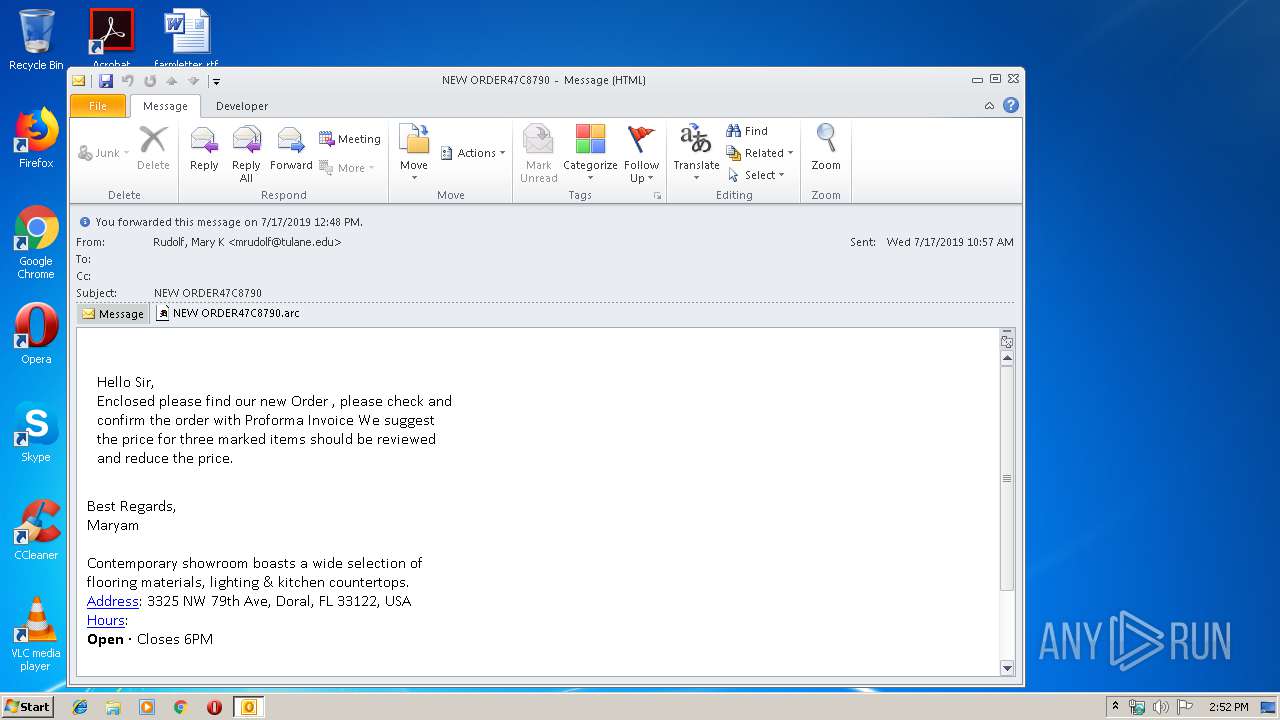
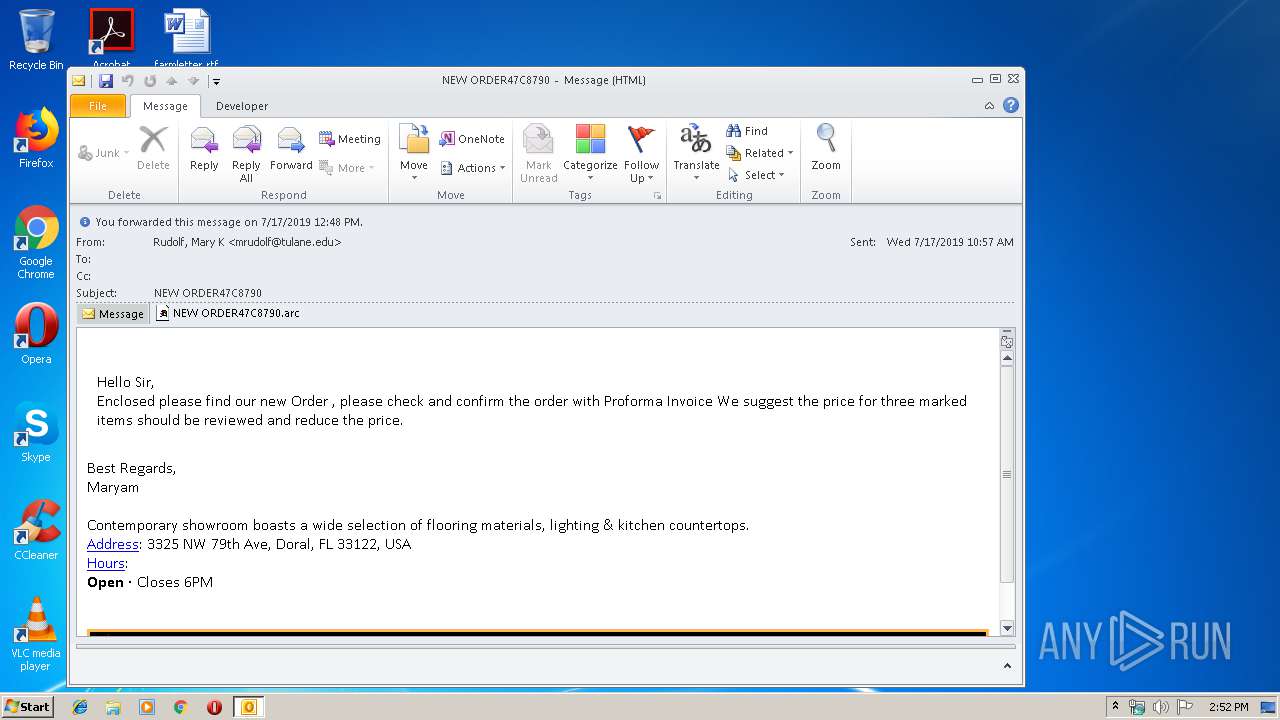
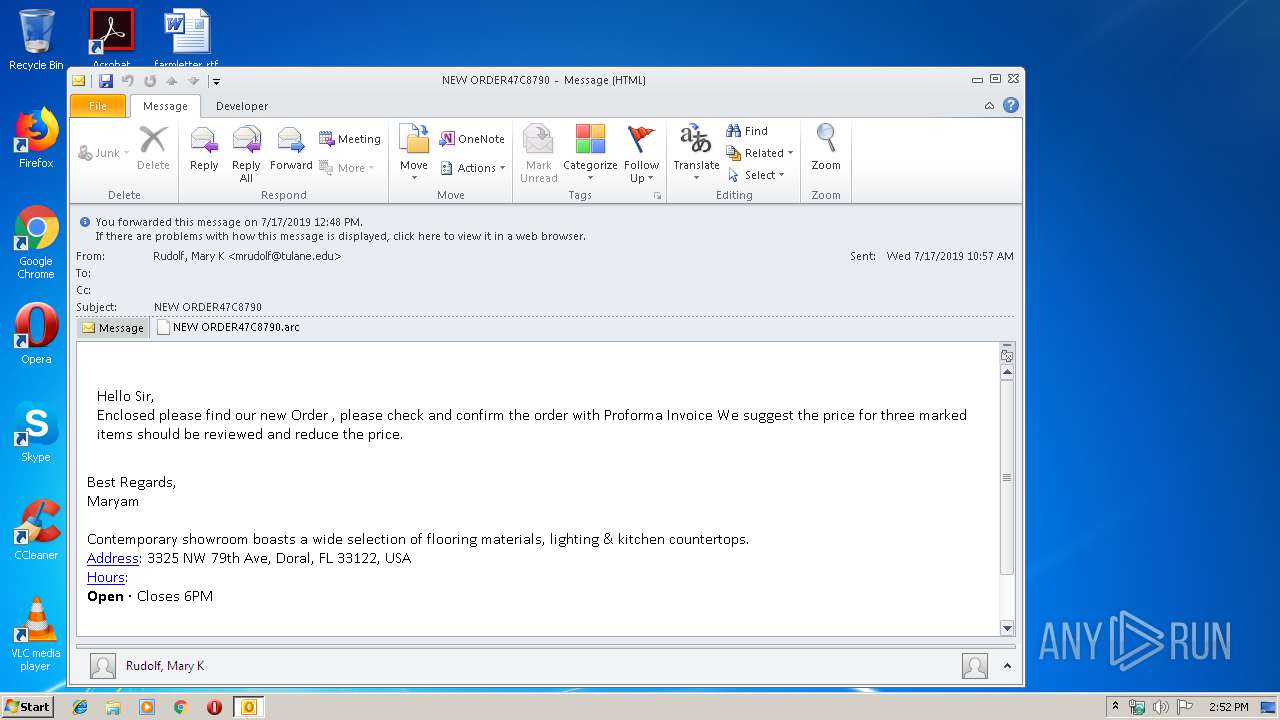
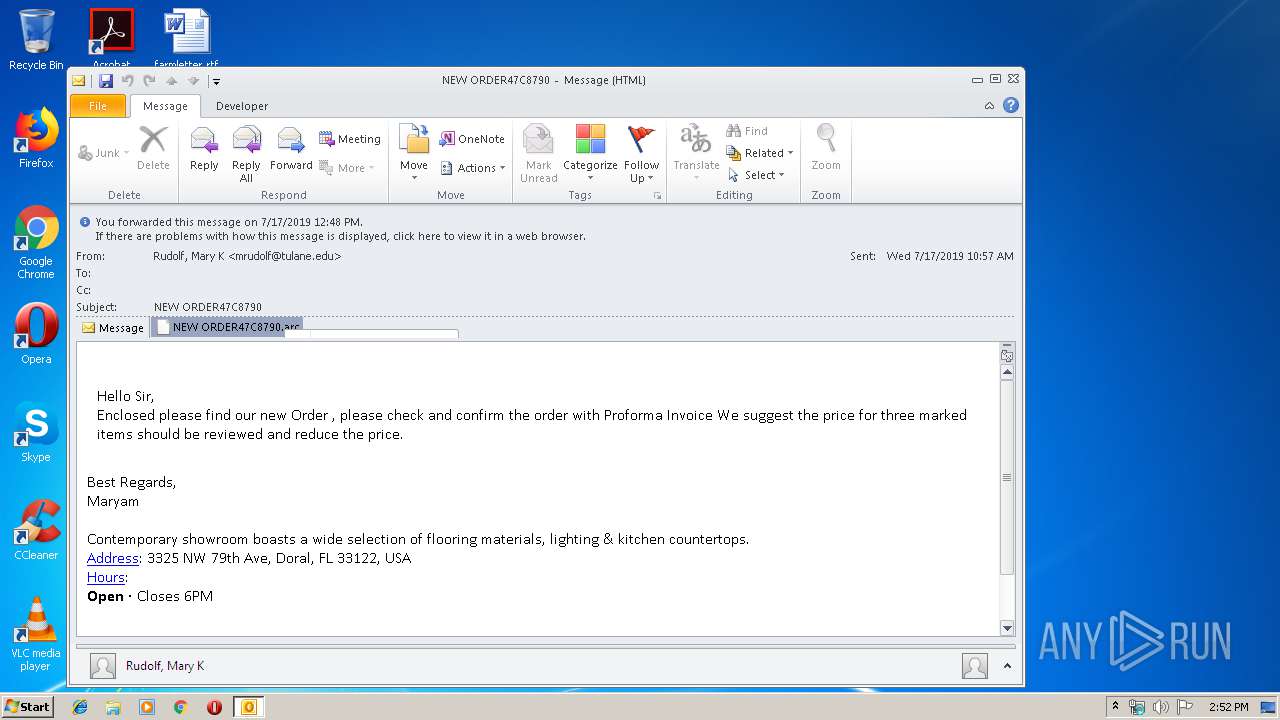
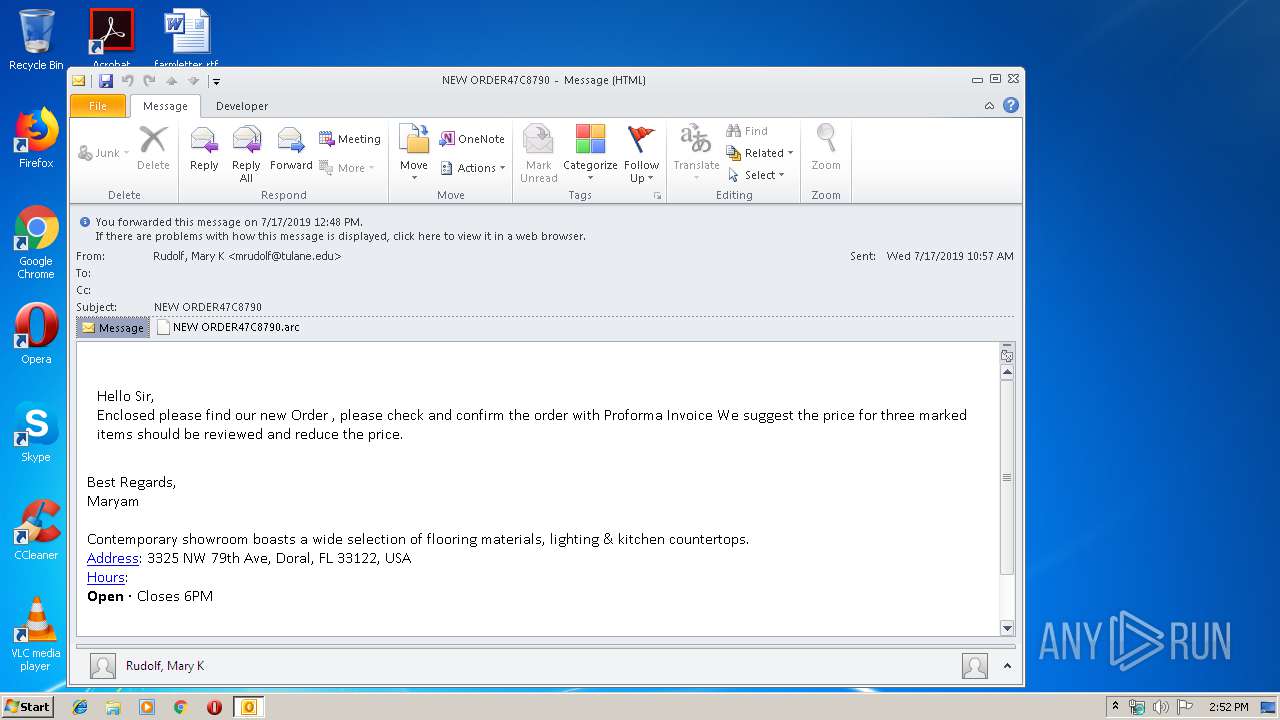
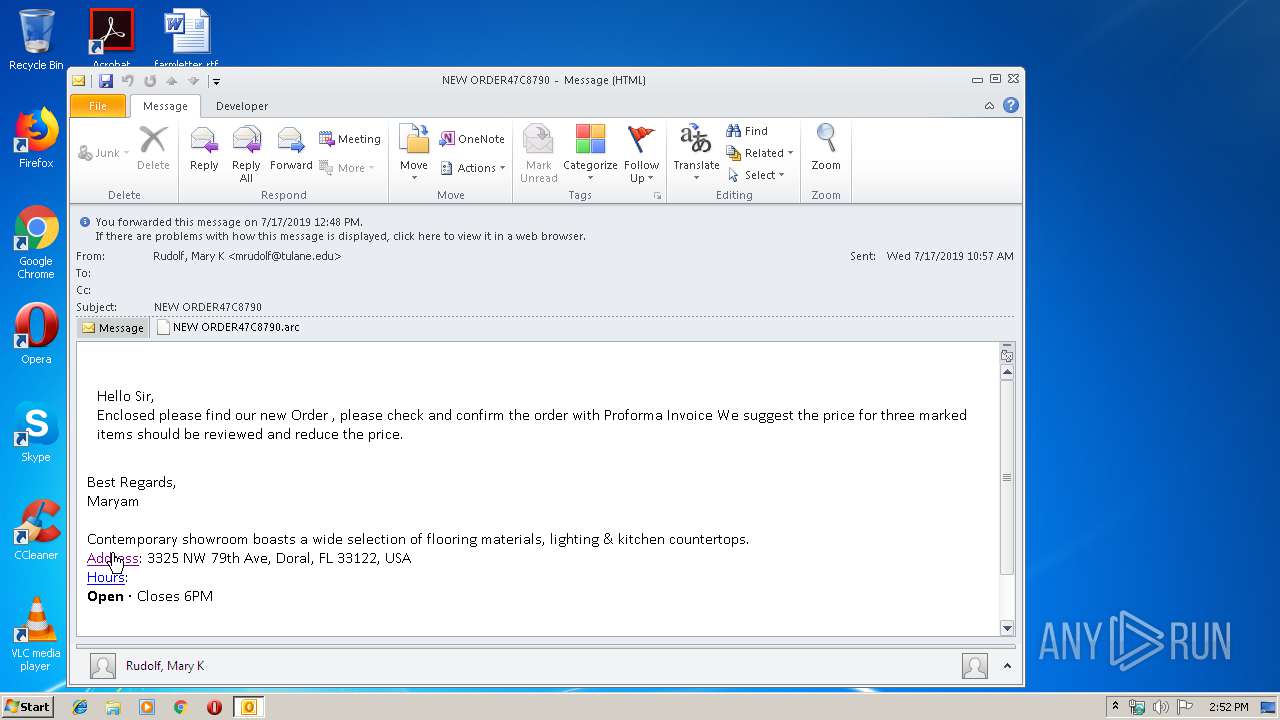
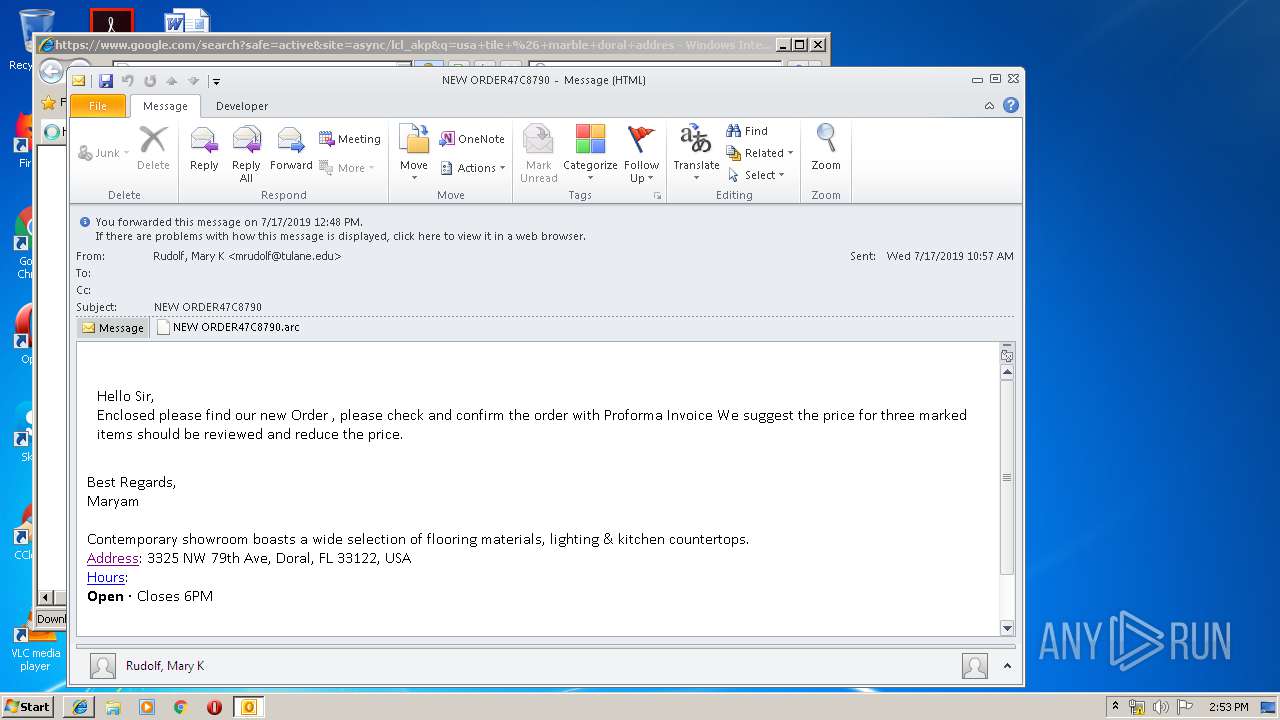
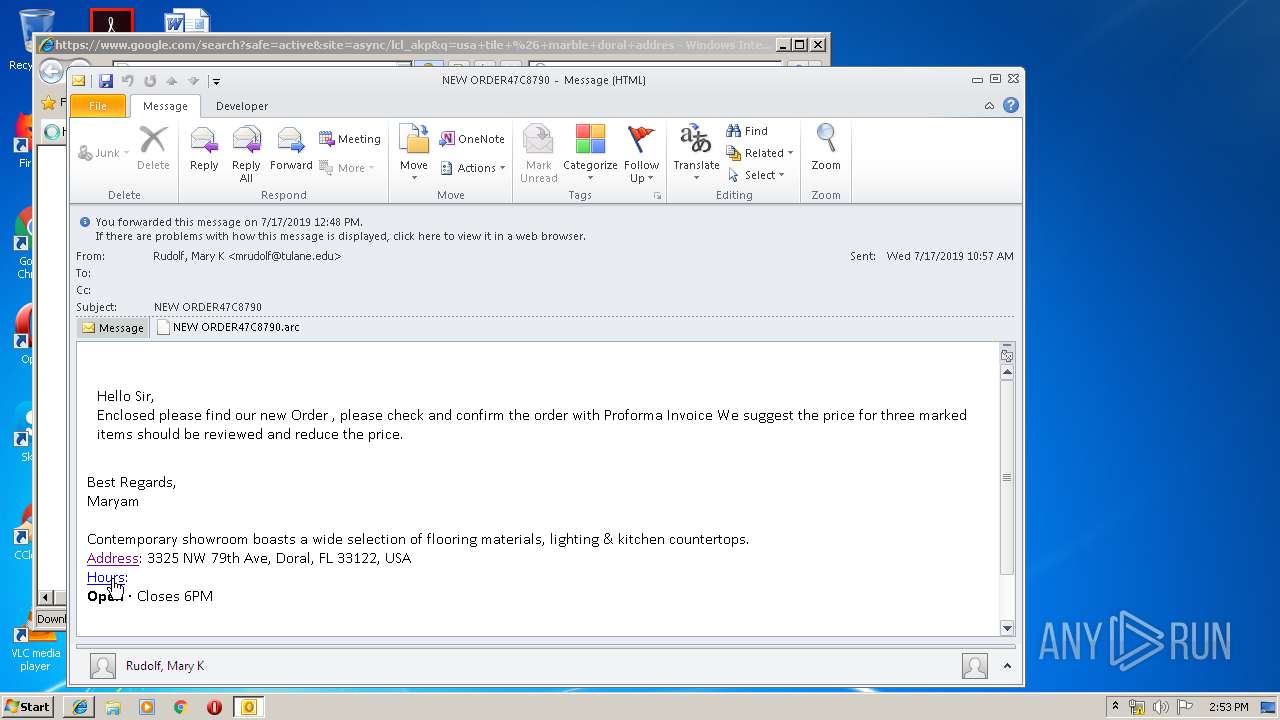
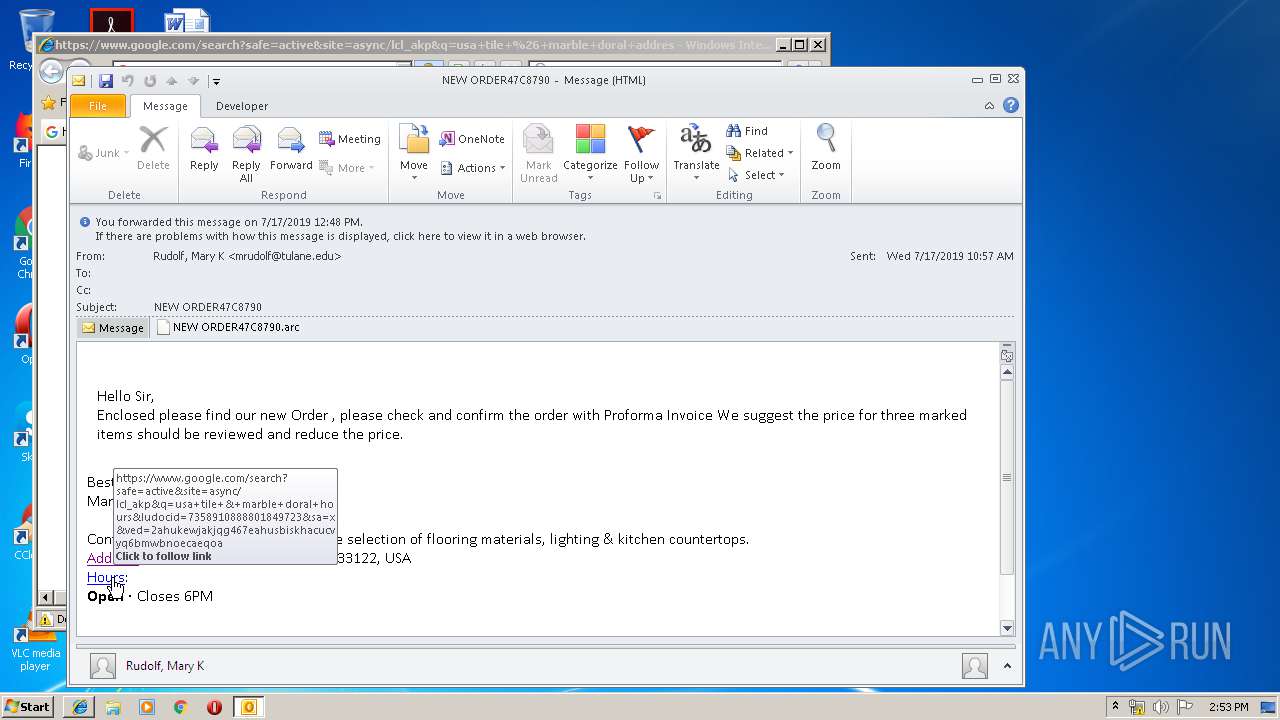
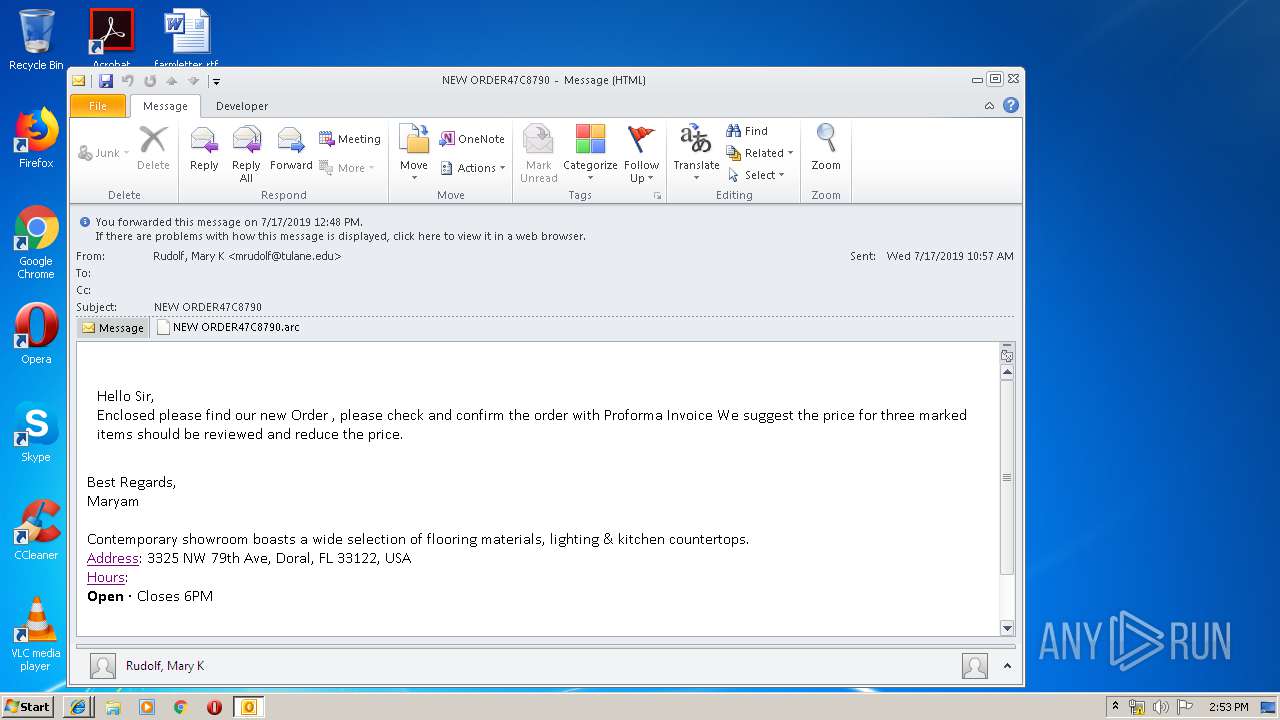
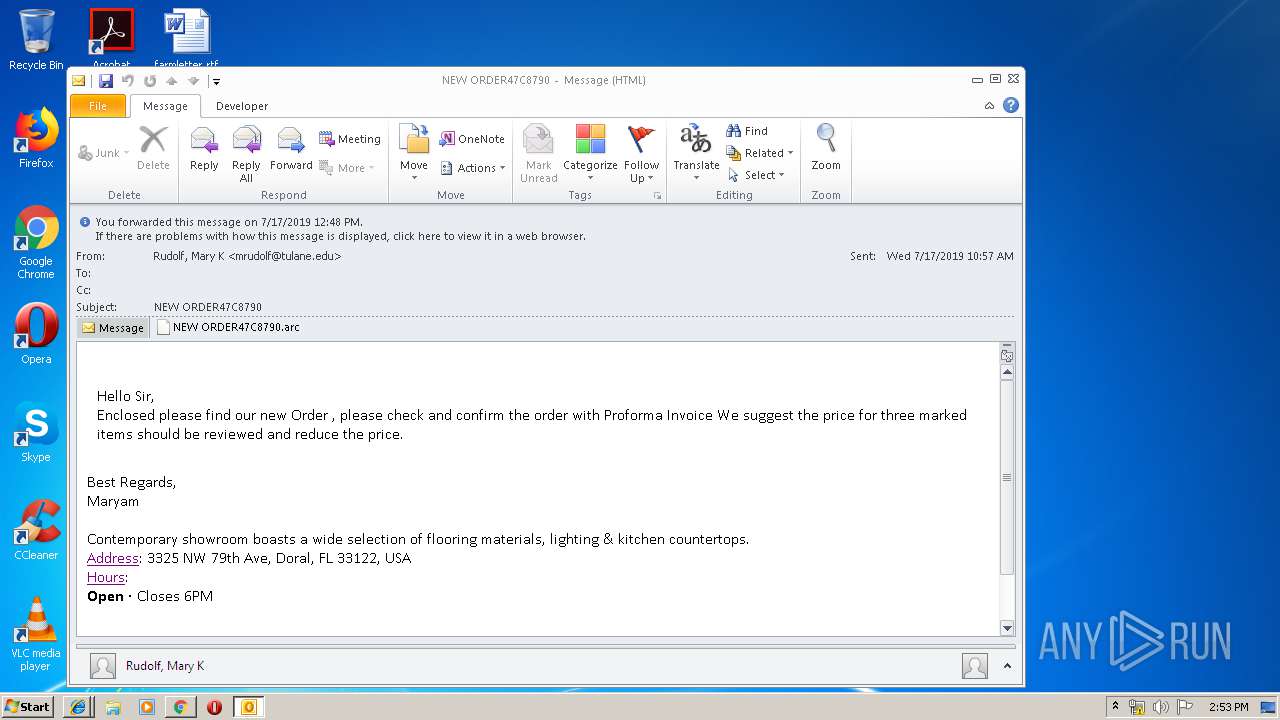
| File name: | NEW ORDER47C8790.msg |
| Full analysis: | https://app.any.run/tasks/b88c4823-b183-4c41-917b-1a2fa4c6cf07 |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 13:51:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 6342AE3C9487056BE3747BED5565A973 |
| SHA1: | 522677DC937A09273873FEA35D7CE19C74AEE2A4 |
| SHA256: | FE724F992090BC15B6761117592BCFC86612F38579FF01F7258D86252642D8BF |
| SSDEEP: | 6144:DYwo+YKi9usRWe00dElE362xuWBf3Wa/PVg2C7cDWx8fP1VGj:0++geEWBua3m2C7GWx8fDU |
MALICIOUS
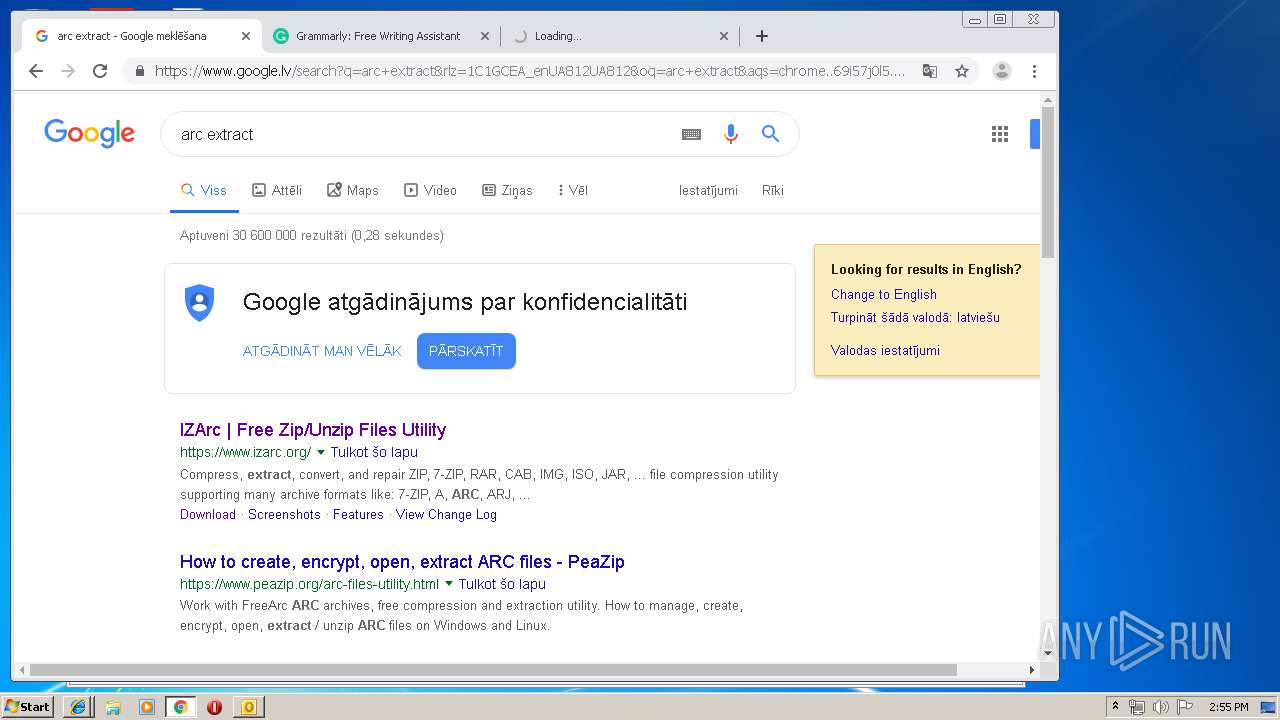
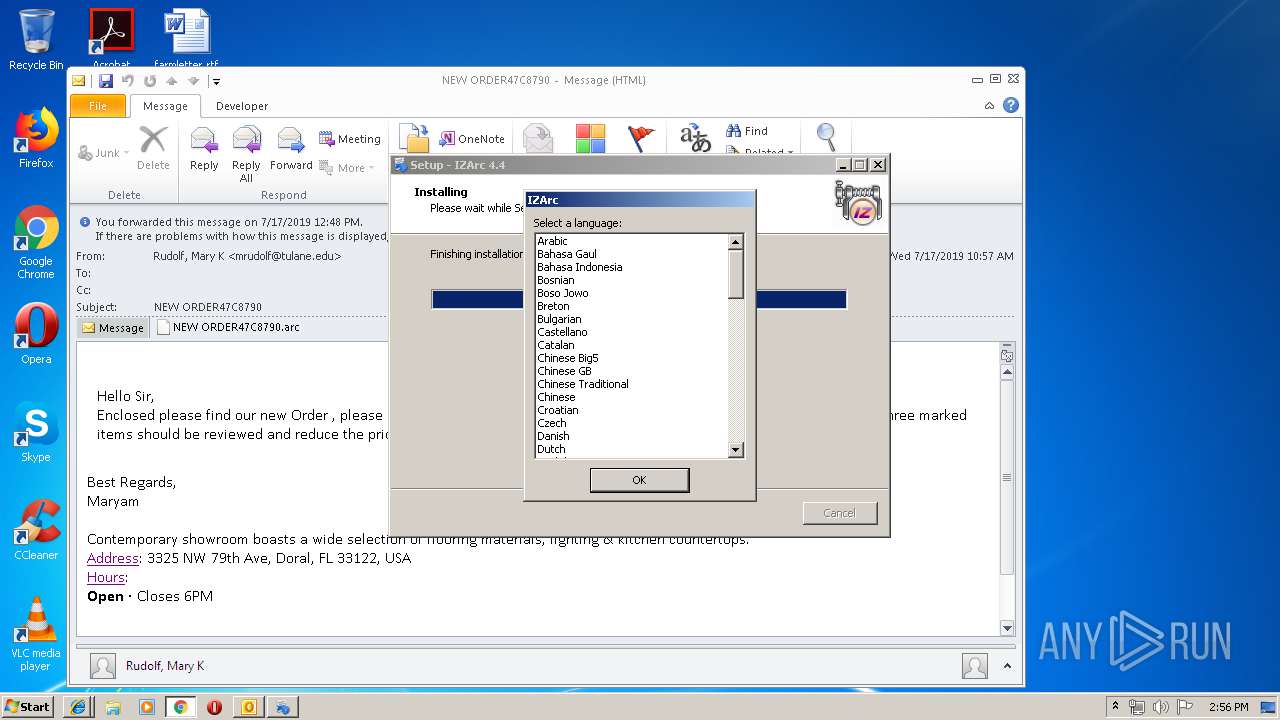
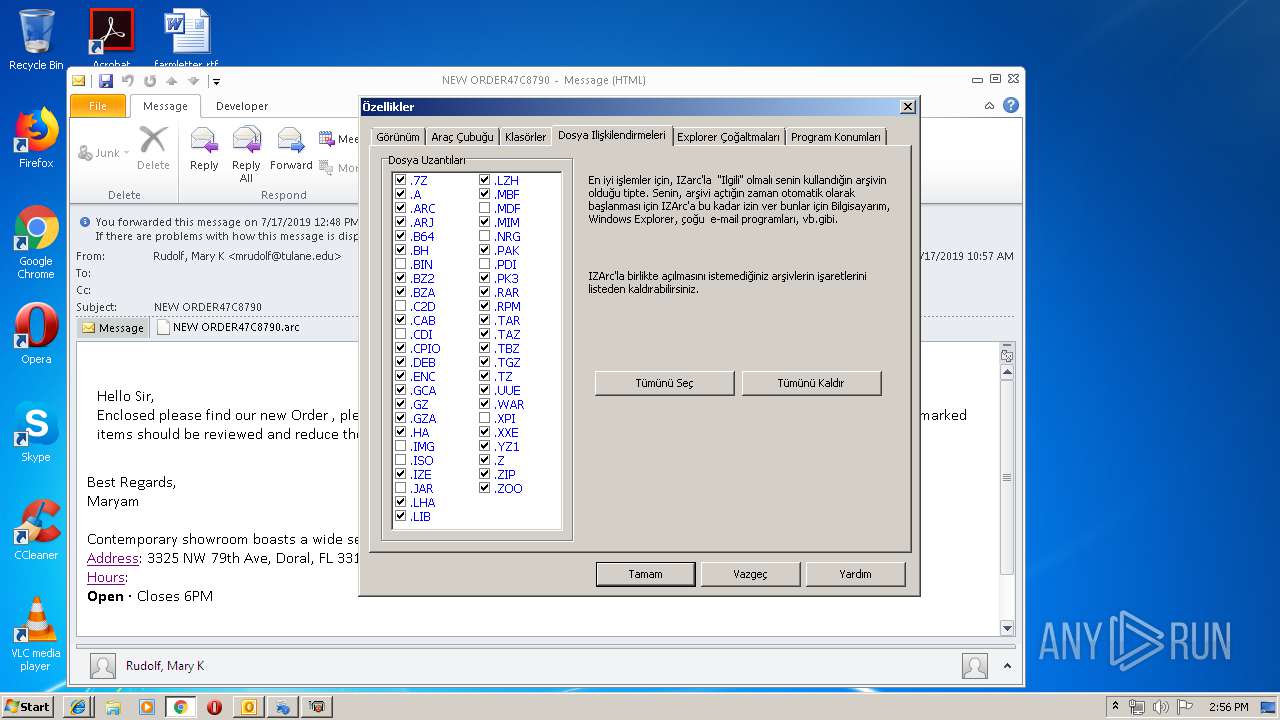
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3412)
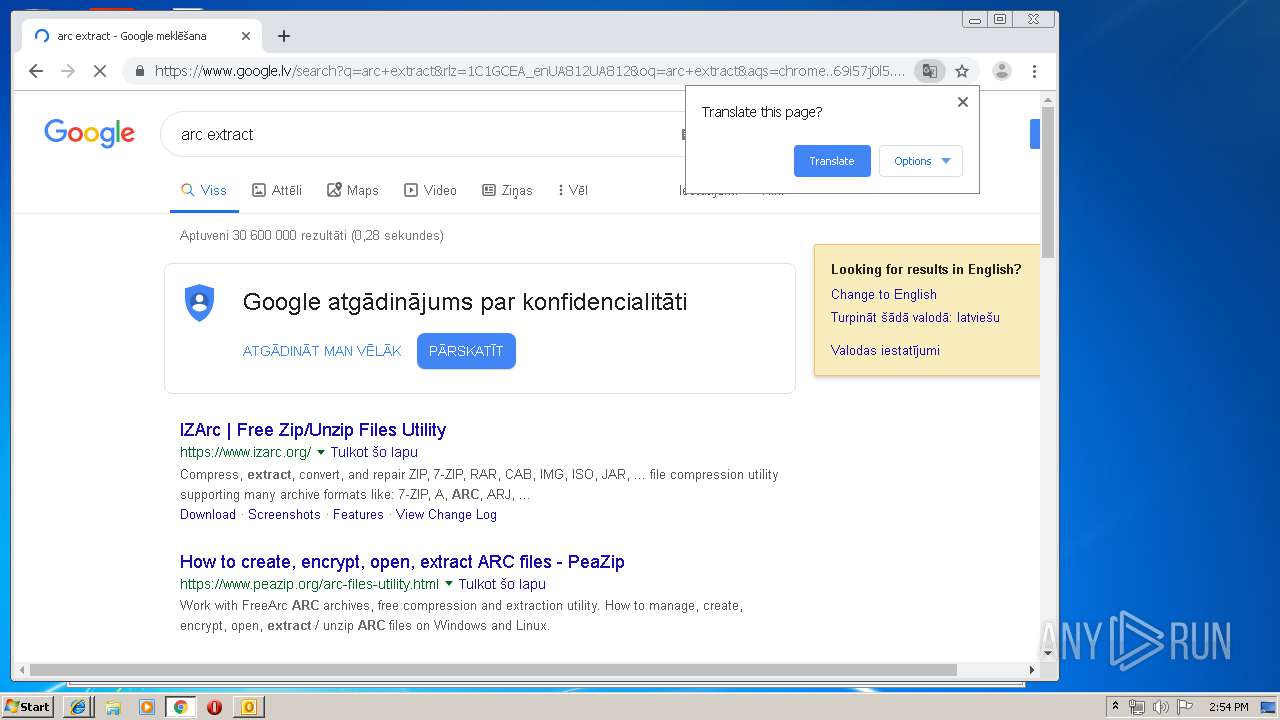
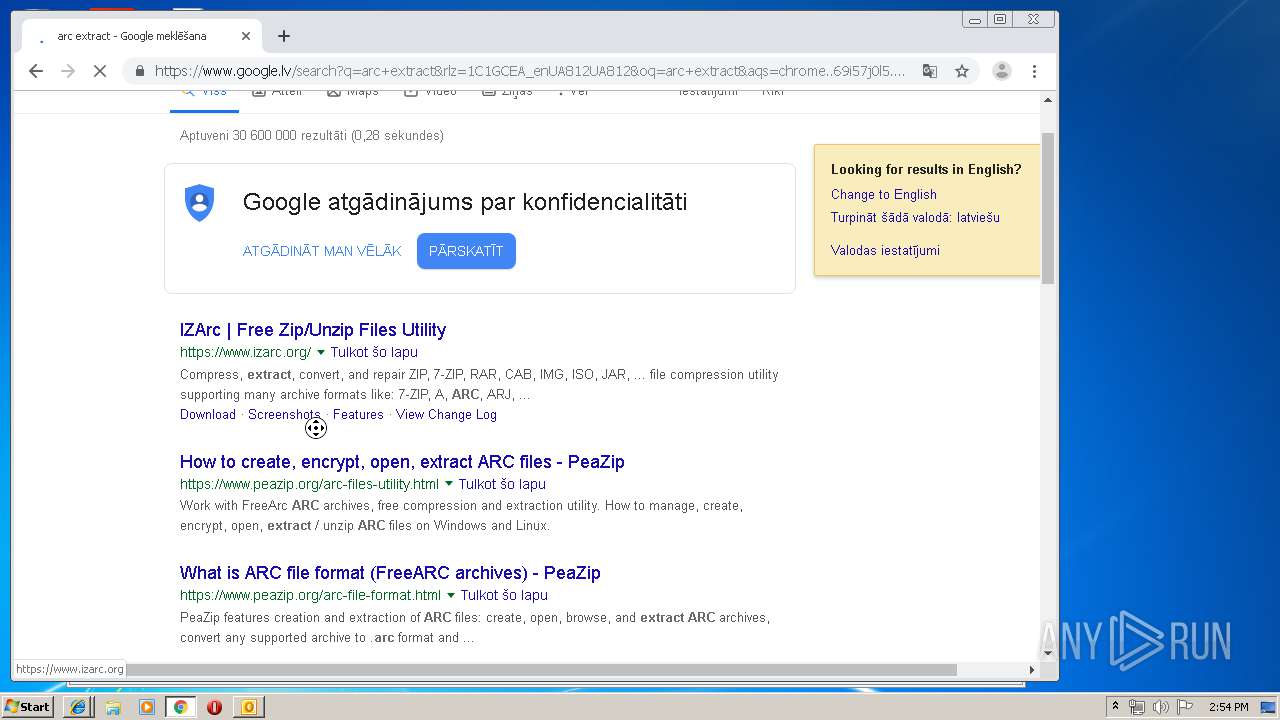
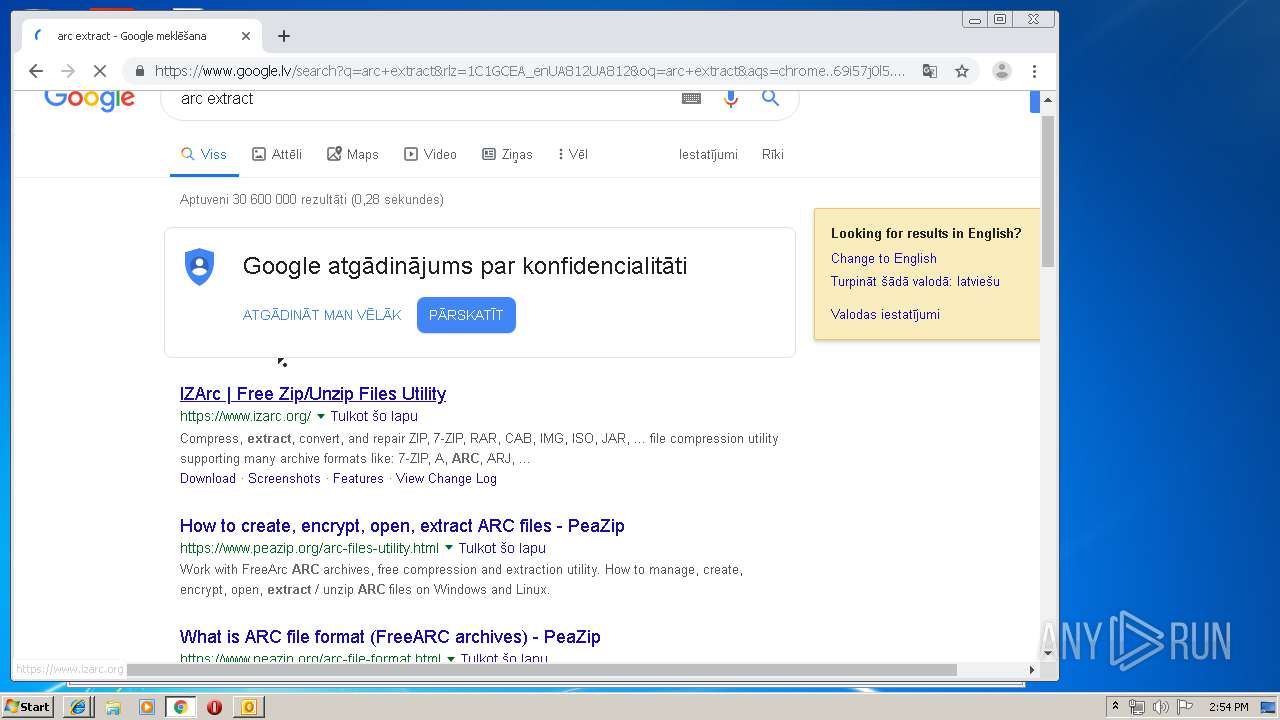
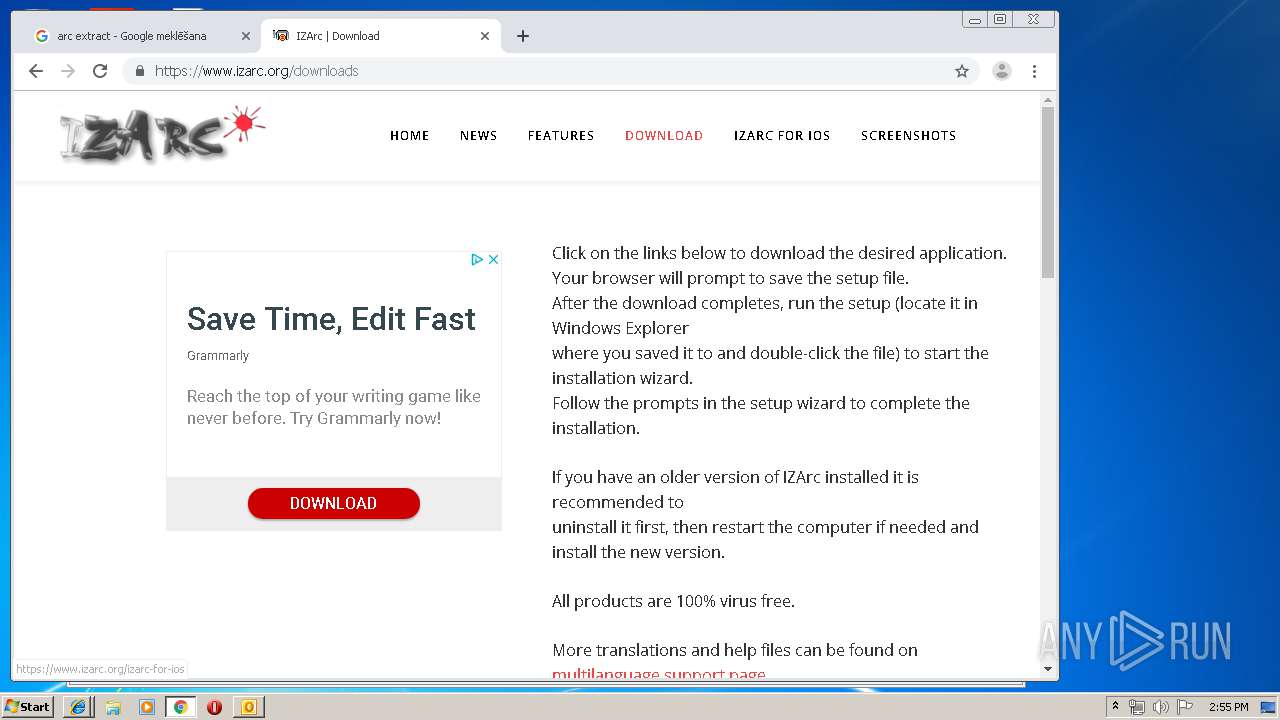
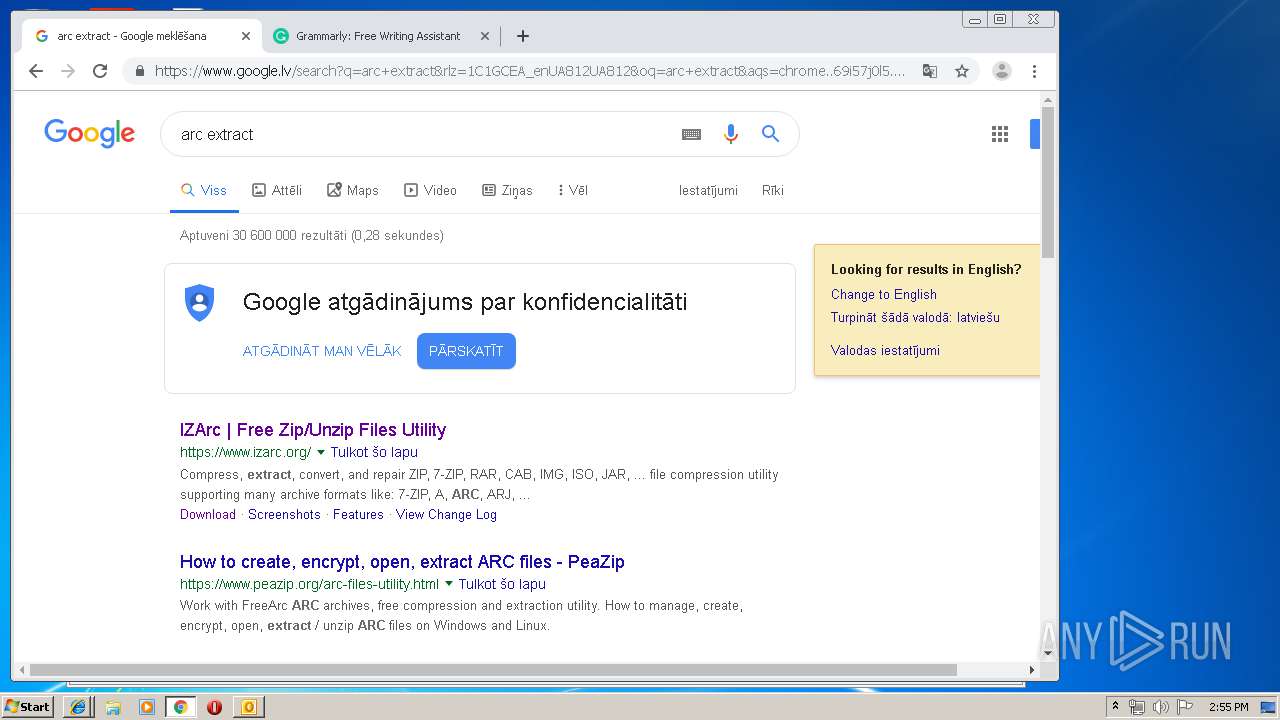
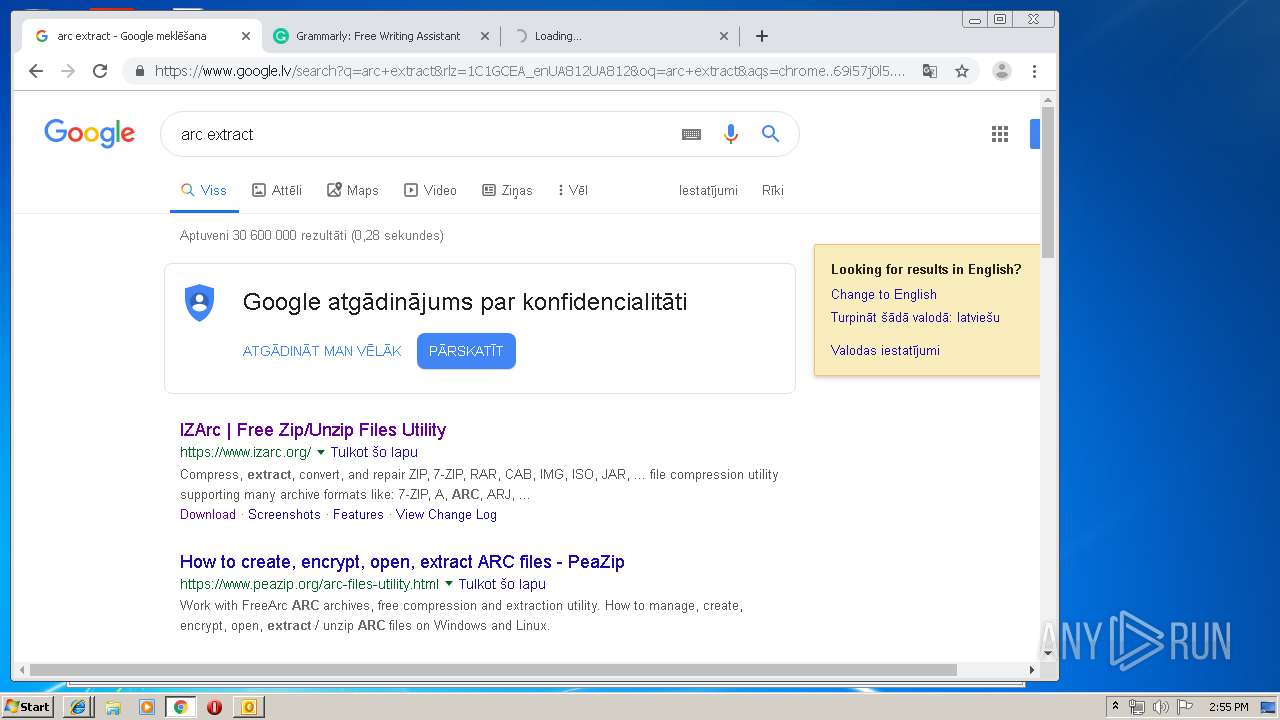
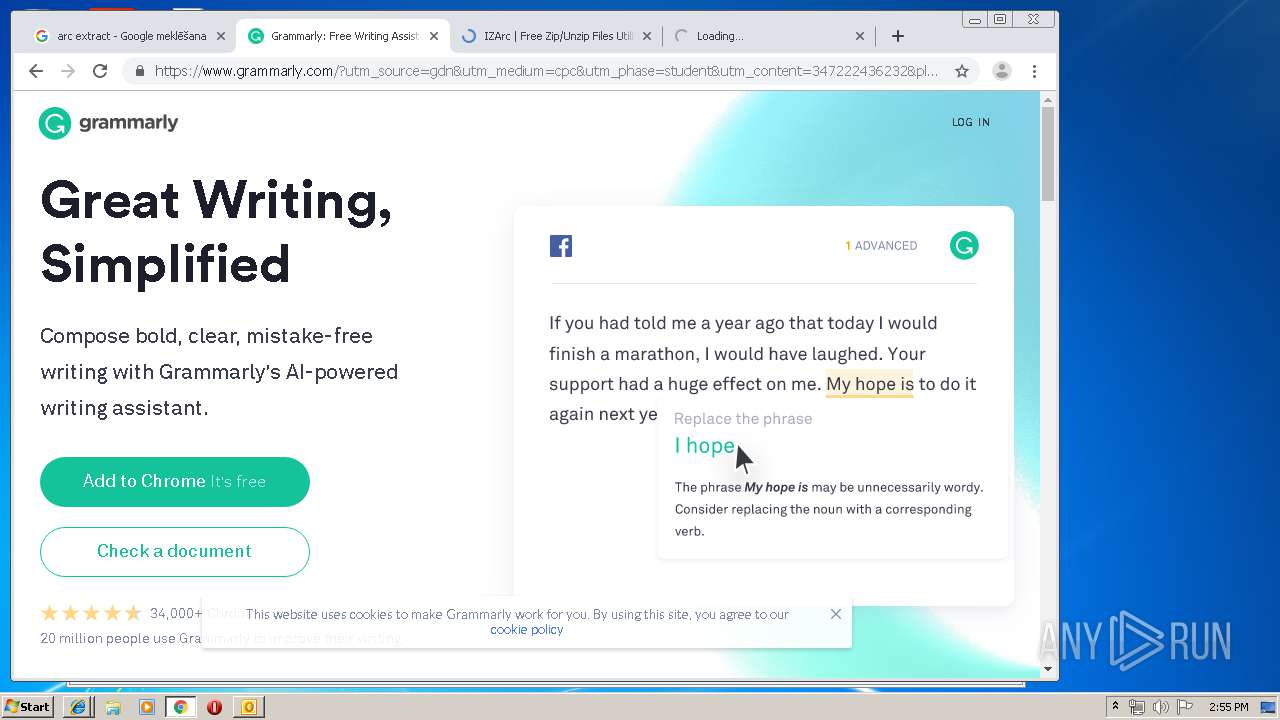
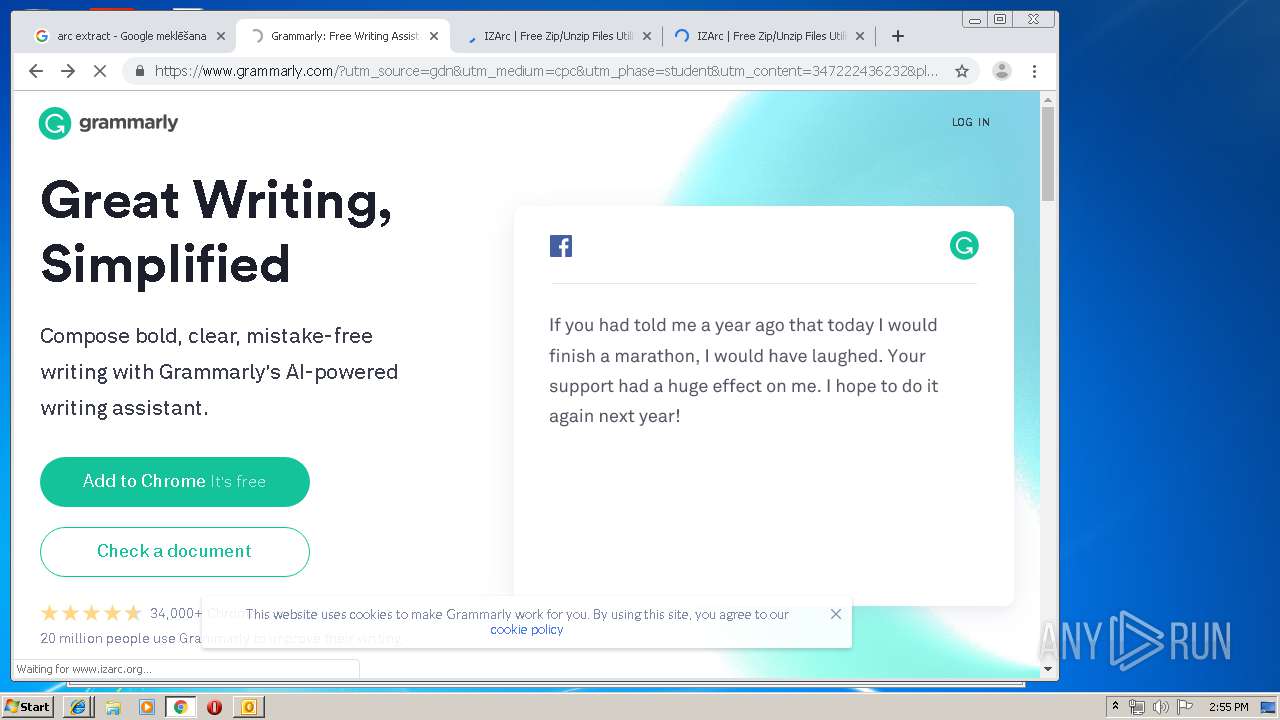
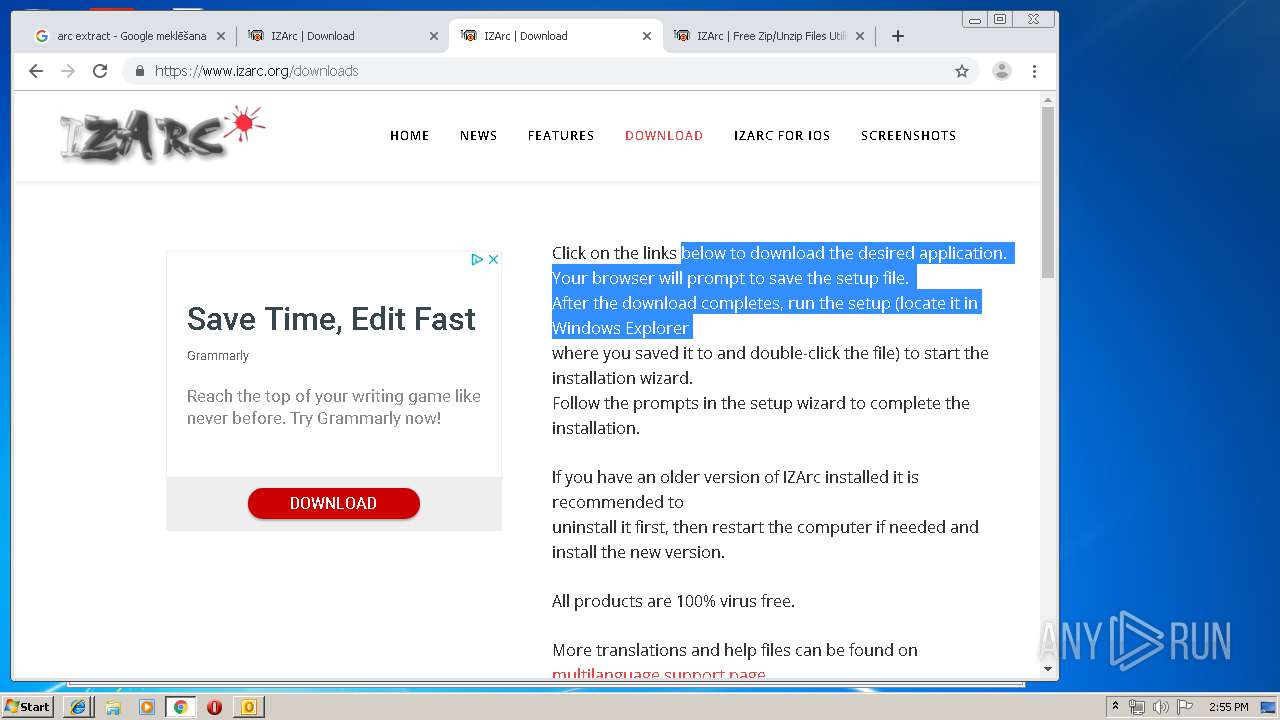
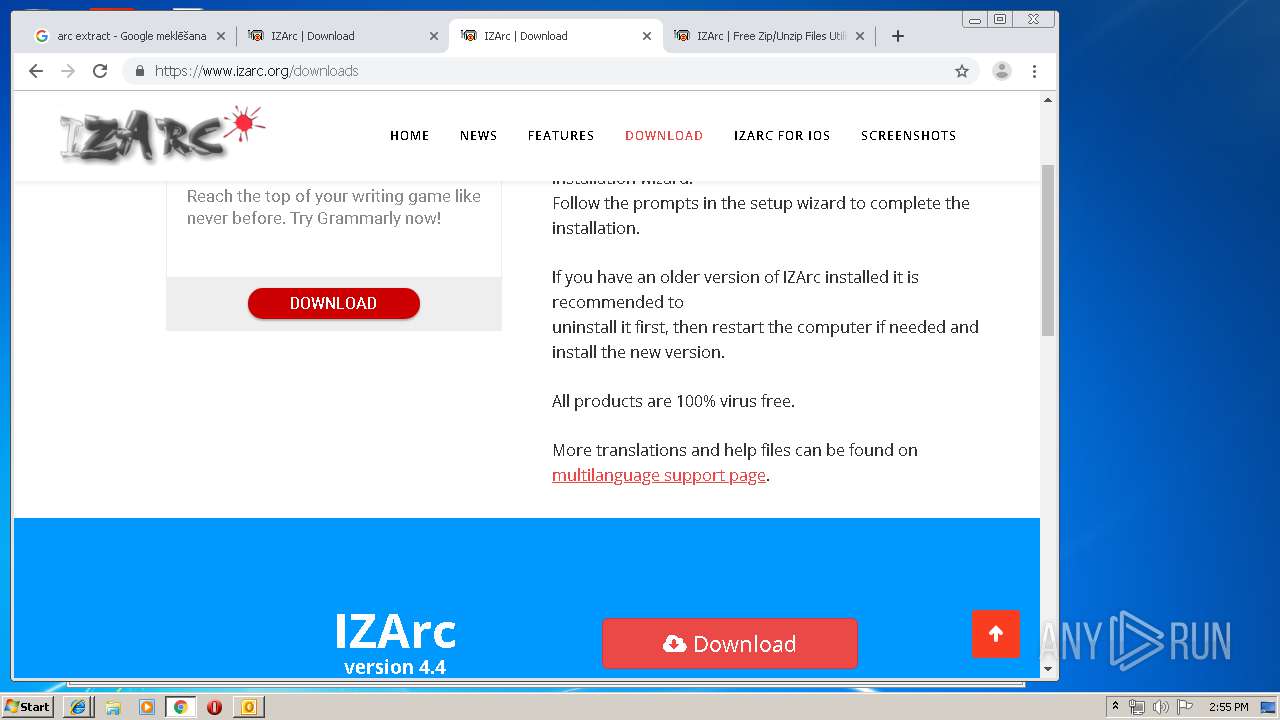
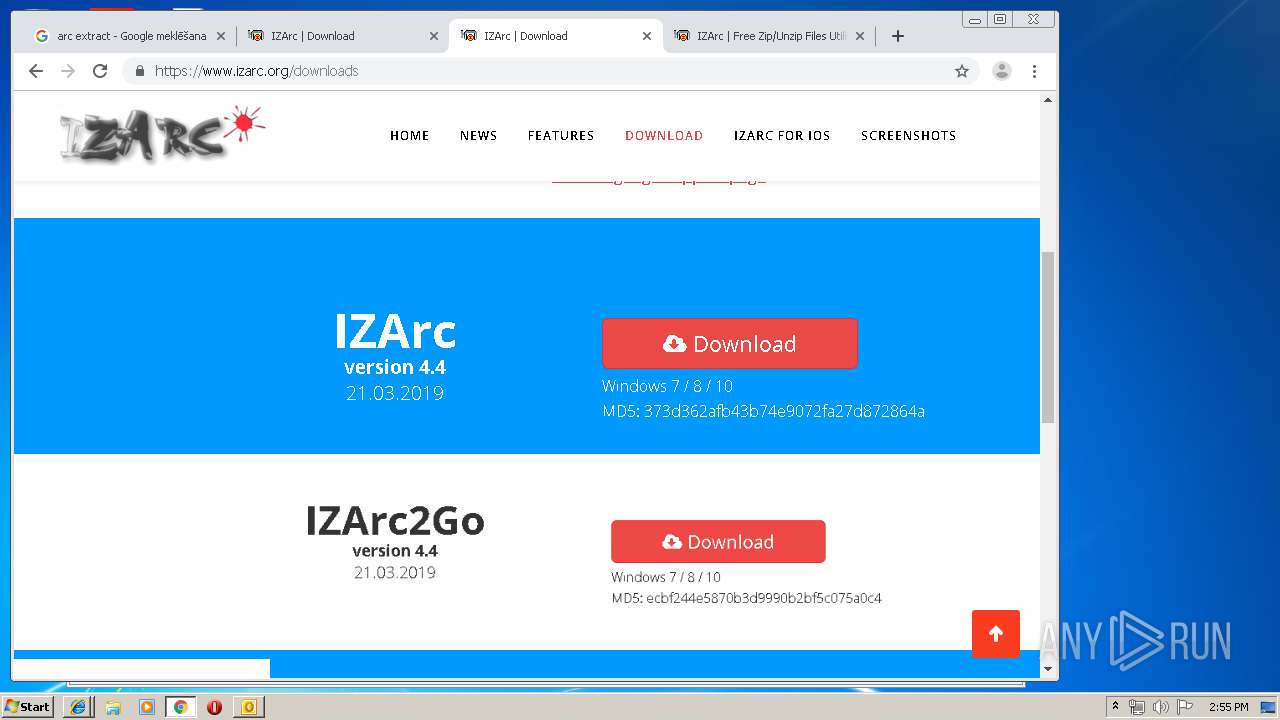
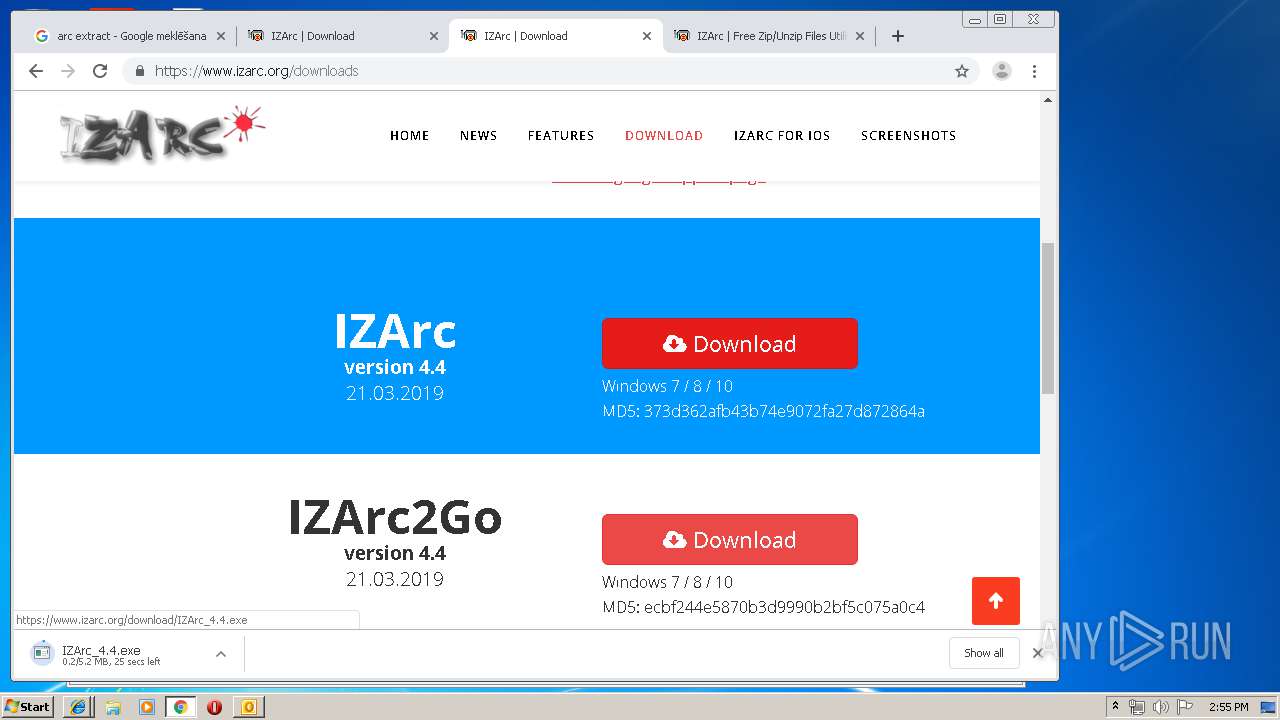
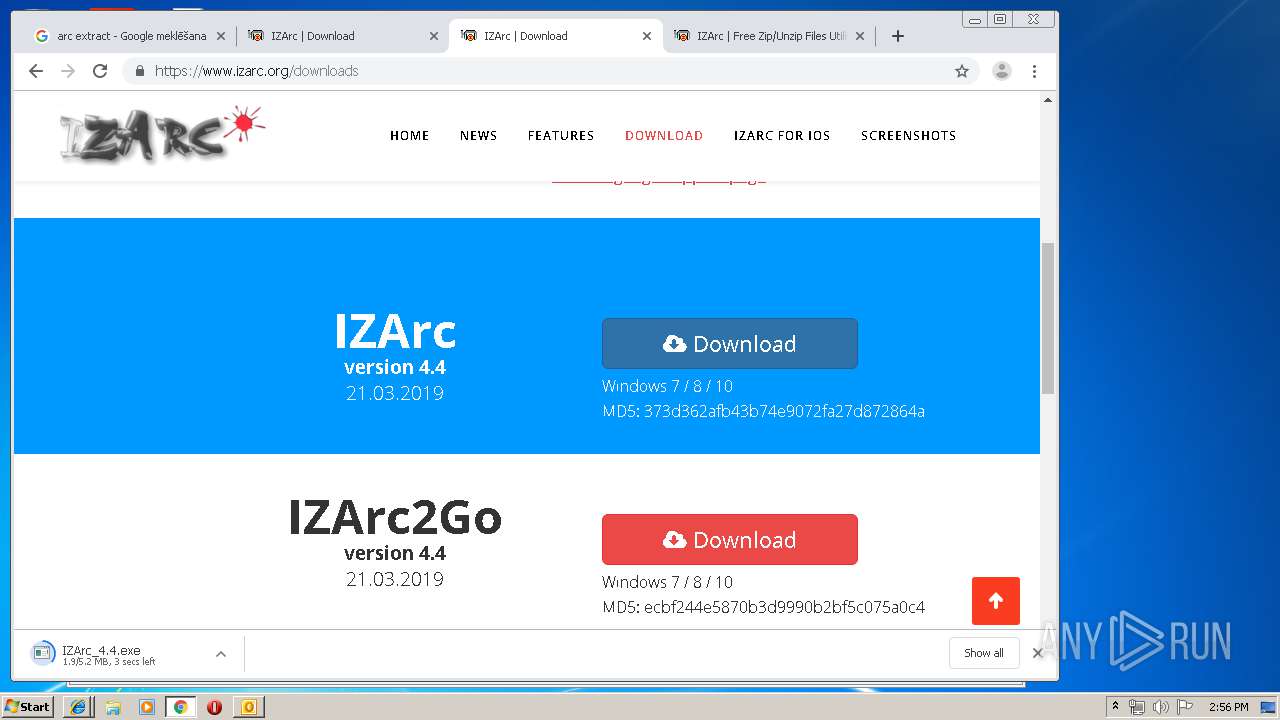
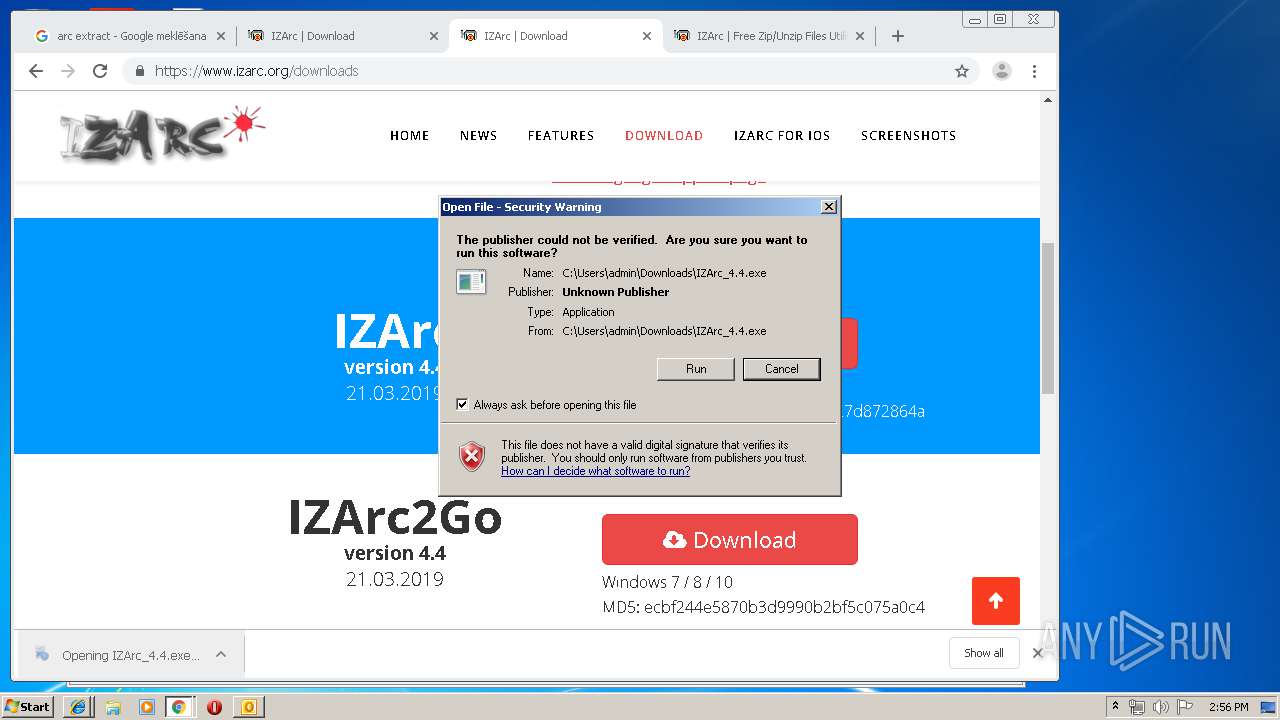
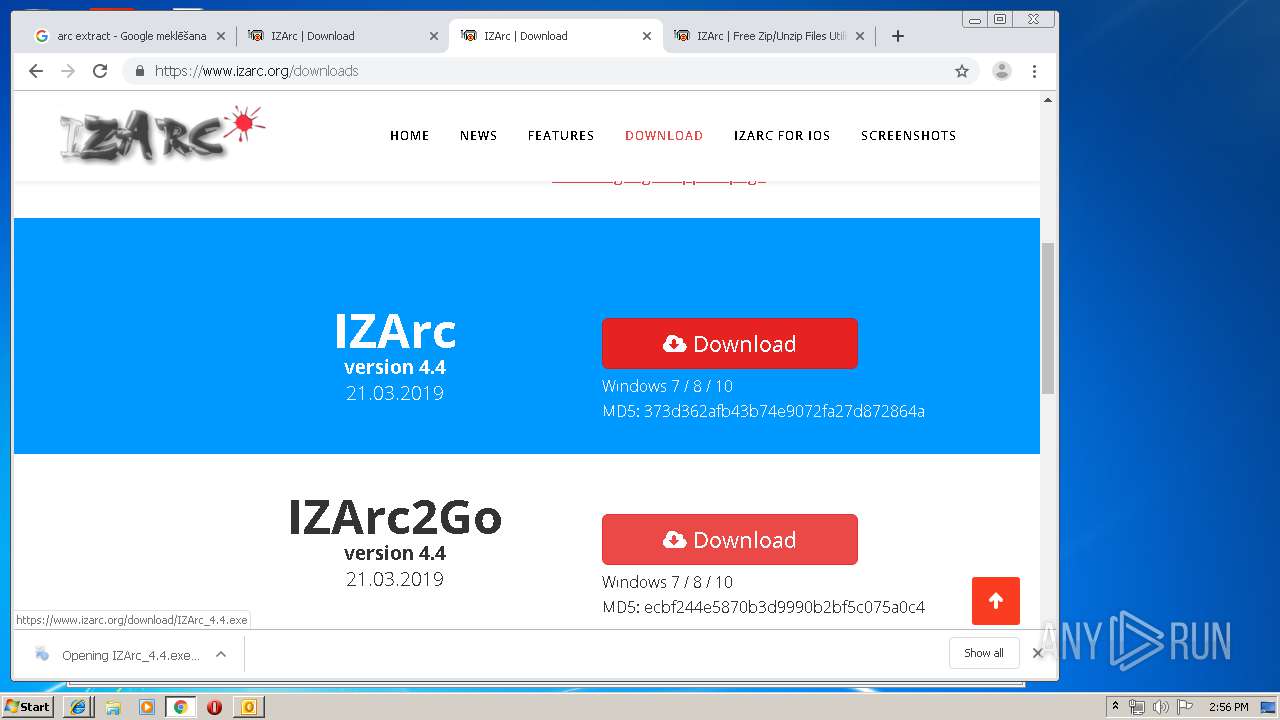
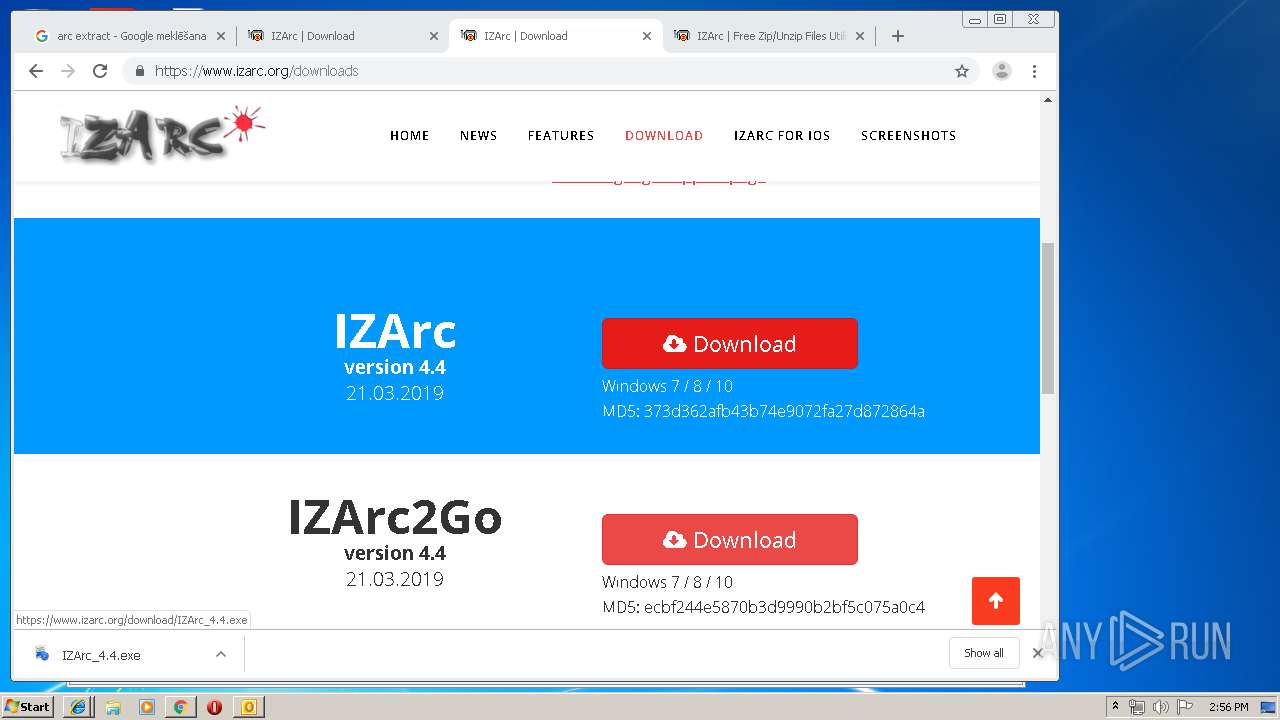
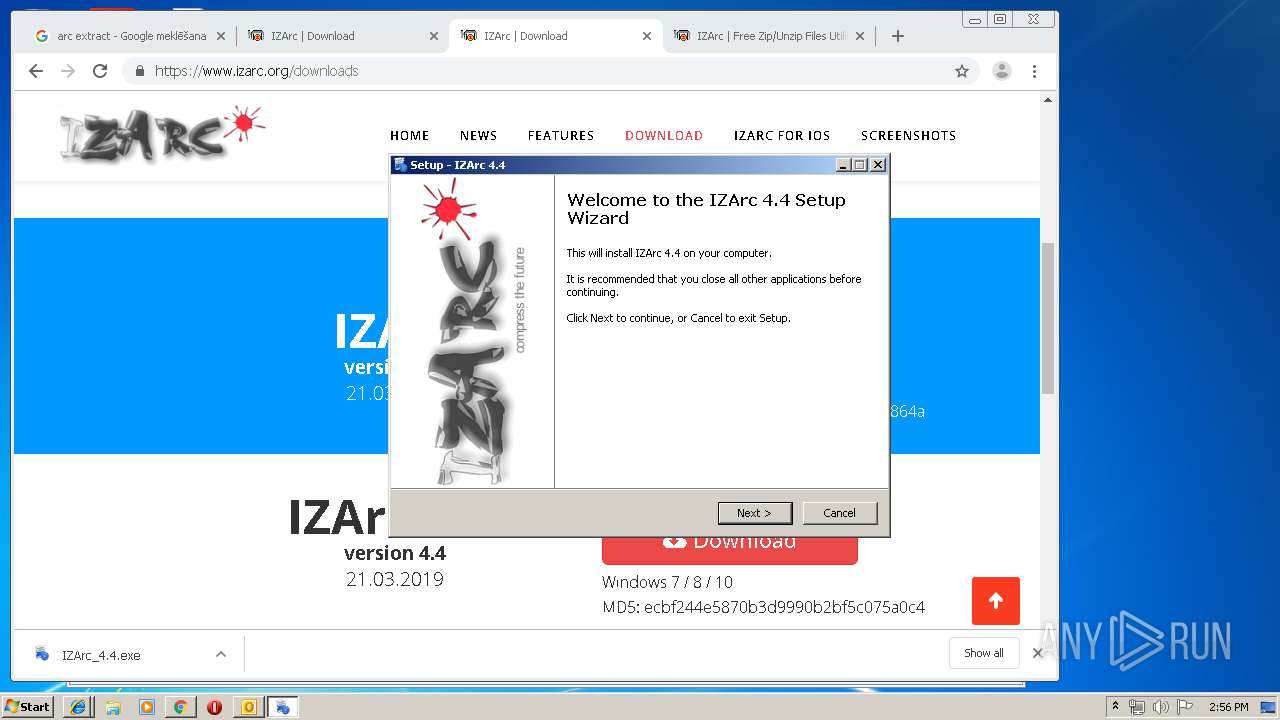
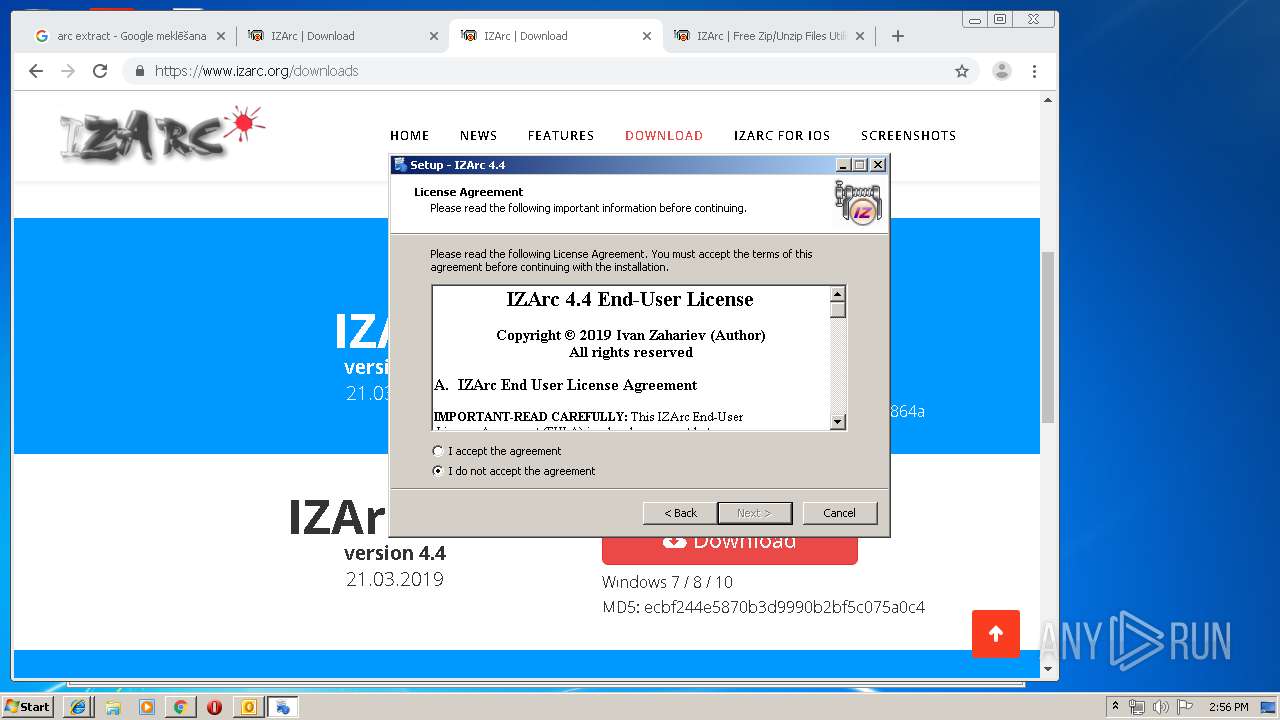
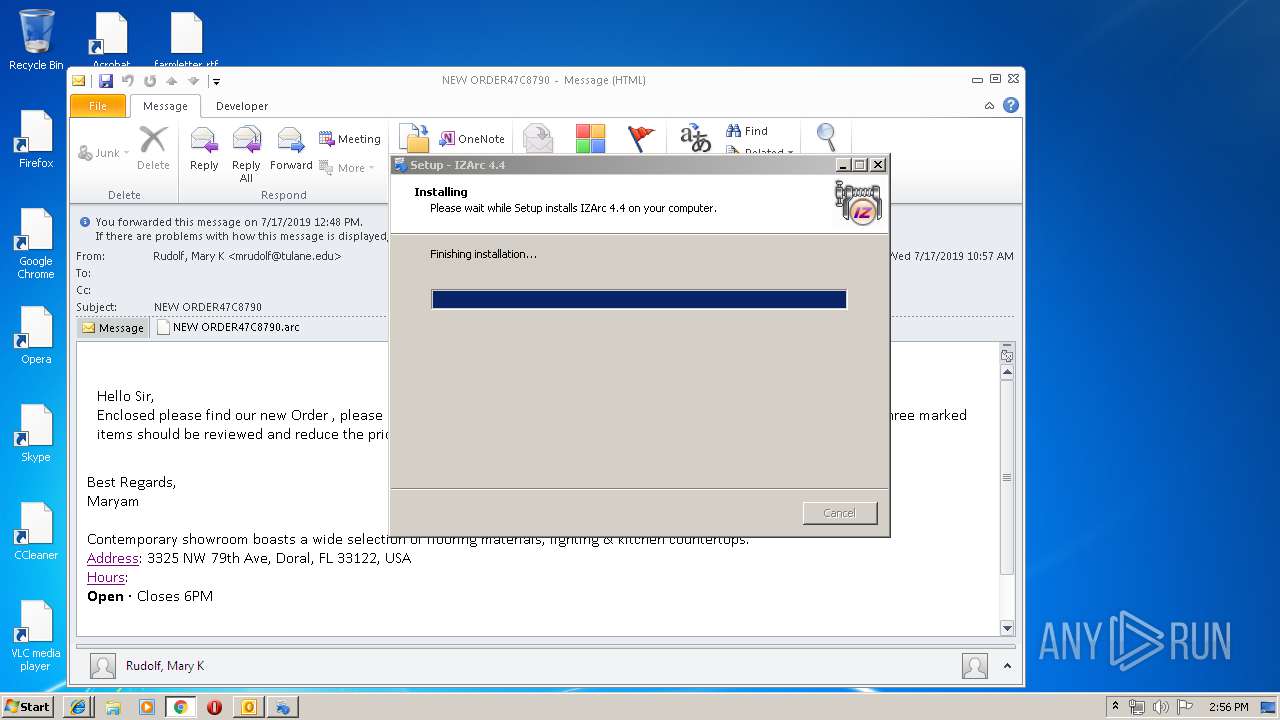
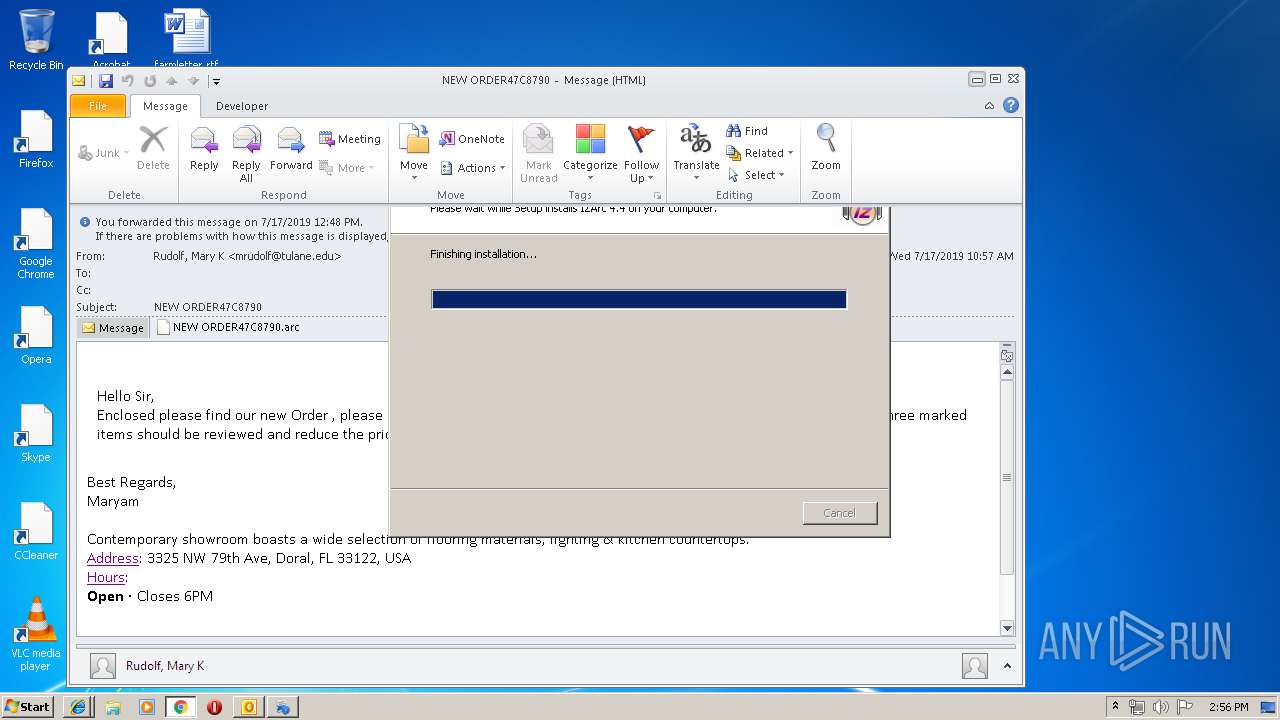
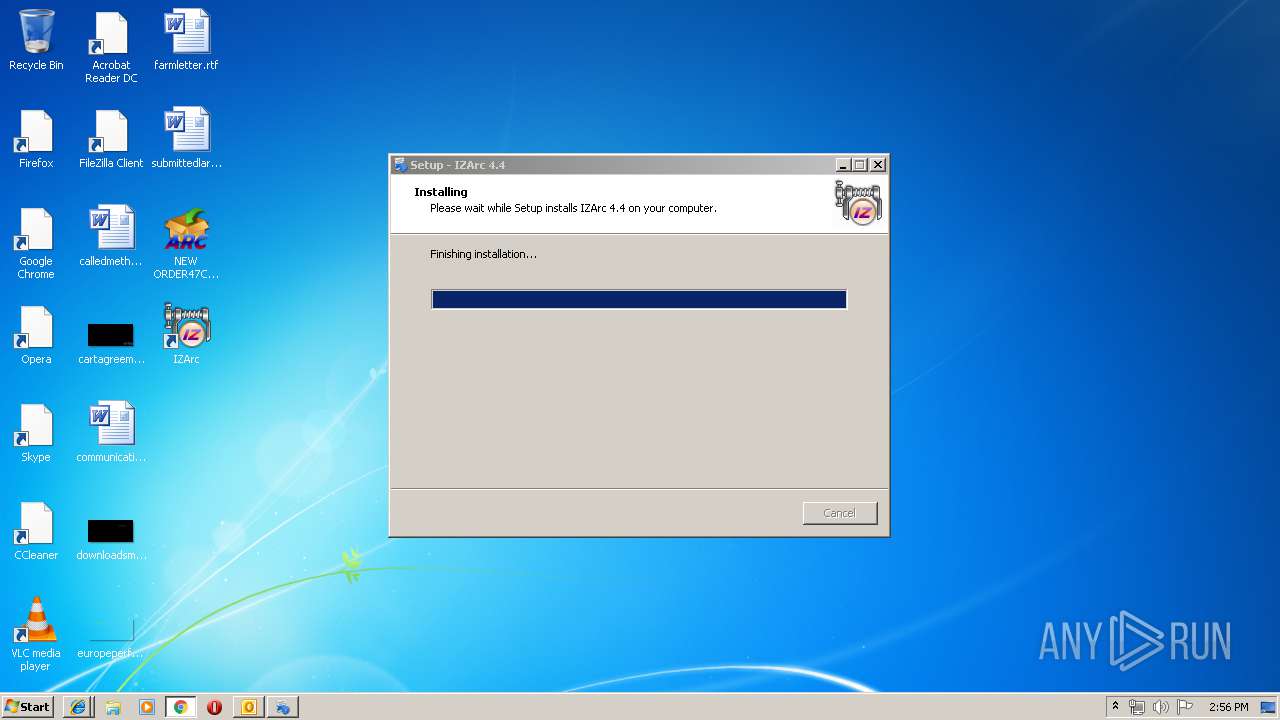
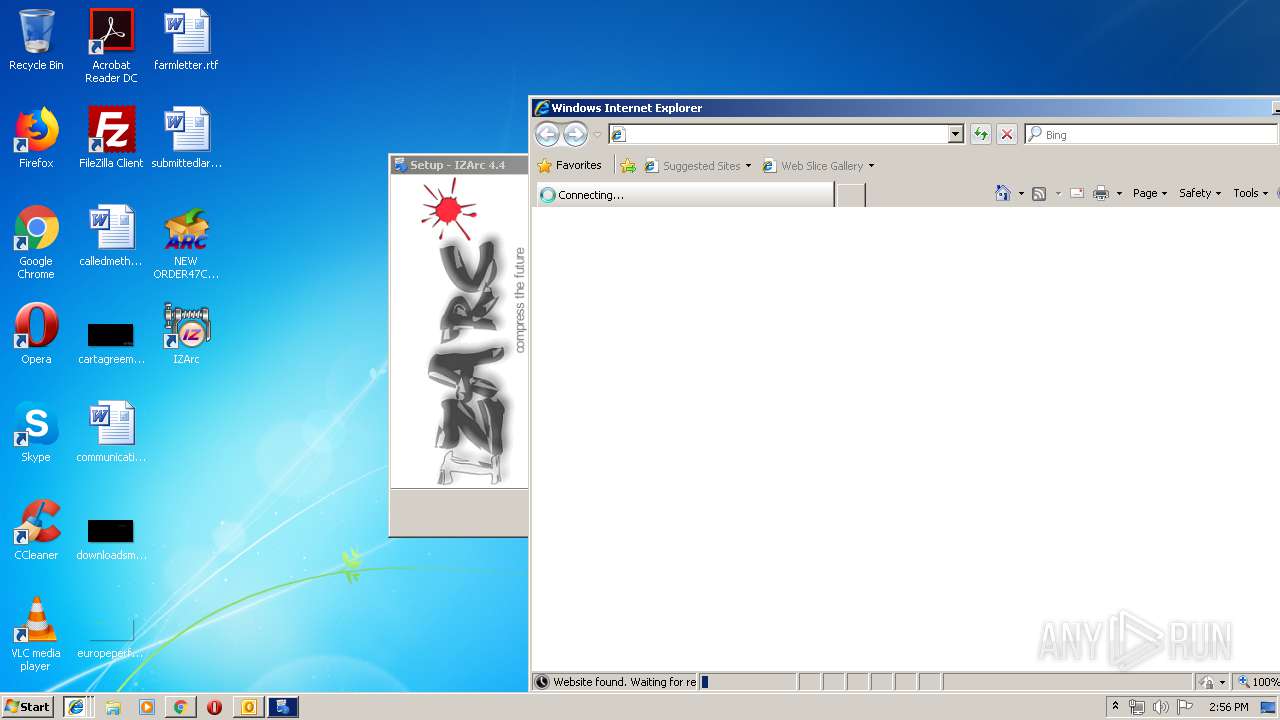
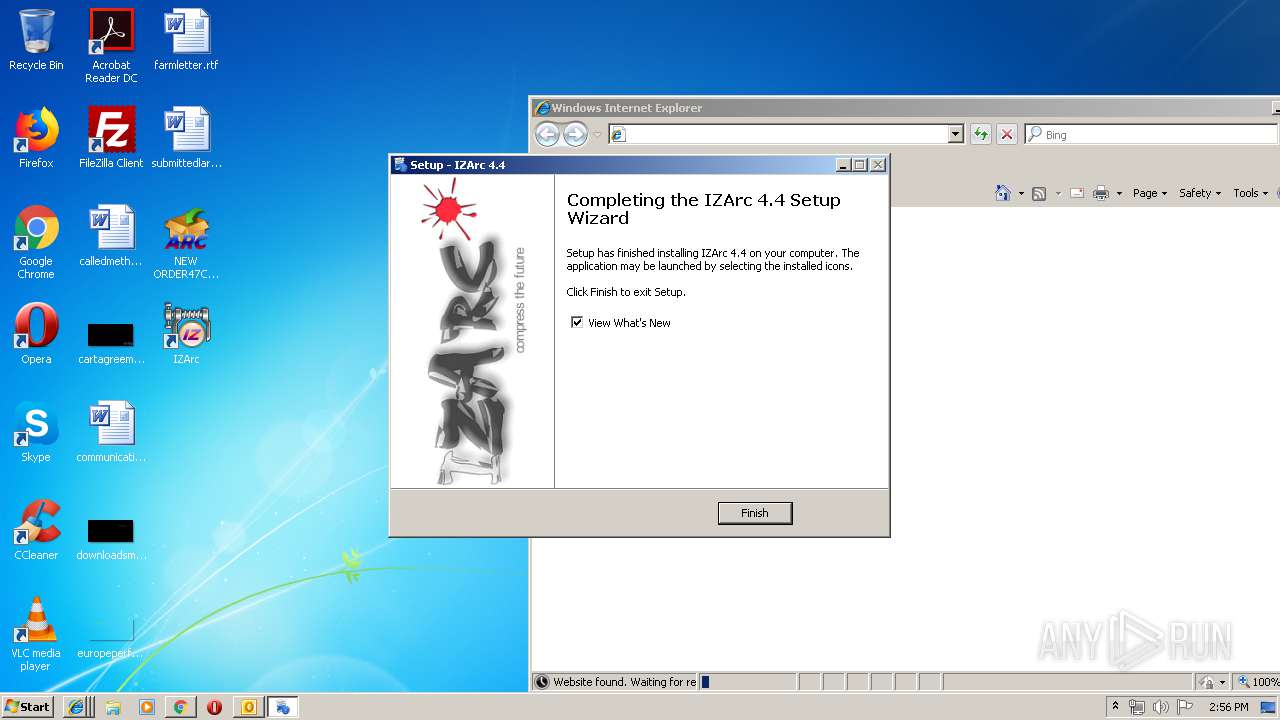
Application was dropped or rewritten from another process
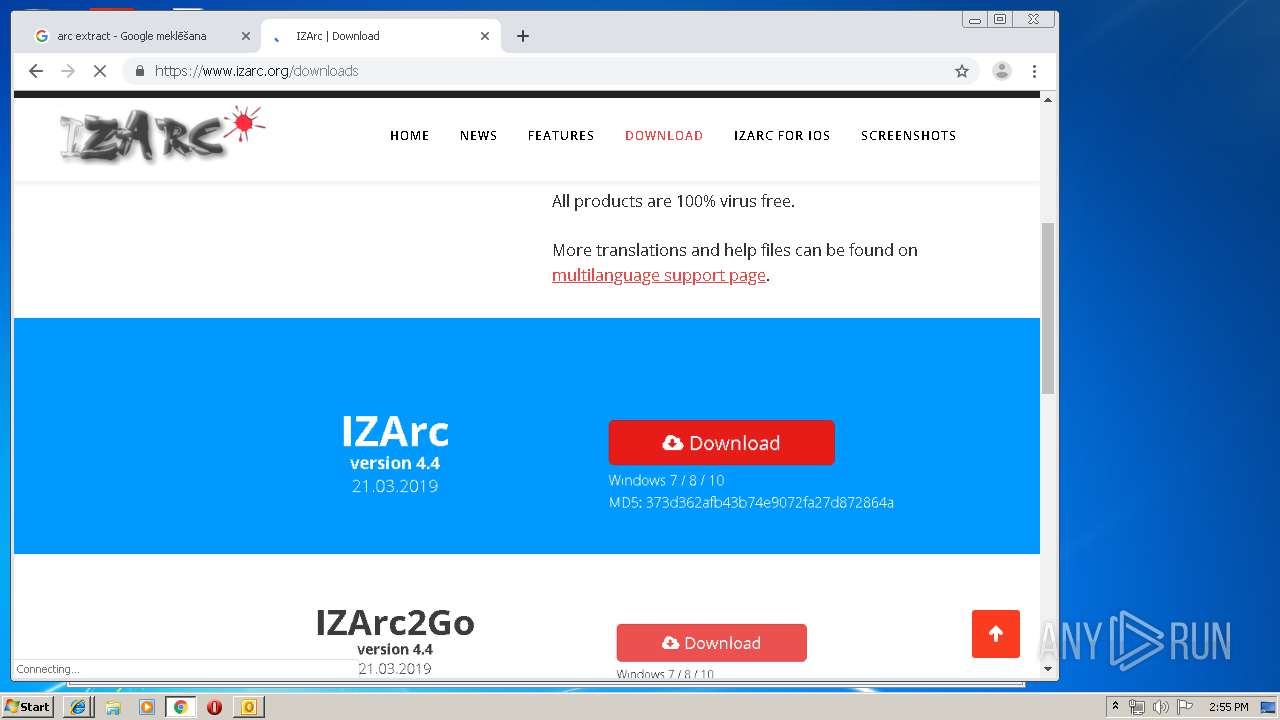
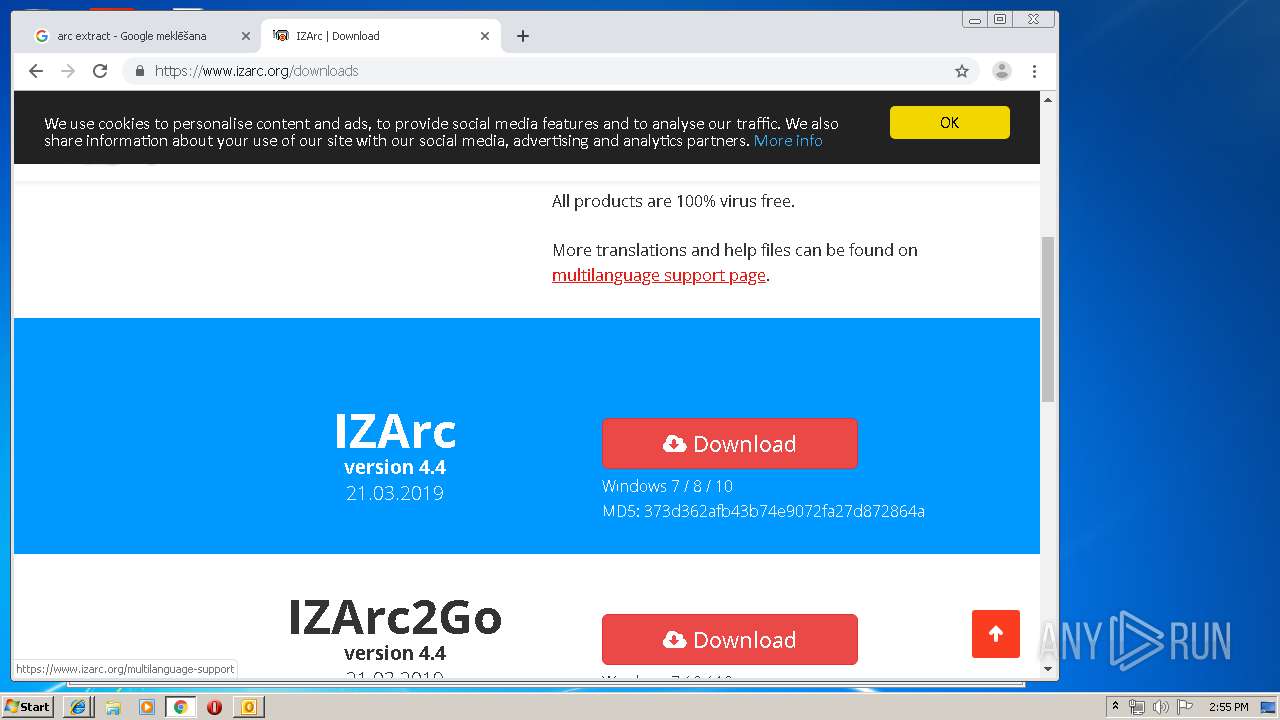
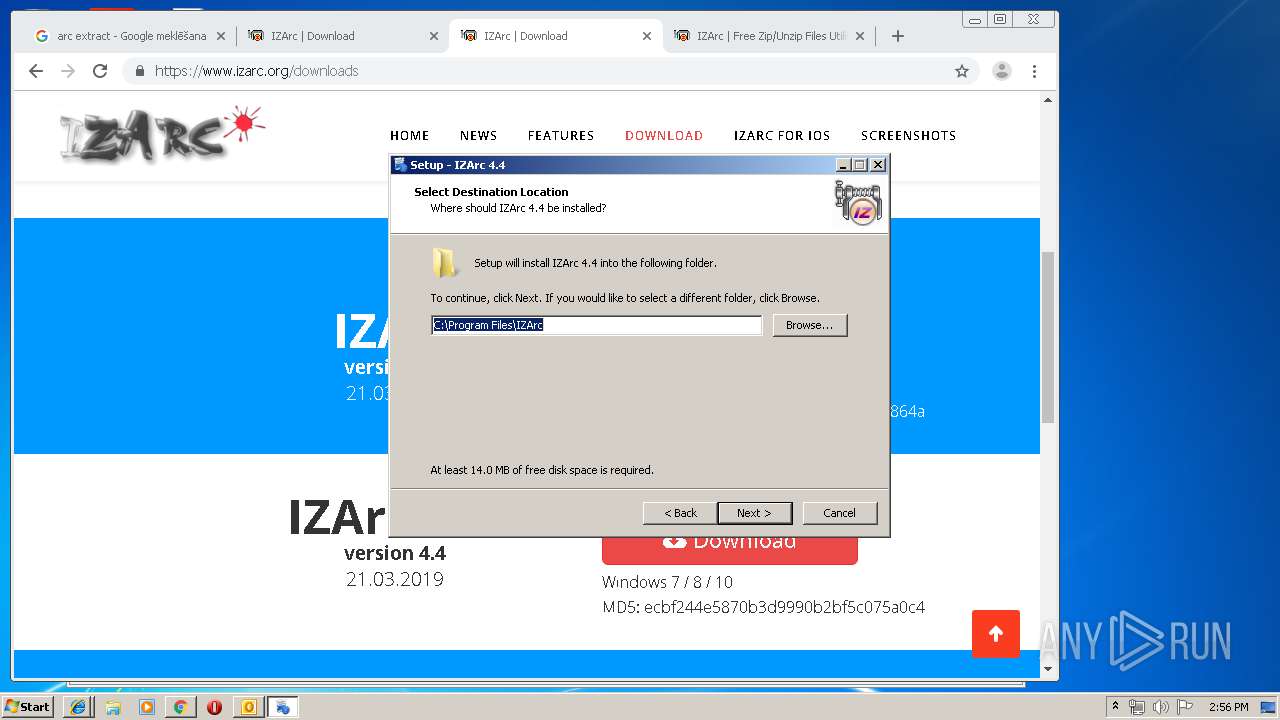
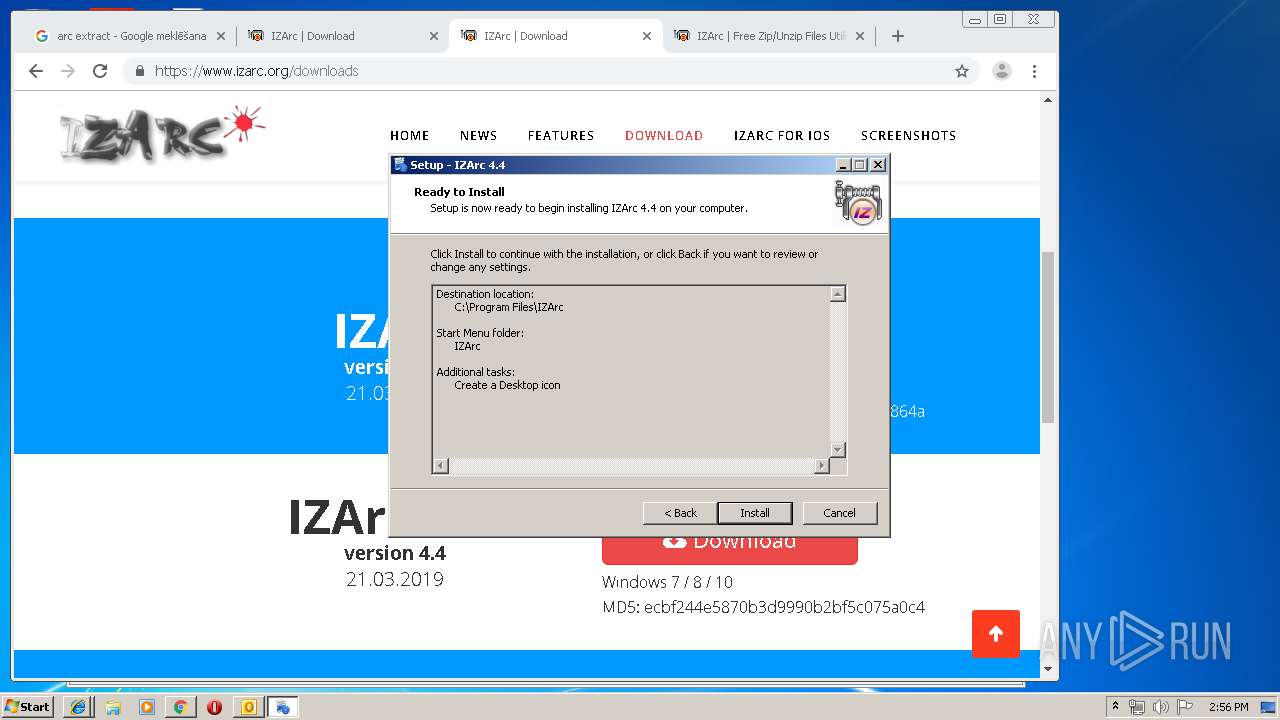
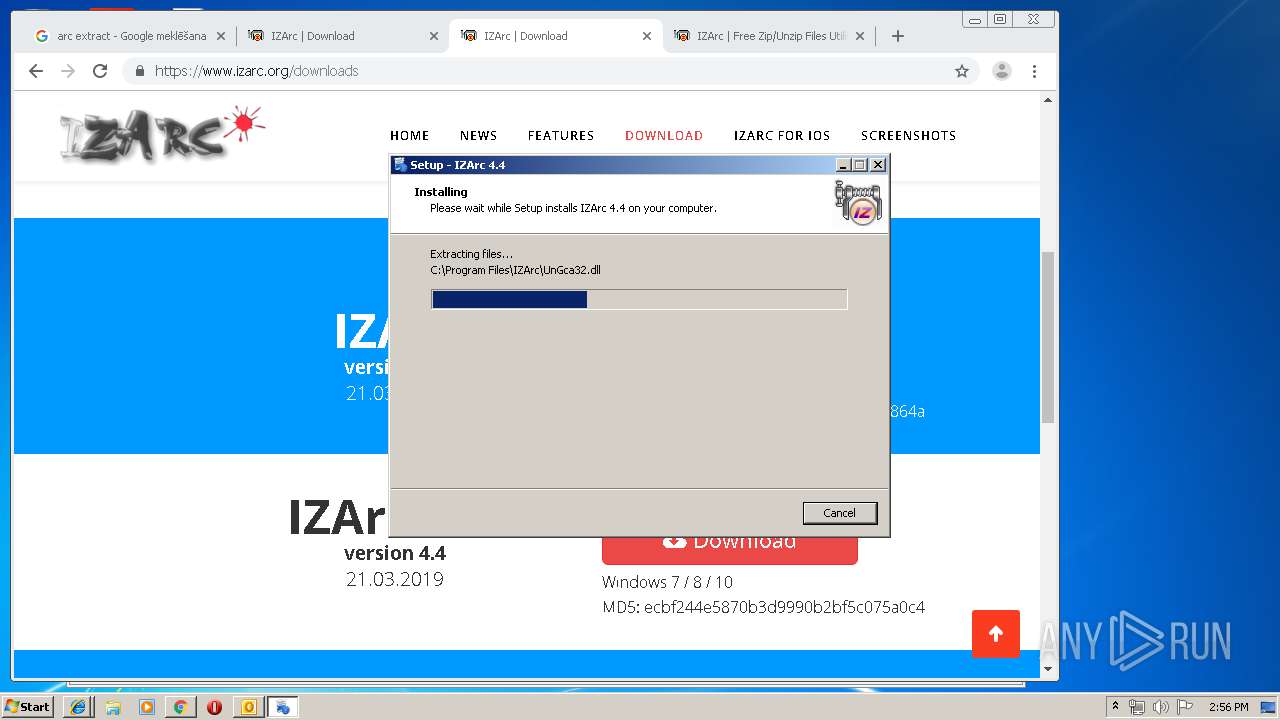
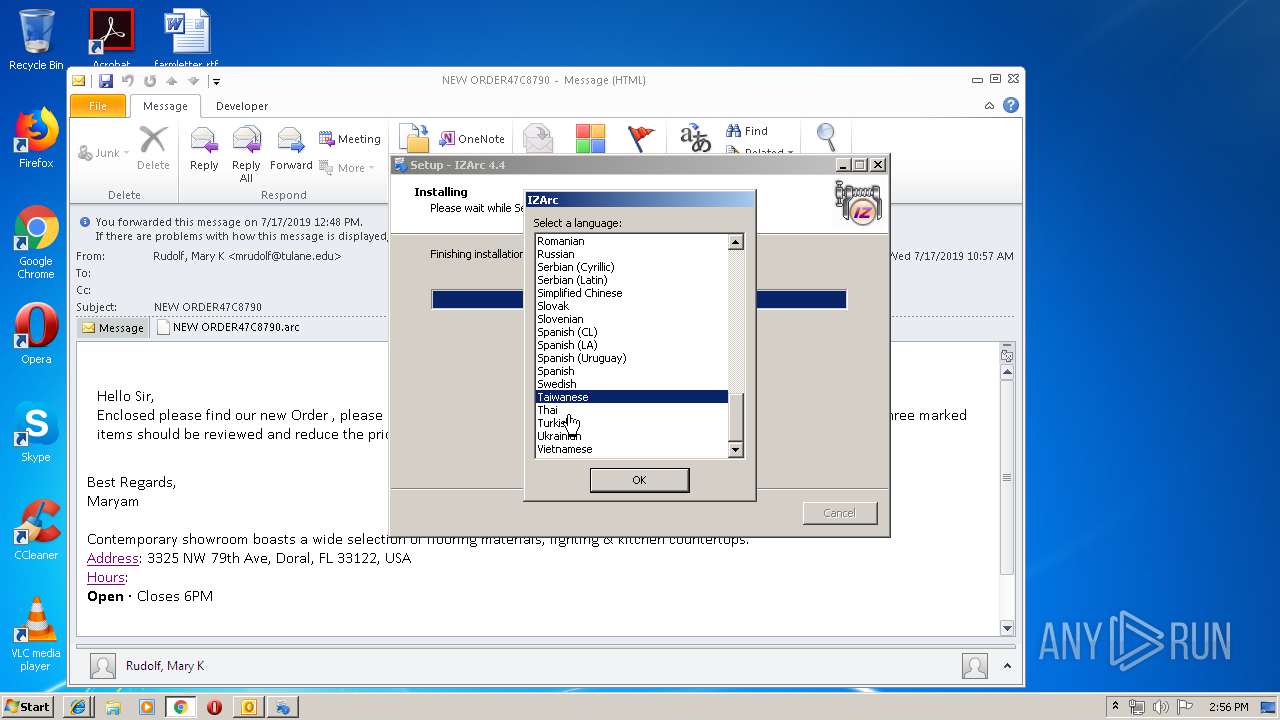
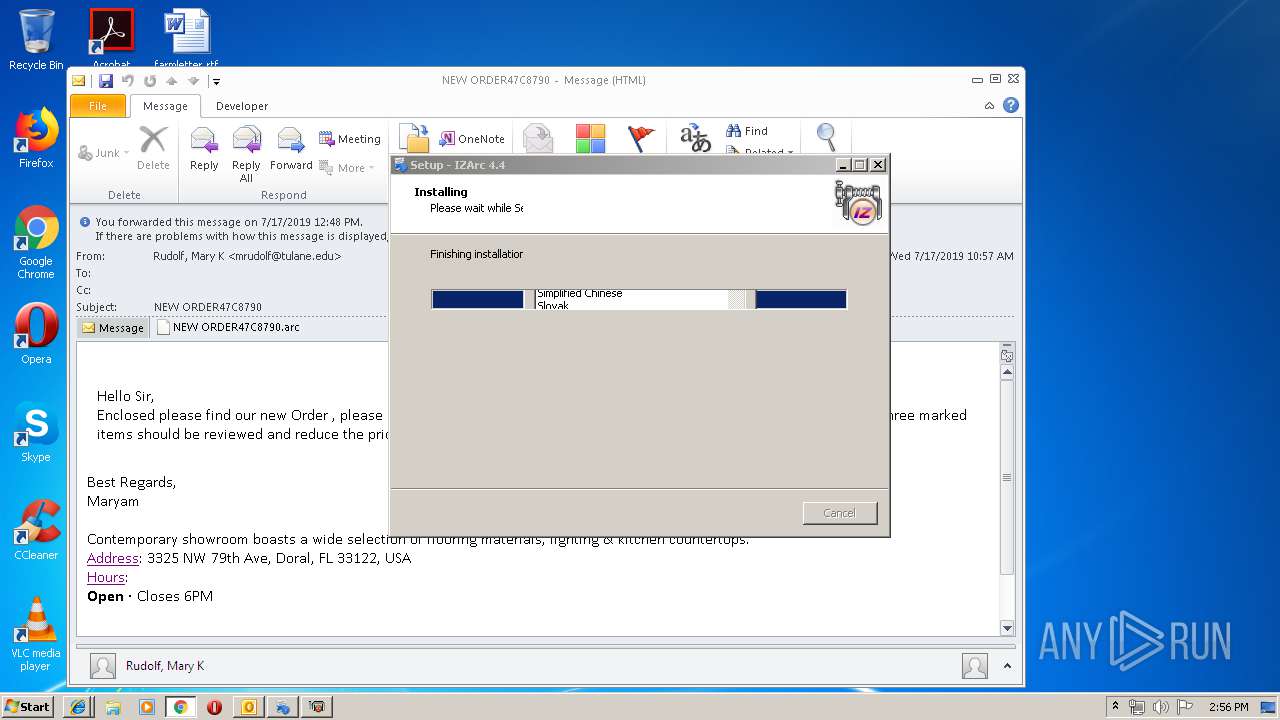
- IZArc_4.4.exe (PID: 3200)
- IZArc_4.4.exe (PID: 928)
- IZArc.exe (PID: 2208)
- IZArc.exe (PID: 3968)
Registers / Runs the DLL via REGSVR32.EXE
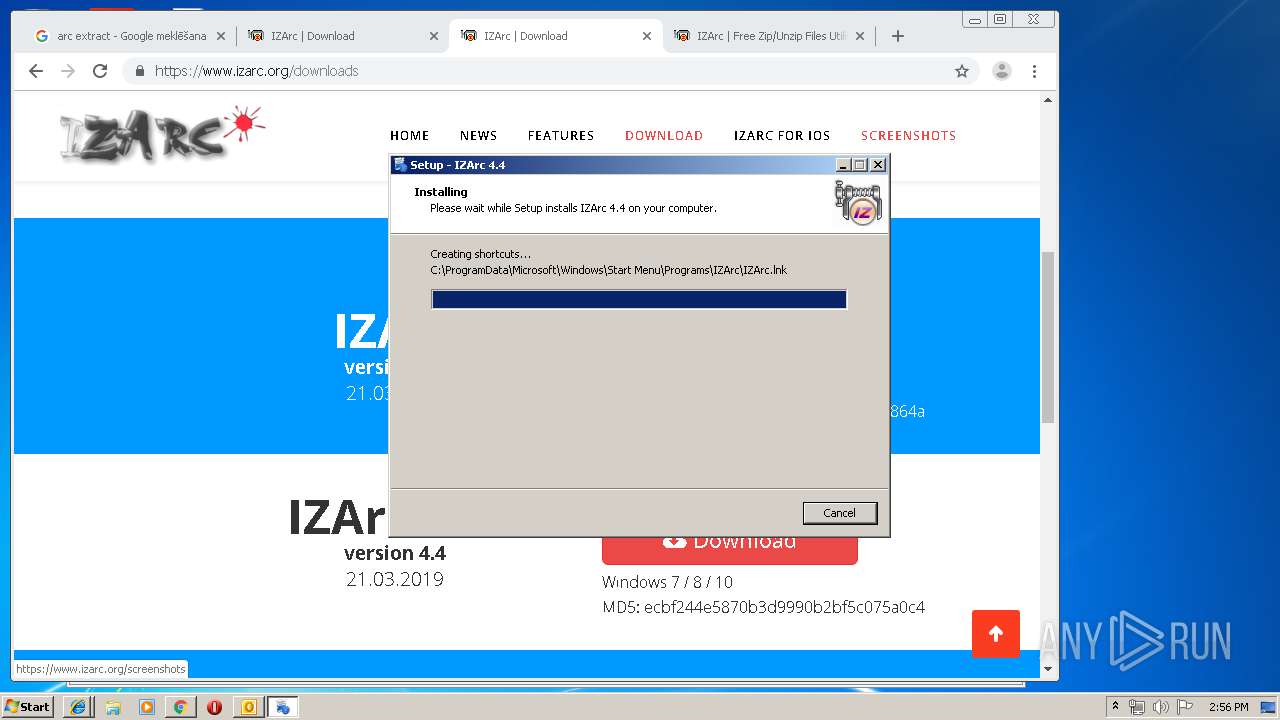
- IZArc_4.4.tmp (PID: 2404)
Loads dropped or rewritten executable
- IZArc.exe (PID: 2208)
- regsvr32.exe (PID: 2656)
- IZArc.exe (PID: 3968)
SUSPICIOUS
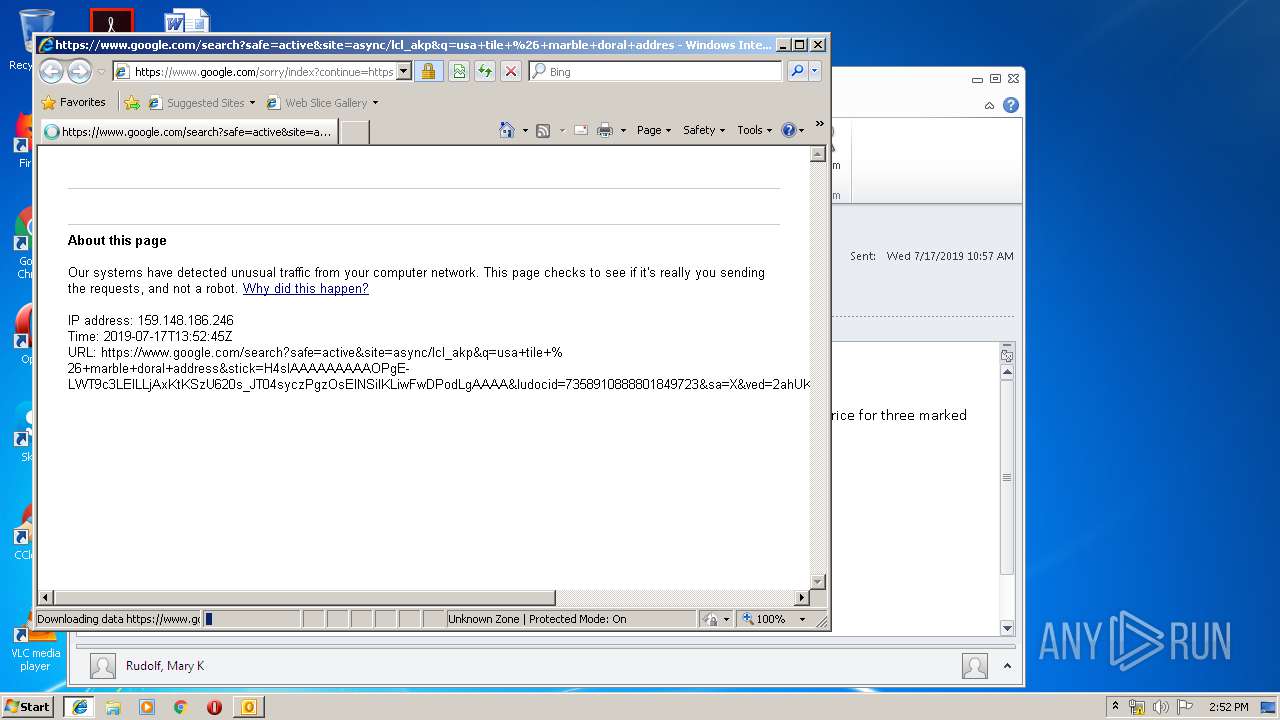
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3412)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3412)
Executable content was dropped or overwritten
- chrome.exe (PID: 3536)
- chrome.exe (PID: 2104)
- IZArc_4.4.tmp (PID: 2404)
- IZArc_4.4.exe (PID: 3200)
- IZArc_4.4.exe (PID: 928)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3412)
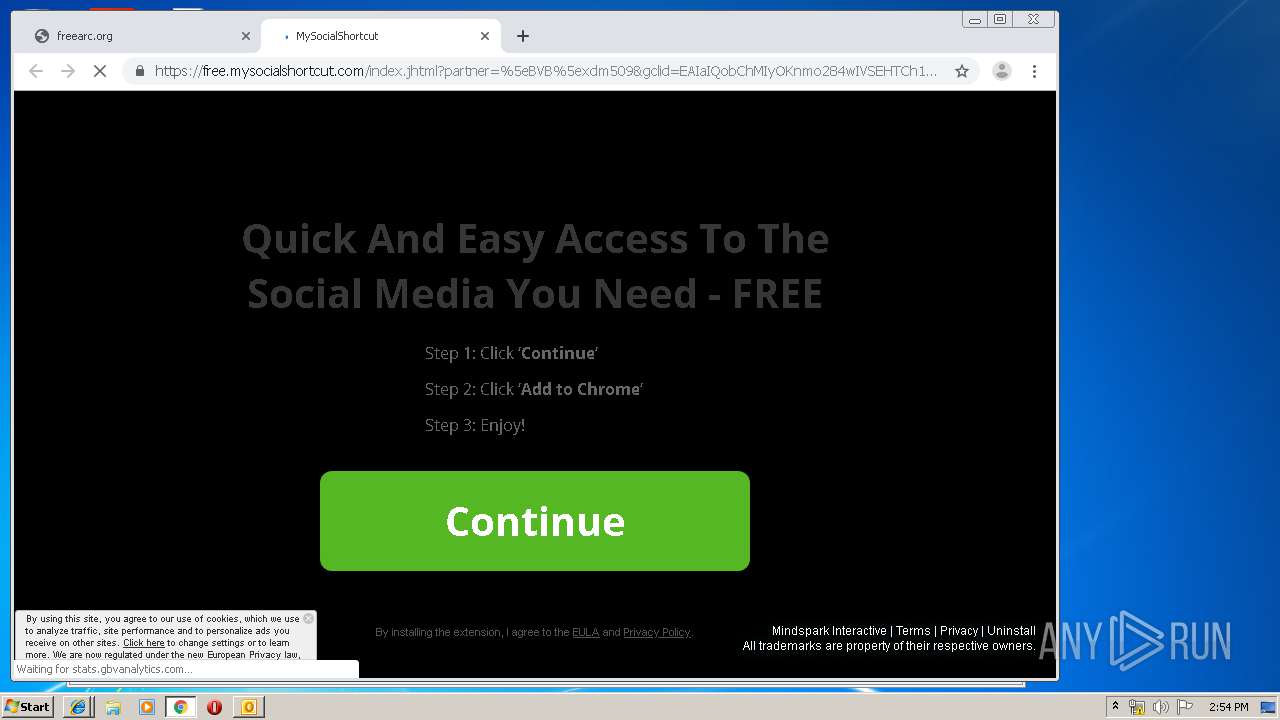
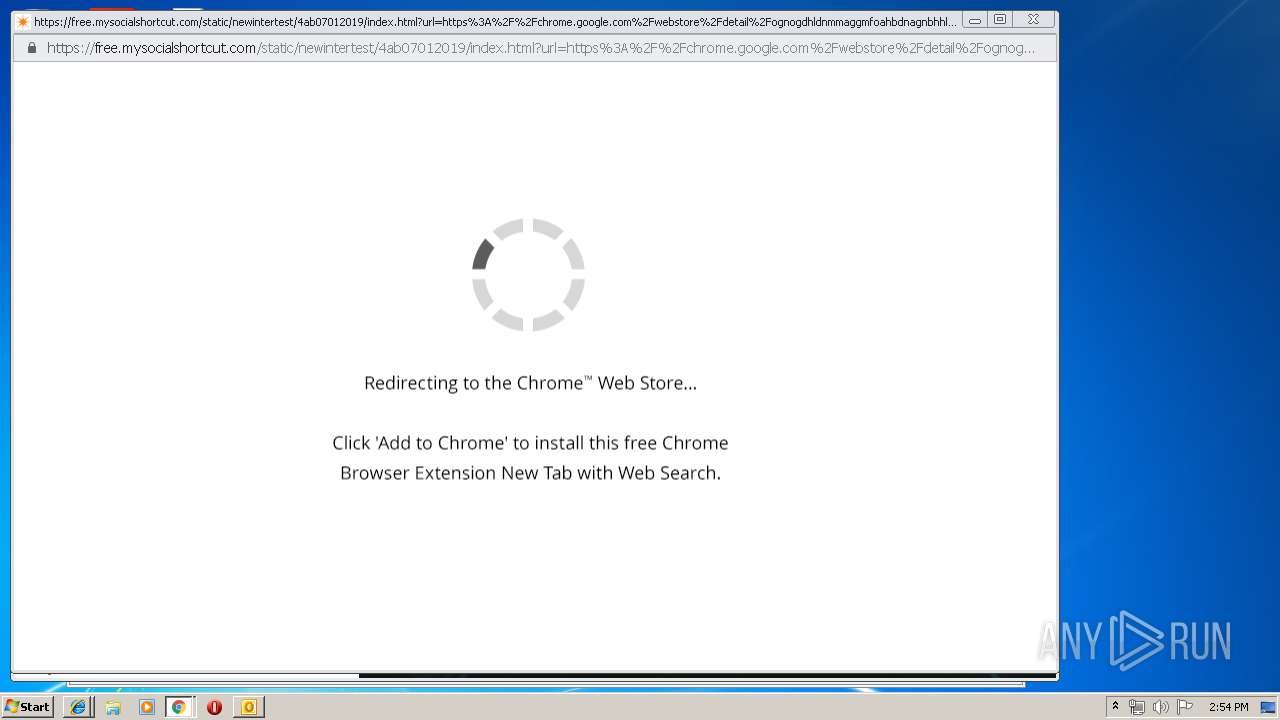
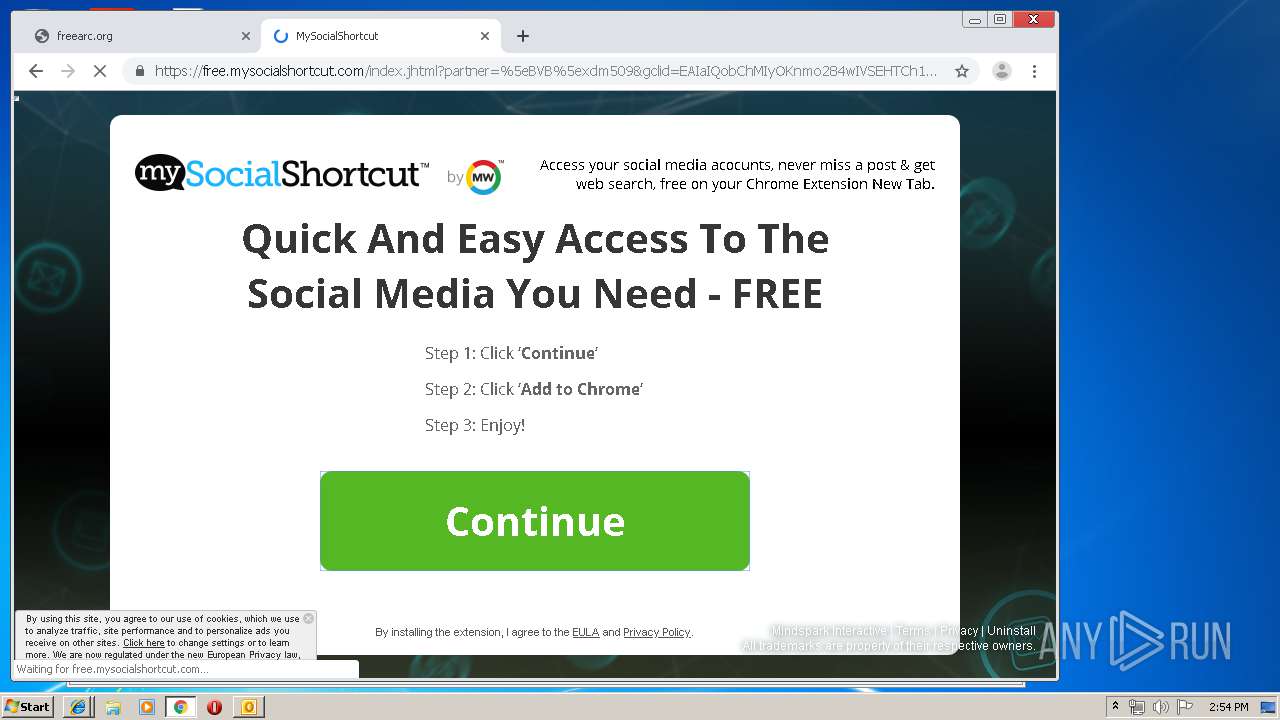
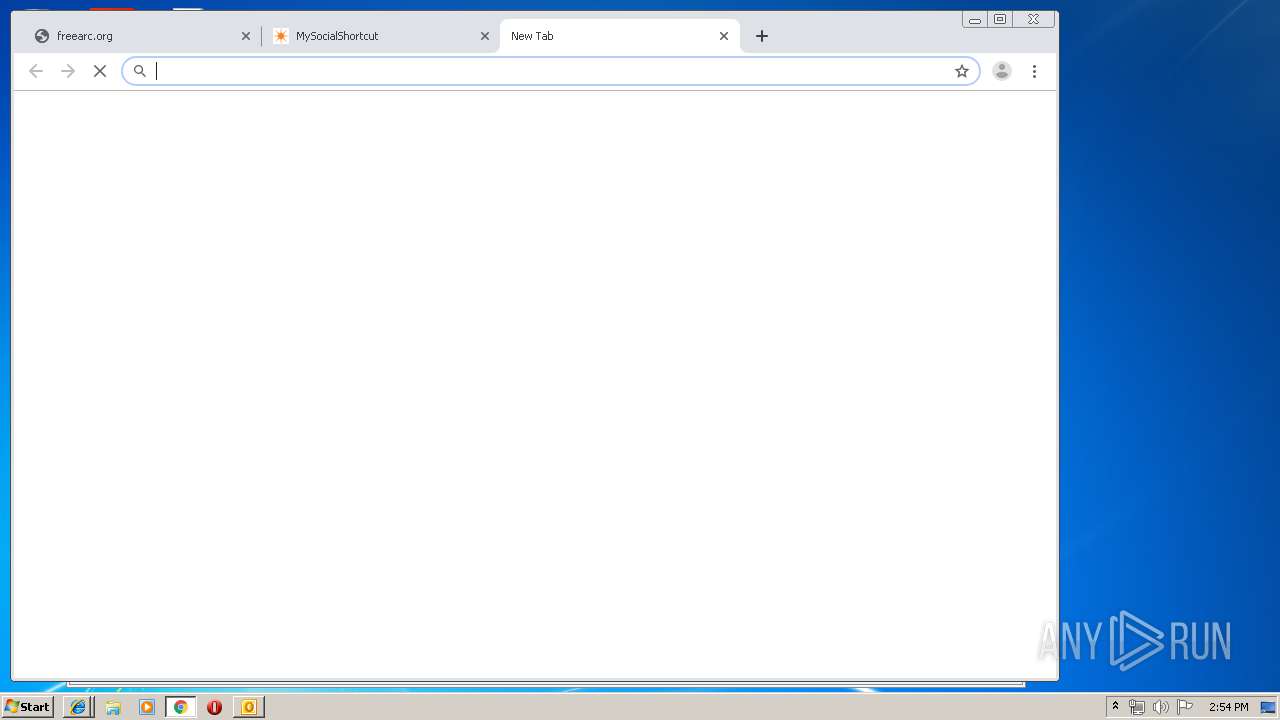
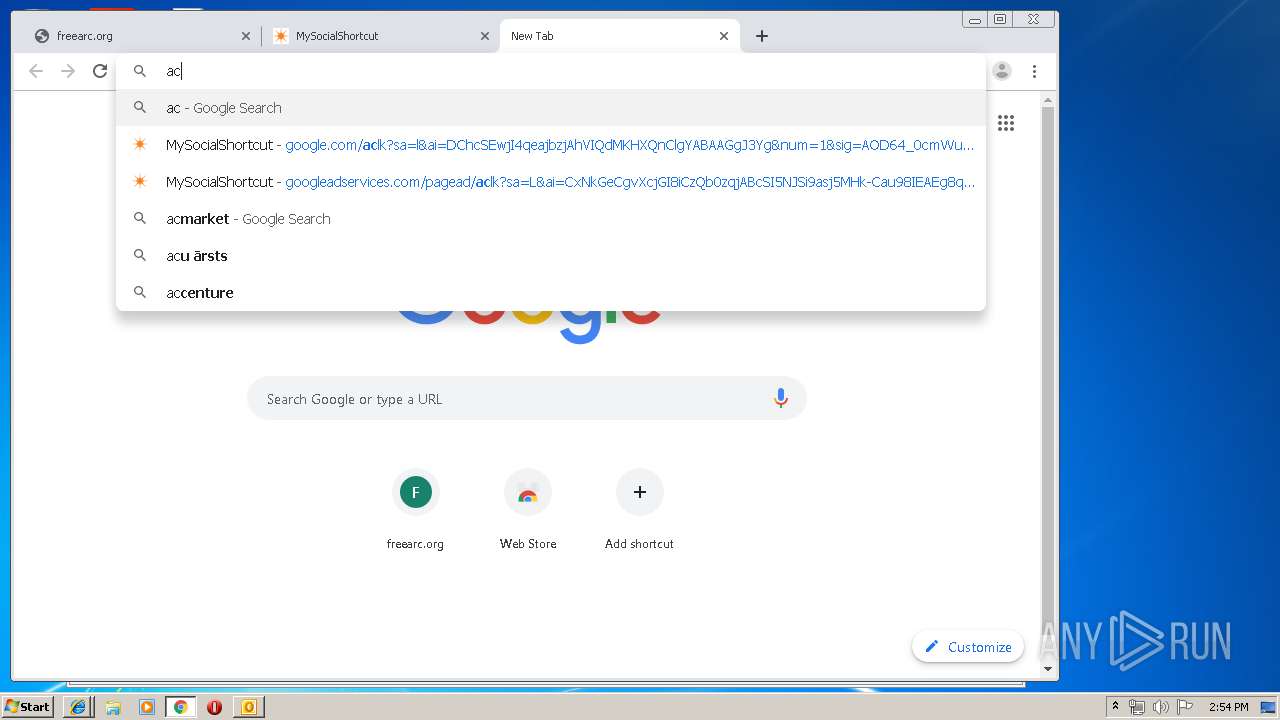
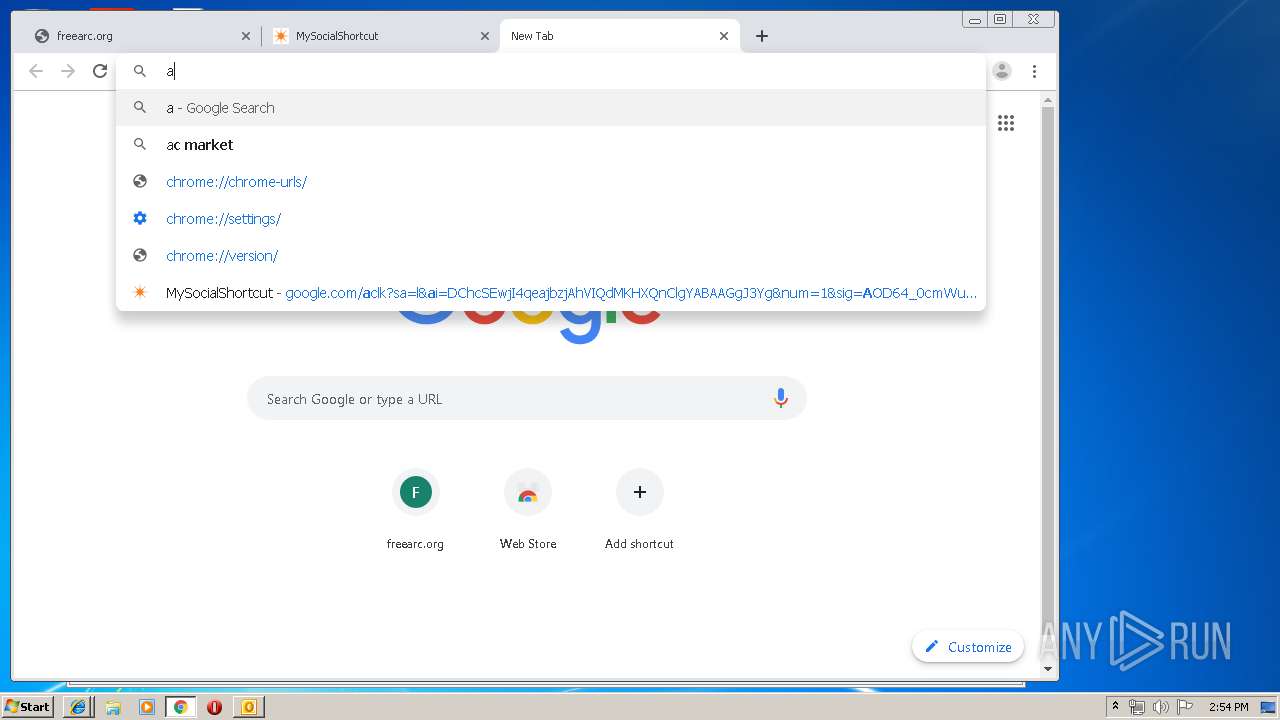
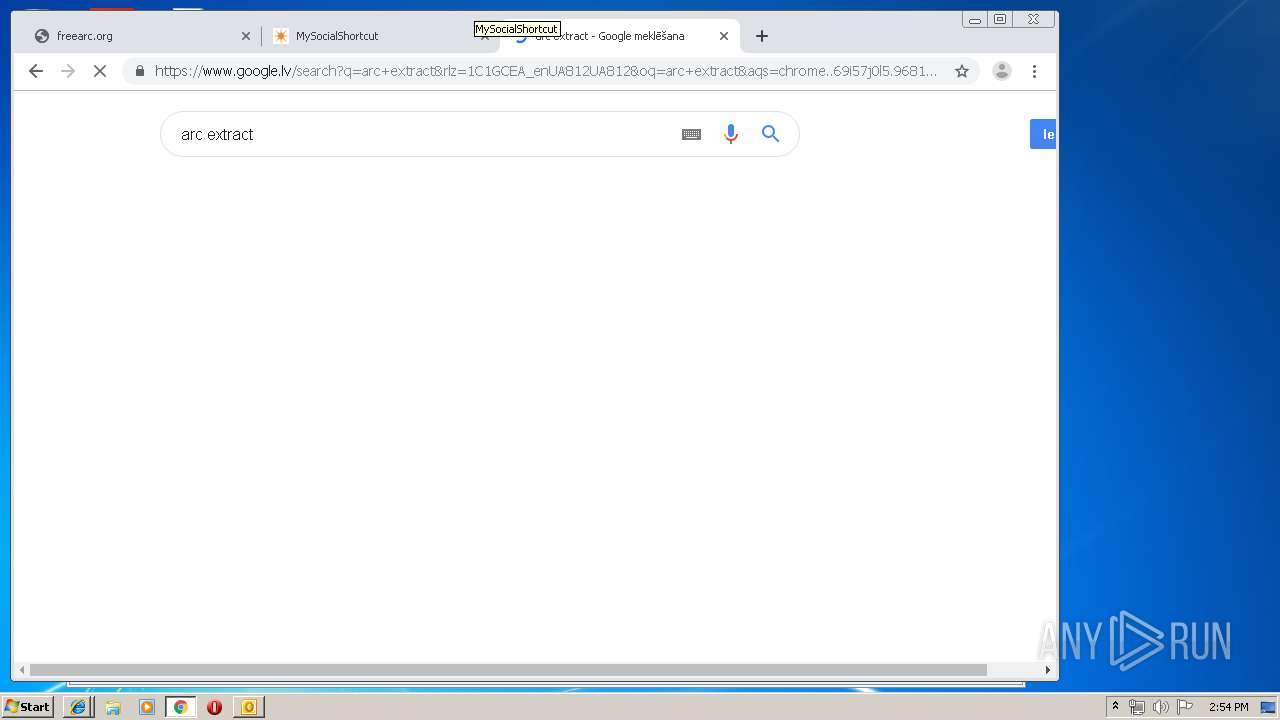
Modifies files in Chrome extension folder
- chrome.exe (PID: 2104)
Creates COM task schedule object
- regsvr32.exe (PID: 2656)
Modifies the open verb of a shell class
- IZArc.exe (PID: 2208)
Executed via COM
- iexplore.exe (PID: 2316)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3412)
Application launched itself
- iexplore.exe (PID: 3972)
- chrome.exe (PID: 2104)
- iexplore.exe (PID: 2316)
Reads internet explorer settings
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 2412)
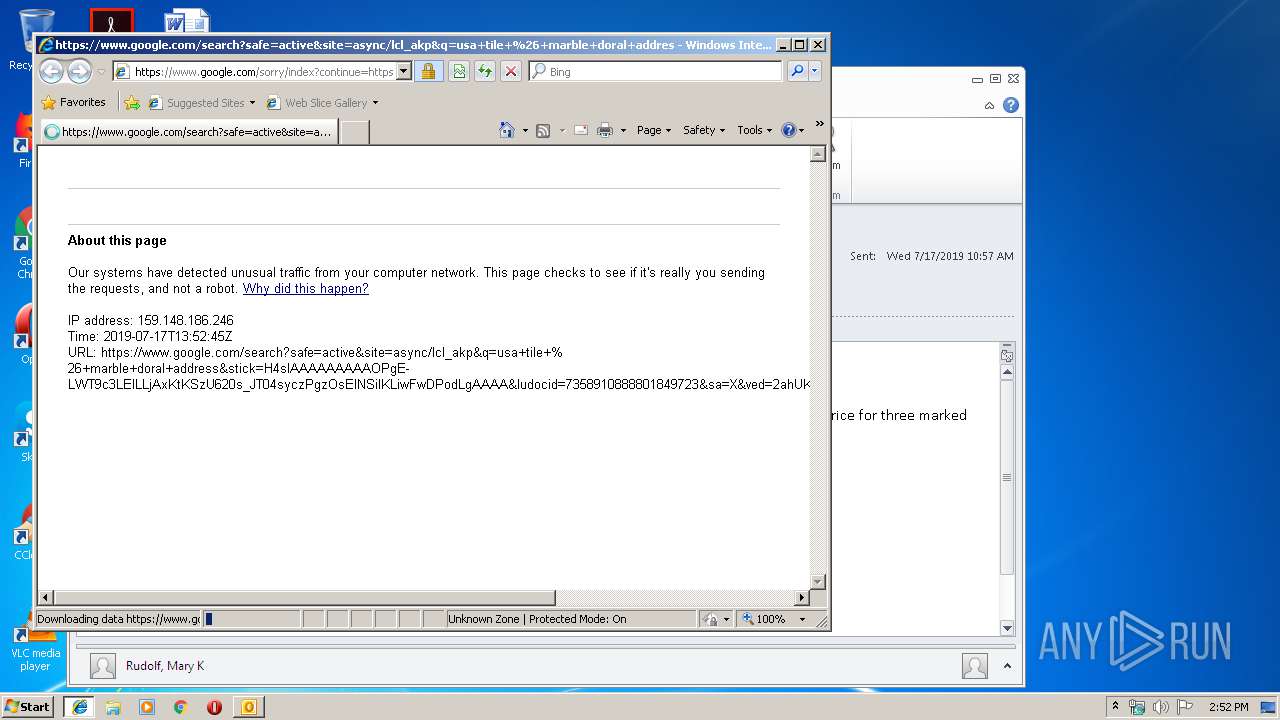
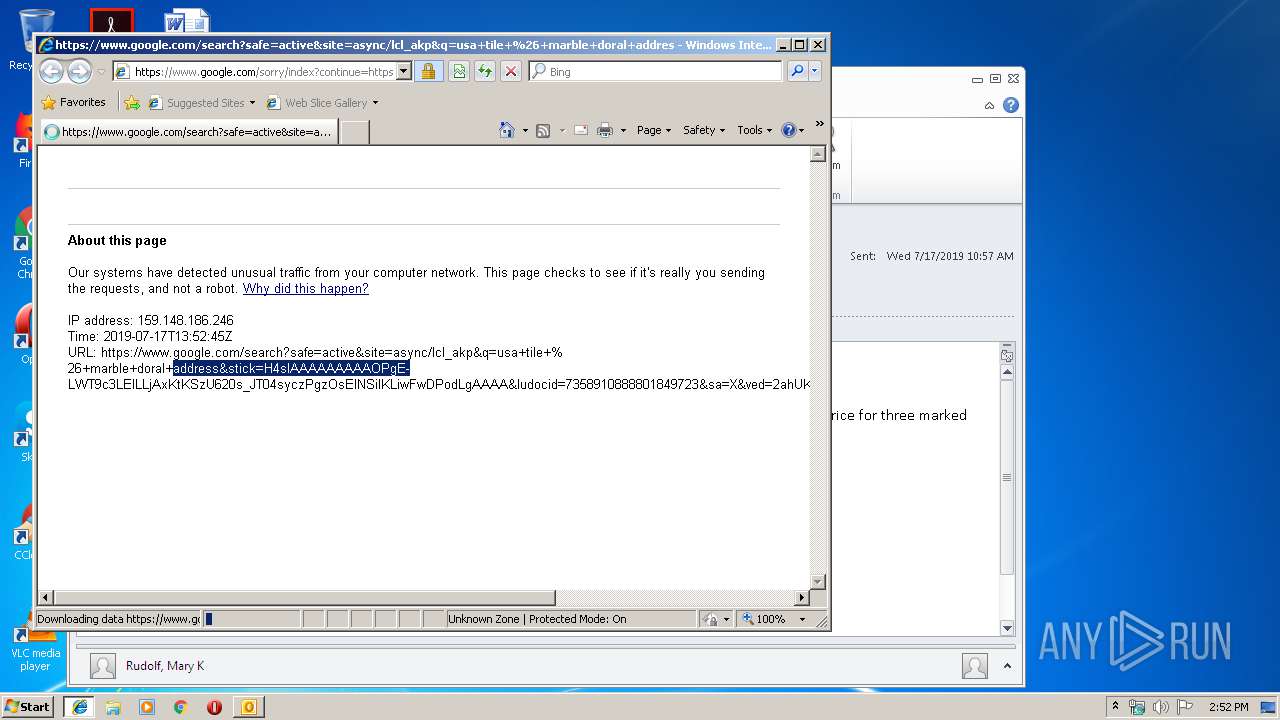
Changes internet zones settings
- iexplore.exe (PID: 3972)
- iexplore.exe (PID: 2316)
Reads Internet Cache Settings
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 2412)
- chrome.exe (PID: 2104)
Creates files in the user directory
- iexplore.exe (PID: 2412)
- iexplore.exe (PID: 2748)
Reads settings of System Certificates
- iexplore.exe (PID: 3972)
Manual execution by user
- chrome.exe (PID: 2104)
- IZArc.exe (PID: 3968)
Application was dropped or rewritten from another process
- IZArc_4.4.tmp (PID: 2240)
- IZArc_4.4.tmp (PID: 2404)
Loads dropped or rewritten executable
- IZArc_4.4.tmp (PID: 2404)
Creates a software uninstall entry
- IZArc_4.4.tmp (PID: 2404)
Changes settings of System certificates
- iexplore.exe (PID: 2396)
Creates files in the program directory
- IZArc_4.4.tmp (PID: 2404)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2396)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
123
Monitored processes
78
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,9961298062473565733,2063039872359095582,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11517039801804514485 --renderer-client-id=40 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4876 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3668 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 928 | "C:\Users\admin\Downloads\IZArc_4.4.exe" /SPAWNWND=$20378 /NOTIFYWND=$30364 | C:\Users\admin\Downloads\IZArc_4.4.exe | IZArc_4.4.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: IZArc 4.4 Setup Exit code: 0 Version: 4.4 Modules
| |||||||||||||||
| 1144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1052,9961298062473565733,2063039872359095582,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9037779130900733289 --mojo-platform-channel-handle=3600 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,9961298062473565733,2063039872359095582,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11660735173875212816 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=888 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1052,9961298062473565733,2063039872359095582,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3976805001269048708 --mojo-platform-channel-handle=4776 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,9961298062473565733,2063039872359095582,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=270735074277794124 --renderer-client-id=51 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3044 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,9961298062473565733,2063039872359095582,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13902776213308436651 --renderer-client-id=37 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4852 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,9961298062473565733,2063039872359095582,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6402956620786171225 --renderer-client-id=43 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1344 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,9961298062473565733,2063039872359095582,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1270961589319197872 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2176 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
5 015
Read events
3 934
Write events
1 048
Delete events
33
Modification events
| (PID) Process: | (3412) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3412) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3412) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | k#% |
Value: 6B232500540D0000010000000000000000000000 | |||
| (PID) Process: | (3412) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 540D0000661F55D4A63CD50100000000 | |||
| (PID) Process: | (3412) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3412) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220129920 | |||
| (PID) Process: | (3412) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3412) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3412) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3412) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1324417045 | |||
Executable files
29
Suspicious files
177
Text files
459
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
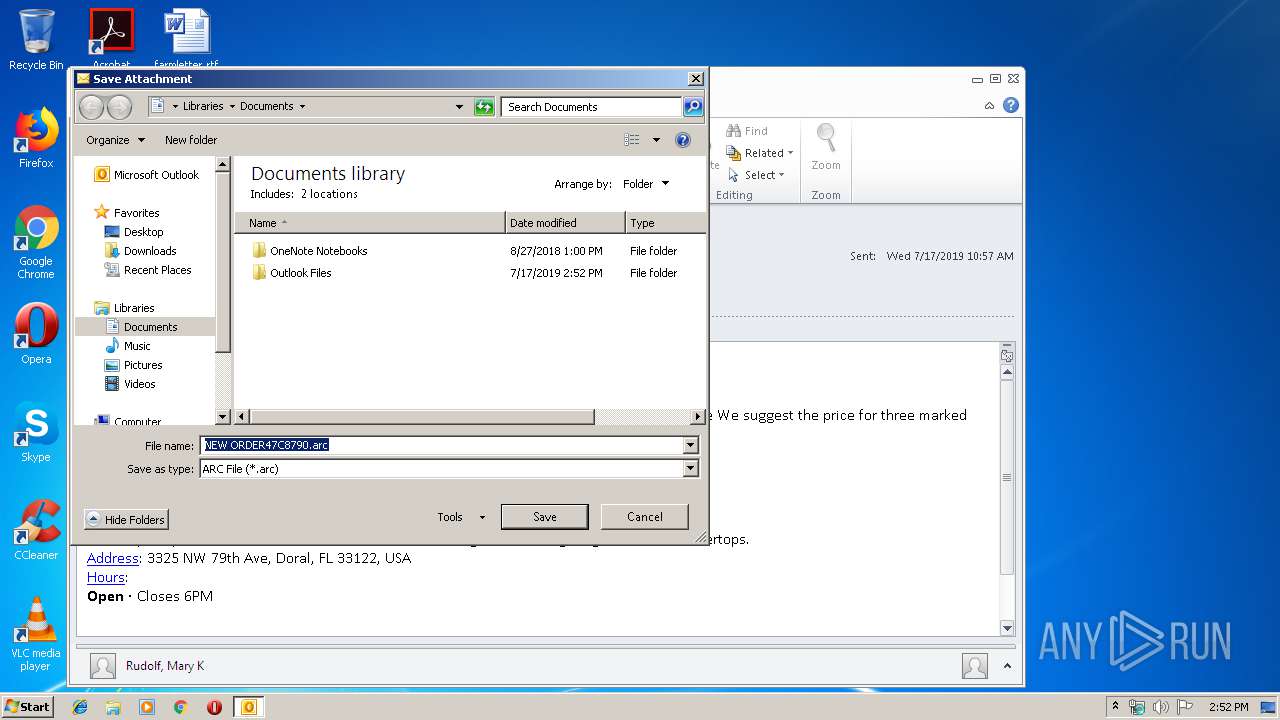
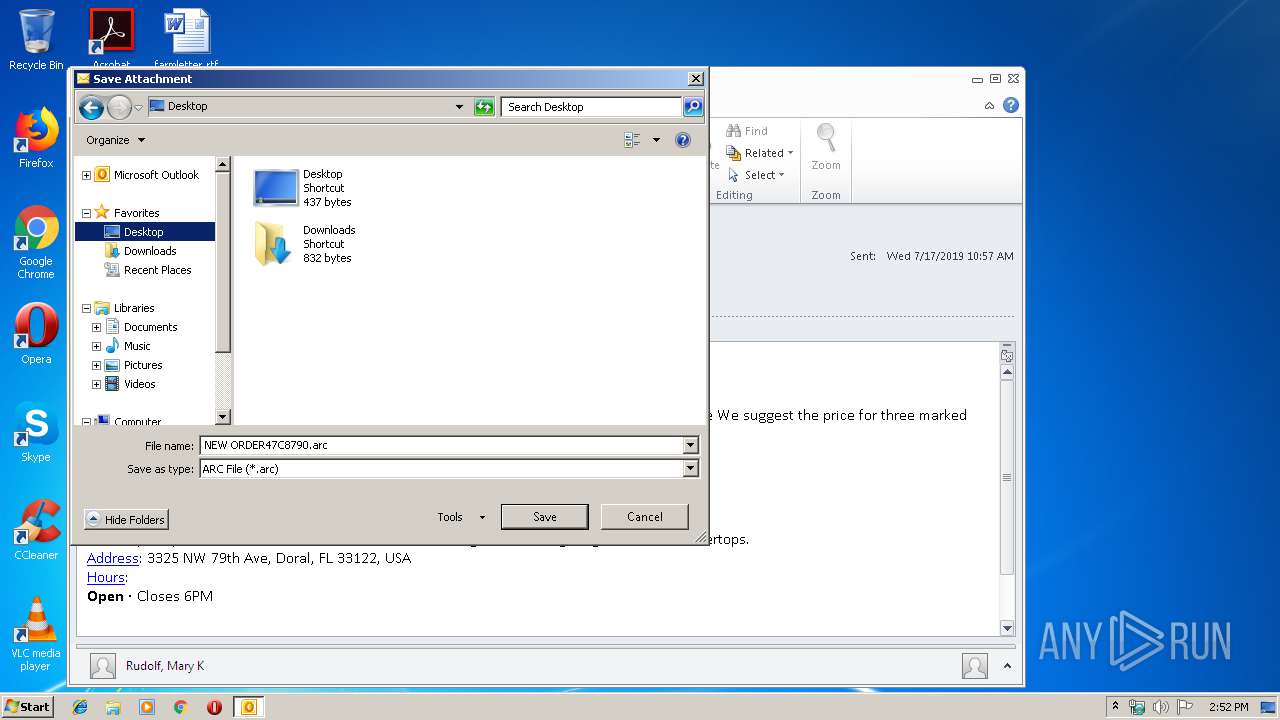
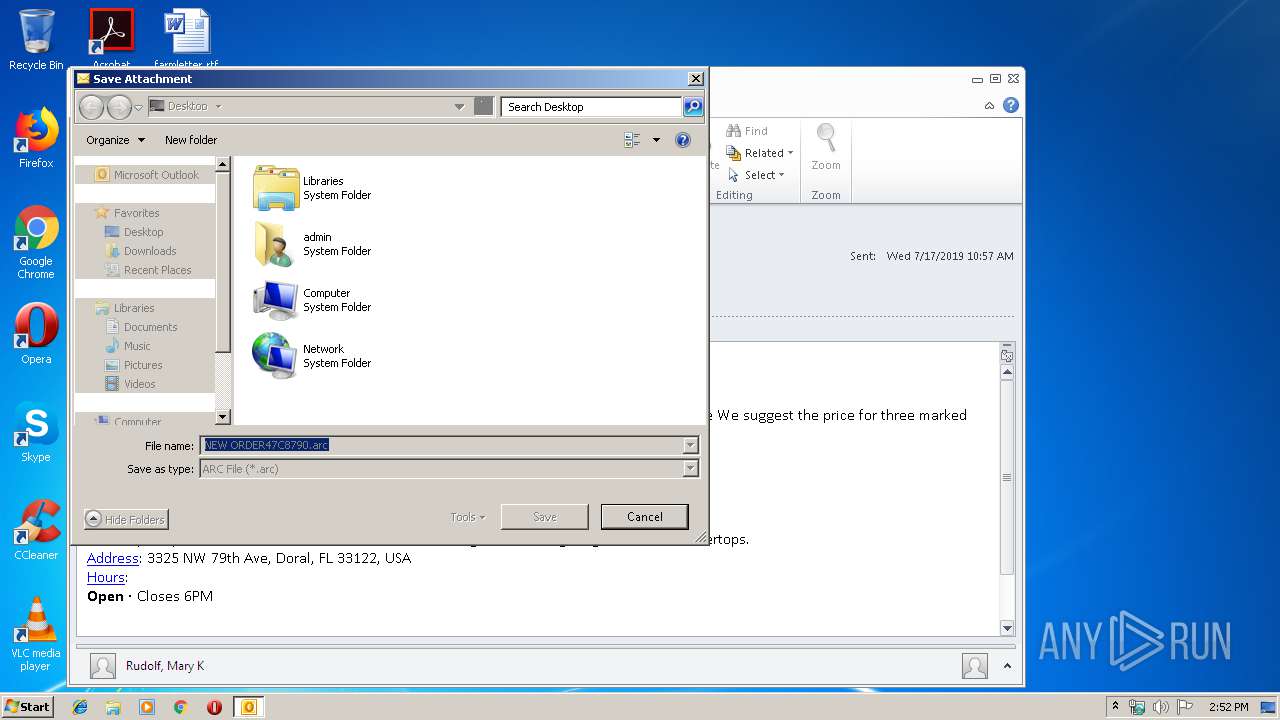
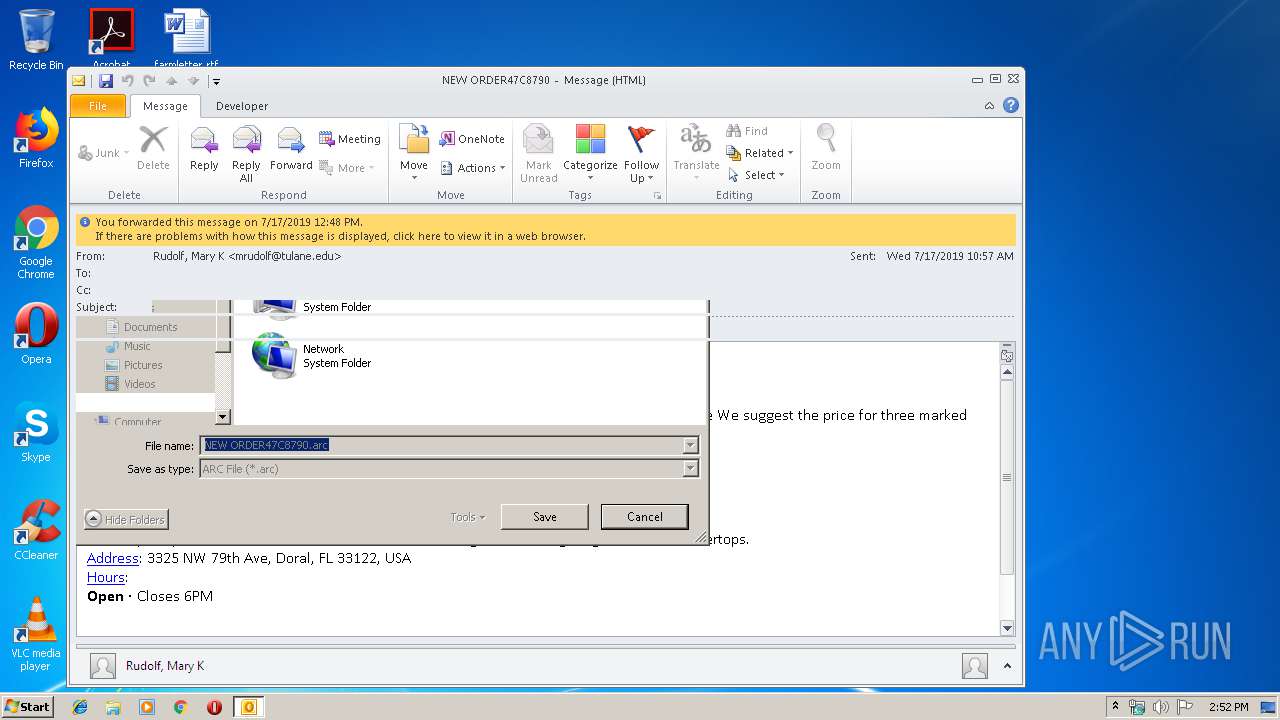
| 3412 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRCBDB.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3412 | OUTLOOK.EXE | C:\Users\admin\Desktop\NEW ORDER47C8790.arc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3412 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3412 | OUTLOOK.EXE | C:\Users\admin\Desktop\NEW ORDER47C8790.arc | compressed | |
MD5:— | SHA256:— | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3412 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\HZM2A91R\NEW ORDER47C8790.arc | compressed | |
MD5:— | SHA256:— | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3412 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{70847C2F-15F4-47FC-A491-64FFA2FC70BE}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:7D80C0A7E3849818695EAF4989186A3C | SHA256:72DC527D78A8E99331409803811CC2D287E812C008A1C869A6AEA69D7A44B597 | |||
| 3412 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_5D03A26E4EA3204F8FD4038B0C17904D.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
| 3412 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_RssRule_2_C38C496D7434A544BE151ECE75D0F44B.dat | xml | |
MD5:D8B37ED0410FB241C283F72B76987F18 | SHA256:31E68049F6B7F21511E70CD7F2D95B9CF1354CF54603E8F47C1FC40F40B7A114 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
170
DNS requests
115
Threats
105
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3412 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
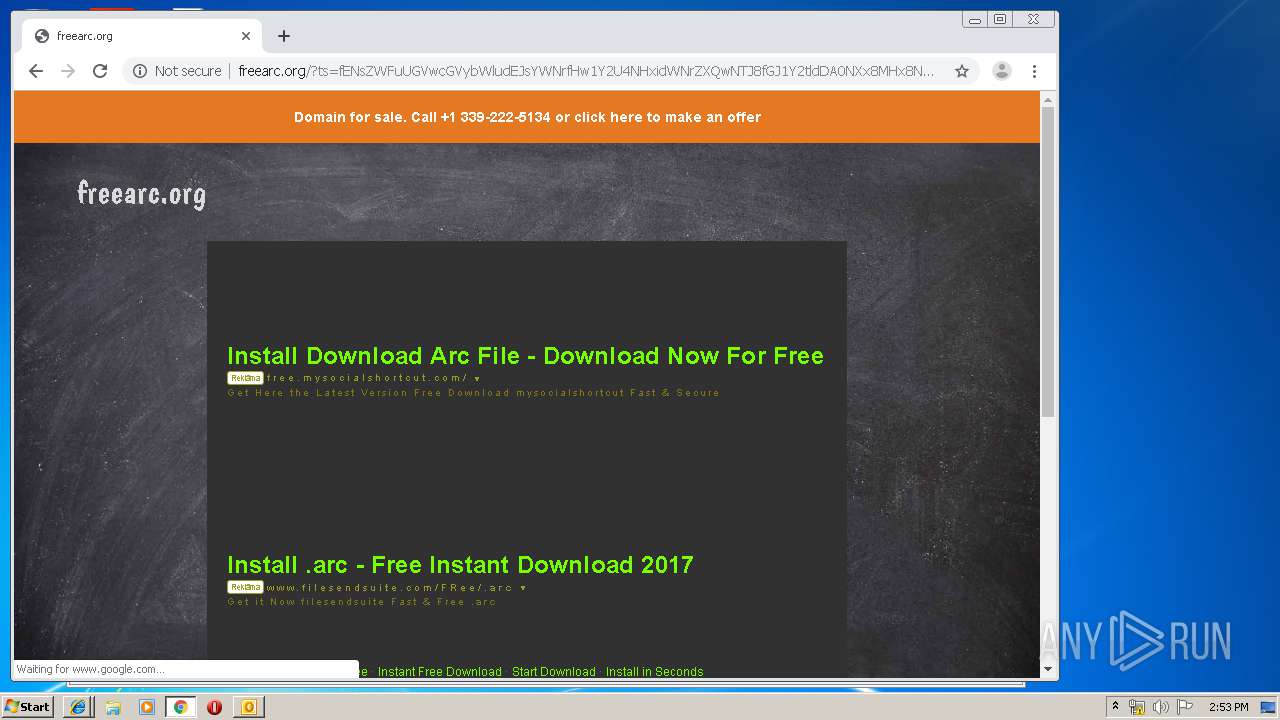
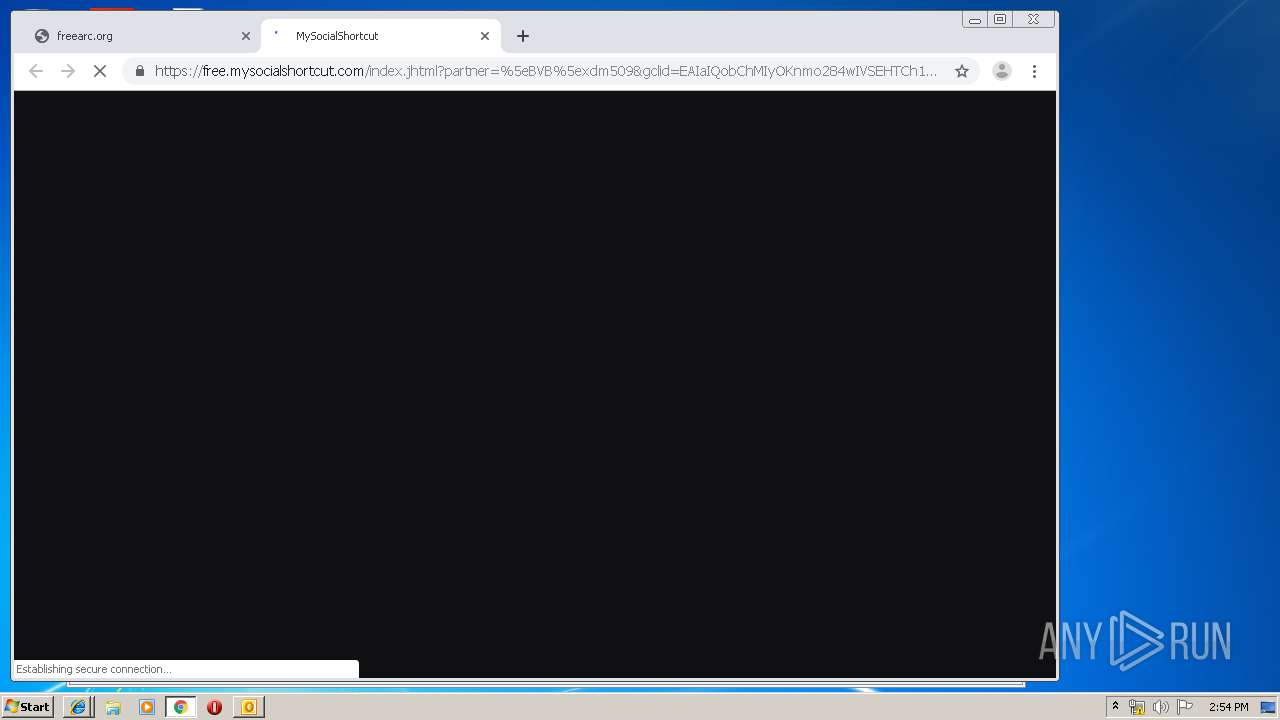
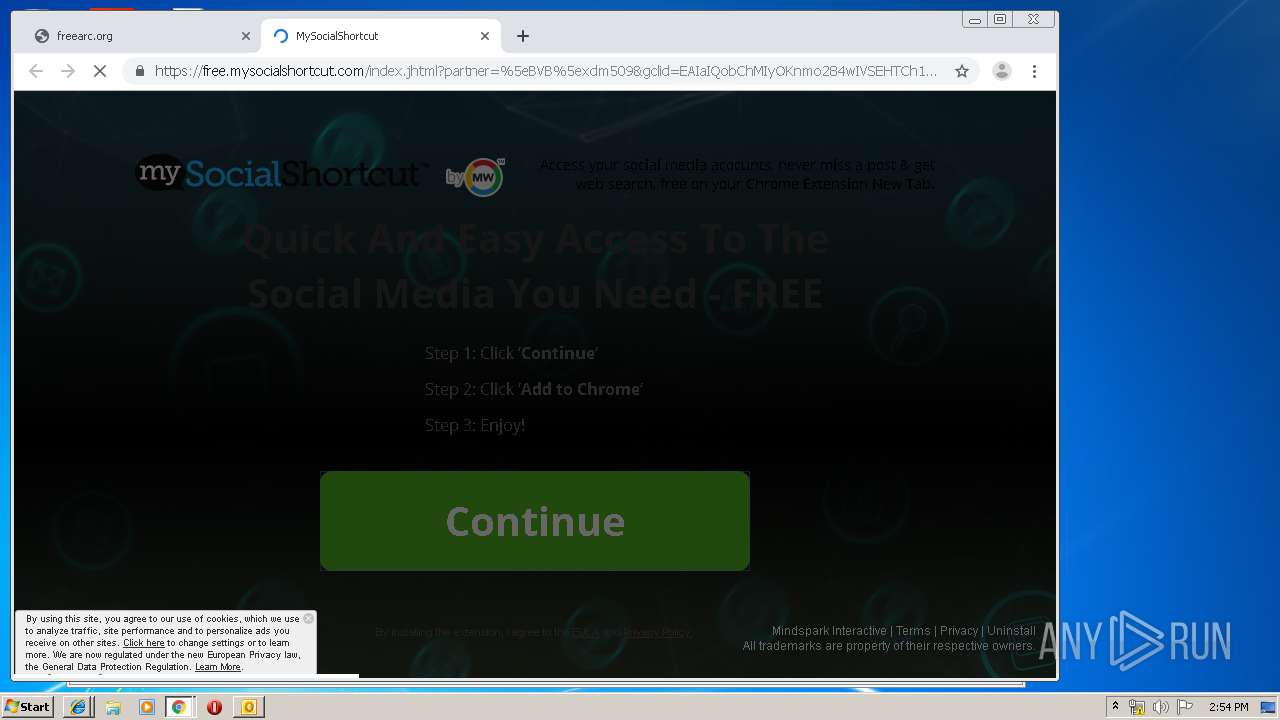
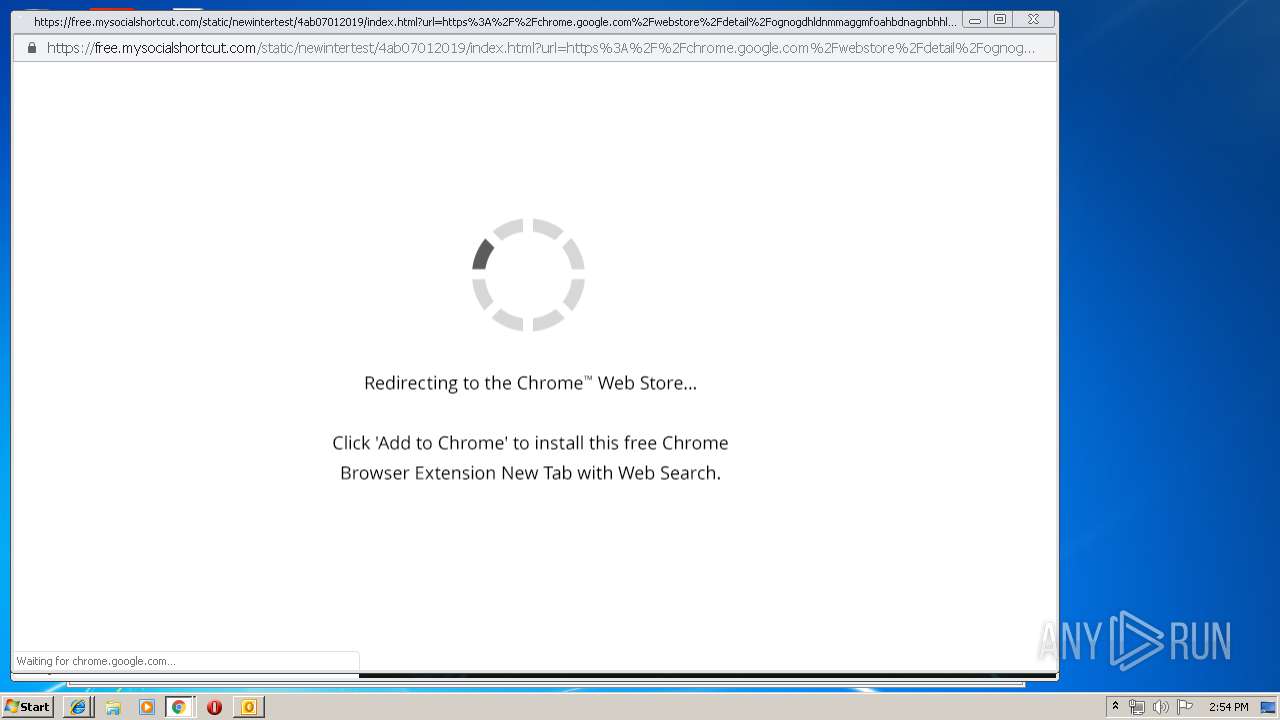
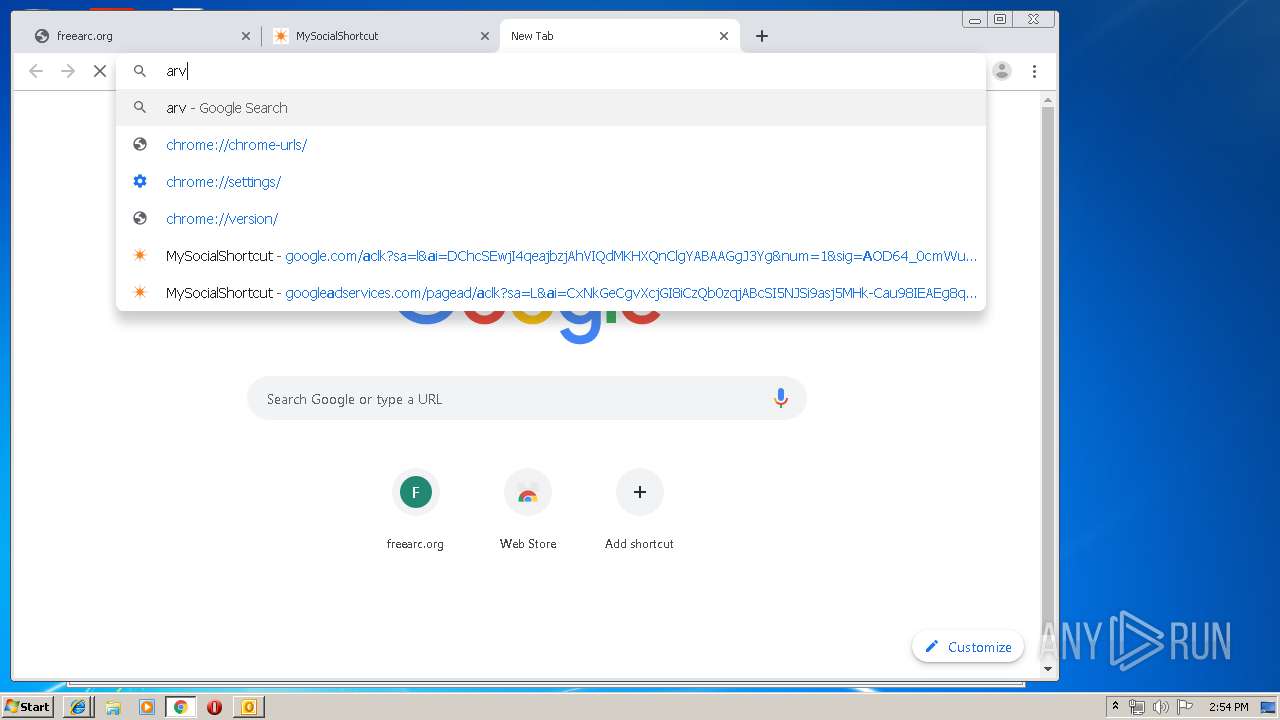
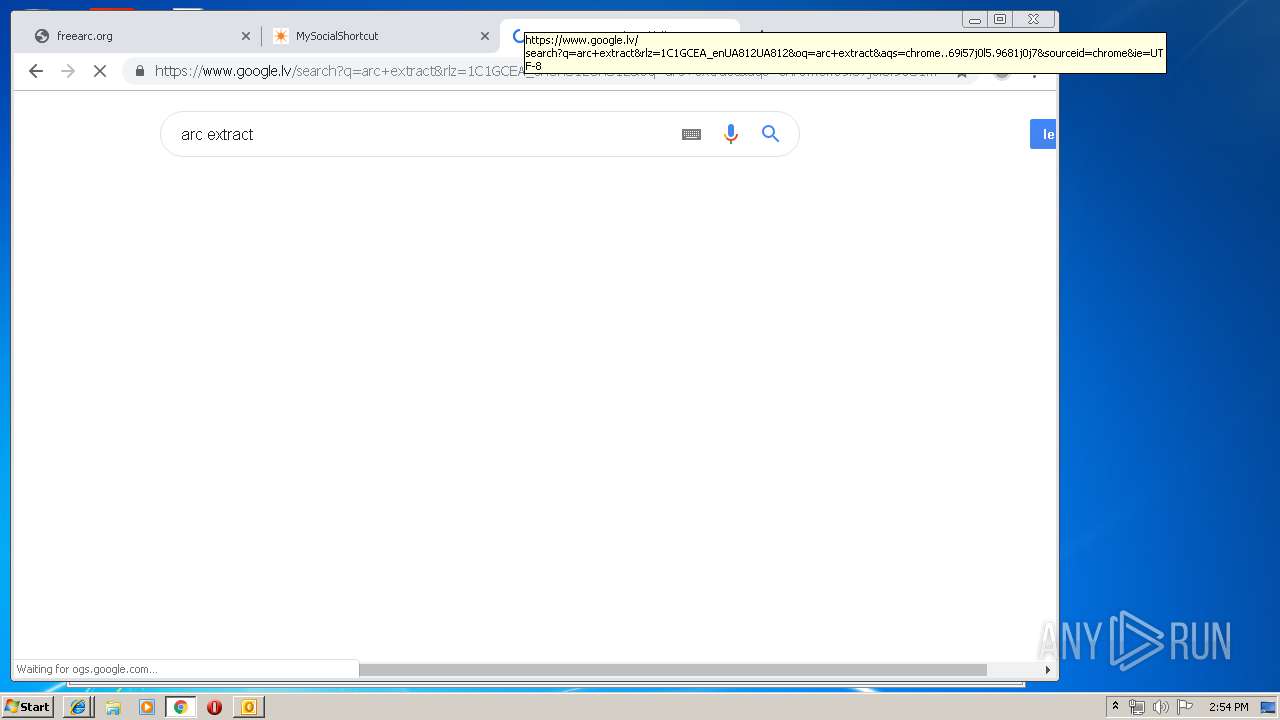
3536 | chrome.exe | GET | 302 | 35.244.218.203:80 | http://free.mysocialshortcut.com/index.jhtml?partner=^BVB^xdm509&gclid=EAIaIQobChMIyOKnmo284wIVSEHTCh10JwpYEAEYASAAEgInAPD_BwE | US | — | — | whitelisted |
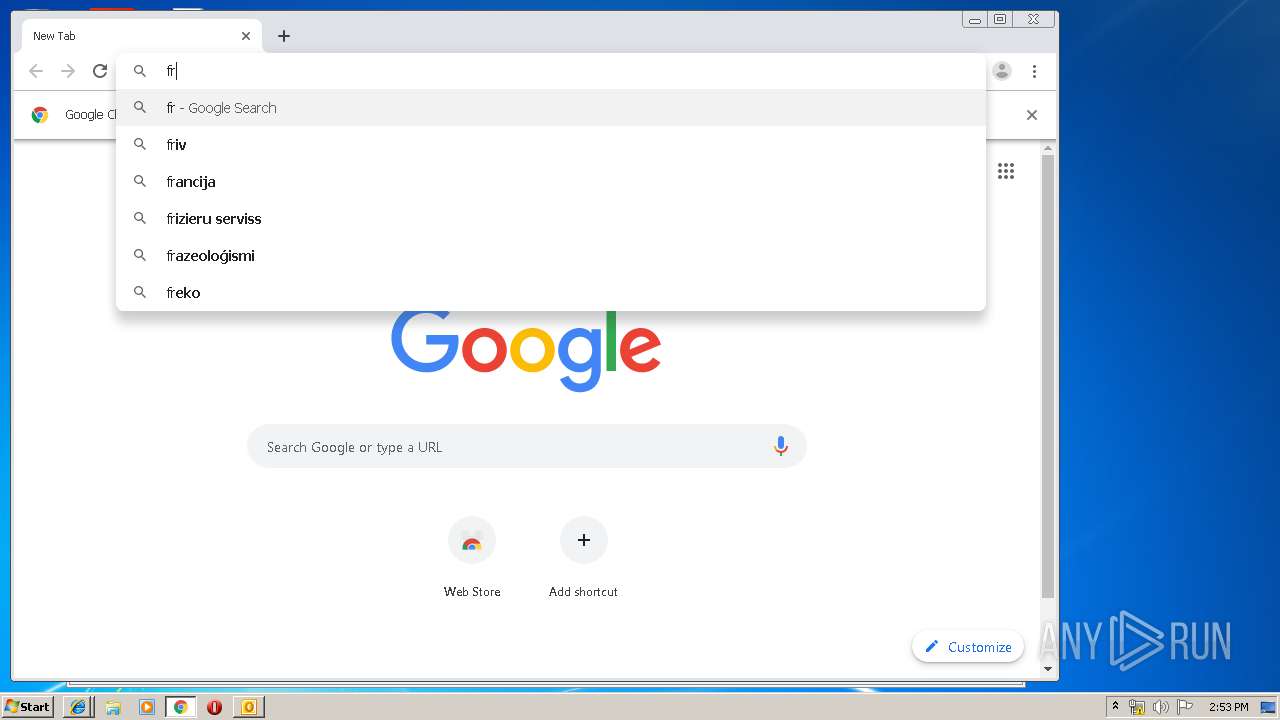
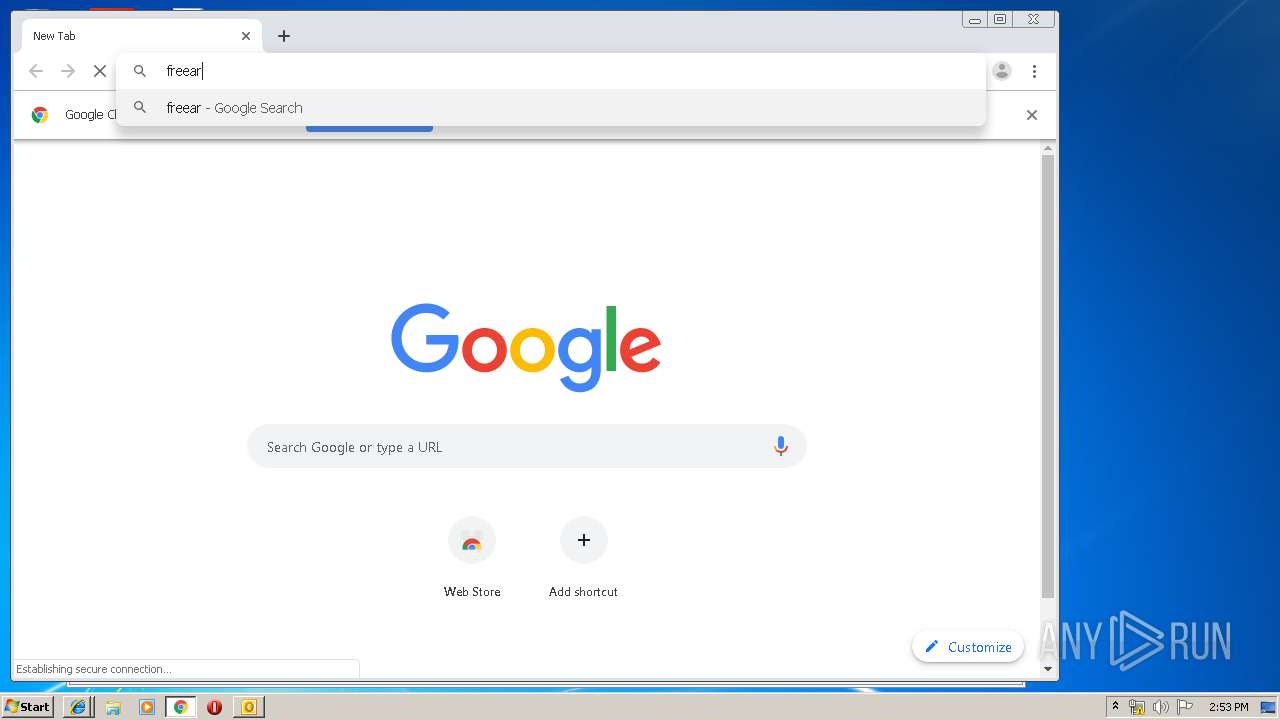
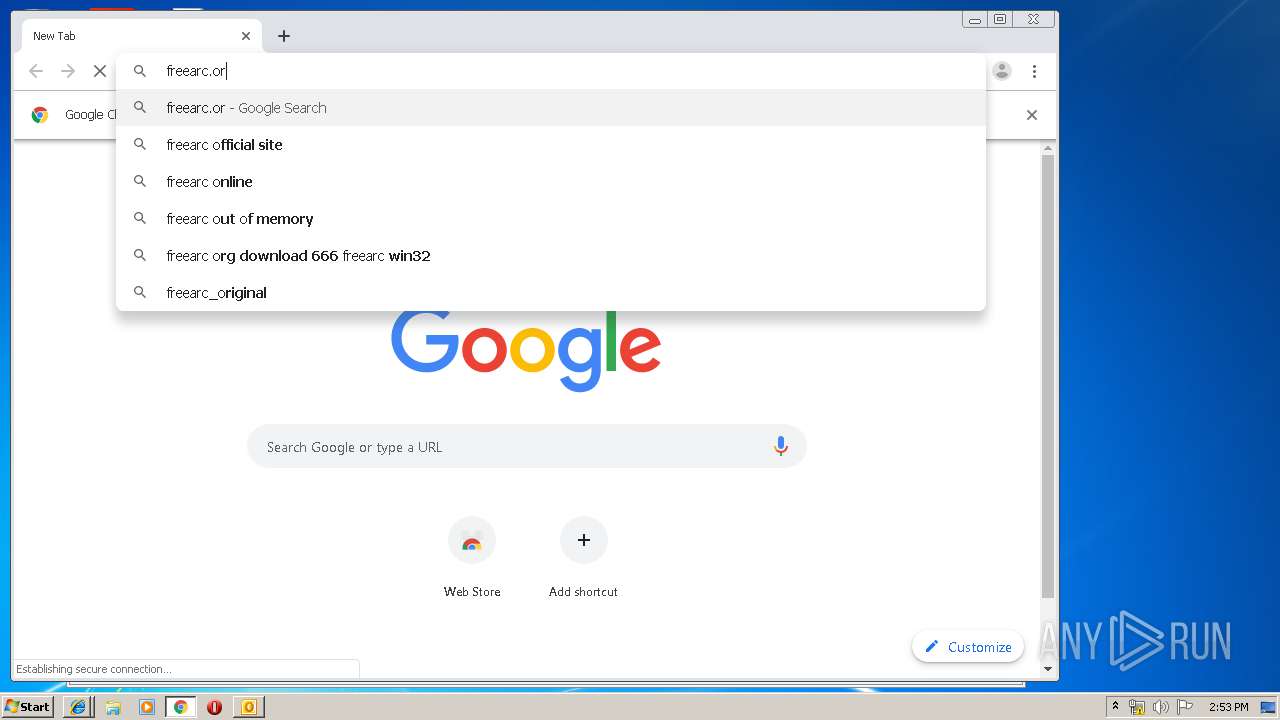
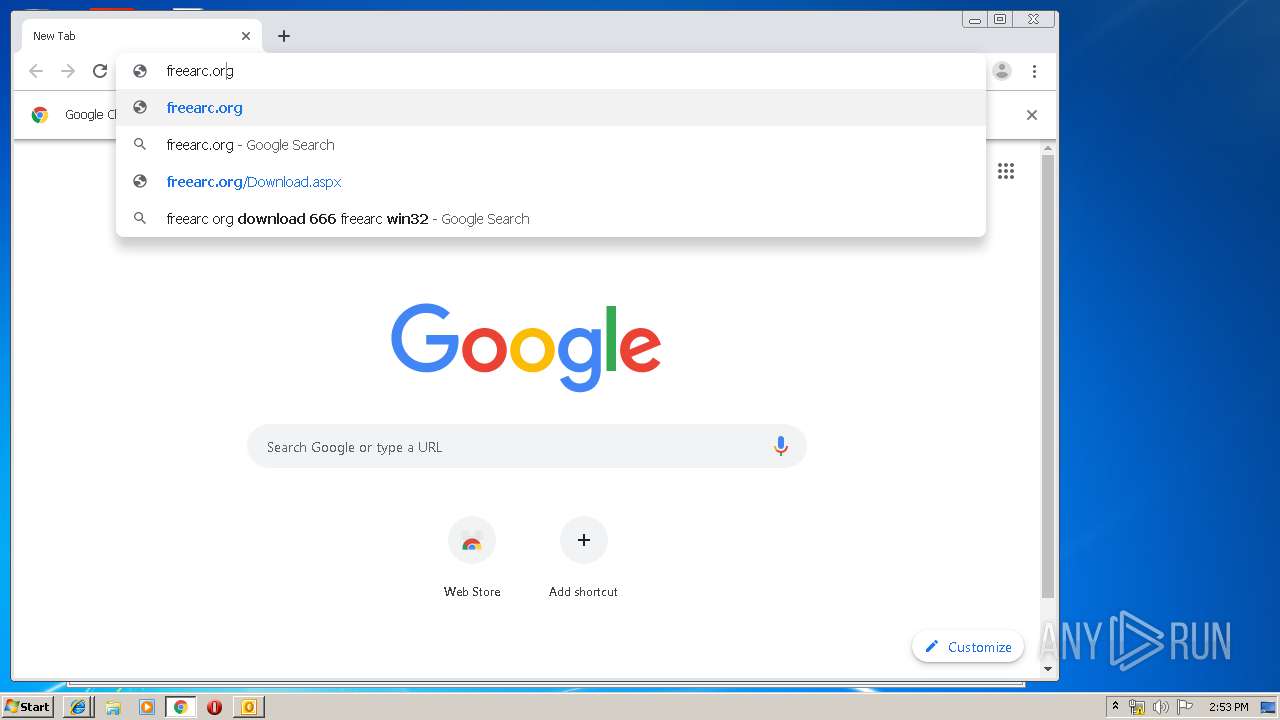
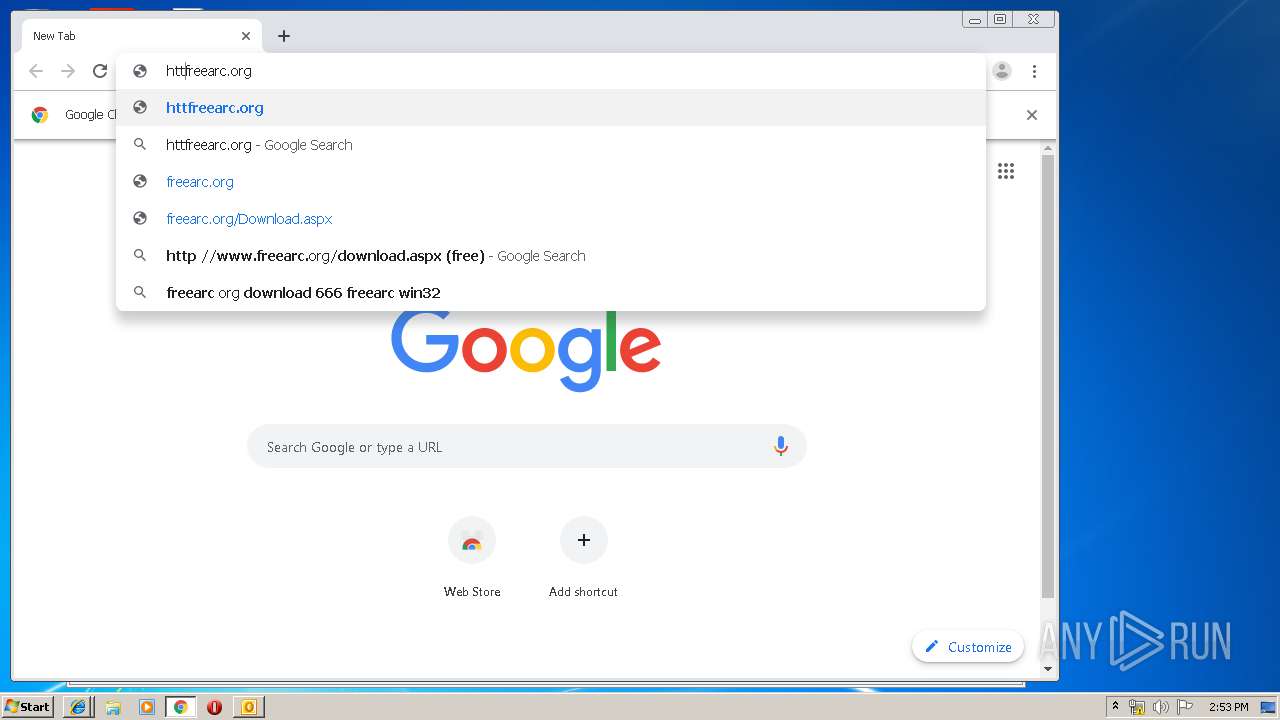
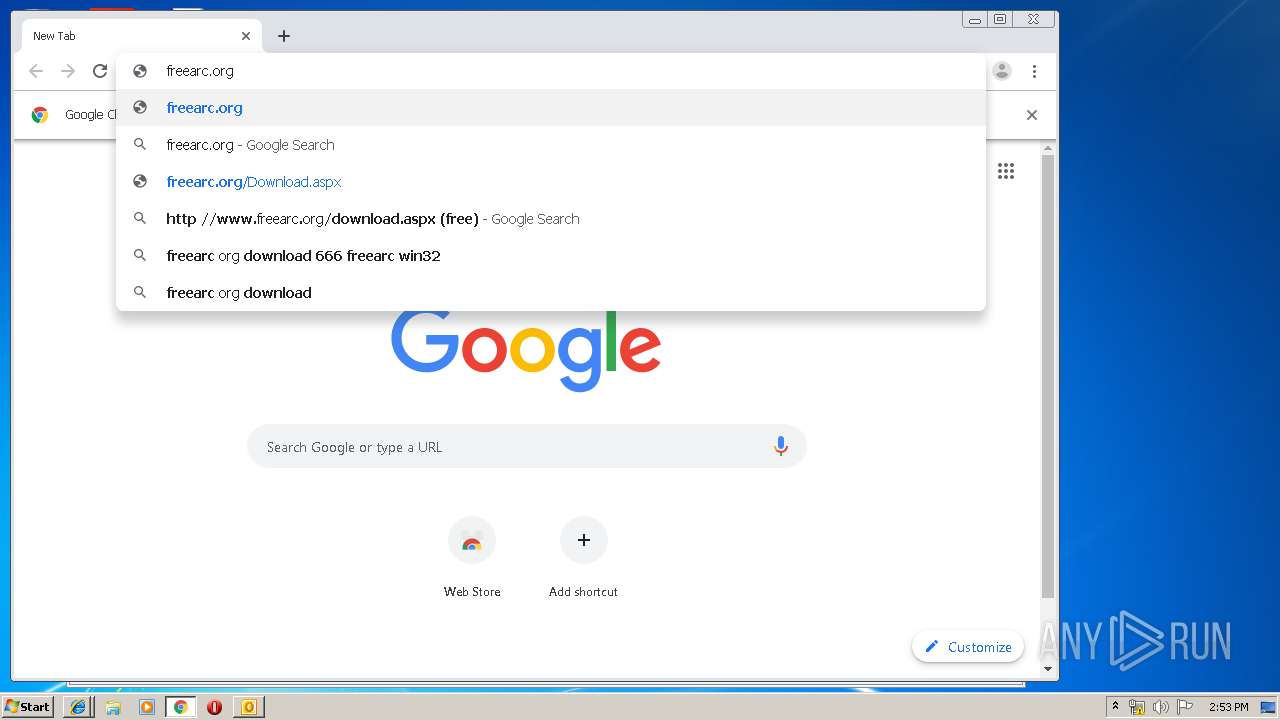
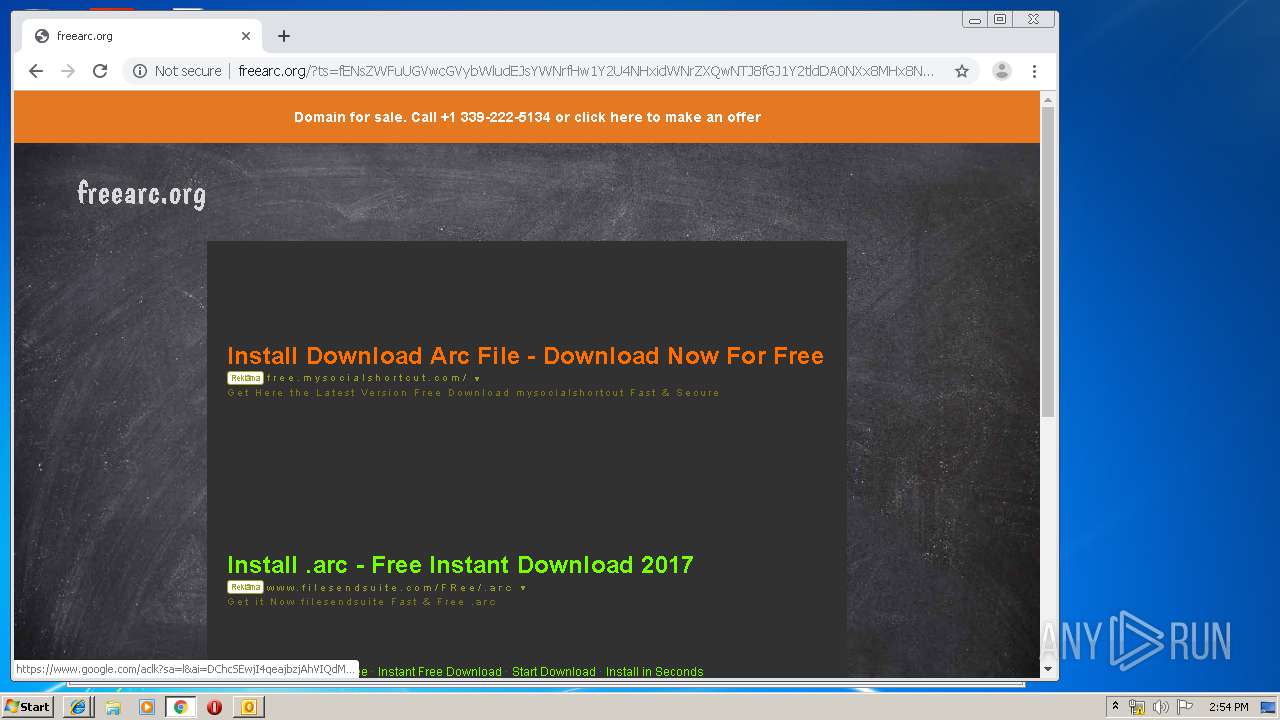
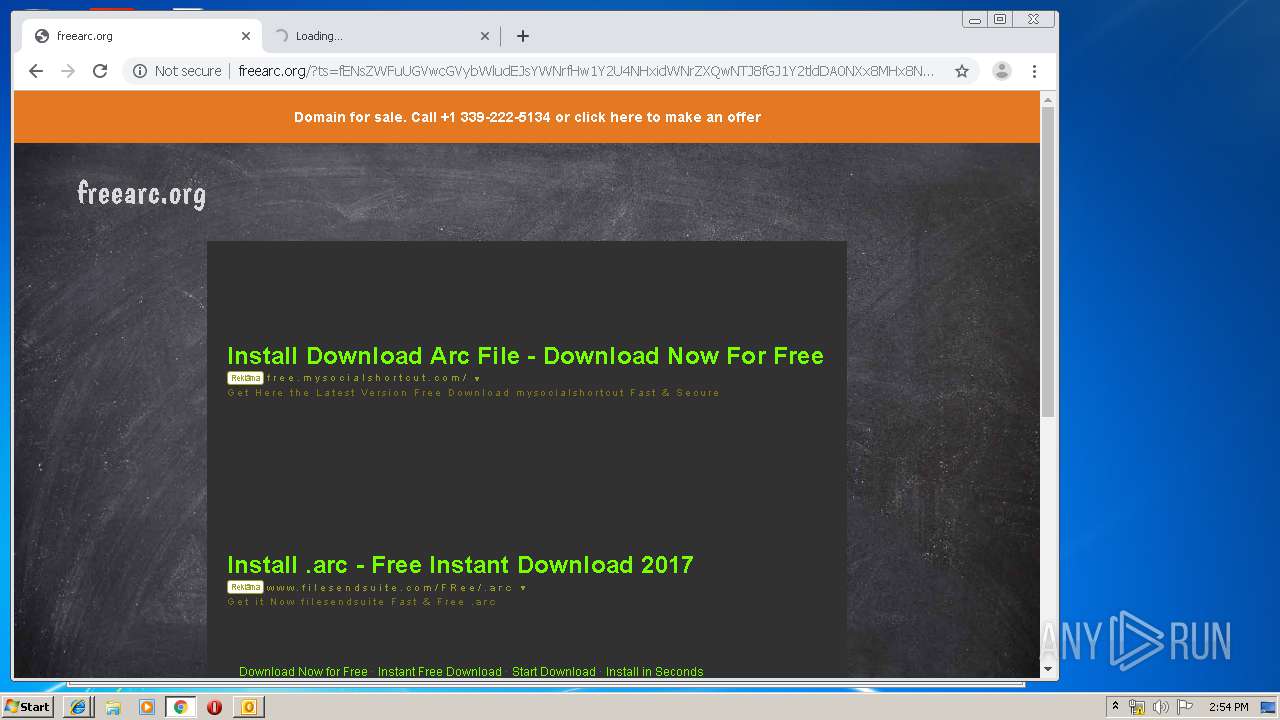
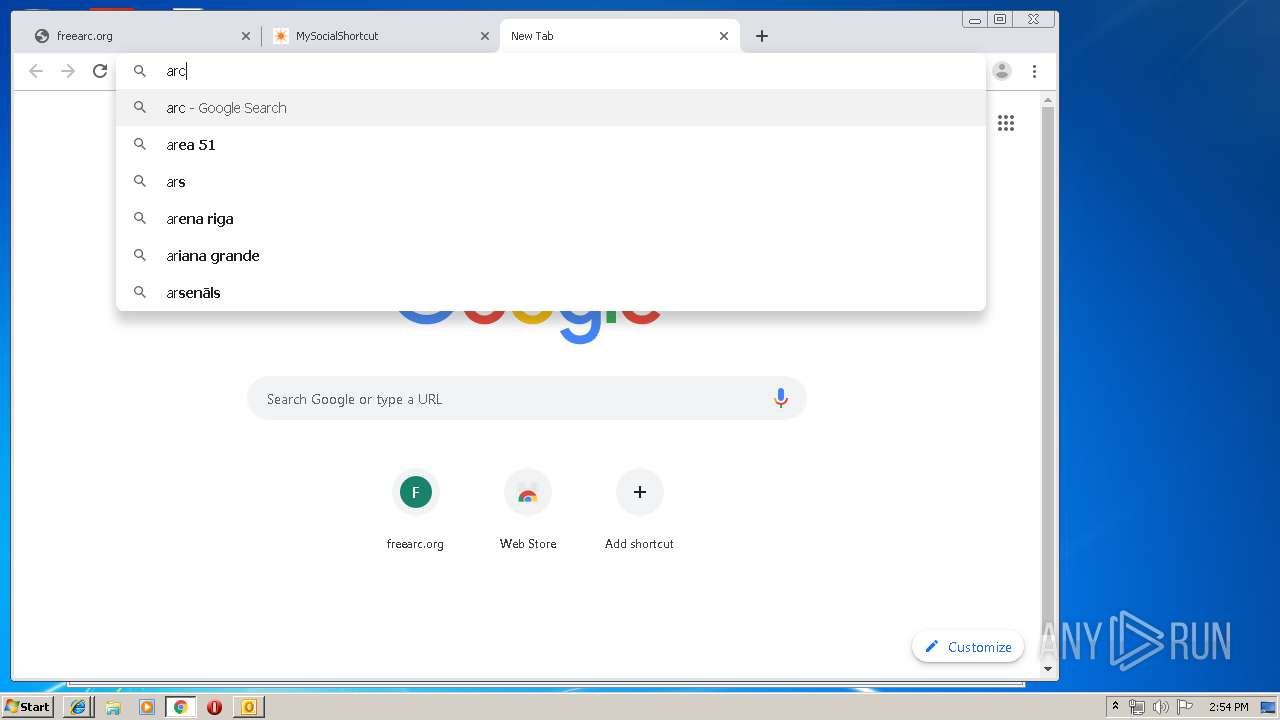
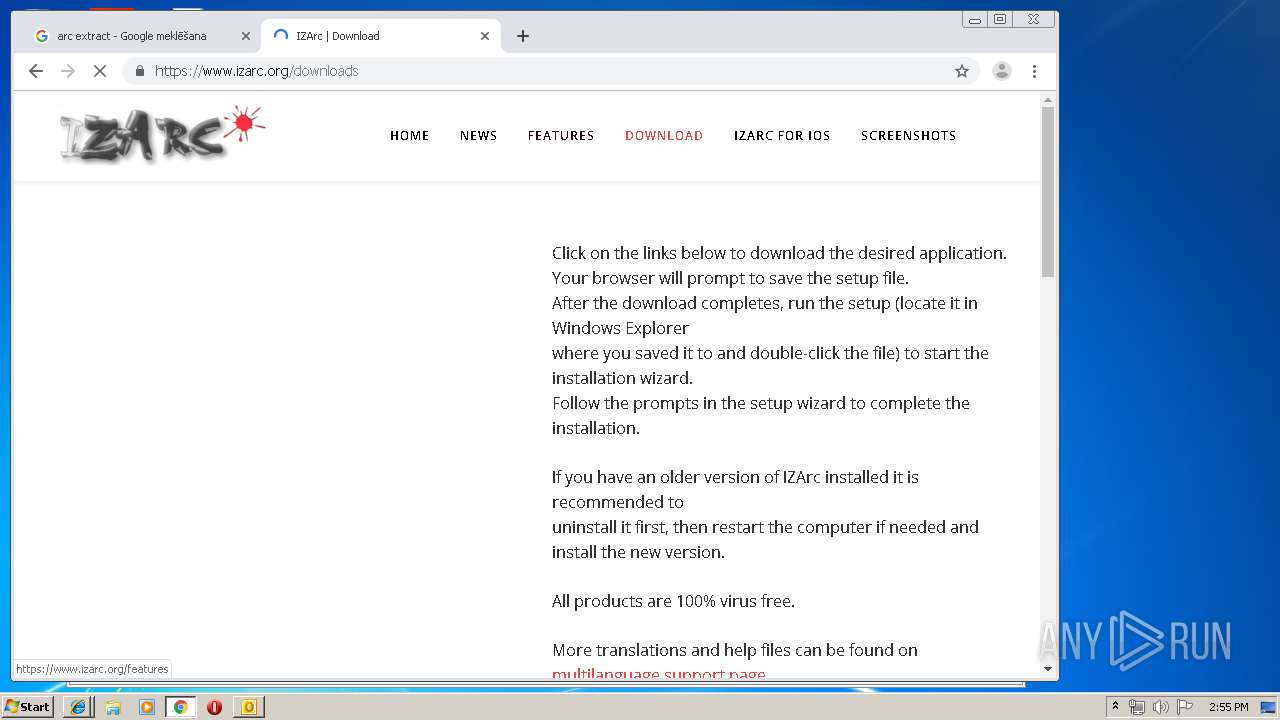
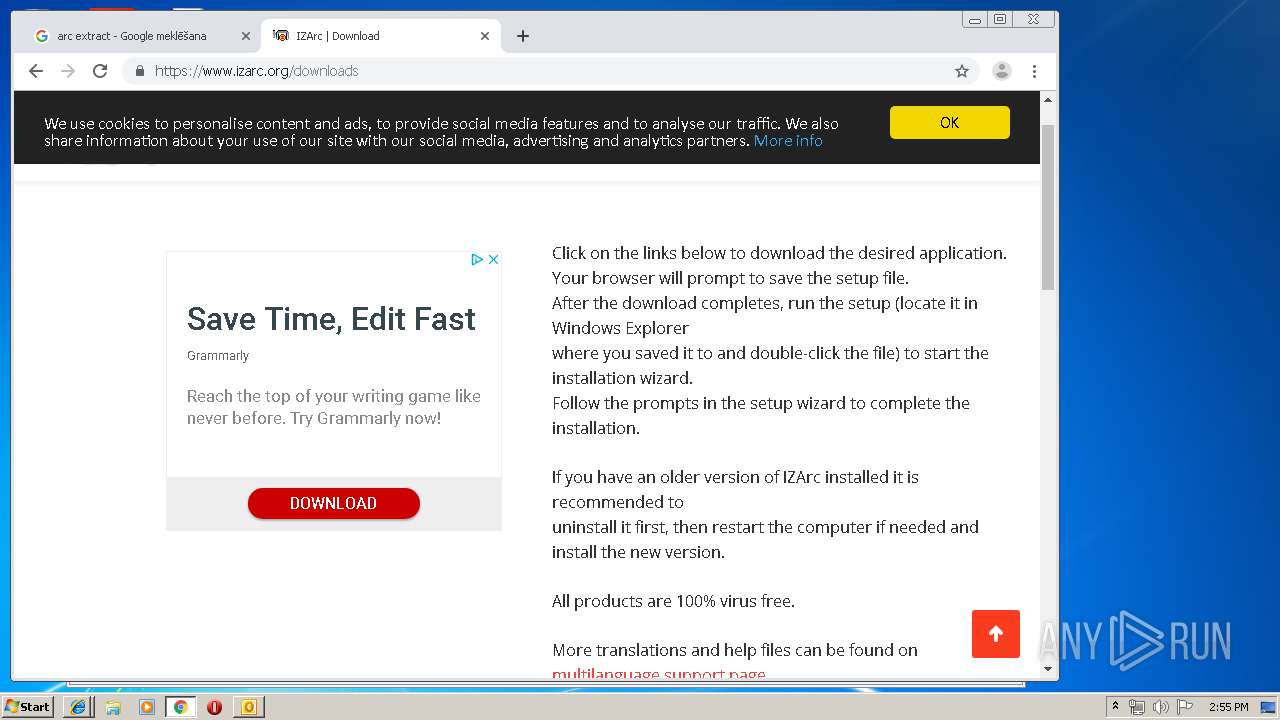
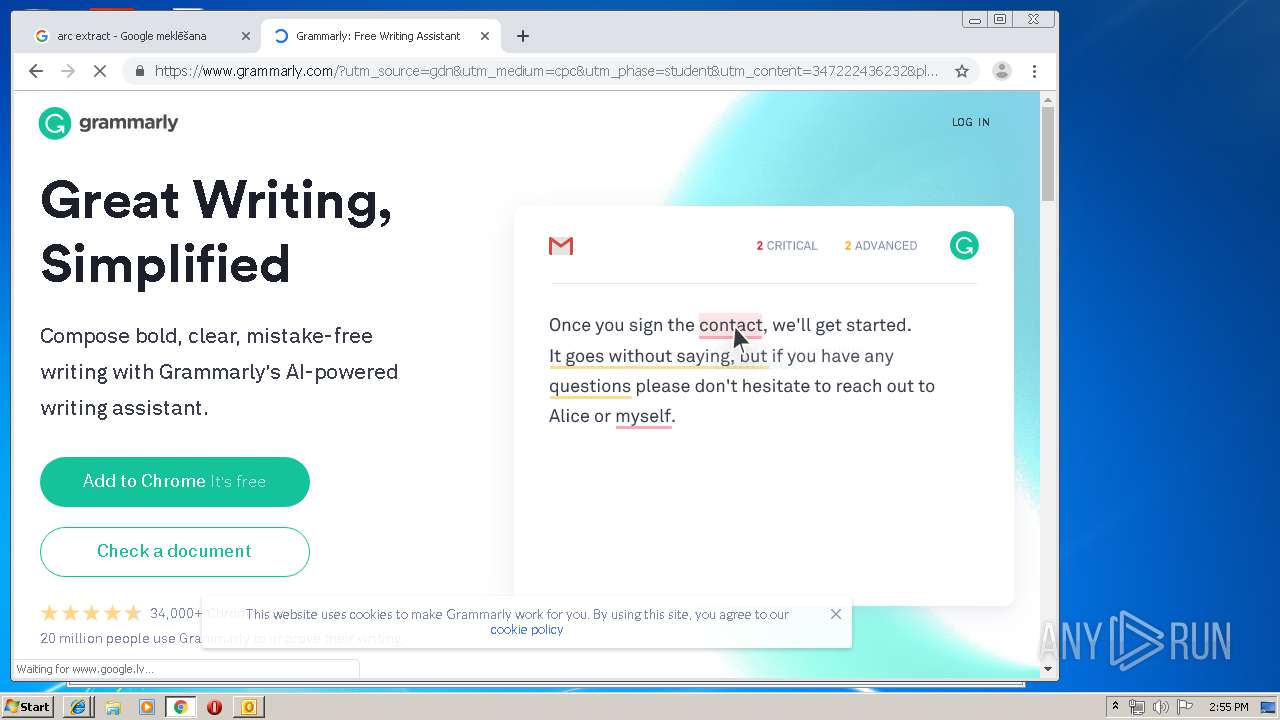
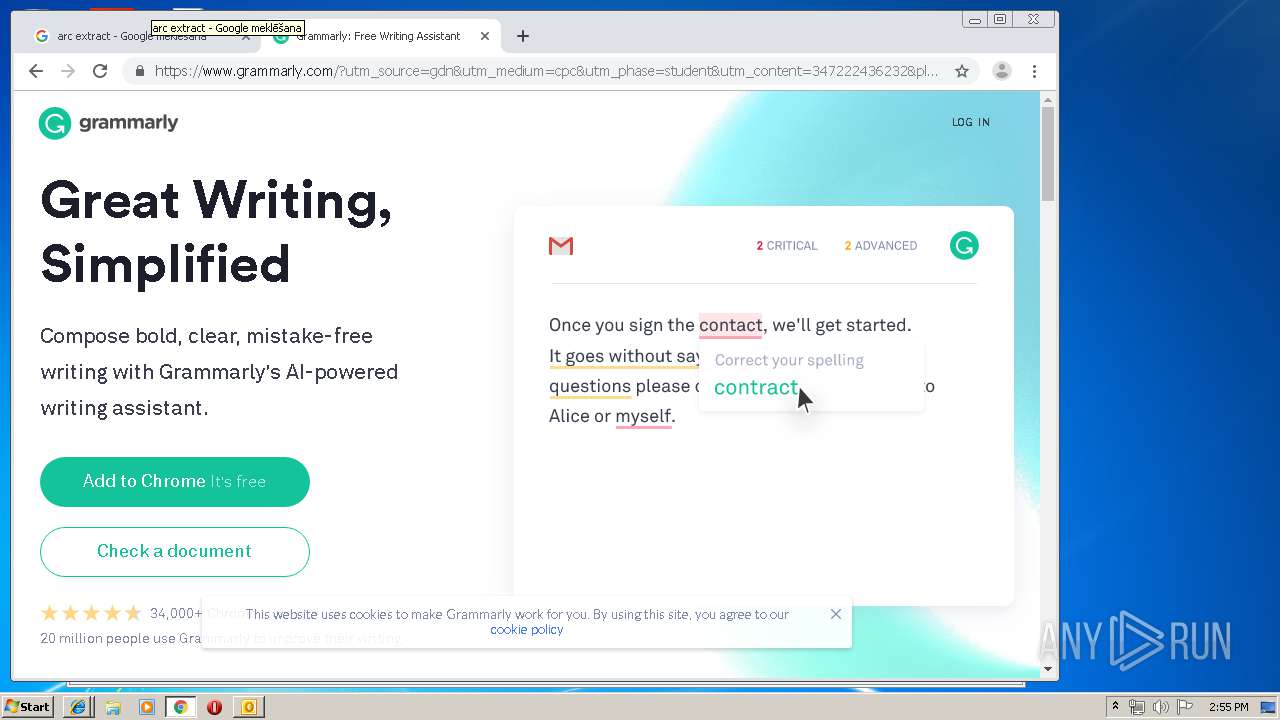
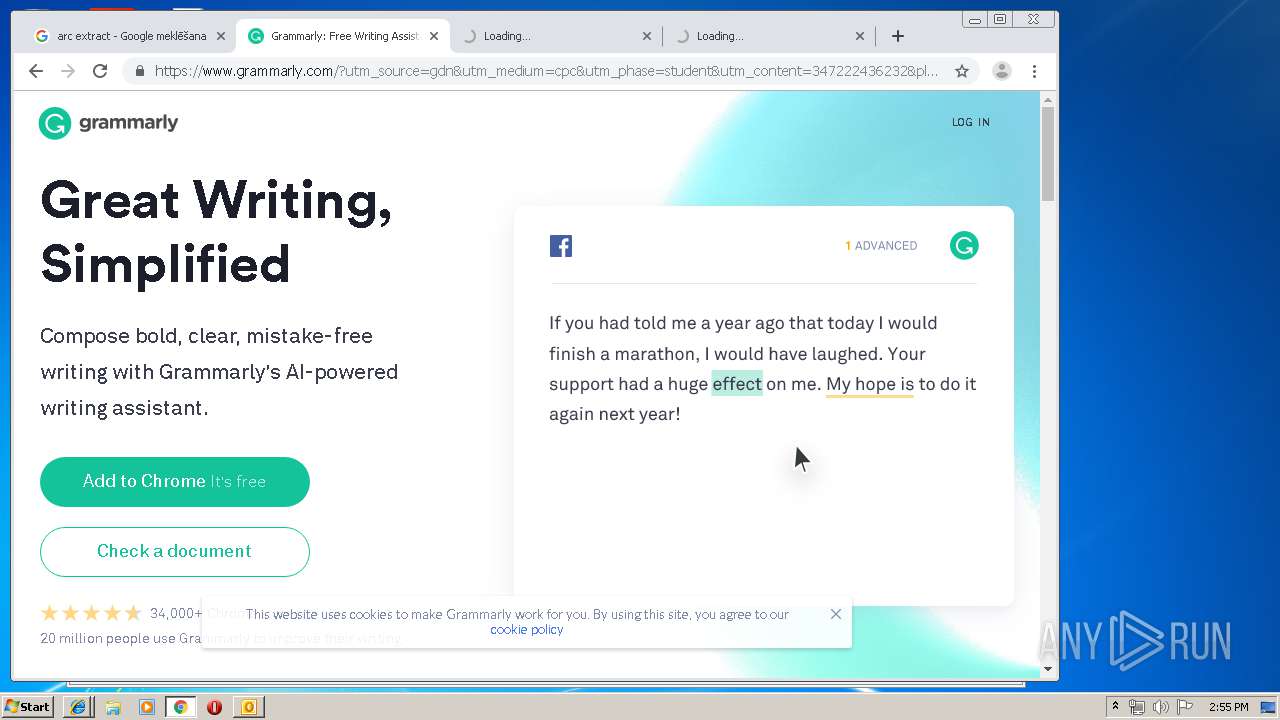
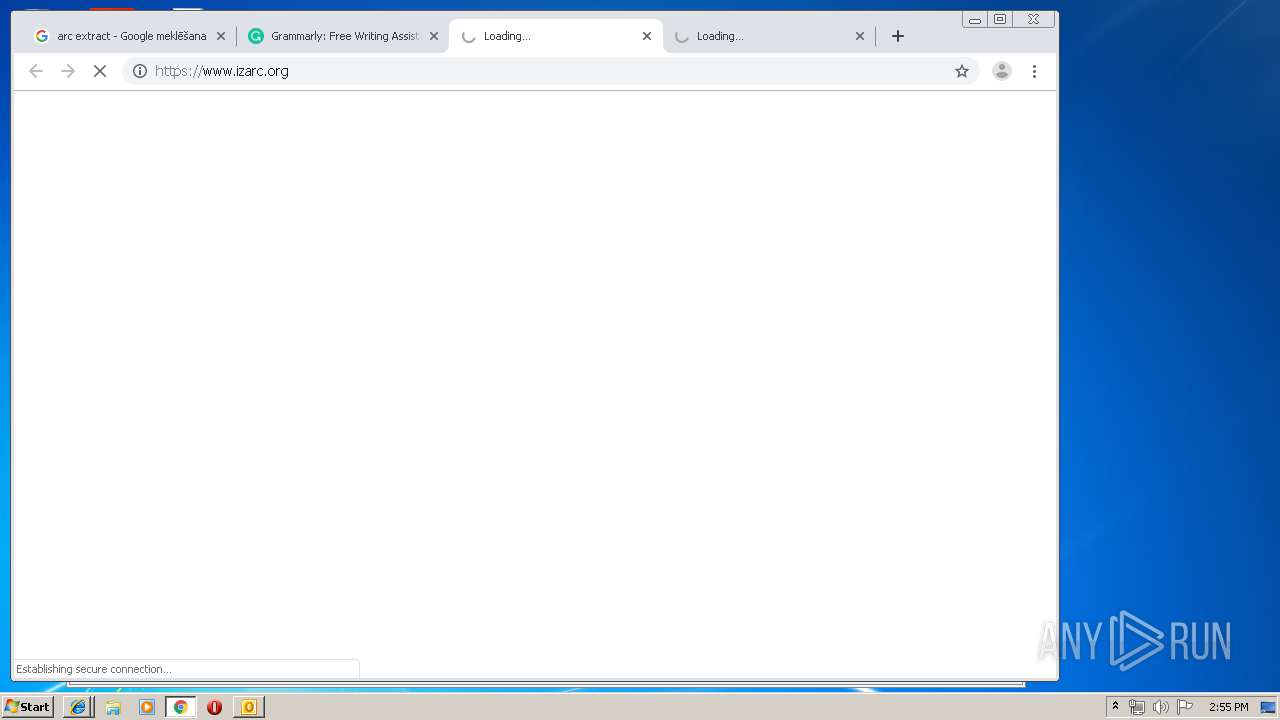
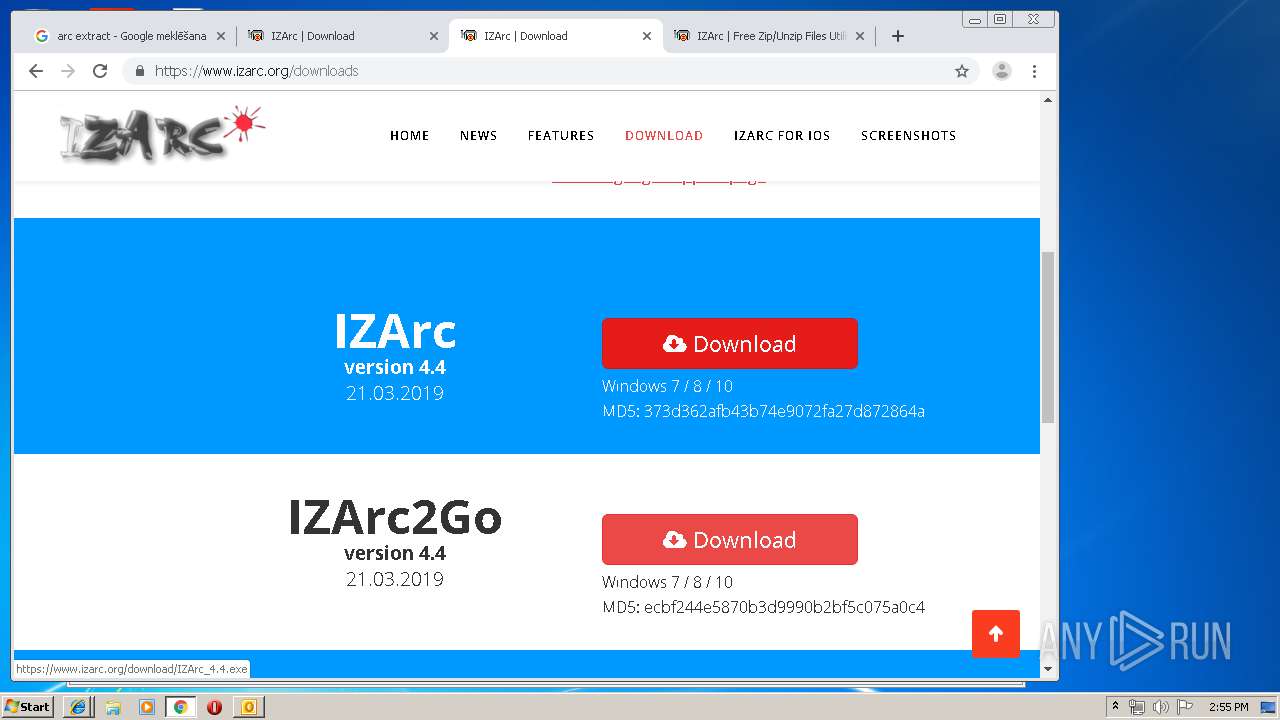
3536 | chrome.exe | GET | 200 | 185.53.178.6:80 | http://freearc.org/ | DE | html | 3.83 Kb | malicious |
3536 | chrome.exe | GET | 200 | 185.53.178.6:80 | http://freearc.org/?ts=fENsZWFuUGVwcGVybWludEJsYWNrfHw1Y2U4NHxidWNrZXQwNTJ8fGJ1Y2tldDA0NXx8MHx8NWQyZjI4NmM4NmM0OHx8fDE1NjMzNzE2MjguNTYxfGQzNjQ2MjEwZDdlYWFkOTAxMDgwMTUwMjlmNzgzZGIxMDY4MzBjNmJ8fHx8fDF8fHwwfDVkMmYyODZjOGYyOWM0NDUzMDhiNDhhYXx8fDF8fHx8fDB8MHx8fHx8fHx8fHwwfDF8NWQyZjI4NmM4ZjI5YzQ0NTMwOGI0OGFhfDB8MHwxfDB8MHxXMTA9fHwx&query=Arc%2520File%2520Extractor&afdToken=3B1g8gTLA42RiWy_wvTMOXaggPwY12kUr7PurX9ipz7F-_jsy-lgHd_9p8FsLILAY3LCTlv1XjT76OoqwNFLIgqCx3JYTM3YfLIh_emEUGw&pcsa=false | DE | html | 3.74 Kb | malicious |
3536 | chrome.exe | GET | 200 | 13.32.177.149:80 | http://d1lxhc4jvstzrp.cloudfront.net/themes/assets/style.css | US | text | 343 b | shared |
3536 | chrome.exe | GET | 302 | 216.58.207.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 522 b | whitelisted |
3536 | chrome.exe | GET | 200 | 13.32.177.149:80 | http://d1lxhc4jvstzrp.cloudfront.net/scripts/js3caf.js | US | text | 6.17 Kb | shared |
3536 | chrome.exe | GET | 200 | 13.32.177.149:80 | http://d1lxhc4jvstzrp.cloudfront.net/themes/cleanPeppermintBlack_14170d94/style.css | US | text | 671 b | shared |
3536 | chrome.exe | GET | 200 | 185.53.178.6:80 | http://freearc.org/track.php?domain=freearc.org&toggle=browserjs&uid=MTU2MzM3MTY0MC4yNDExOmMwM2MzYTVkODdhMmYzMmM1NjBmYmE4OTg2MTYzYTM4MmI4NmU0NmIxM2Y1MzQxOWZmODRiNWY5MDhiNTEzZGI6NWQyZjI4NzgzYWRmZQ%3D%3D | DE | binary | 20 b | malicious |
3536 | chrome.exe | GET | 200 | 185.53.178.6:80 | http://freearc.org/track.php?domain=freearc.org&caf=1&toggle=answercheck&answer=yes&uid=MTU2MzM3MTY0MC4yNDExOmMwM2MzYTVkODdhMmYzMmM1NjBmYmE4OTg2MTYzYTM4MmI4NmU0NmIxM2Y1MzQxOWZmODRiNWY5MDhiNTEzZGI6NWQyZjI4NzgzYWRmZQ%3D%3D | DE | binary | 20 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3412 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3972 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3972 | iexplore.exe | 172.217.18.4:443 | www.google.com | Google Inc. | US | whitelisted |
2412 | iexplore.exe | 172.217.18.4:443 | www.google.com | Google Inc. | US | whitelisted |
2748 | iexplore.exe | 172.217.18.4:443 | www.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.18.4:443 | www.google.com | Google Inc. | US | whitelisted |
3536 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3536 | chrome.exe | 172.217.21.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3536 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3536 | chrome.exe | 172.217.16.174:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
www.google.com |
| malicious |
www.bing.com |
| whitelisted |
dns.msftncsi.com |
| shared |
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3536 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |