| File name: | Free porn.exe |
| Full analysis: | https://app.any.run/tasks/8f6c1008-83f4-4b60-86ee-6e8857a6136d |
| Verdict: | Malicious activity |
| Analysis date: | August 05, 2020, 17:09:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 137860D1B5FEB9398AB44431F89D91CB |
| SHA1: | 456279AEFA02CC3EAAC1E2BD6534E86742608DA5 |
| SHA256: | FE625188DA34D9B6551CE1C34627CEFD1A3E4DA78F1DACC9442D04BD0EA944B0 |
| SSDEEP: | 48:KrMqTVH79ACs5jJLIb3zPlRVCyXLhG7erSRycGaPqw0+EvWK2:kMGVw3eD1EeGRBDE92 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
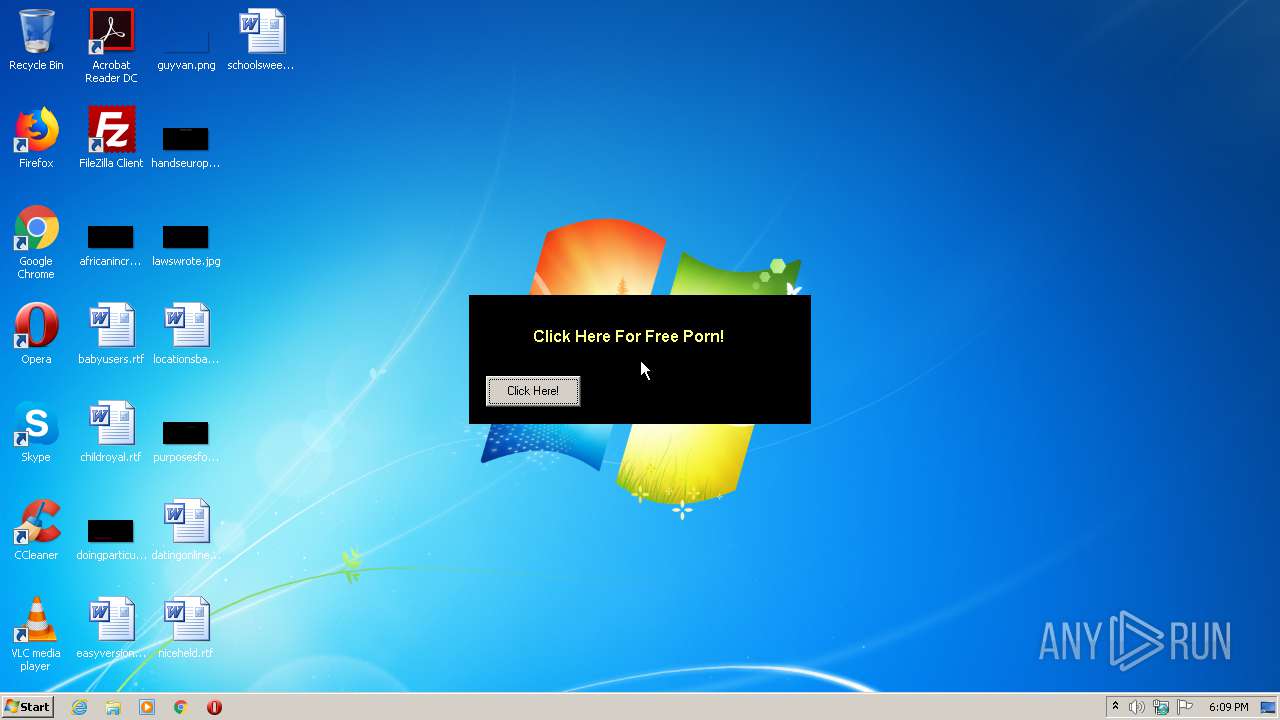
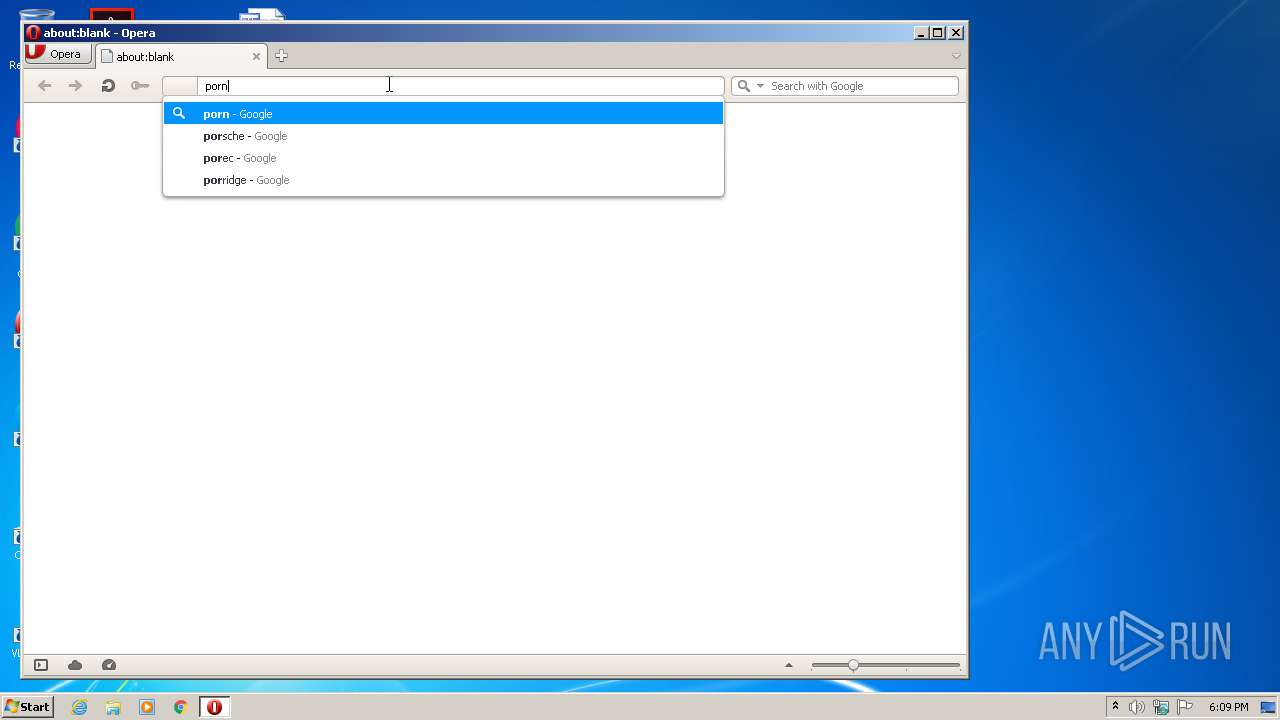
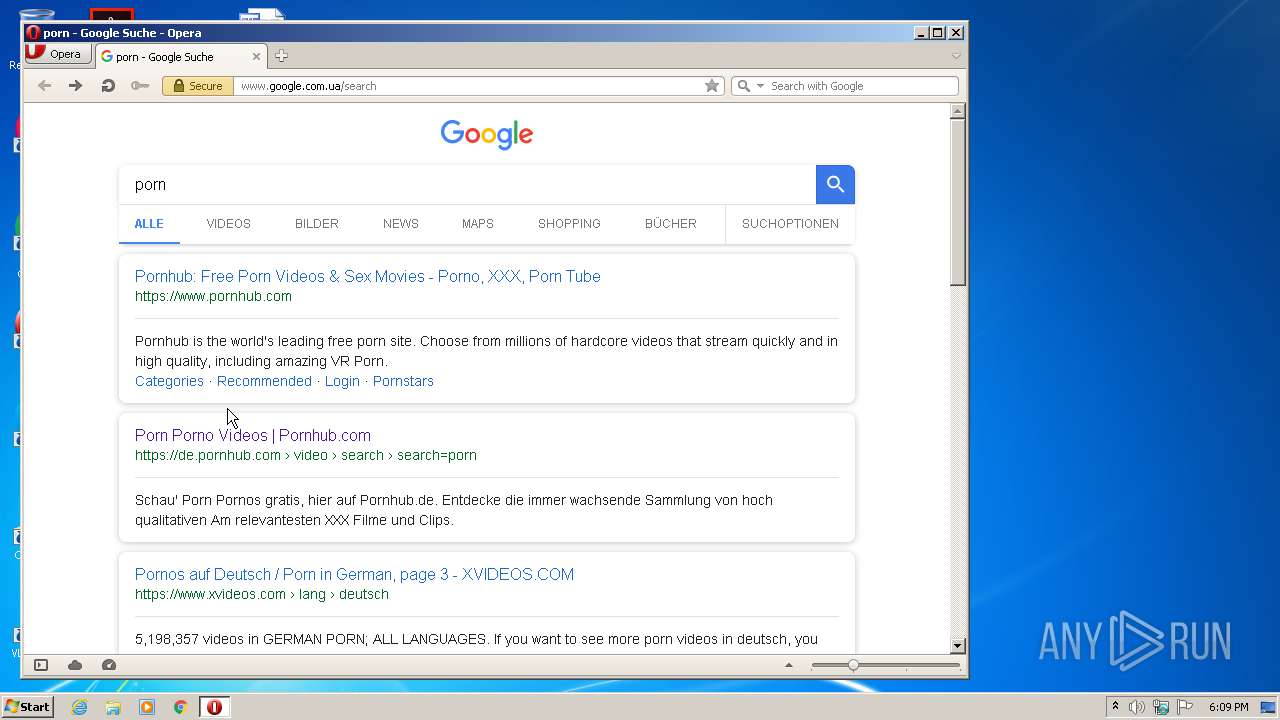
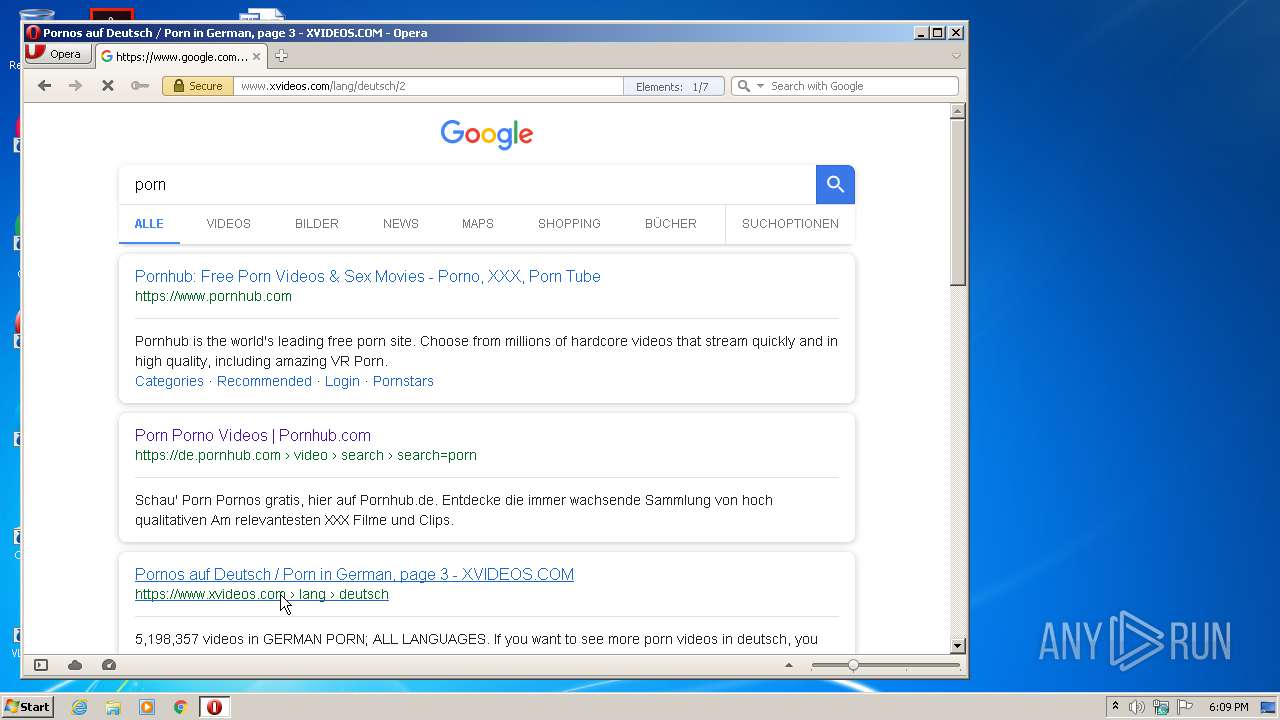
Manual execution by user
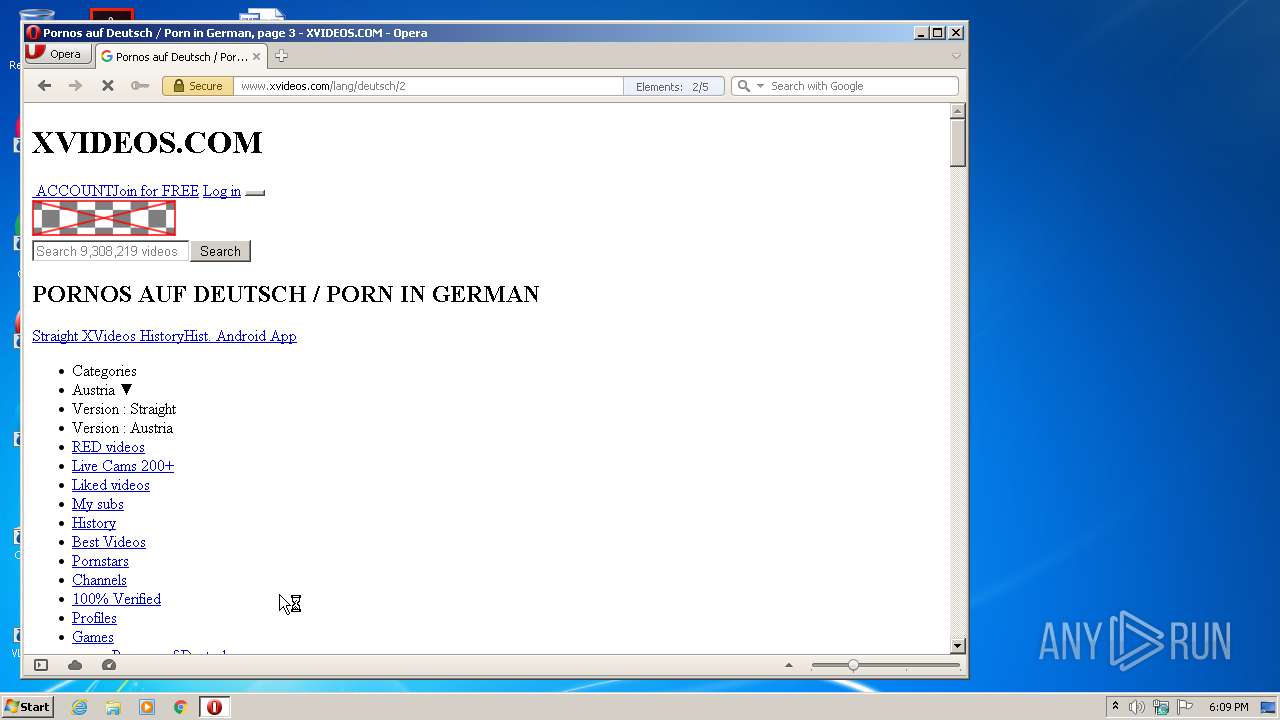
- opera.exe (PID: 2416)
Creates files in the user directory
- opera.exe (PID: 2416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (84.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (6.7) |
| .exe | | | Win32 Executable (generic) (4.6) |
| .exe | | | Generic Win/DOS Executable (2) |
| .exe | | | DOS Executable Generic (2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:08:25 08:52:10+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 4096 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1044 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | BSG |
| ProductName: | Free porn |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | Free porn |
| OriginalFileName: | Free porn.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Aug-2013 06:52:10 |
| Detected languages: |
|
| CompanyName: | BSG |
| ProductName: | Free porn |
| FileVersion: | 1.00 |
| ProductVersion: | 1.00 |
| InternalName: | Free porn |
| OriginalFilename: | Free porn.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000B0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 25-Aug-2013 06:52:10 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000C04 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 3.05261 |
.data | 0x00002000 | 0x000009E4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00003000 | 0x000008CC | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.93384 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.13726 | 524 | Unicode (UTF 16LE) | English - United States | RT_VERSION |
30001 | 2.57965 | 304 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30002 | 1.76987 | 744 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30003 | 2.07177 | 296 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
Imports
MSVBVM60.DLL |
Total processes
39
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
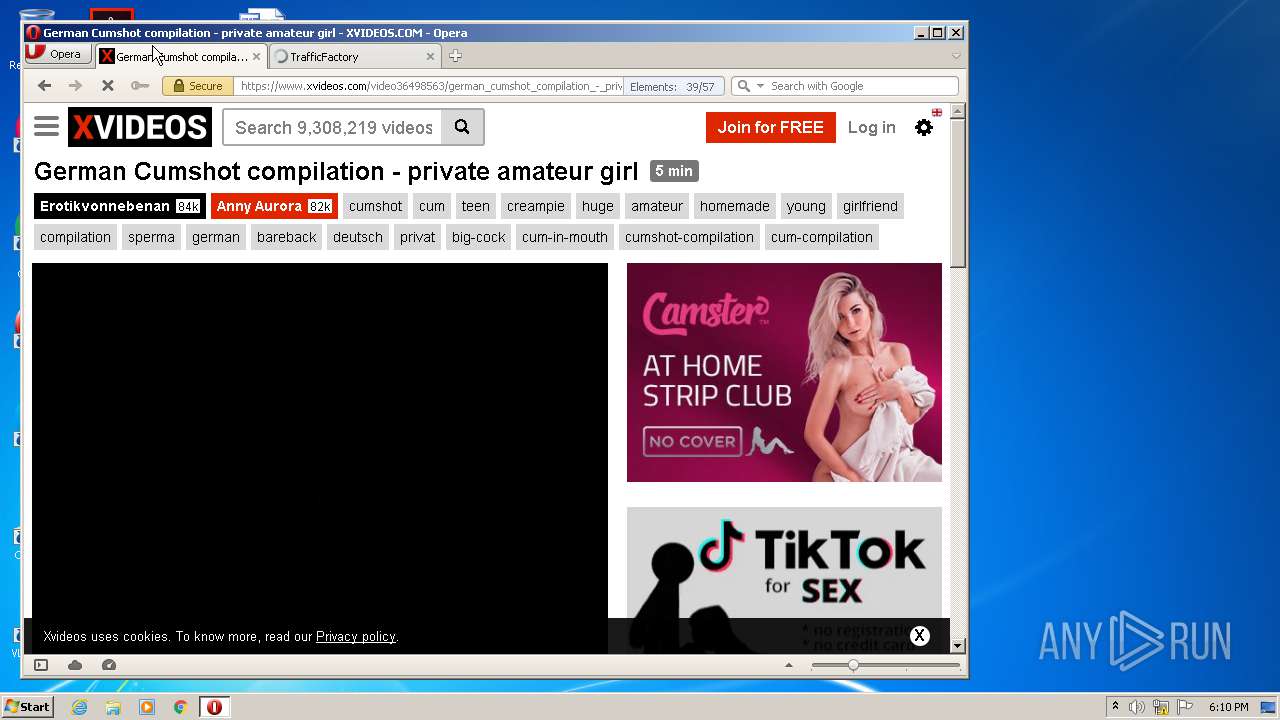
| 2416 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 2808 | "C:\Users\admin\AppData\Local\Temp\Free porn.exe" | C:\Users\admin\AppData\Local\Temp\Free porn.exe | — | explorer.exe | |||||||||||
User: admin Company: BSG Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
206
Read events
147
Write events
59
Delete events
0
Modification events
| (PID) Process: | (2416) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe | |||
| (PID) Process: | (2416) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\135\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2416) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\135\52C64B7E |
| Operation: | write | Name: | @"%windir%\System32\ie4uinit.exe",-732 |
Value: Finds and displays information and Web sites on the Internet. | |||
Executable files
0
Suspicious files
35
Text files
62
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2416 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr128A.tmp | — | |
MD5:— | SHA256:— | |||
| 2416 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr12C9.tmp | — | |
MD5:— | SHA256:— | |||
| 2416 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\6BOOK2I1WI36BKZIWV9A.temp | — | |
MD5:— | SHA256:— | |||
| 2416 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00001.tmp | — | |
MD5:— | SHA256:— | |||
| 2416 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr28E2.tmp | — | |
MD5:— | SHA256:— | |||
| 2416 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 2416 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2416 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr34AB.tmp | — | |
MD5:— | SHA256:— | |||
| 2416 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
| 2416 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms~RFe1e32.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
182
DNS requests
27
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
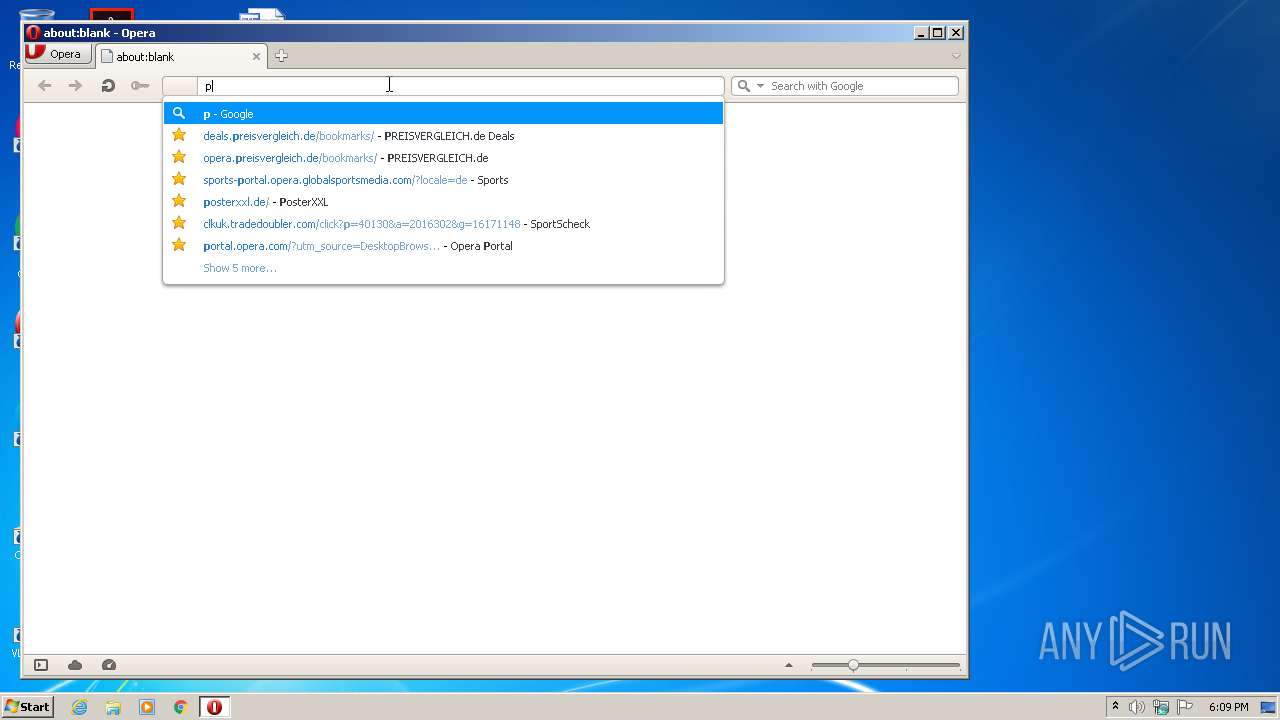
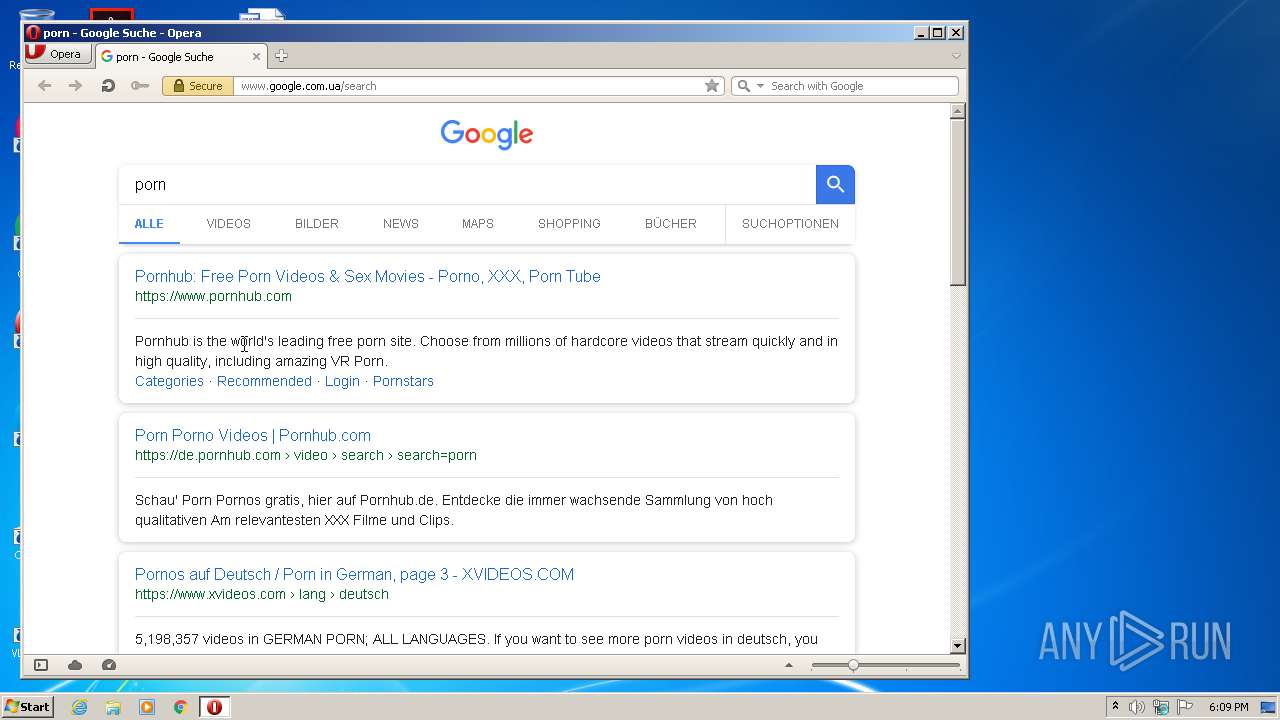
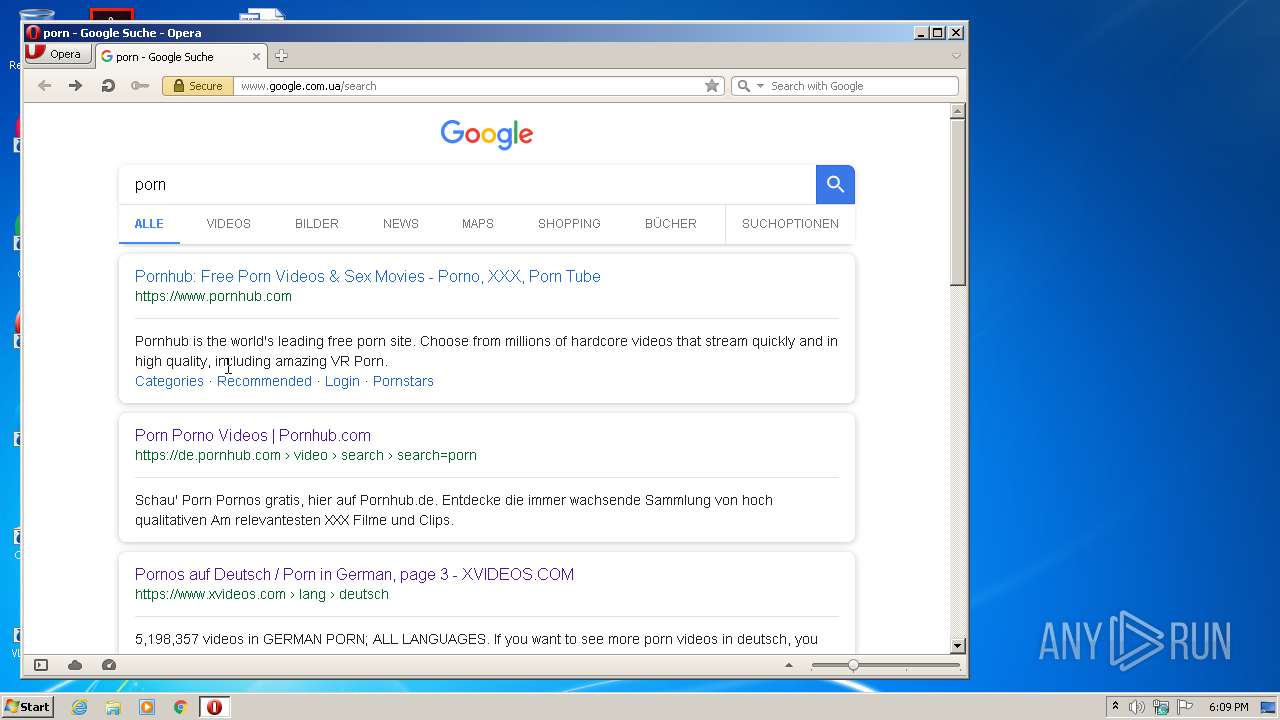
2416 | opera.exe | GET | 302 | 172.217.16.195:80 | http://www.google.com.ua/search?client=opera&q=porn&sourceid=opera&ie=utf-8&oe=utf-8&channel=suggest | US | html | 333 b | whitelisted |
2416 | opera.exe | GET | 302 | 172.217.16.195:80 | http://www.google.com.ua/search?q=porn&sourceid=opera&ie=utf-8&oe=utf-8&channel=suggest | US | html | 317 b | whitelisted |
2416 | opera.exe | GET | 200 | 93.184.220.29:80 | http://status.rapidssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRhhZrQET0hvbSHUJmNfBKqR%2FiT7wQUU8oXWfxrwAMhLxqu5KqoHIJW2nUCEATZGbzA54z2vc3WFqb5HW4%3D | US | der | 471 b | shared |
2416 | opera.exe | GET | 200 | 151.139.128.14:80 | http://crl.comodoca.com/AAACertificateServices.crl | US | der | 506 b | whitelisted |
2416 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertGlobalRootCA.crl | US | der | 631 b | whitelisted |
2416 | opera.exe | GET | 200 | 151.139.128.14:80 | http://crl.comodoca.com/COMODORSACertificationAuthority.crl | US | der | 812 b | whitelisted |
2416 | opera.exe | GET | 200 | 93.184.220.29:80 | http://status.rapidssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRhhZrQET0hvbSHUJmNfBKqR%2FiT7wQUU8oXWfxrwAMhLxqu5KqoHIJW2nUCEAUFZiGxD3Dxd9eTEf0Ms%2Bg%3D | US | der | 471 b | shared |
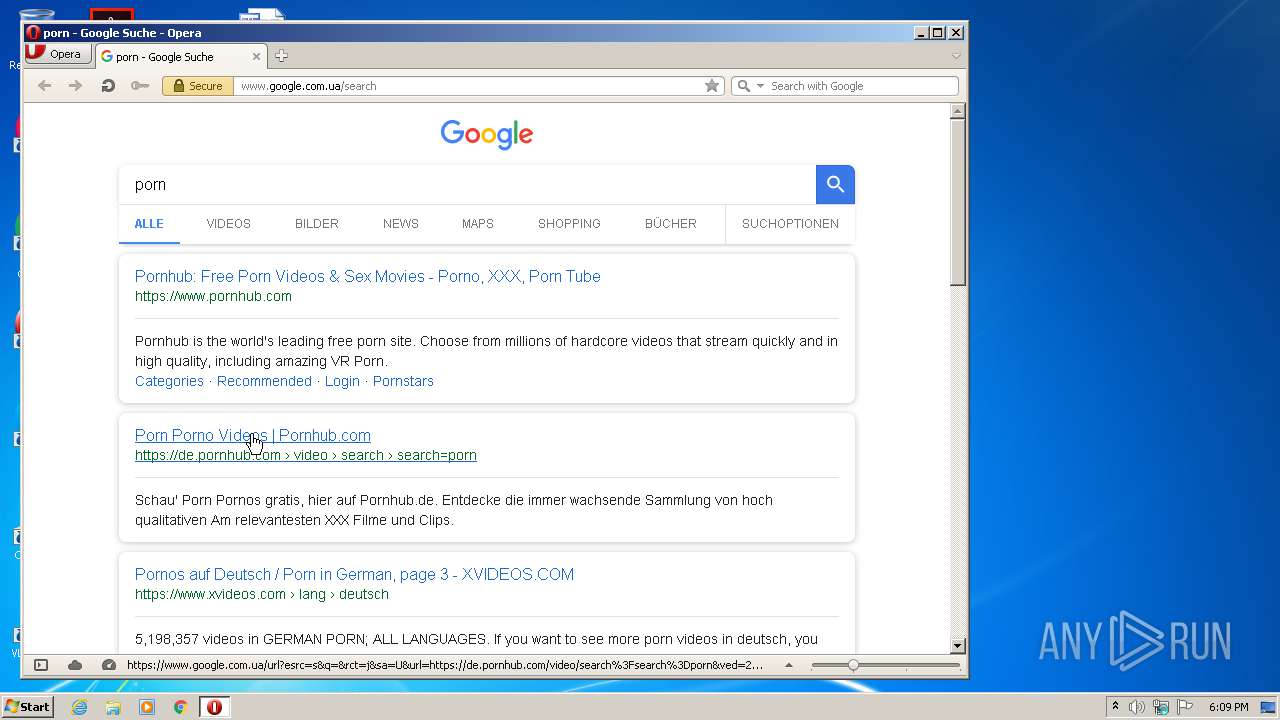
2416 | opera.exe | GET | 200 | 185.88.180.106:80 | http://rpc-php.trafficfactory.biz/click/.45083qGgax5EVLUSRXg45B_AGvfTTKJBZ3TLZ7oQp-18KEttmCKtznQEM-28GEGjMWBQN1DorIjCStEip1-2gN1Ntb3lO1McxNHAeHeRF6Ukzwk1w5C_cJXhK0dtw-O6dosgM60Q6yCrPuPLRmNQM3XU2gLvel9_5GiOS3zqUzRMXUGGJC6nvVjqn0tnHNH0JRmdzTOX2P4c2ffe9Wg-G9bs6-X9iOlr3JcVlXRpvKNLuDQqPc3eBpEA4fCIVnnknCgTs6-VEChdkZH0Nbd0EfgMOMMUc0j2jhLthPolXXX6RtXuWsePY8BjroTkkt0z9ILpsVu5AwhjGRCT9E_hNCx50yNz_1j14MB6DeYFHXGvCX5KL7gVBzLAzYlSbF84KoZu-yBFvInOyATxw65Ku0zgn36iuObXKUi7qAj32ic12mA=/5e91f73339f325d35b034720f72e7d10 | NL | html | 4.67 Kb | suspicious |
2416 | opera.exe | GET | 200 | 192.35.177.64:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | US | der | 994 b | whitelisted |
2416 | opera.exe | GET | 400 | 185.26.182.112:80 | http://sitecheck2.opera.com/?host=www.google.com.ua&hdn=Nxr6KEmdGjdmqcWka8dkkA== | unknown | html | 150 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2416 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
2416 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2416 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
2416 | opera.exe | 172.217.22.14:80 | clients1.google.com | Google Inc. | US | whitelisted |
2416 | opera.exe | 172.217.16.195:80 | www.google.com.ua | Google Inc. | US | whitelisted |
2416 | opera.exe | 185.26.182.112:80 | sitecheck2.opera.com | Opera Software AS | — | malicious |
2416 | opera.exe | 172.217.16.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2416 | opera.exe | 172.217.18.99:80 | crl.pki.goog | Google Inc. | US | whitelisted |
2416 | opera.exe | 172.217.23.163:443 | id.google.com | Google Inc. | US | whitelisted |
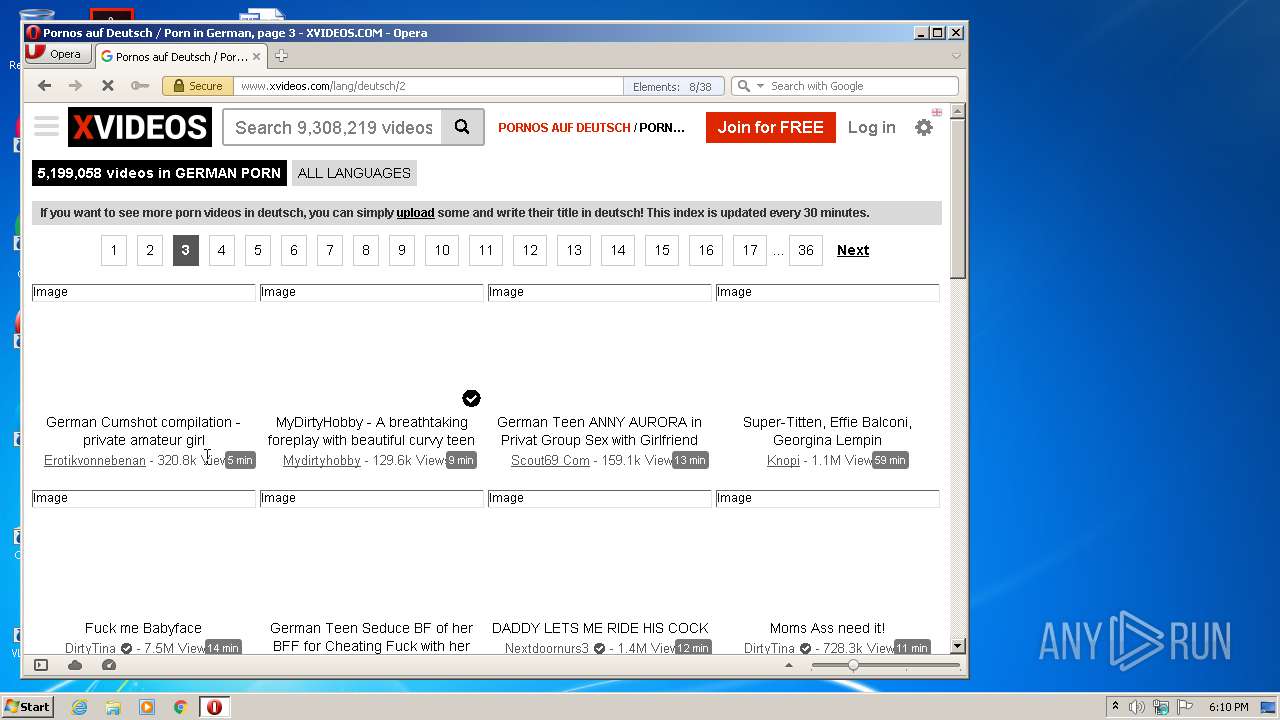
2416 | opera.exe | 8.252.24.243:443 | img-l3.xvideos-cdn.com | Level 3 Communications, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
sitecheck2.opera.com |
| whitelisted |
crl.pki.goog |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
id.google.com.ua |
| whitelisted |
id.google.com |
| whitelisted |
de.pornhub.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
2416 | opera.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
2416 | opera.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
2416 | opera.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
2416 | opera.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |