| File name: | aep.exe |
| Full analysis: | https://app.any.run/tasks/4a3b25ce-46ac-4d86-b650-1708f8e23bea |
| Verdict: | Malicious activity |
| Analysis date: | July 04, 2018, 16:10:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2965A0A1FA80D211C8B244E1491831DD |
| SHA1: | A22E9A02640FDC681E6037EE335CB198ACB32EE8 |
| SHA256: | FE5F5CE3BAC6809FEB30B5F65487442C92C324E4C3BBEFF298EF8A3664BA5531 |
| SSDEEP: | 49152:qvZRPCUcG2v/UecDvRs6sSQlUtYaBaL3+Ward7IEsjdYPpOOakQ3WPxPw:iPCU6nUecD5veCYaBO9takOakQGJw |
MALICIOUS
Application was dropped or rewritten from another process
- AirExplorer.exe (PID: 3452)
- airexplorerportable.exe (PID: 2788)
Loads dropped or rewritten executable
- airexplorerportable.exe (PID: 2788)
- AirExplorer.exe (PID: 3452)
SUSPICIOUS
Executable content was dropped or overwritten
- aep.exe (PID: 932)
- airexplorerportable.exe (PID: 2788)
Reads internet explorer settings
- AirExplorer.exe (PID: 3452)
- aep.exe (PID: 932)
Creates files in the user directory
- AirExplorer.exe (PID: 3452)
Changes IE settings (feature browser emulation)
- airexplorerportable.exe (PID: 2788)
- AirExplorer.exe (PID: 3452)
INFO
Reads settings of System Certificates
- AirExplorer.exe (PID: 3452)
Dropped object may contain URL's
- AirExplorer.exe (PID: 3452)
- aep.exe (PID: 932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:08:11 15:54:06+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 188928 |
| InitializedDataSize: | 194560 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1cec9 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Aug-2017 13:54:06 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 11-Aug-2017 13:54:06 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002E1CB | 0x0002E200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69427 |
.rdata | 0x00030000 | 0x000098A0 | 0x00009A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.12106 |
.data | 0x0003A000 | 0x0001F290 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.23719 |
.gfids | 0x0005A000 | 0x000000E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.05507 |
.rsrc | 0x0005B000 | 0x00004680 | 0x00004800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.6389 |
.reloc | 0x00060000 | 0x00001F58 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.62297 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.88998 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 4.12176 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 4.68705 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 3.1586 | 482 | UNKNOWN | English - United States | RT_STRING |
8 | 3.11685 | 460 | UNKNOWN | English - United States | RT_STRING |
9 | 3.15447 | 494 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
11 | 3.2036 | 1094 | UNKNOWN | English - United States | RT_STRING |
12 | 3.12889 | 358 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
Total processes
35
Monitored processes
3
Malicious processes
3
Suspicious processes
0
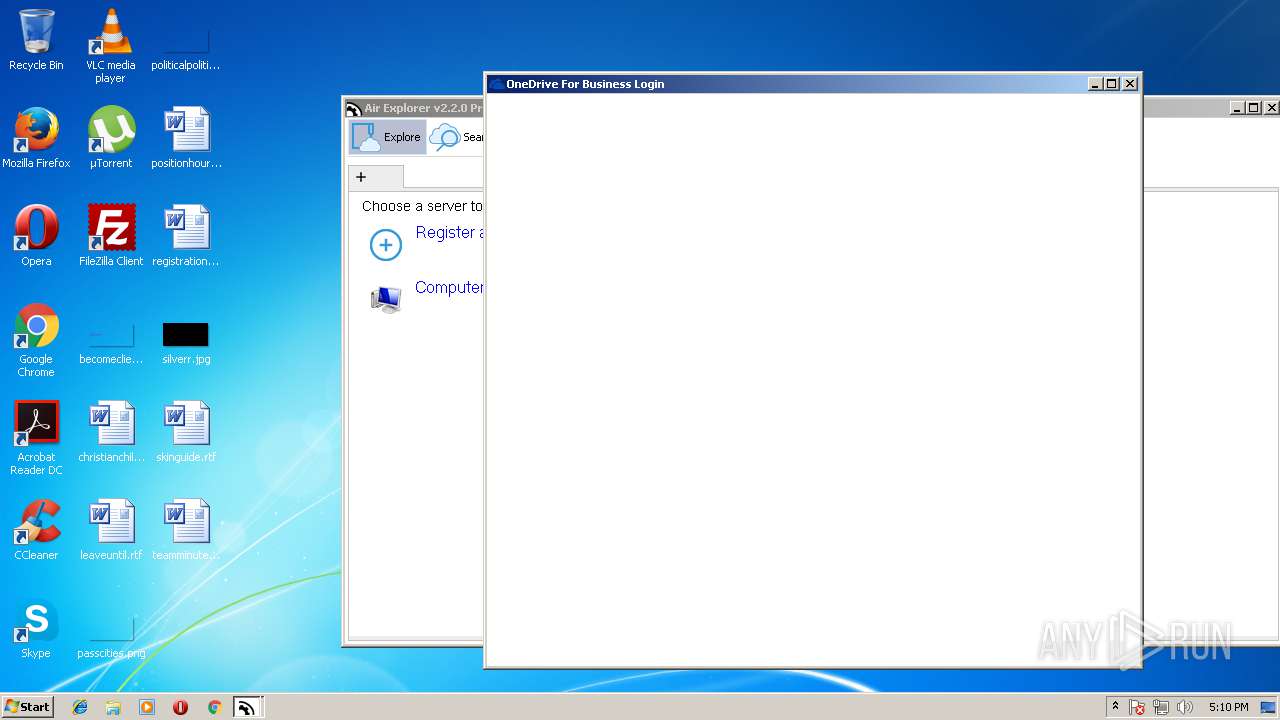
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 932 | "C:\Users\admin\AppData\Local\Temp\aep.exe" | C:\Users\admin\AppData\Local\Temp\aep.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
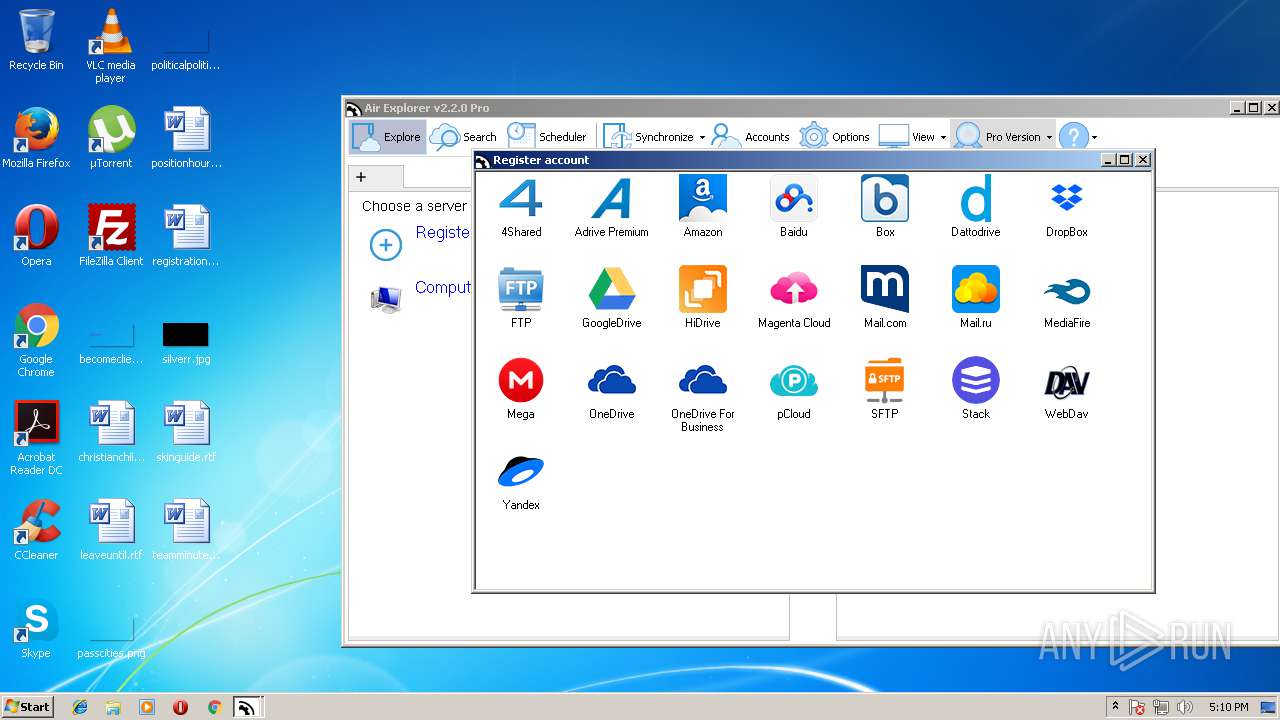
| 2788 | "C:\temp\airexplorerportable.exe" | C:\temp\airexplorerportable.exe | aep.exe | ||||||||||||
User: admin Company: jooseng.blog.163.com Integrity Level: MEDIUM Description: AirExplorer Portable Launcher Exit code: 0 Version: 2.2.0.0 Modules
| |||||||||||||||
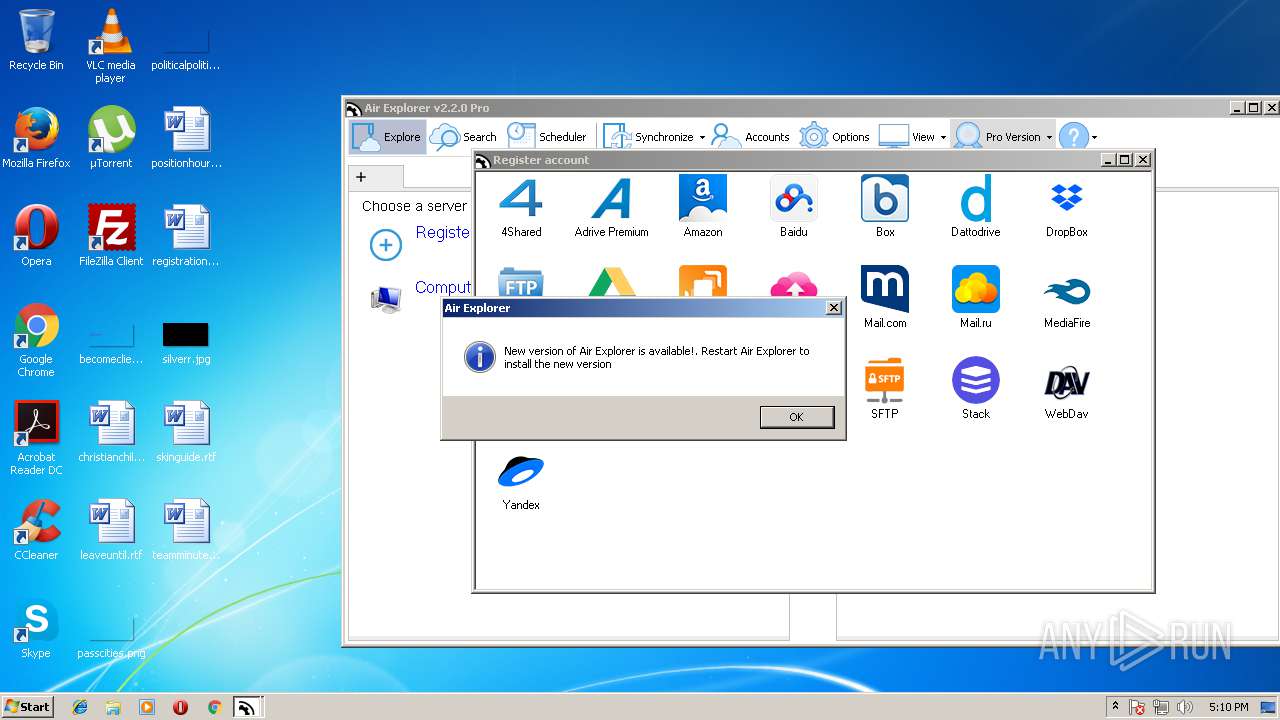
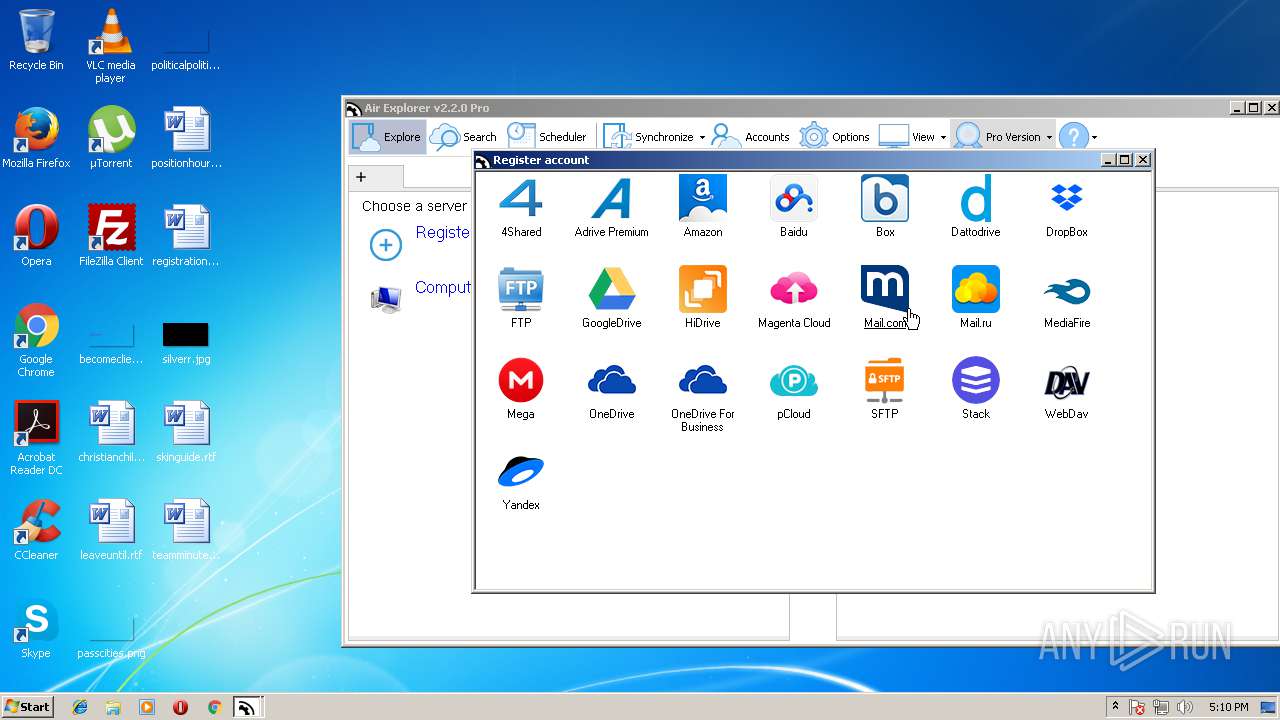
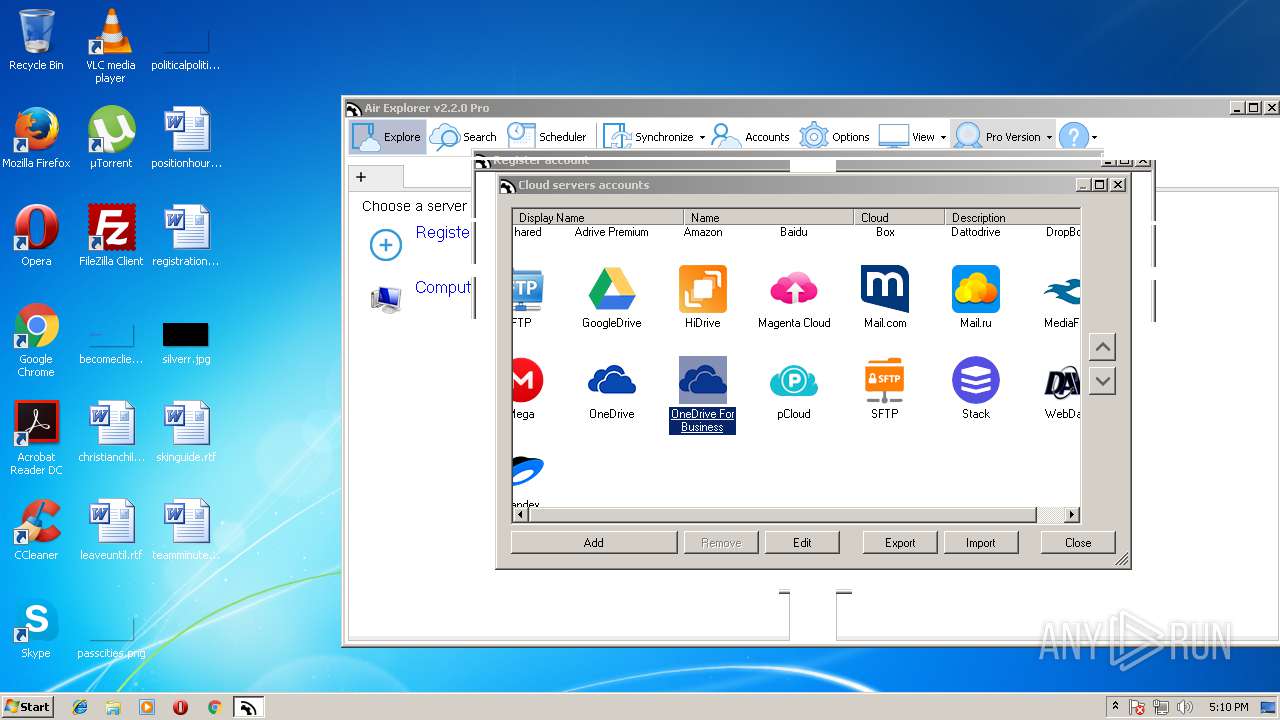
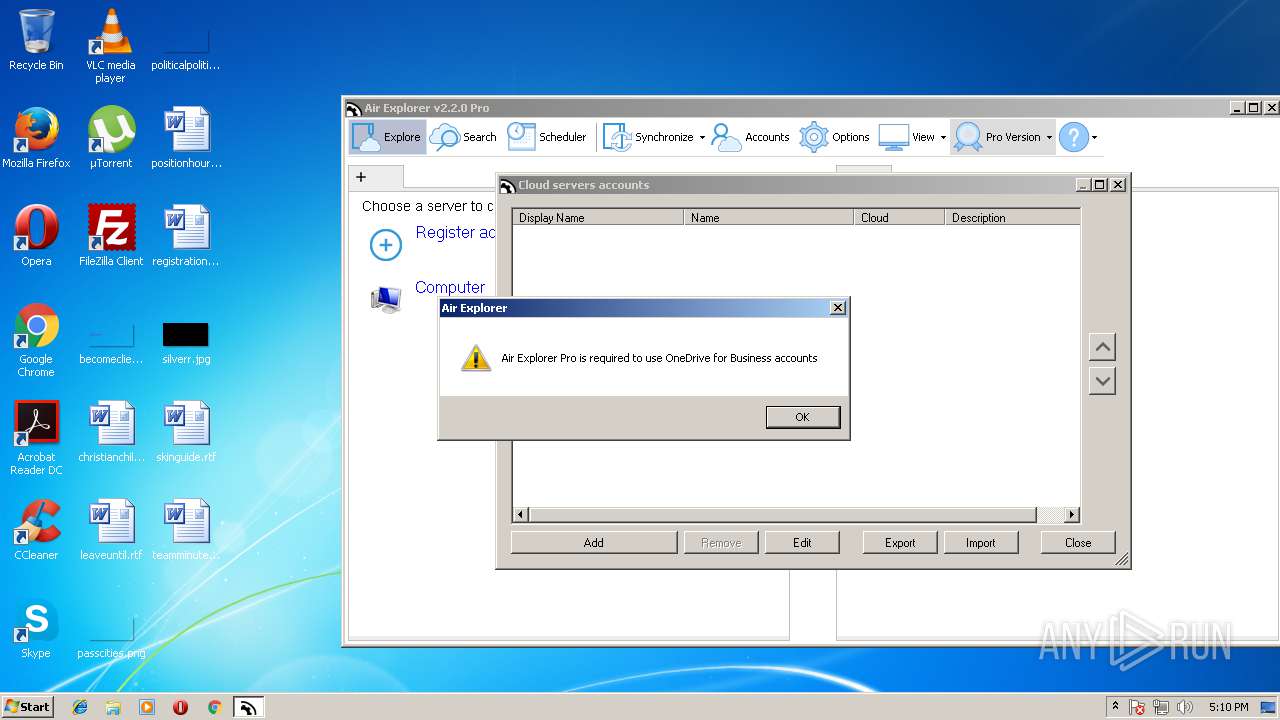
| 3452 | C:\temp\App\ProgramFiles\AirExplorer.exe | C:\temp\App\ProgramFiles\AirExplorer.exe | airexplorerportable.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Air Explorer Exit code: 0 Version: 2.2.0.0 Modules
| |||||||||||||||
Total events
399
Read events
357
Write events
42
Delete events
0
Modification events
| (PID) Process: | (932) aep.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (932) aep.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
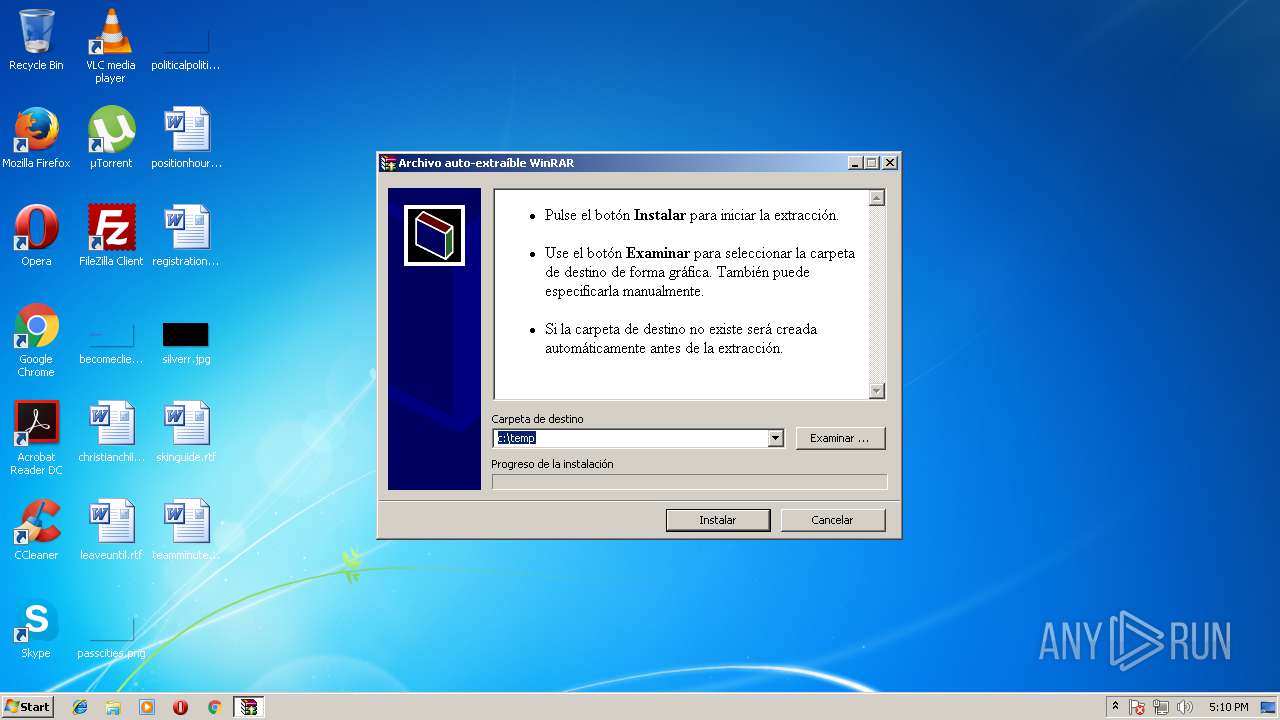
| (PID) Process: | (932) aep.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR SFX |
| Operation: | write | Name: | c%%temp |
Value: c:\temp | |||
| (PID) Process: | (2788) airexplorerportable.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2788) airexplorerportable.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2788) airexplorerportable.exe | Key: | HKEY_CURRENT_USER\Software\PortableAppC\Keys\HKCU\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | AcroRd32.exe |
Value: 8888 | |||
| (PID) Process: | (3452) AirExplorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AirExplorer_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3452) AirExplorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AirExplorer_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3452) AirExplorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AirExplorer_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3452) AirExplorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AirExplorer_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
30
Suspicious files
2
Text files
74
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 932 | aep.exe | C:\temp\App\ProgramFiles\AirExplorer.exe | executable | |
MD5:— | SHA256:— | |||
| 932 | aep.exe | C:\temp\App\ProgramFiles\CIDSave.reg | text | |
MD5:— | SHA256:— | |||
| 932 | aep.exe | C:\temp\App\AppInfo\appicon_128.png | image | |
MD5:FD5F0A923327BB98AA8075A61AE0B76F | SHA256:CD7225FF7FF87DA654A034CD2309A556DFEB63EB1789A1E13A124043AB658515 | |||
| 932 | aep.exe | C:\temp\App\ProgramFiles\AirExplorerCmd.exe | executable | |
MD5:— | SHA256:— | |||
| 932 | aep.exe | C:\temp\App\AppInfo\appicon.ico | image | |
MD5:B47205303089826D4D96C6CA9D055BE6 | SHA256:9C7B12675D42899E2422E6751875604503BFA7C0E4C53AA0F120A44B3373B939 | |||
| 932 | aep.exe | C:\temp\App\ProgramFiles\Language\airexplorer_bg-BG.xml | xml | |
MD5:— | SHA256:— | |||
| 932 | aep.exe | C:\temp\App\ProgramFiles\Language\airexplorer_ar-jo.xml | xml | |
MD5:— | SHA256:— | |||
| 932 | aep.exe | C:\temp\App\ProgramFiles\KRBTabControl.dll | executable | |
MD5:— | SHA256:— | |||
| 932 | aep.exe | C:\temp\App\AppInfo\appinfo.ini | ini | |
MD5:— | SHA256:— | |||
| 932 | aep.exe | C:\temp\App\ProgramFiles\Language\airexplorer_ca-ES.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
14
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3452 | AirExplorer.exe | GET | 304 | 2.16.186.56:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
3452 | AirExplorer.exe | GET | 200 | 192.35.177.64:80 | http://apps.identrust.com/roots/dstrootcax3.p7c | US | cat | 893 b | shared |
3452 | AirExplorer.exe | GET | 301 | 164.132.99.166:80 | http://www.airexplorer.net/checkversion/?ad=1&sv=1&p=1&v=2.2.0&l=en-US&s=AirExplorer | FR | html | 193 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3452 | AirExplorer.exe | 164.132.99.166:80 | www.airexplorer.net | OVH SAS | FR | malicious |
3452 | AirExplorer.exe | 164.132.99.166:443 | www.airexplorer.net | OVH SAS | FR | malicious |
3452 | AirExplorer.exe | 192.35.177.64:80 | apps.identrust.com | IdenTrust | US | malicious |
3452 | AirExplorer.exe | 2.16.186.56:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
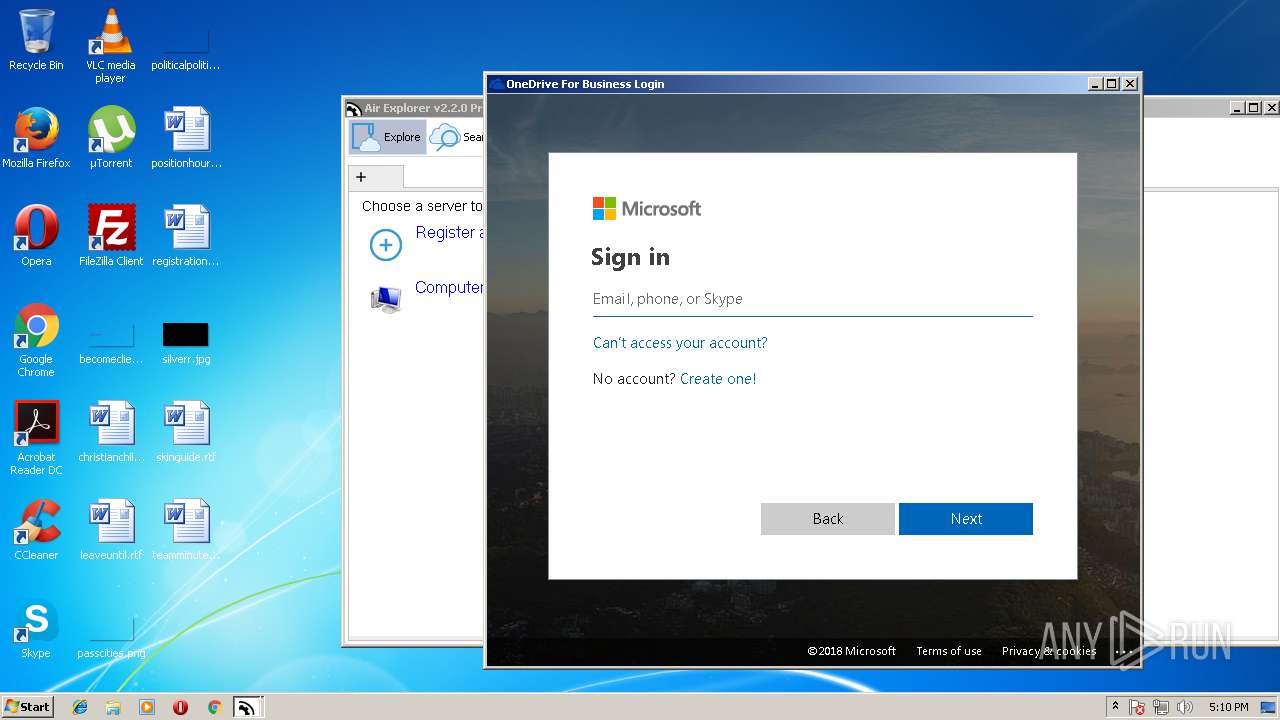
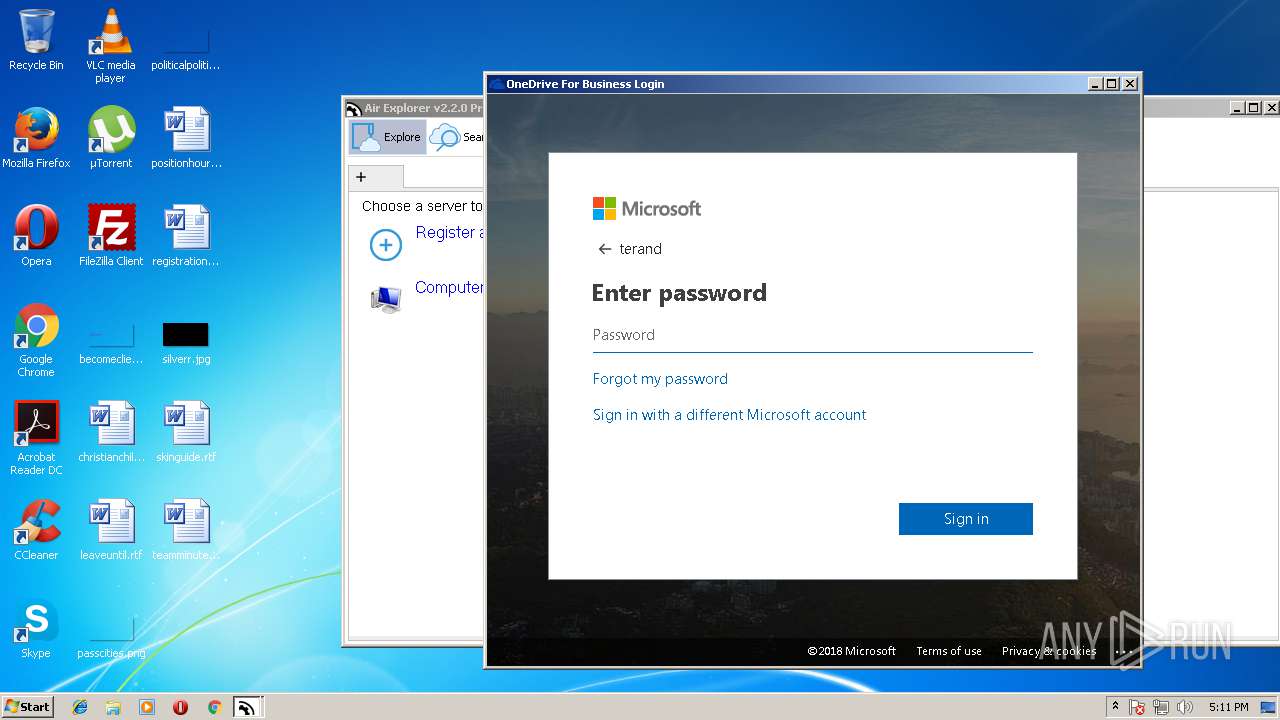
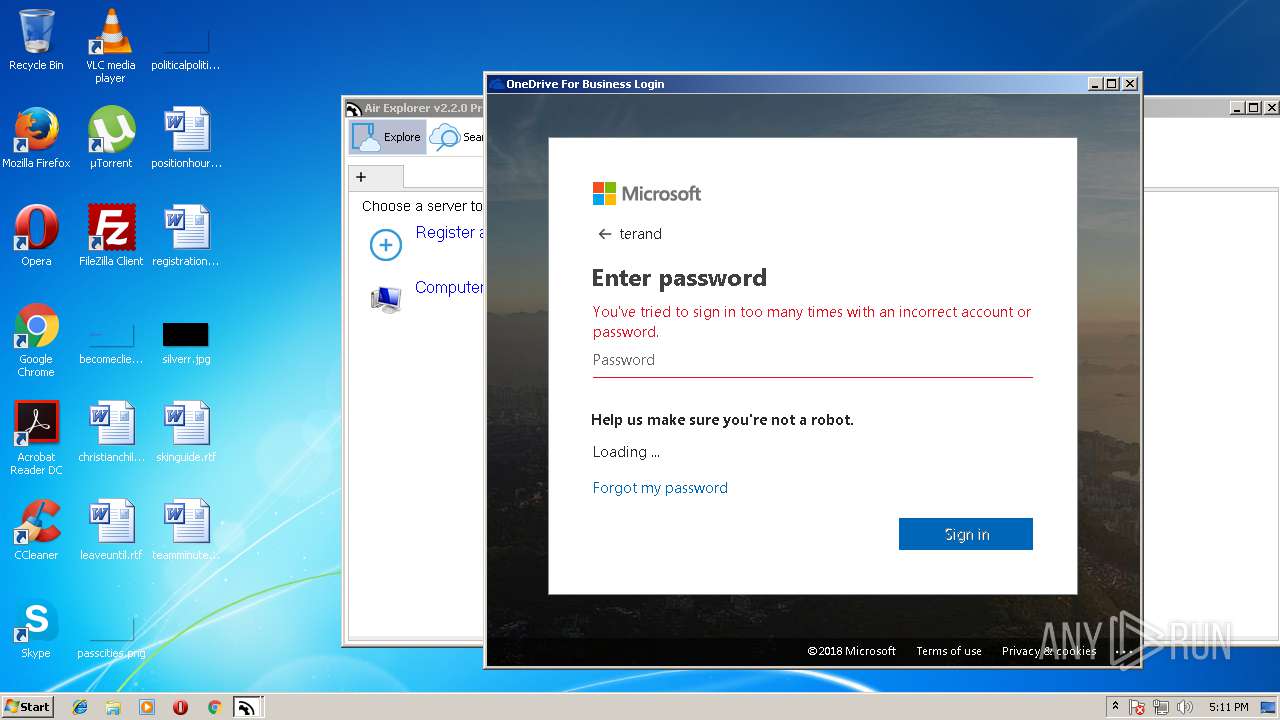
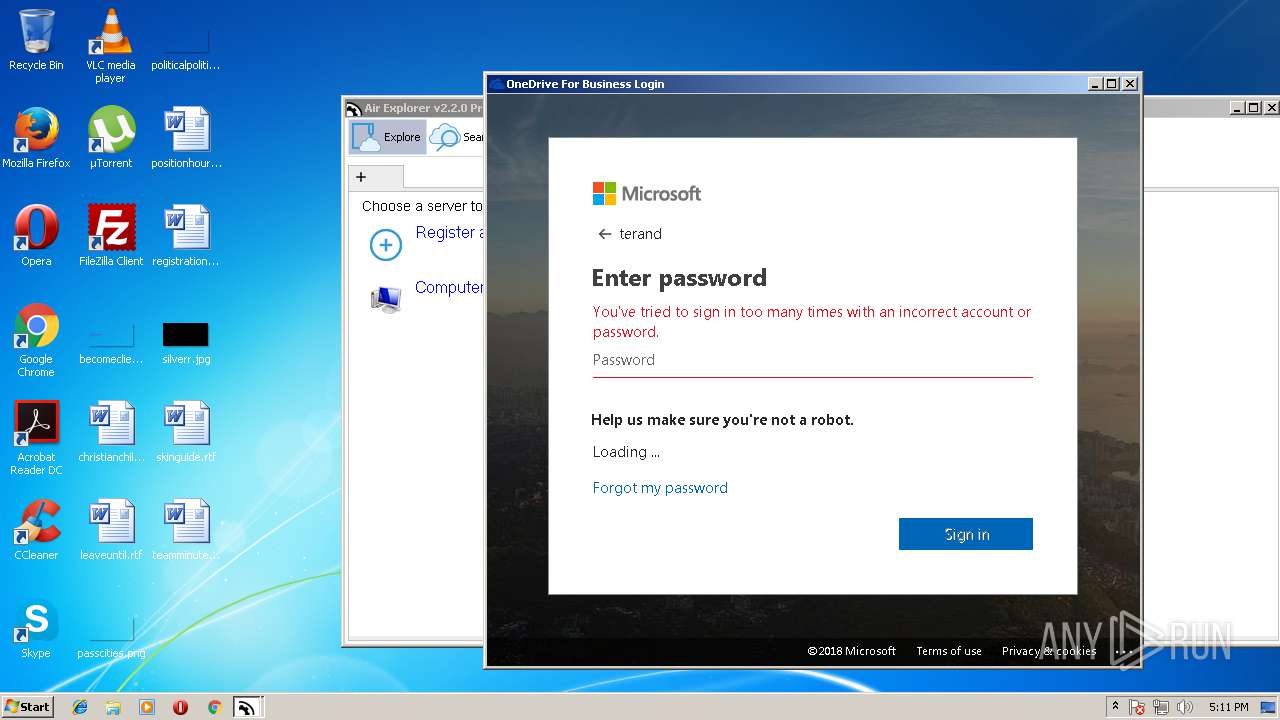
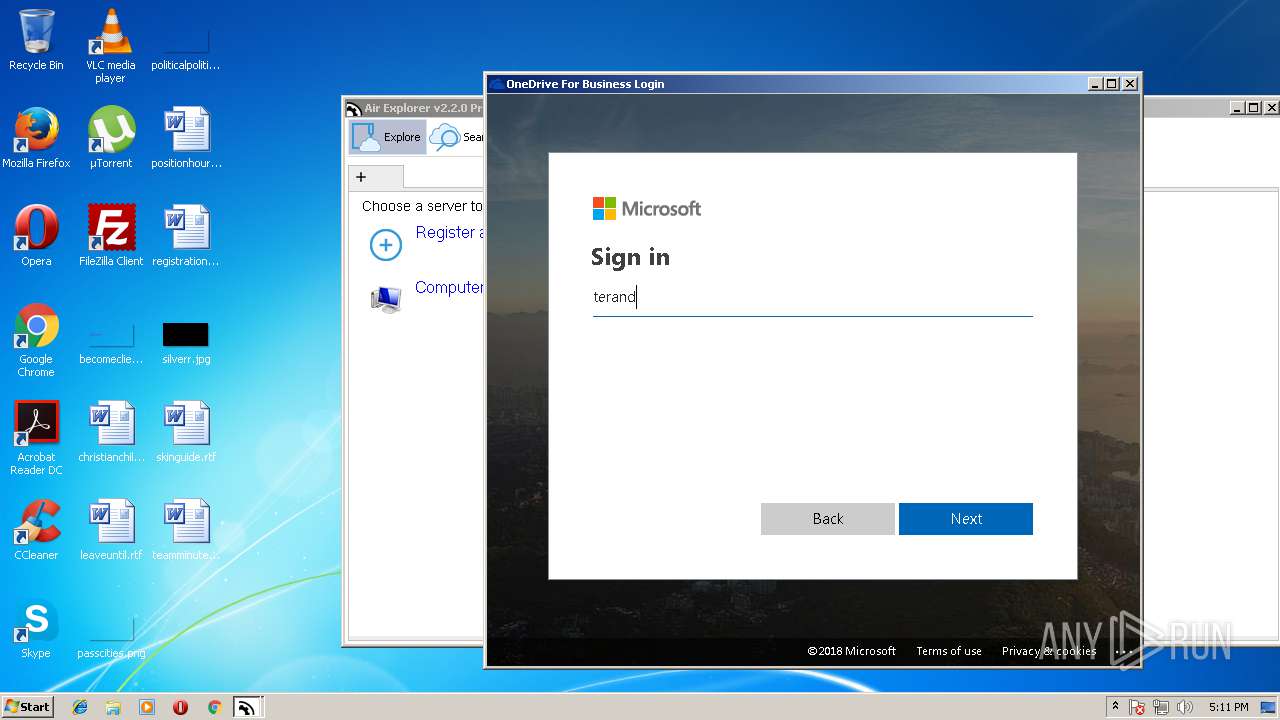
3452 | AirExplorer.exe | 104.41.216.16:443 | login.microsoftonline.com | Microsoft Corporation | IE | whitelisted |
3452 | AirExplorer.exe | 104.111.246.18:443 | secure.aadcdn.microsoftonline-p.com | Akamai International B.V. | NL | whitelisted |
3452 | AirExplorer.exe | 131.253.61.100:443 | login.live.com | Microsoft Corporation | US | whitelisted |
3452 | AirExplorer.exe | 40.71.94.214:443 | client.hip.live.com | Microsoft Corporation | US | whitelisted |
3452 | AirExplorer.exe | 104.111.245.227:443 | auth.gfx.ms | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.airexplorer.net |
| malicious |
apps.identrust.com |
| shared |
www.download.windowsupdate.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
secure.aadcdn.microsoftonline-p.com |
| whitelisted |
login.live.com |
| whitelisted |
auth.gfx.ms |
| whitelisted |
client.hip.live.com |
| whitelisted |