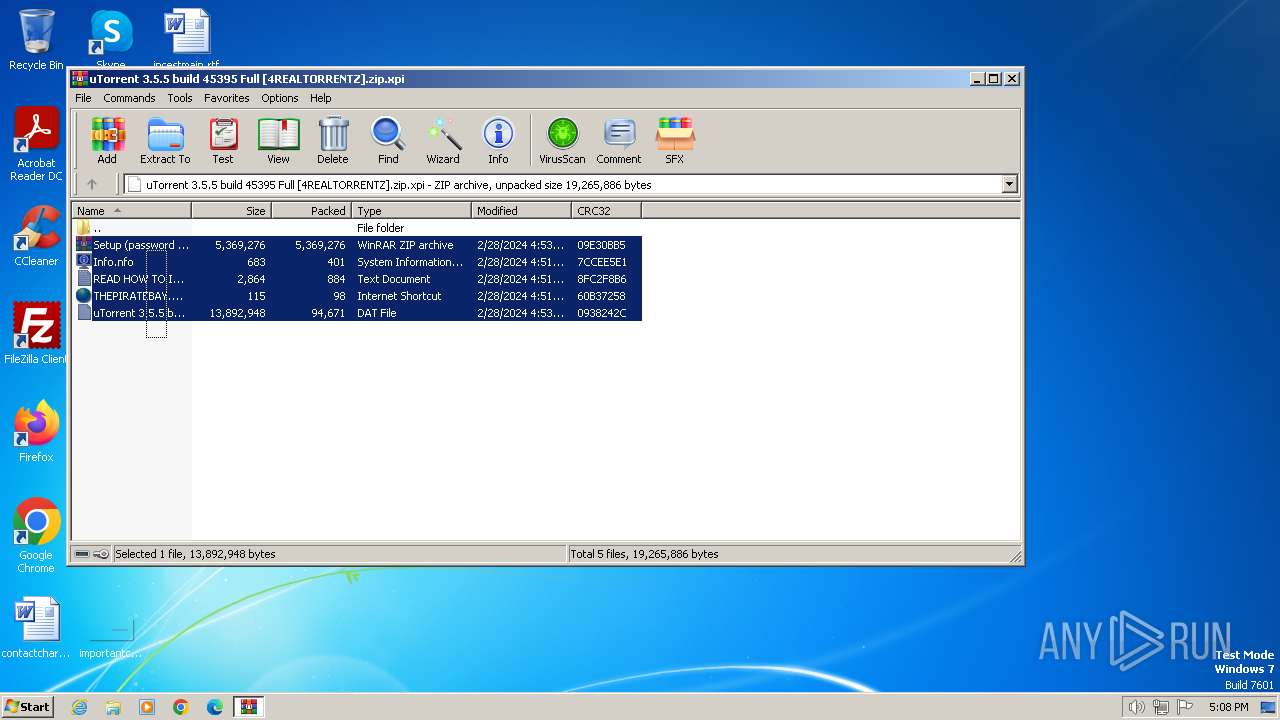
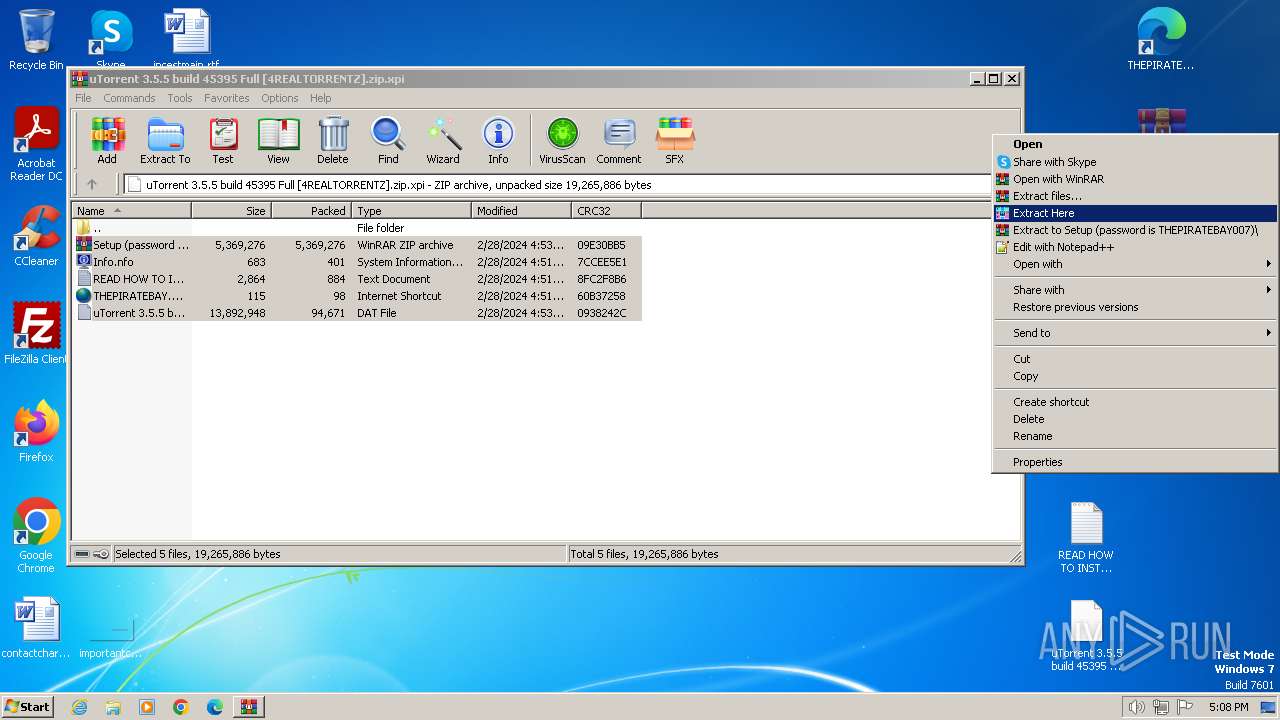
| File name: | uTorrent 3.5.5 build 45395 Full [4REALTORRENTZ].zip |
| Full analysis: | https://app.any.run/tasks/6948aebd-2680-42a5-9588-1c930821117b |
| Verdict: | Malicious activity |
| Analysis date: | February 28, 2024, 17:07:27 |
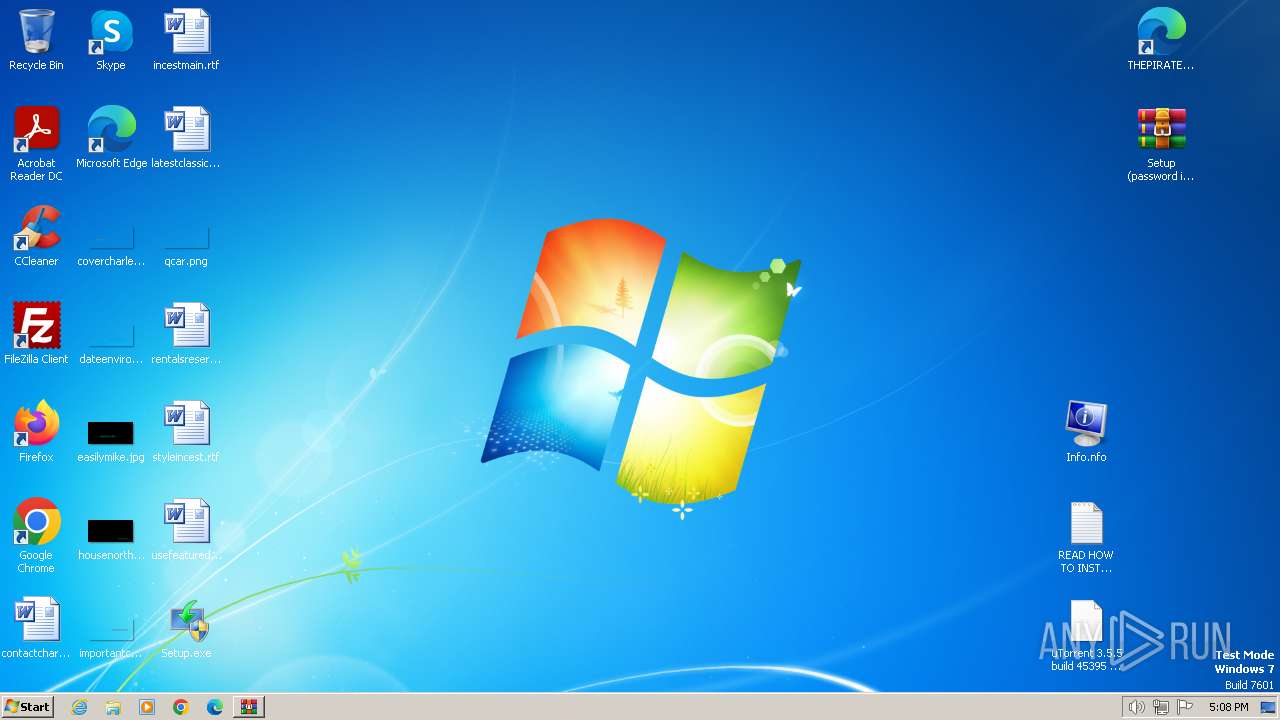
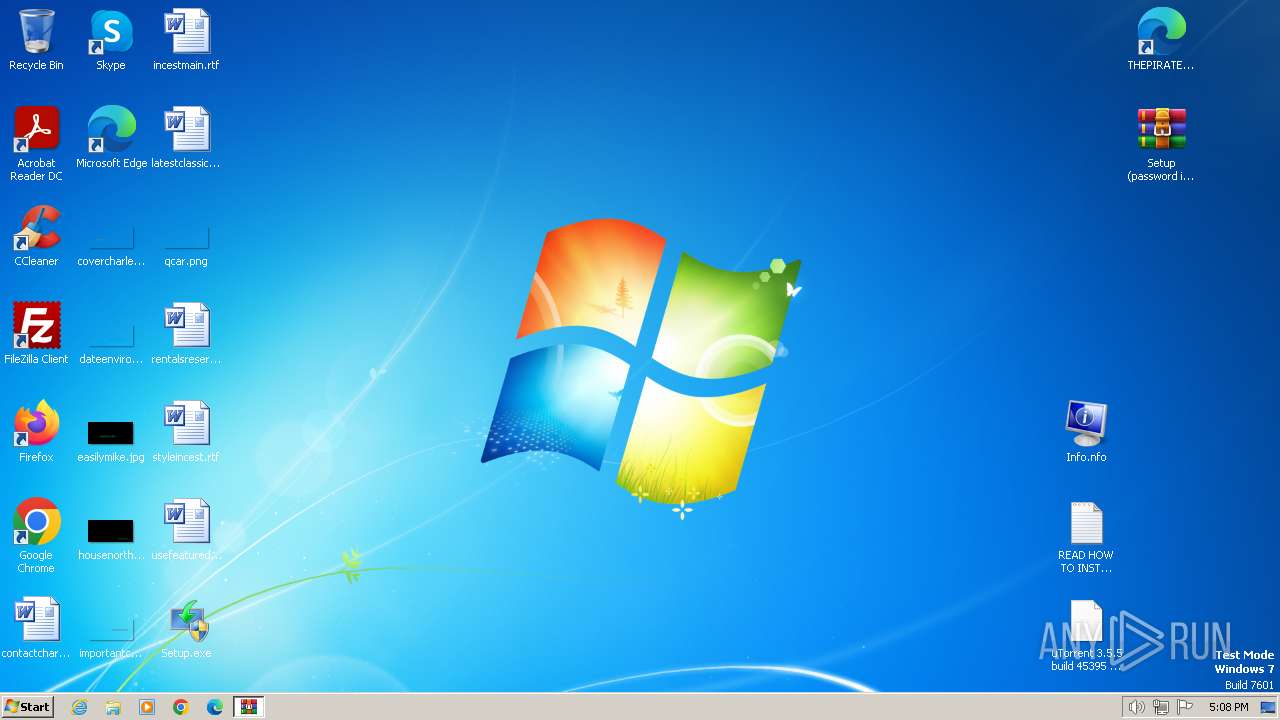
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | F5D938A8D7D7B4ED38A5CCA134516CE4 |
| SHA1: | A96B18D40AE09AB200ADECDD9B43B17D7F378813 |
| SHA256: | FE5F4971527FAC3D4B1C067E8C8A2F6787AADF4248C97CEFA26411B7C129B1C6 |
| SSDEEP: | 98304:sV8DfojEP0spDkhBVTEog5hzVXqQhiY118D8wYLQPXqTrZn5x2dewdJ7IMdpS3gh:HcG6lLaGUS |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- rundll32.exe (PID: 3864)
- Setup.exe (PID: 1560)
Reads security settings of Internet Explorer
- Setup.exe (PID: 1560)
Application launched itself
- Setup.exe (PID: 1888)
Checks for external IP
- Setup.exe (PID: 1560)
INFO
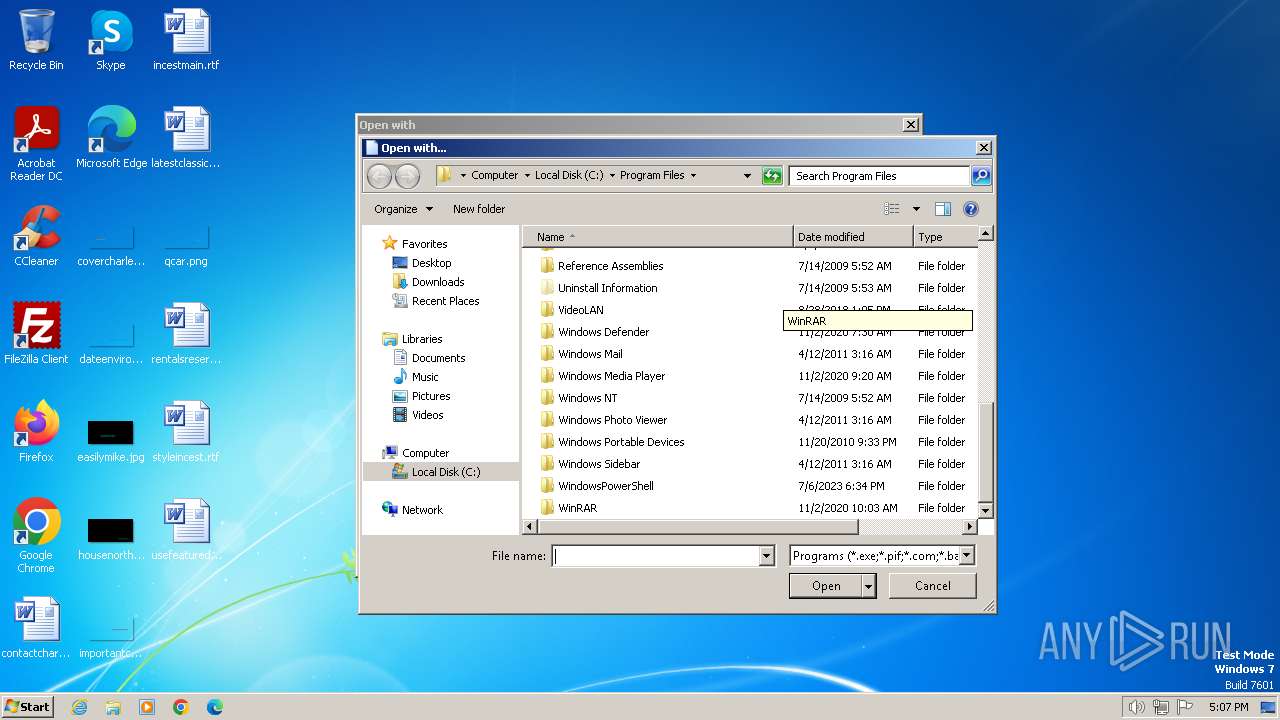
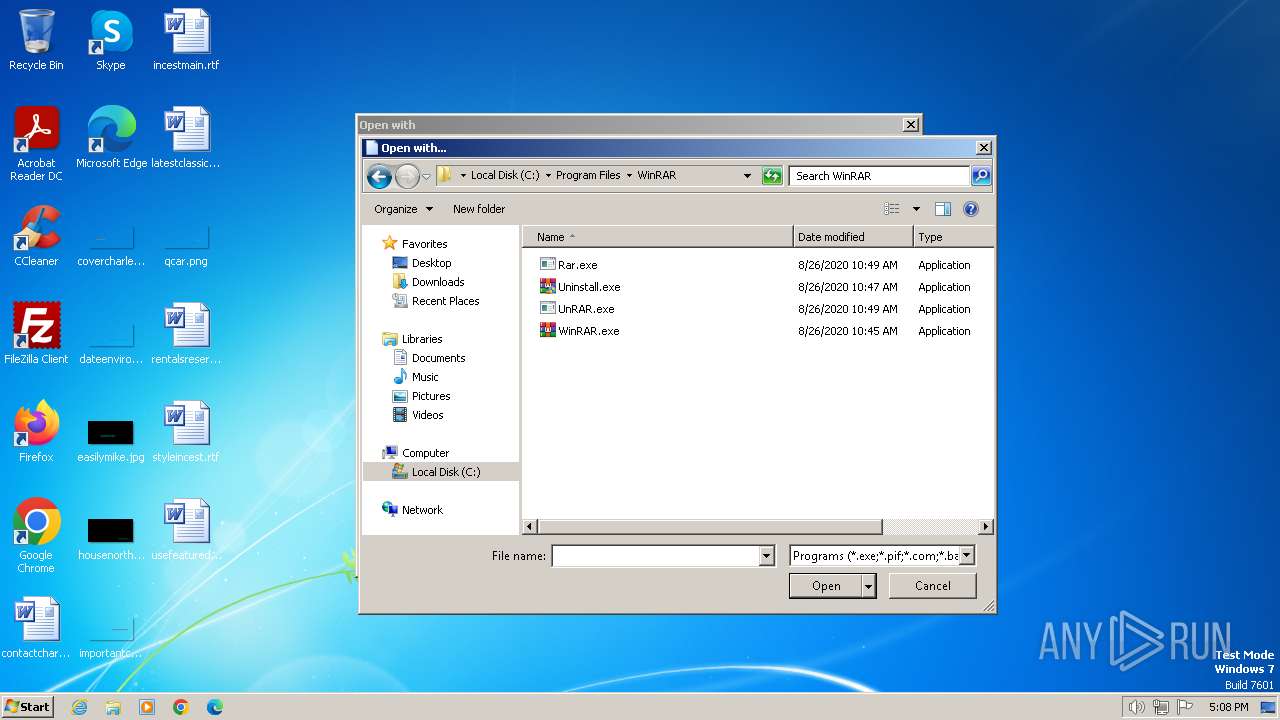
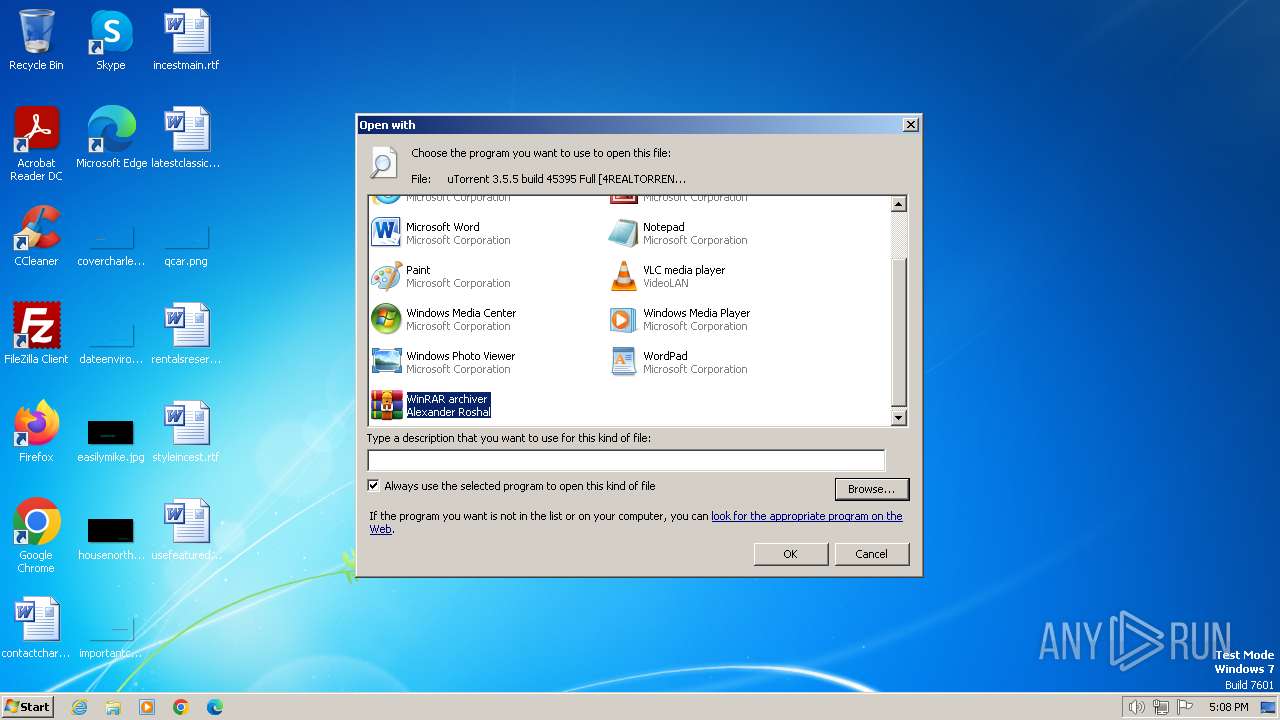
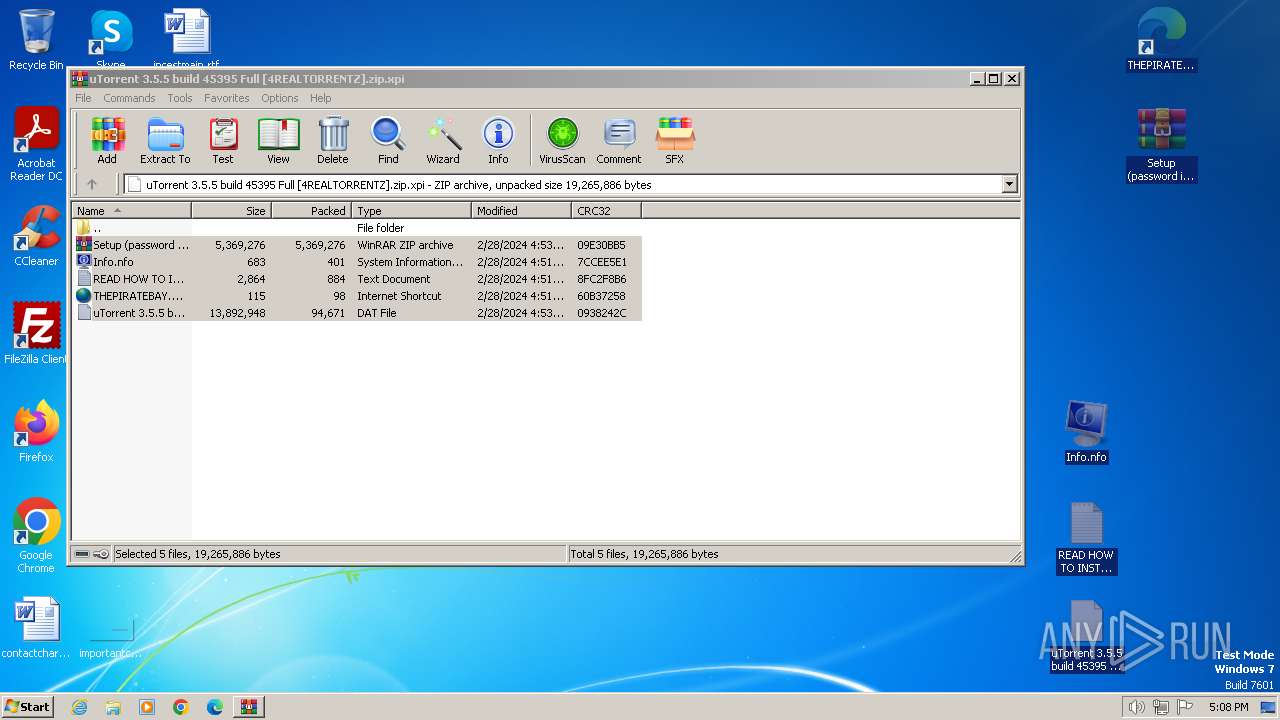
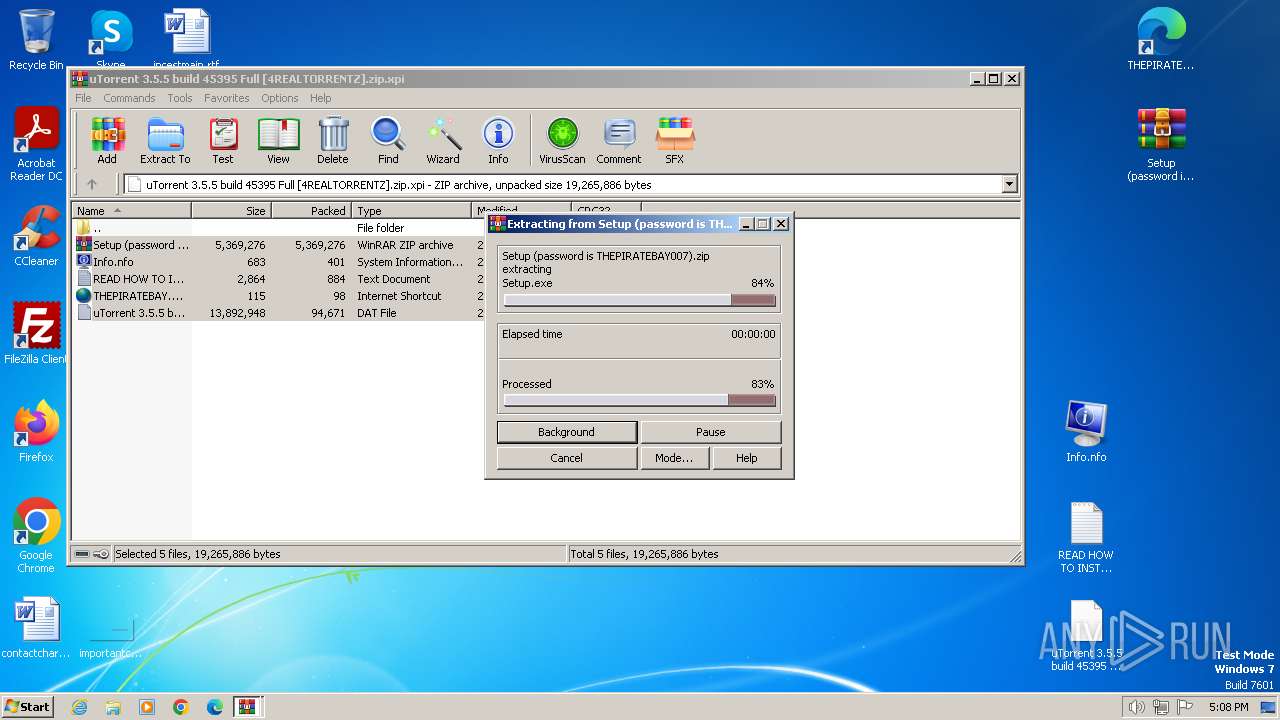
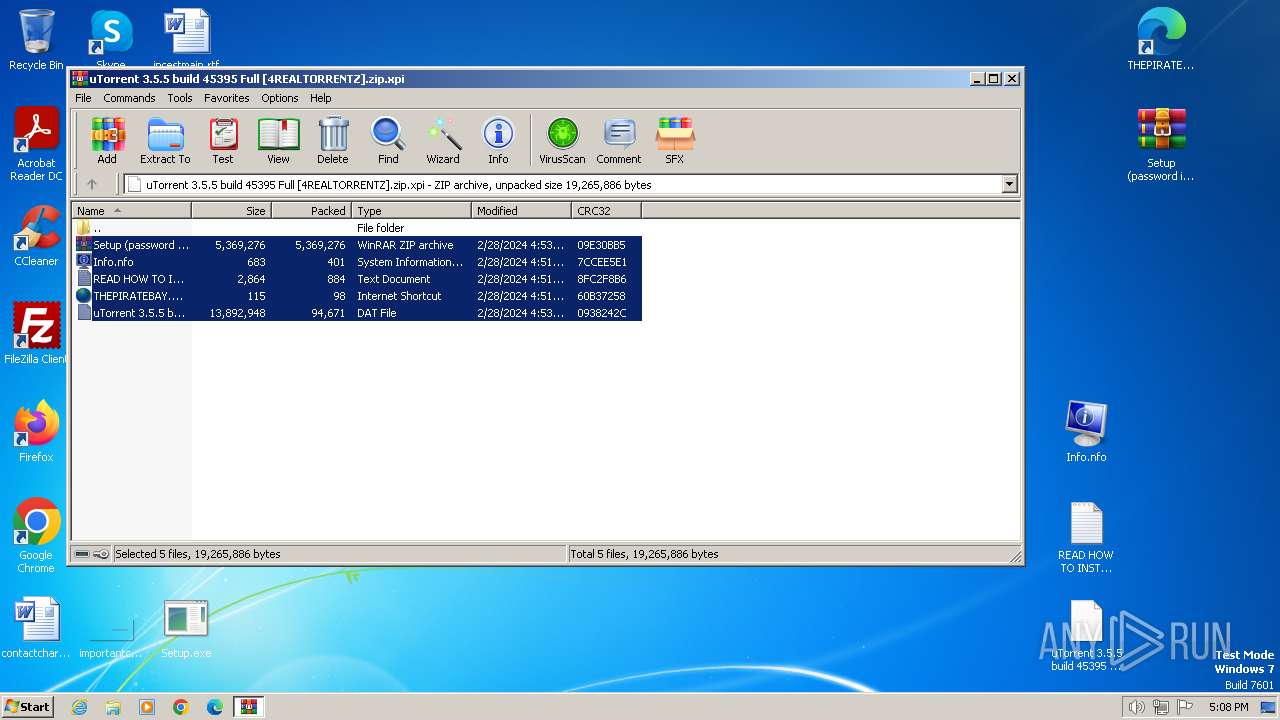
Manual execution by a user
- WinRAR.exe (PID: 1836)
- wmpnscfg.exe (PID: 116)
- Setup.exe (PID: 1824)
- Setup.exe (PID: 1888)
Checks supported languages
- Setup.exe (PID: 1560)
- Setup.exe (PID: 1888)
- wmpnscfg.exe (PID: 116)
Reads the computer name
- wmpnscfg.exe (PID: 116)
- Setup.exe (PID: 1560)
Checks proxy server information
- Setup.exe (PID: 1560)
Reads the machine GUID from the registry
- Setup.exe (PID: 1560)
Creates files in the program directory
- Setup.exe (PID: 1560)
Creates files or folders in the user directory
- Setup.exe (PID: 1560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:02:28 19:53:32 |
| ZipCRC: | 0x09e30bb5 |
| ZipCompressedSize: | 5369276 |
| ZipUncompressedSize: | 5369276 |
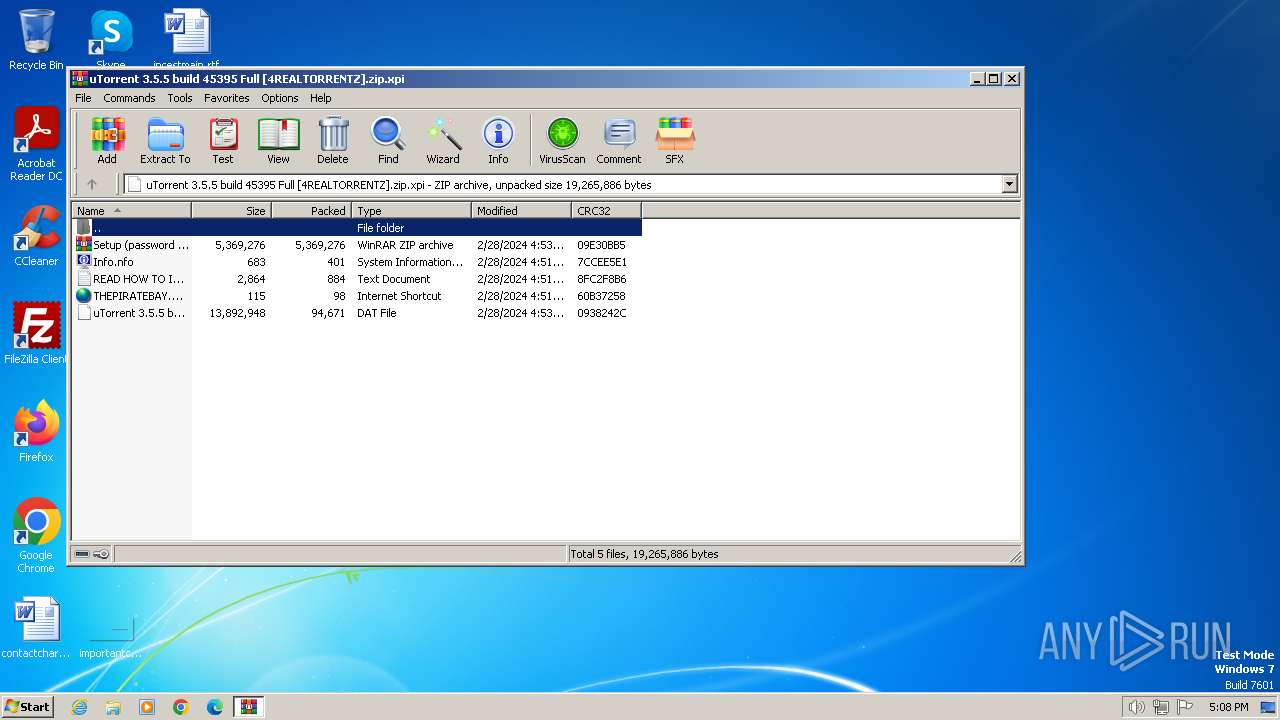
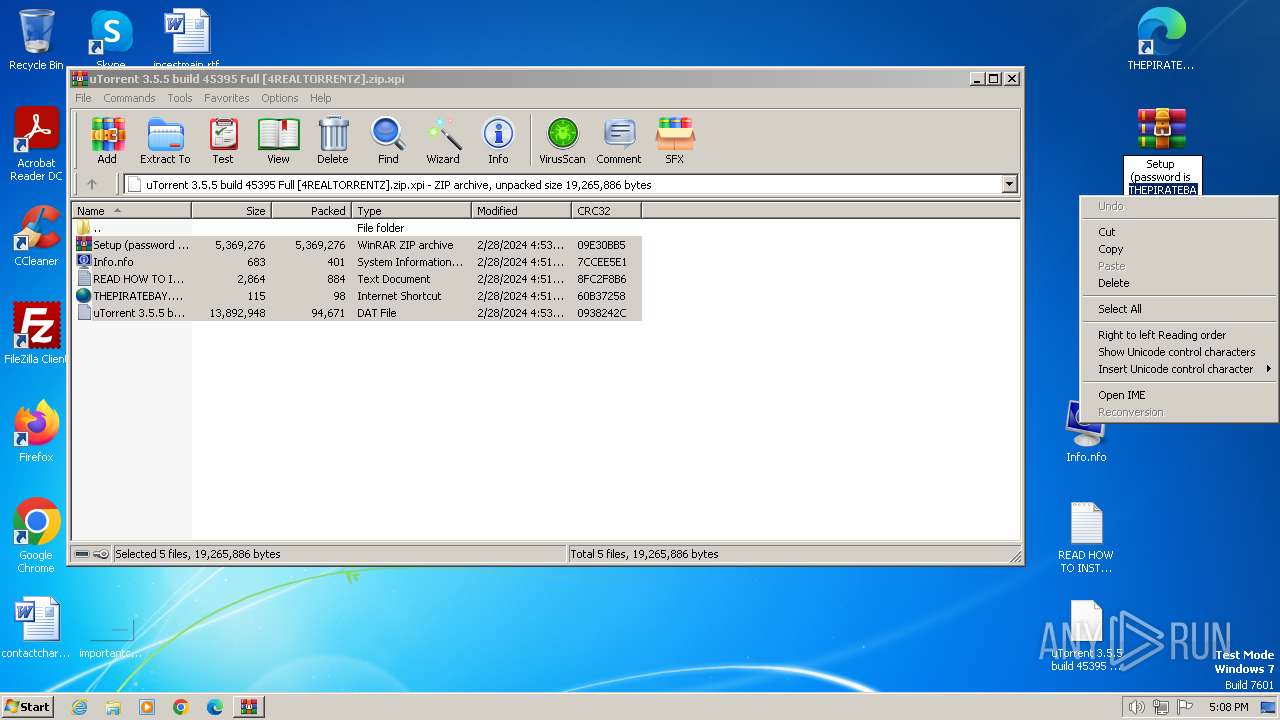
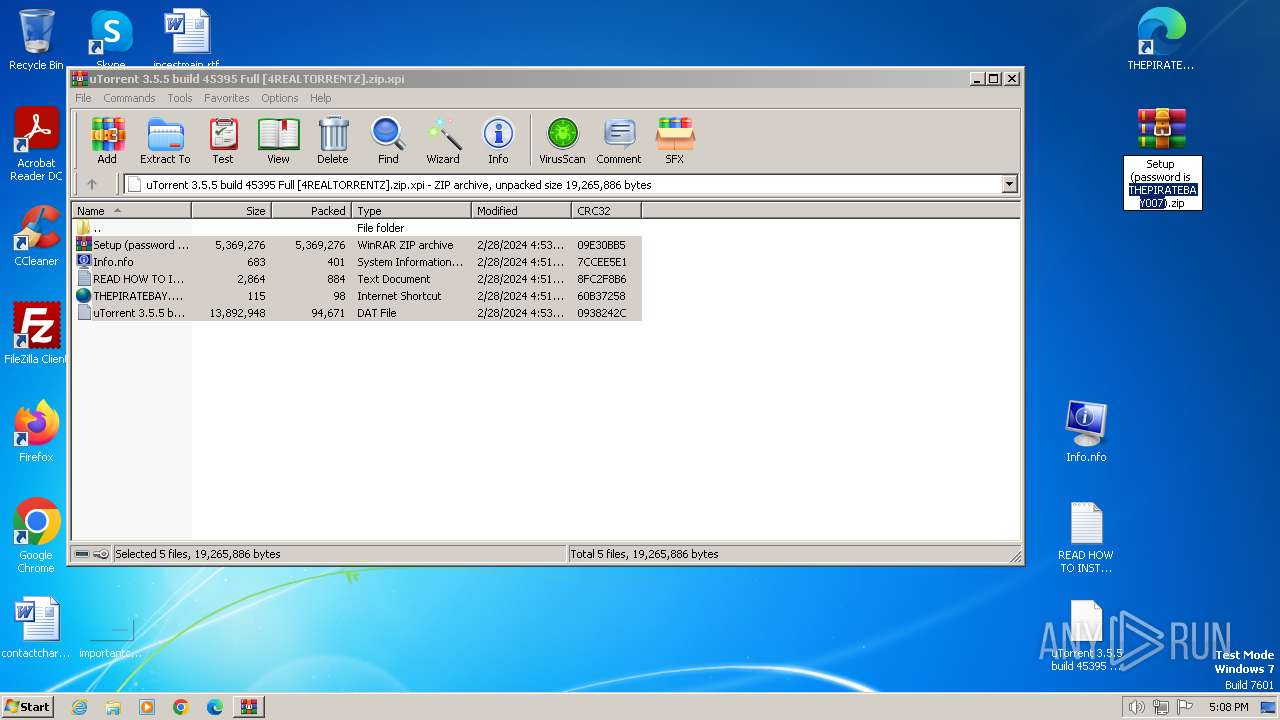
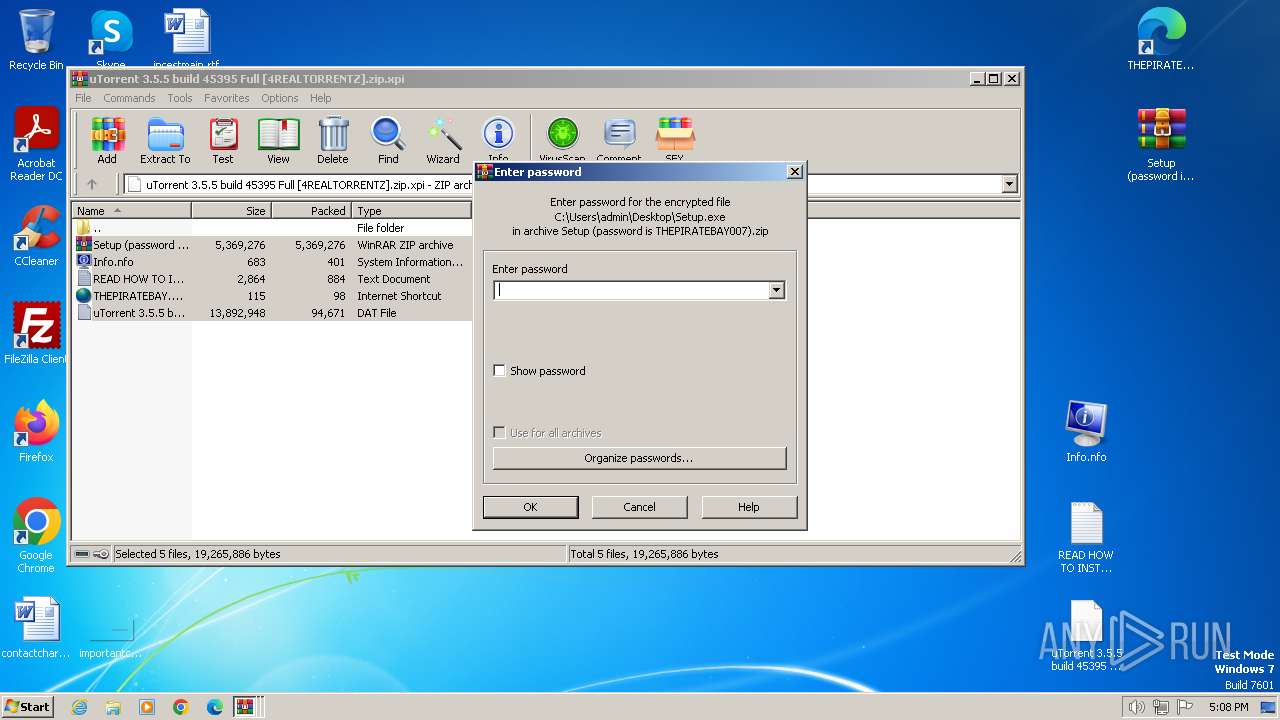
| ZipFileName: | Setup (password is THEPIRATEBAY007).zip |
Total processes
49
Monitored processes
7
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1560 | "C:\Users\admin\Desktop\Setup.exe" | C:\Users\admin\Desktop\Setup.exe | Setup.exe | ||||||||||||
User: admin Company: Ilya Morozov Integrity Level: HIGH Description: Balabolka Exit code: 0 Version: 2.15.0.783 Modules
| |||||||||||||||
| 1776 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\uTorrent 3.5.5 build 45395 Full [4REALTORRENTZ].zip.xpi" | C:\Program Files\WinRAR\WinRAR.exe | — | rundll32.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
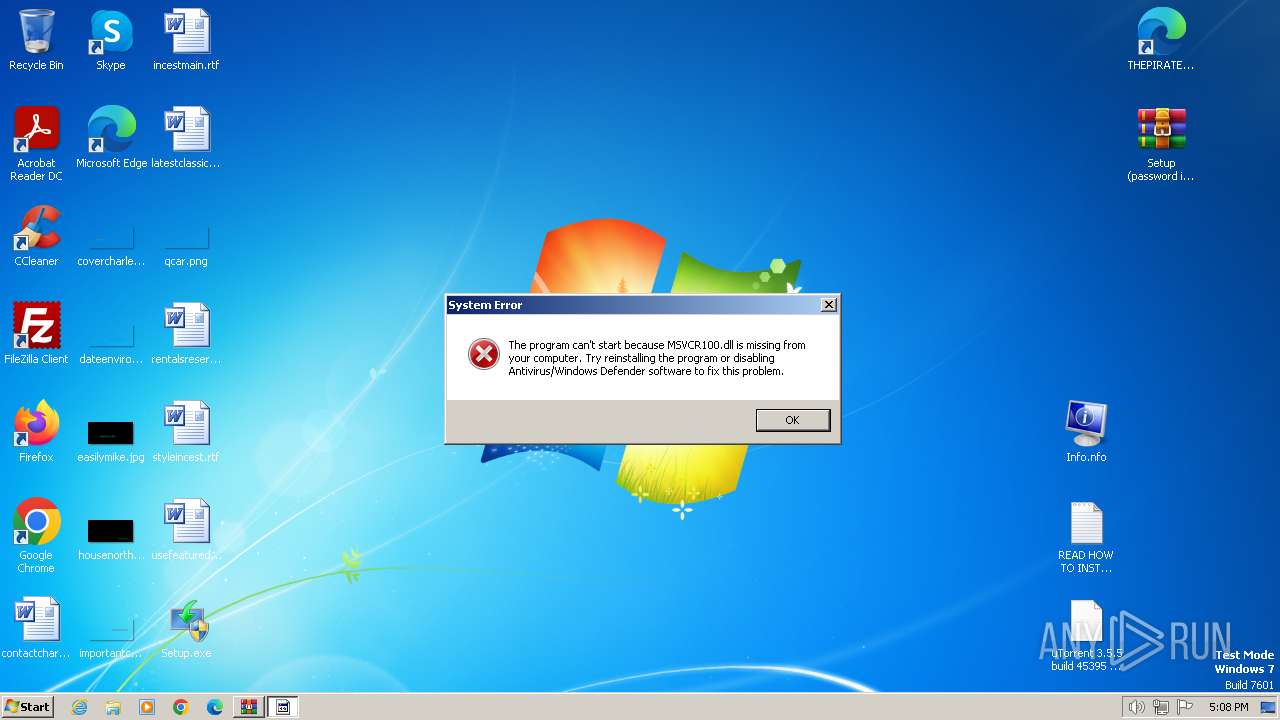
| 1824 | "C:\Users\admin\Desktop\Setup.exe" | C:\Users\admin\Desktop\Setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Ilya Morozov Integrity Level: MEDIUM Description: Balabolka Exit code: 3221226540 Version: 2.15.0.783 Modules
| |||||||||||||||
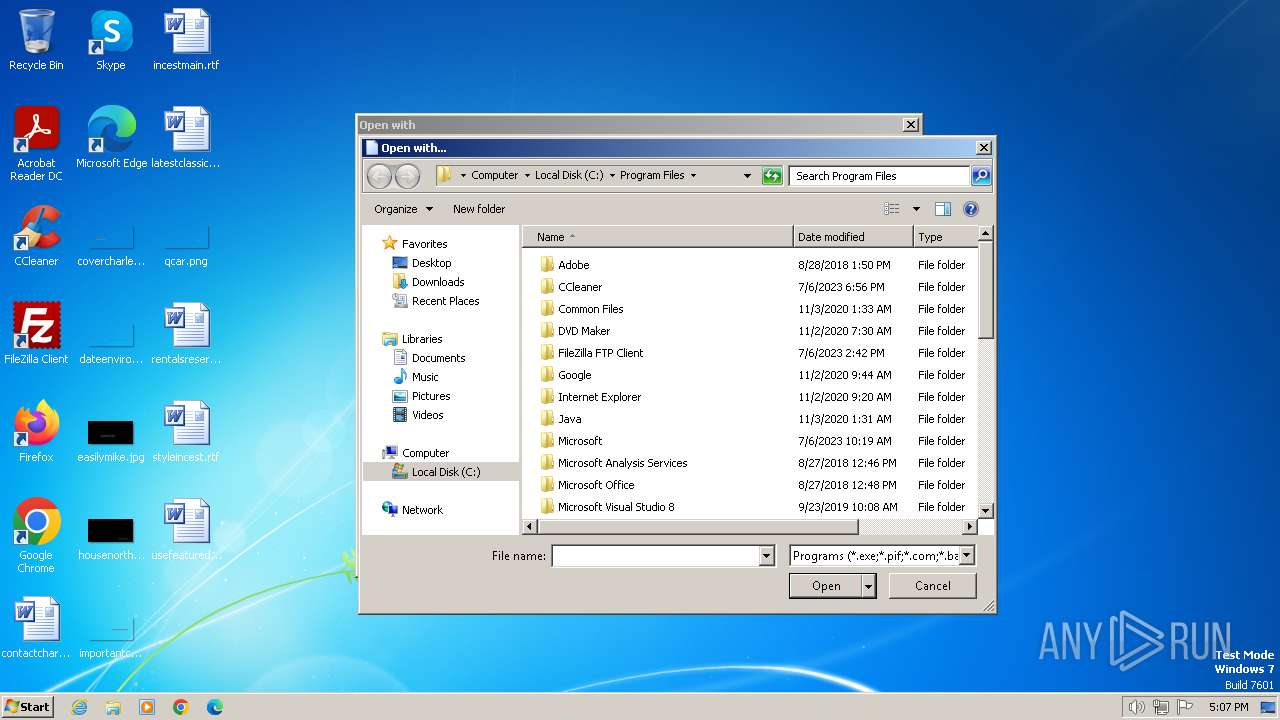
| 1836 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\Setup (password is THEPIRATEBAY007).zip" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1888 | "C:\Users\admin\Desktop\Setup.exe" | C:\Users\admin\Desktop\Setup.exe | explorer.exe | ||||||||||||
User: admin Company: Ilya Morozov Integrity Level: HIGH Description: Balabolka Exit code: 0 Version: 2.15.0.783 Modules
| |||||||||||||||
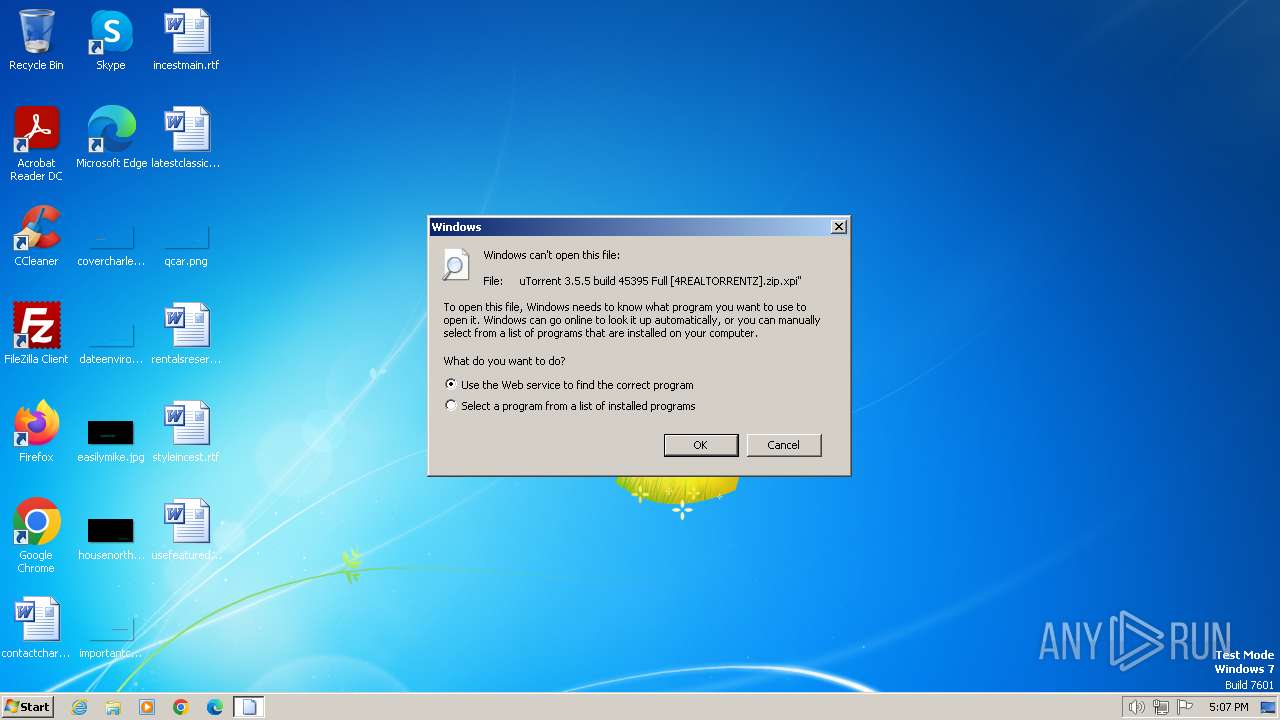
| 3864 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL "C:\Users\admin\AppData\Local\Temp\uTorrent 3.5.5 build 45395 Full [4REALTORRENTZ].zip.xpi" | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
14 587
Read events
14 451
Write events
126
Delete events
10
Modification events
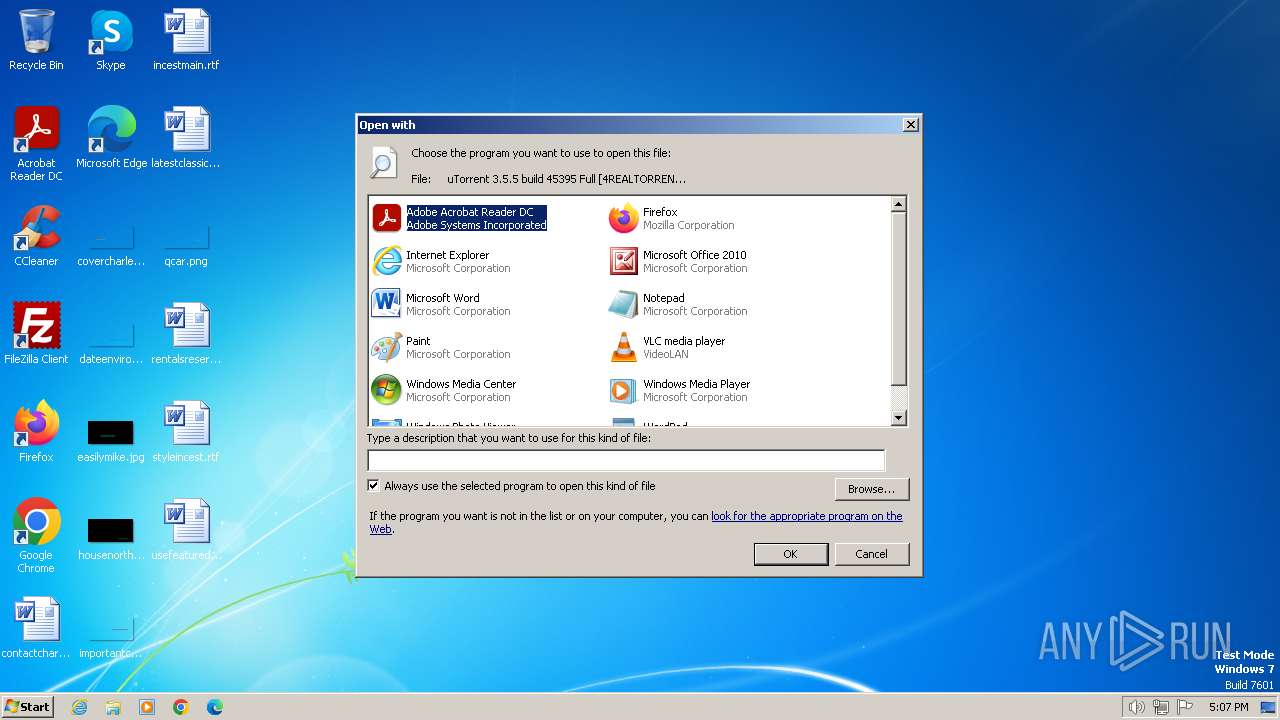
| (PID) Process: | (3864) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (3864) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (3864) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: Firefox | |||
| (PID) Process: | (3864) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Internet Explorer\iexplore.exe |
Value: Internet Explorer | |||
| (PID) Process: | (3864) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (3864) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (3864) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (3864) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (3864) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
| (PID) Process: | (3864) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE |
Value: Microsoft Word | |||
Executable files
0
Suspicious files
3
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1776 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1776.7478\uTorrent 3.5.5 build 45395 Full [4REALTORRENTZ].dat | — | |
MD5:— | SHA256:— | |||
| 1560 | Setup.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\SNH9O3YU.txt | text | |
MD5:D5A0E606D70B156F3C1CE3F535D5D13B | SHA256:111021DA888FF186FD09397D5BD860EAAAF3736E7C0D411D9788DF8499C82A78 | |||
| 1560 | Setup.exe | C:\ProgramData\krosqm.txt | text | |
MD5:D5A0E606D70B156F3C1CE3F535D5D13B | SHA256:111021DA888FF186FD09397D5BD860EAAAF3736E7C0D411D9788DF8499C82A78 | |||
| 1776 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1776.7478\THEPIRATEBAY.ORG.url | url | |
MD5:F0A05245942DF80720C52D58064731EE | SHA256:650CAE89065A9B00E4A7A1F3DFE4FB03A33F5BF96453A71DB1C05B30F5469F66 | |||
| 1776 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1776.7478\Info.nfo | txt | |
MD5:5DB66BBA9EDCFE4C4BD7D8F02A91558E | SHA256:73A437EB96F4D6730569A6517A998488A9F211557B925E32C13A0A4A7EDAF5CD | |||
| 1776 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1776.7478\Setup (password is THEPIRATEBAY007).zip | compressed | |
MD5:5A7B05AF6BE77D411D38E4B9603DE6FB | SHA256:F9FF859F39A9E54D733F9C3DA77A0C42A4F9C6C53ECCCCFD7E874B8B5018EC96 | |||
| 1776 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1776.7478\READ HOW TO INSTALL.txt | text | |
MD5:F0C167FF42EF37405C7E03BBCCB656CD | SHA256:8846AB9D218B3ACC19BBF05CC3442BD27E9D31AC2E36C2B5462ACDF0E6205E4E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
138
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1560 | Setup.exe | GET | 200 | 104.26.12.205:80 | http://api.ipify.org/?format=xml | unknown | text | 15 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1560 | Setup.exe | 104.26.12.205:80 | api.ipify.org | CLOUDFLARENET | US | unknown |
1560 | Setup.exe | 45.93.201.181:80 | — | IT Resheniya LLC | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.ipify.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
1560 | Setup.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup (ipify .org) |
1560 | Setup.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] Received IP address from server as result of HTTP request |