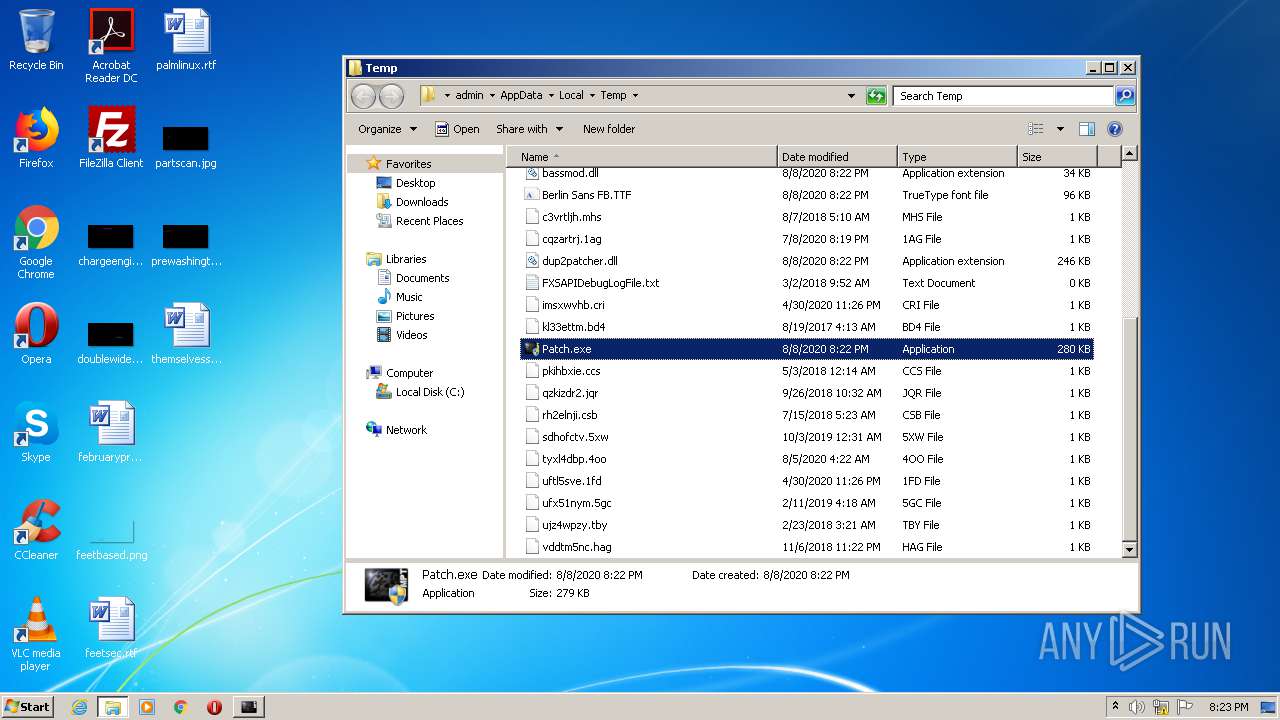
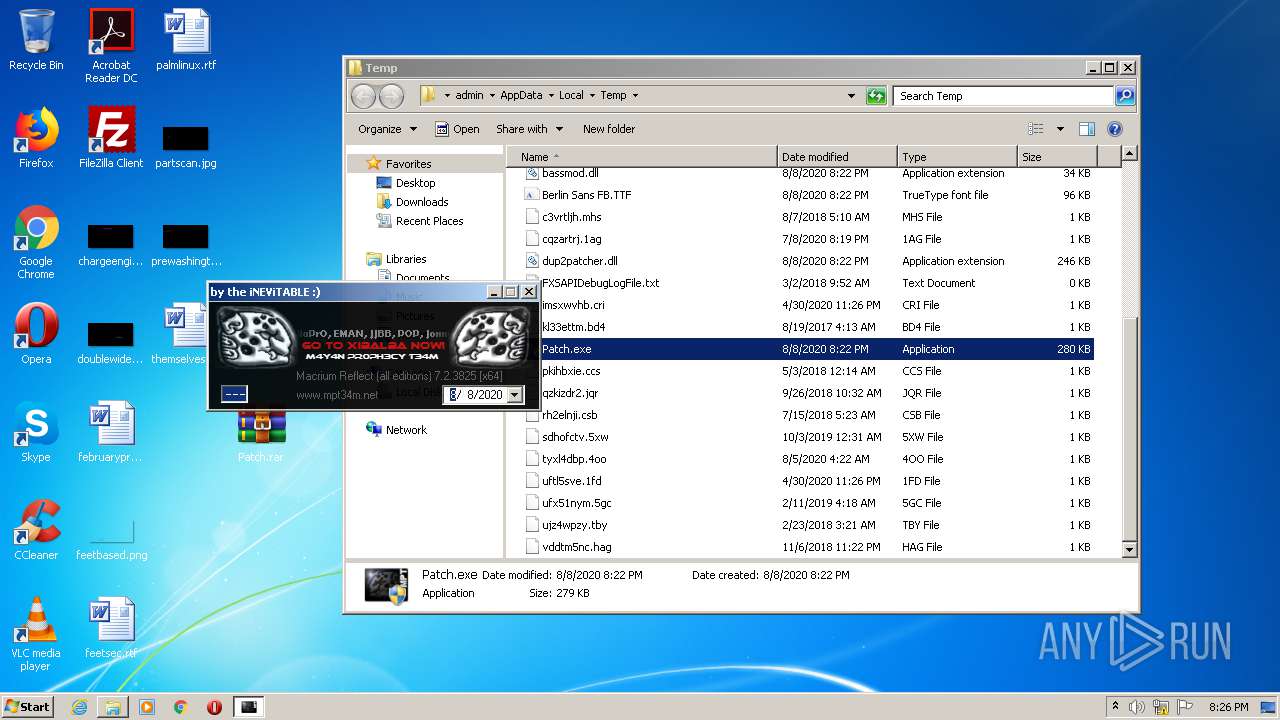
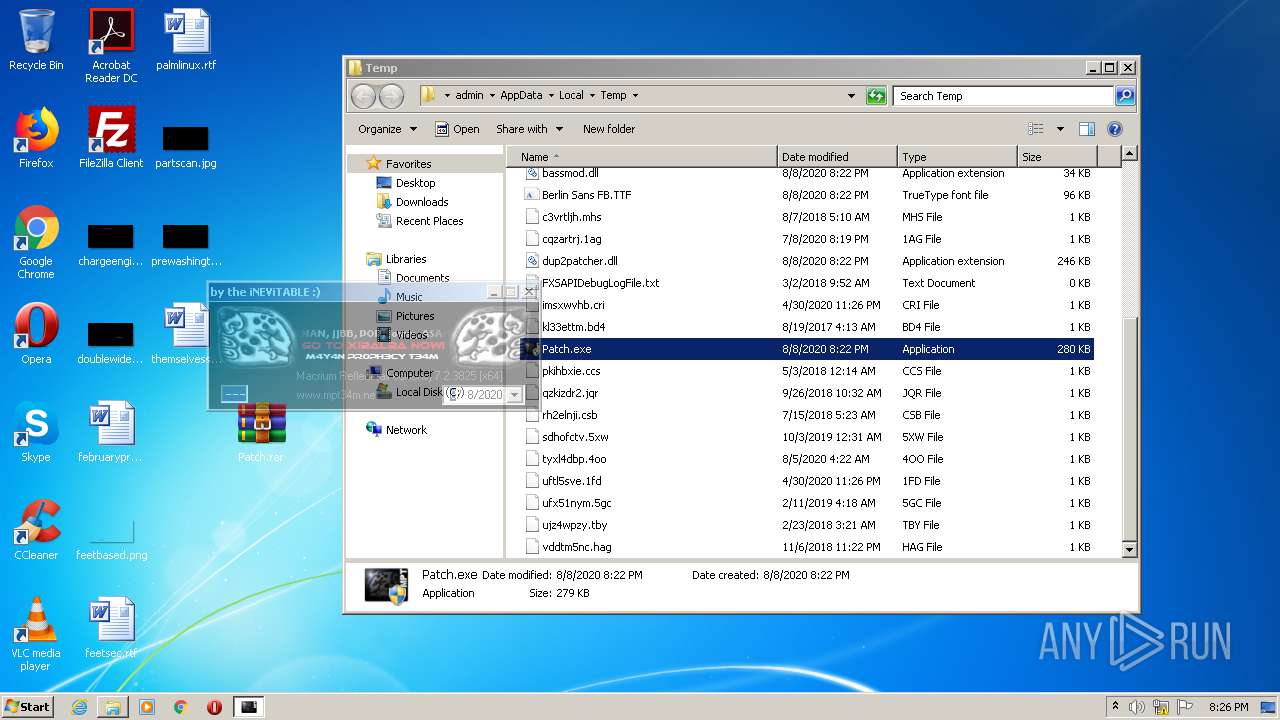
| File name: | Patch.exe |
| Full analysis: | https://app.any.run/tasks/8725ee68-387c-48a5-9b7e-0336111b661d |
| Verdict: | Malicious activity |
| Analysis date: | August 08, 2020, 19:22:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9EC06E71C956C414C278C67F69564CD9 |
| SHA1: | E679492EF90199232DD633F8776C8CD32E78CEF2 |
| SHA256: | FE511ACB318D59F80D753EE9300B4CF937E25C4B1980A07F60B45DC1C3B12C8D |
| SSDEEP: | 6144:3l+1mg8GTMYq+KmpzZ2/5W/Y0JPPuj5MRFWGGB:3Uv8Ge+Pp12/B0VyMRm |
MALICIOUS
Loads dropped or rewritten executable
- Patch.exe (PID: 3812)
- explorer.exe (PID: 352)
Starts NET.EXE for service management
- cmd.exe (PID: 2544)
- cmd.exe (PID: 3260)
SUSPICIOUS
Executable content was dropped or overwritten
- Patch.exe (PID: 3812)
- explorer.exe (PID: 352)
Starts CMD.EXE for commands execution
- Patch.exe (PID: 3812)
INFO
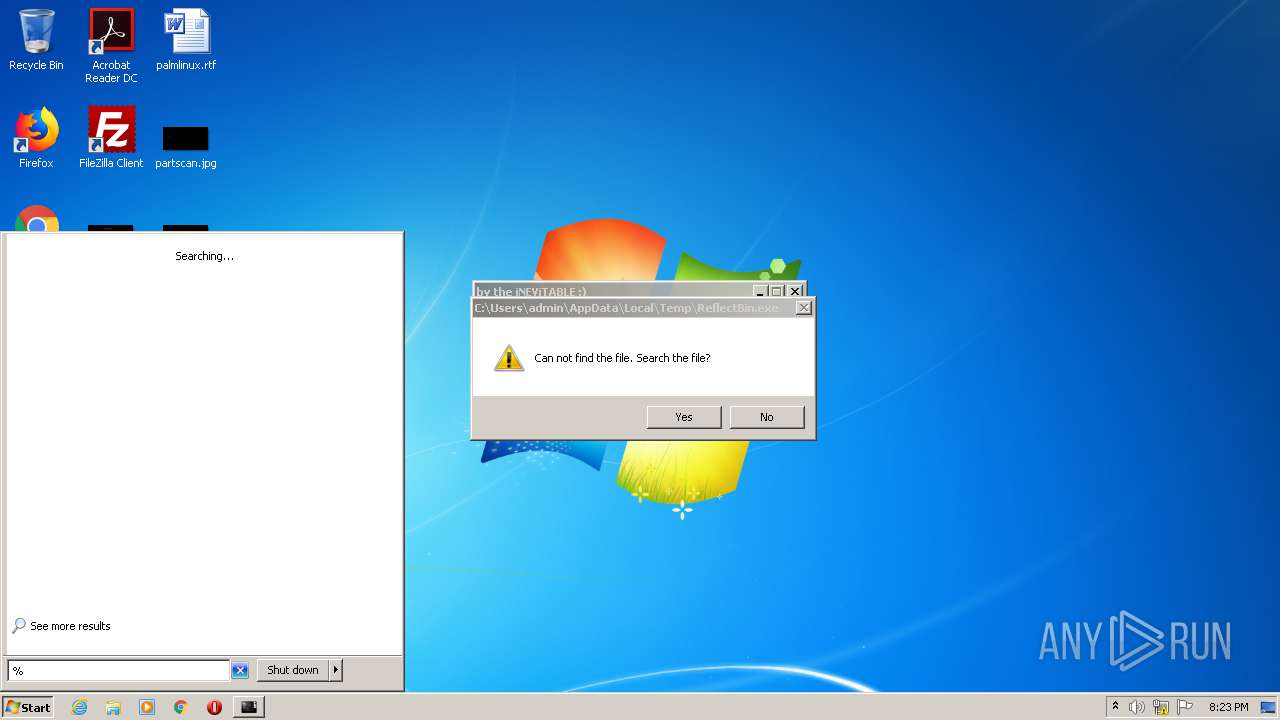
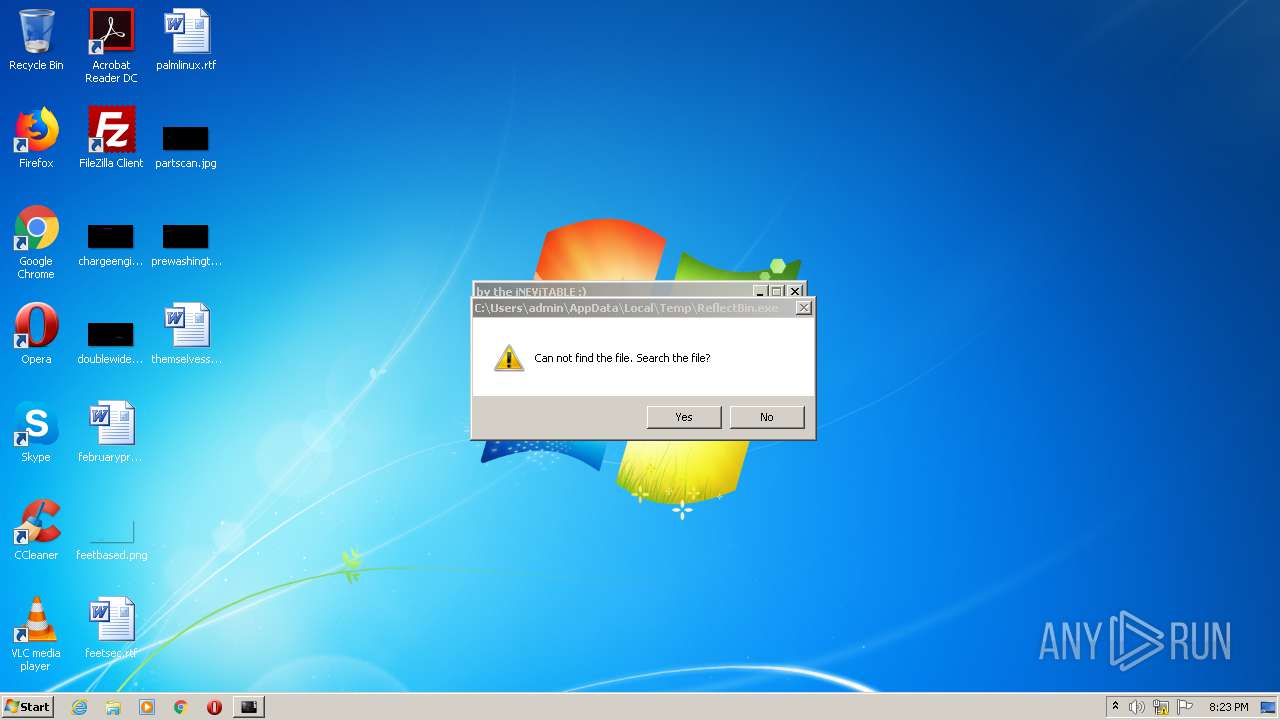
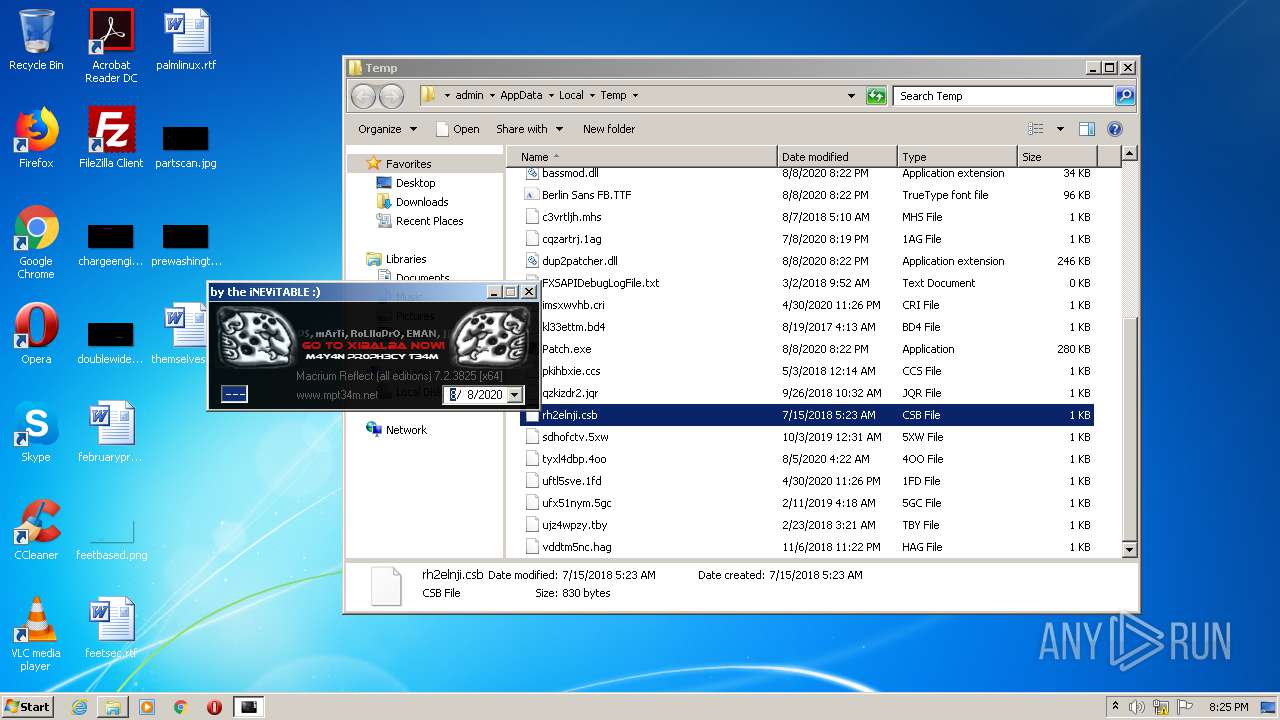
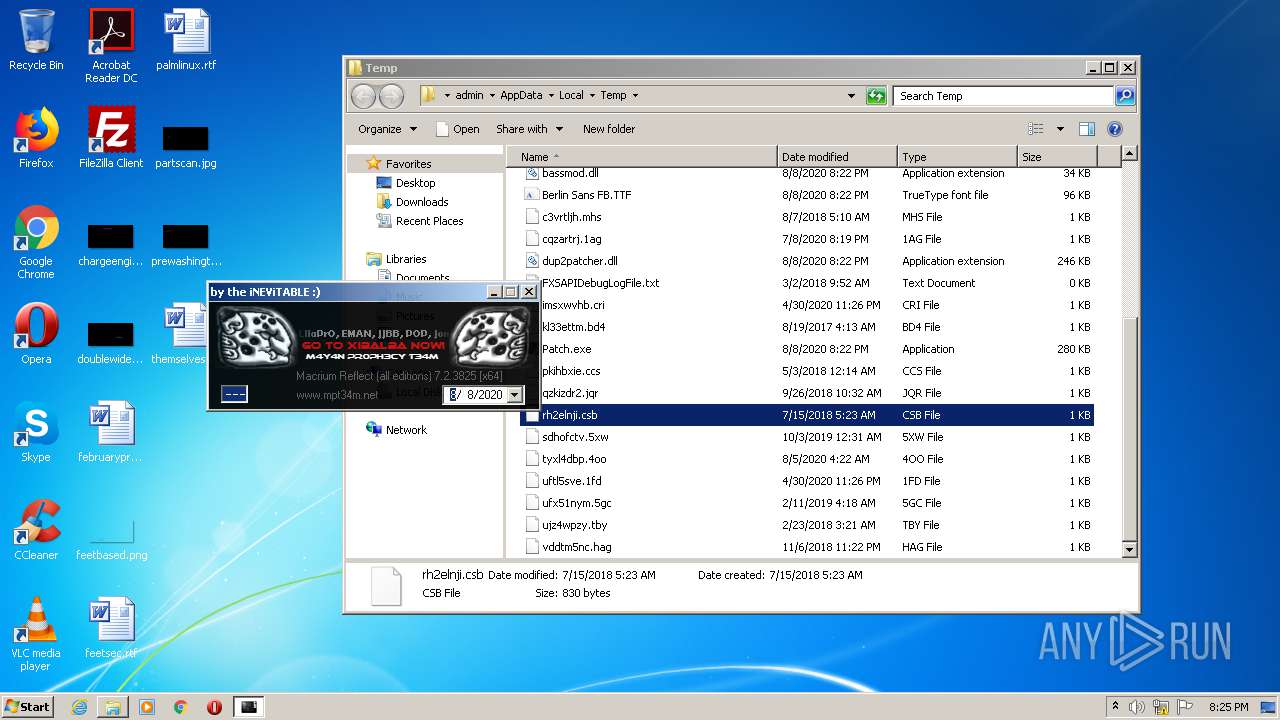
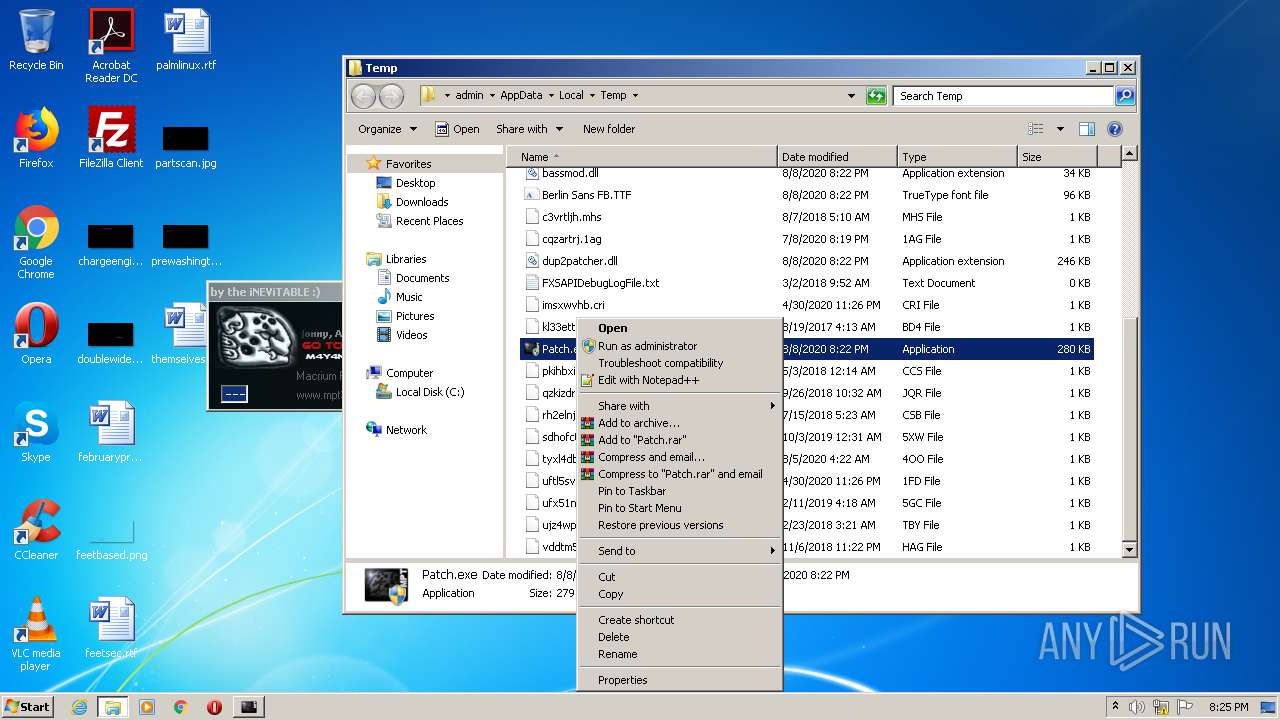
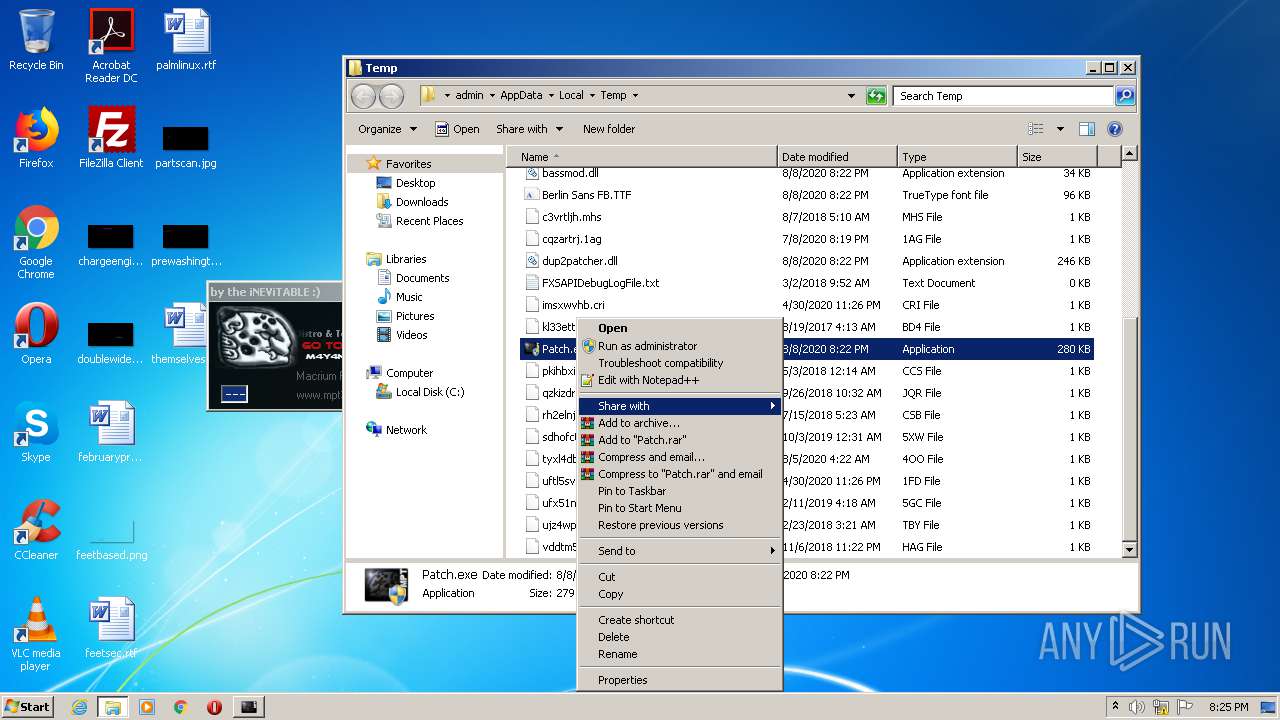
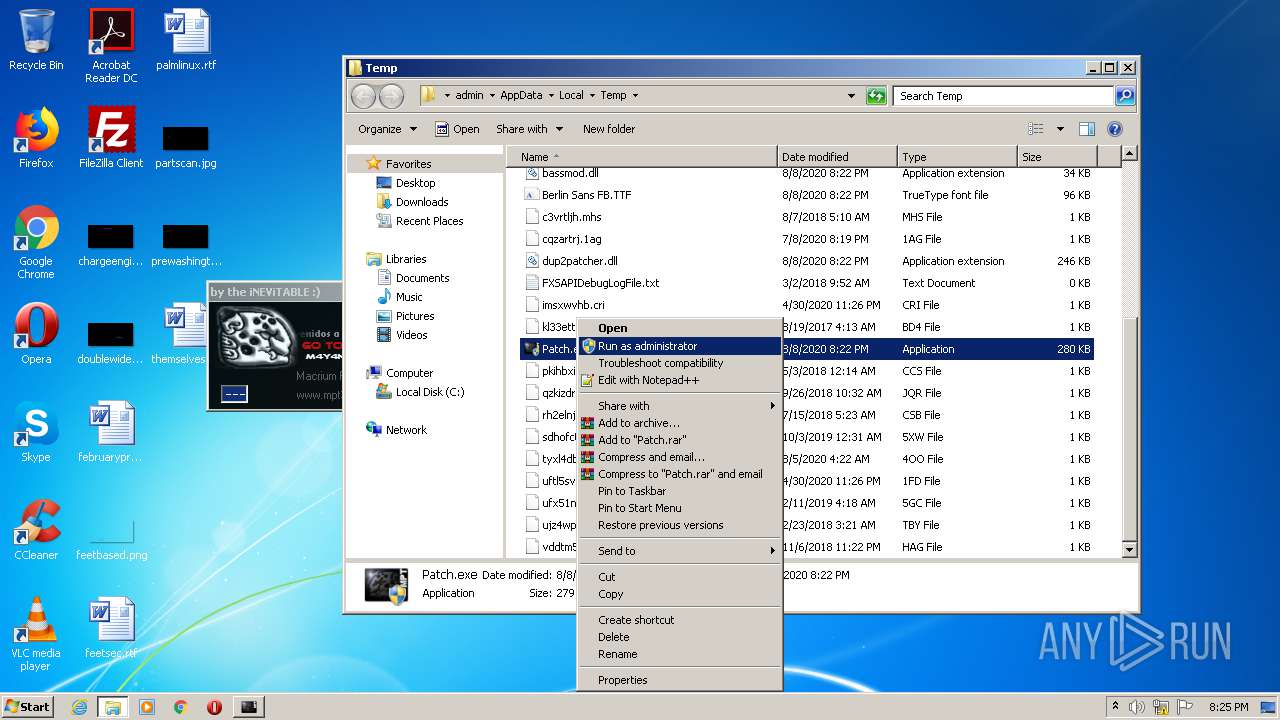
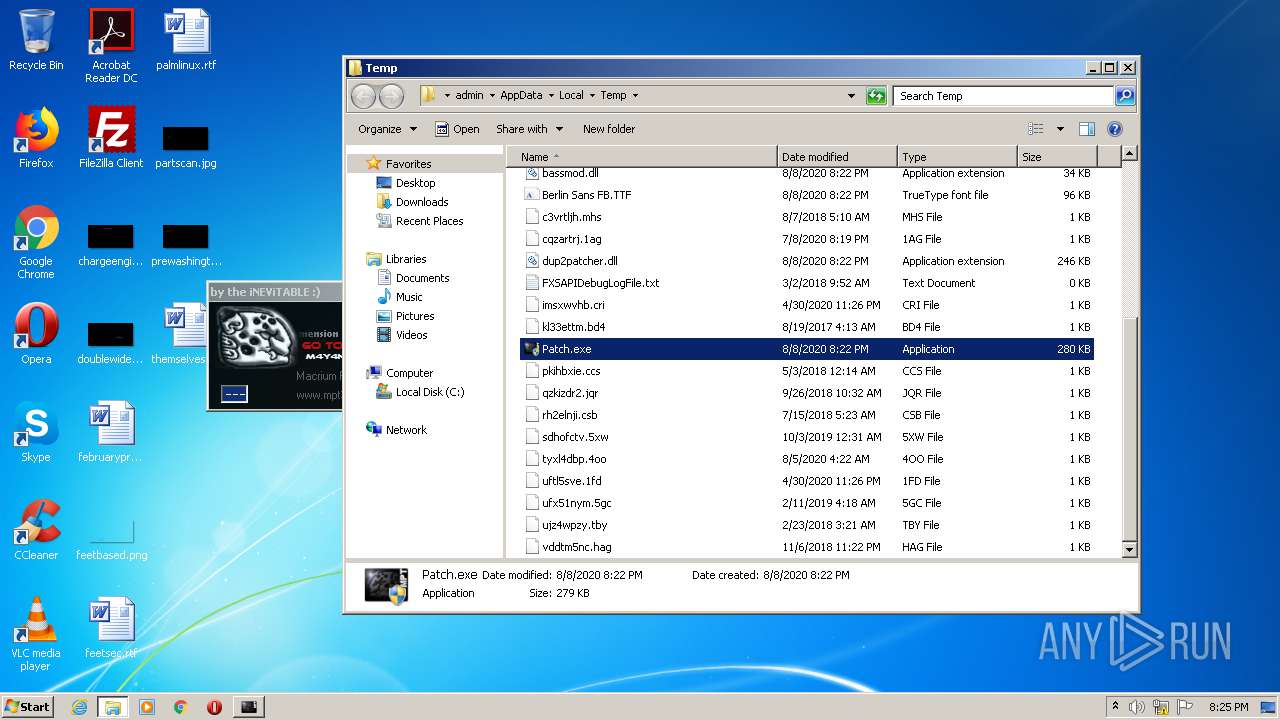
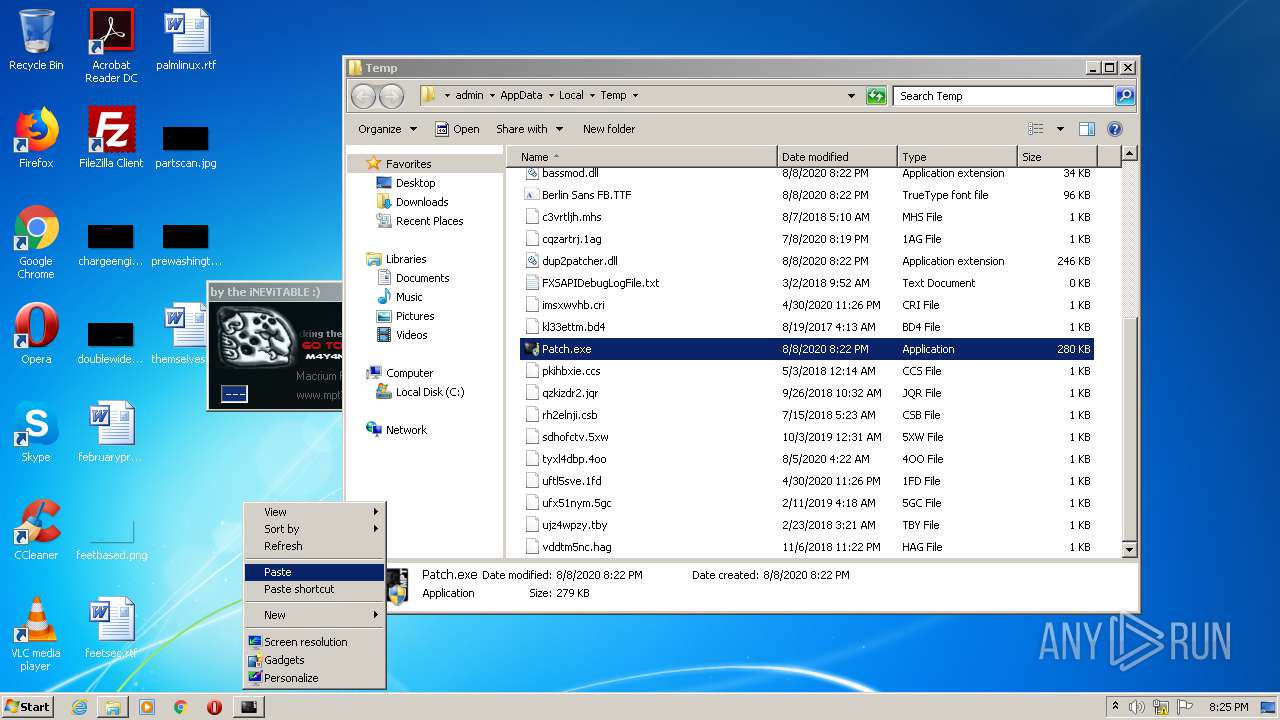
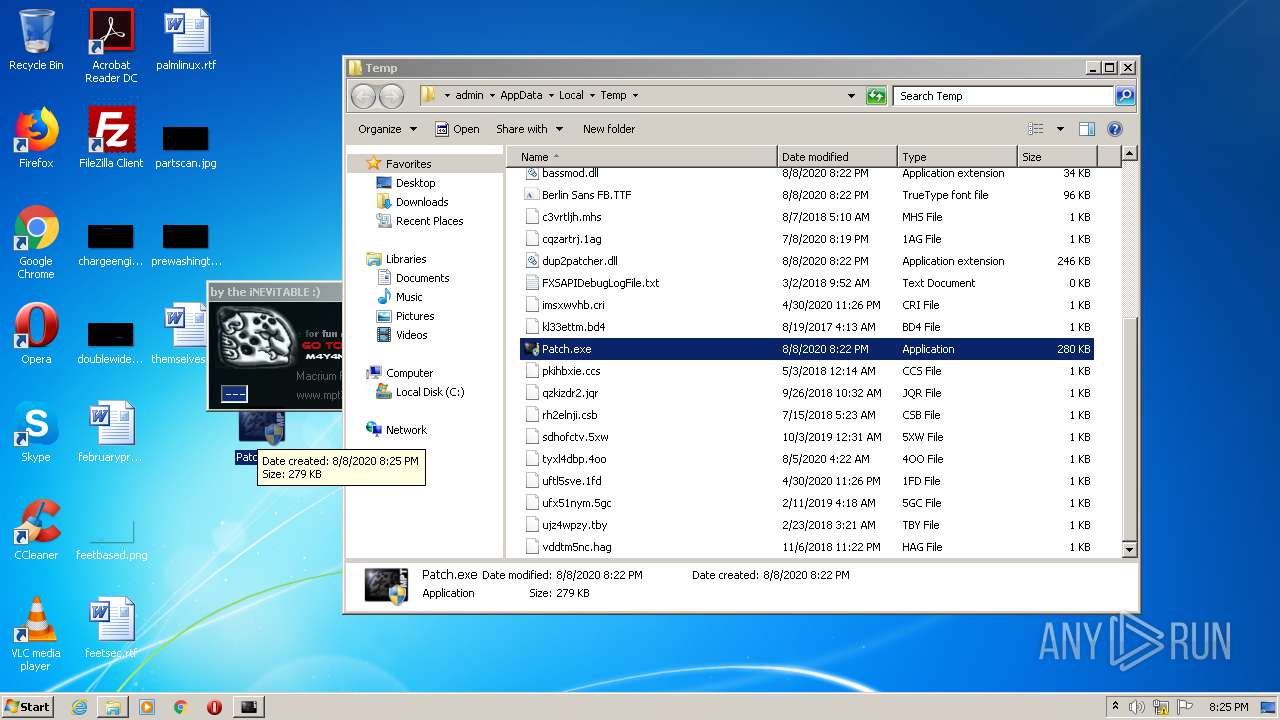
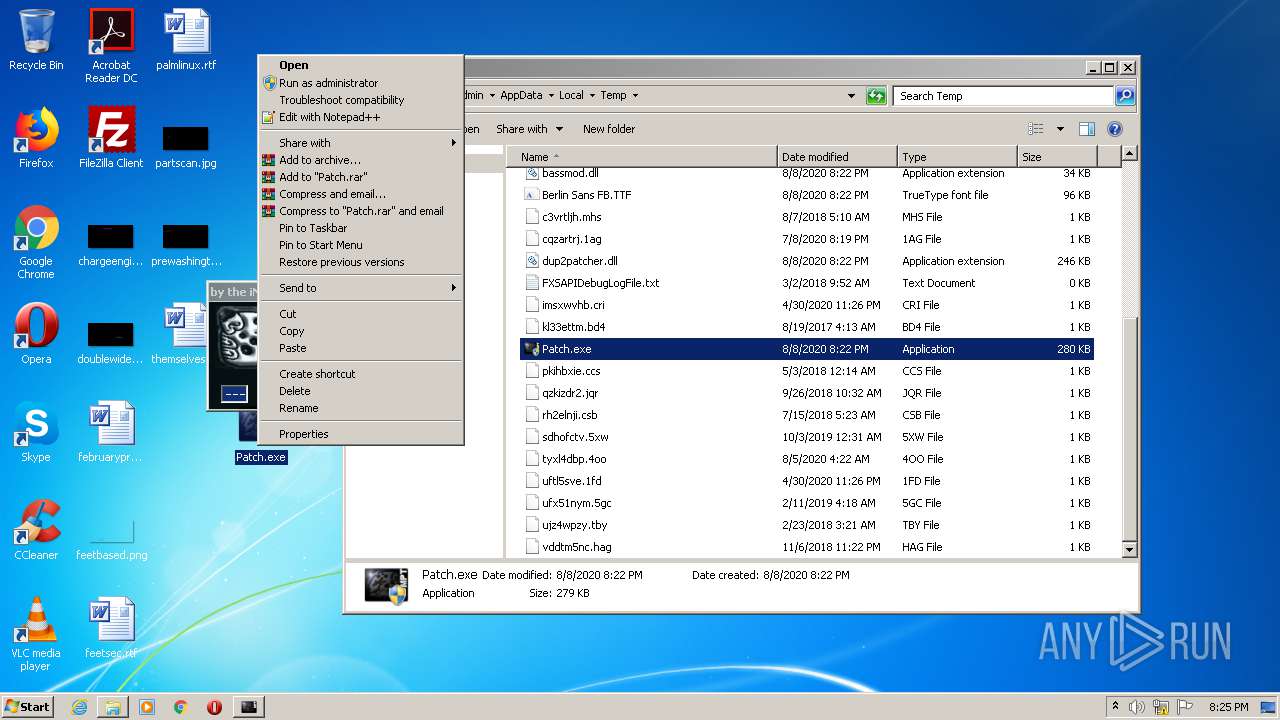
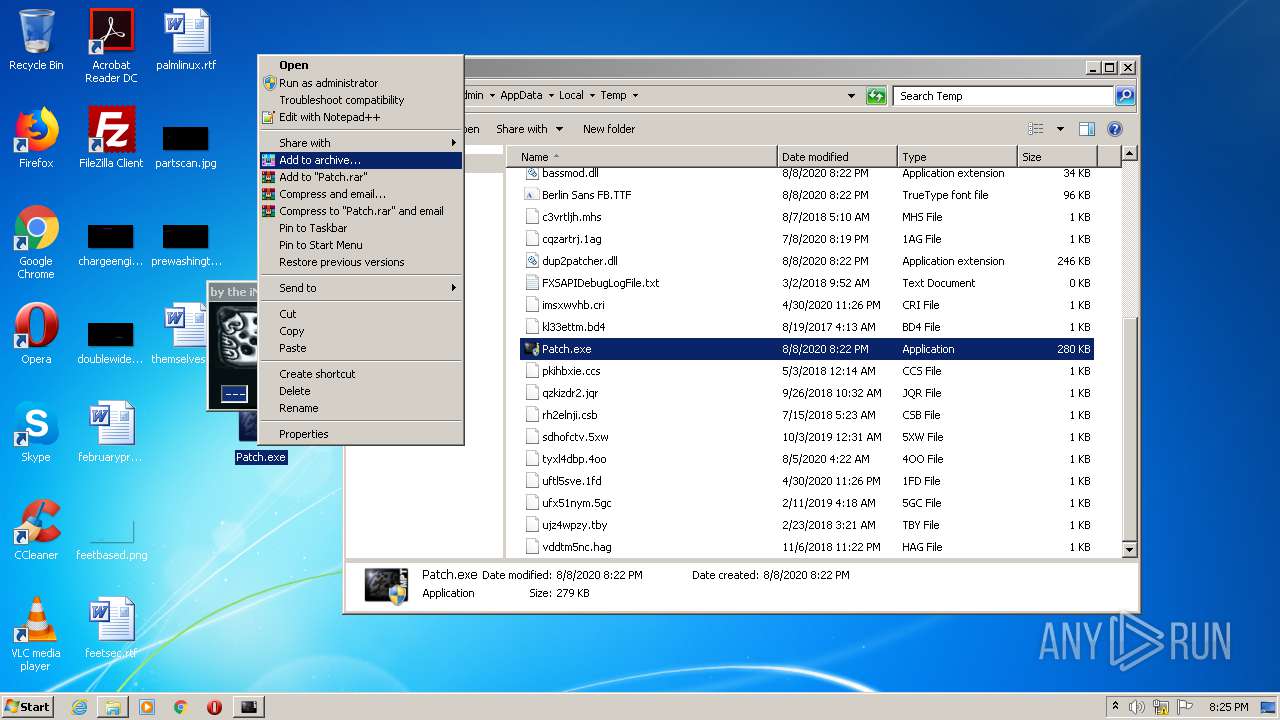
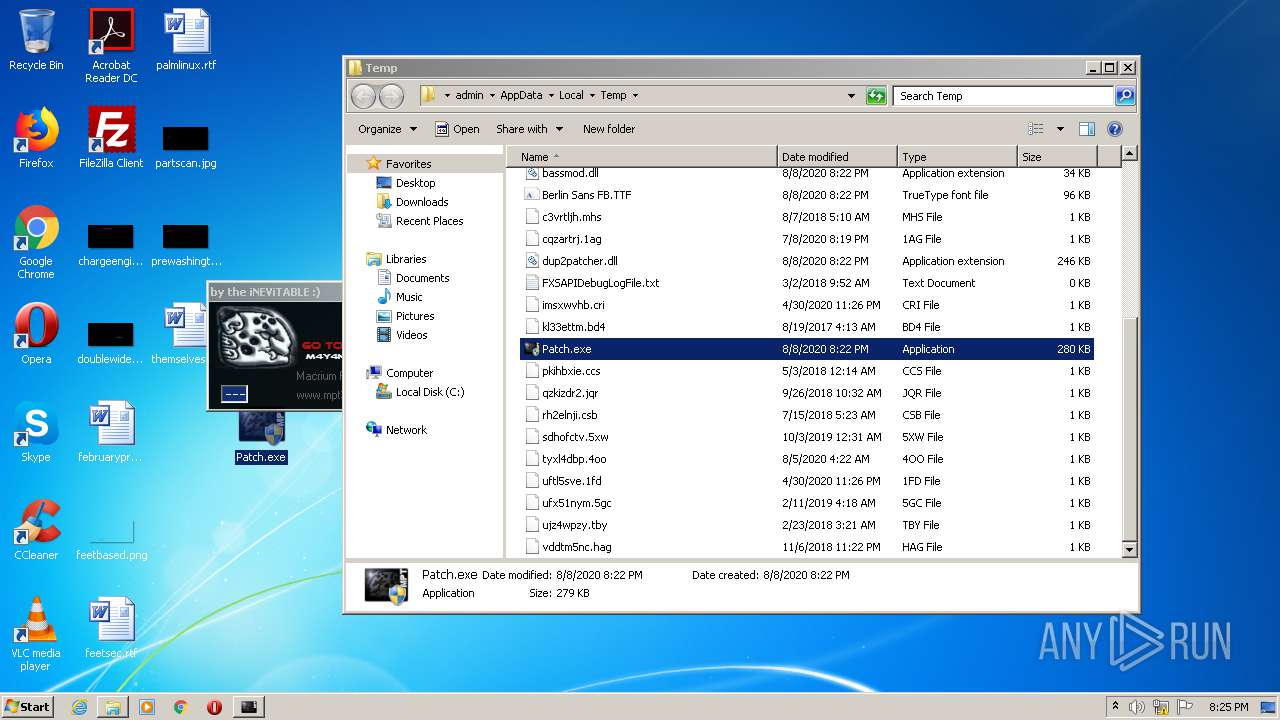
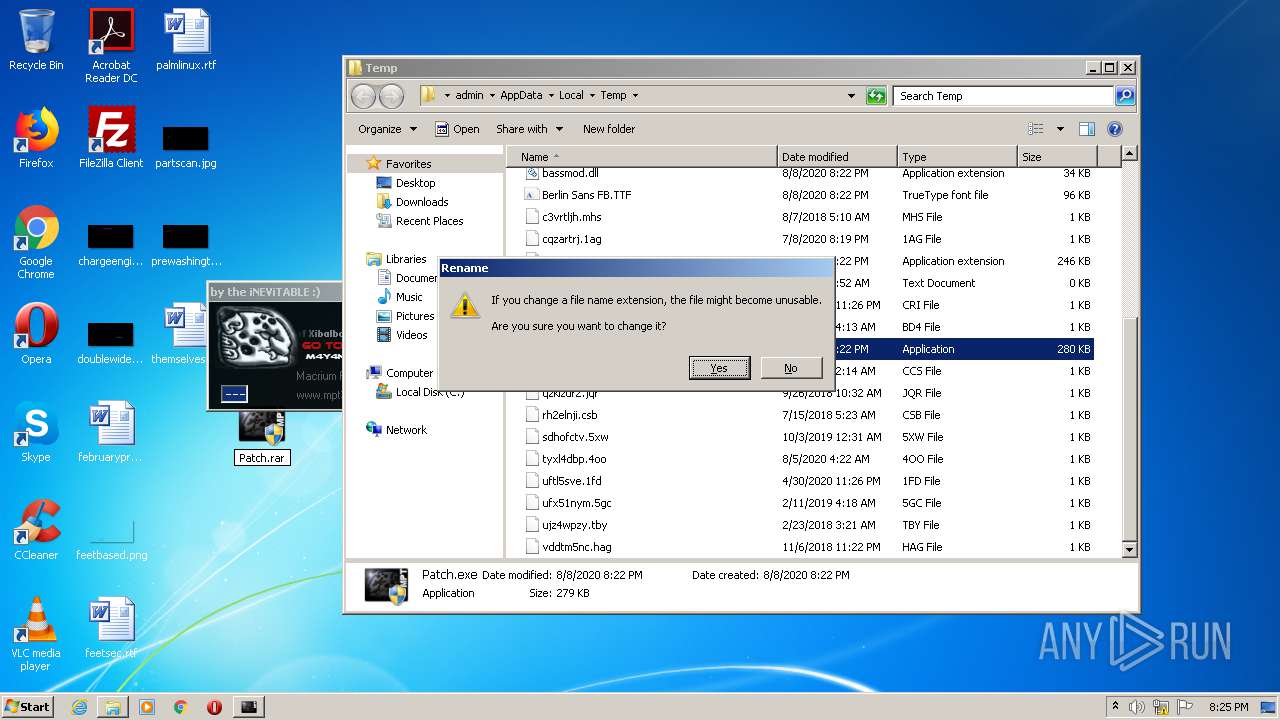
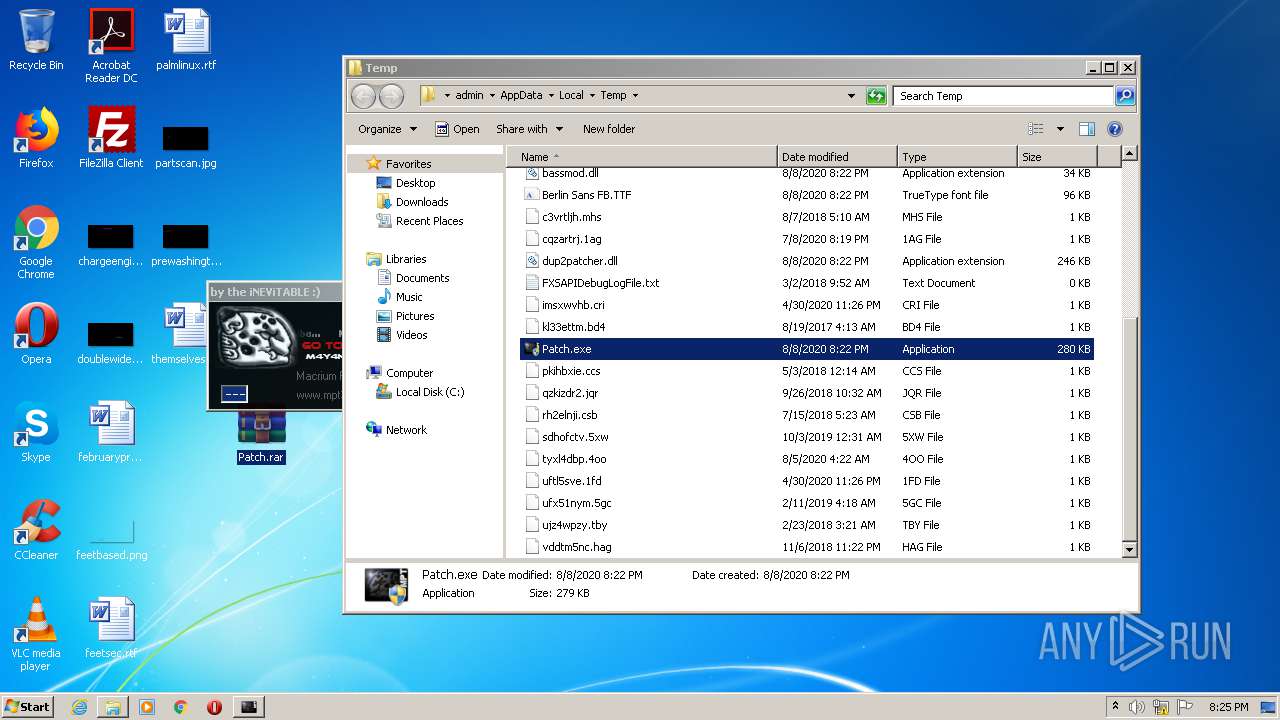
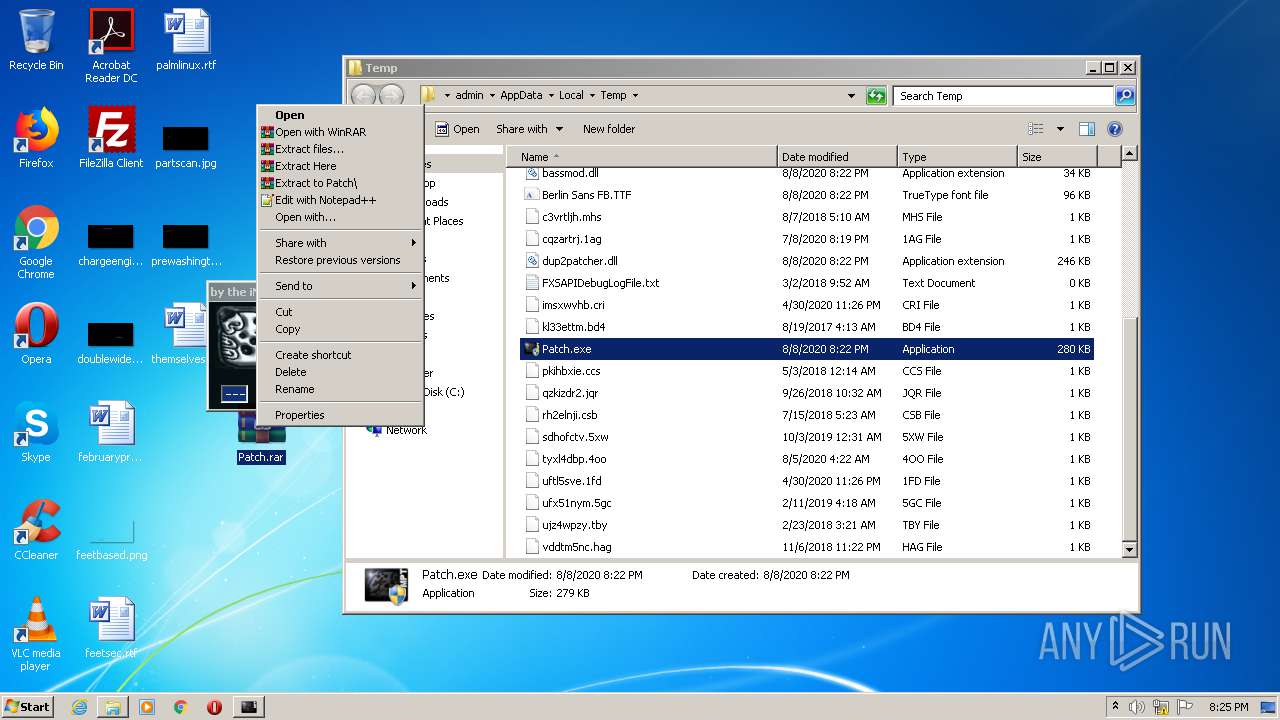
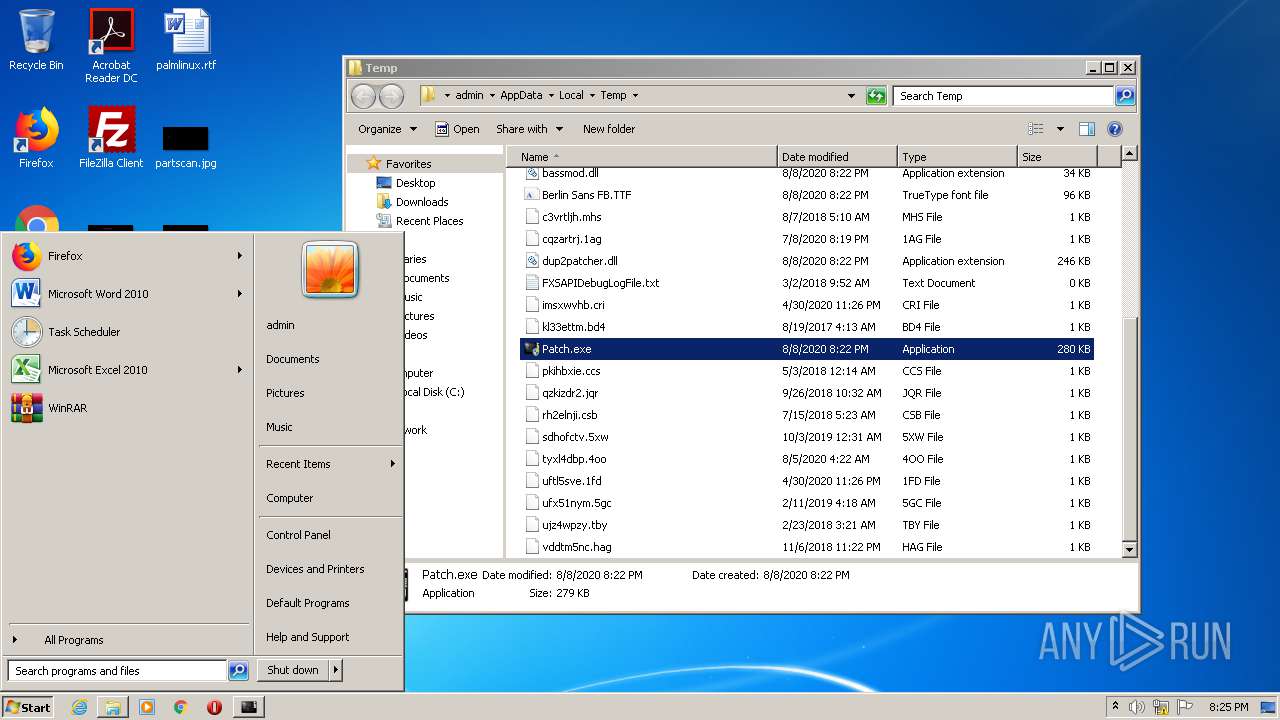
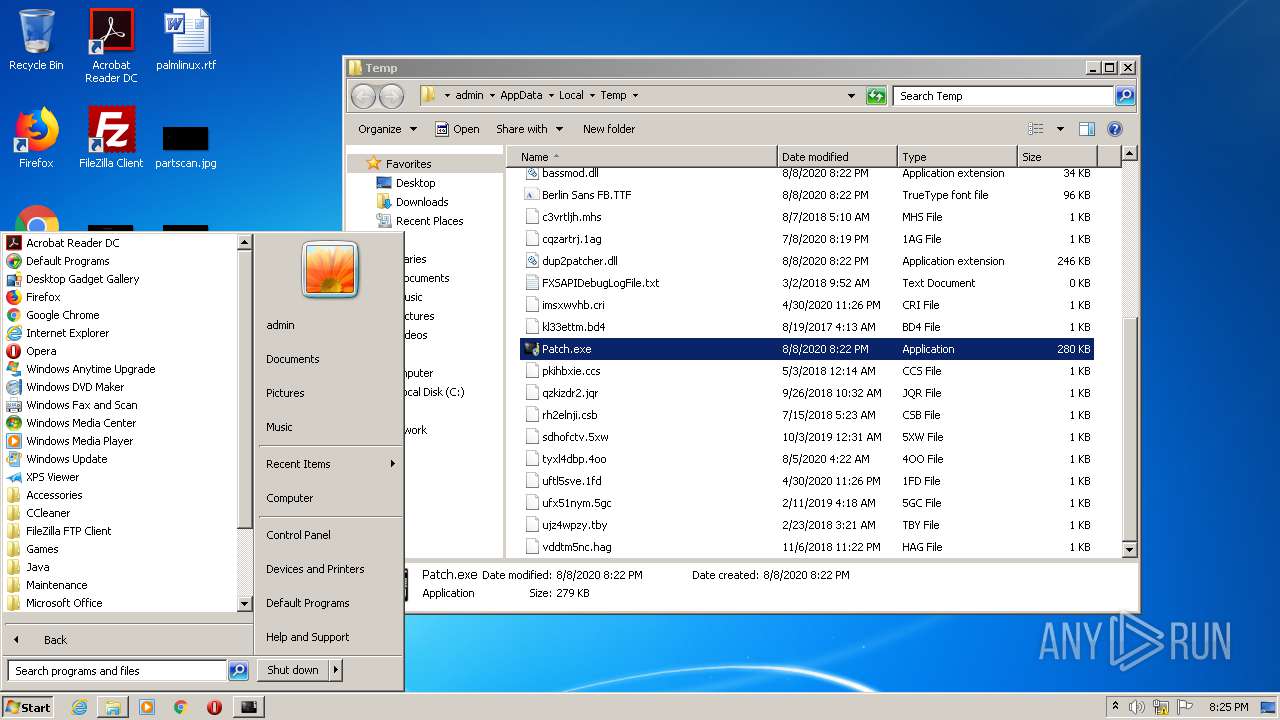
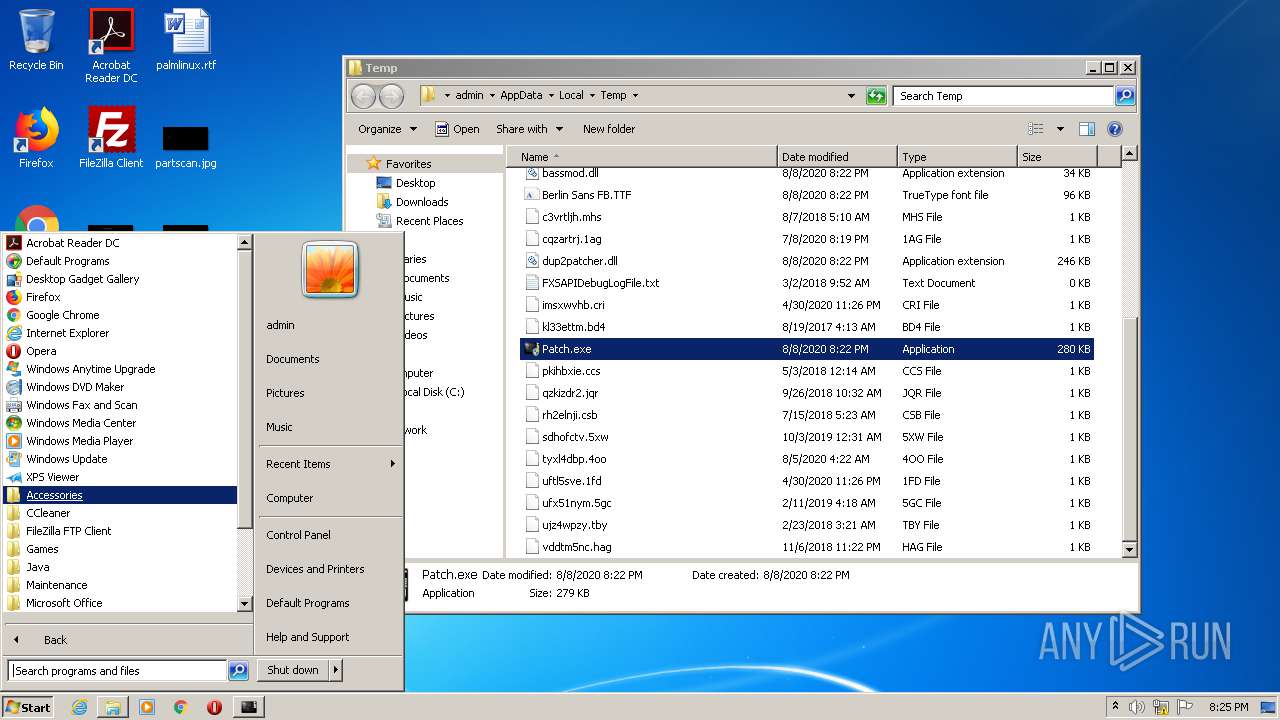
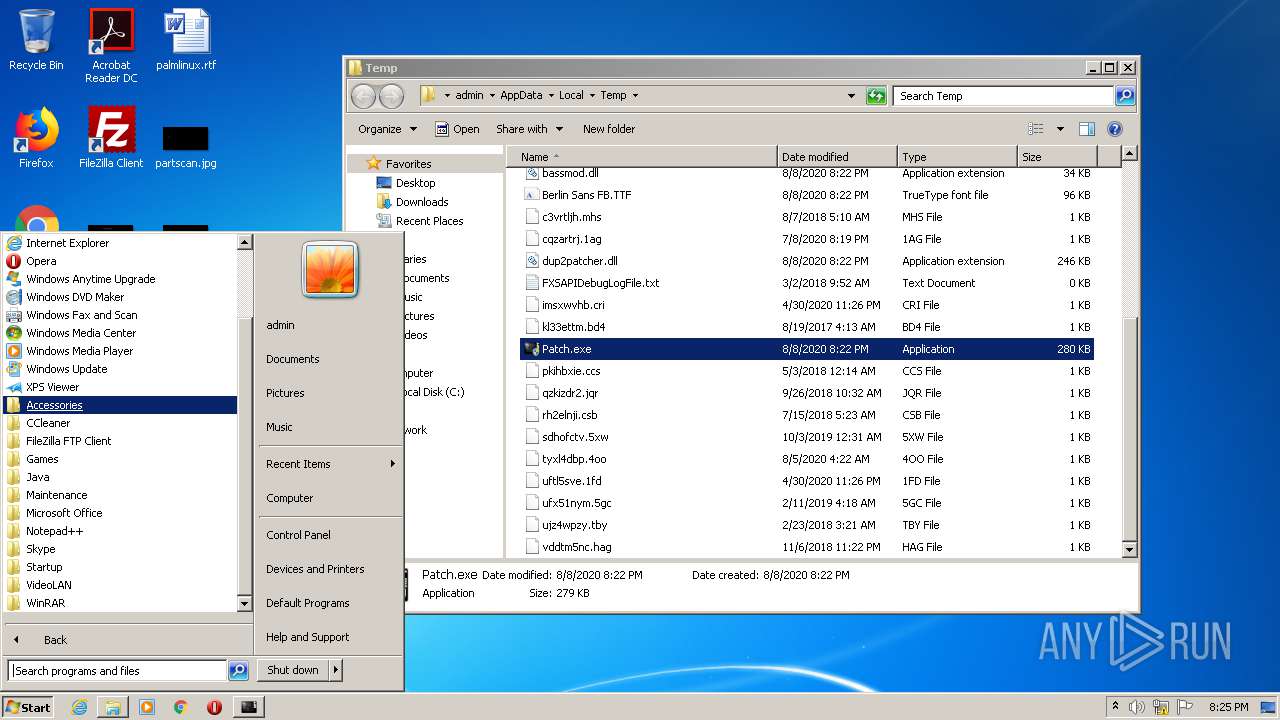
Manual execution by user
- verclsid.exe (PID: 620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:12:21 21:59:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 512 |
| InitializedDataSize: | 284672 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x102b |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Dec-2012 20:59:46 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 21-Dec-2012 20:59:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000001F6 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.06408 |
.rdata | 0x00002000 | 0x000001D8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.27064 |
.data | 0x00003000 | 0x00000034 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.568988 |
.rsrc | 0x00004000 | 0x0004519C | 0x00045200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.88517 |
.reloc | 0x0004A000 | 0x00000052 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.736046 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.85663 | 898 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 3.34777 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.08777 | 488 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 2.65367 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.72922 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 6.11731 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 6.09324 | 1736 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 4.62248 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 4.86341 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
10 | 4.93104 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
kernel32.dll |
Total processes
61
Monitored processes
12
Malicious processes
2
Suspicious processes
0
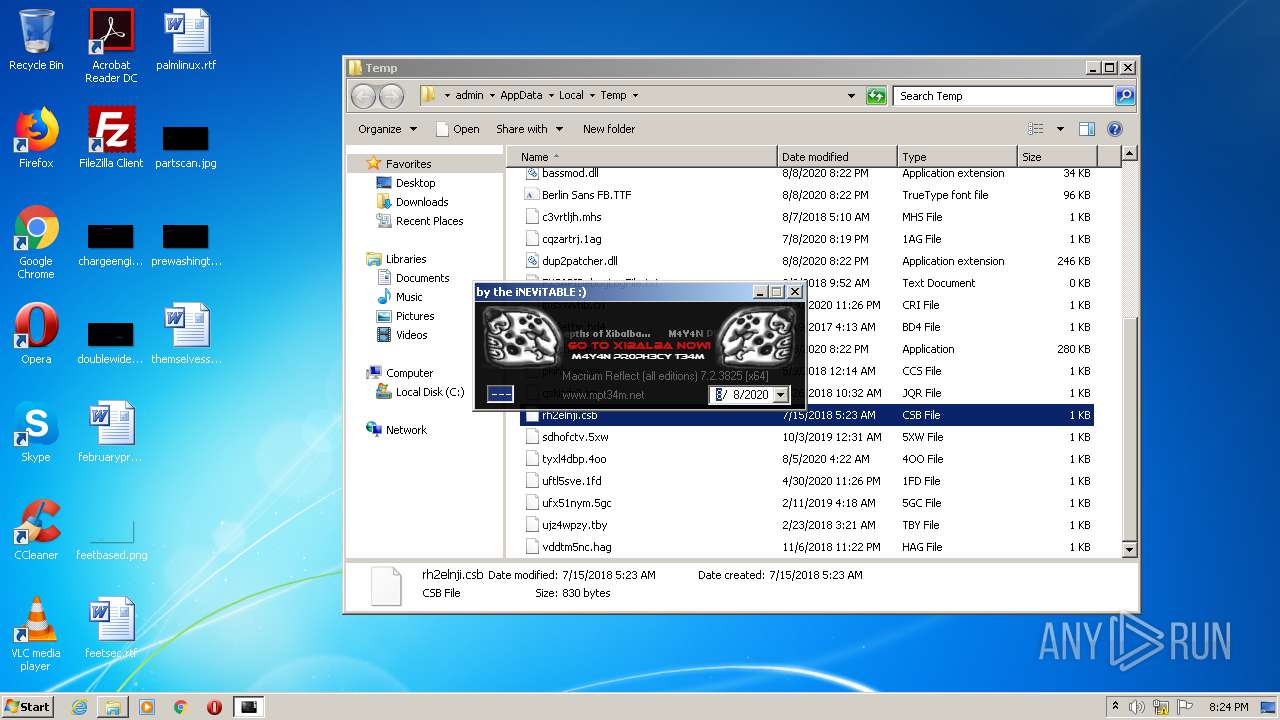
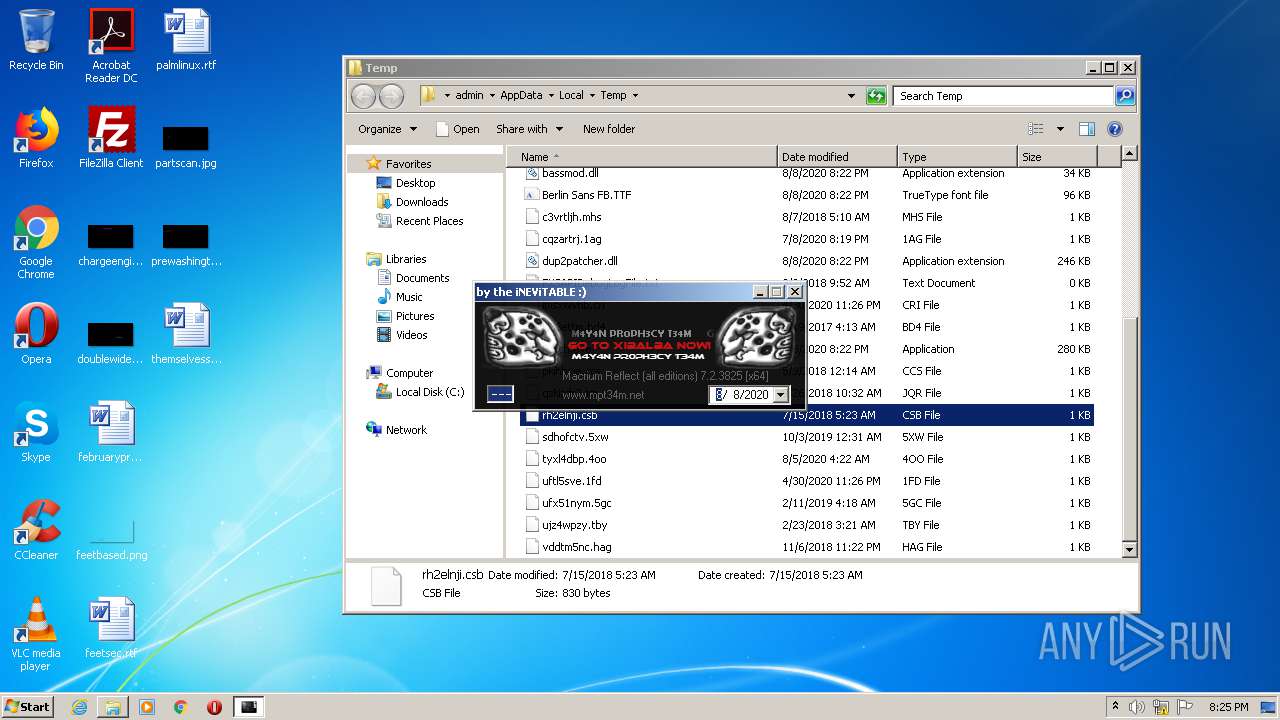
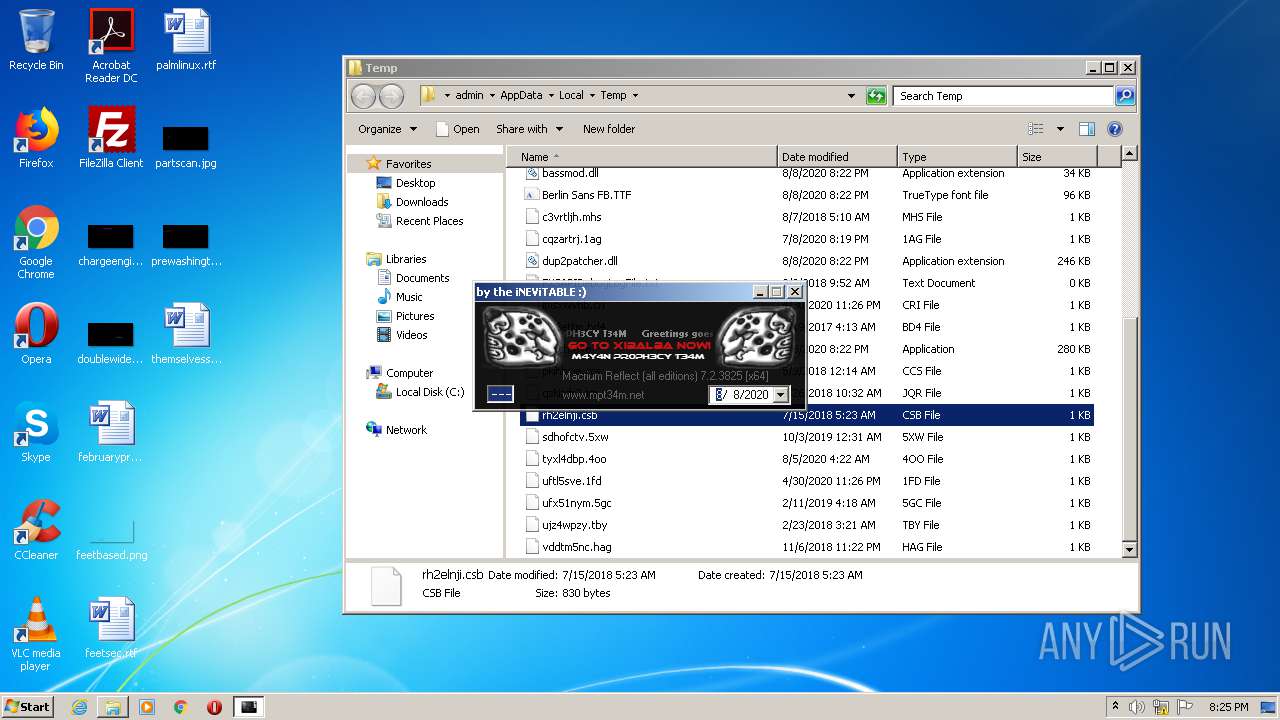
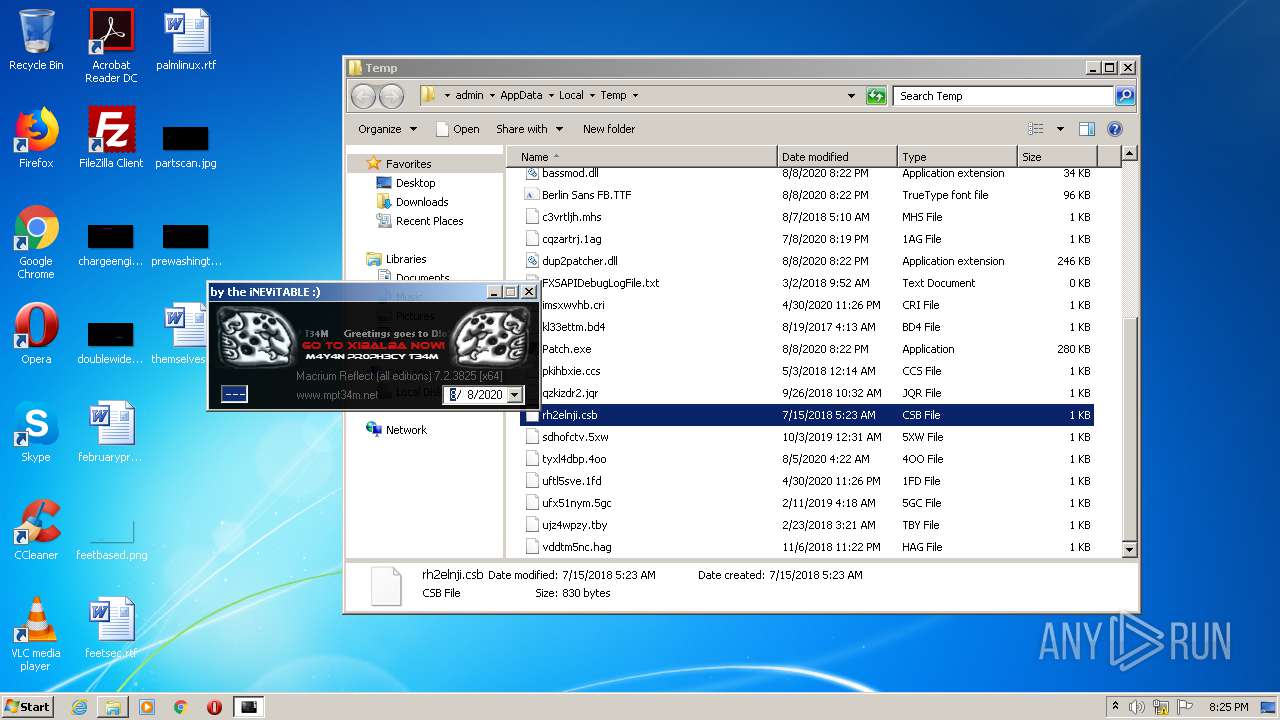
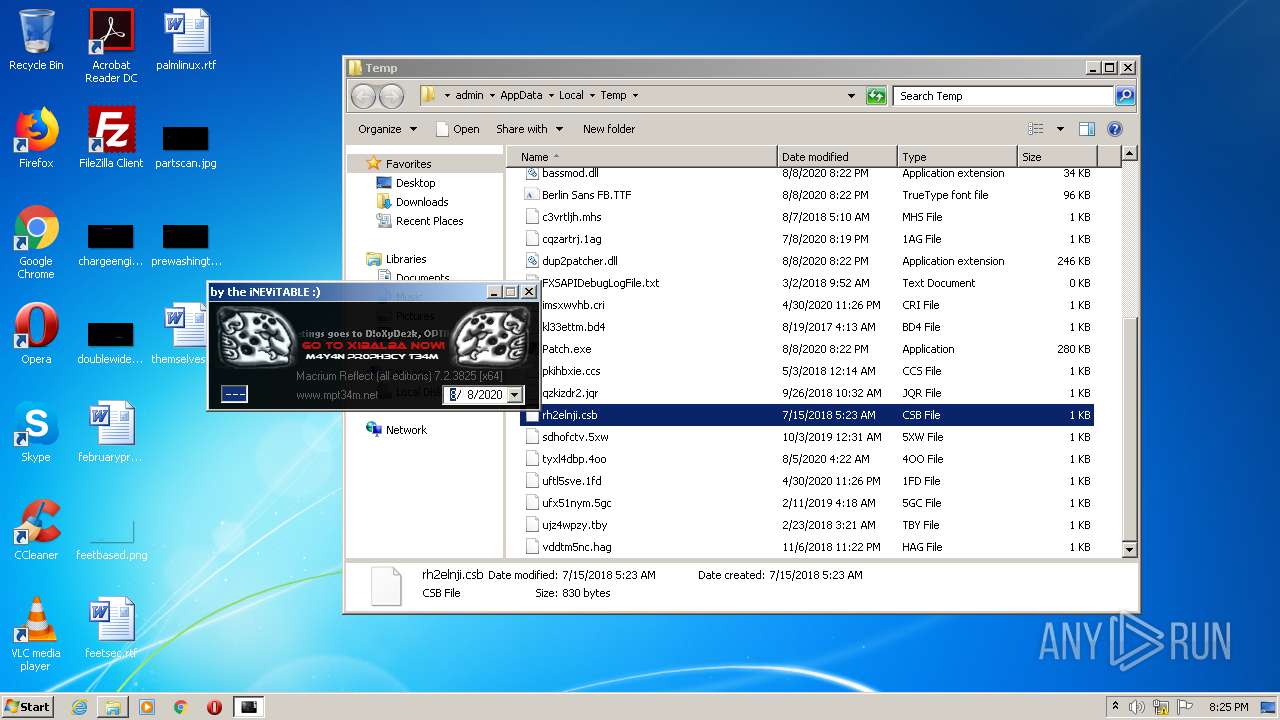
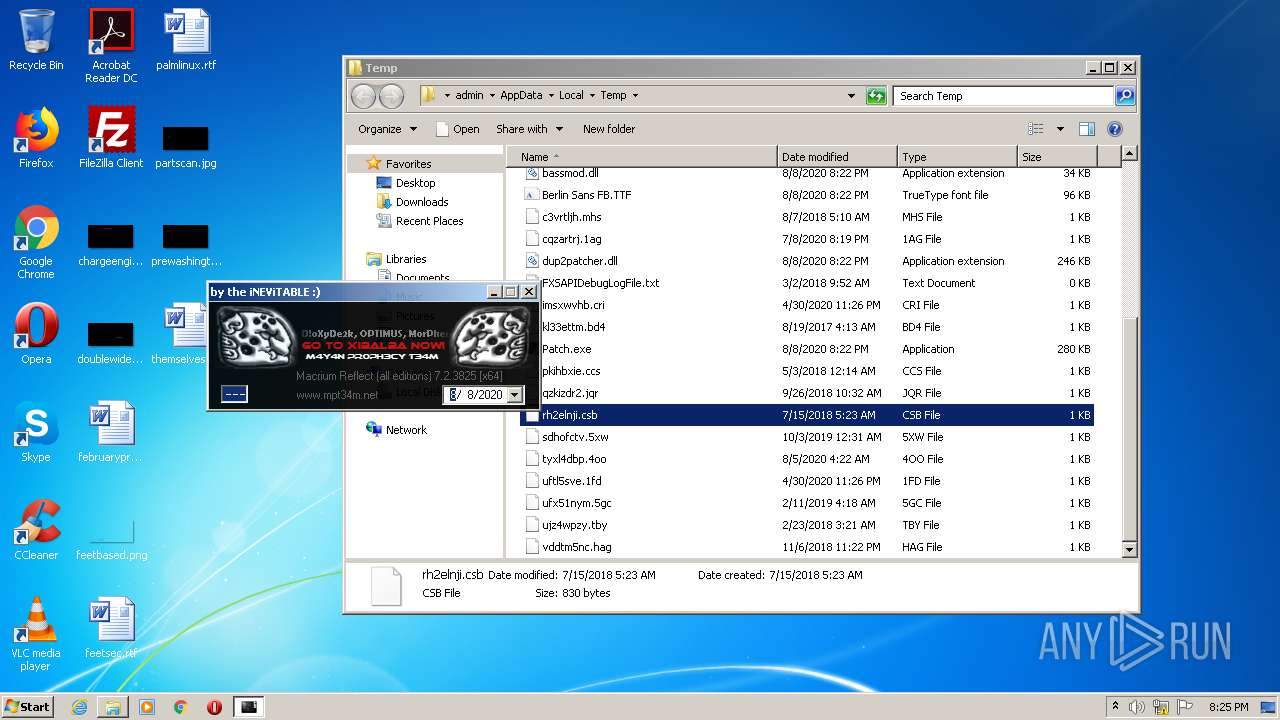
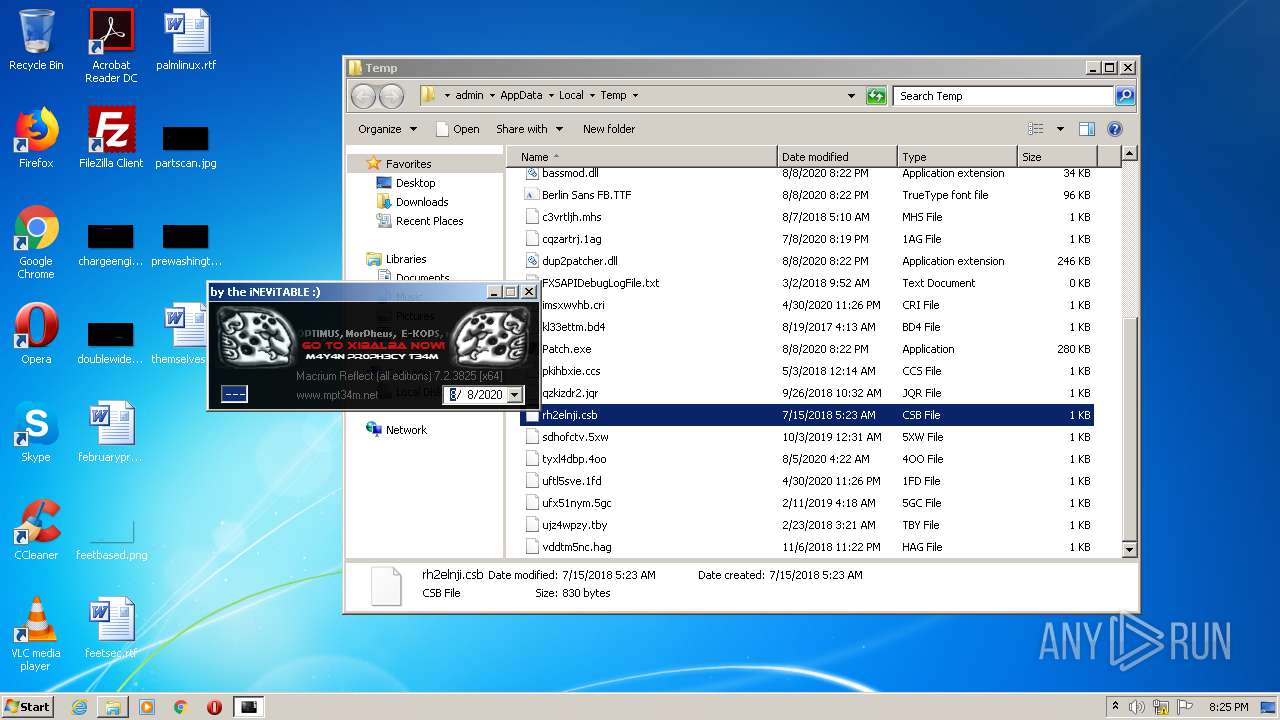
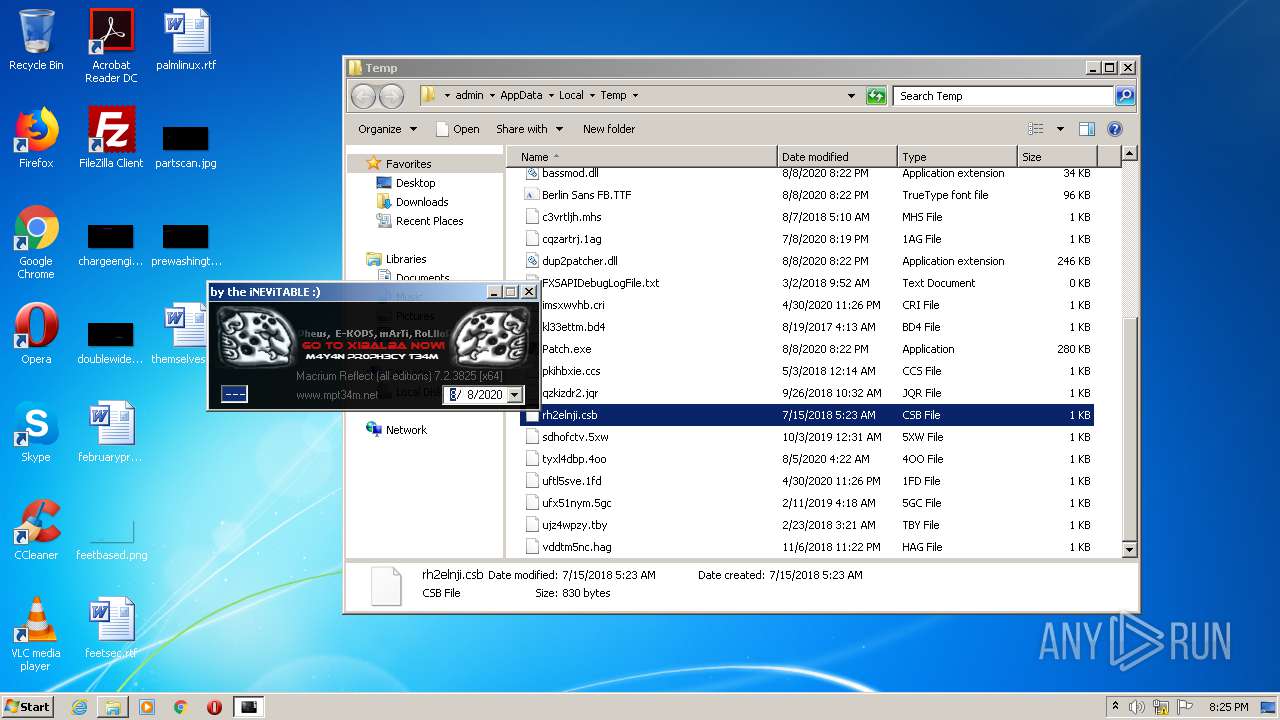
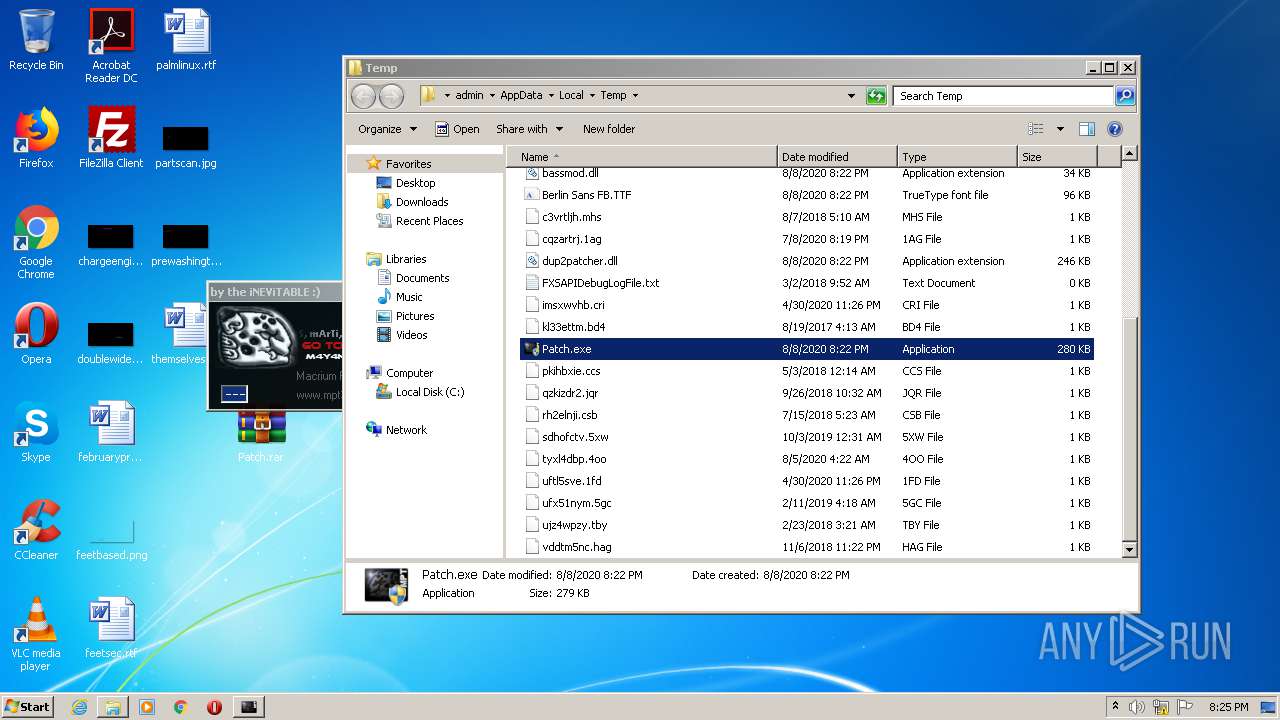
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 620 | "C:\Windows\system32\verclsid.exe" /S /C {0B2C9183-C9FA-4C53-AE21-C900B0C39965} /I {0C733A8A-2A1C-11CE-ADE5-00AA0044773D} /X 0x401 | C:\Windows\system32\verclsid.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extension CLSID Verification Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1952 | C:\Windows\system32\net1 stop "MacriumService" | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
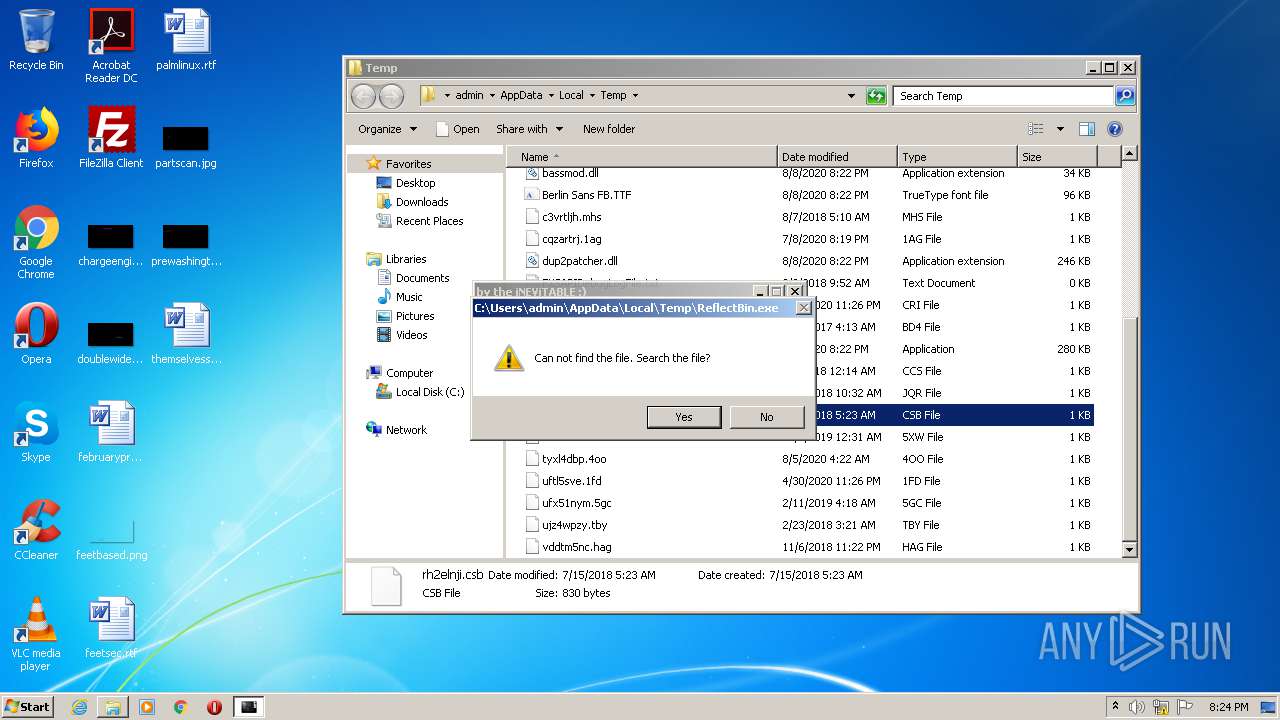
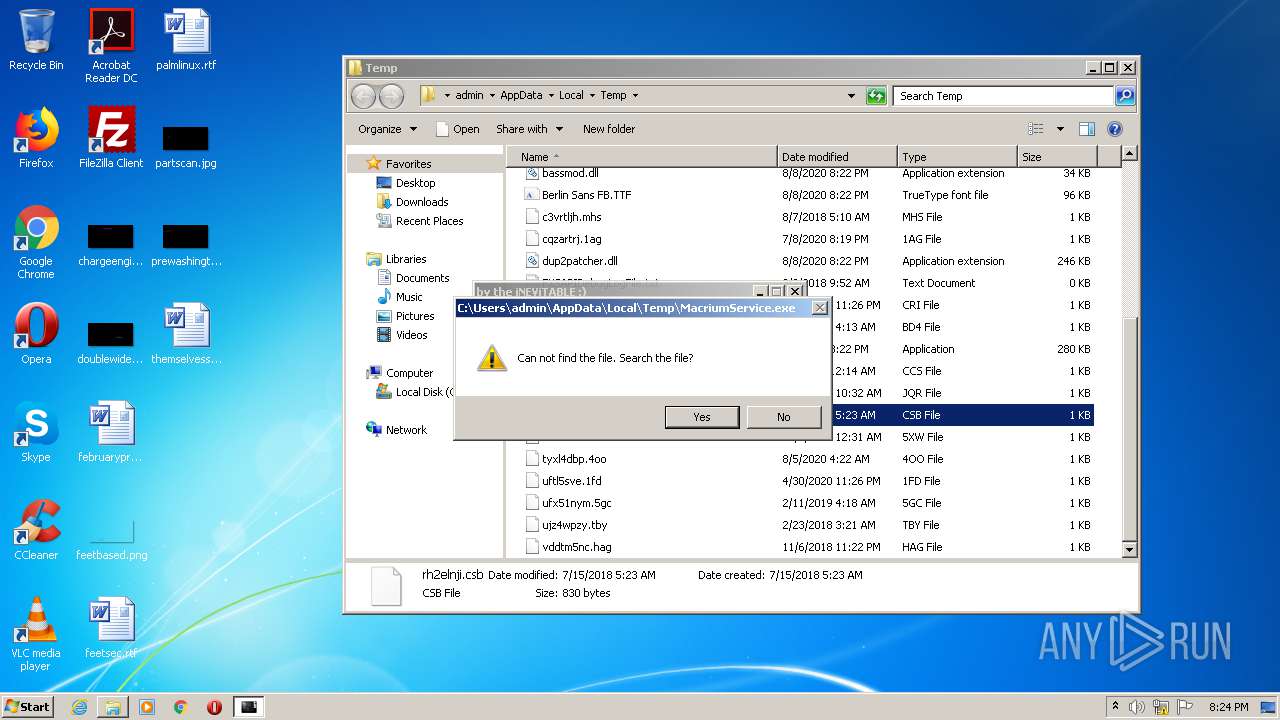
| 2544 | cmd /c "C:\Users\admin\AppData\Local\Temp\mptstop.bat" | C:\Windows\system32\cmd.exe | — | Patch.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
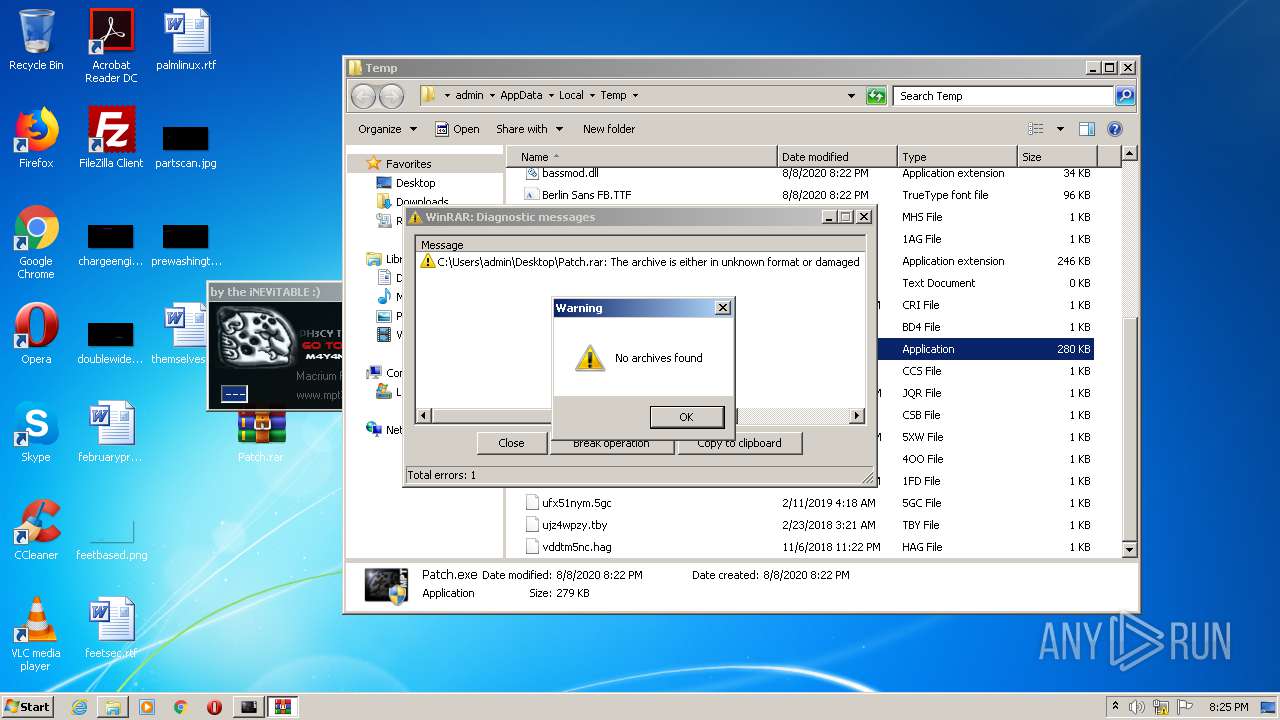
| 2764 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\Patch.rar" C:\Users\admin\Desktop\Patch\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1 Version: 5.60.0 Modules
| |||||||||||||||
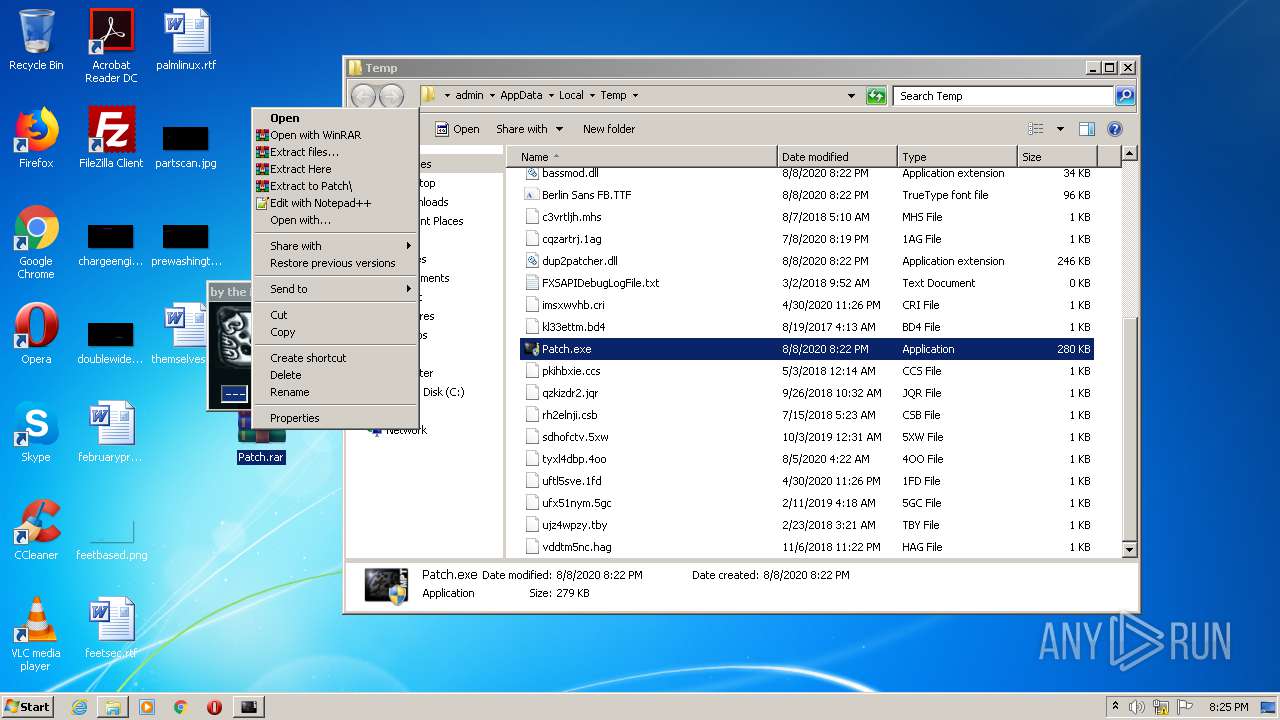
| 2780 | "C:\Users\admin\AppData\Local\Temp\Patch.exe" | C:\Users\admin\AppData\Local\Temp\Patch.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 | |||||||||||||||
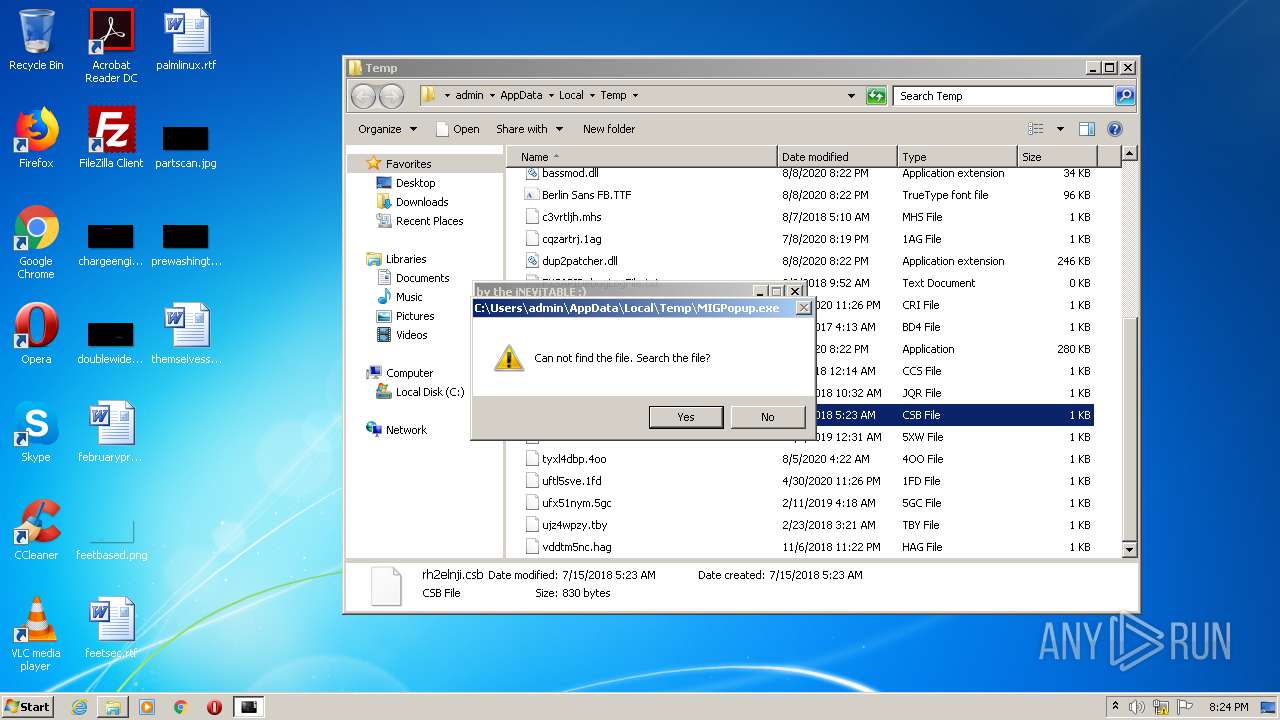
| 3108 | net start "MacriumService" | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3188 | net stop "MacriumService" | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3260 | cmd /c "C:\Users\admin\AppData\Local\Temp\mptstart.bat" | C:\Windows\system32\cmd.exe | — | Patch.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3380 | C:\Windows\system32\net1 start "MacriumService" | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
4 910
Read events
3 983
Write events
927
Delete events
0
Modification events
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\Cngpu.rkr |
Value: 00000000000000000000000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000004A000000710000007C7532000C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D020C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D020C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D02 | |||
| (PID) Process: | (3812) Patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3812) Patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
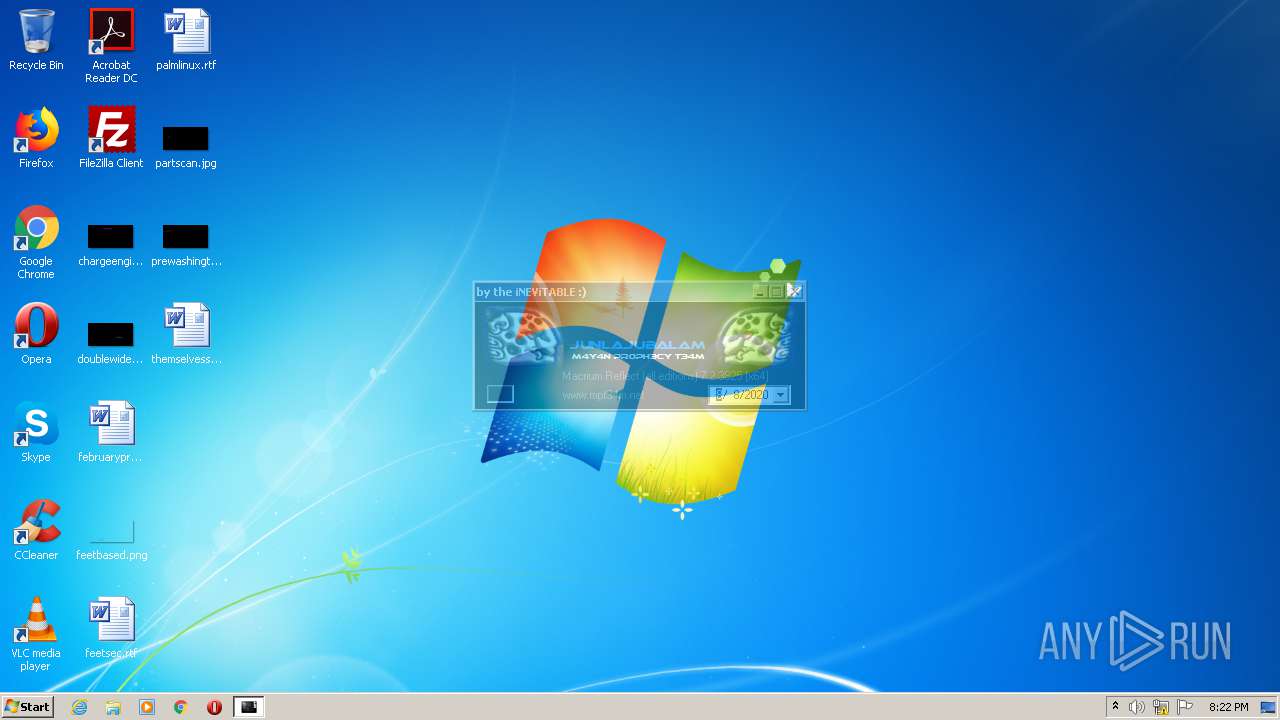
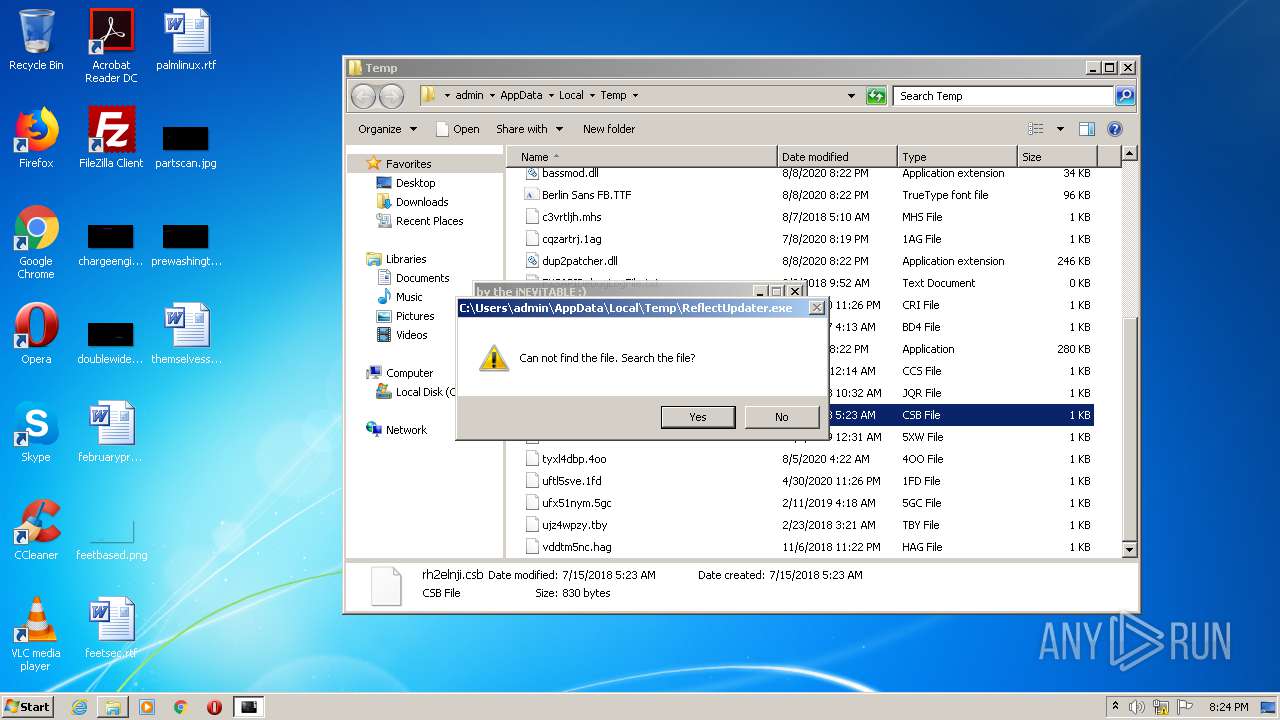
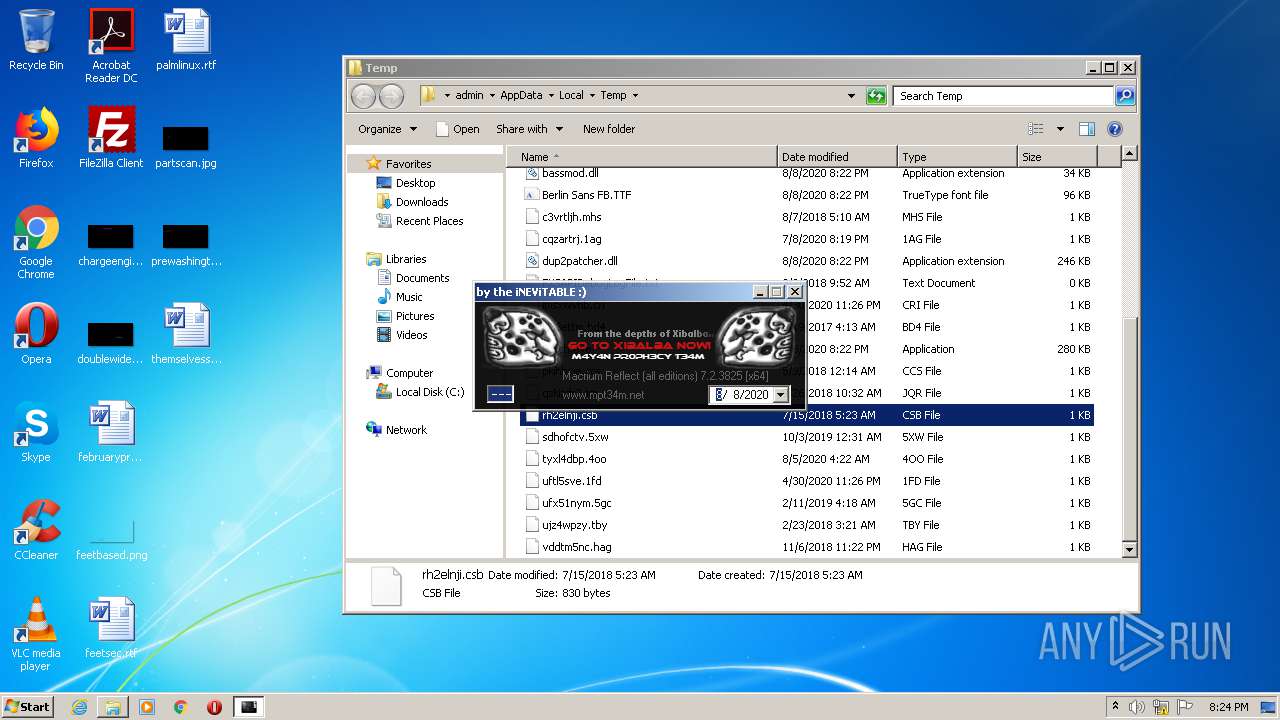
| (PID) Process: | (3588) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Macrium\Reflect |
| Operation: | write | Name: | Licensee |
Value: JUNLAJUBALAM | |||
| (PID) Process: | (3588) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Macrium\Reflect |
| Operation: | write | Name: | SupportData |
Value: 020000000000000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {Q65231O0-O2S1-4857-N4PR-N8R7P6RN7Q27}\pzq.rkr |
Value: 0000000004000000060000001EA10100000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF004EA402C559D60100000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000004A00000071000000377632000C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D020C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D020C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D02 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ApplicationDestinations |
| Operation: | write | Name: | MaxEntries |
Value: 15 | |||
Executable files
6
Suspicious files
1
Text files
1
Unknown types
2
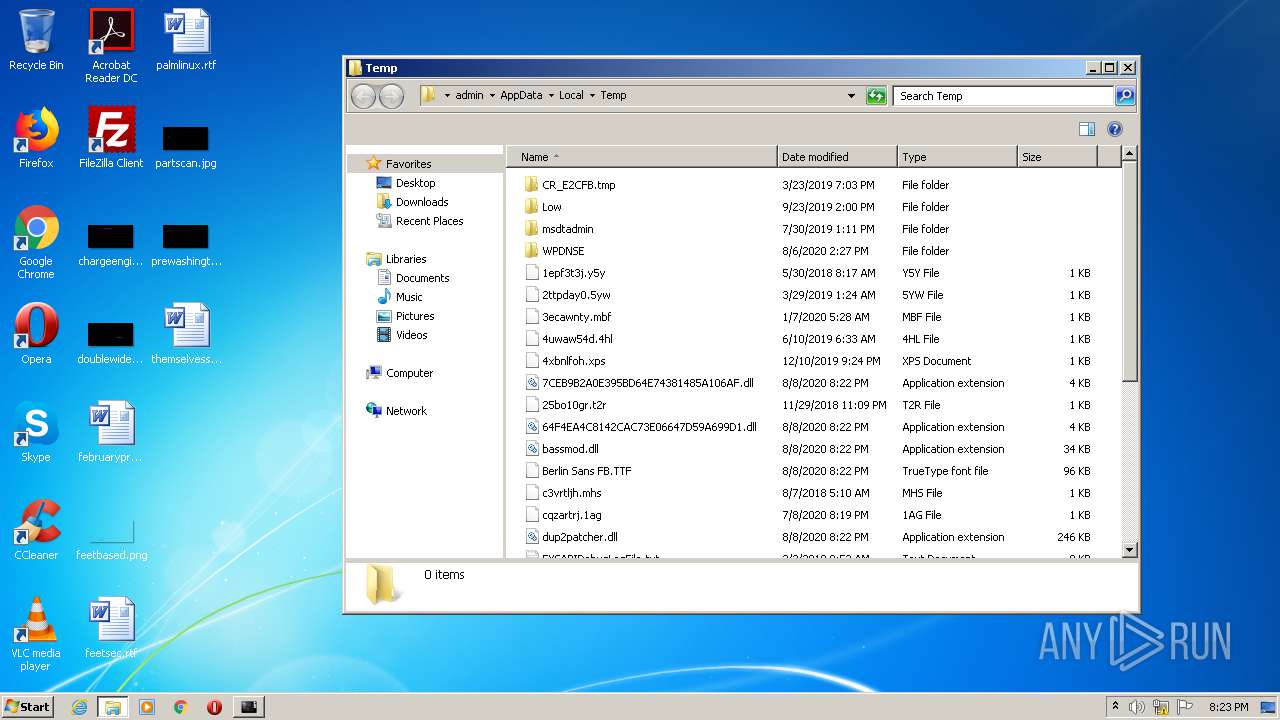
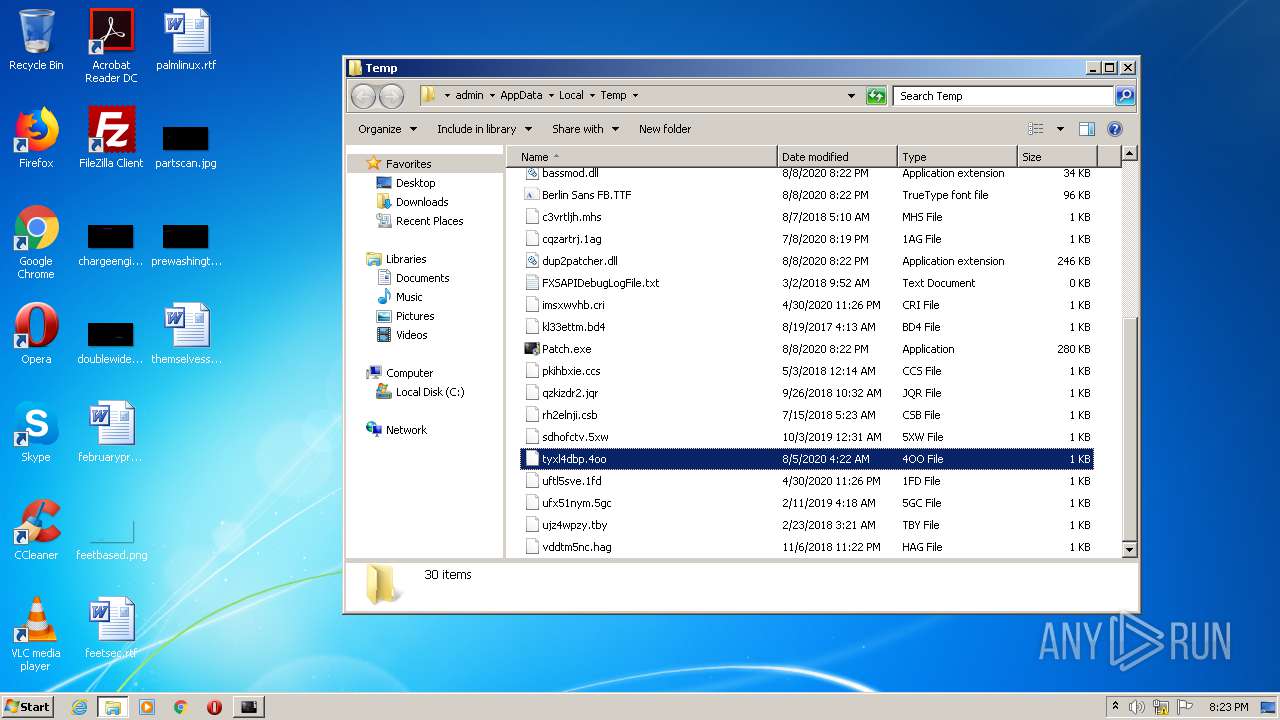
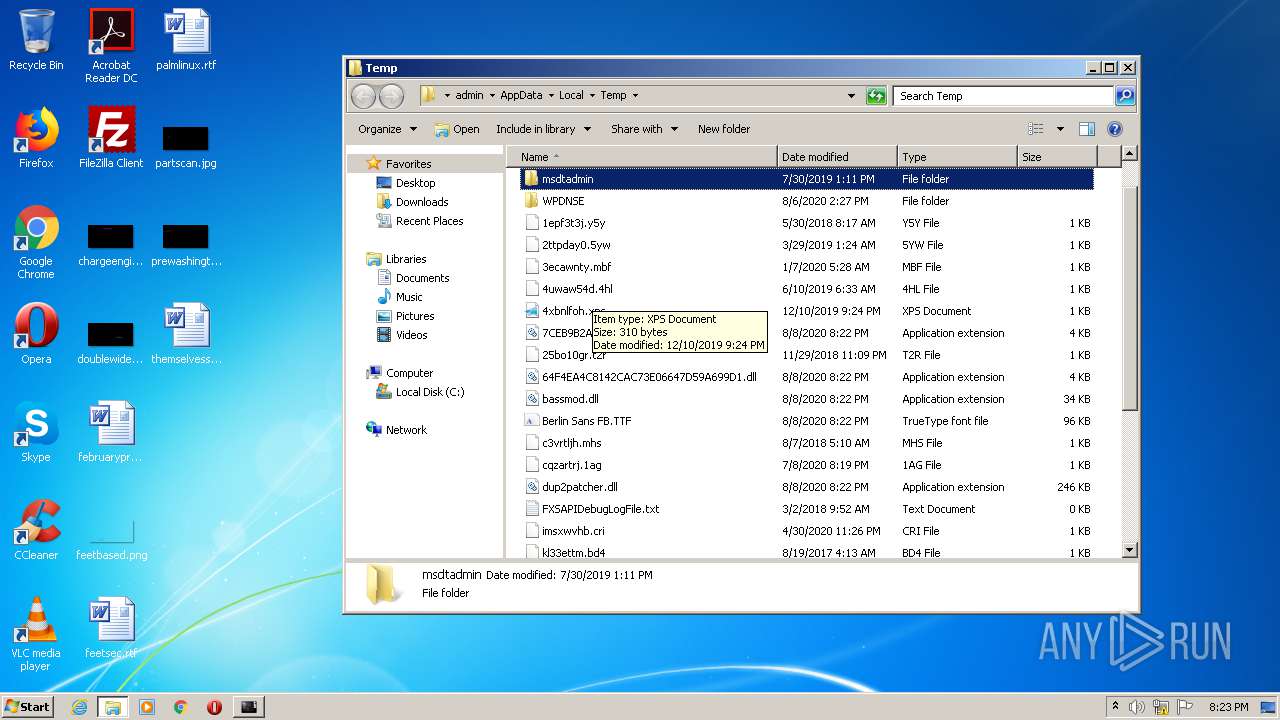
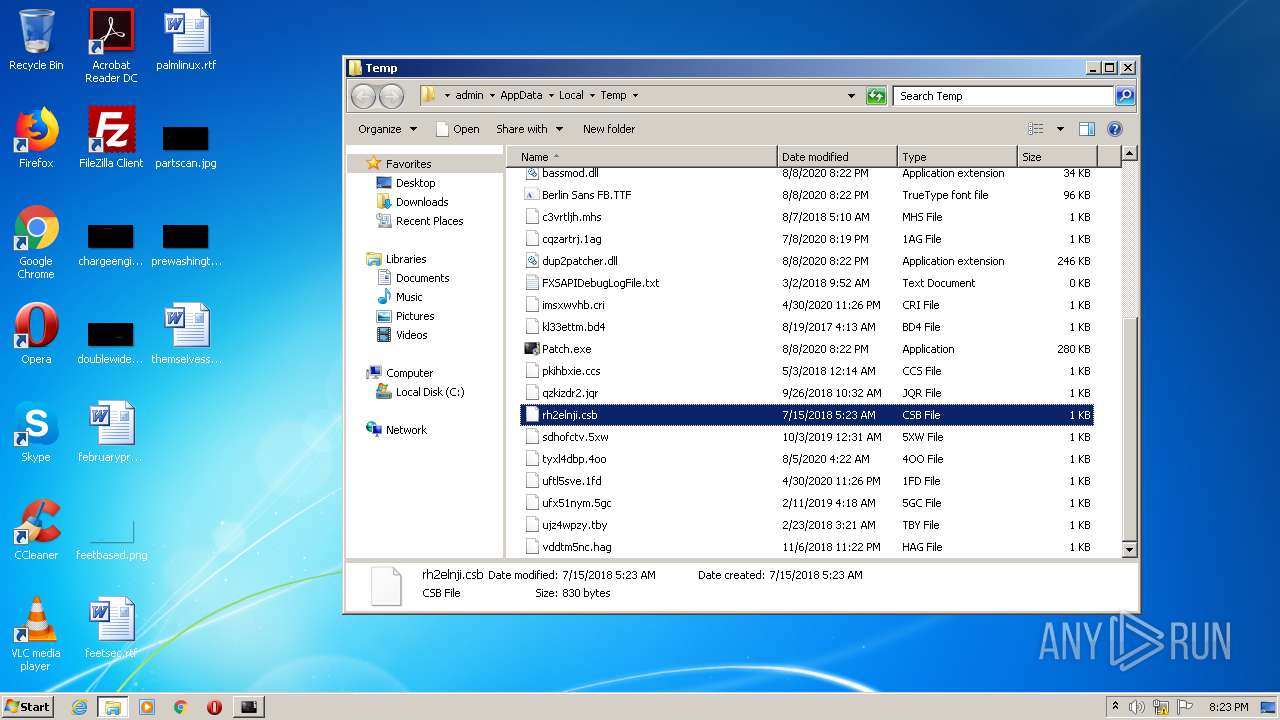
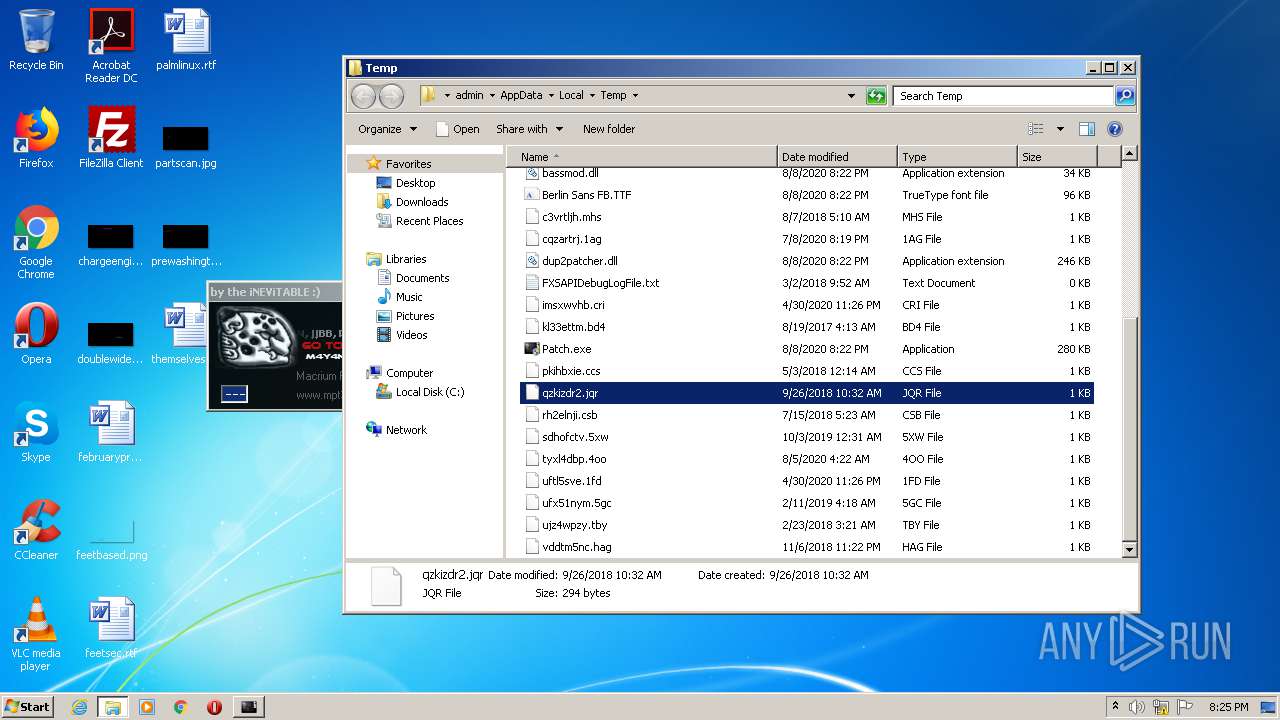
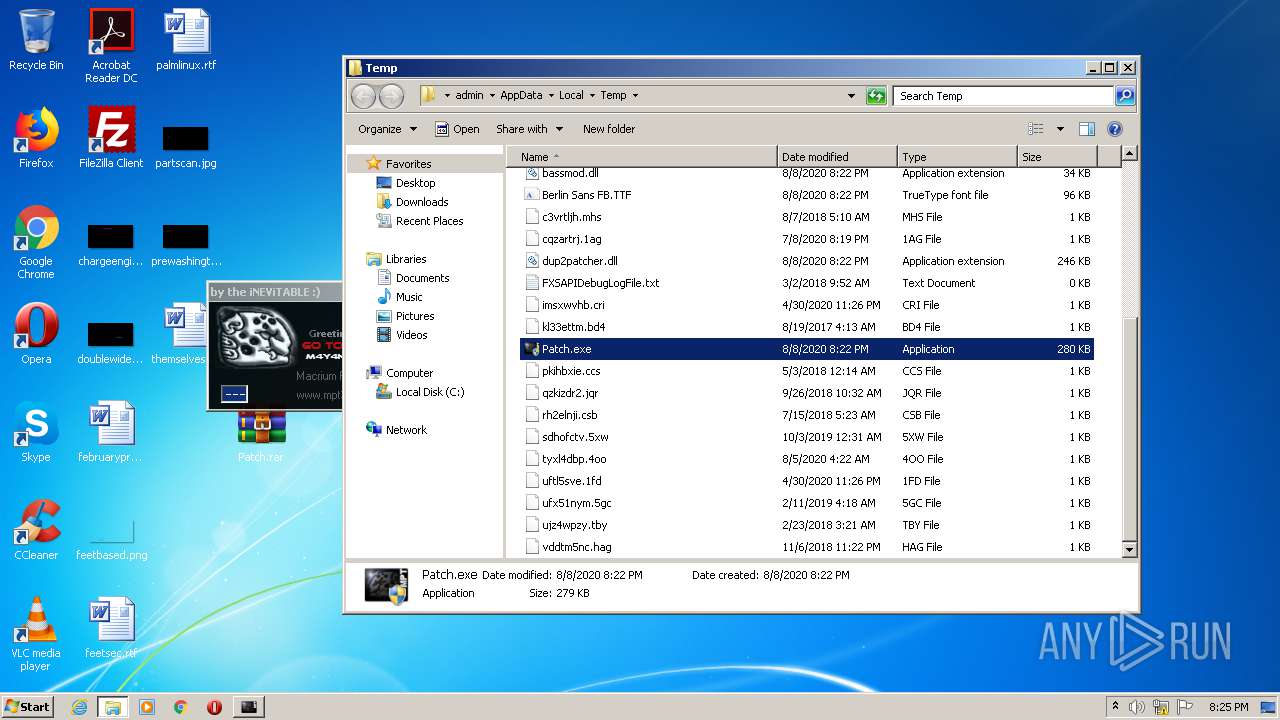
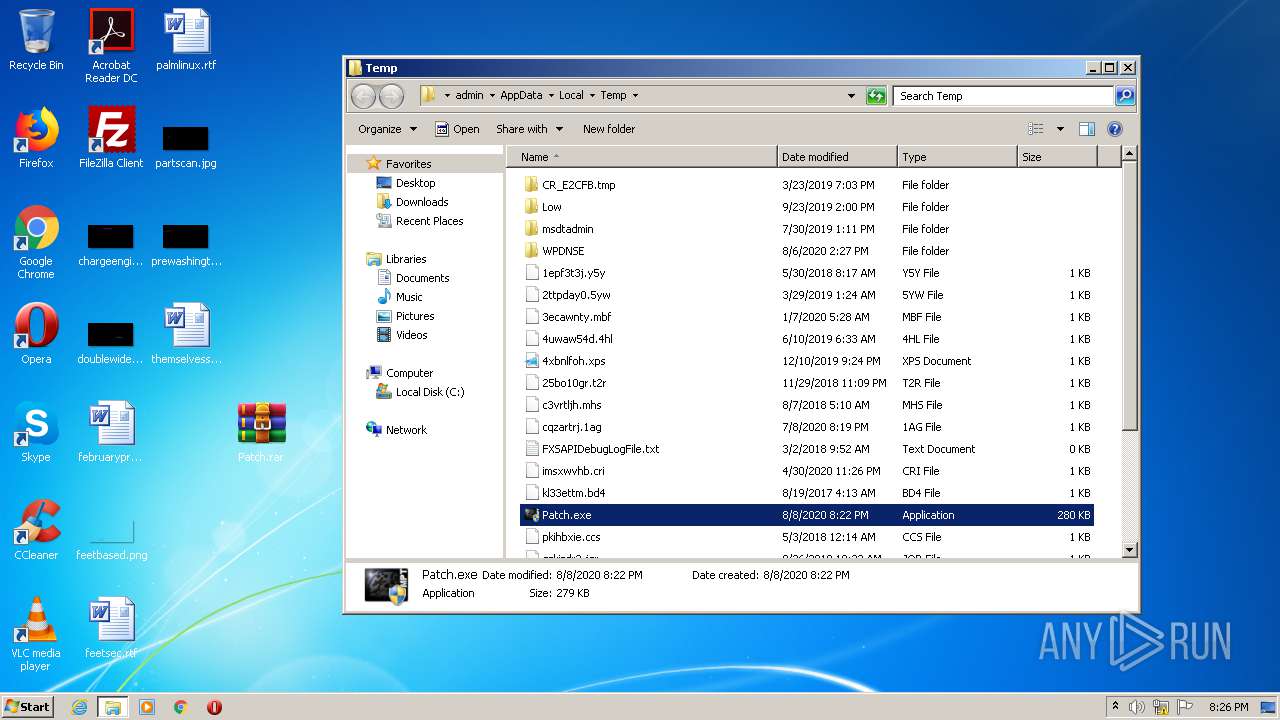
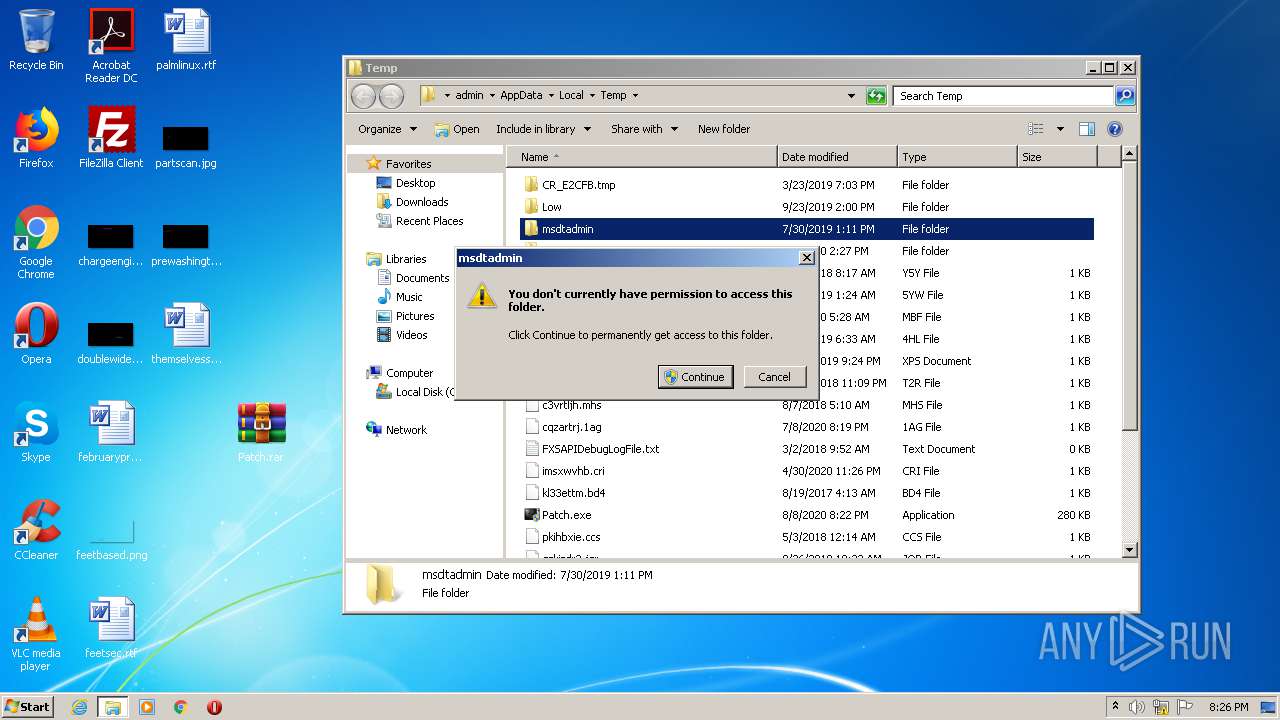
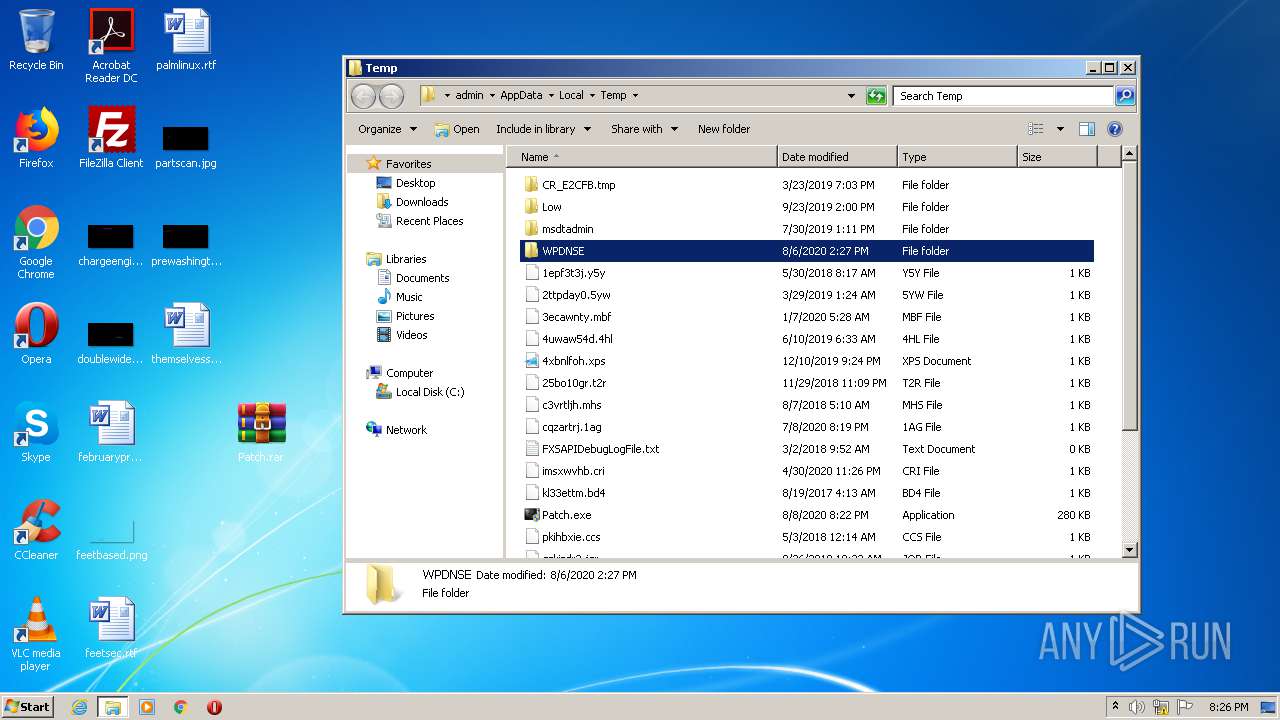
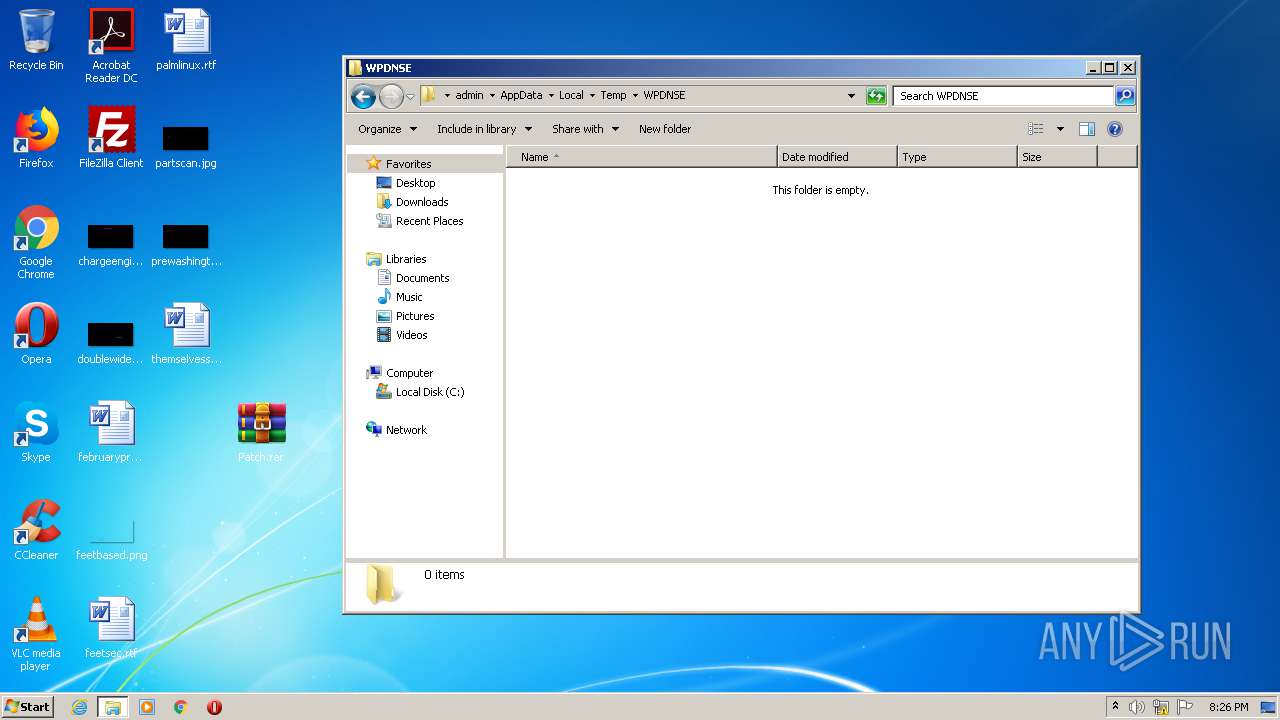
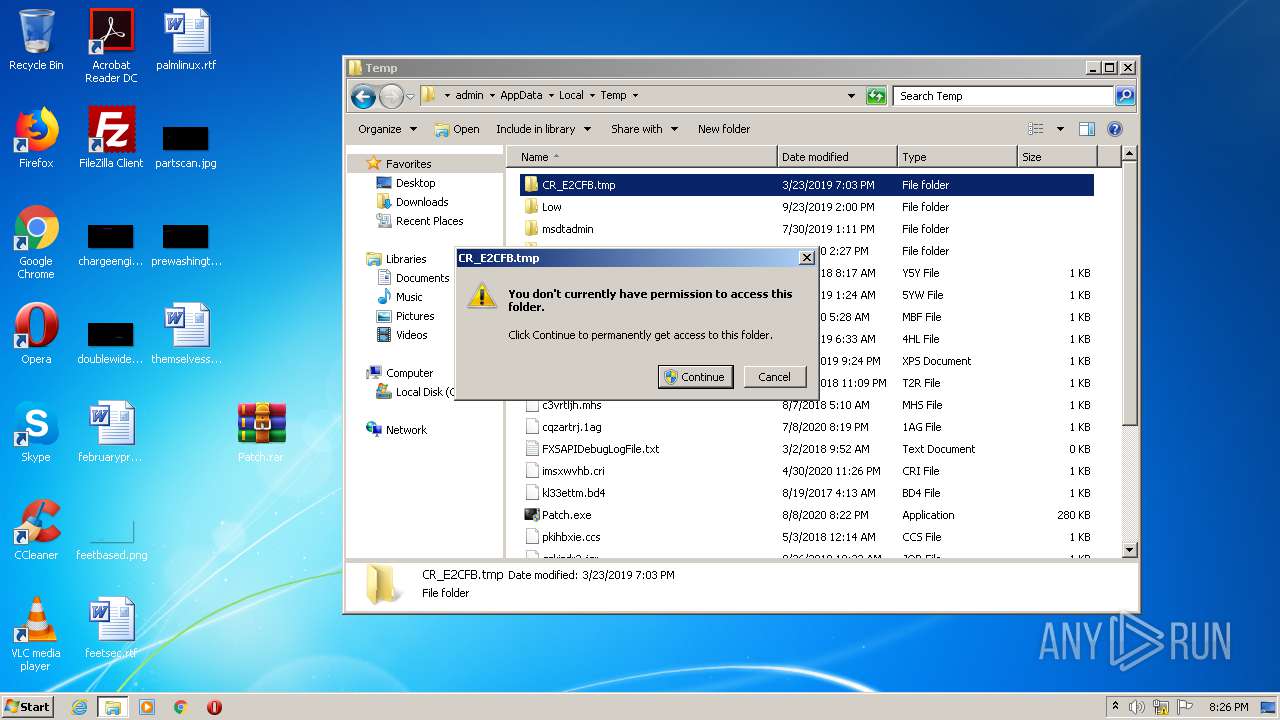
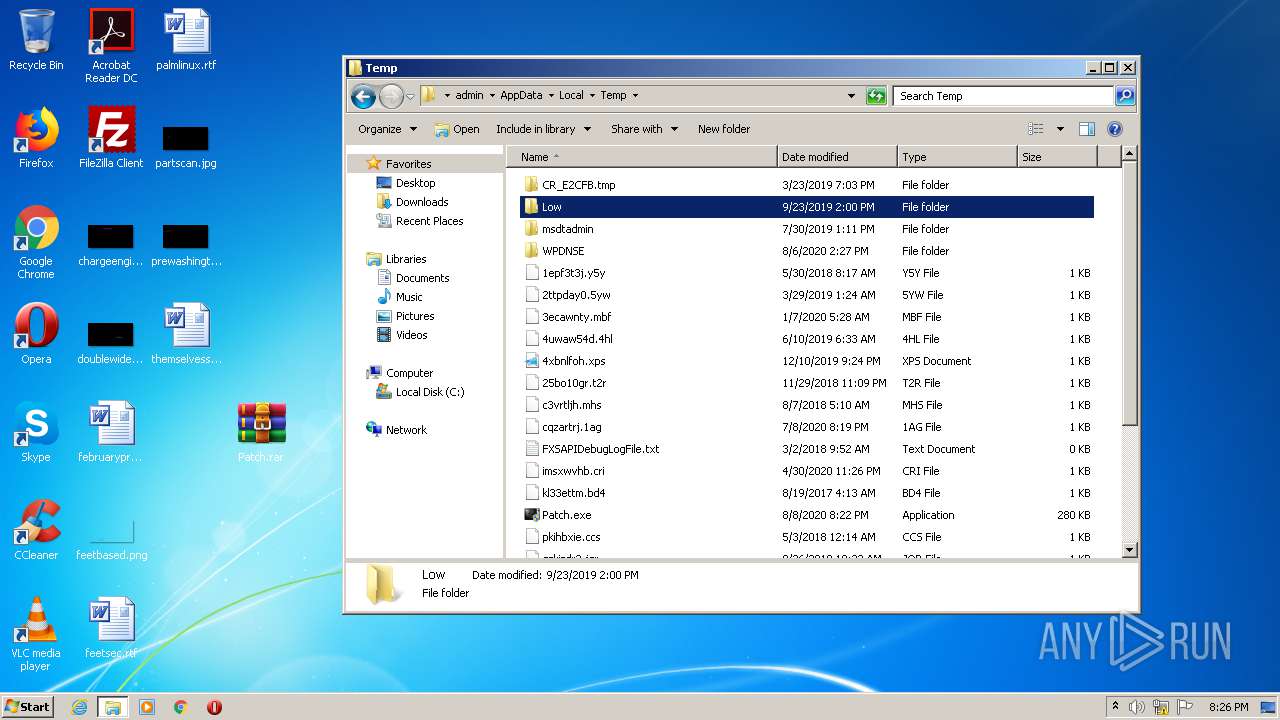
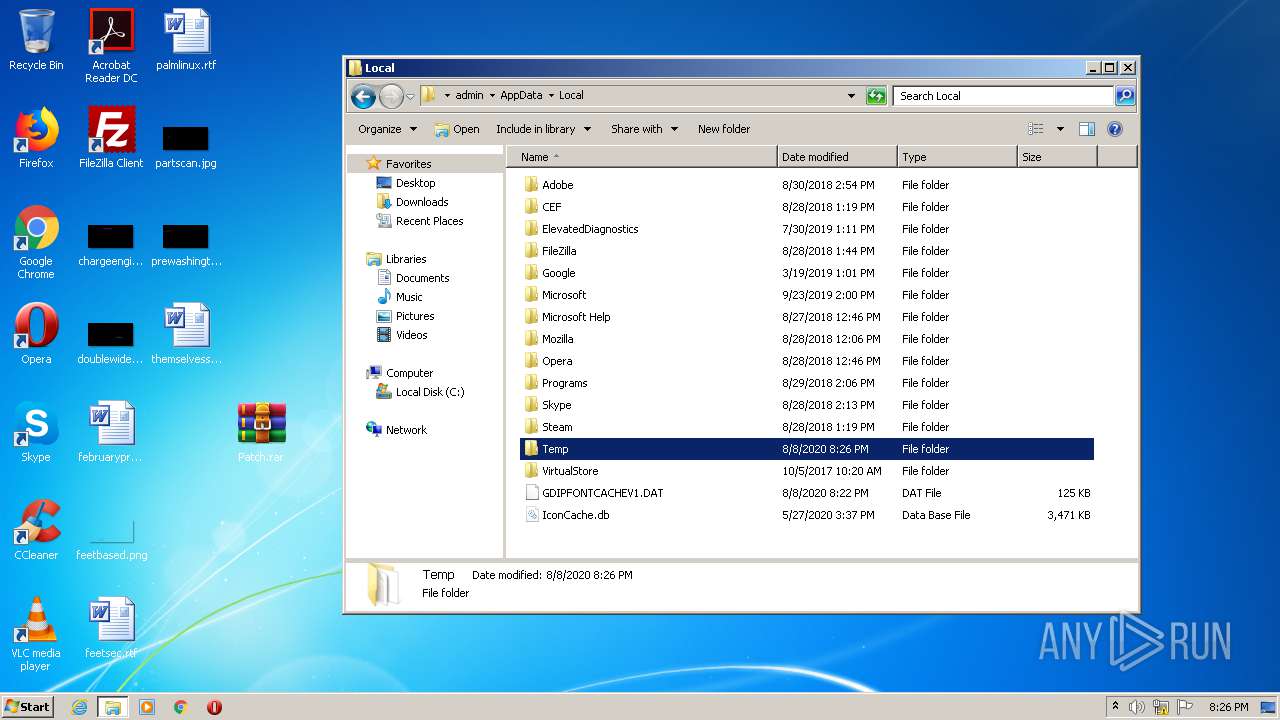
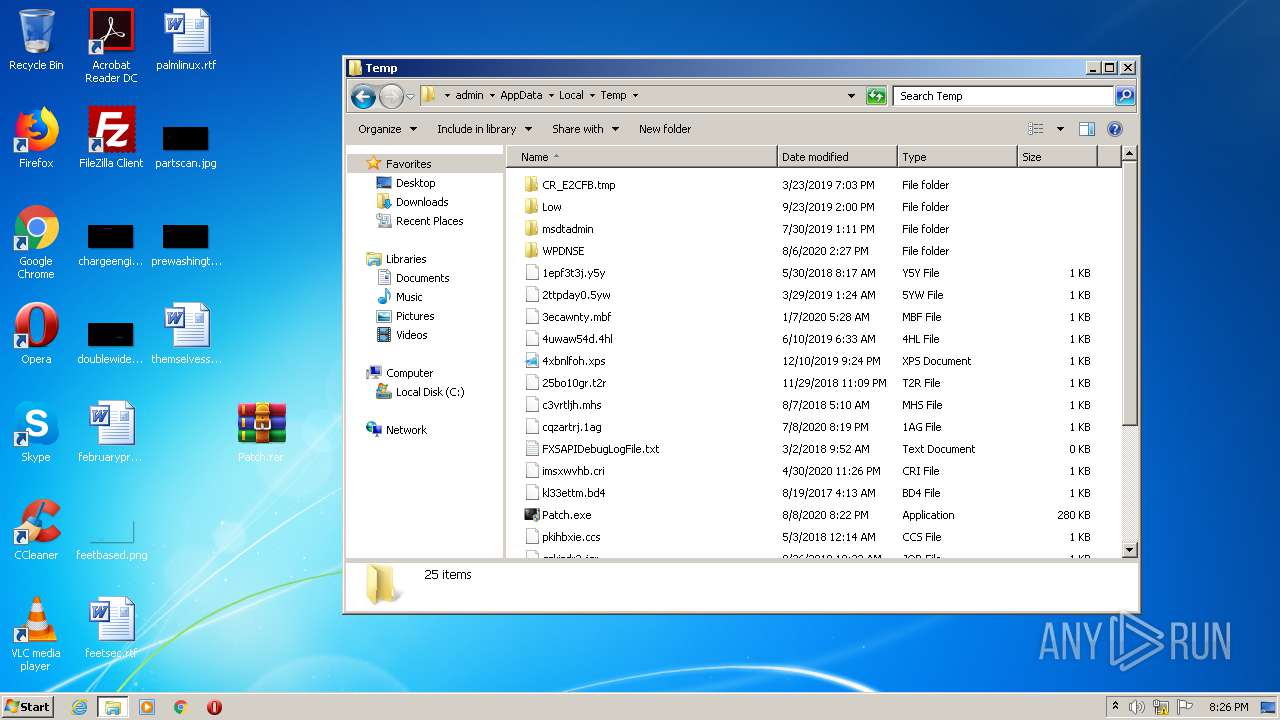
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3812 | Patch.exe | C:\Users\admin\AppData\Local\Temp\mptstop.bat | — | |
MD5:— | SHA256:— | |||
| 3812 | Patch.exe | C:\Users\admin\AppData\Local\Temp\mptstart.bat | — | |
MD5:— | SHA256:— | |||
| 3812 | Patch.exe | C:\Users\admin\AppData\Local\Temp\Berlin Sans FB.TTF | odttf | |
MD5:FE2027C27B6A24505F548C6FD2E1076D | SHA256:0B6044C72E67AAAE9C2AE3C8B4BB06D066FDBC02779C68E3883984ACBBE24CB8 | |||
| 3812 | Patch.exe | C:\Users\admin\AppData\Local\Temp\bassmod.dll | executable | |
MD5:E4EC57E8508C5C4040383EBE6D367928 | SHA256:8AD9E47693E292F381DA42DDC13724A3063040E51C26F4CA8E1F8E2F1DDD547F | |||
| 352 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 352 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Explorer\thumbcache_idx.db | binary | |
MD5:— | SHA256:— | |||
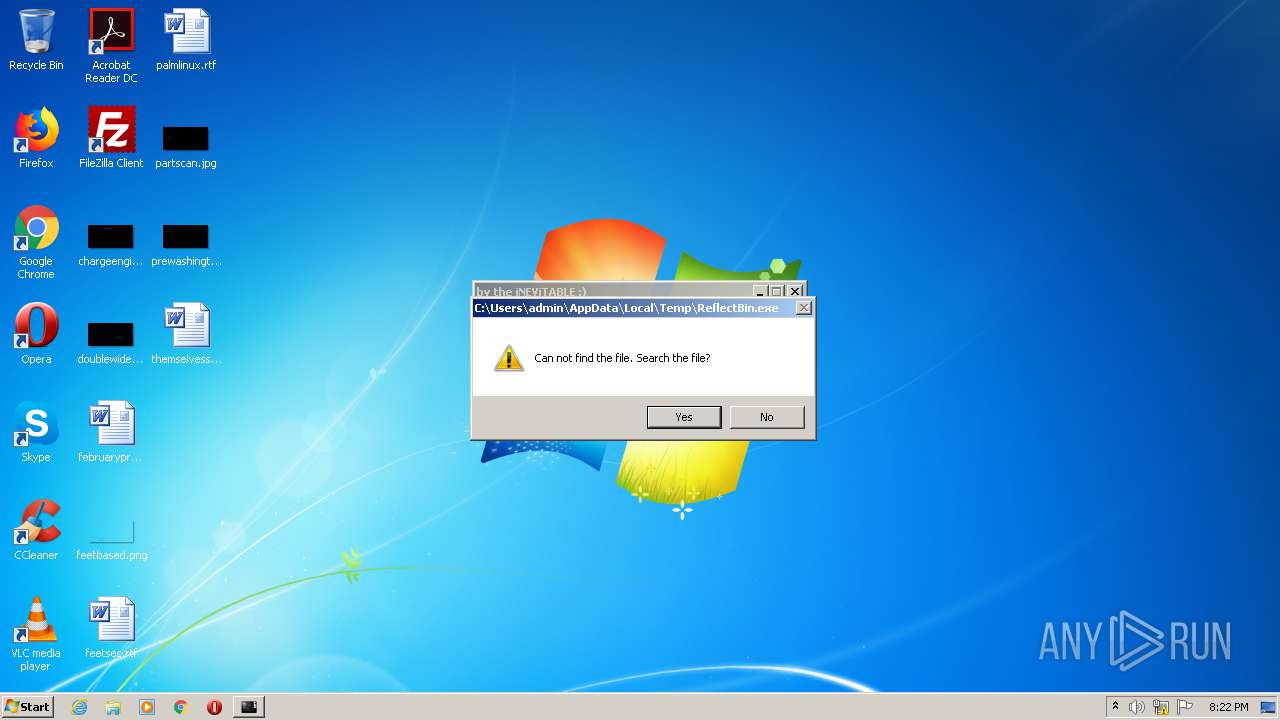
| 3812 | Patch.exe | C:\Users\admin\AppData\Local\Temp\64F4EA4C8142CAC73E06647D59A699D1.dll | executable | |
MD5:14DD1F05C6BD3CE4ACAB3EBDB9F0903B | SHA256:9A9296A1CC6C243E166B301346C4CD9DEC45028BBC80FDE3903B6C3740C6A239 | |||
| 3812 | Patch.exe | C:\Users\admin\AppData\Local\Temp\7CEB9B2A0E395BD64E74381485A106AF.dll | executable | |
MD5:5AFB011D9DB047BB0400C5C5CA2E450B | SHA256:125FC74E03435B3E0EDE0FF523D625D9C1FBB299286E9E2DBD1442E506150DA6 | |||
| 352 | explorer.exe | C:\Users\admin\Desktop\Patch.exe | executable | |
MD5:9EC06E71C956C414C278C67F69564CD9 | SHA256:FE511ACB318D59F80D753EE9300B4CF937E25C4B1980A07F60B45DC1C3B12C8D | |||
| 3812 | Patch.exe | C:\Users\admin\AppData\Local\Temp\dup2patcher.dll | executable | |
MD5:026477C8657C7B51FE625AE49A1B5ACF | SHA256:7947A5633484880E50C3BB5A7D2B6BC59993D289555F5ACD0414058AB0338DB8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report