| File name: | 0bd6cfa2-287f-f639-d046-f5e5e0f9c79a.eml |
| Full analysis: | https://app.any.run/tasks/006a97d4-ecad-4a46-9af8-3ba54efaf83f |
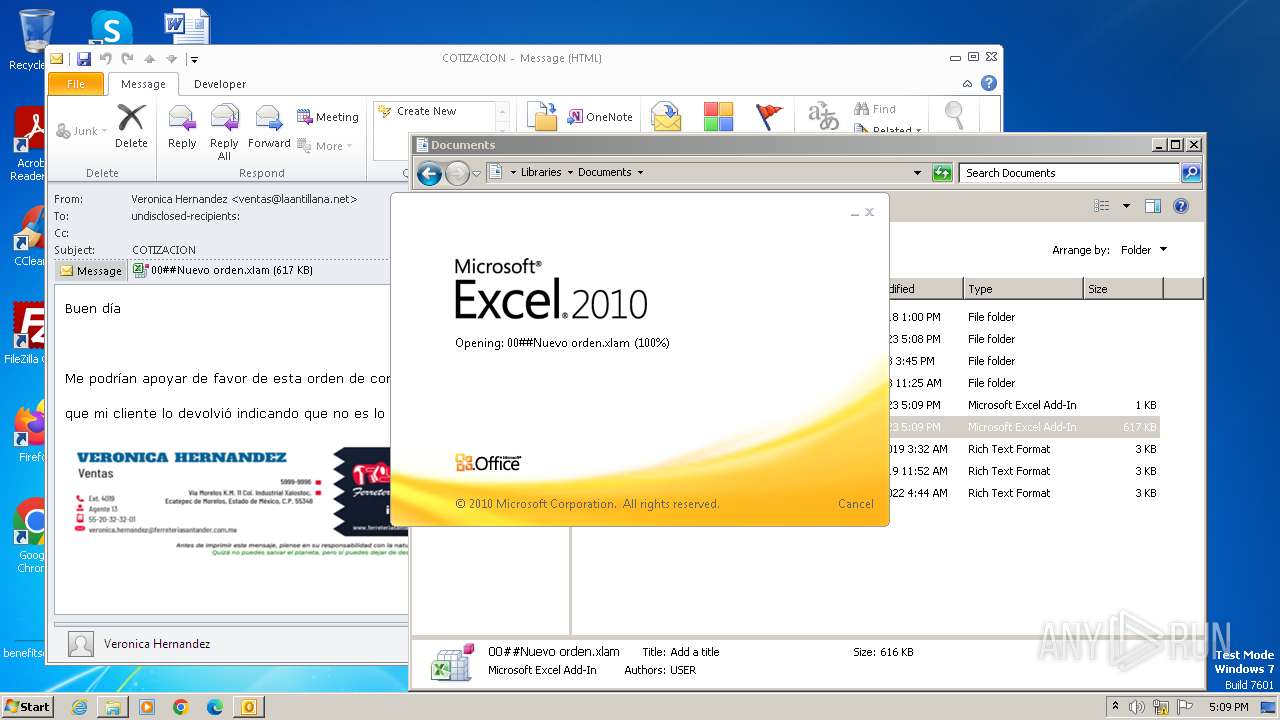
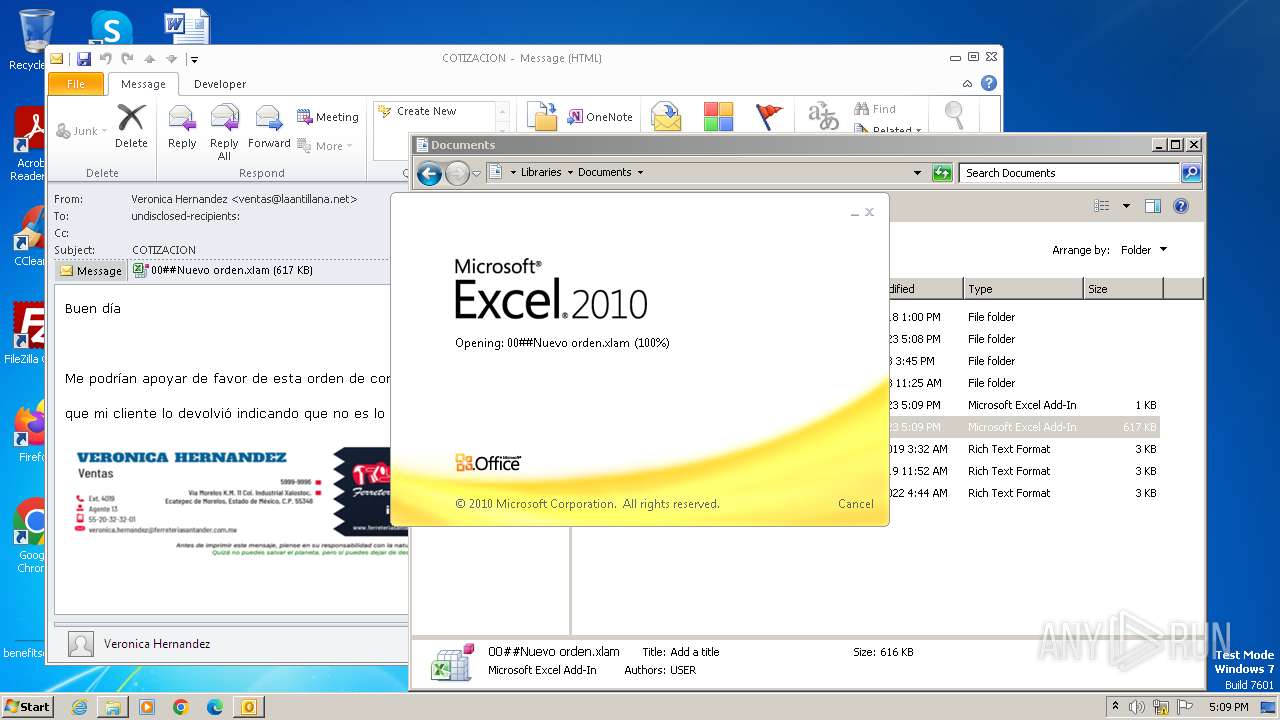
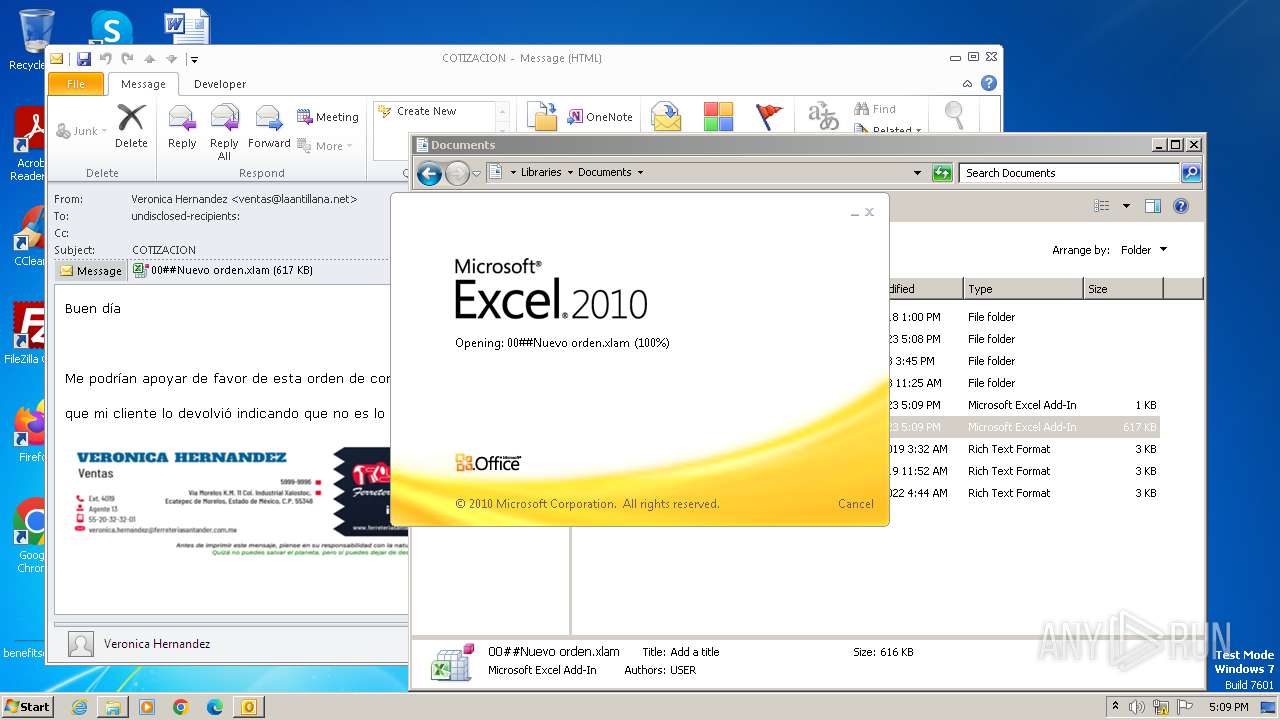
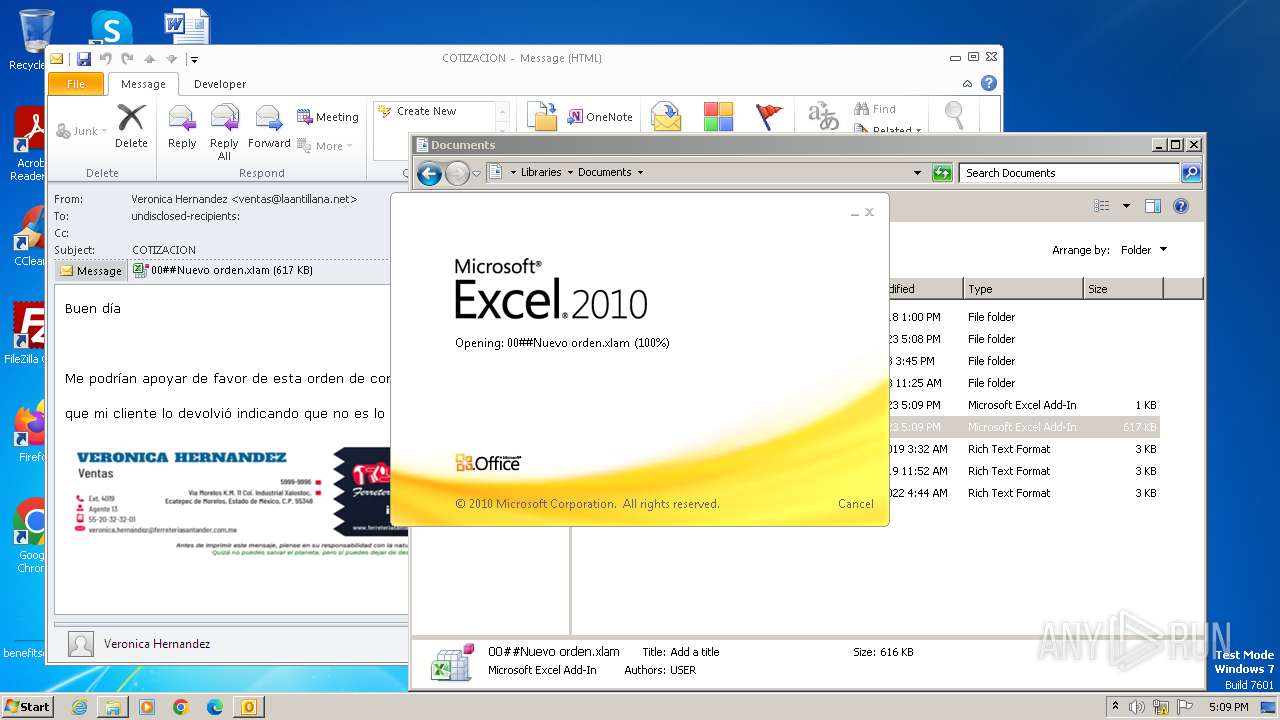
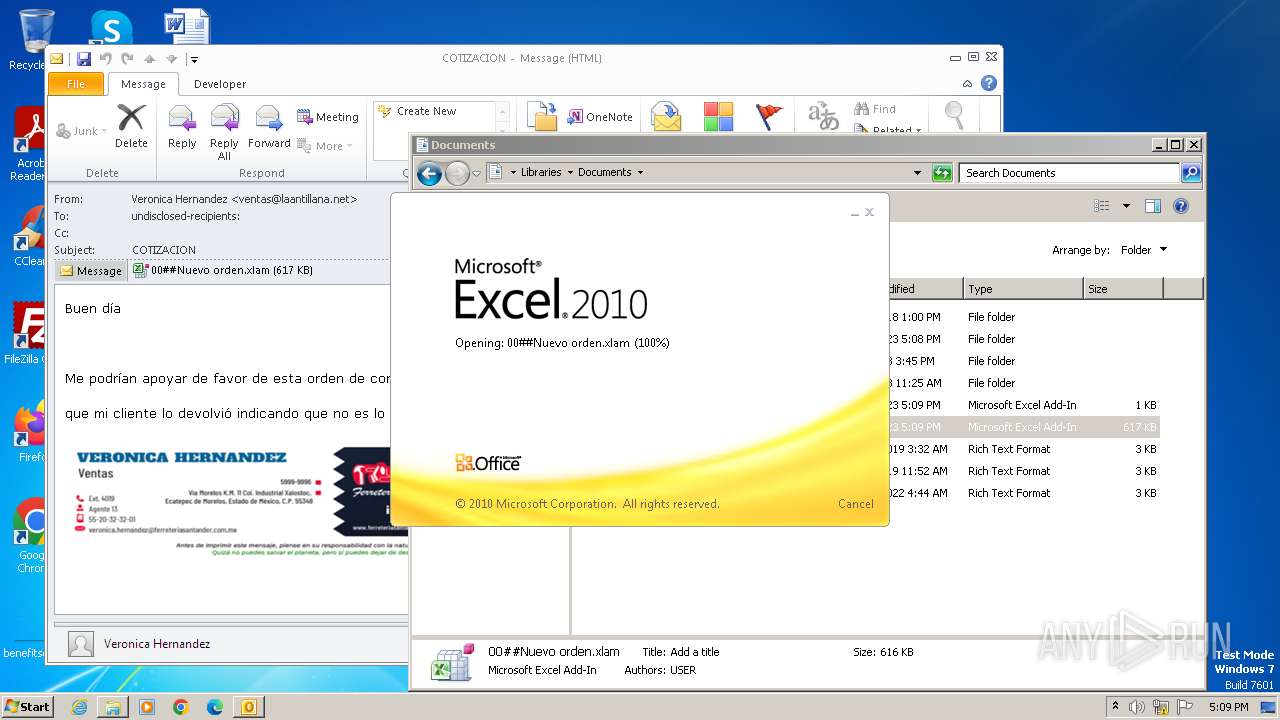
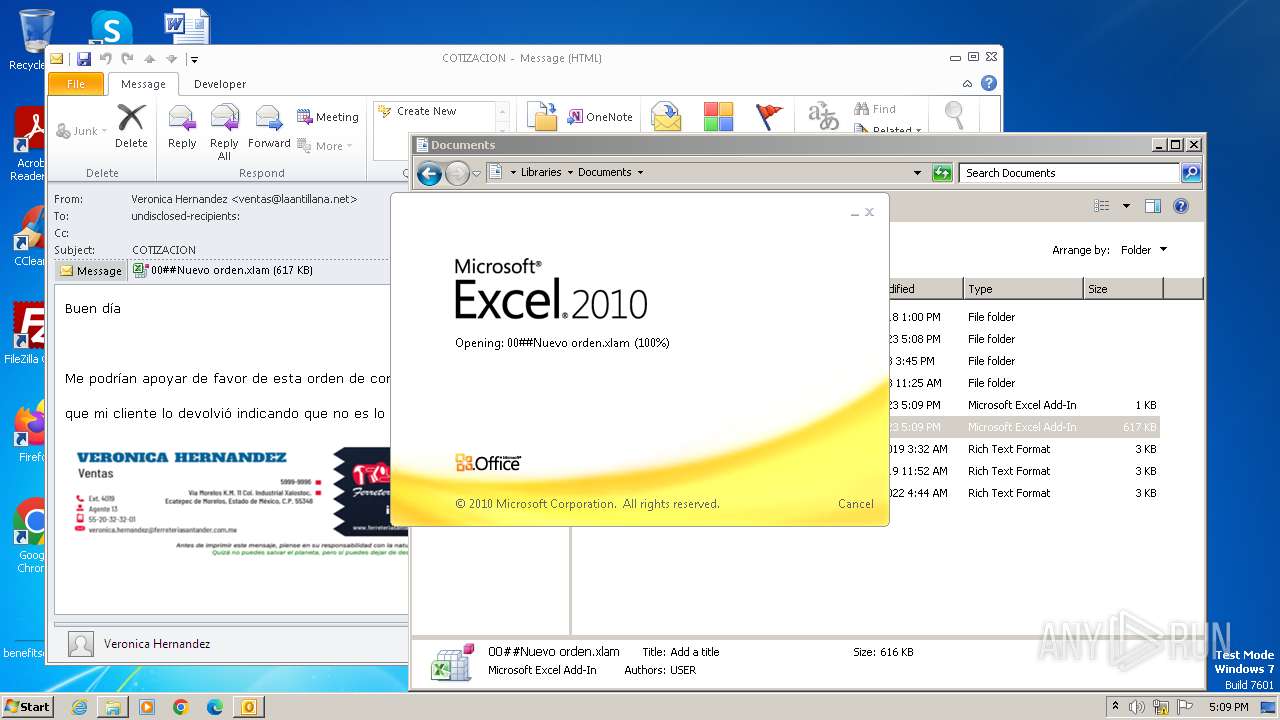
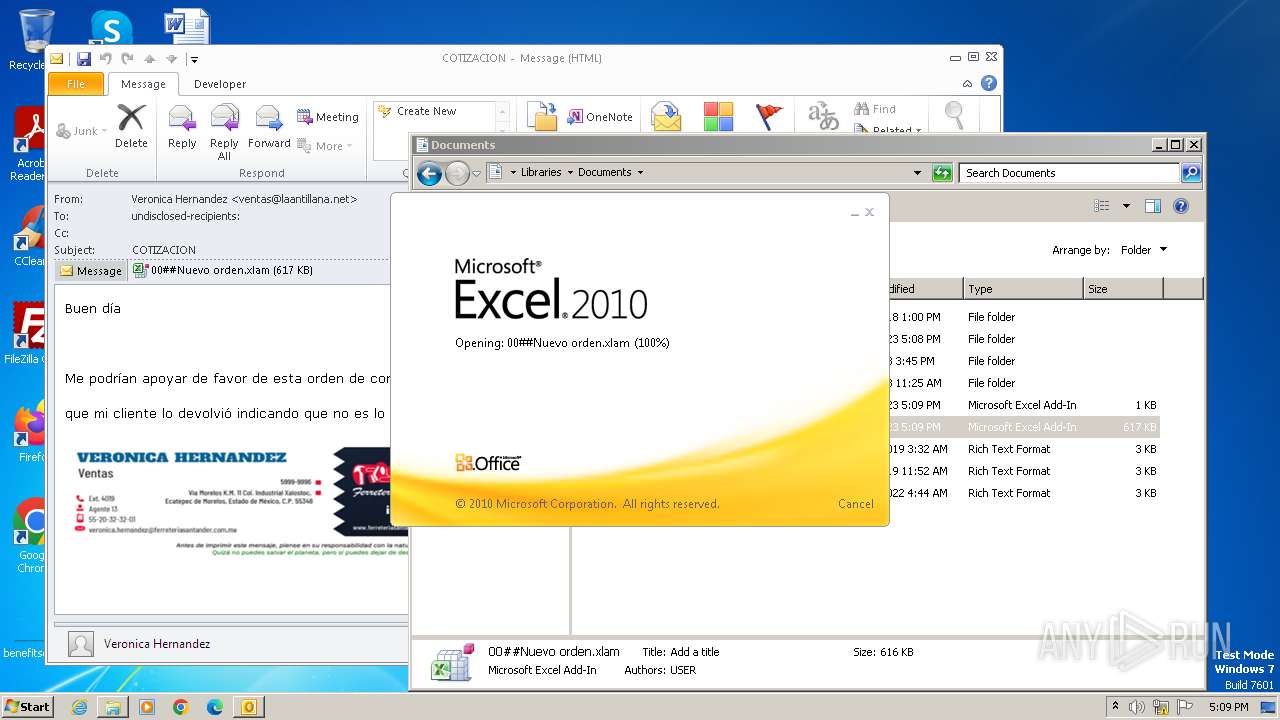
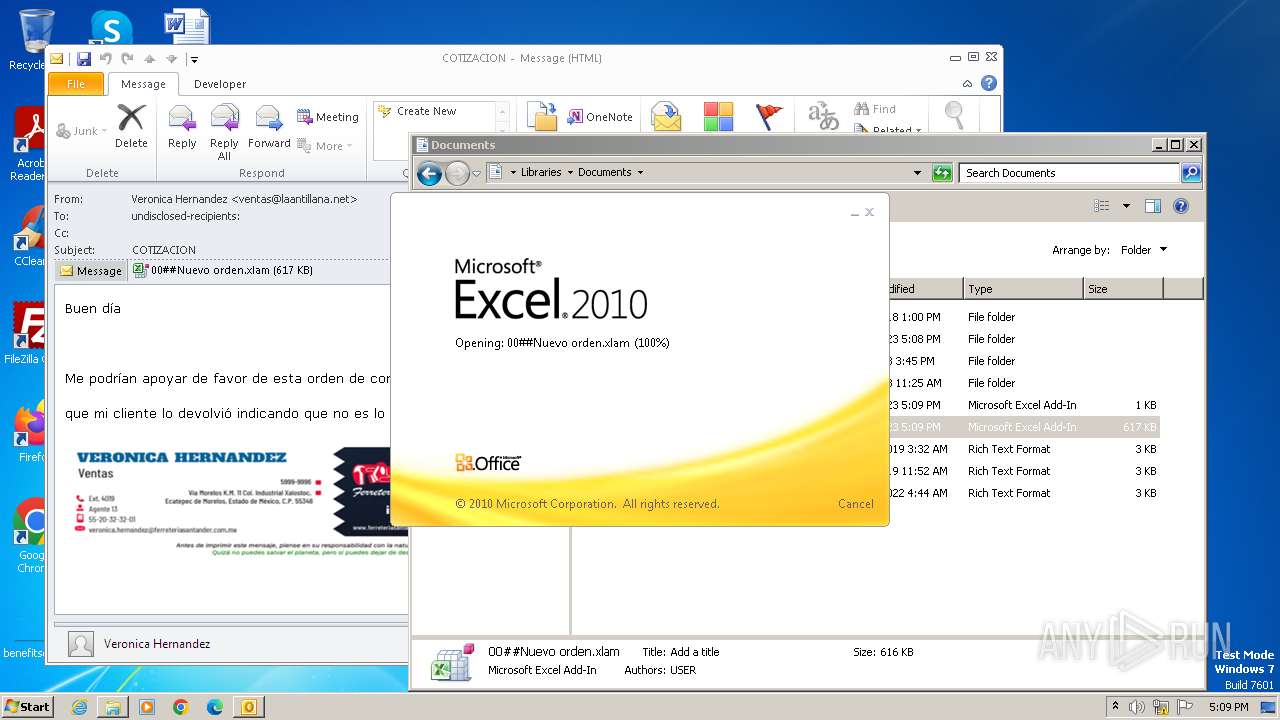
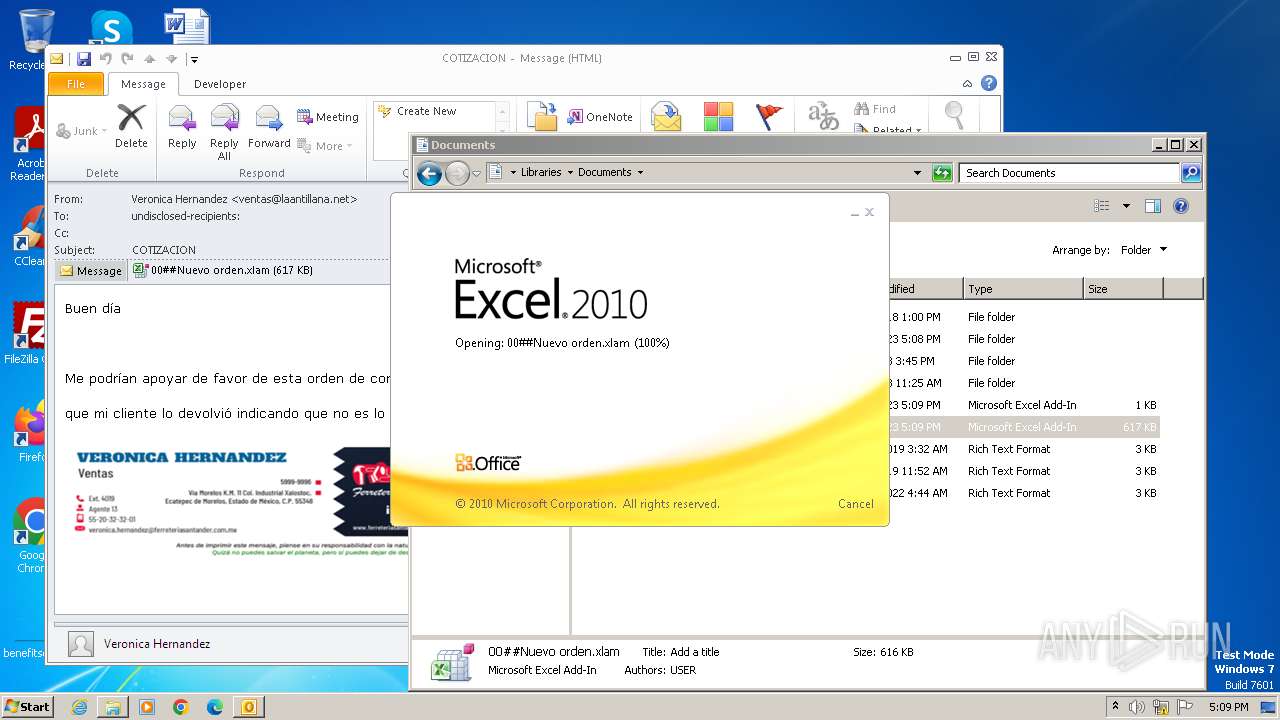
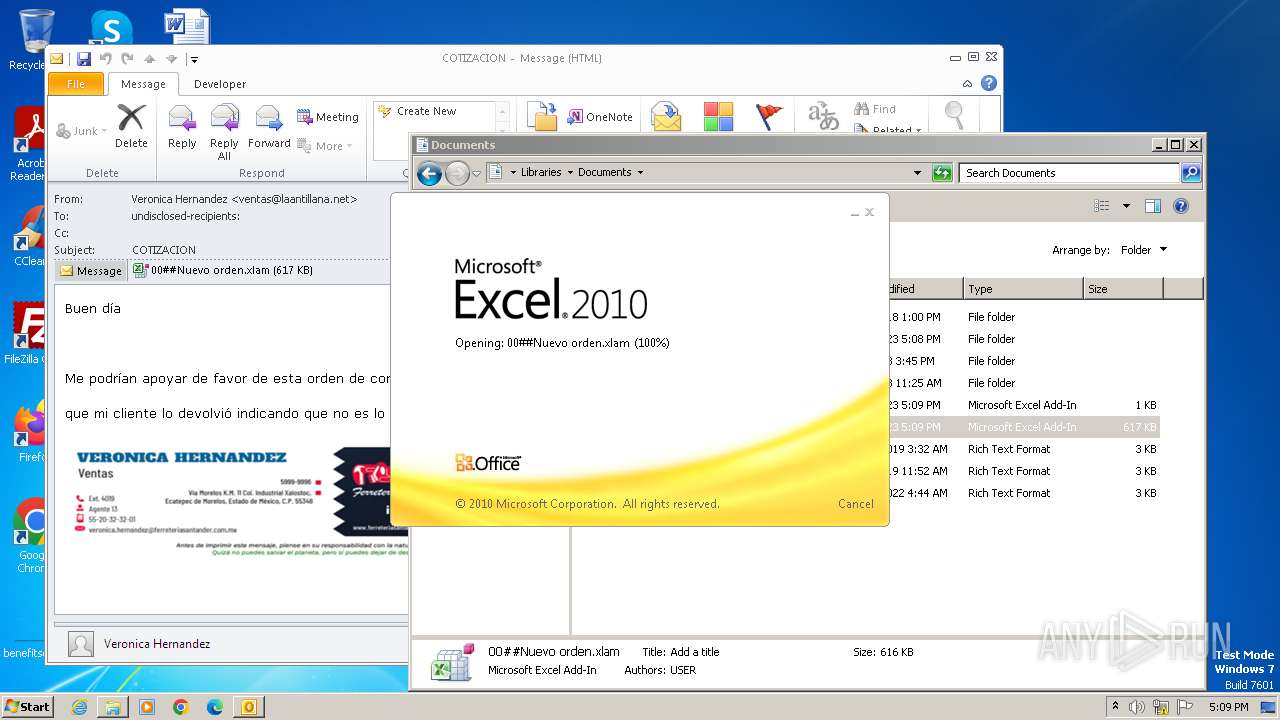
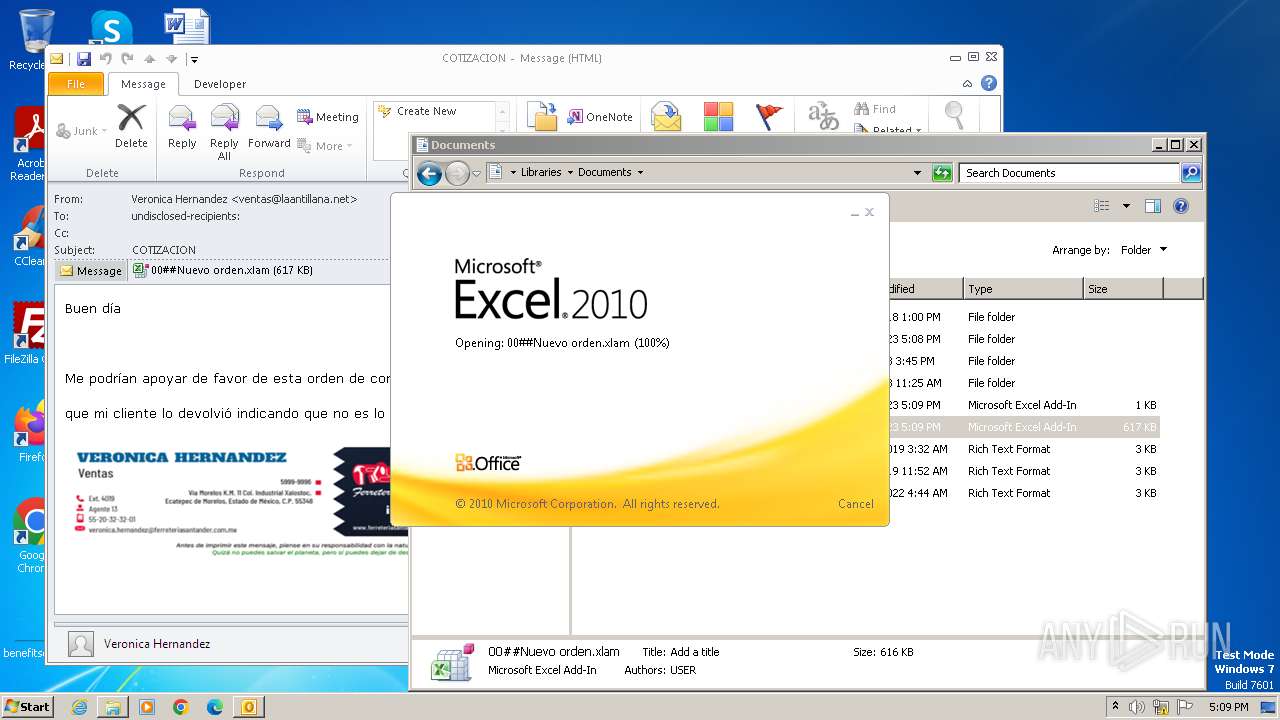
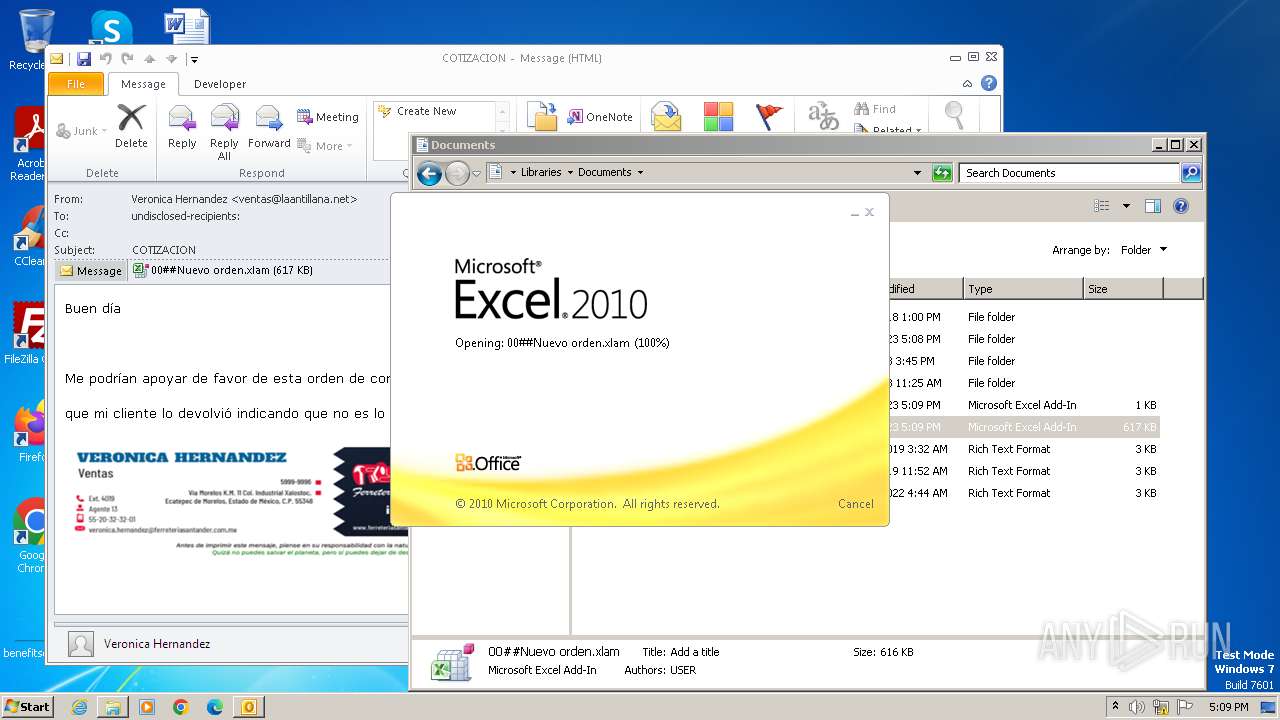
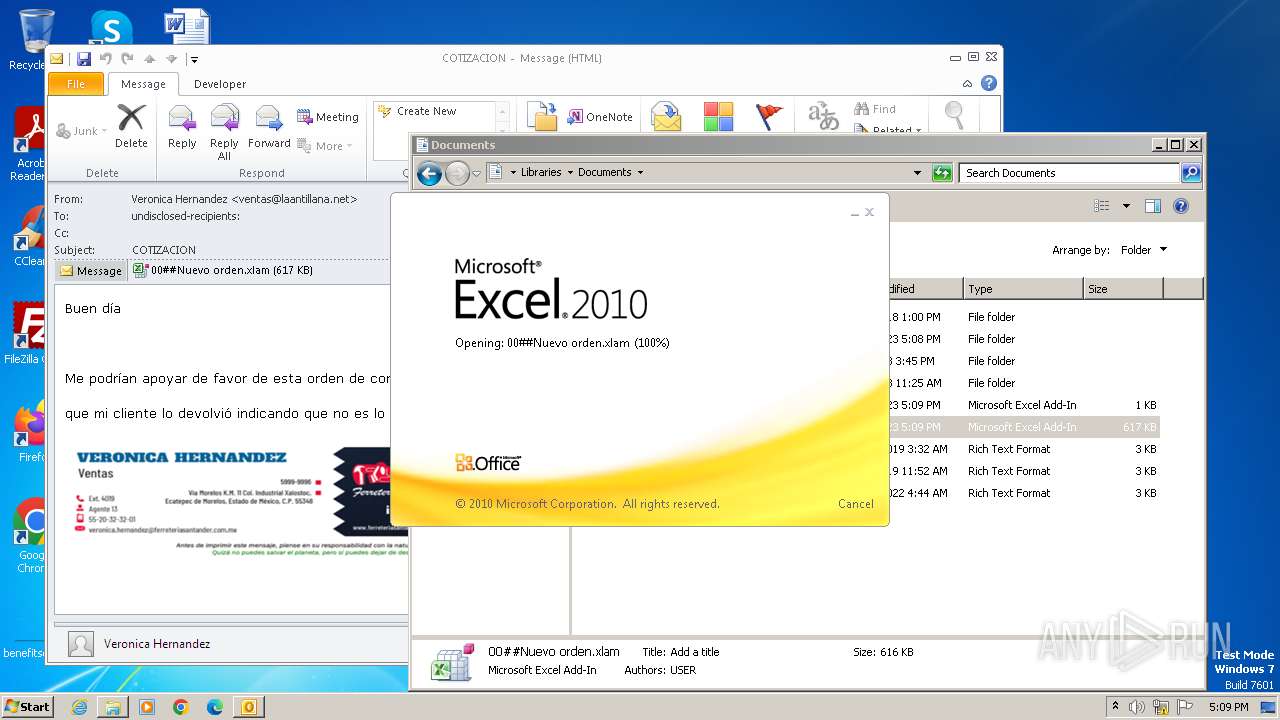
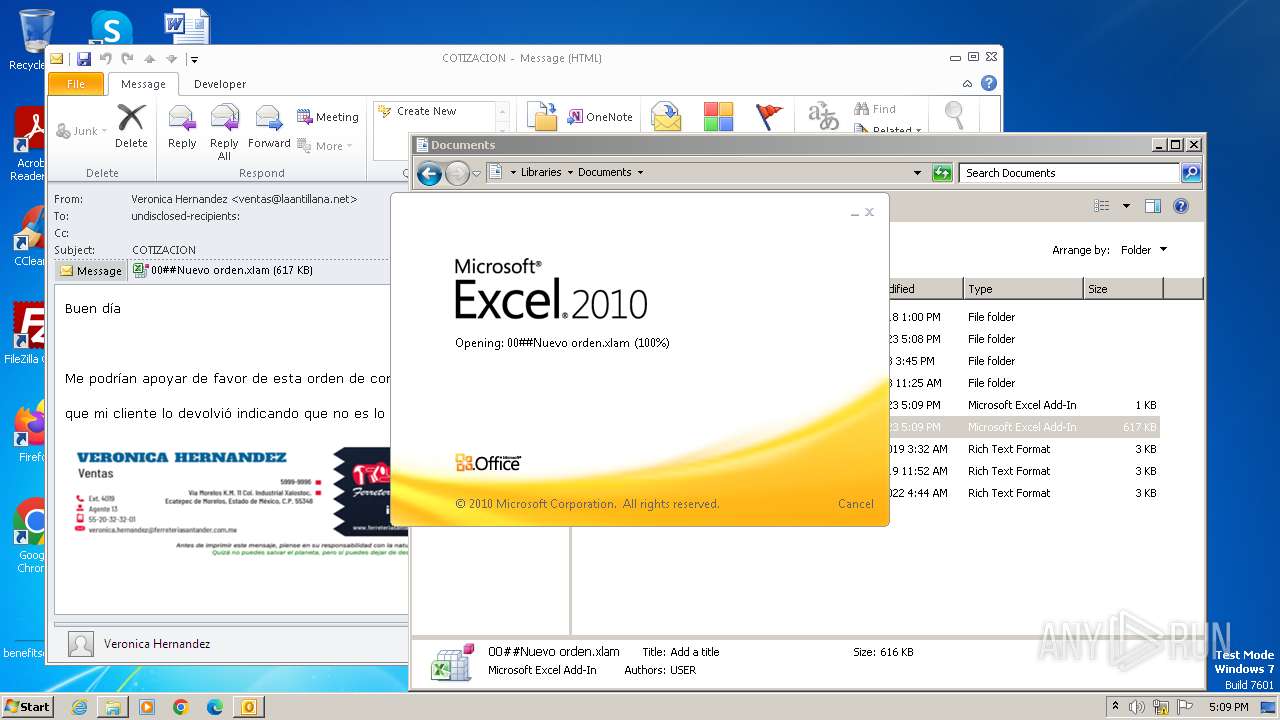
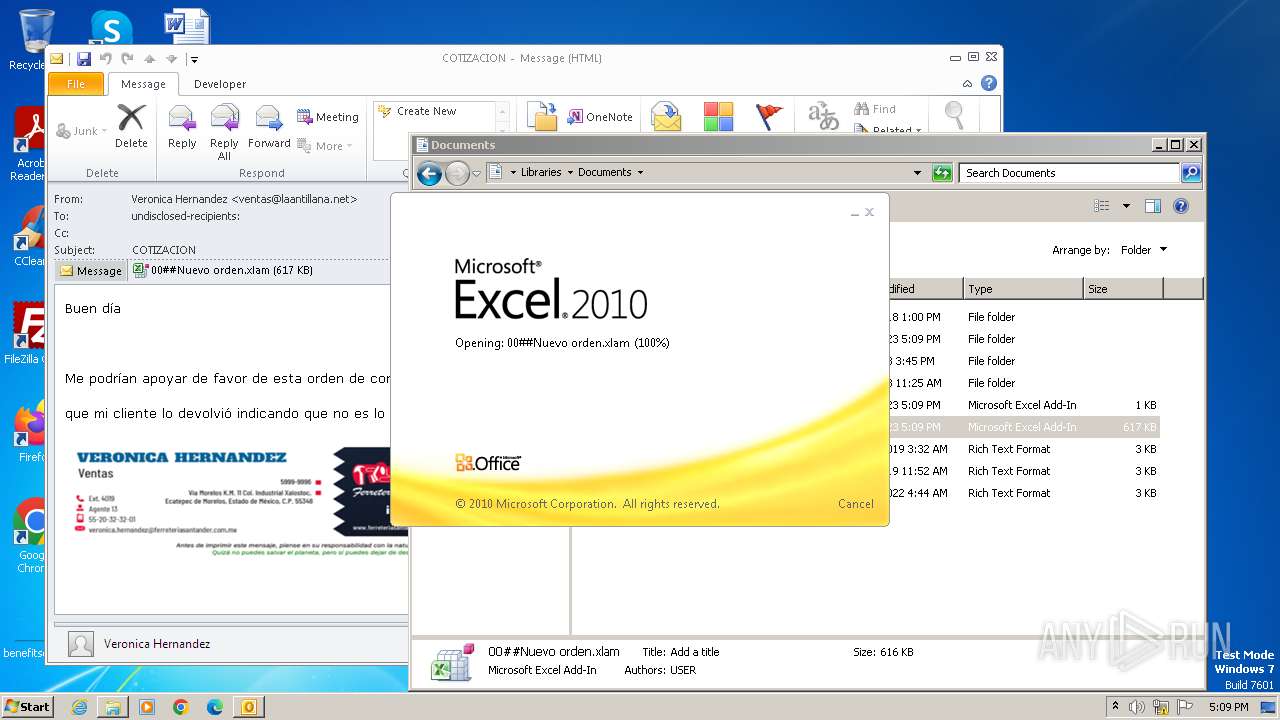
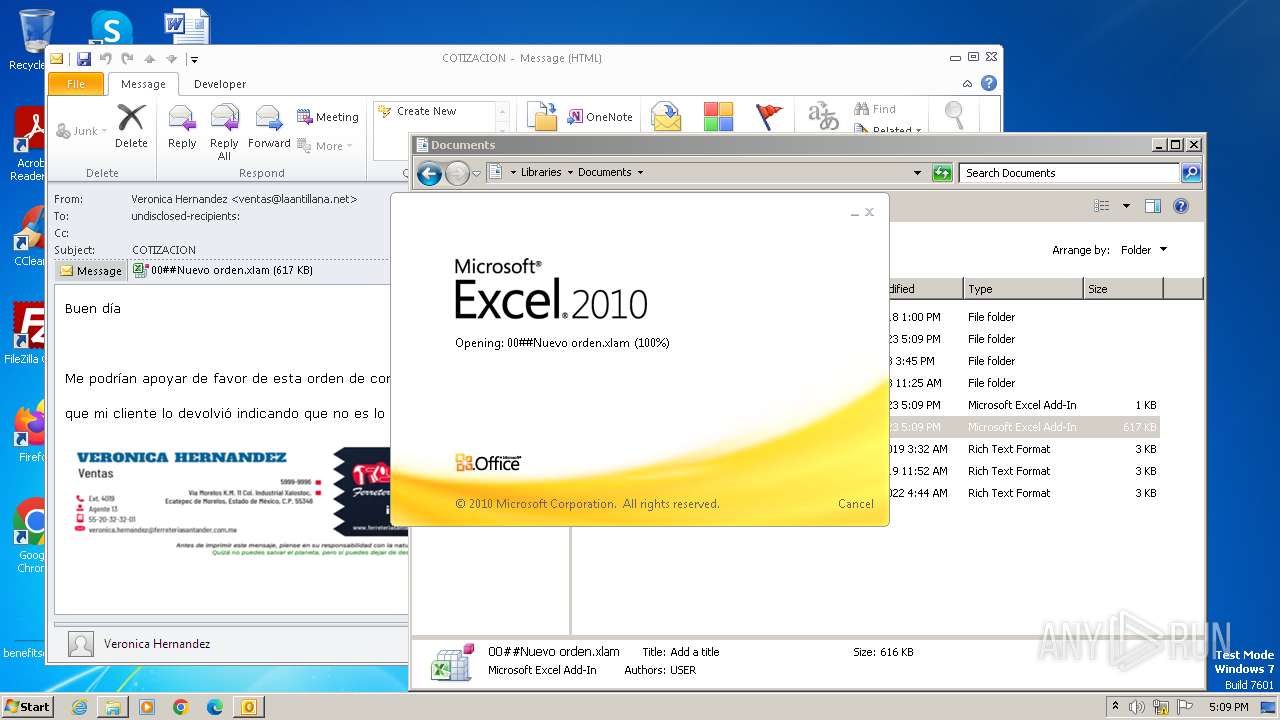
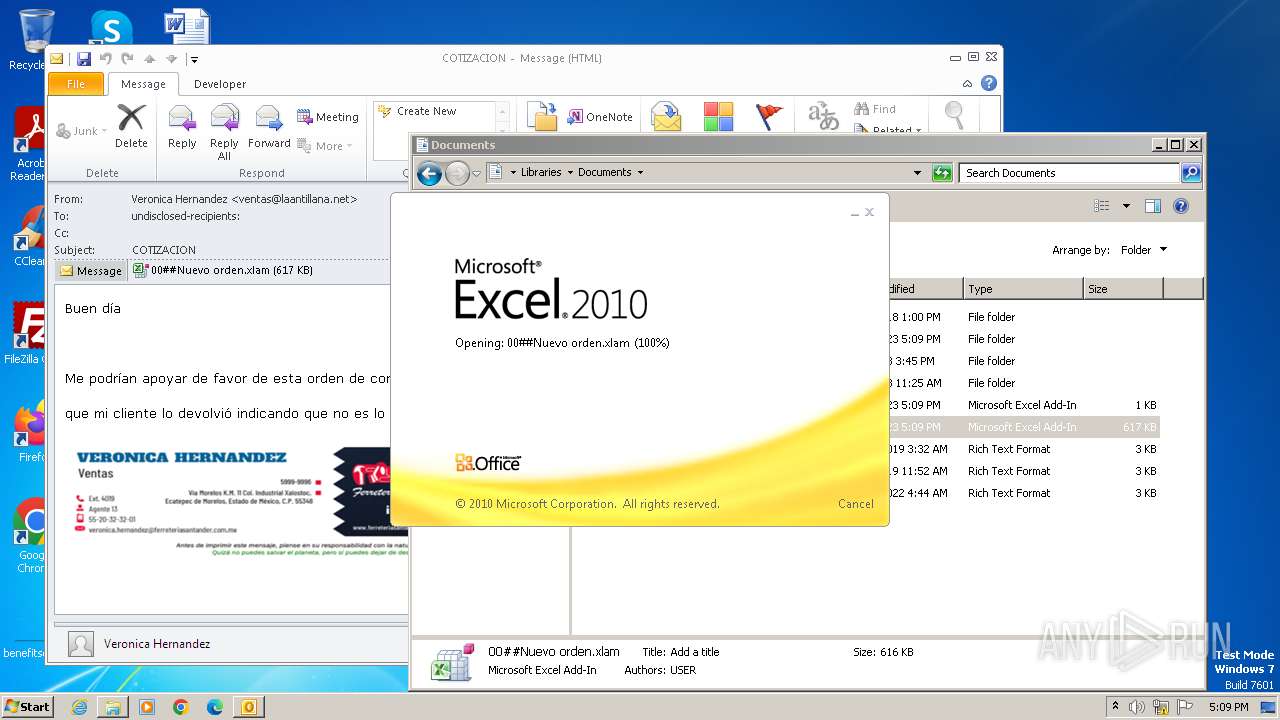
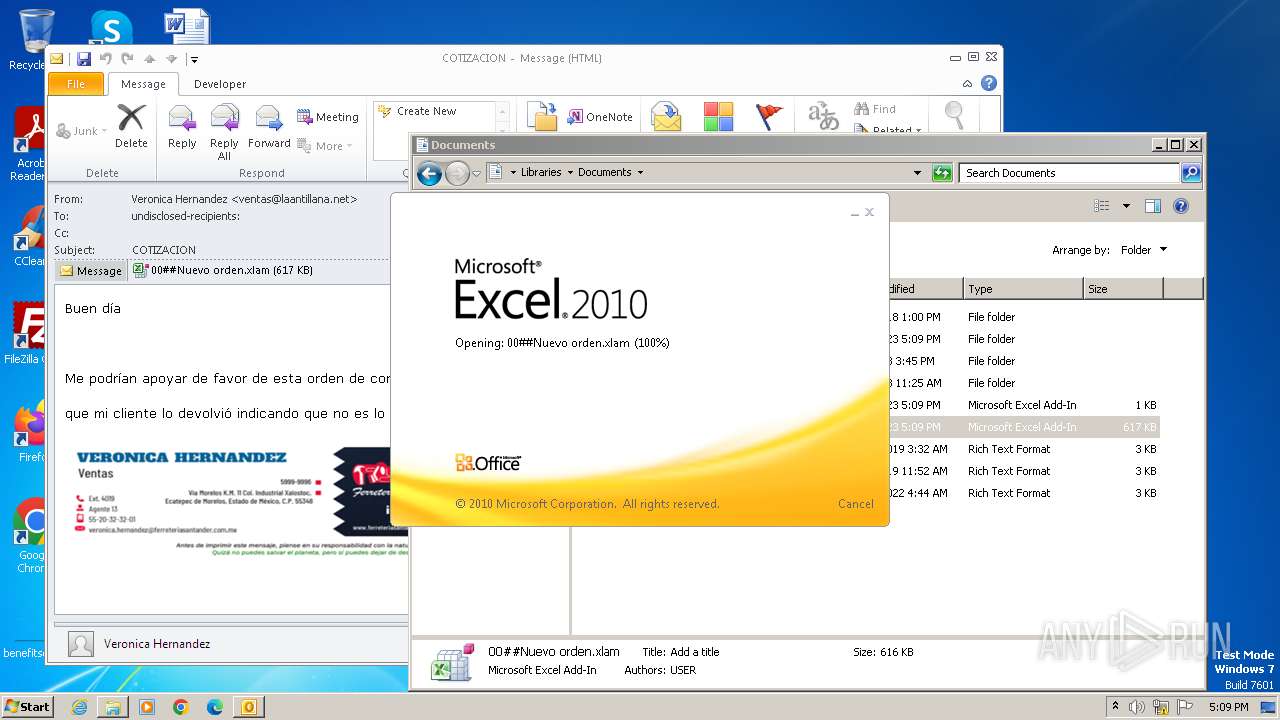
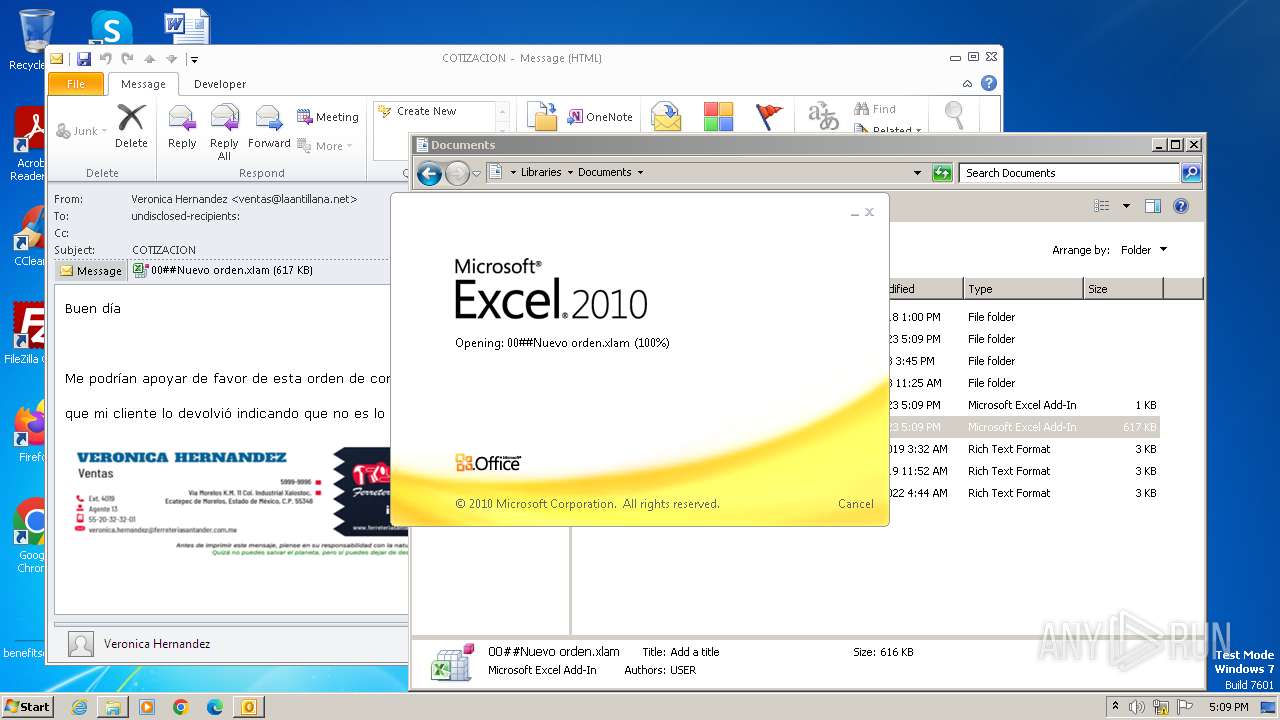
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2023, 17:08:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, UTF-8 Unicode text, with very long lines, with CRLF line terminators |
| MD5: | FC5BC21E22C1C018F70E889CE7360503 |
| SHA1: | D983DCA0650520C91434AC3F3EB1AA9FC9496035 |
| SHA256: | FE4EE8302F14D88A8A277B2175CBDBC46F5AFA8261AC078976A8339C6D8C3FA7 |
| SSDEEP: | 24576:Ib6H6aJavfJa4hnfRT0cCXQfltC2IiCjFEHicZXtQAONBEPMHu7KpSMi:yIKcKfcAf/RLq+Vi/aE3gJ |
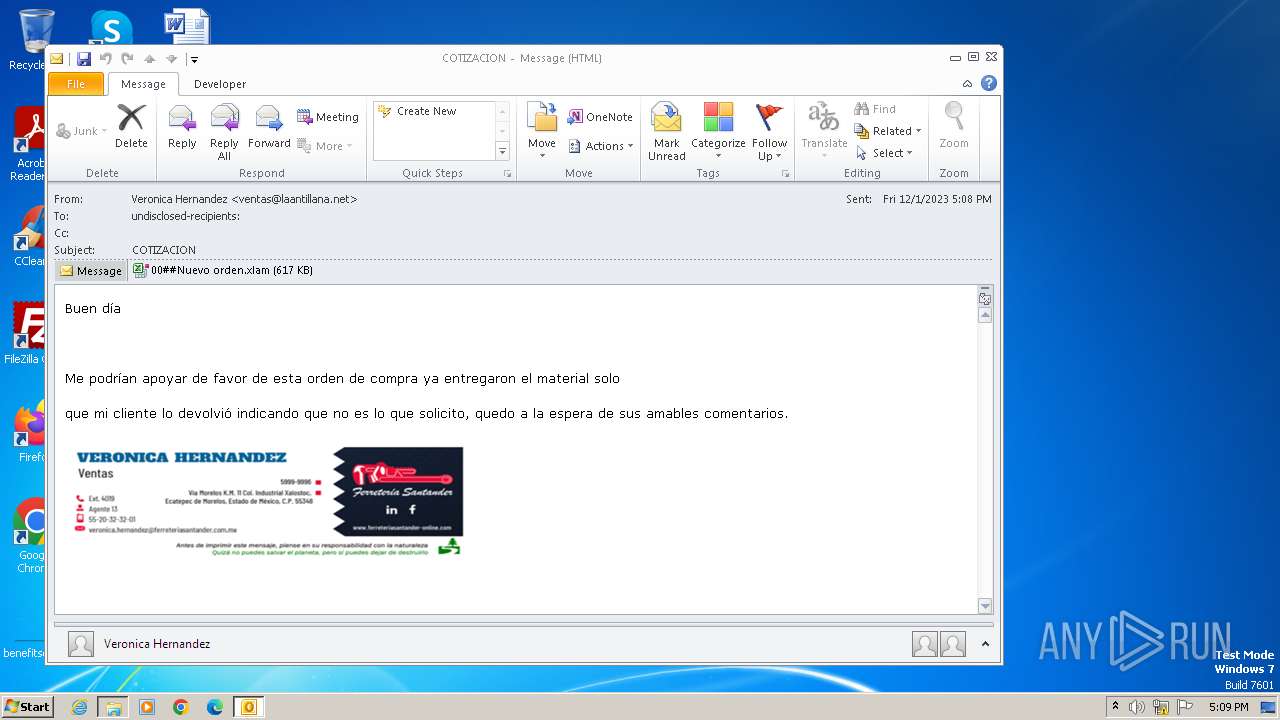
MALICIOUS
Suspicious connection from the Equation Editor
- EQNEDT32.EXE (PID: 3252)
SUSPICIOUS
Reads the Internet Settings
- EQNEDT32.EXE (PID: 3252)
INFO
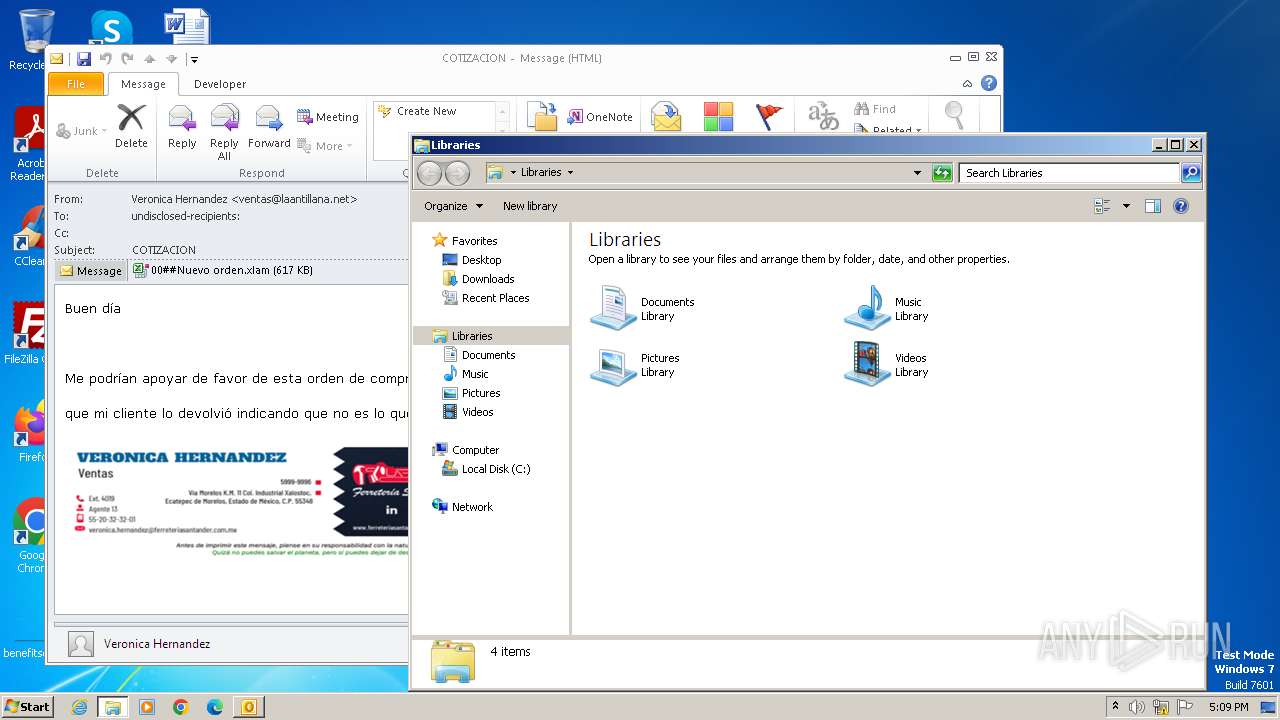
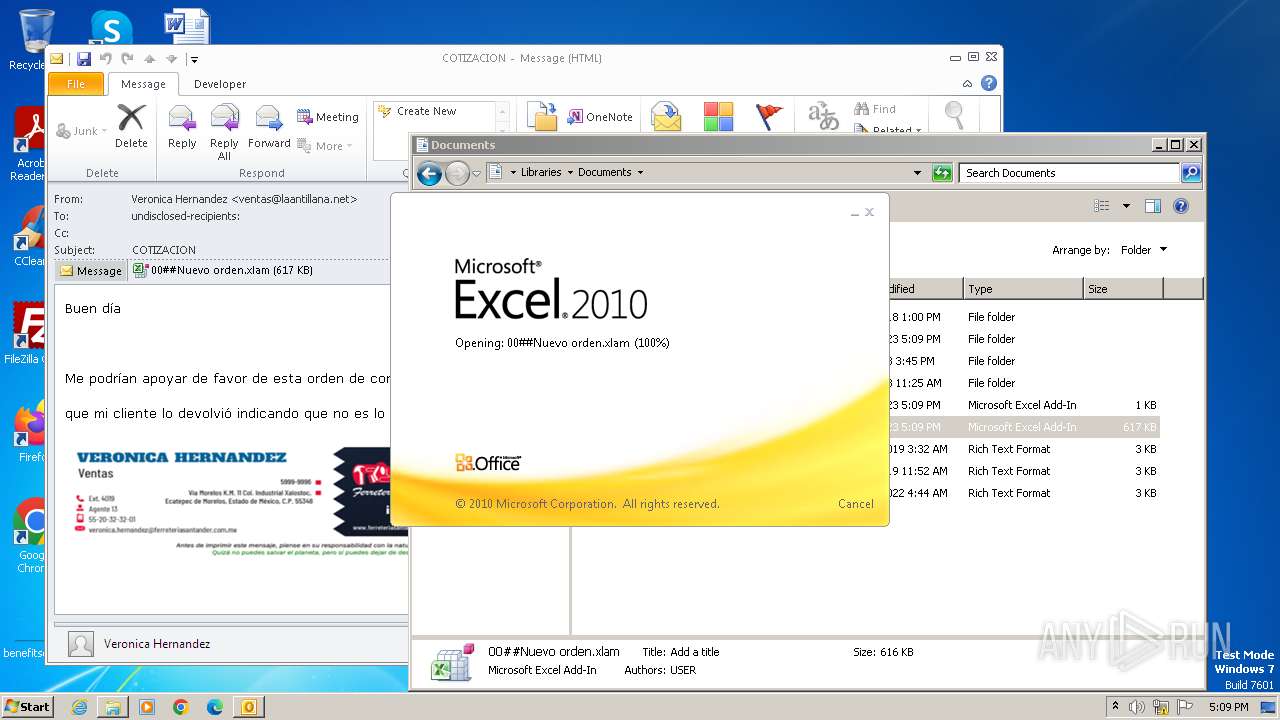
The process uses the downloaded file
- OUTLOOK.EXE (PID: 844)
Manual execution by a user
- explorer.exe (PID: 3964)
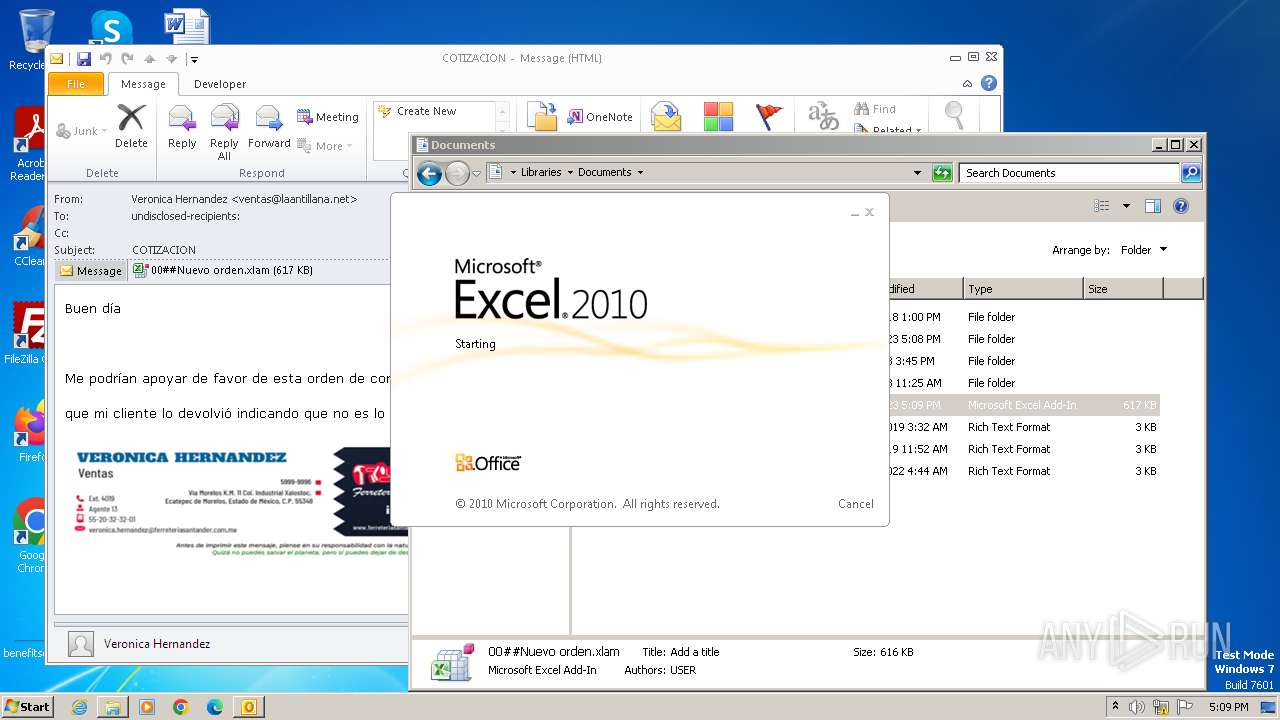
- EXCEL.EXE (PID: 3288)
Checks supported languages
- EQNEDT32.EXE (PID: 3252)
Checks proxy server information
- EQNEDT32.EXE (PID: 3252)
Reads the computer name
- EQNEDT32.EXE (PID: 3252)
Reads the machine GUID from the registry
- EQNEDT32.EXE (PID: 3252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
44
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 844 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\0bd6cfa2-287f-f639-d046-f5e5e0f9c79a.eml" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3252 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 3288 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\microsoft office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3964 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
7 042
Read events
6 585
Write events
424
Delete events
33
Modification events
| (PID) Process: | (844) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (844) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: On | |||
| (PID) Process: | (844) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: On | |||
| (PID) Process: | (844) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: On | |||
| (PID) Process: | (844) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: On | |||
| (PID) Process: | (844) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: On | |||
| (PID) Process: | (844) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: On | |||
| (PID) Process: | (844) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: On | |||
| (PID) Process: | (844) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: On | |||
| (PID) Process: | (844) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: On | |||
Executable files
1
Suspicious files
7
Text files
5
Unknown types
0
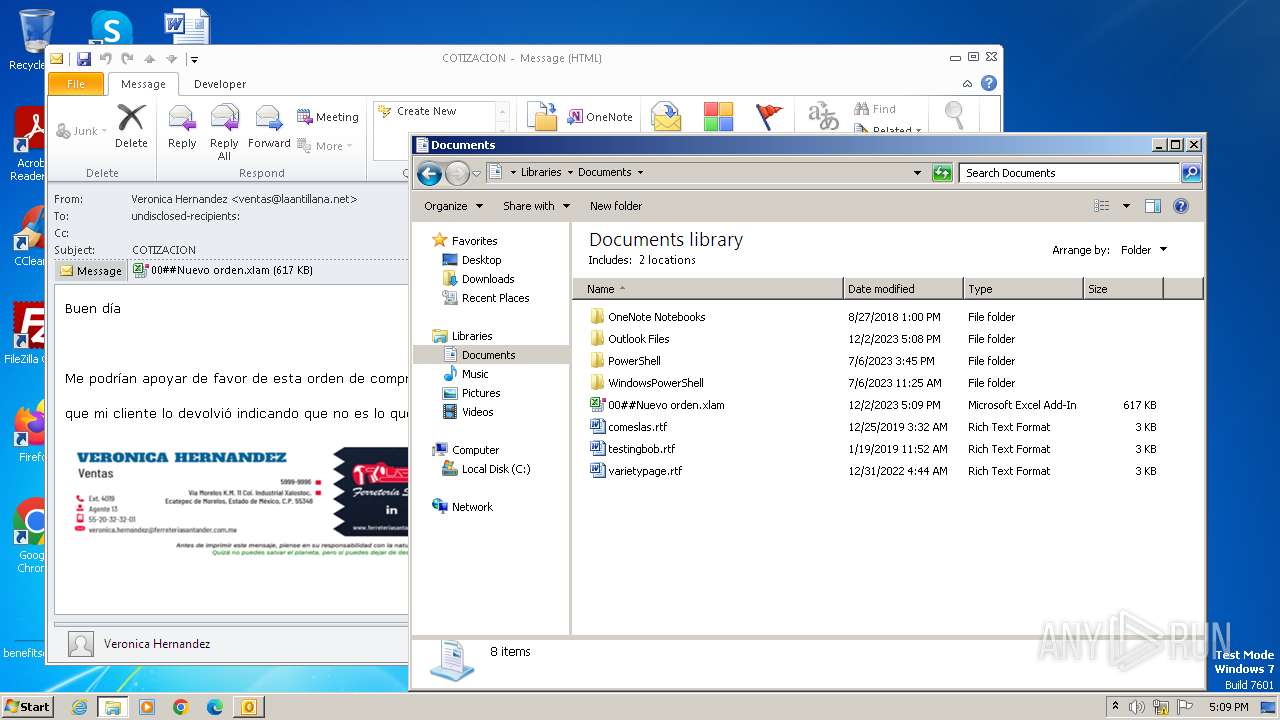
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 844 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR6D16.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 844 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 3288 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRF6A8.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 844 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 844 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmp6E31.tmp | binary | |
MD5:05043135084C7F89ED89E3955BA51013 | SHA256:663E7562C8675163A2D510BDE3FF4C67F63C16725FDDC053EC478F679ADC23E9 | |||
| 844 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmp6E20.tmp | binary | |
MD5:14B5971A92C84CEED5B010FAC3EEF051 | SHA256:C5C1856020B64669627876F24FB95A7B3FF572261D106AFD96B162E62D625676 | |||
| 844 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | binary | |
MD5:A66281831BFD6063A6EB650074E97385 | SHA256:E643B944225AE6F30541BEA24C8633CC84731CF40AD3F093795FE15A0E35AAD6 | |||
| 844 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\E0AB36LQ\00##Nuevo orden.xlam:Zone.Identifier | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
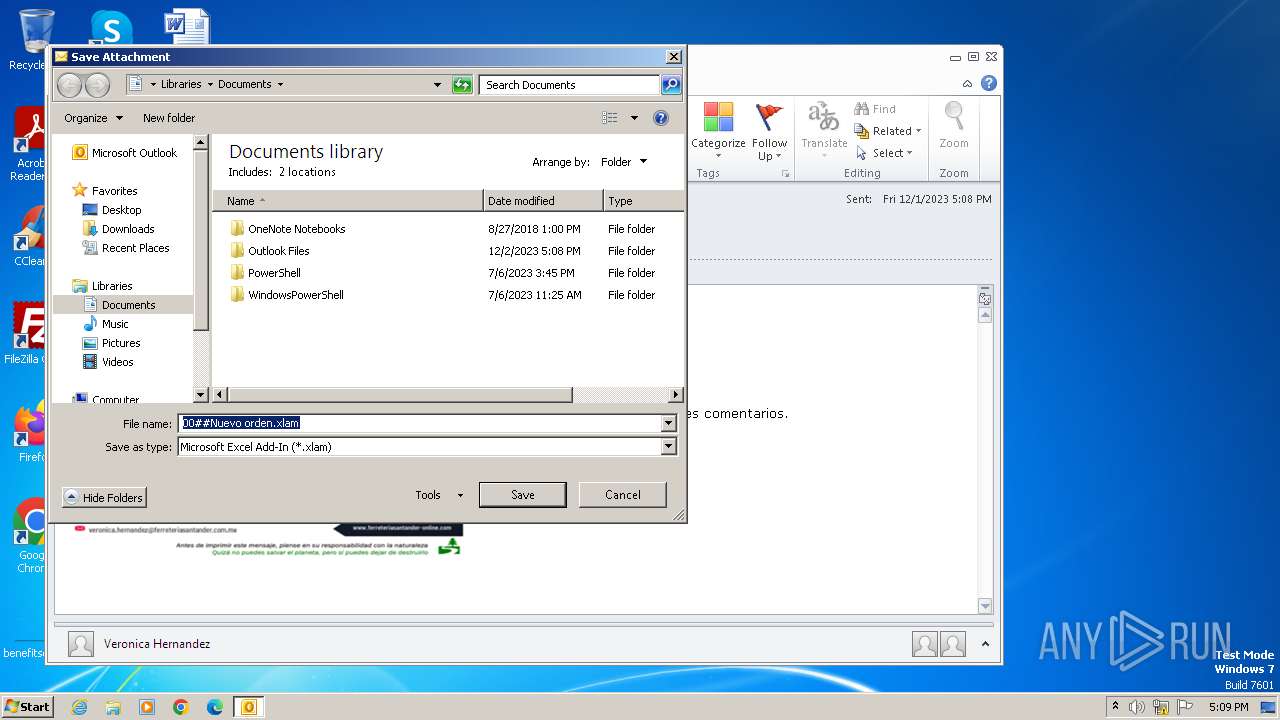
| 844 | OUTLOOK.EXE | C:\Users\admin\Documents\00##Nuevo orden.xlam:Zone.Identifier:$DATA | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
| 844 | OUTLOOK.EXE | C:\Users\admin\Documents\00##Nuevo orden.xlam | document | |
MD5:9D0710F01D7A78666E92B673D2AA4021 | SHA256:8C1BDF89F0D1081FE4331D85DB0339D3C4EF98D6EC089107A713BB4CC8161ABB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
844 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3252 | EQNEDT32.EXE | 91.92.250.98:80 | — | — | BG | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
dns.msftncsi.com |
| shared |