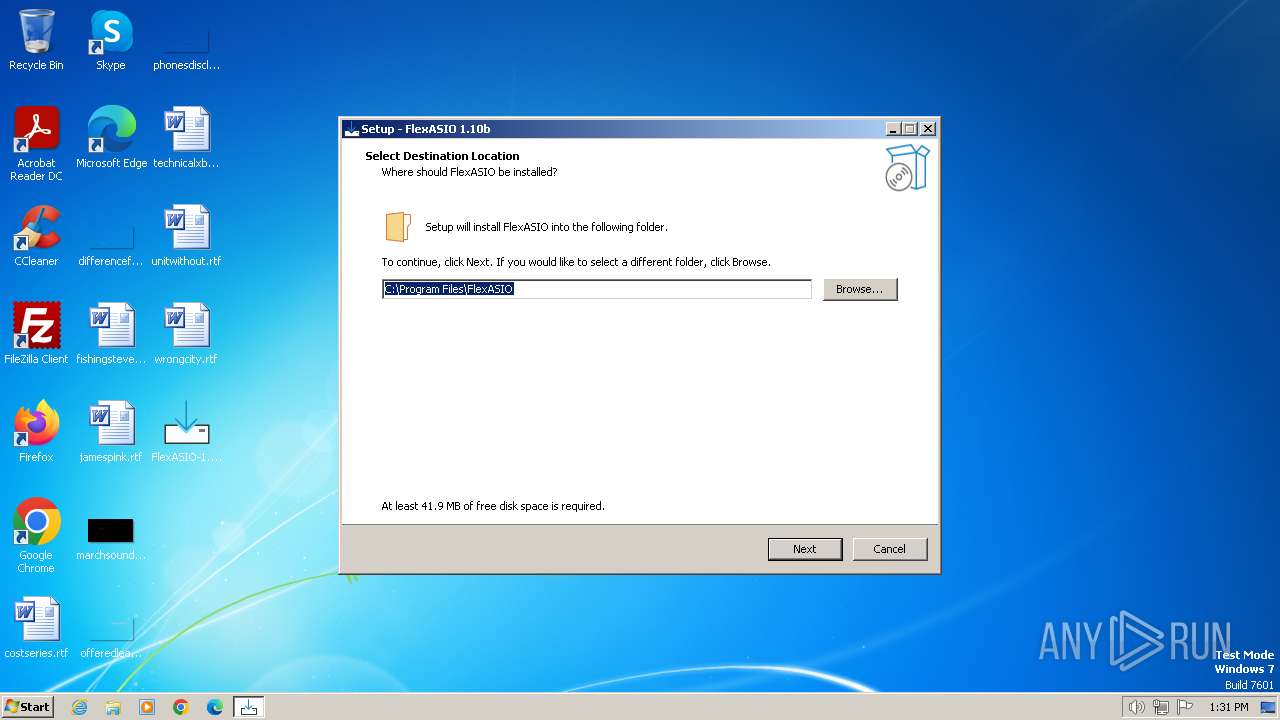
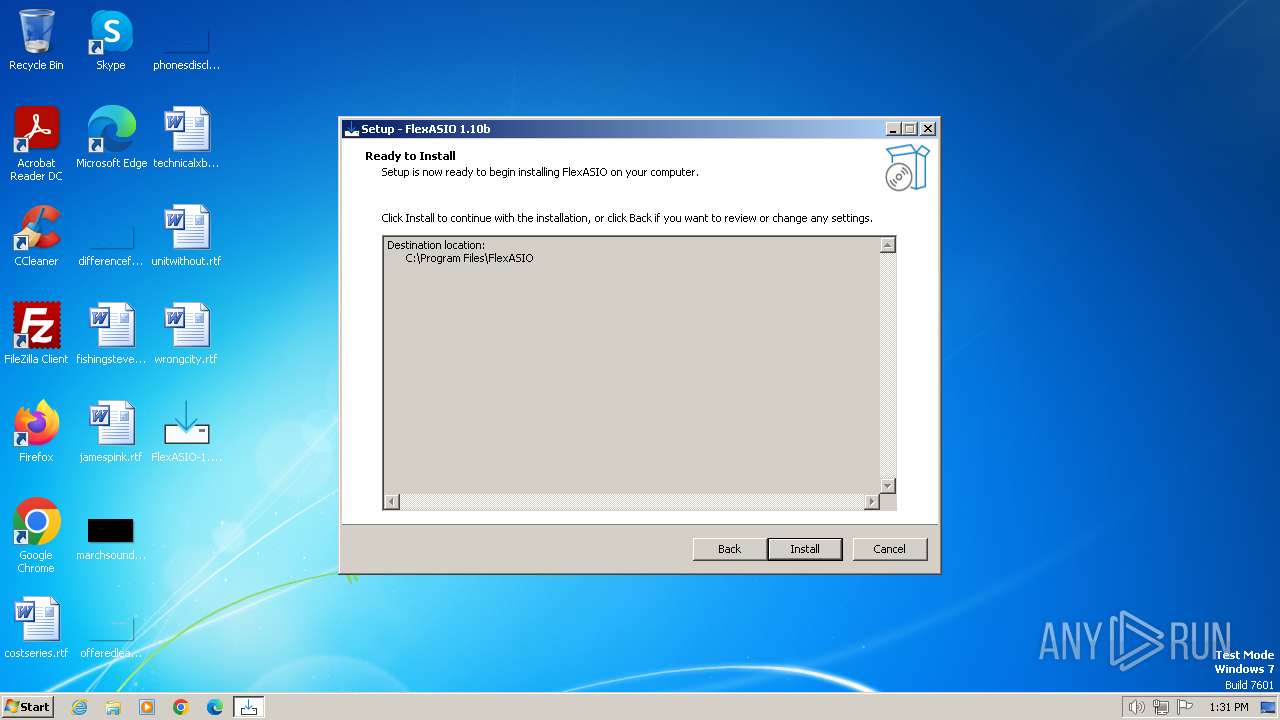
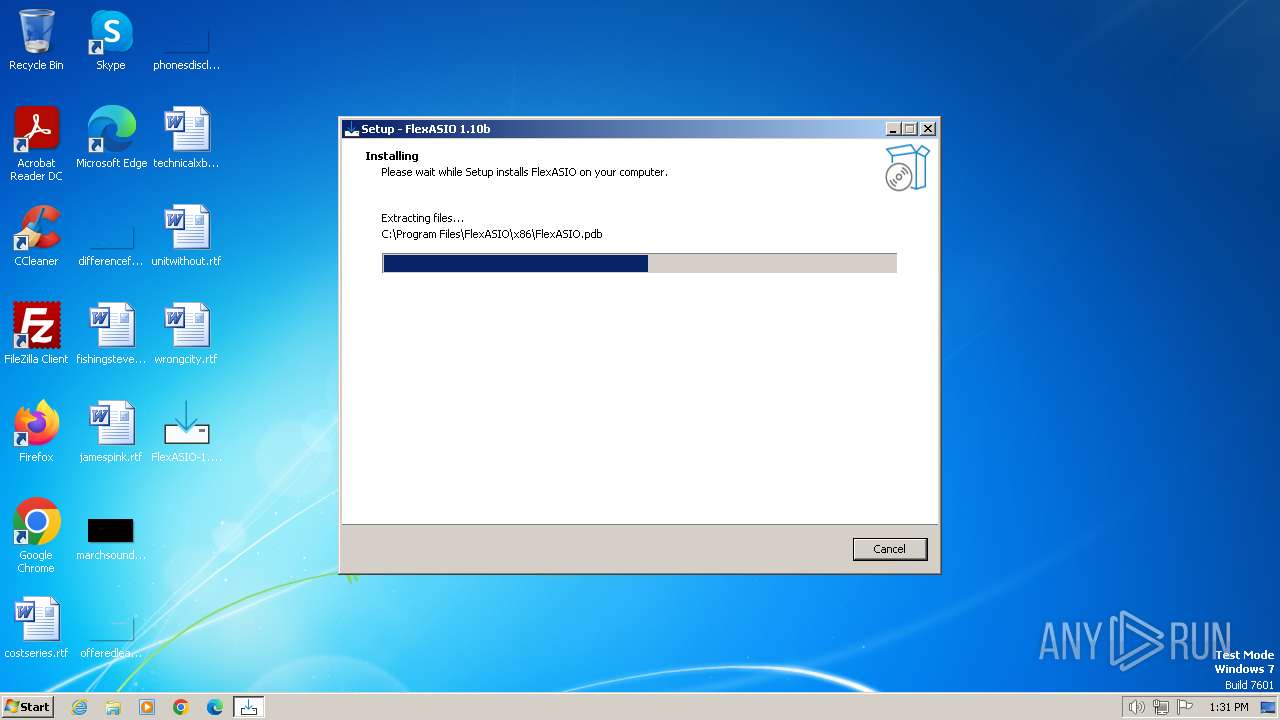
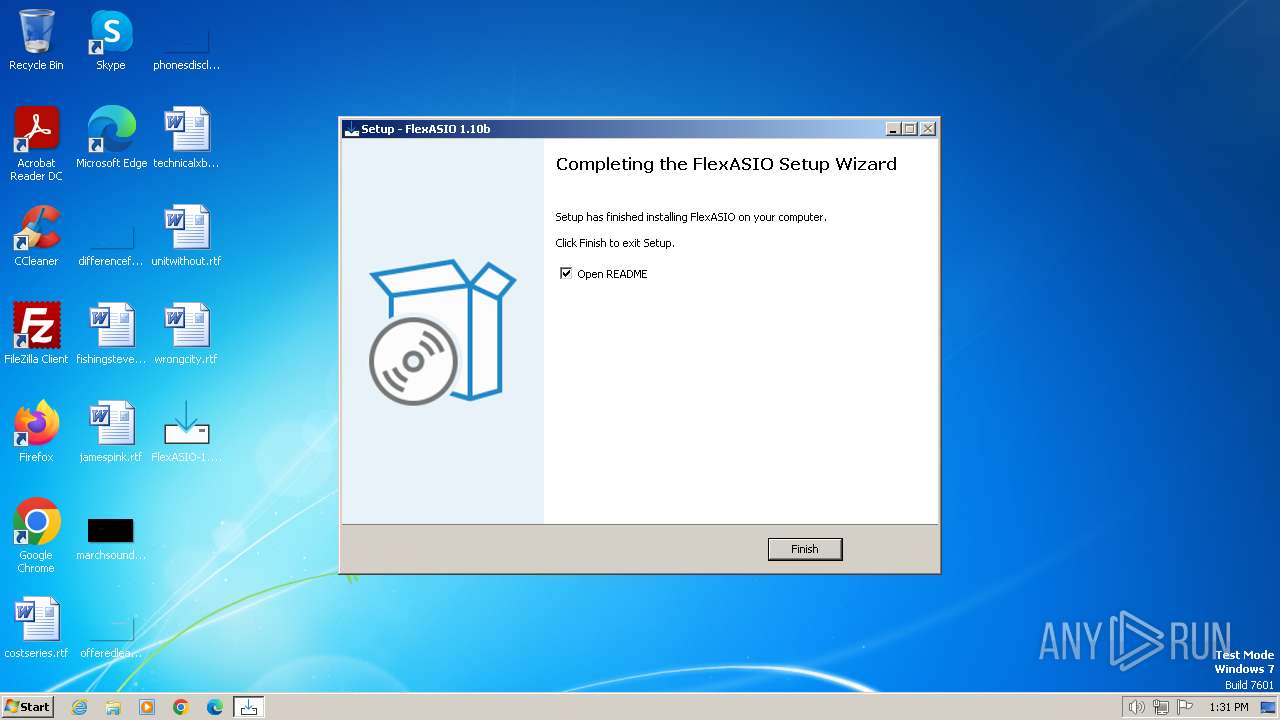
| File name: | FlexASIO-1.10b.exe |
| Full analysis: | https://app.any.run/tasks/77469e55-9a0a-4e91-ba92-3b8a33016487 |
| Verdict: | Malicious activity |
| Analysis date: | July 06, 2024, 12:31:33 |
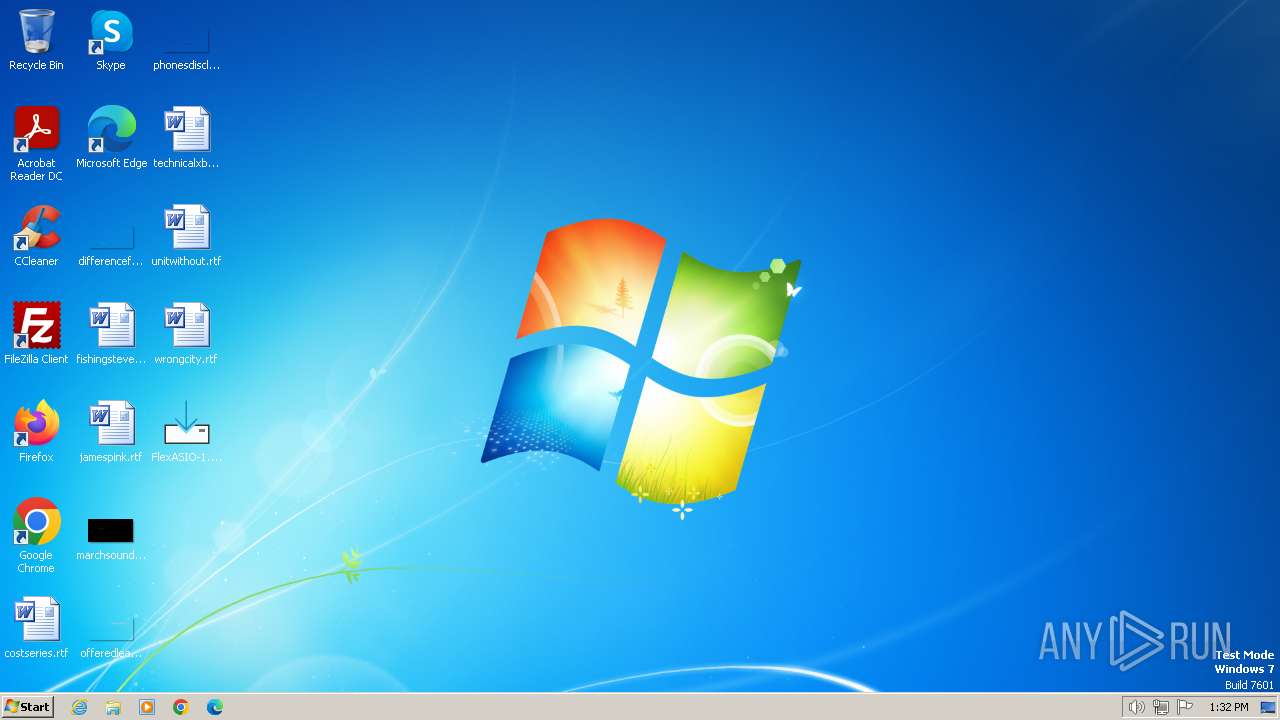
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FA5AF7F01E339742A19786C775B38679 |
| SHA1: | 6CDF85C4EB29DB19BE7BF709AB9399F08DB71403 |
| SHA256: | FE496BCC08D6C421C6244C8A60AC7B538560BDA138000FD1A54AB8EBCE031209 |
| SSDEEP: | 98304:m+cD4dnvv9H9U6747oNvVXh3BZrVAb3FqyR64ig1iRp07dncdN+Vrkk3Nf6XgEl1:nh7WX1S+8S74US/rAYwuj9eDDgWYB |
MALICIOUS
Drops the executable file immediately after the start
- FlexASIO-1.10b.exe (PID: 3344)
- FlexASIO-1.10b.exe (PID: 680)
- FlexASIO-1.10b.tmp (PID: 2748)
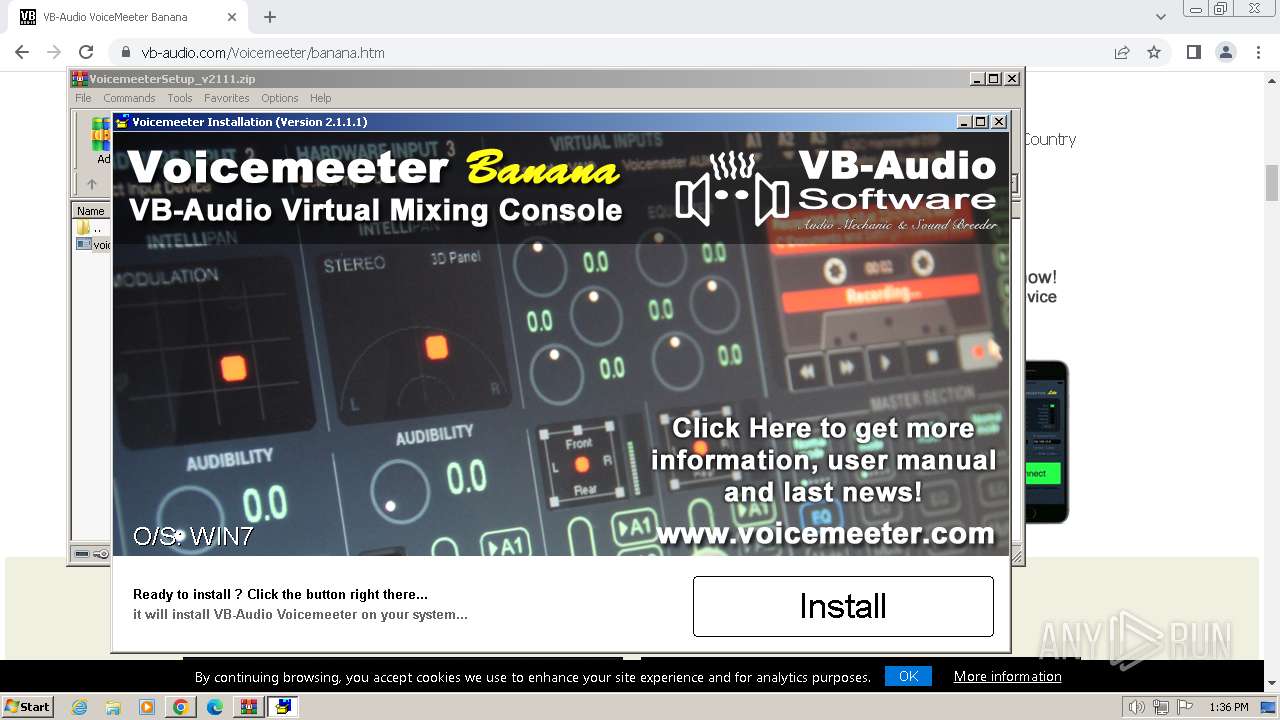
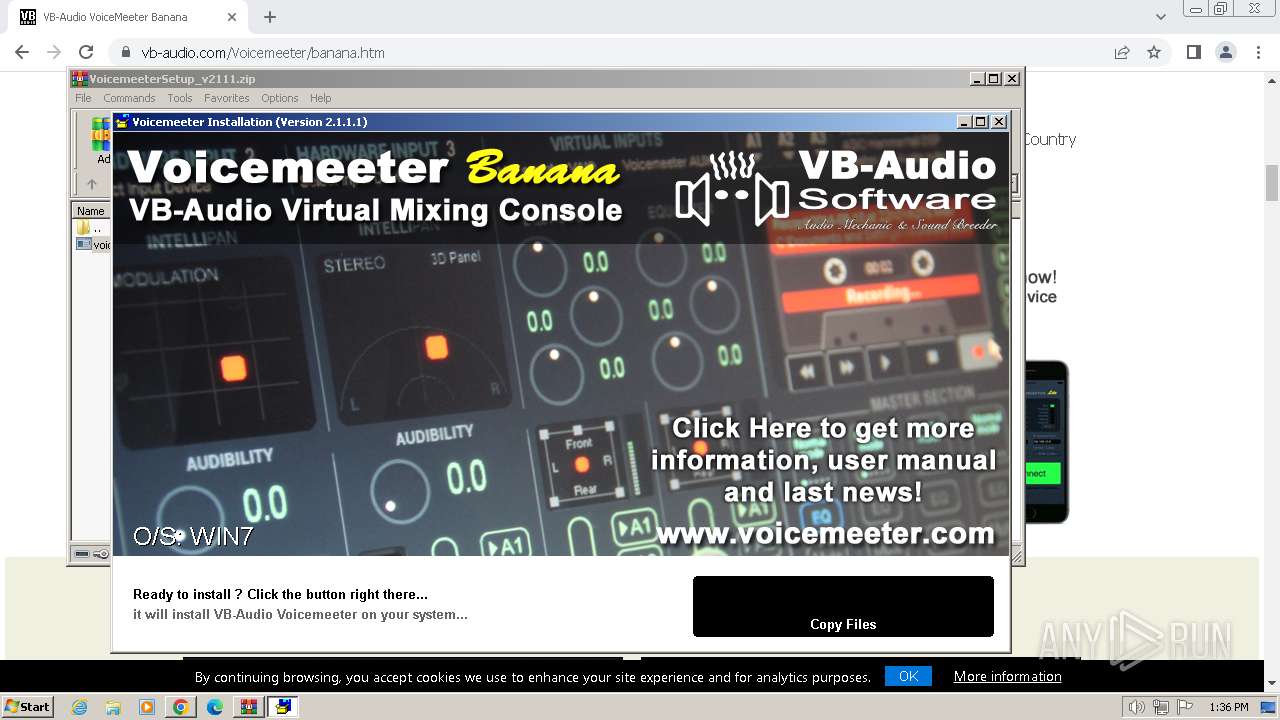
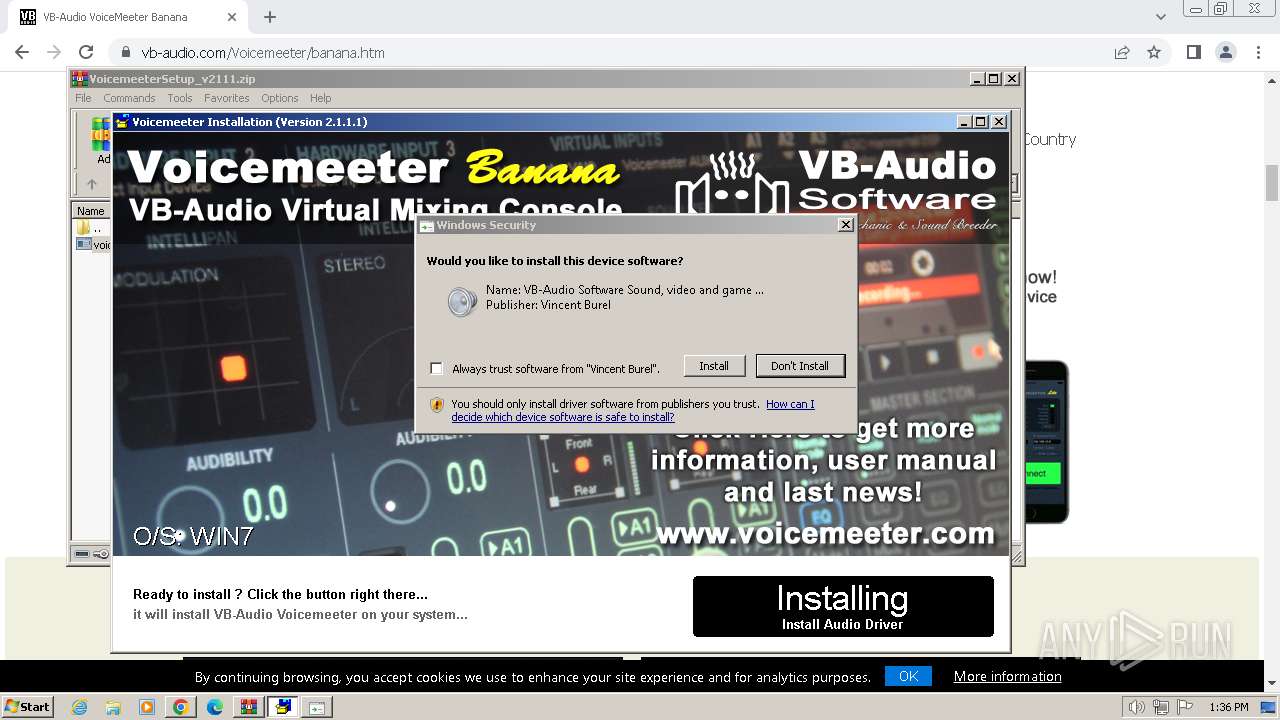
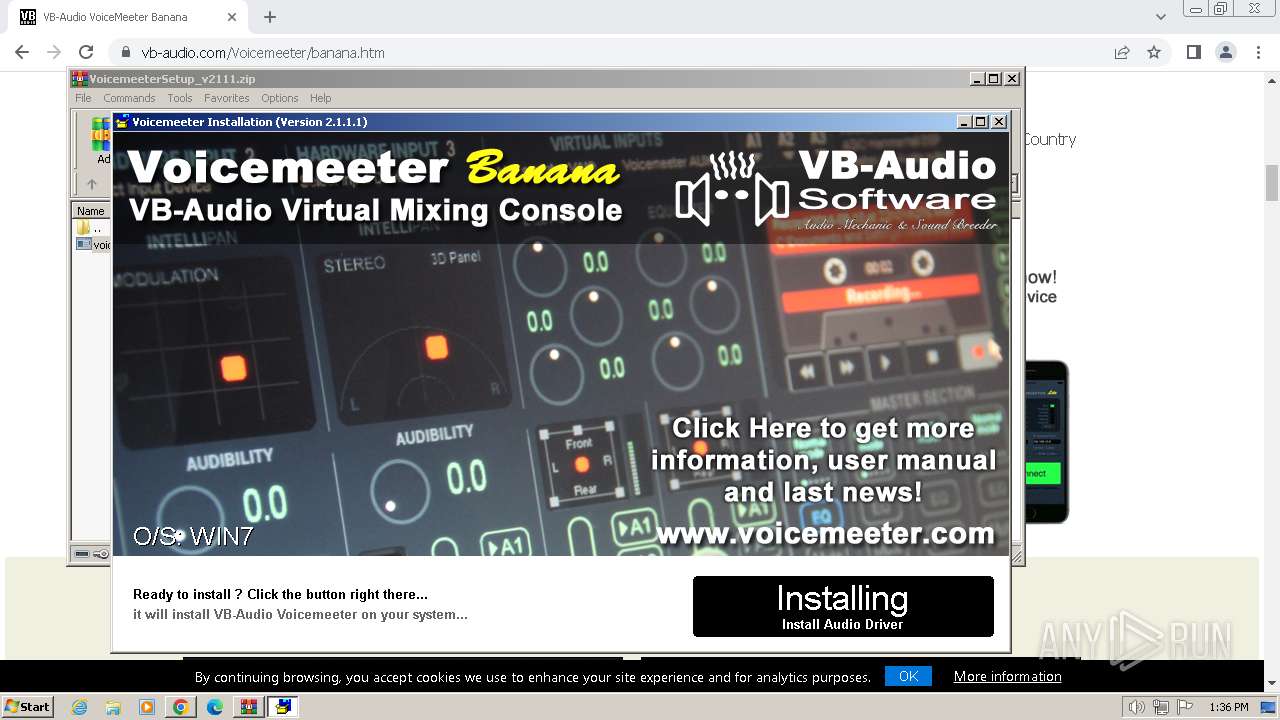
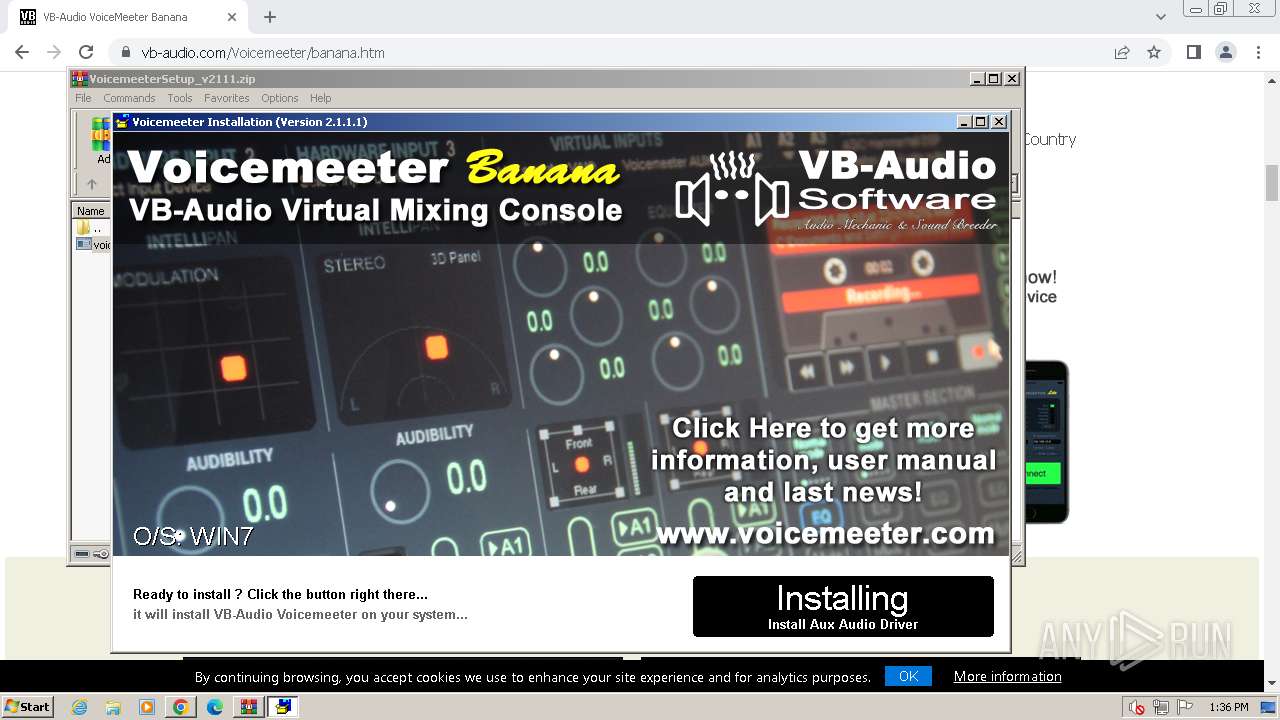
- voicemeeterprosetup.exe (PID: 3844)
- VBCABLE_Setup.exe (PID: 3132)
- drvinst.exe (PID: 1432)
- drvinst.exe (PID: 2008)
- VBVMAUX_Setup.exe (PID: 1420)
- drvinst.exe (PID: 2352)
- drvinst.exe (PID: 2164)
Registers / Runs the DLL via REGSVR32.EXE
- FlexASIO-1.10b.tmp (PID: 2748)
Creates a writable file in the system directory
- drvinst.exe (PID: 1432)
- drvinst.exe (PID: 2008)
- drvinst.exe (PID: 2352)
SUSPICIOUS
Executable content was dropped or overwritten
- FlexASIO-1.10b.exe (PID: 3344)
- FlexASIO-1.10b.exe (PID: 680)
- FlexASIO-1.10b.tmp (PID: 2748)
- voicemeeterprosetup.exe (PID: 3844)
- VBCABLE_Setup.exe (PID: 3132)
- drvinst.exe (PID: 1432)
- drvinst.exe (PID: 2008)
- VBVMAUX_Setup.exe (PID: 1420)
- drvinst.exe (PID: 2352)
- drvinst.exe (PID: 2164)
Reads the Windows owner or organization settings
- FlexASIO-1.10b.tmp (PID: 2748)
Process drops legitimate windows executable
- FlexASIO-1.10b.tmp (PID: 2748)
The process drops C-runtime libraries
- FlexASIO-1.10b.tmp (PID: 2748)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 540)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3904)
- VBCABLE_Setup.exe (PID: 3132)
- VBVMAUX_Setup.exe (PID: 1420)
Drops a system driver (possible attempt to evade defenses)
- voicemeeterprosetup.exe (PID: 3844)
- VBCABLE_Setup.exe (PID: 3132)
- drvinst.exe (PID: 1432)
- drvinst.exe (PID: 2008)
- VBVMAUX_Setup.exe (PID: 1420)
- drvinst.exe (PID: 2352)
- drvinst.exe (PID: 2164)
Checks Windows Trust Settings
- VBCABLE_Setup.exe (PID: 3132)
- drvinst.exe (PID: 1432)
- drvinst.exe (PID: 2008)
- VBVMAUX_Setup.exe (PID: 1420)
- drvinst.exe (PID: 2352)
Reads settings of System Certificates
- VBCABLE_Setup.exe (PID: 3132)
- rundll32.exe (PID: 2036)
- rundll32.exe (PID: 3464)
- VBVMAUX_Setup.exe (PID: 1420)
Creates files in the driver directory
- drvinst.exe (PID: 1432)
- drvinst.exe (PID: 2008)
- drvinst.exe (PID: 2352)
Executes as Windows Service
- VSSVC.exe (PID: 1196)
There is functionality for taking screenshot (YARA)
- voicemeeterprosetup.exe (PID: 3844)
INFO
Checks supported languages
- FlexASIO-1.10b.exe (PID: 3344)
- FlexASIO-1.10b.tmp (PID: 3416)
- FlexASIO-1.10b.exe (PID: 680)
- FlexASIO-1.10b.tmp (PID: 2748)
- voicemeeterprosetup.exe (PID: 3844)
- VBCABLE_Setup.exe (PID: 3132)
- drvinst.exe (PID: 1432)
- drvinst.exe (PID: 2008)
- VBVMAUX_Setup.exe (PID: 1420)
- drvinst.exe (PID: 2352)
Reads the computer name
- FlexASIO-1.10b.tmp (PID: 3416)
- FlexASIO-1.10b.tmp (PID: 2748)
- voicemeeterprosetup.exe (PID: 3844)
- VBCABLE_Setup.exe (PID: 3132)
- drvinst.exe (PID: 1432)
- drvinst.exe (PID: 2008)
- VBVMAUX_Setup.exe (PID: 1420)
- drvinst.exe (PID: 2352)
Create files in a temporary directory
- FlexASIO-1.10b.exe (PID: 3344)
- FlexASIO-1.10b.exe (PID: 680)
- VBCABLE_Setup.exe (PID: 3132)
- VBVMAUX_Setup.exe (PID: 1420)
Creates files in the program directory
- FlexASIO-1.10b.tmp (PID: 2748)
- voicemeeterprosetup.exe (PID: 3844)
- VBCABLE_Setup.exe (PID: 3132)
Creates a software uninstall entry
- FlexASIO-1.10b.tmp (PID: 2748)
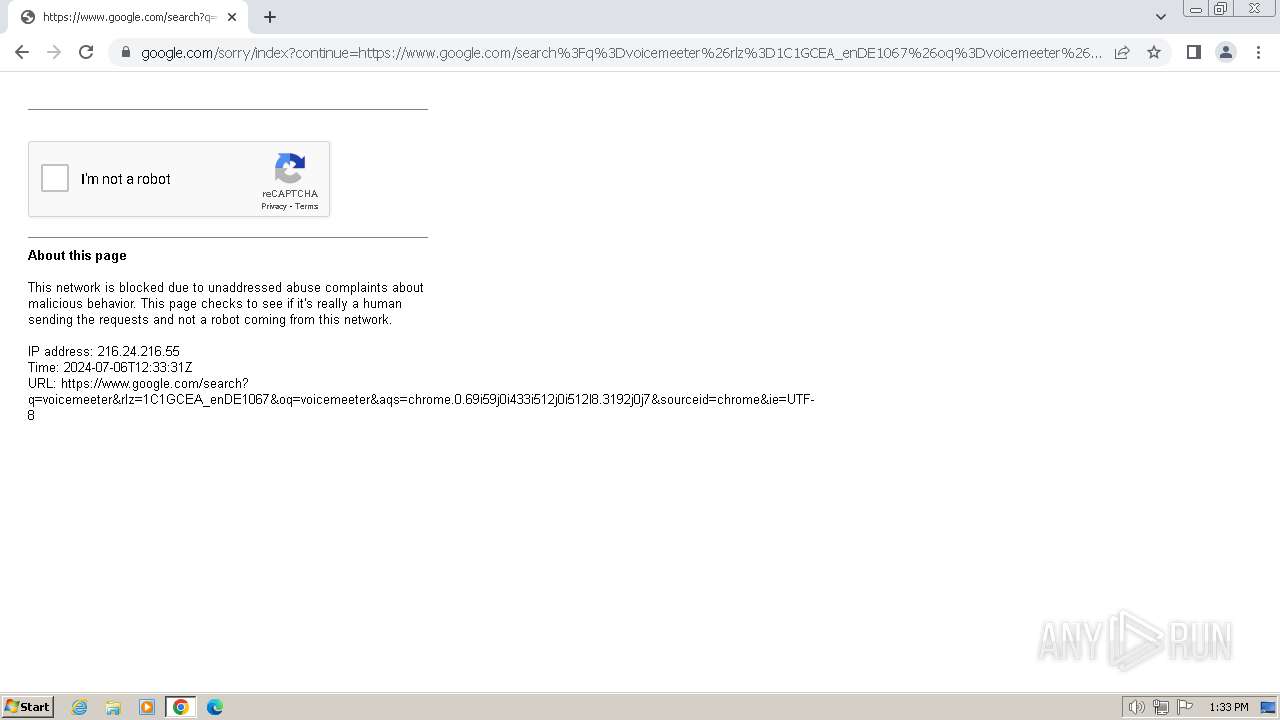
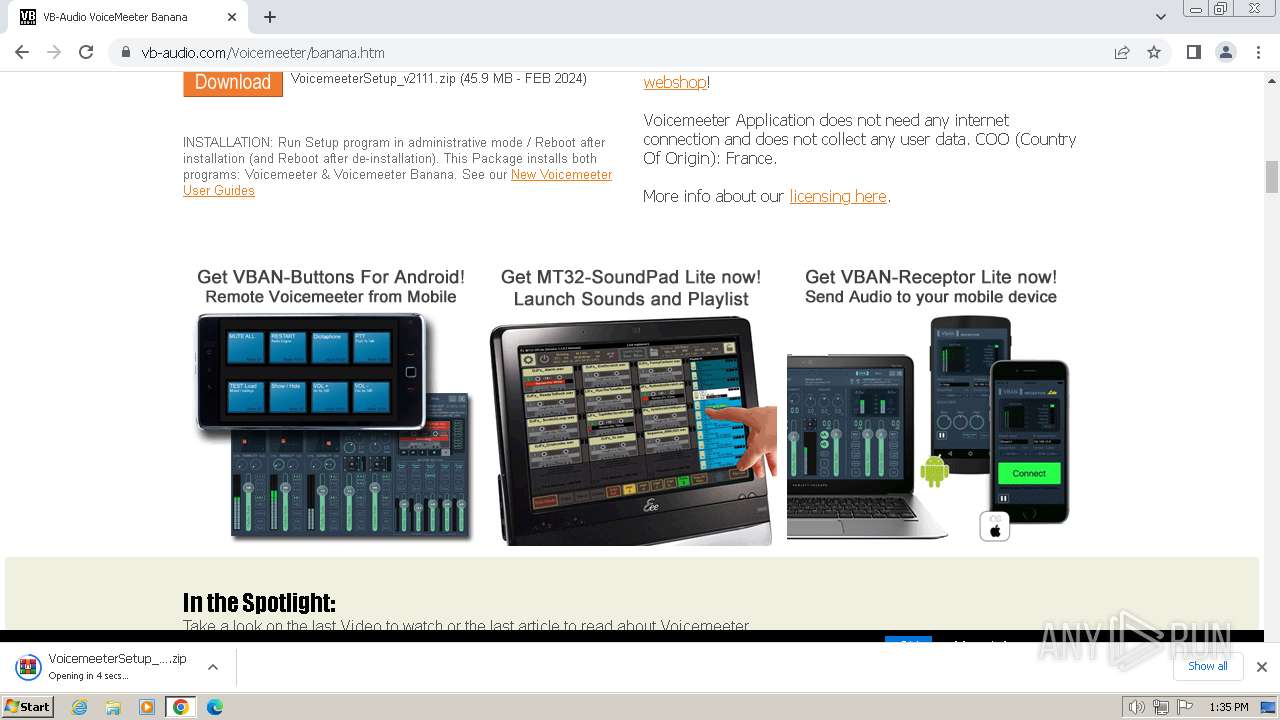
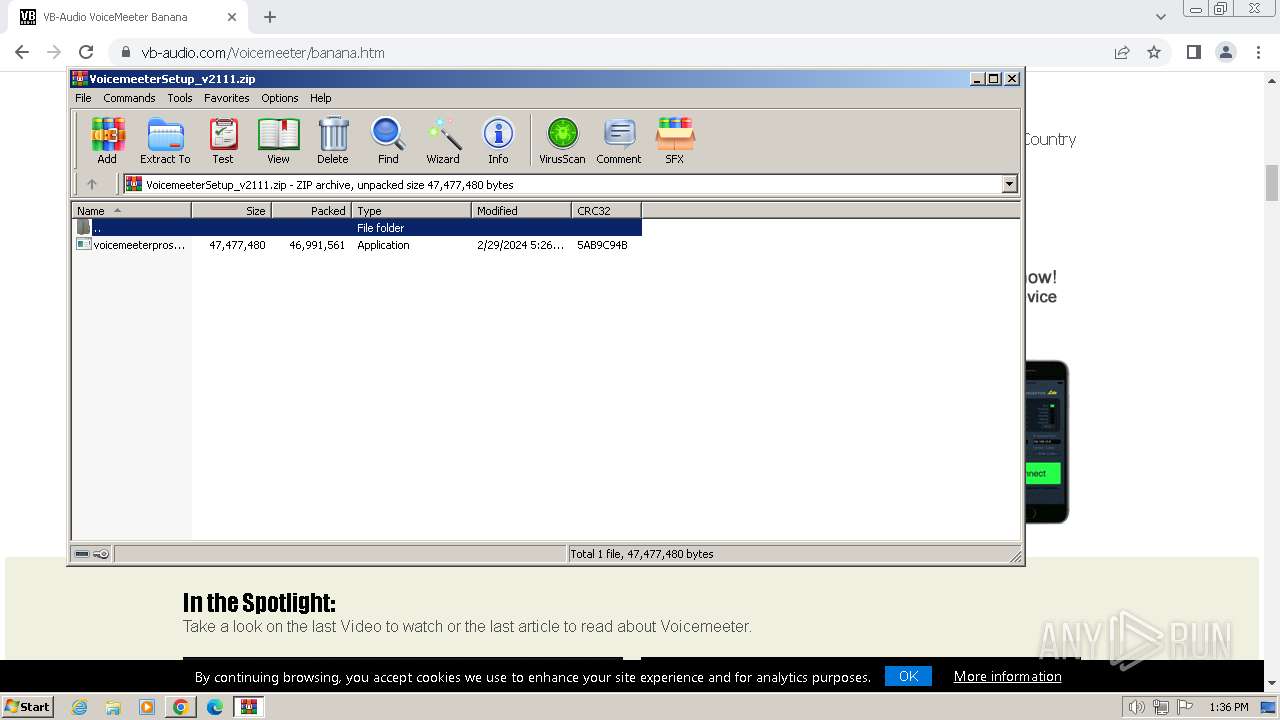
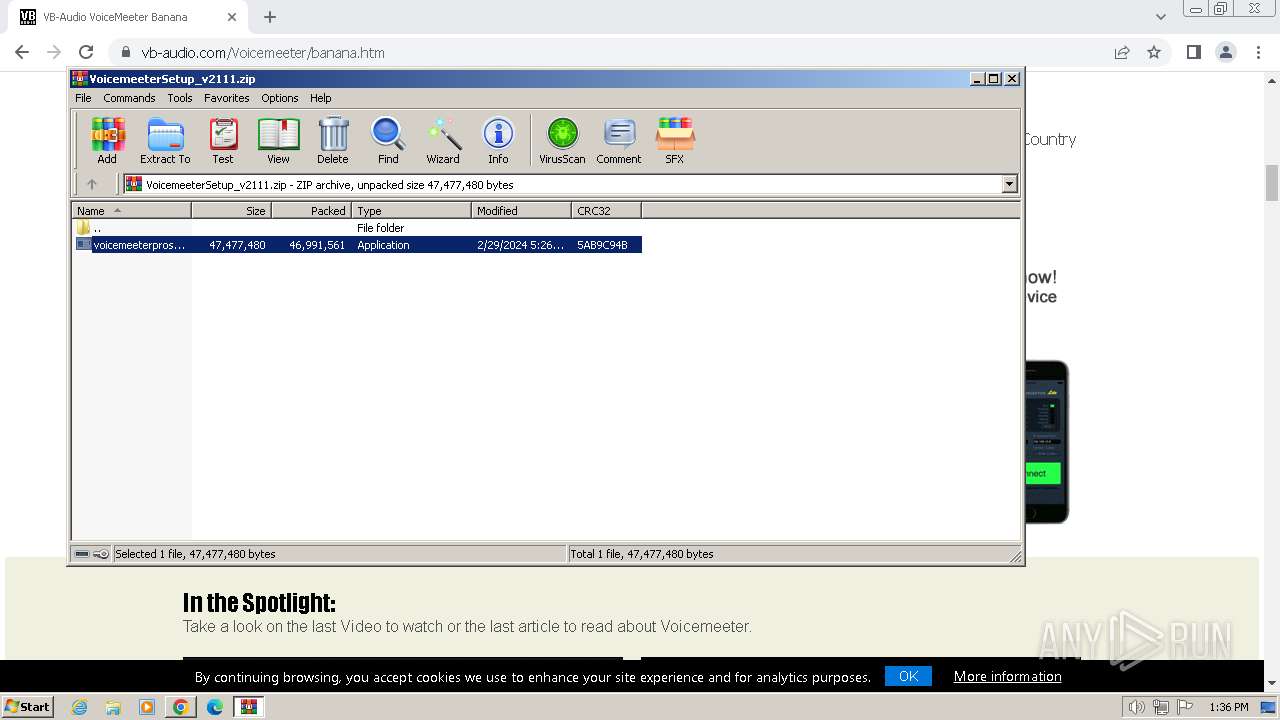
The process uses the downloaded file
- chrome.exe (PID: 2264)
- WinRAR.exe (PID: 3904)
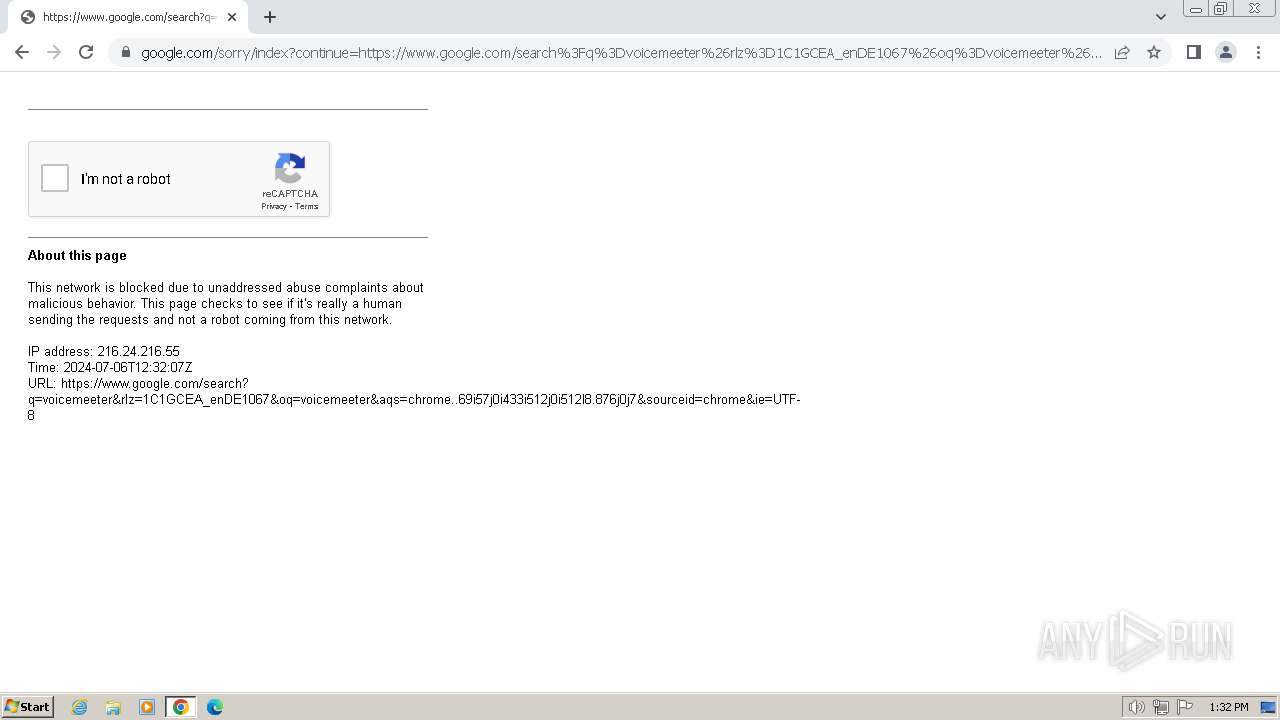
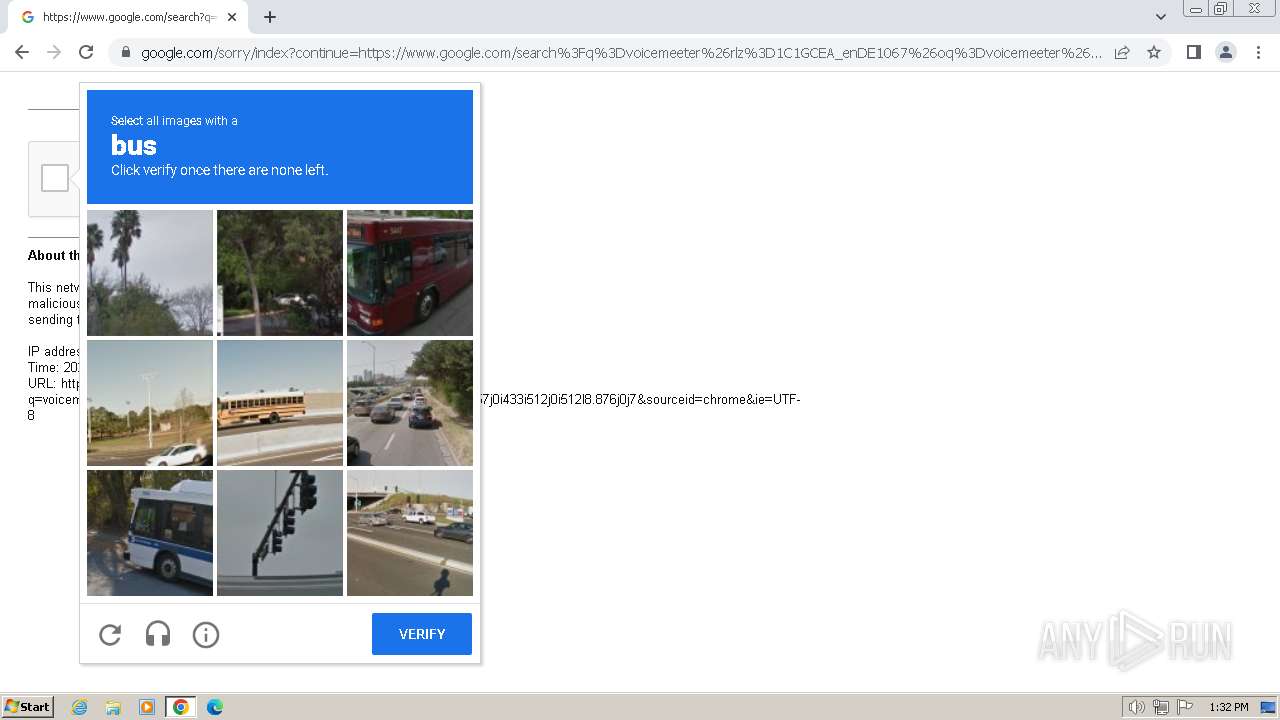
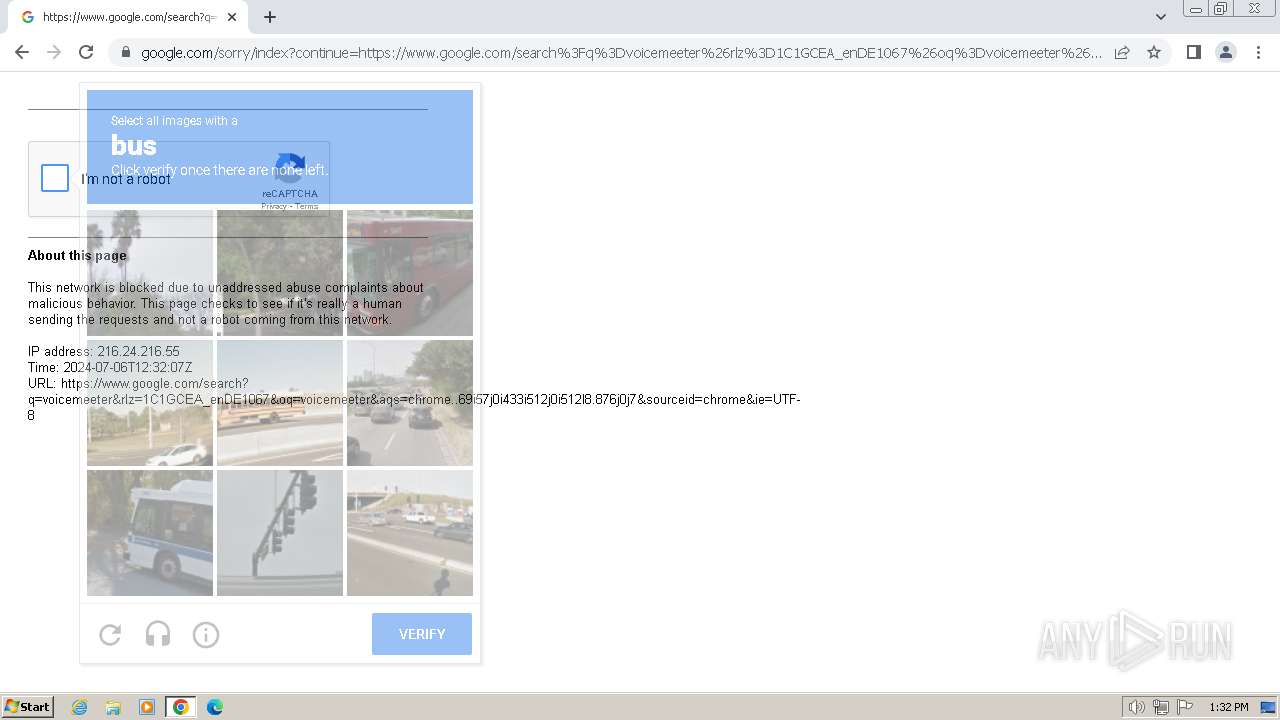
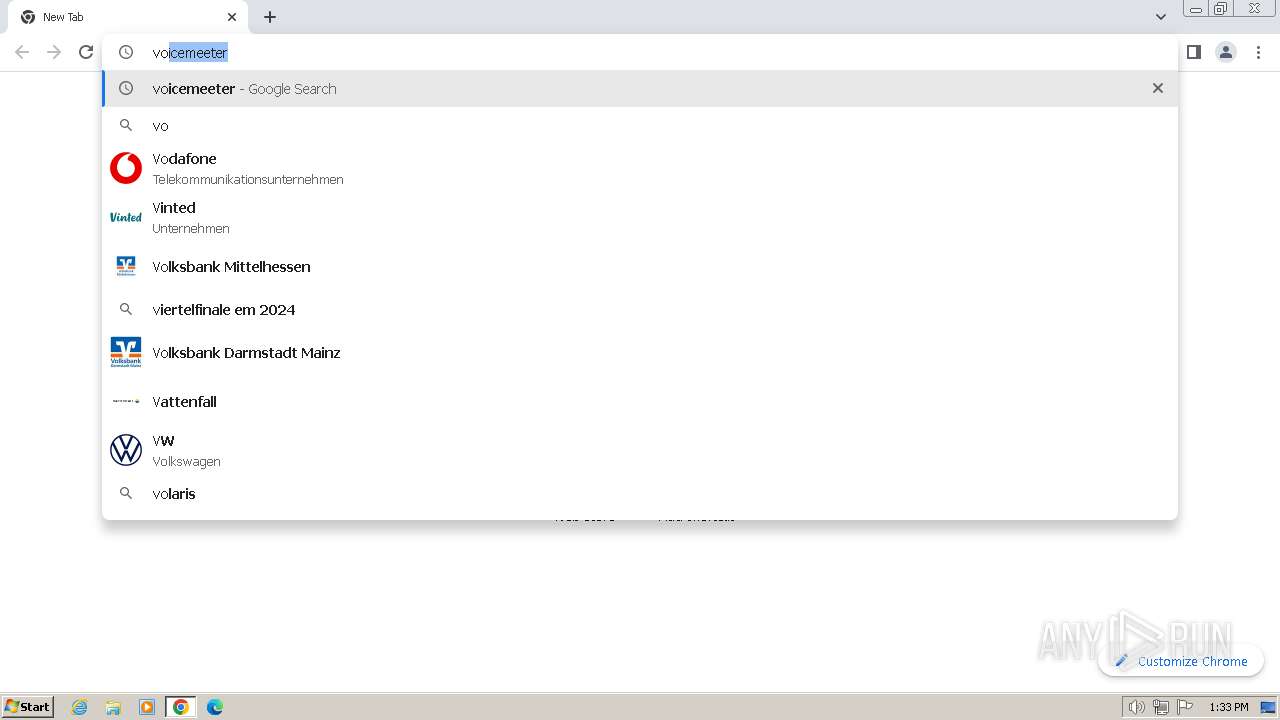
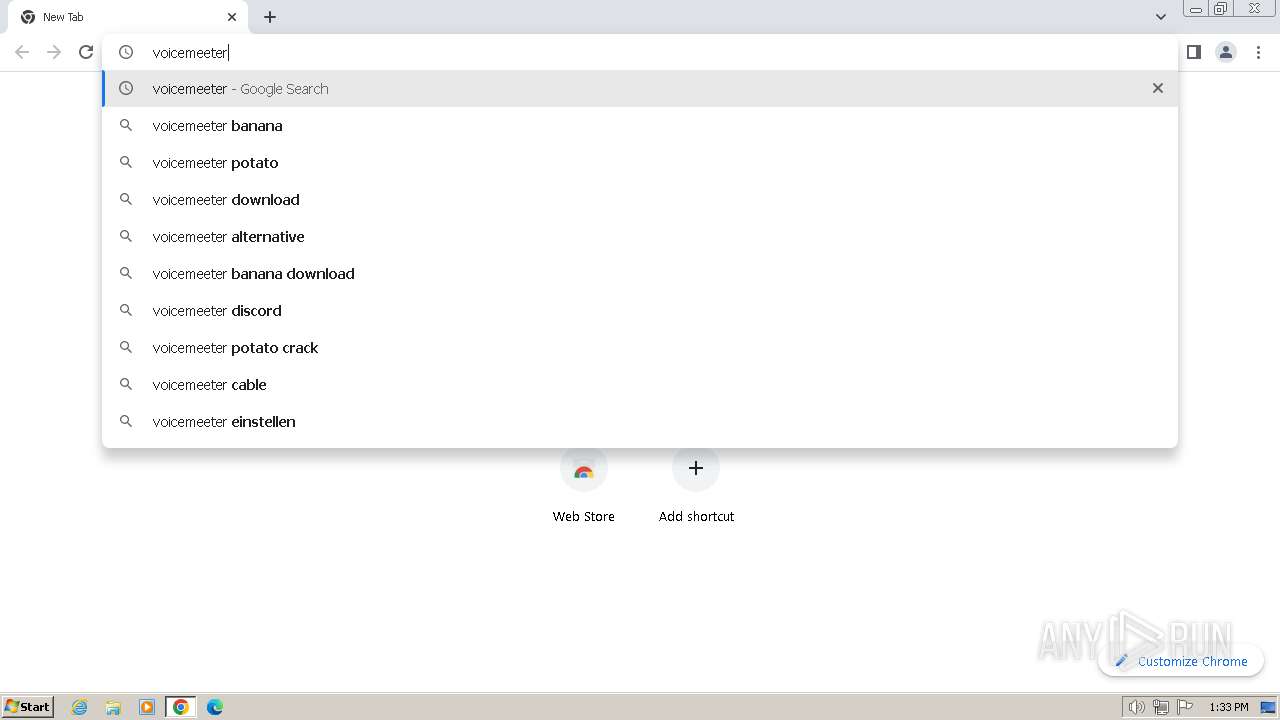
Manual execution by a user
- chrome.exe (PID: 2948)
- chrome.exe (PID: 3800)
- msedge.exe (PID: 3196)
Application launched itself
- chrome.exe (PID: 3800)
- chrome.exe (PID: 2948)
- msedge.exe (PID: 3888)
- msedge.exe (PID: 3196)
Drops the executable file immediately after the start
- chrome.exe (PID: 3800)
Reads the machine GUID from the registry
- VBCABLE_Setup.exe (PID: 3132)
- drvinst.exe (PID: 1432)
- drvinst.exe (PID: 2008)
- VBVMAUX_Setup.exe (PID: 1420)
- drvinst.exe (PID: 2352)
Reads the software policy settings
- VBCABLE_Setup.exe (PID: 3132)
- drvinst.exe (PID: 1432)
- rundll32.exe (PID: 2036)
- drvinst.exe (PID: 2008)
- VBVMAUX_Setup.exe (PID: 1420)
- rundll32.exe (PID: 3464)
- drvinst.exe (PID: 2352)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 2036)
- rundll32.exe (PID: 3464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (53.5) |
|---|---|---|
| .exe | | | InstallShield setup (21) |
| .exe | | | Win32 EXE PECompact compressed (generic) (20.2) |
| .exe | | | Win32 Executable (generic) (2.1) |
| .exe | | | Win16/32 Executable Delphi generic (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:02:15 14:54:16+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741888 |
| InitializedDataSize: | 89600 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Etienne Dechamps |
| FileDescription: | FlexASIO Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | FlexASIO |
| ProductVersion: | 1.10b |
Total processes
116
Monitored processes
69
Malicious processes
14
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 540 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\FlexASIO\x86\FlexASIO.dll" | C:\Windows\System32\regsvr32.exe | — | FlexASIO-1.10b.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3428 --field-trial-handle=1148,i,17062225188276298042,9440508177094603591,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 680 | "C:\Users\admin\Desktop\FlexASIO-1.10b.exe" /SPAWNWND=$4010A /NOTIFYWND=$B016A | C:\Users\admin\Desktop\FlexASIO-1.10b.exe | FlexASIO-1.10b.tmp | ||||||||||||
User: admin Company: Etienne Dechamps Integrity Level: HIGH Description: FlexASIO Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1668 --field-trial-handle=1148,i,17062225188276298042,9440508177094603591,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1596 --field-trial-handle=1148,i,17062225188276298042,9440508177094603591,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1196 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1080 --field-trial-handle=1148,i,17062225188276298042,9440508177094603591,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1420 | -h -i -H -n | C:\Program Files\VB\Voicemeeter\VBVMAUX_Setup.exe | voicemeeterprosetup.exe | ||||||||||||
User: admin Company: VB-AUDIO Software Integrity Level: HIGH Description: VB-AUDIO Virtual Cable Installer Exit code: 0 Version: 2, 1, 5, 2 Modules
| |||||||||||||||
| 1432 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{67882483-cfd1-6d6a-f47c-cc64163c1e4a}\vbvmvaio_win7.inf" "0" "6d2b90767" "000004C8" "WinSta0\Default" "000005E4" "208" "c:\program files\vb\voicemeeter" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --mojo-platform-channel-handle=2496 --field-trial-handle=1148,i,17062225188276298042,9440508177094603591,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
49 982
Read events
49 205
Write events
758
Delete events
19
Modification events
| (PID) Process: | (2748) FlexASIO-1.10b.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: BC0A00003C82D574A0CFDA01 | |||
| (PID) Process: | (2748) FlexASIO-1.10b.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 37271E97A52748027633C46B759D9490A9344E32E563E28F5B8784EF43EBB13E | |||
| (PID) Process: | (2748) FlexASIO-1.10b.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2748) FlexASIO-1.10b.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\FlexASIO\x86\FlexASIO.dll | |||
| (PID) Process: | (2748) FlexASIO-1.10b.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: B67EFA74578EA352BB15333051AA326124E711ECF528E99D9D756CCC2D9B55F2 | |||
| (PID) Process: | (540) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{462F2ABF-5278-436A-95B6-72CBF65482AE}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (540) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ASIO\FlexASIO |
| Operation: | write | Name: | CLSID |
Value: {462F2ABF-5278-436A-95B6-72CBF65482AE} | |||
| (PID) Process: | (540) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ASIO\FlexASIO |
| Operation: | write | Name: | Description |
Value: FlexASIO | |||
| (PID) Process: | (2748) FlexASIO-1.10b.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\FlexASIO_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.2.2 | |||
| (PID) Process: | (2748) FlexASIO-1.10b.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\FlexASIO_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\FlexASIO | |||
Executable files
105
Suspicious files
369
Text files
131
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2748 | FlexASIO-1.10b.tmp | C:\Program Files\FlexASIO\x86\is-SQ5B1.tmp | — | |
MD5:— | SHA256:— | |||
| 2748 | FlexASIO-1.10b.tmp | C:\Program Files\FlexASIO\x86\ASIOTest.pdb | — | |
MD5:— | SHA256:— | |||
| 2748 | FlexASIO-1.10b.tmp | C:\Program Files\FlexASIO\x86\is-UC13M.tmp | — | |
MD5:— | SHA256:— | |||
| 2748 | FlexASIO-1.10b.tmp | C:\Program Files\FlexASIO\x86\FlexASIO.pdb | — | |
MD5:— | SHA256:— | |||
| 2748 | FlexASIO-1.10b.tmp | C:\Program Files\FlexASIO\is-O7B26.tmp | executable | |
MD5:7FC2B20E15B6234CB2A09C79BD73AA9E | SHA256:94BE34E6762D8BCD4CB4930F6B05F0703A91544630BC919FE0C739C21DAEDED9 | |||
| 680 | FlexASIO-1.10b.exe | C:\Users\admin\AppData\Local\Temp\is-M36LI.tmp\FlexASIO-1.10b.tmp | executable | |
MD5:328787E5C2761540F4E7636002908C79 | SHA256:D2972F1FCE7437F6AF9FB518589EEE5FC219CC1E425D7A2D3A17B10612FD5772 | |||
| 2748 | FlexASIO-1.10b.tmp | C:\Program Files\FlexASIO\x86\FlexASIO.dll | executable | |
MD5:5B4E1ADBEDF6B491AA62D997C088AF6C | SHA256:836D367E8B5C33B0AF977155184CCC9EFB2BDCD56F28089474D6BC8D19715FD5 | |||
| 2748 | FlexASIO-1.10b.tmp | C:\Program Files\FlexASIO\x86\is-U58QA.tmp | executable | |
MD5:C243944FEFC72AE1B2BC7937B21A0FE1 | SHA256:C69F31337073FED245CDECCC6FB1E76EF5E9AE09AD595E98D447E95CC7303213 | |||
| 2748 | FlexASIO-1.10b.tmp | C:\Program Files\FlexASIO\x86\ASIOTest.dll | executable | |
MD5:C243944FEFC72AE1B2BC7937B21A0FE1 | SHA256:C69F31337073FED245CDECCC6FB1E76EF5E9AE09AD595E98D447E95CC7303213 | |||
| 3344 | FlexASIO-1.10b.exe | C:\Users\admin\AppData\Local\Temp\is-M39J8.tmp\FlexASIO-1.10b.tmp | executable | |
MD5:328787E5C2761540F4E7636002908C79 | SHA256:D2972F1FCE7437F6AF9FB518589EEE5FC219CC1E425D7A2D3A17B10612FD5772 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
76
DNS requests
97
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fbe613066ac7852b | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
2708 | chrome.exe | GET | 204 | 142.250.186.163:80 | http://www.gstatic.com/generate_204 | unknown | — | — | unknown |
844 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | unknown | — | — | unknown |
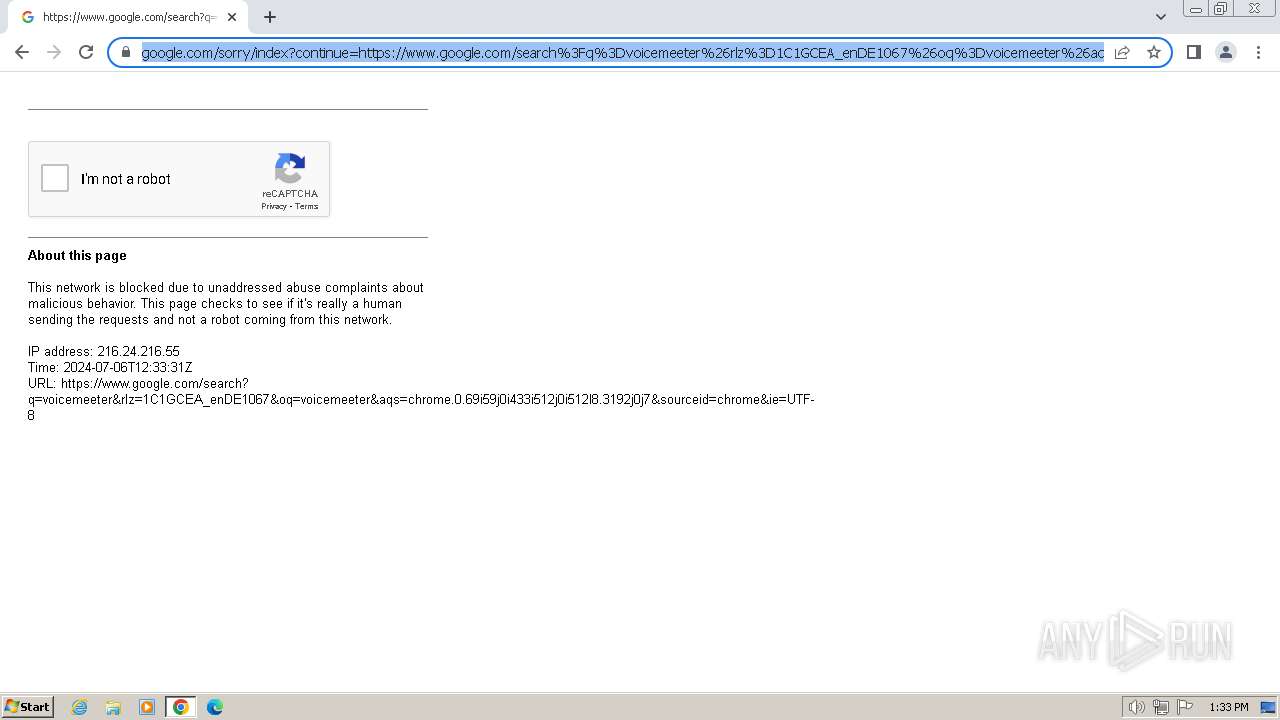
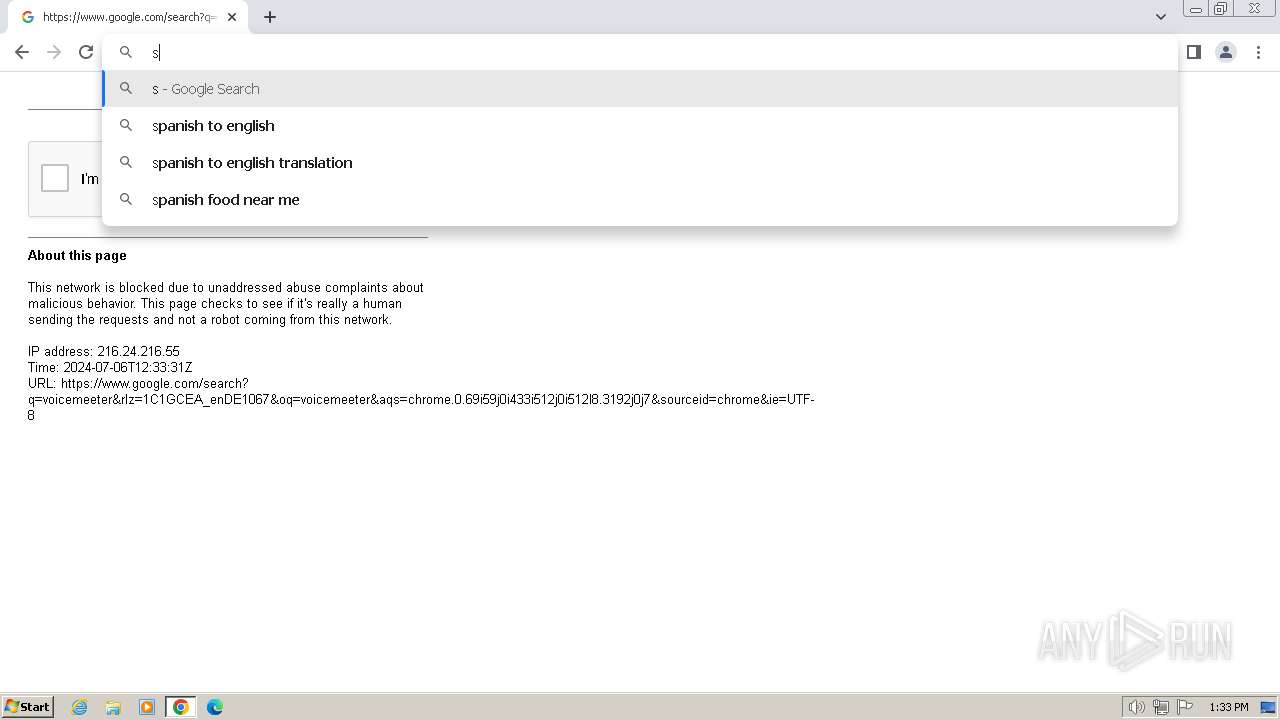
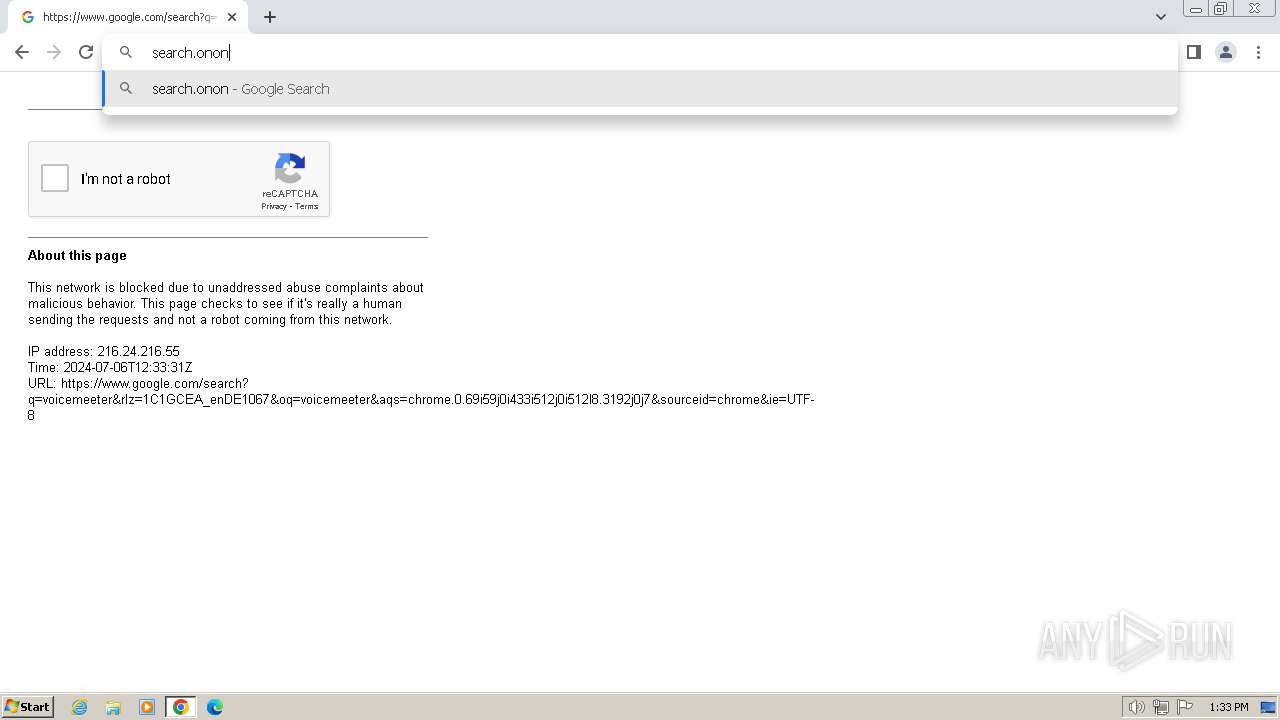
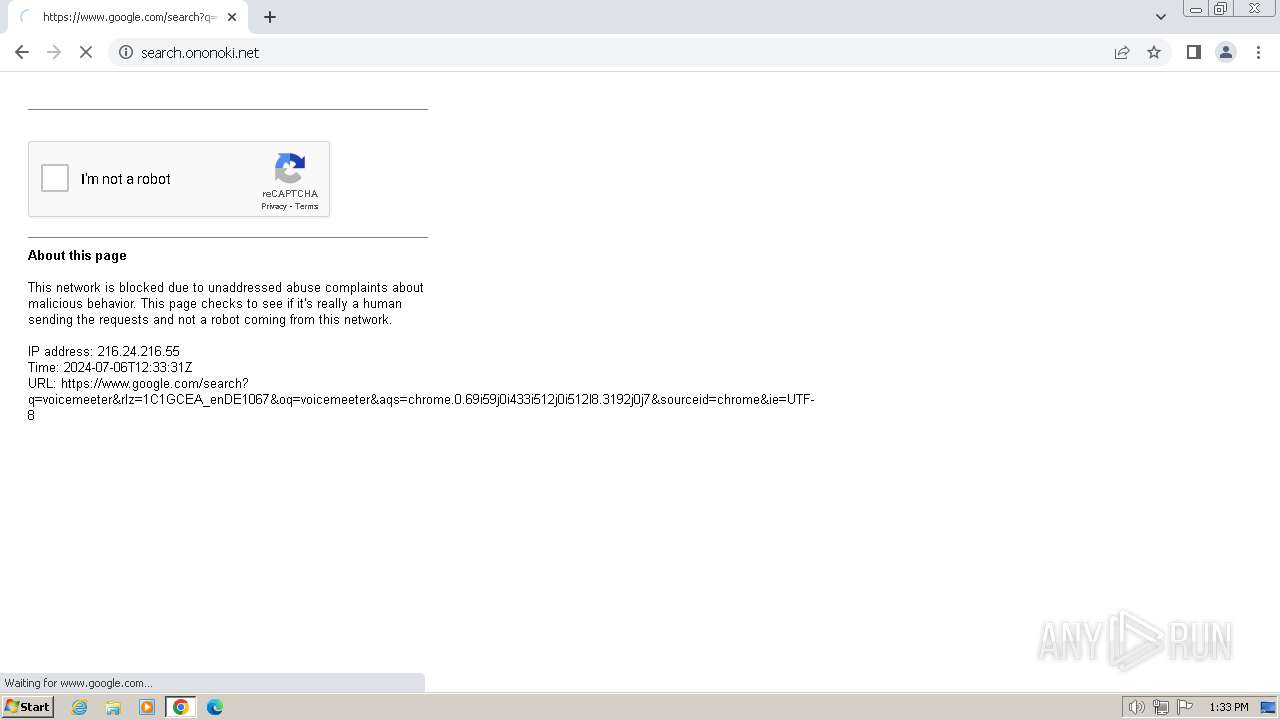
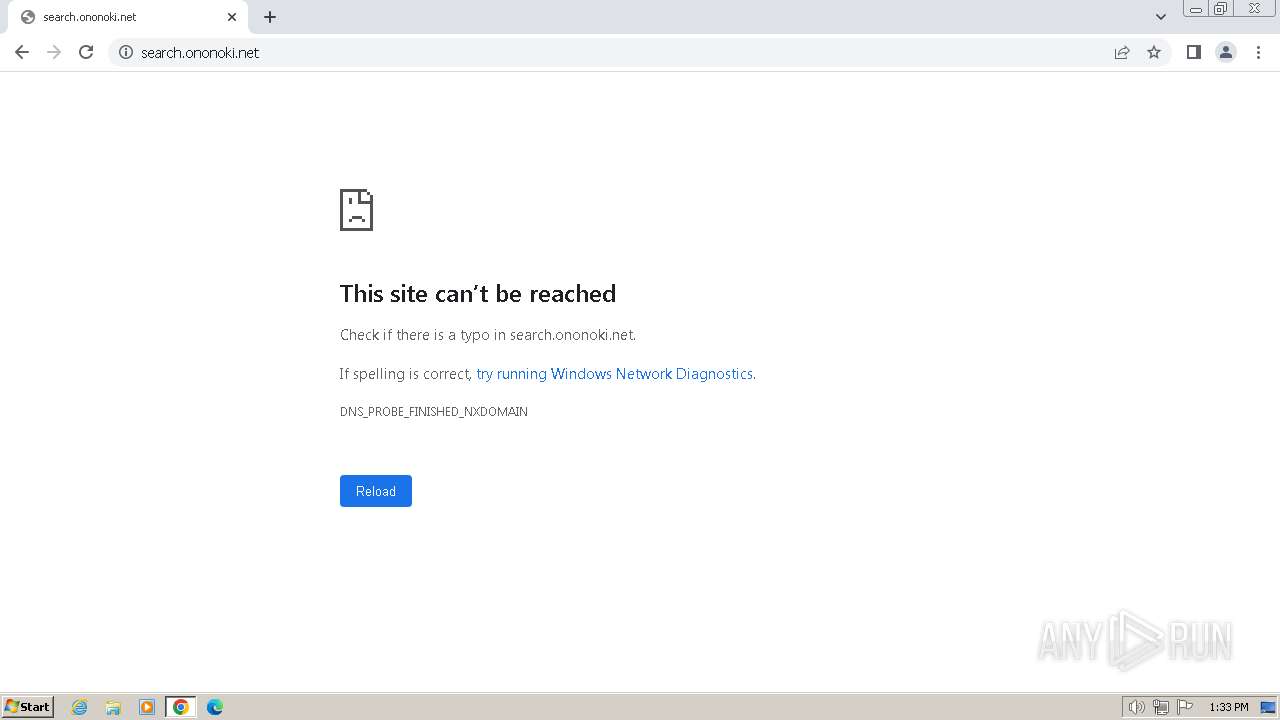
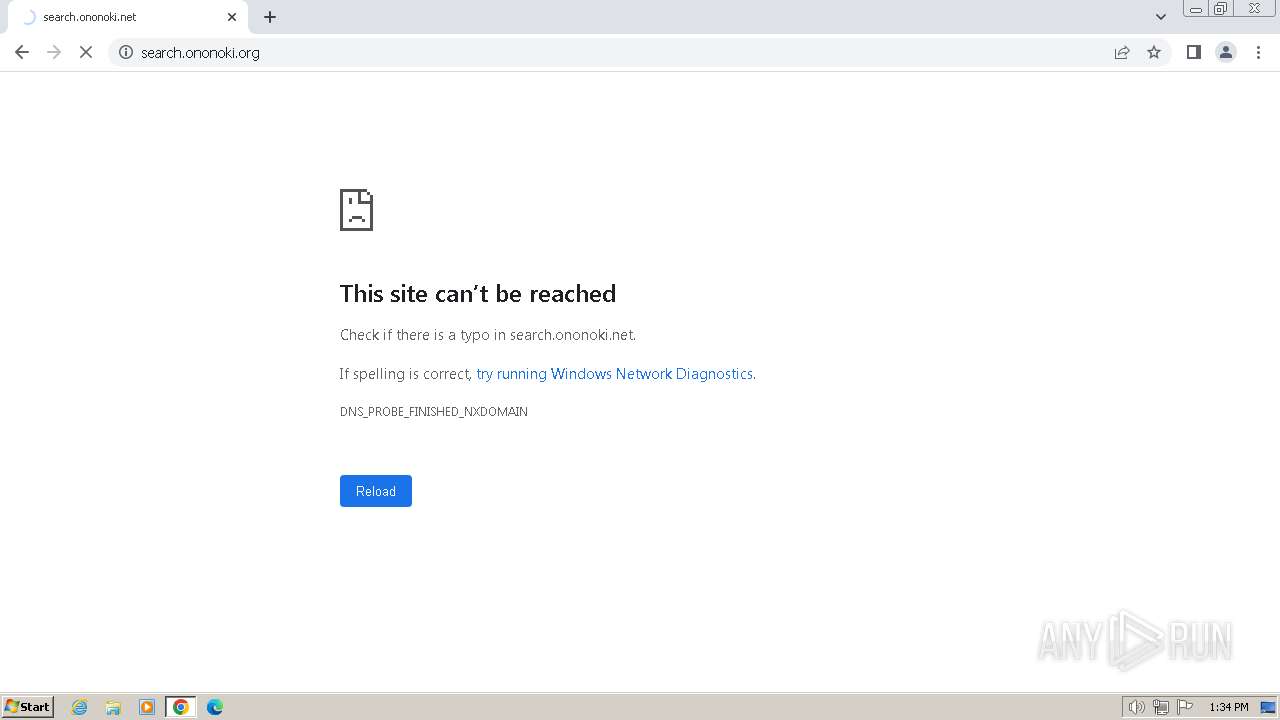
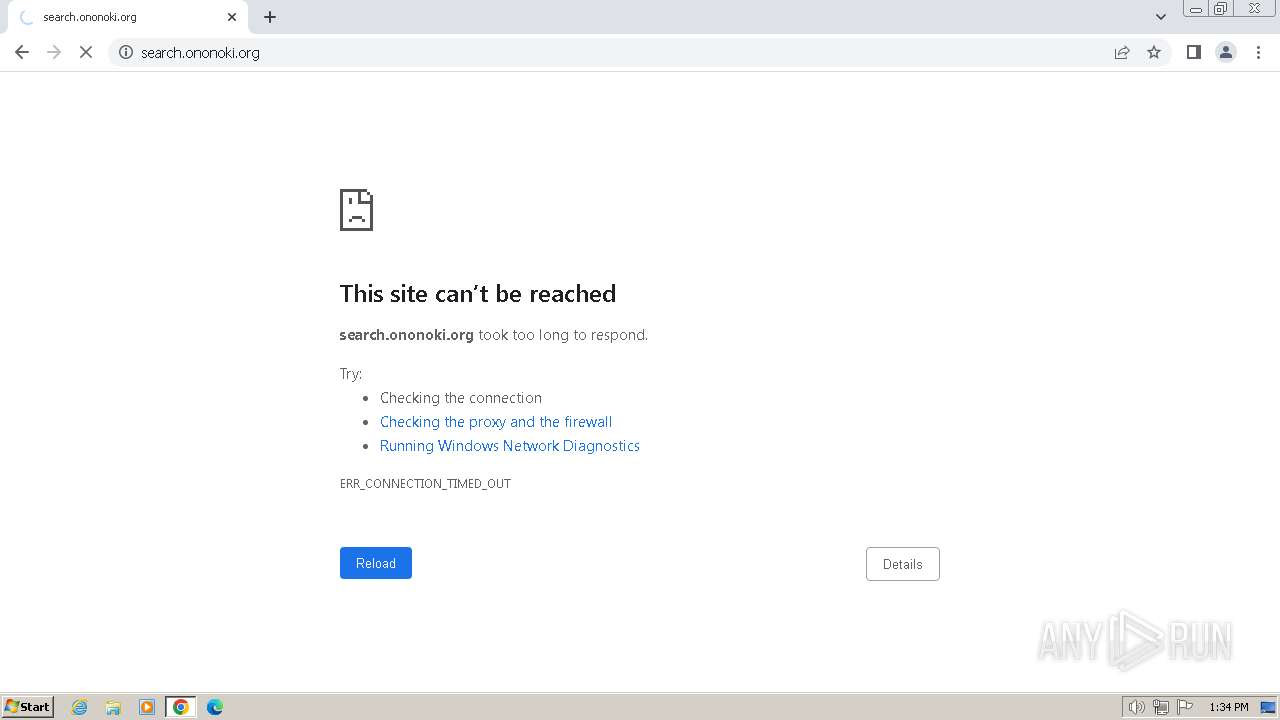
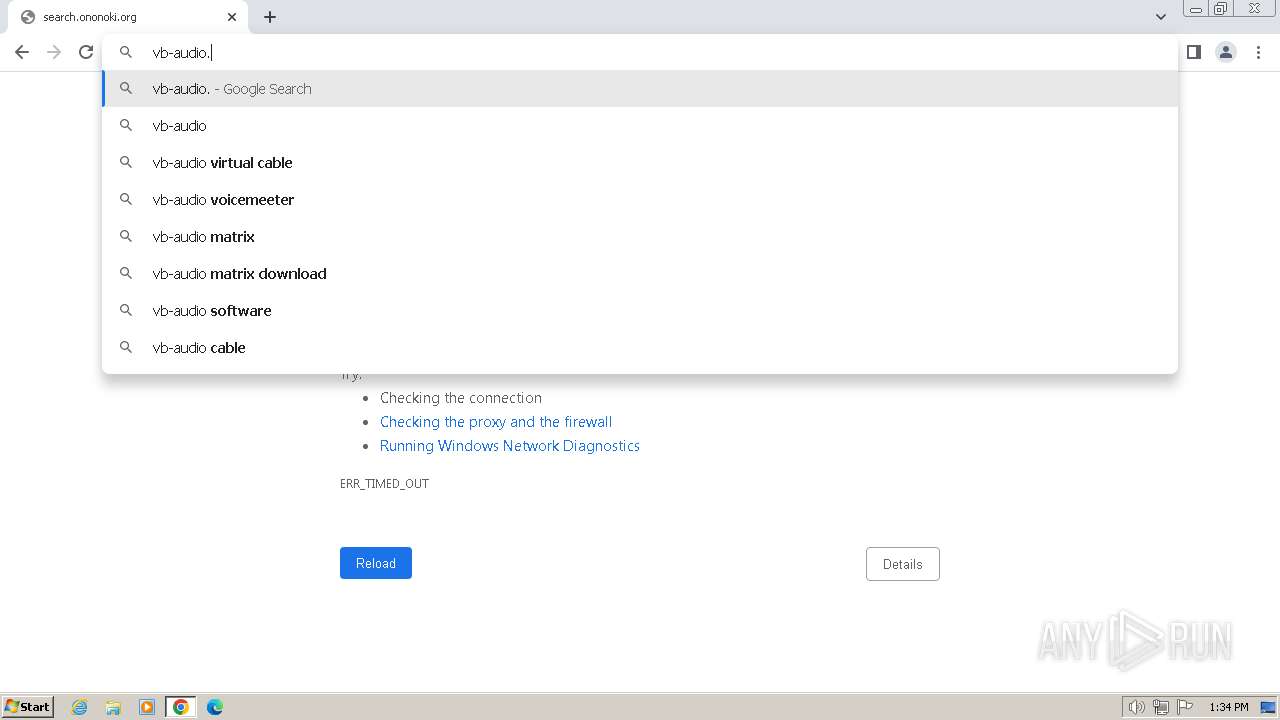
2708 | chrome.exe | GET | 308 | 148.135.82.45:80 | http://search.ononoki.org/ | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1372 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2948 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1372 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1372 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
3676 | chrome.exe | 142.250.145.84:443 | accounts.google.com | GOOGLE | US | unknown |
3676 | chrome.exe | 142.250.186.131:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |