| File name: | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc |
| Full analysis: | https://app.any.run/tasks/643f3a0b-eece-41ad-a245-e23fb0dc2499 |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 04:03:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C001CFC7570D69E16EB0AA0782F3E42E |
| SHA1: | 81D53DD12D24B04F221F796B2957720F34AA032B |
| SHA256: | FE46EB55DD70A4A5136D9F75B4E7A1F49BBFA6BC20368D00A0314B6CF5827FBC |
| SSDEEP: | 49152:W/FNliL4RLEFZ3sMlbTChxKCnFnQXBbrtgb/iQvu0UHOC:WsL46H1l6hxvWbrtUTrUHOC |
MALICIOUS
Application was dropped or rewritten from another process
- @AE7094.tmp.exe (PID: 3888)
- WdExt.exe (PID: 872)
- fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe (PID: 3500)
- launch.exe (PID: 3228)
- wtmps.exe (PID: 2068)
Changes the autorun value in the registry
- launch.exe (PID: 3228)
- mscaps.exe (PID: 3188)
Application was injected by another process
- explorer.exe (PID: 372)
Runs injected code in another process
- launch.exe (PID: 3228)
Loads dropped or rewritten executable
- @AE7094.tmp.exe (PID: 3888)
- windanr.exe (PID: 2604)
- fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe (PID: 3500)
- WdExt.exe (PID: 872)
- explorer.exe (PID: 372)
- wtmps.exe (PID: 2068)
- mscaps.exe (PID: 3188)
SUSPICIOUS
Executable content was dropped or overwritten
- explorer.exe (PID: 3316)
- @AE7094.tmp.exe (PID: 3888)
- WdExt.exe (PID: 872)
- mscaps.exe (PID: 3188)
Creates files in the user directory
- WdExt.exe (PID: 872)
- @AE7094.tmp.exe (PID: 3888)
- wtmps.exe (PID: 2068)
- launch.exe (PID: 3228)
- mscaps.exe (PID: 3188)
Starts CMD.EXE for commands execution
- @AE7094.tmp.exe (PID: 3888)
- WdExt.exe (PID: 872)
- launch.exe (PID: 3228)
Reads Internet Cache Settings
- fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe (PID: 3500)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:03:05 09:37:55+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 2560 |
| InitializedDataSize: | 444416 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x167f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.0.1 |
| ProductVersionNumber: | 1.1.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | NetDiagnosisTool Microsoft 基础类应用程序 |
| FileVersion: | 1, 1, 0, 1 |
| InternalName: | NetDiagnosisTool |
| LegalCopyright: | 版权所有 (C) 2011 |
| LegalTrademarks: | - |
| OriginalFileName: | NetDiagnosisTool.EXE |
| PrivateBuild: | - |
| ProductName: | NetDiagnosisTool 应用程序 |
| ProductVersion: | 1, 1, 0, 1 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Mar-2012 08:37:55 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | NetDiagnosisTool Microsoft 基础类应用程序 |
| FileVersion: | 1, 1, 0, 1 |
| InternalName: | NetDiagnosisTool |
| LegalCopyright: | 版权所有 (C) 2011 |
| LegalTrademarks: | - |
| OriginalFilename: | NetDiagnosisTool.EXE |
| PrivateBuild: | - |
| ProductName: | NetDiagnosisTool 应用程序 |
| ProductVersion: | 1, 1, 0, 1 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 05-Mar-2012 08:37:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000083C | 0x00000A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.43891 |
.rdata | 0x00002000 | 0x000005C6 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.85919 |
.data | 0x00003000 | 0x000BB000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.545274 |
.rsrc | 0x000BE000 | 0x0006B6D0 | 0x0006C000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.21279 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.52216 | 900 | UNKNOWN | Chinese - PRC | RT_VERSION |
2 | 2.55844 | 296 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 3.94266 | 7336 | UNKNOWN | Chinese - PRC | RT_ICON |
4 | 5.73236 | 2216 | UNKNOWN | Chinese - PRC | RT_ICON |
5 | 4.79427 | 1384 | UNKNOWN | Chinese - PRC | RT_ICON |
6 | 4.7237 | 1788 | UNKNOWN | Chinese - PRC | RT_ICON |
7 | 6.08851 | 588 | UNKNOWN | Chinese - PRC | RT_STRING |
8 | 0.570401 | 34 | UNKNOWN | Chinese - PRC | RT_STRING |
9 | 3.87799 | 744 | UNKNOWN | Chinese - PRC | RT_ICON |
10 | 3.53513 | 488 | UNKNOWN | Chinese - PRC | RT_ICON |
Imports
KERNEL32.dll |
MSVCRT.dll |
SHELL32.dll |
USER32.dll |
Total processes
49
Monitored processes
14
Malicious processes
8
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 872 | "C:\Users\admin\AppData\Roaming\Microsoft\Messenger\Extension\WdExt.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Messenger\Extension\WdExt.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Defender Extension Exit code: 1 Version: 6.1.7600.16385 Modules
| |||||||||||||||
| 2068 | "C:\Users\admin\AppData\Local\Temp\wtmps.exe" | C:\Users\admin\AppData\Local\Temp\wtmps.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2404 | cmd /c ""C:\Users\admin\AppData\Roaming\Temp\admin0.bat" " | C:\Windows\system32\cmd.exe | — | @AE7094.tmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2604 | "windanr.exe" | C:\Windows\system32\windanr.exe | — | qemu-ga.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2700 | cmd /c ""C:\Users\admin\AppData\Roaming\Temp\admin1.bat" " | C:\Windows\system32\cmd.exe | — | WdExt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3096 | cmd /c ""C:\Users\admin\AppData\Roaming\Temp\admin0.bat" " | C:\Windows\system32\cmd.exe | — | launch.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3188 | "C:\Users\admin\AppData\Roaming\Microsoft\Protect\SETUP\mscaps.exe" /C:\Users\admin\AppData\Local\Temp\wtmps.exe | C:\Users\admin\AppData\Roaming\Microsoft\Protect\SETUP\mscaps.exe | wtmps.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3228 | "C:\Users\admin\AppData\Roaming\Microsoft\Defender\launch.exe" /i 872 | C:\Users\admin\AppData\Roaming\Microsoft\Defender\launch.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Nt Module Starter Exit code: 1 Version: 6.1.7600.16385 Modules
| |||||||||||||||
| 3316 | explorer.exe | C:\Windows\explorer.exe | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 506
Read events
1 451
Write events
55
Delete events
0
Modification events
| (PID) Process: | (2604) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | APPSTARTING |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2604) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | ARROW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2604) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | CROSS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2604) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HAND |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2604) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HELP |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2604) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | IBEAM |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2604) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | NO |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2604) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZEALL |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2604) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENESW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2604) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
Executable files
22
Suspicious files
1
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3888 | @AE7094.tmp.exe | C:\Users\admin\AppData\Local\Temp\tmp722B.tmp | — | |
MD5:— | SHA256:— | |||
| 3888 | @AE7094.tmp.exe | C:\Users\admin\AppData\Local\Temp\Sp727A.tmp | — | |
MD5:— | SHA256:— | |||
| 3888 | @AE7094.tmp.exe | C:\Users\admin\AppData\Local\Temp\Se727B.tmp | — | |
MD5:— | SHA256:— | |||
| 3888 | @AE7094.tmp.exe | C:\Users\admin\AppData\Roaming\Temp\admin1.bat | — | |
MD5:— | SHA256:— | |||
| 872 | WdExt.exe | C:\Users\admin\AppData\Local\Temp\tmp74AB.tmp | — | |
MD5:— | SHA256:— | |||
| 872 | WdExt.exe | C:\Users\admin\AppData\Local\Temp\tmp74CC.tmp | — | |
MD5:— | SHA256:— | |||
| 872 | WdExt.exe | C:\Users\admin\AppData\Local\Temp\tmp74CD.tmp | — | |
MD5:— | SHA256:— | |||
| 872 | WdExt.exe | C:\Users\admin\AppData\Local\Temp\tmp74DD.tmp | — | |
MD5:— | SHA256:— | |||
| 872 | WdExt.exe | C:\Users\admin\AppData\Local\Temp\tmp74DE.tmp | — | |
MD5:— | SHA256:— | |||
| 872 | WdExt.exe | C:\Users\admin\AppData\Local\Temp\tmp74EF.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
15
DNS requests
15
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
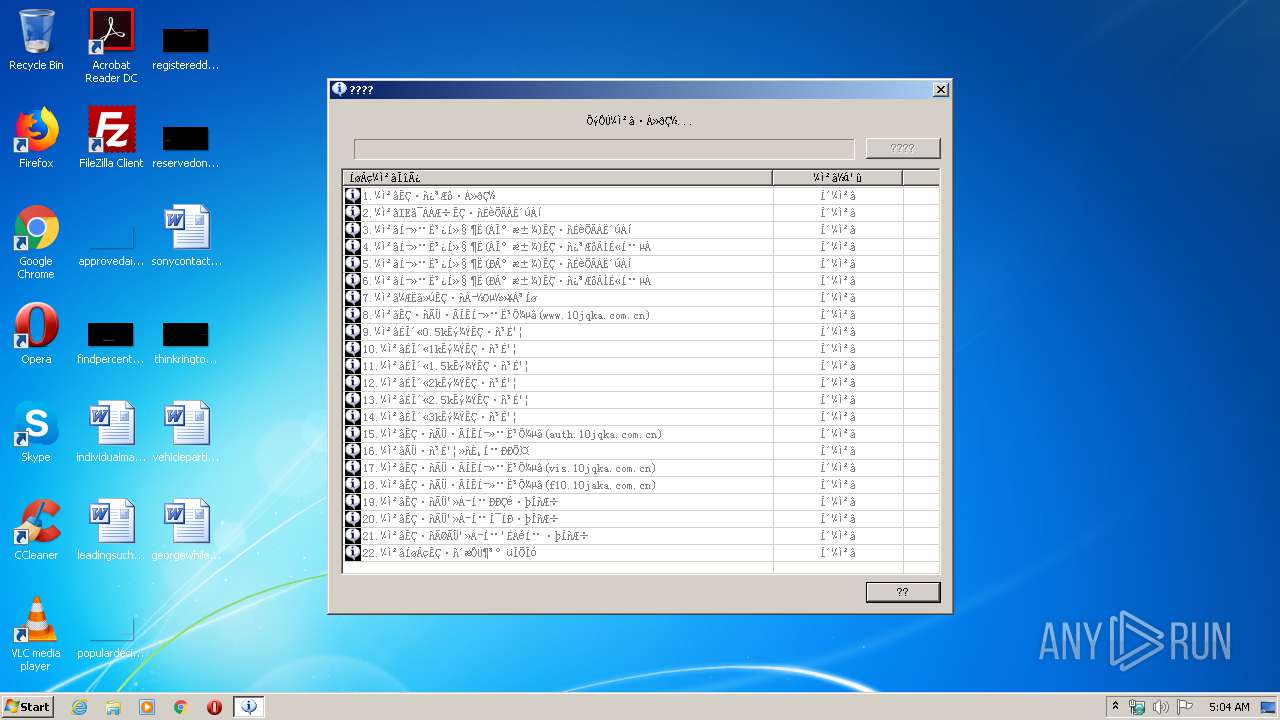
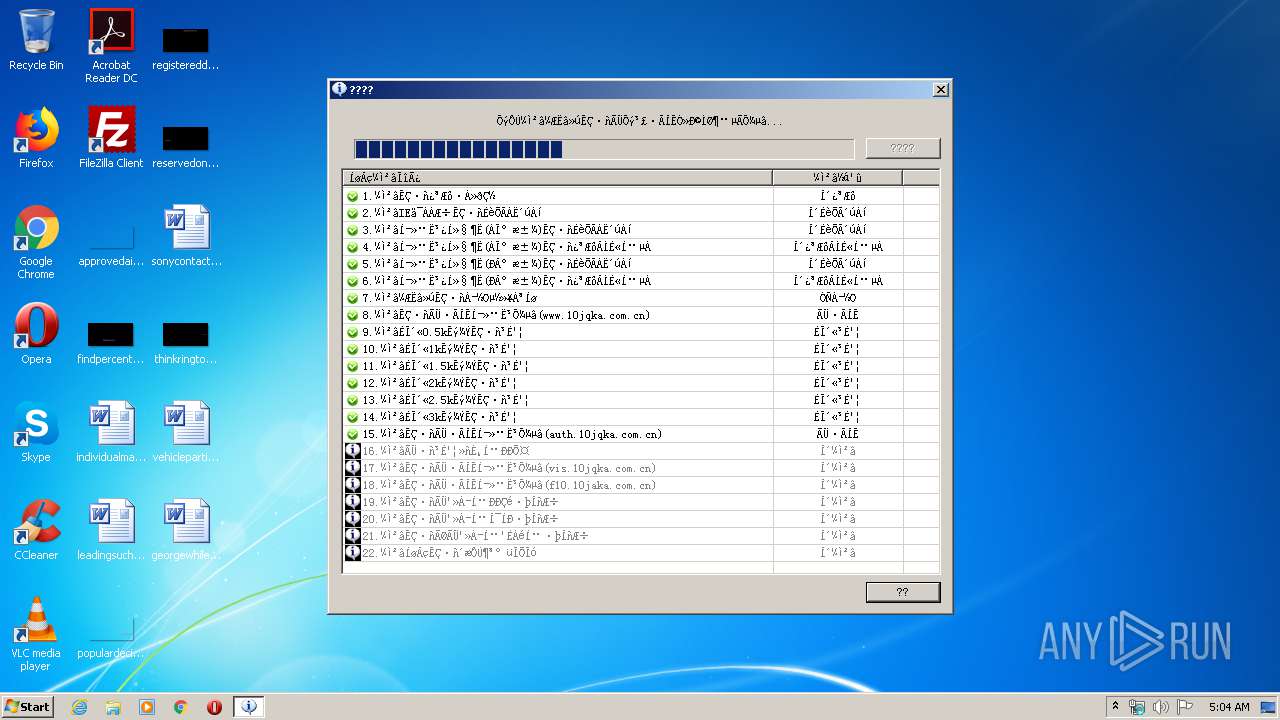
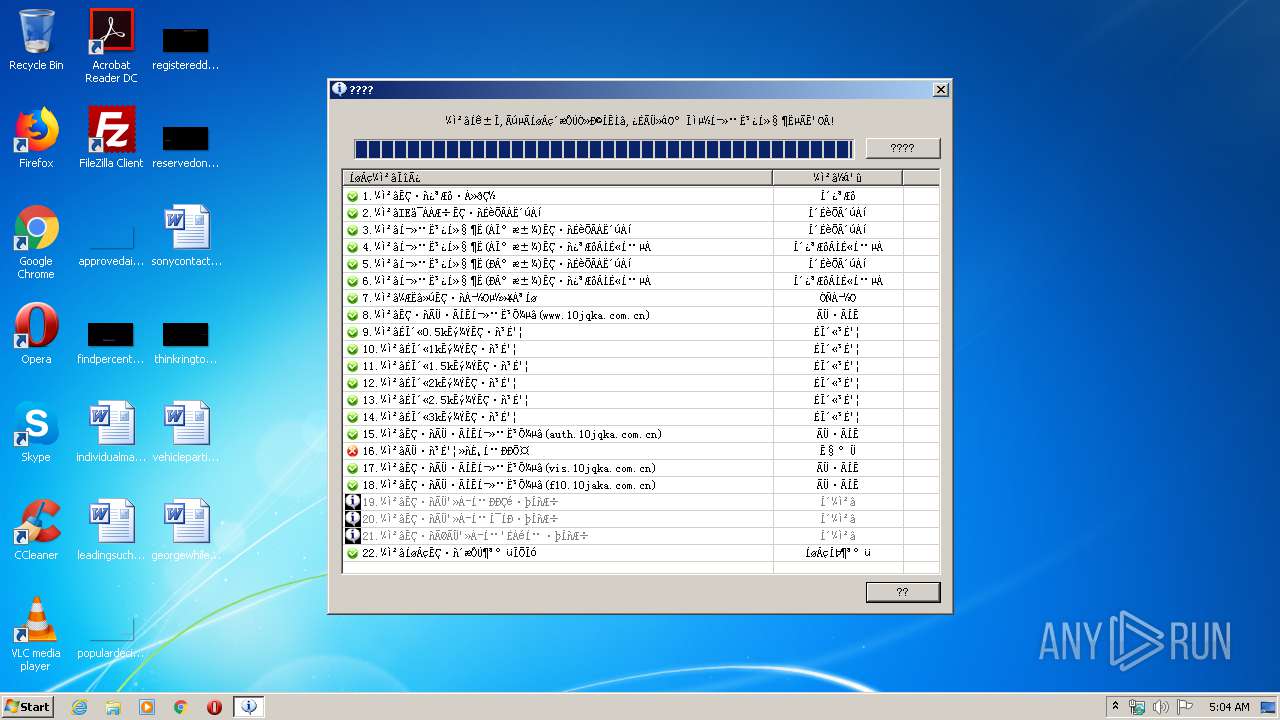
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | POST | 200 | 183.131.12.246:80 | http://www.10jqka.com.cn/ceshi.php | CN | html | 1.10 Kb | suspicious |
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | POST | 200 | 121.201.108.220:80 | http://www.10jqka.com.cn/ceshi.php | CN | html | 1.10 Kb | suspicious |
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | POST | 200 | 61.147.165.140:80 | http://www.10jqka.com.cn/ceshi.php | CN | html | 1.10 Kb | suspicious |
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | POST | 200 | 61.147.165.142:80 | http://www.10jqka.com.cn/ceshi.php | CN | html | 1.10 Kb | suspicious |
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | POST | 200 | 183.131.12.187:80 | http://www.10jqka.com.cn/ceshi.php | CN | html | 1.10 Kb | suspicious |
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | POST | 200 | 119.97.156.106:80 | http://www.10jqka.com.cn/ceshi.php | CN | html | 1.10 Kb | suspicious |
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | POST | 200 | 122.224.106.14:80 | http://auth.10jqka.com.cn/verify | CN | xml | 164 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | 61.147.165.140:80 | www.10jqka.com.cn | AS Number for CHINANET jiangsu province backbone | CN | suspicious |
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | 183.131.12.246:80 | www.10jqka.com.cn | No.31,Jin-rong Street | CN | suspicious |
372 | explorer.exe | 151.80.13.35:53 | a.gwas.perl.sh | OVH SAS | FR | malicious |
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | 121.201.108.220:80 | www.10jqka.com.cn | Guangdong | CN | suspicious |
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | 183.131.12.187:80 | www.10jqka.com.cn | No.31,Jin-rong Street | CN | suspicious |
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | 122.224.106.14:80 | auth.10jqka.com.cn | No.288,Fu-chun Road | CN | suspicious |
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | 122.228.73.238:80 | www.10jqka.com.cn | CHINANET Sichuan province Chengdu MAN network | CN | unknown |
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | 122.228.73.237:80 | www.10jqka.com.cn | CHINANET Sichuan province Chengdu MAN network | CN | unknown |
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | 119.97.156.106:80 | www.10jqka.com.cn | No.31,Jin-rong Street | CN | suspicious |
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | 61.147.165.142:80 | www.10jqka.com.cn | AS Number for CHINANET jiangsu province backbone | CN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
windowsupdate.microsoft.com |
| malicious |
www.10jqka.com.cn |
| suspicious |
update.microsoft.com |
| whitelisted |
a.gwas.perl.sh |
| malicious |
a6ppymYKqCxnxmeGBgaG6AaG6Ek.g.s |
| unknown |
auth.10jqka.com.cn |
| suspicious |
vis.10jqka.com.cn |
| suspicious |
f10.10jqka.com.cn |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | Potential Corporate Privacy Violation | ET POLICY Suspicious Malformed Double Accept Header |
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | Potential Corporate Privacy Violation | ET POLICY Suspicious Malformed Double Accept Header |
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | Potential Corporate Privacy Violation | ET POLICY Suspicious Malformed Double Accept Header |
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | Potential Corporate Privacy Violation | ET POLICY Suspicious Malformed Double Accept Header |
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | Potential Corporate Privacy Violation | ET POLICY Suspicious Malformed Double Accept Header |
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | Potential Corporate Privacy Violation | ET POLICY Suspicious Malformed Double Accept Header |
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | Potential Corporate Privacy Violation | ET POLICY Suspicious Malformed Double Accept Header |
3500 | fe46eb55dd70a4a5136d9f75b4e7a1f49bbfa6bc20368d00a0314b6cf5827fbc.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains passwd= in cleartext |