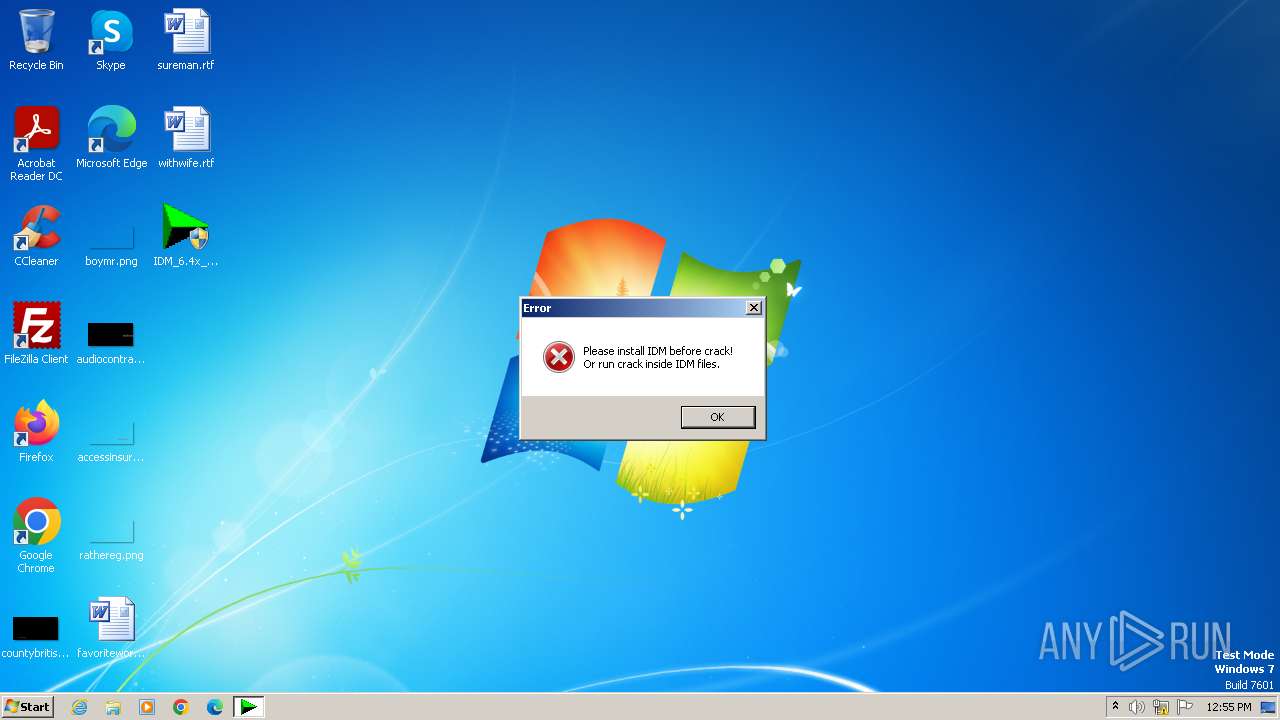
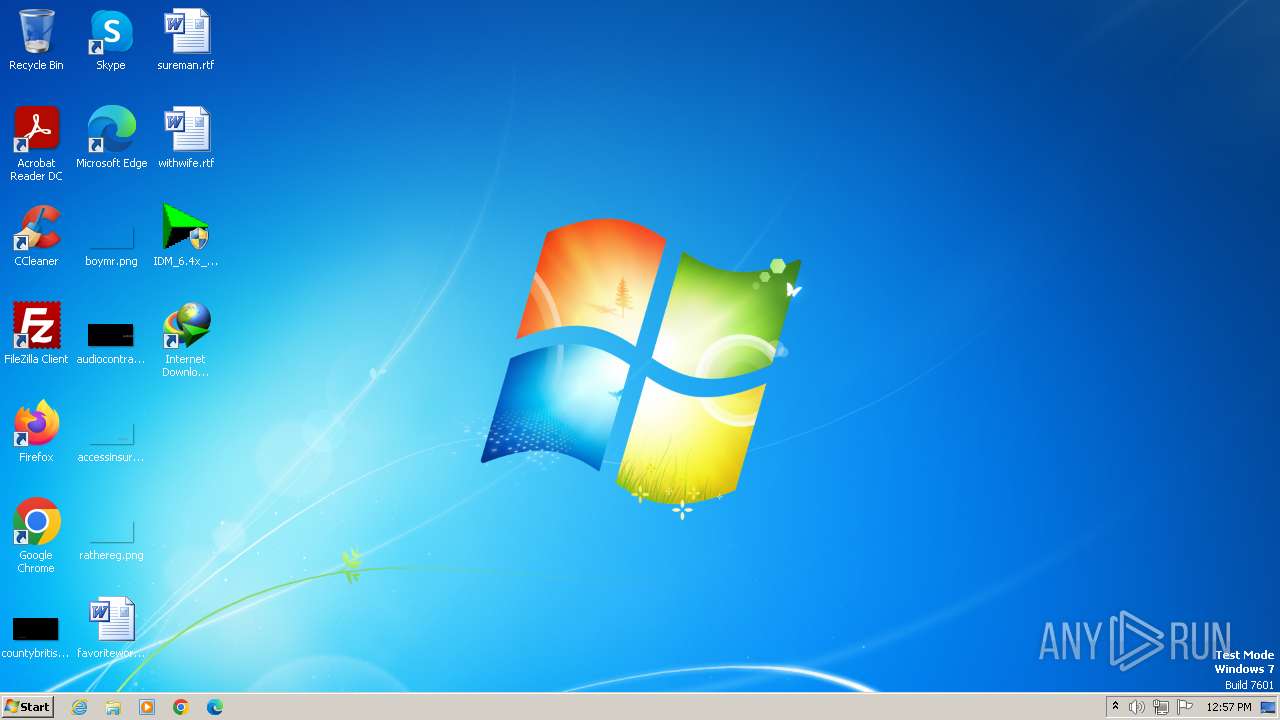
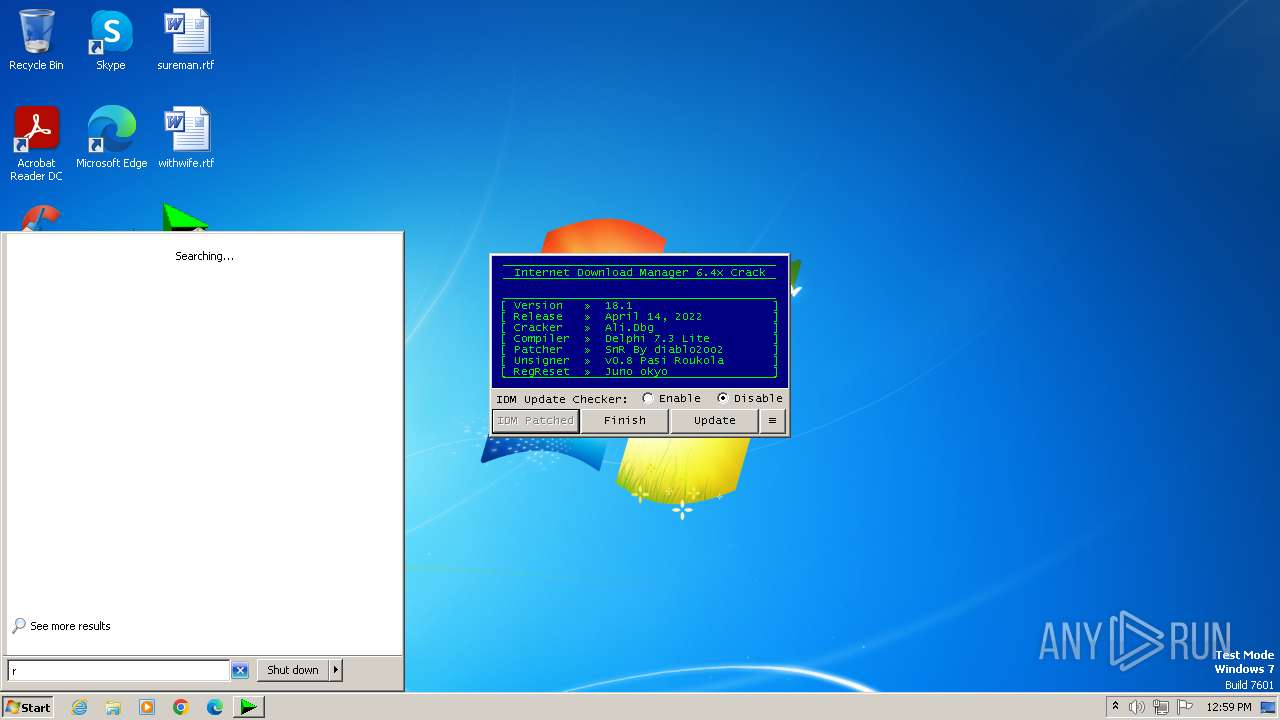
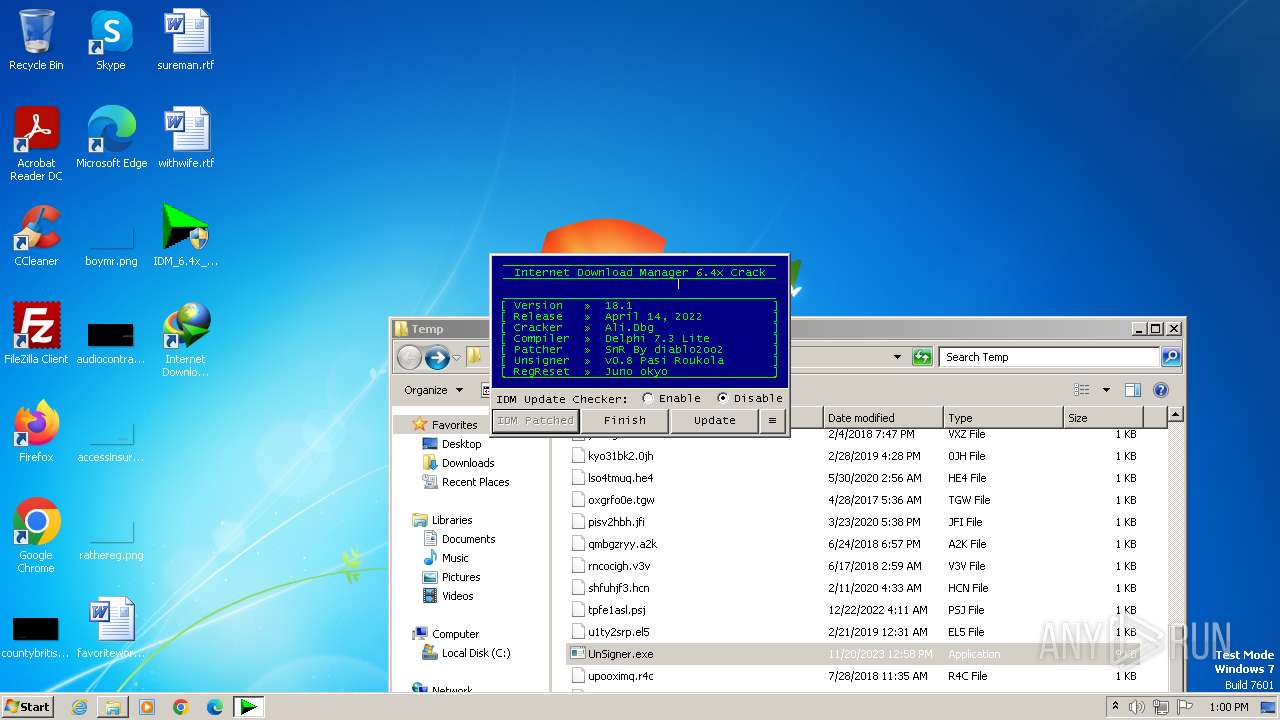
| File name: | IDM_6.4x_Crack_v18.1.exe |
| Full analysis: | https://app.any.run/tasks/75a0596a-e46e-416d-87bc-5b11ebb35aff |
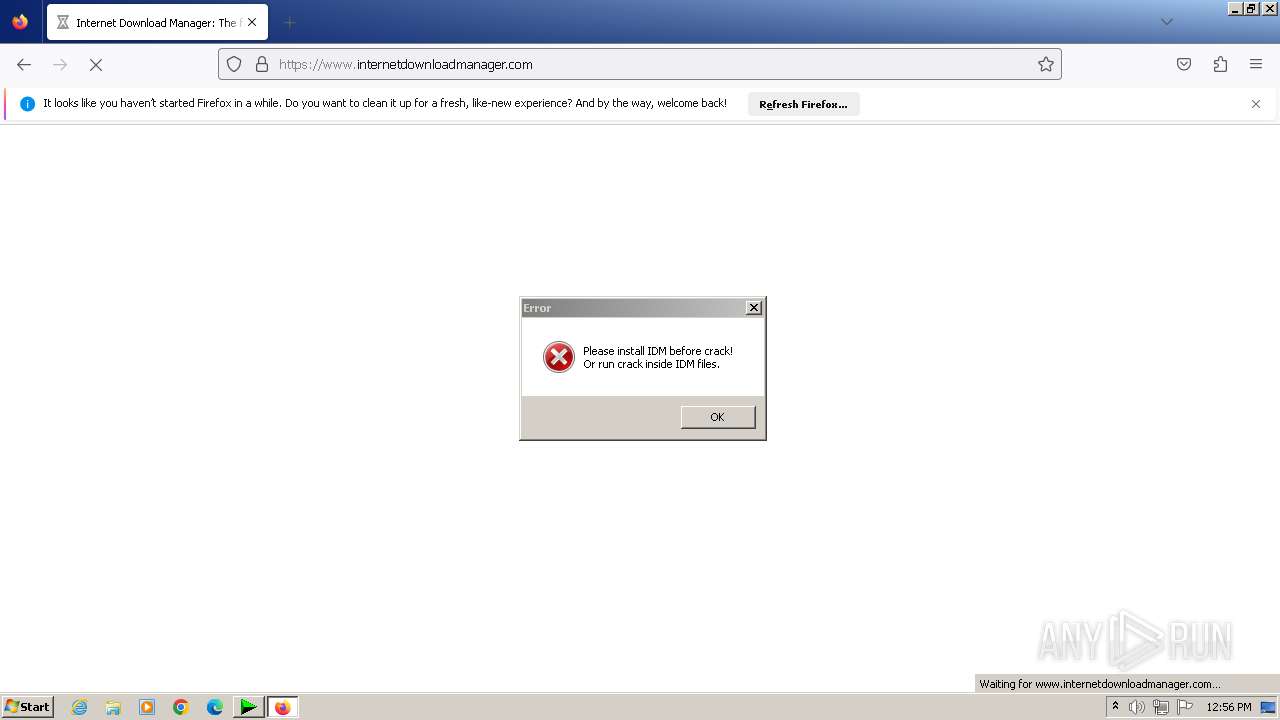
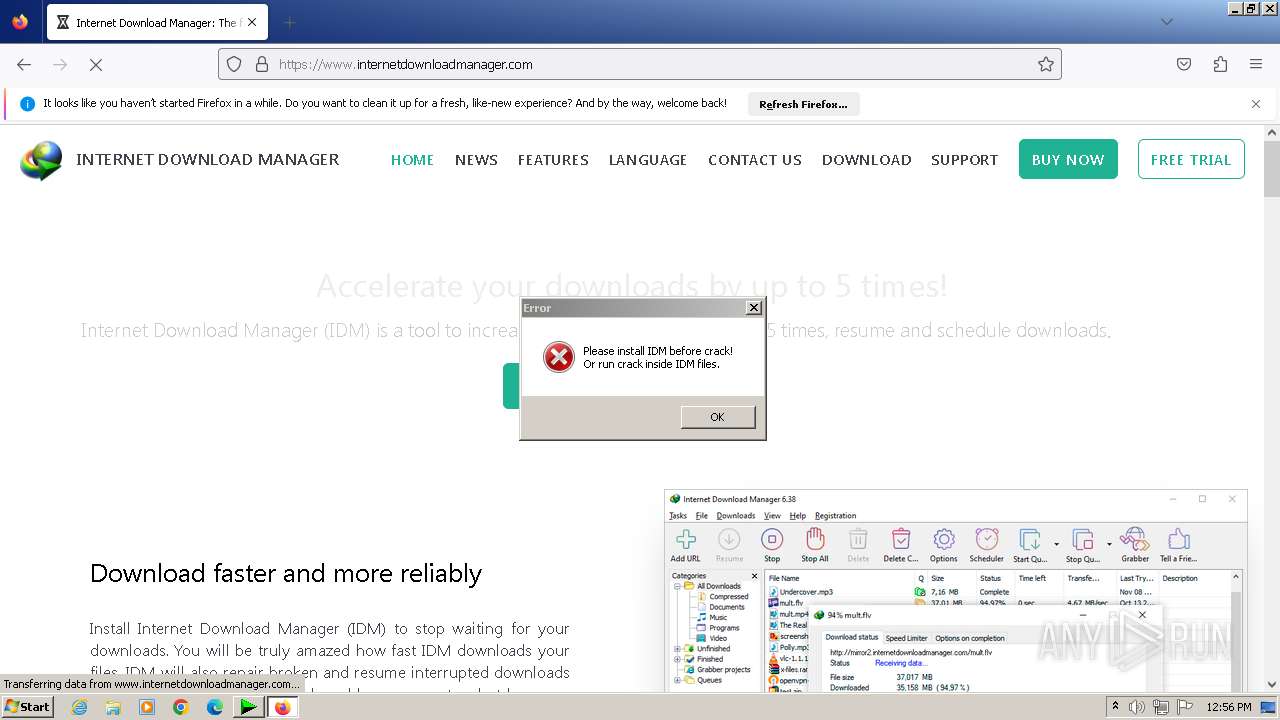
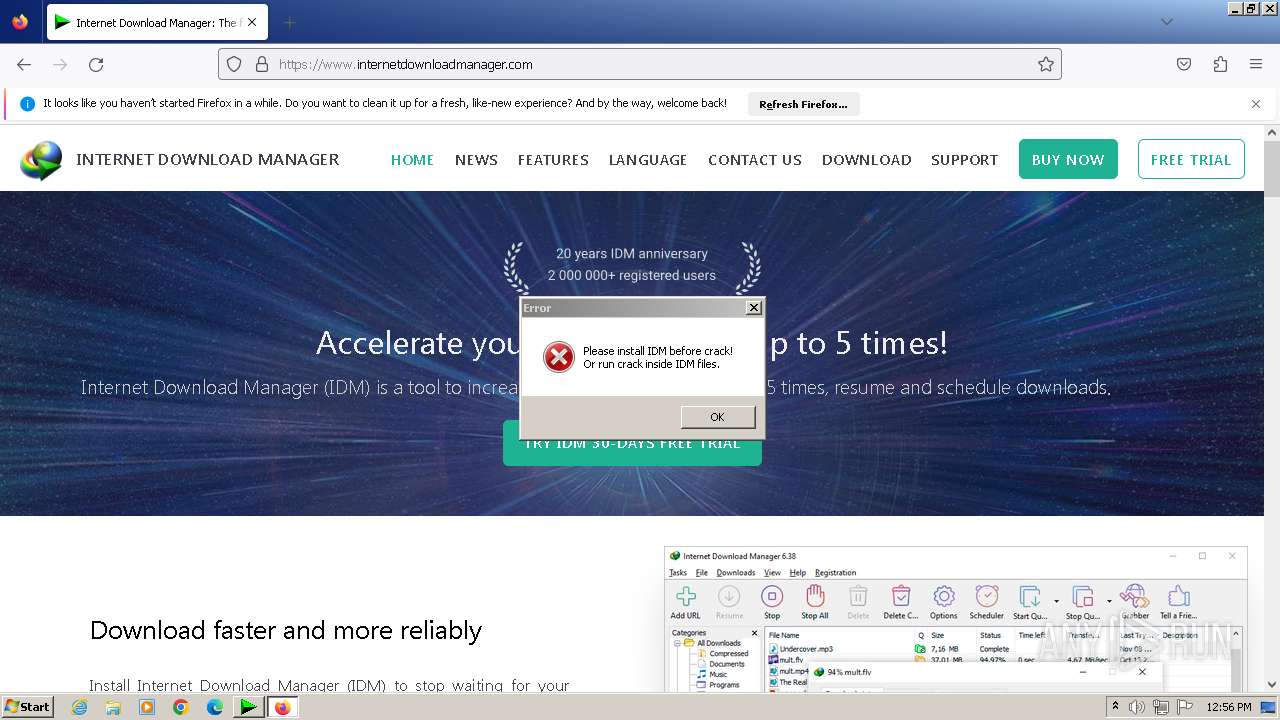
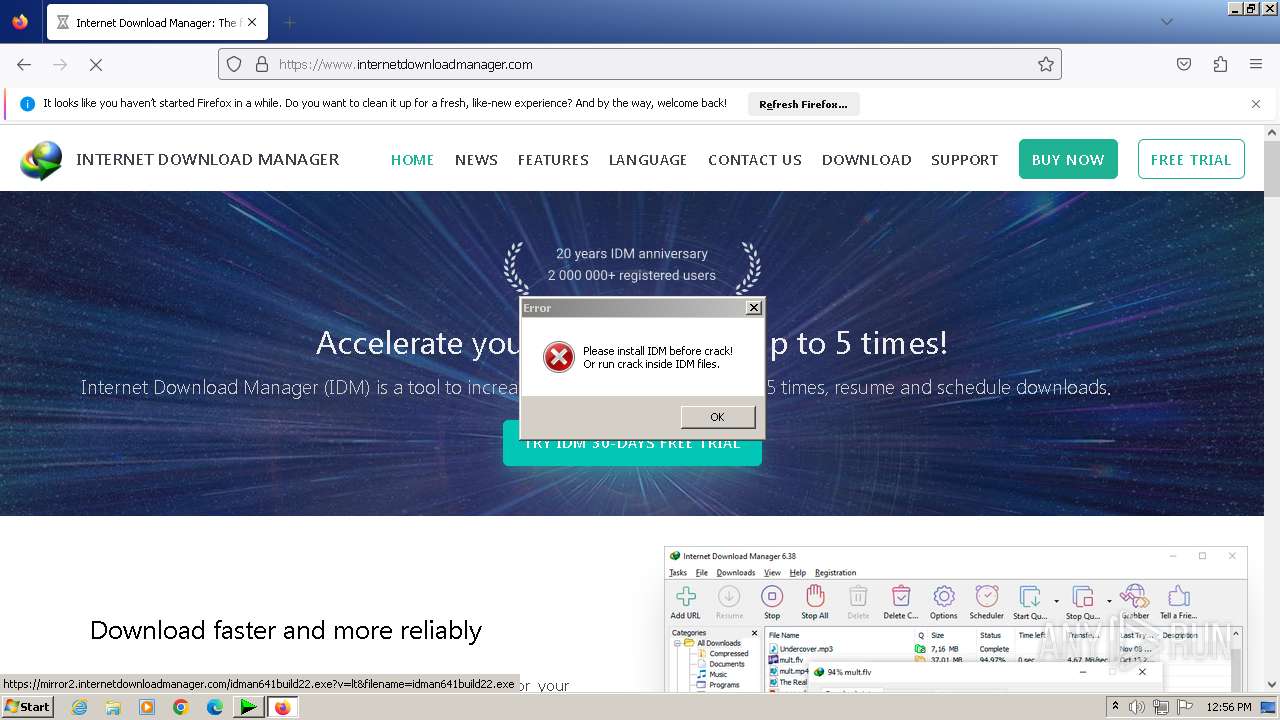
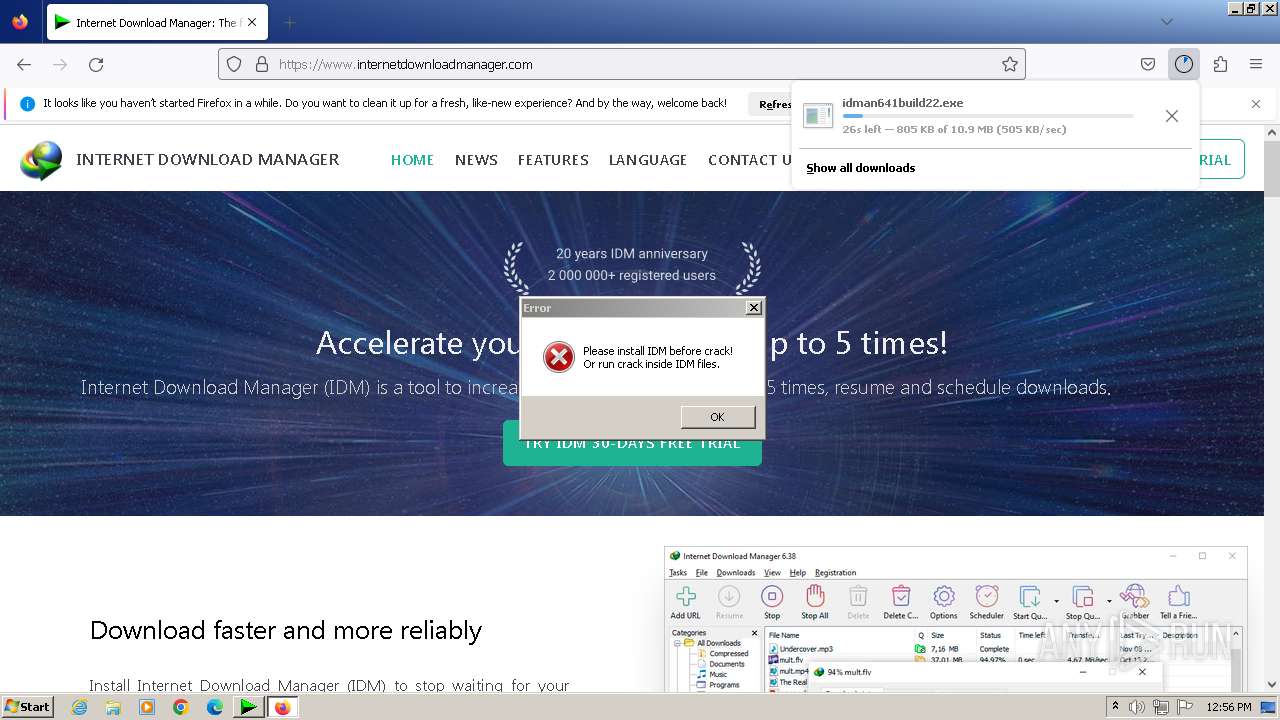
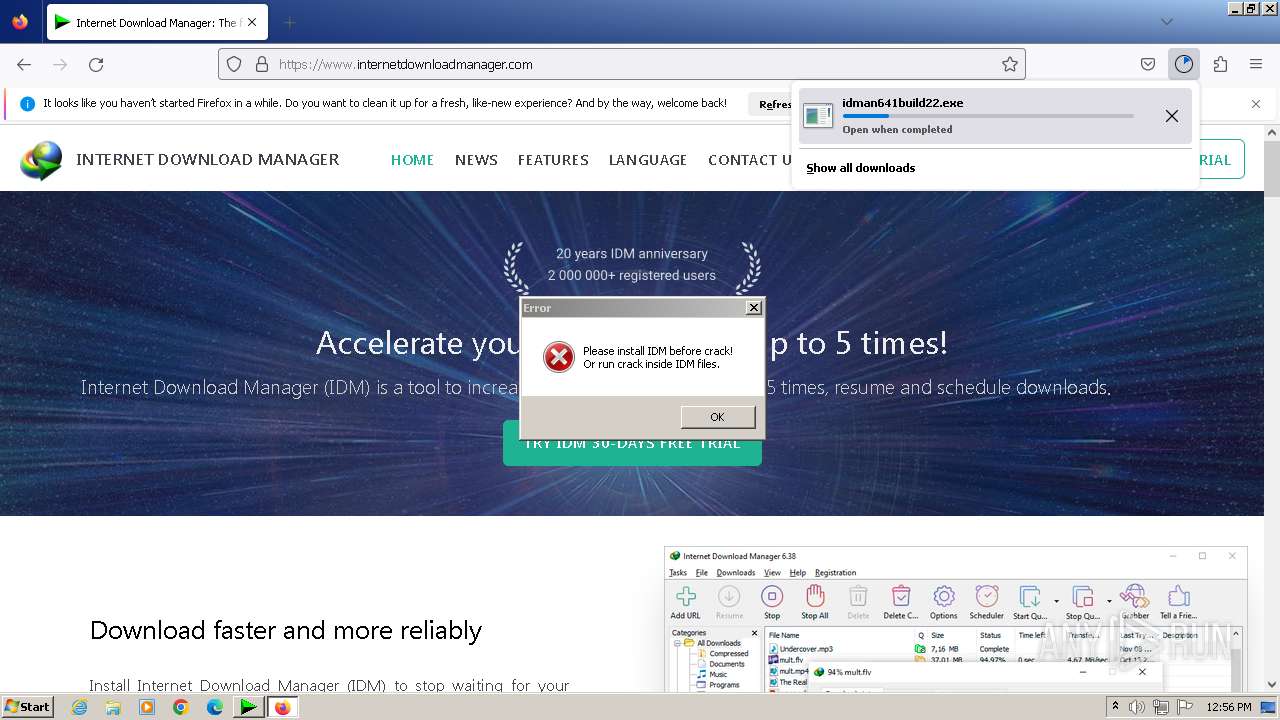
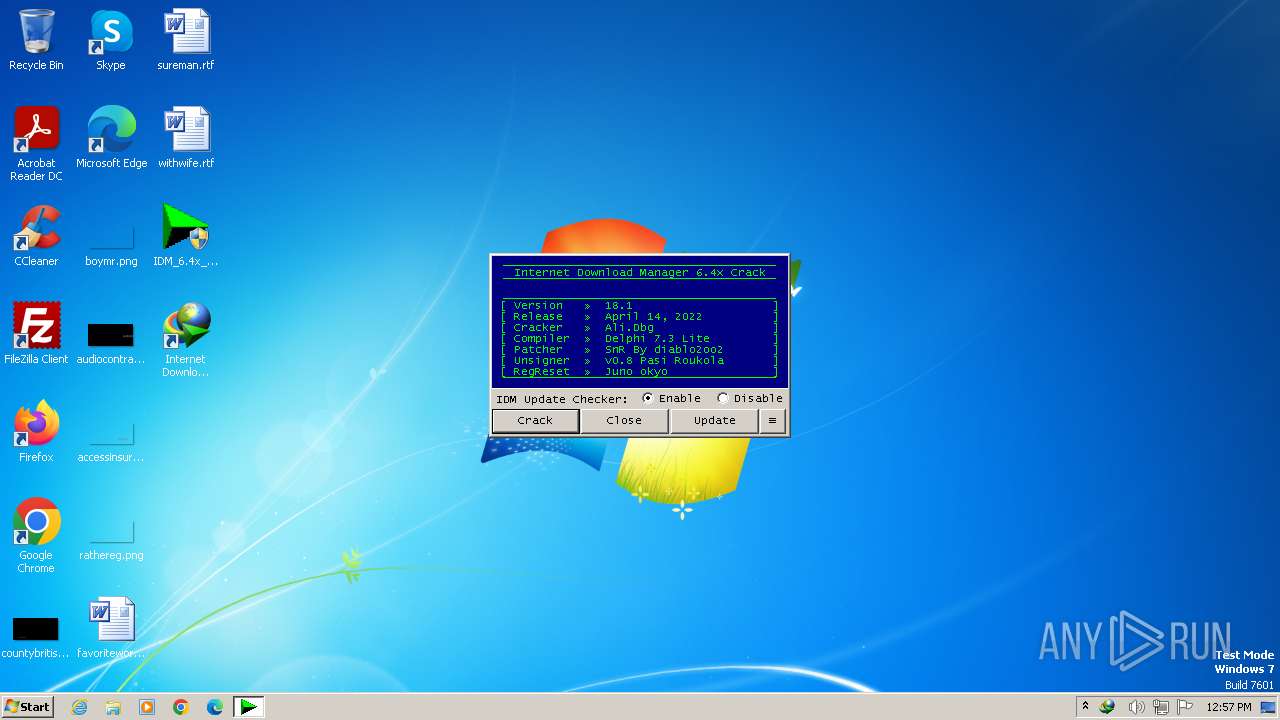
| Verdict: | Malicious activity |
| Analysis date: | November 20, 2023, 12:55:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DCDC109069B6E0D80D776C143FECDE3F |
| SHA1: | 761589C94BA8C2FD57D3AE9666A0FDC0D1B72EB5 |
| SHA256: | FE44F050AB9EA33F87ACEF449ED57157A331A19956207D6243522676C894E284 |
| SSDEEP: | 768:Jfs8N18U/TZklIrB/zkHsXaH61xxpBf/0y1gGAT/ZHgf4sMM34zCT1TyM:lrf9kY7kyaE8DzjCf4sMM0CFyM |
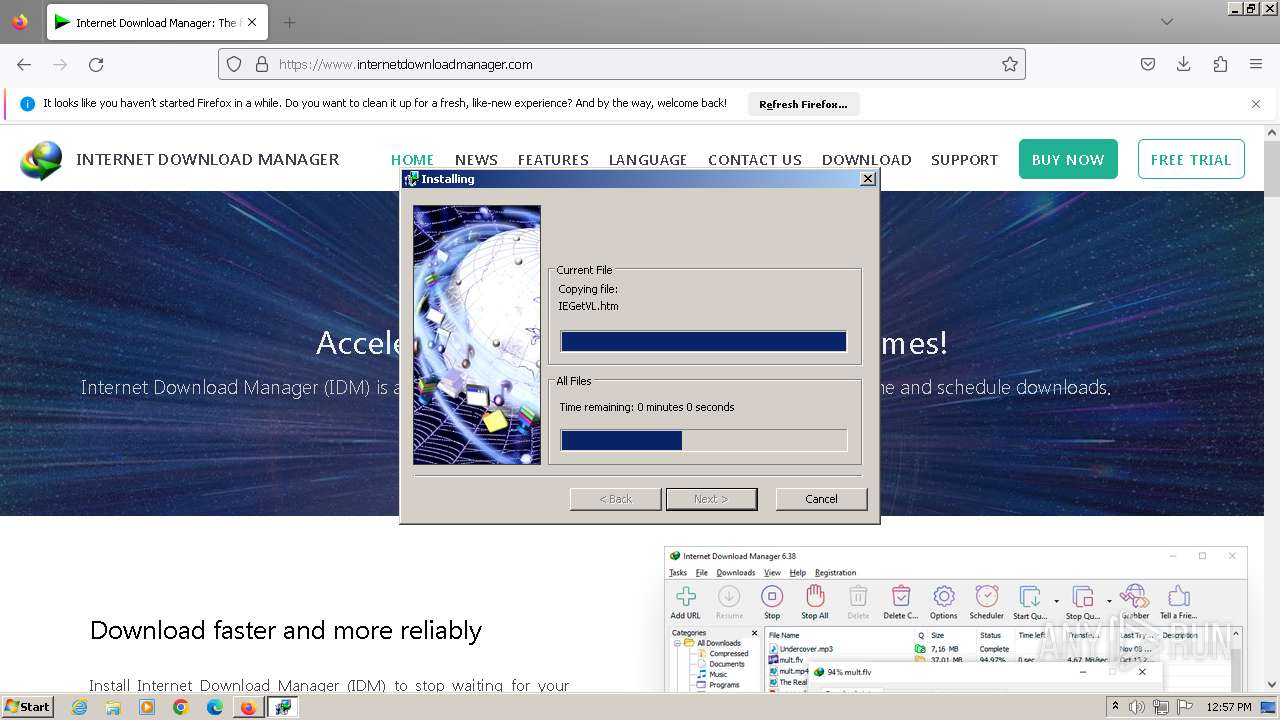
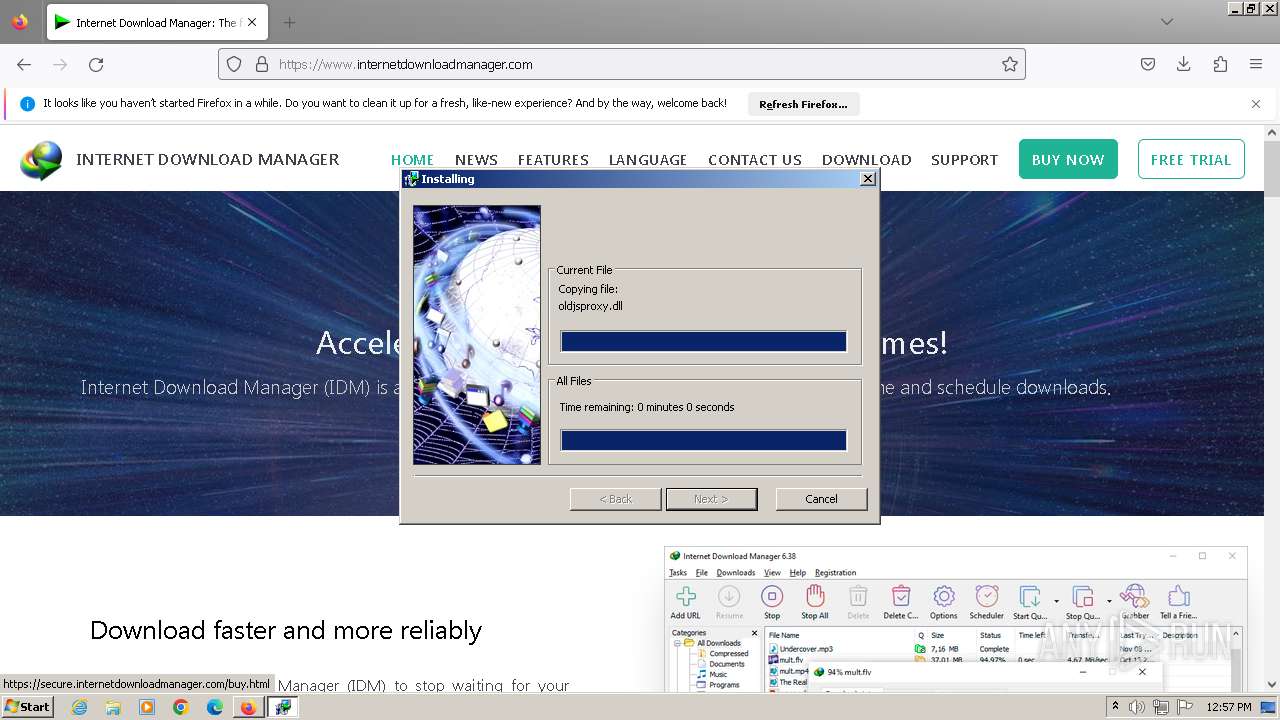
MALICIOUS
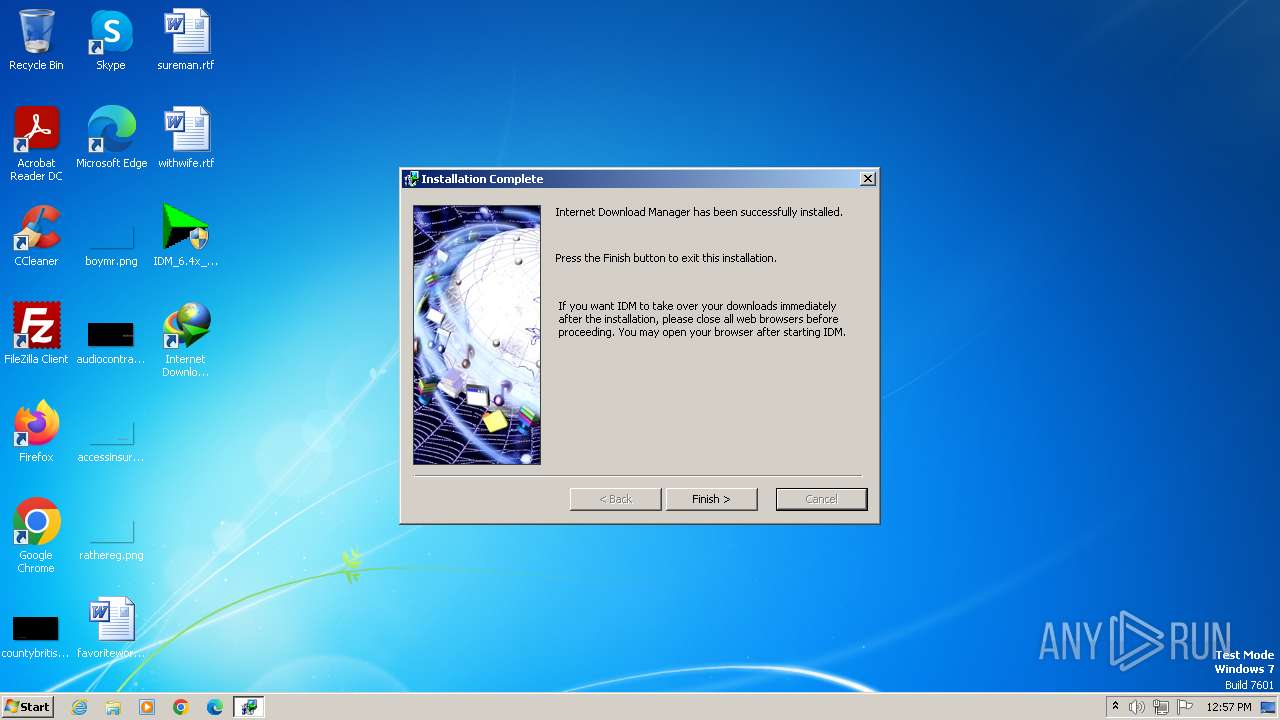
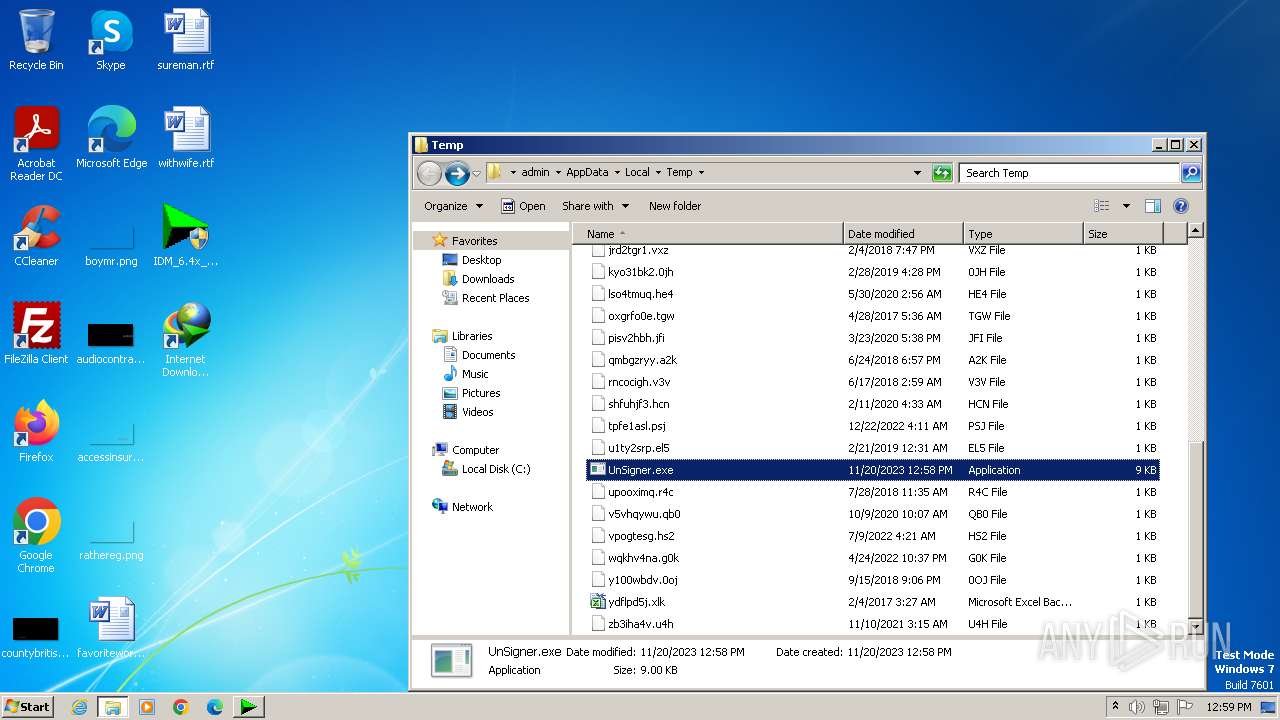
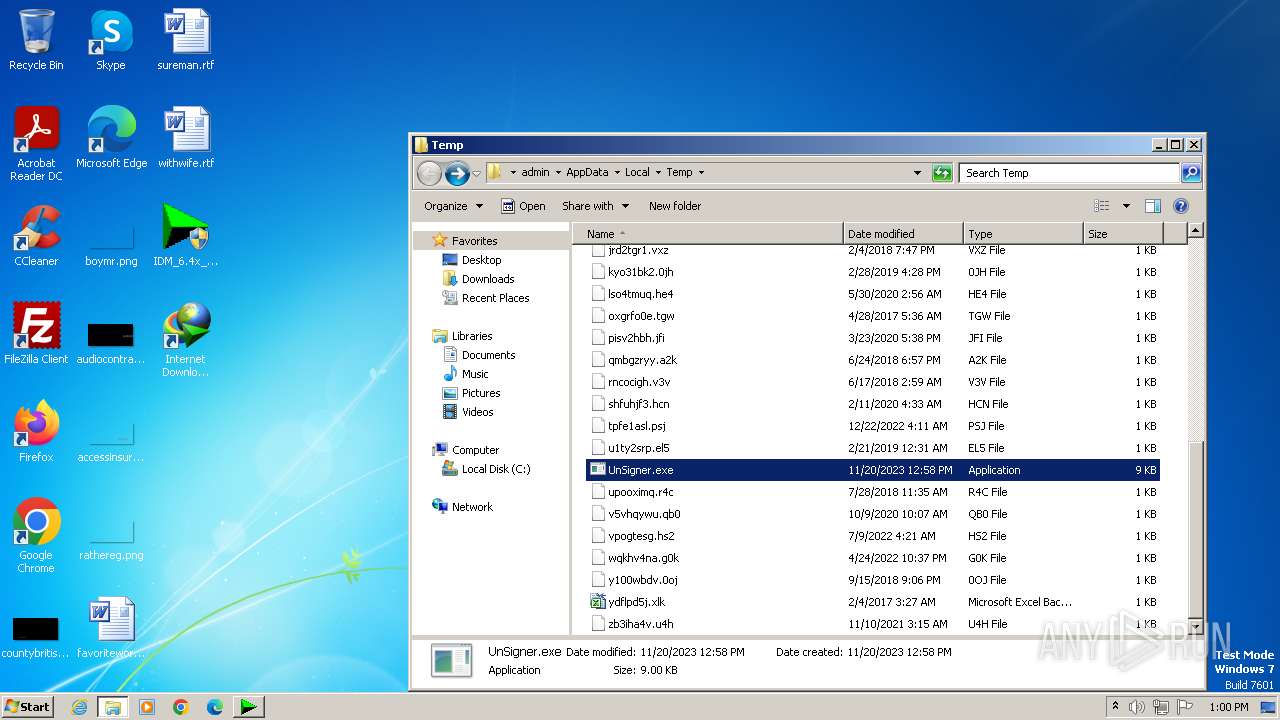
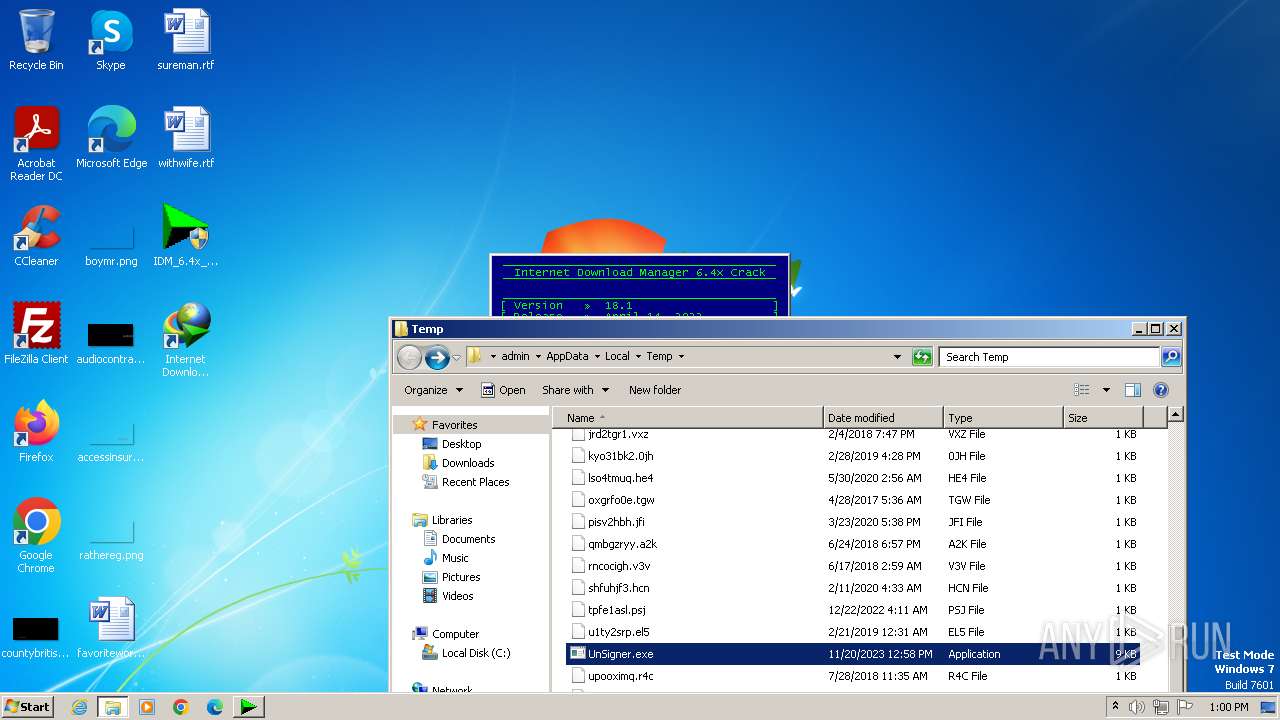
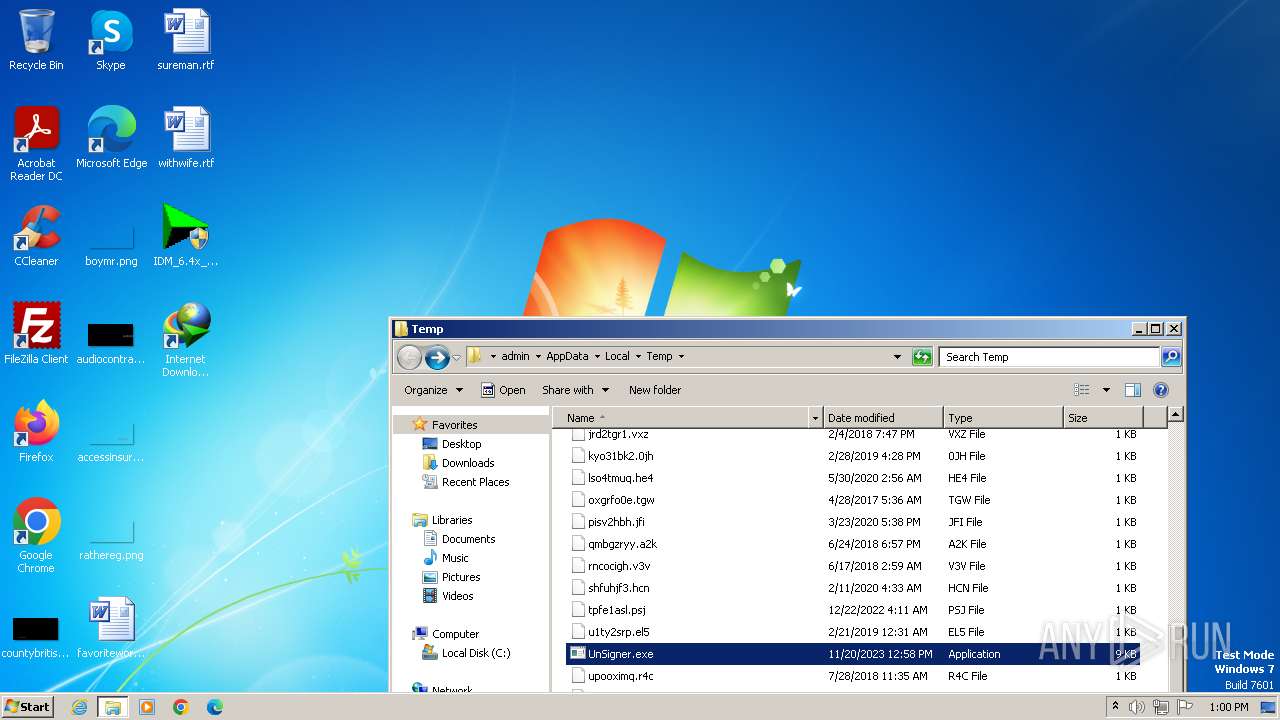
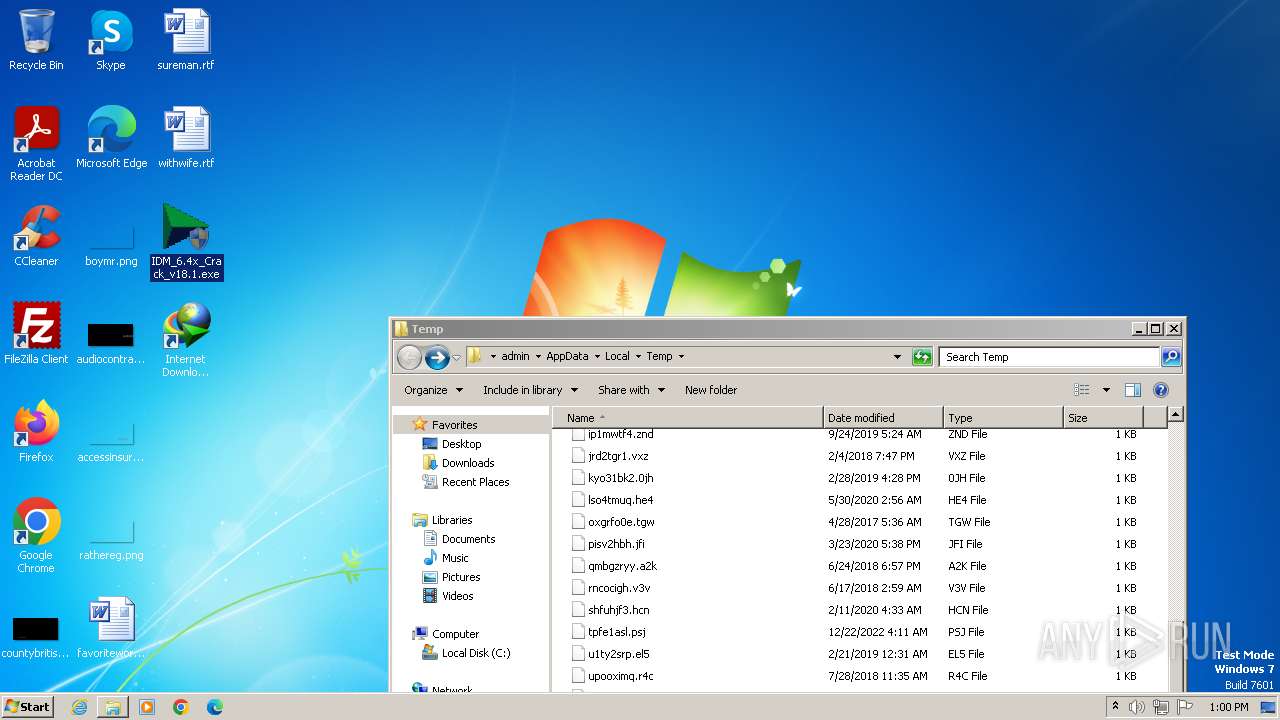
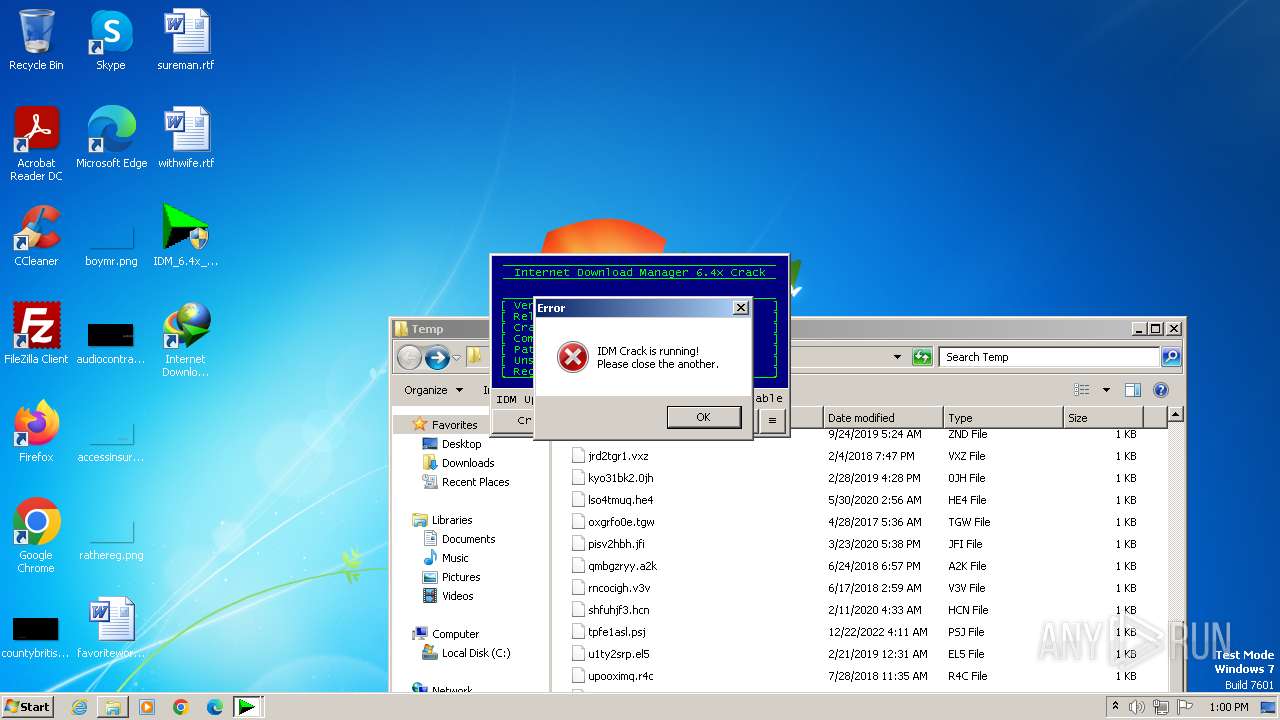
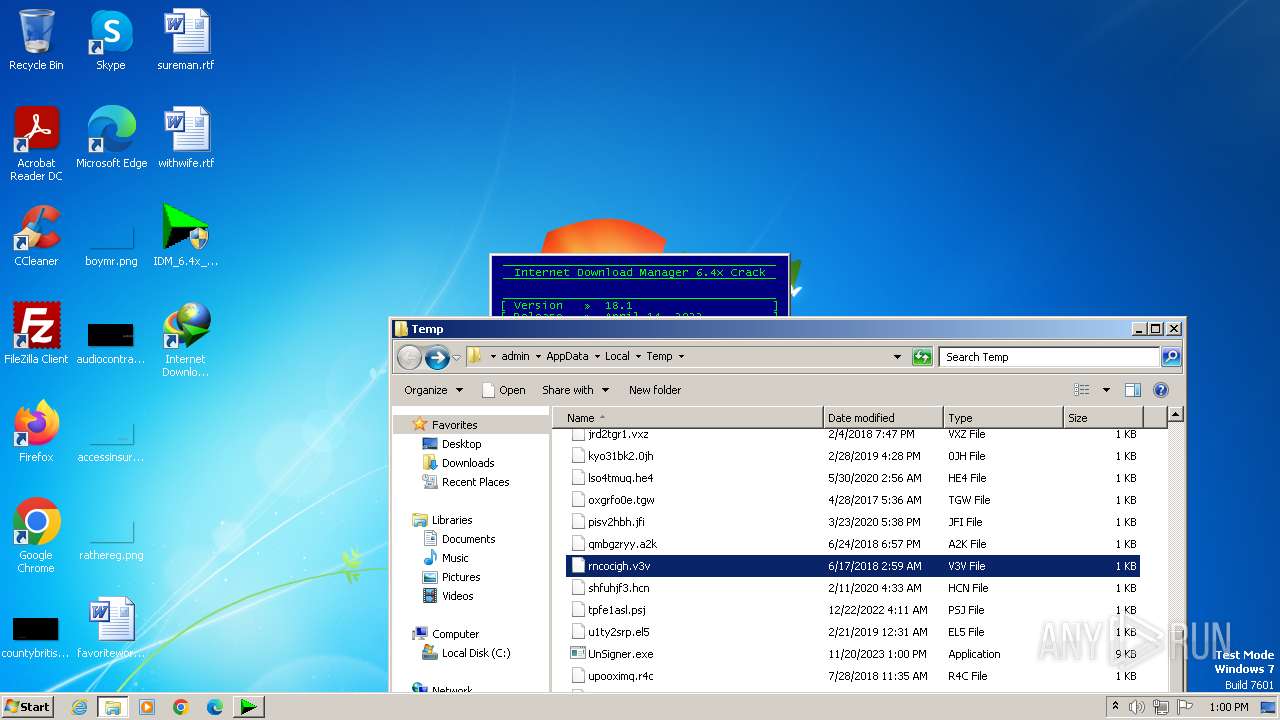
Drops the executable file immediately after the start
- IDMan.exe (PID: 2820)
- IDM_6.4x_Crack_v18.1.exe (PID: 1028)
- wscript.exe (PID: 3388)
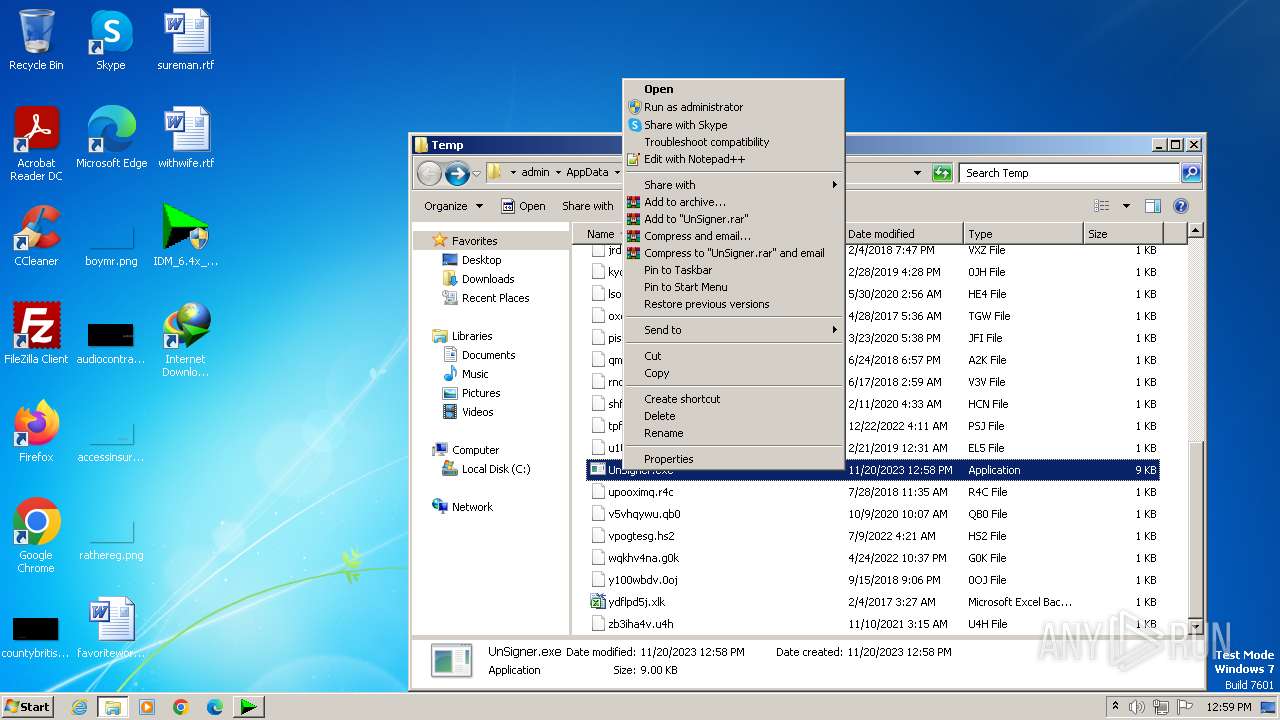
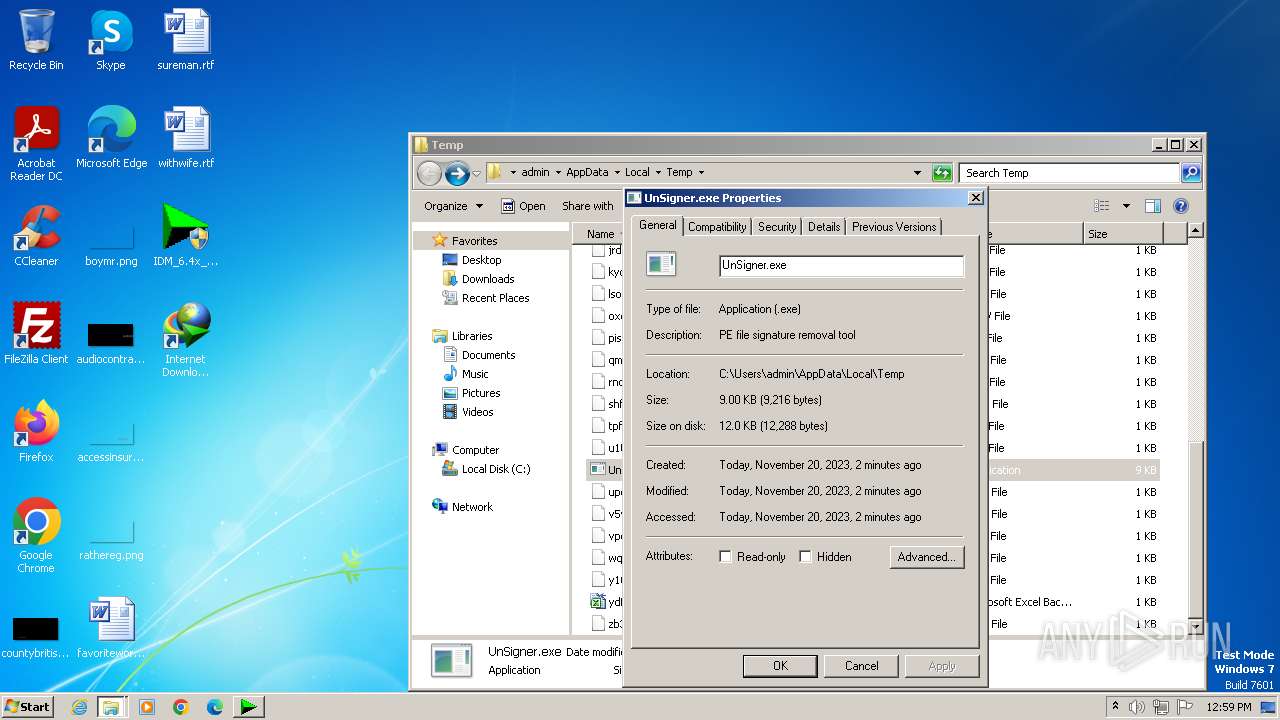
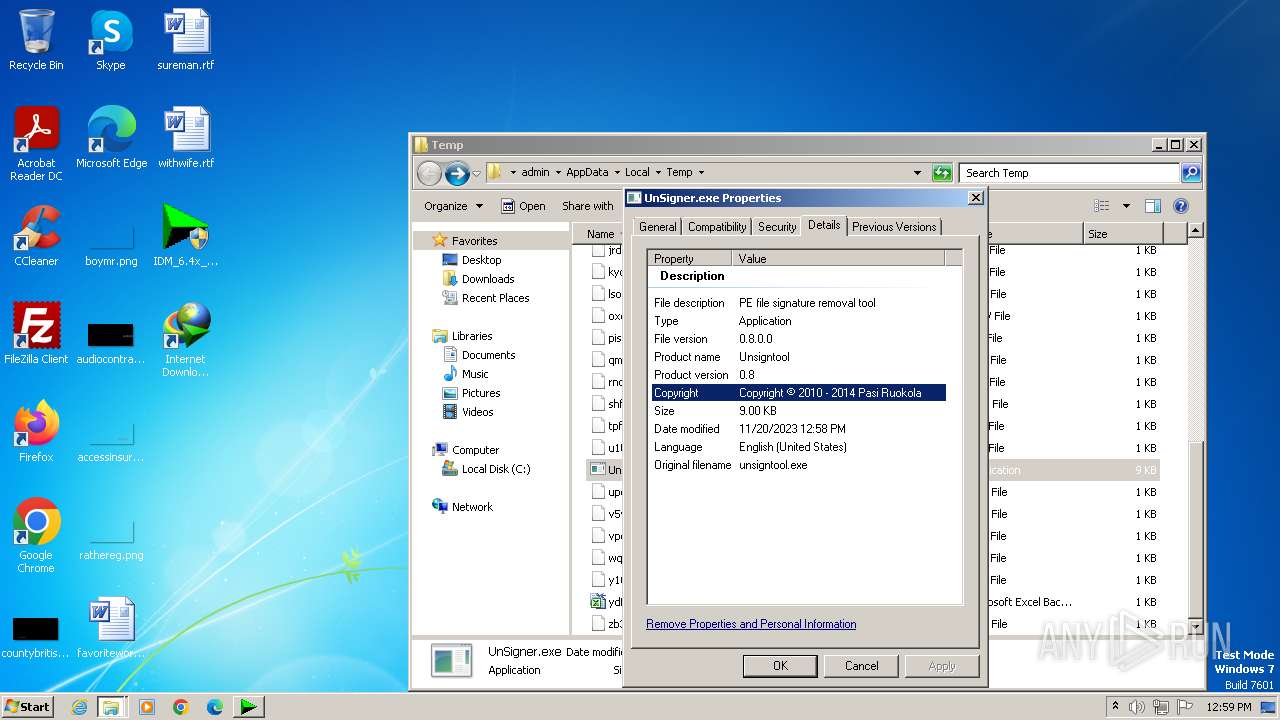
- UnSigner.exe (PID: 120)
- IDM_6.4x_Crack_v18.1.exe (PID: 4044)
Creates a writable file the system directory
- rundll32.exe (PID: 1848)
Starts NET.EXE for service management
- net.exe (PID: 3956)
- Uninstall.exe (PID: 3816)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 3388)
- wscript.exe (PID: 3668)
Deletes a file (SCRIPT)
- wscript.exe (PID: 3388)
- wscript.exe (PID: 3668)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- wscript.exe (PID: 3388)
- wscript.exe (PID: 3668)
Copies file to a new location (SCRIPT)
- wscript.exe (PID: 3388)
SUSPICIOUS
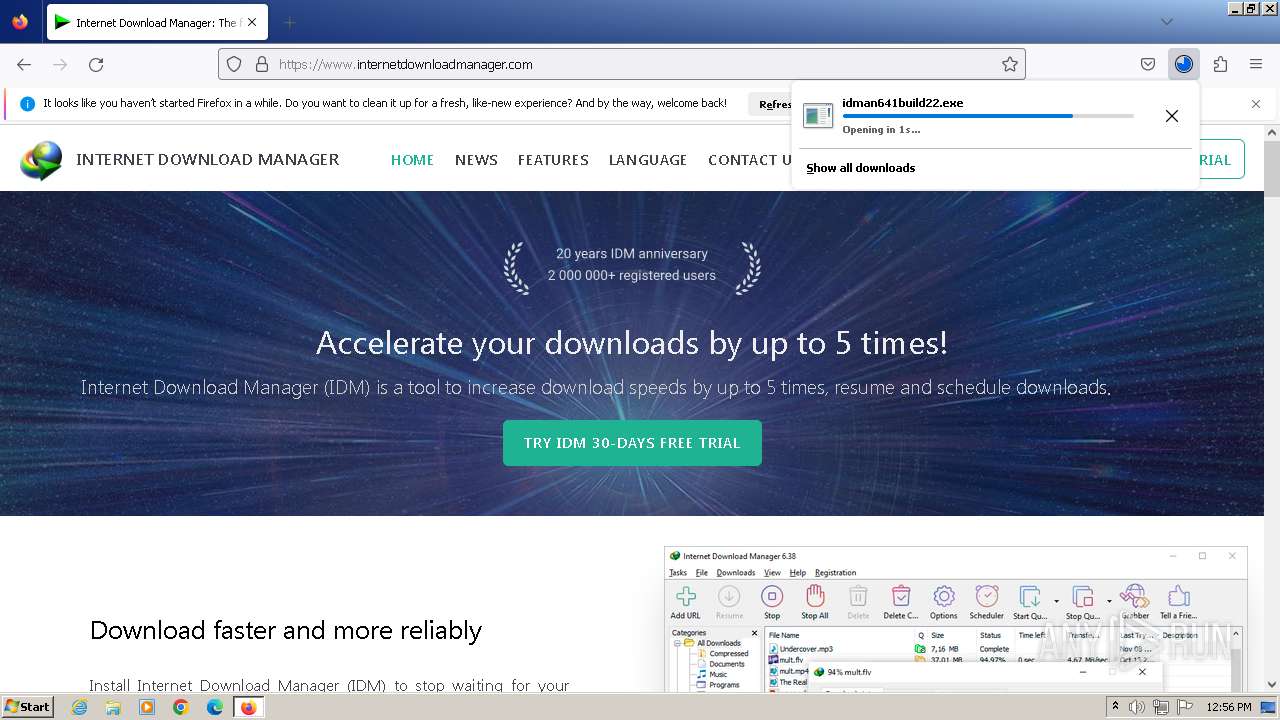
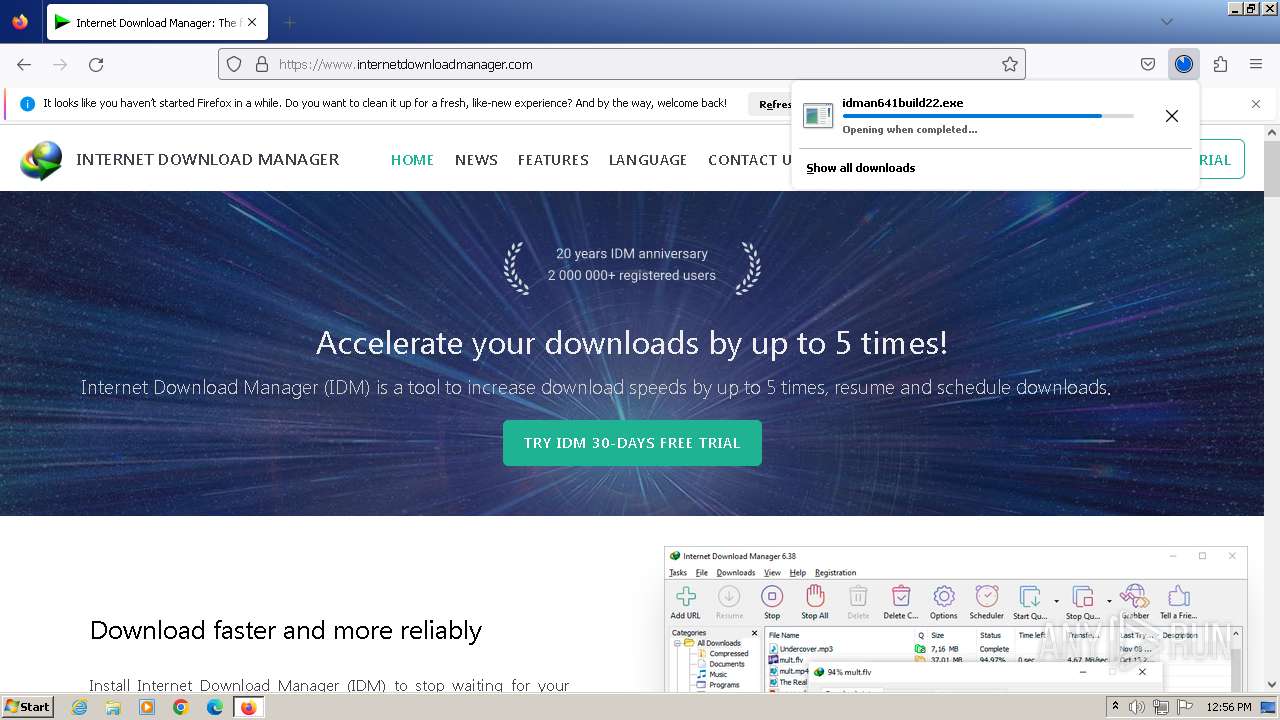
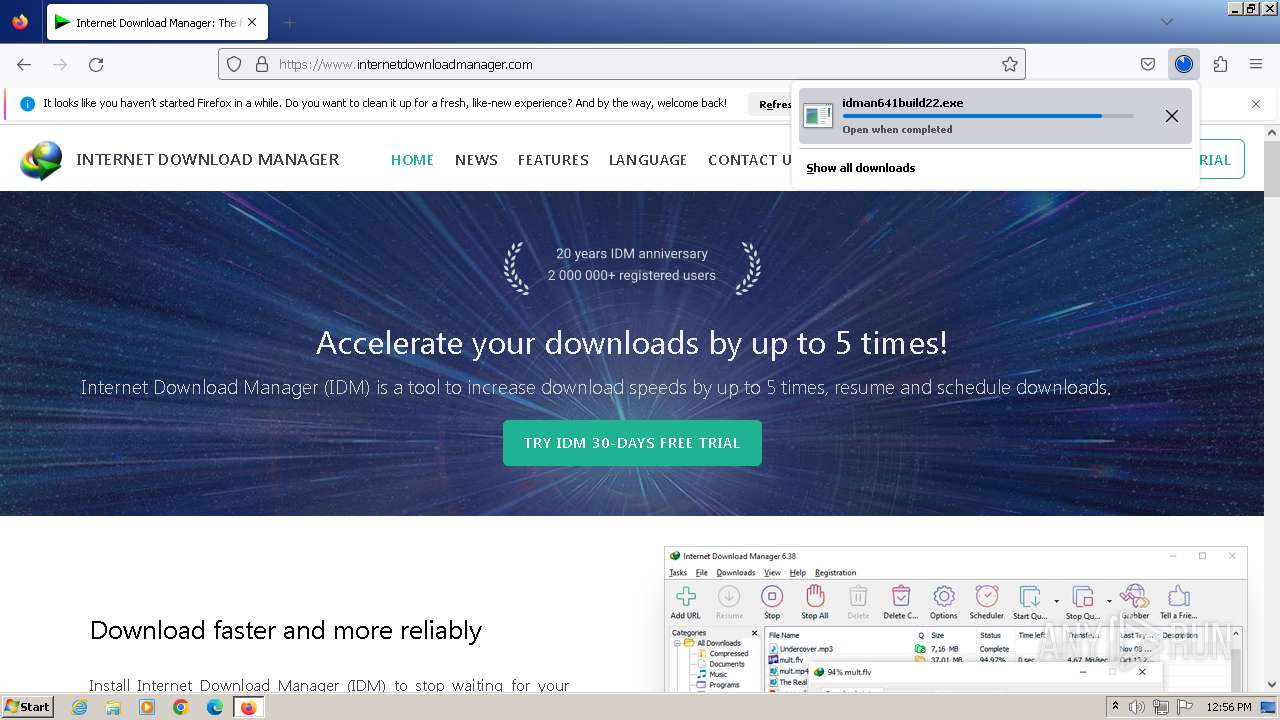
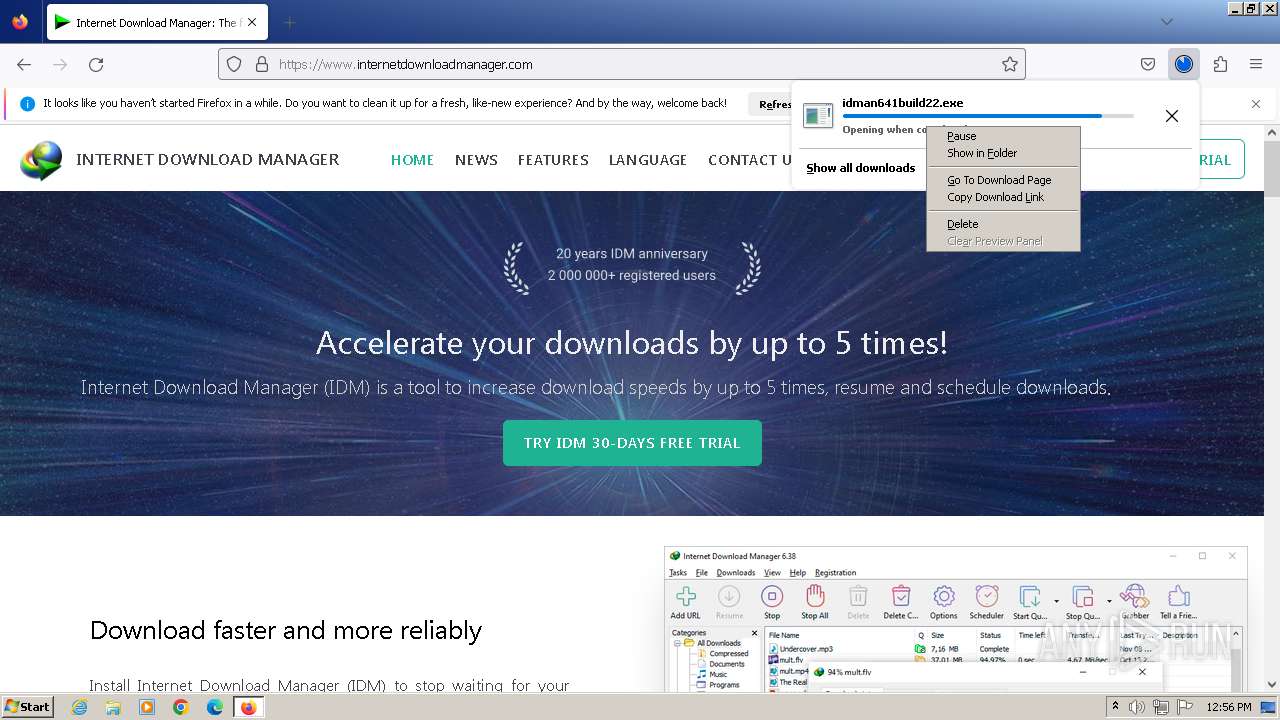
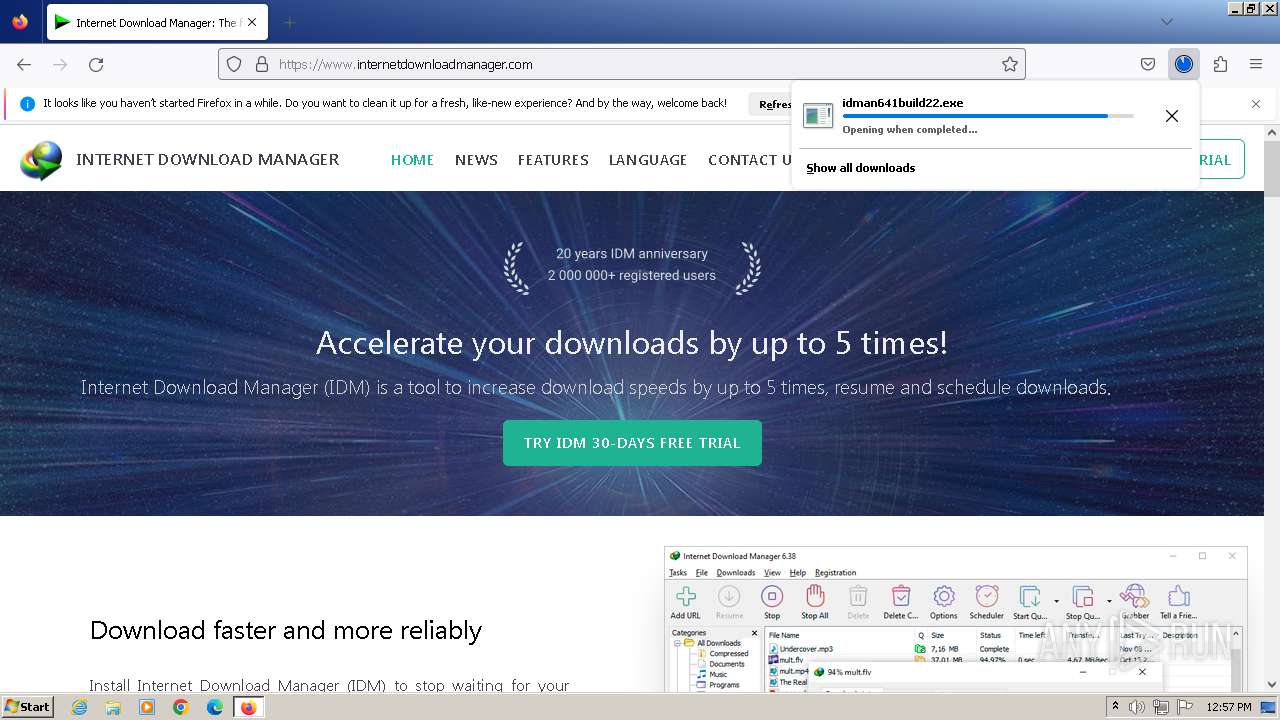
Starts application with an unusual extension
- idman641build22.exe (PID: 2396)
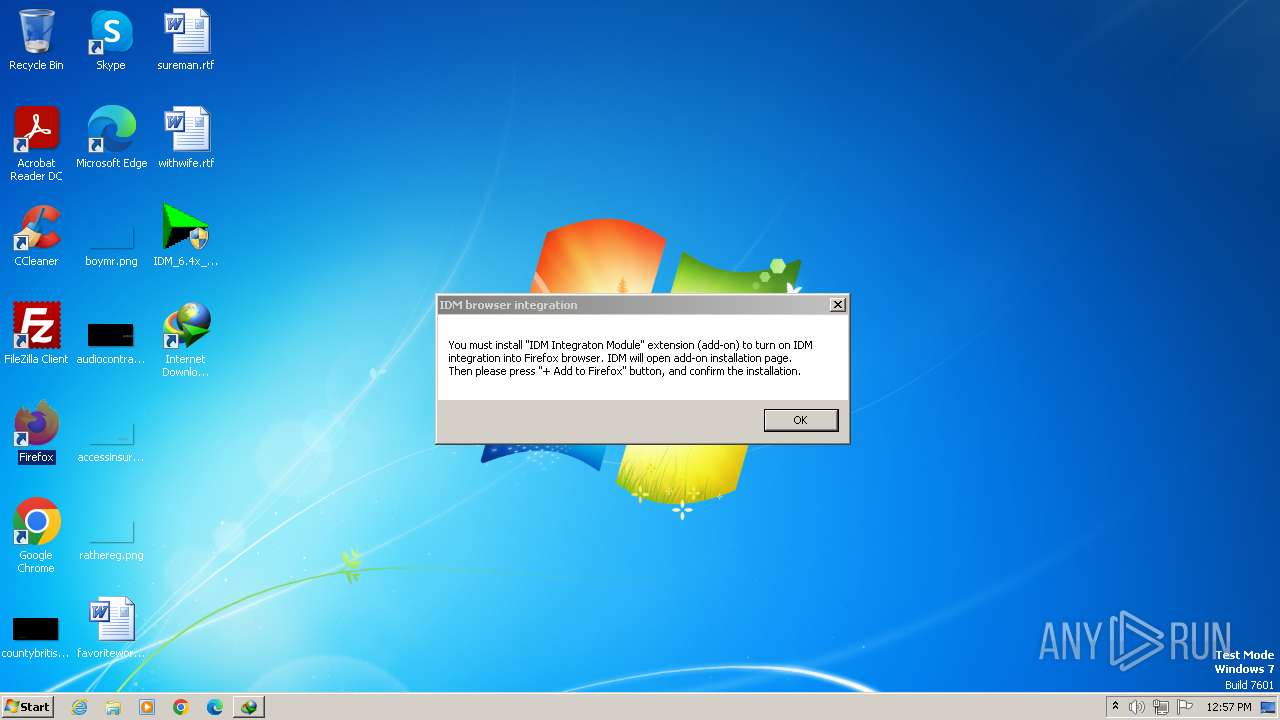
Reads security settings of Internet Explorer
- IDMan.exe (PID: 2820)
- IDMan.exe (PID: 3532)
Checks Windows Trust Settings
- IDMan.exe (PID: 2820)
- IDMan.exe (PID: 3532)
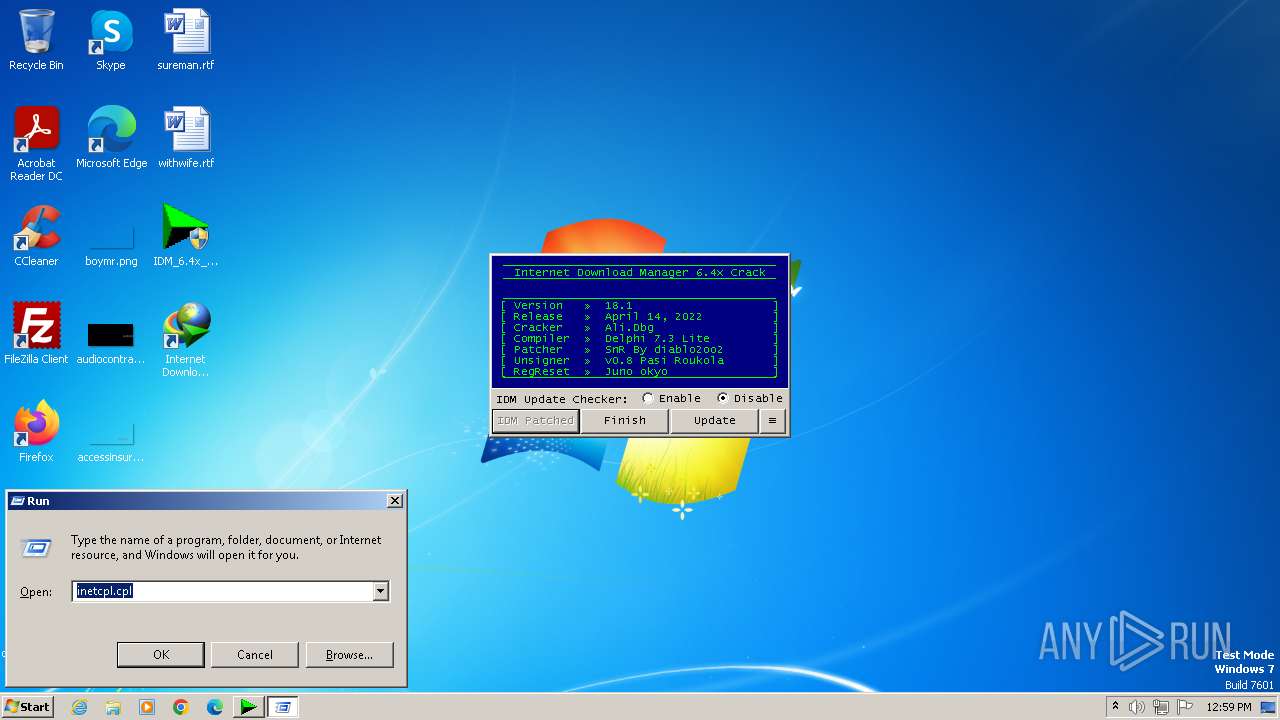
Reads the Internet Settings
- IDMan.exe (PID: 2820)
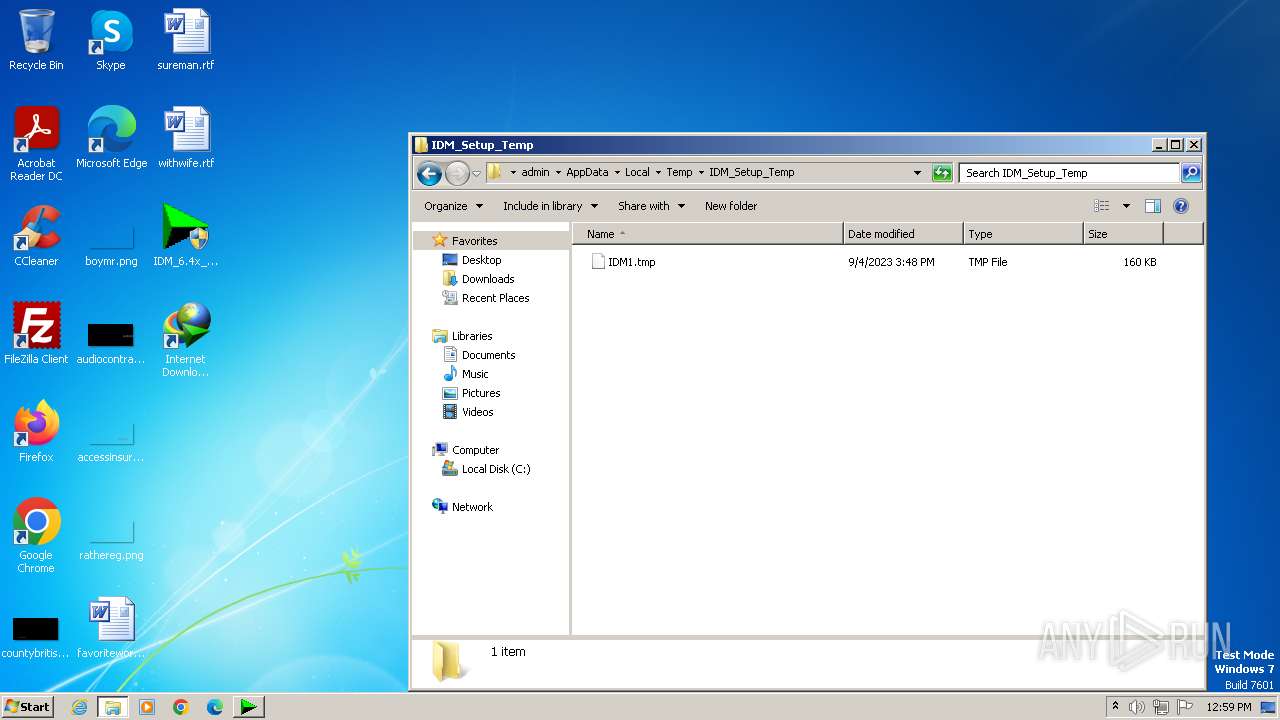
- IDM1.tmp (PID: 2708)
- Uninstall.exe (PID: 3816)
- runonce.exe (PID: 188)
- IDMan.exe (PID: 3532)
- IDM_6.4x_Crack_v18.1.exe (PID: 1028)
Reads settings of System Certificates
- IDMan.exe (PID: 2820)
- IDMan.exe (PID: 3532)
Creates/Modifies COM task schedule object
- IDMan.exe (PID: 2820)
- Uninstall.exe (PID: 3816)
The process creates files with name similar to system file names
- IDM1.tmp (PID: 2708)
Uses RUNDLL32.EXE to load library
- Uninstall.exe (PID: 3816)
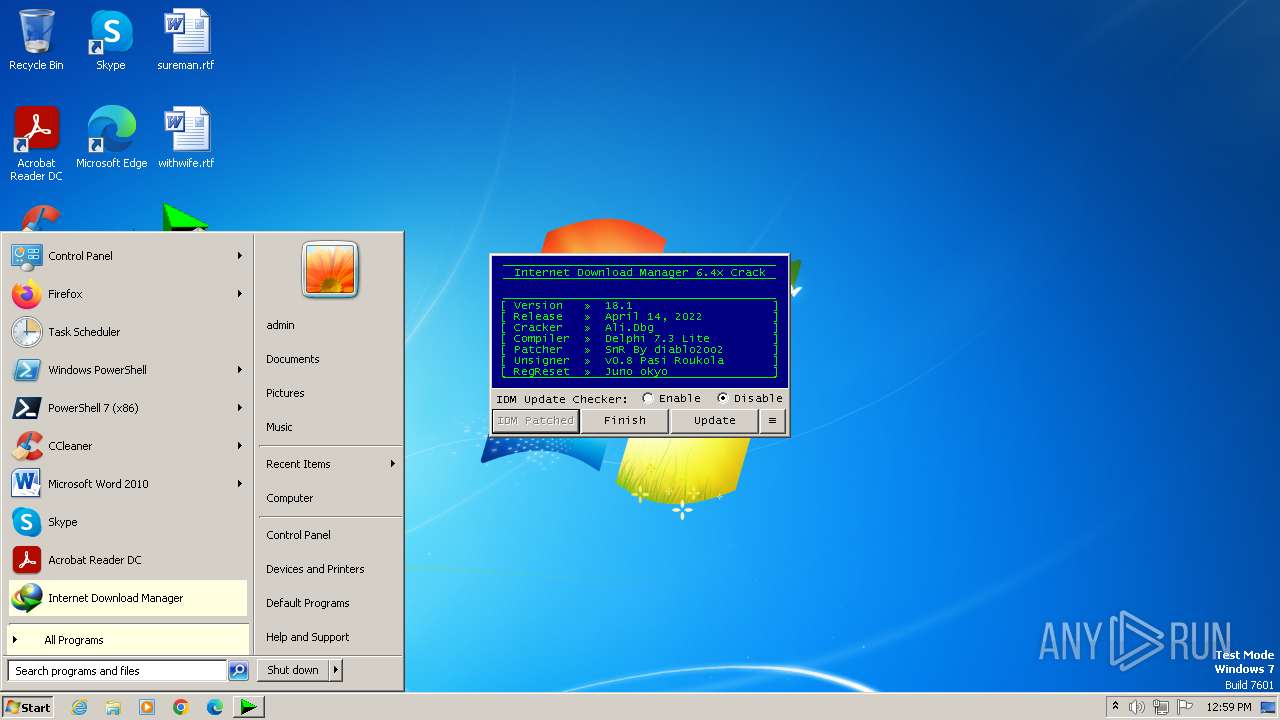
Creates or modifies Windows services
- Uninstall.exe (PID: 3816)
Drops a system driver (possible attempt to evade defenses)
- rundll32.exe (PID: 1848)
Searches for installed software
- IDM_6.4x_Crack_v18.1.exe (PID: 1028)
- IDM_6.4x_Crack_v18.1.exe (PID: 4044)
The process executes VB scripts
- IDM_6.4x_Crack_v18.1.exe (PID: 1028)
- IDM_6.4x_Crack_v18.1.exe (PID: 4044)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 3388)
- wscript.exe (PID: 3668)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 3388)
- wscript.exe (PID: 3668)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 3388)
- wscript.exe (PID: 3668)
Uses TASKKILL.EXE to kill process
- IDM_6.4x_Crack_v18.1.exe (PID: 1028)
- IDM_6.4x_Crack_v18.1.exe (PID: 4044)
Uses REG/REGEDIT.EXE to modify registry
- IDM_6.4x_Crack_v18.1.exe (PID: 1028)
- cmd.exe (PID: 3052)
- IDM_6.4x_Crack_v18.1.exe (PID: 4044)
- cmd.exe (PID: 604)
Starts CMD.EXE for commands execution
- IDM_6.4x_Crack_v18.1.exe (PID: 1028)
- cmd.exe (PID: 3052)
- cmd.exe (PID: 604)
- IDM_6.4x_Crack_v18.1.exe (PID: 4044)
Executing commands from a ".bat" file
- IDM_6.4x_Crack_v18.1.exe (PID: 1028)
- IDM_6.4x_Crack_v18.1.exe (PID: 4044)
Application launched itself
- cmd.exe (PID: 3052)
- cmd.exe (PID: 604)
Identifying current user with WHOAMI command
- cmd.exe (PID: 2508)
- cmd.exe (PID: 3788)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3052)
- cmd.exe (PID: 604)
Powershell version downgrade attack
- powershell.exe (PID: 2632)
- powershell.exe (PID: 2904)
- powershell.exe (PID: 2116)
- powershell.exe (PID: 2324)
- powershell.exe (PID: 3880)
- powershell.exe (PID: 2780)
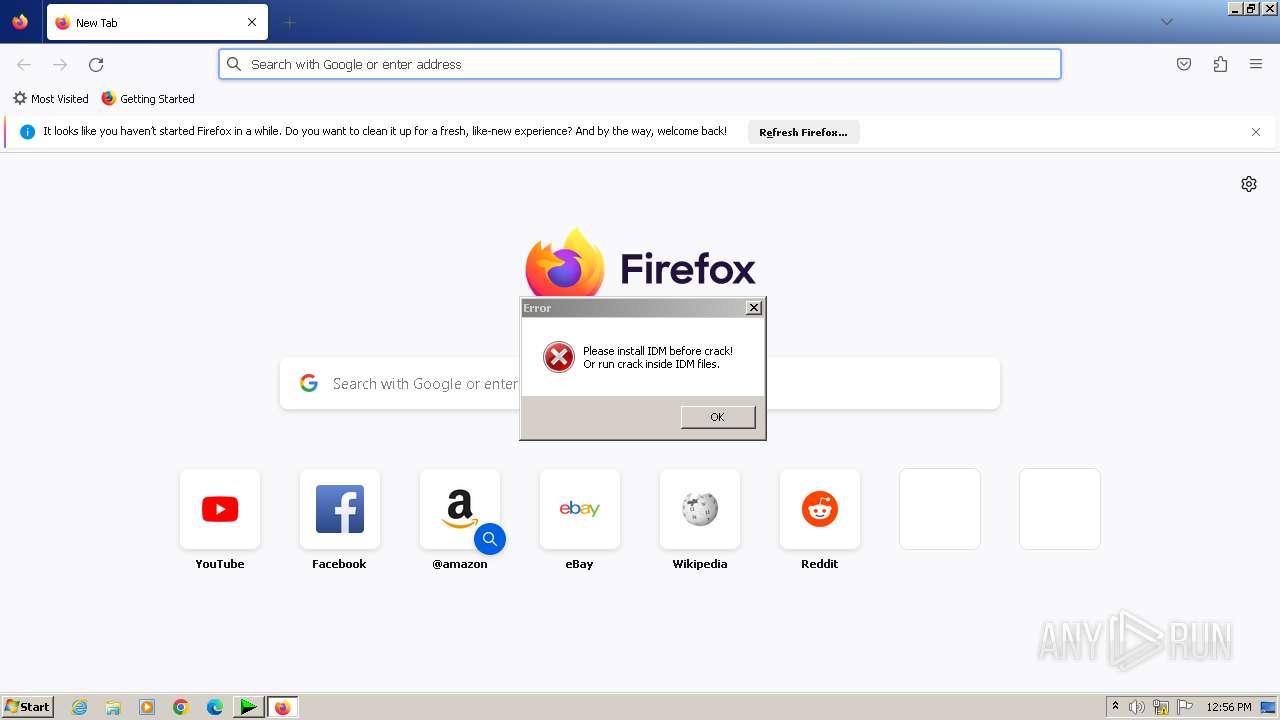
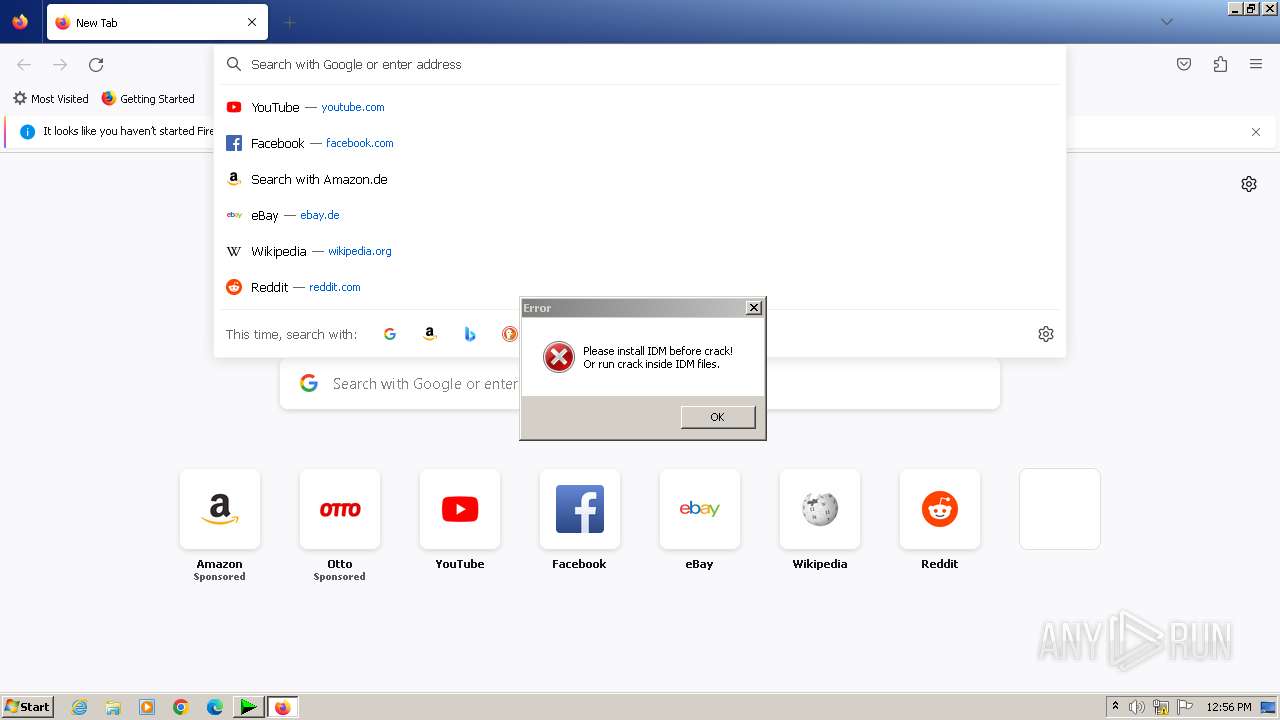
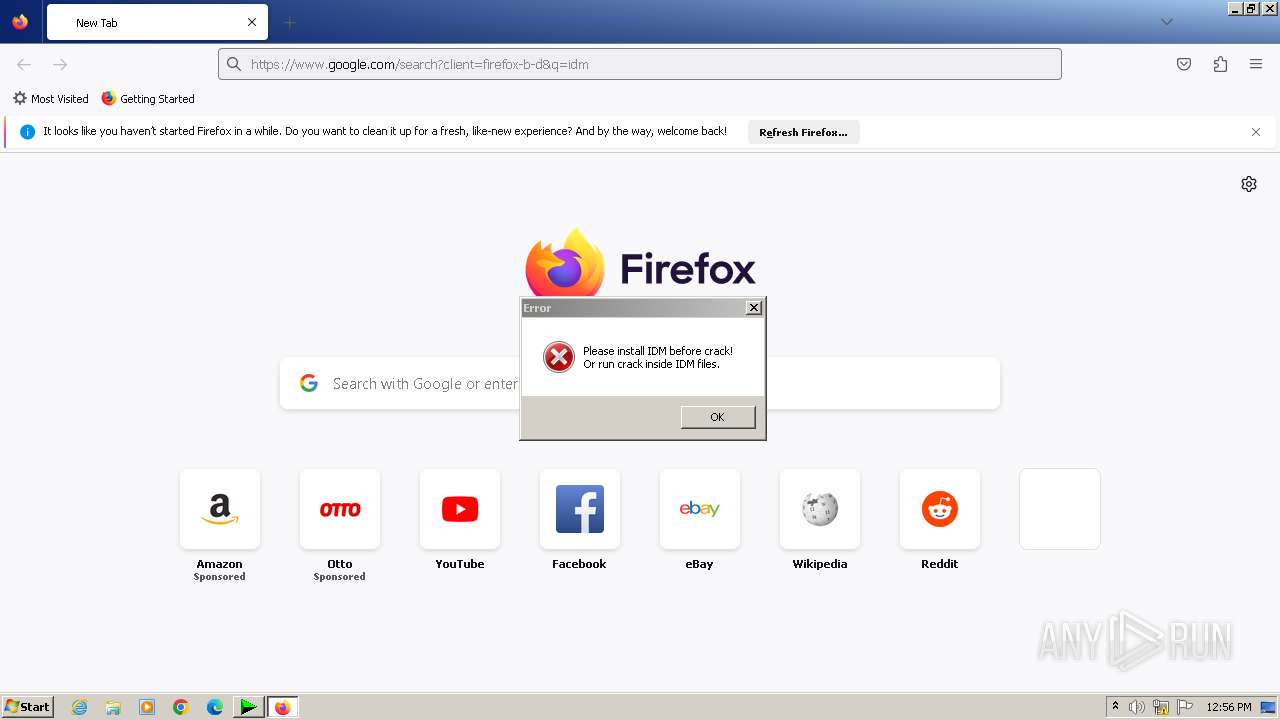
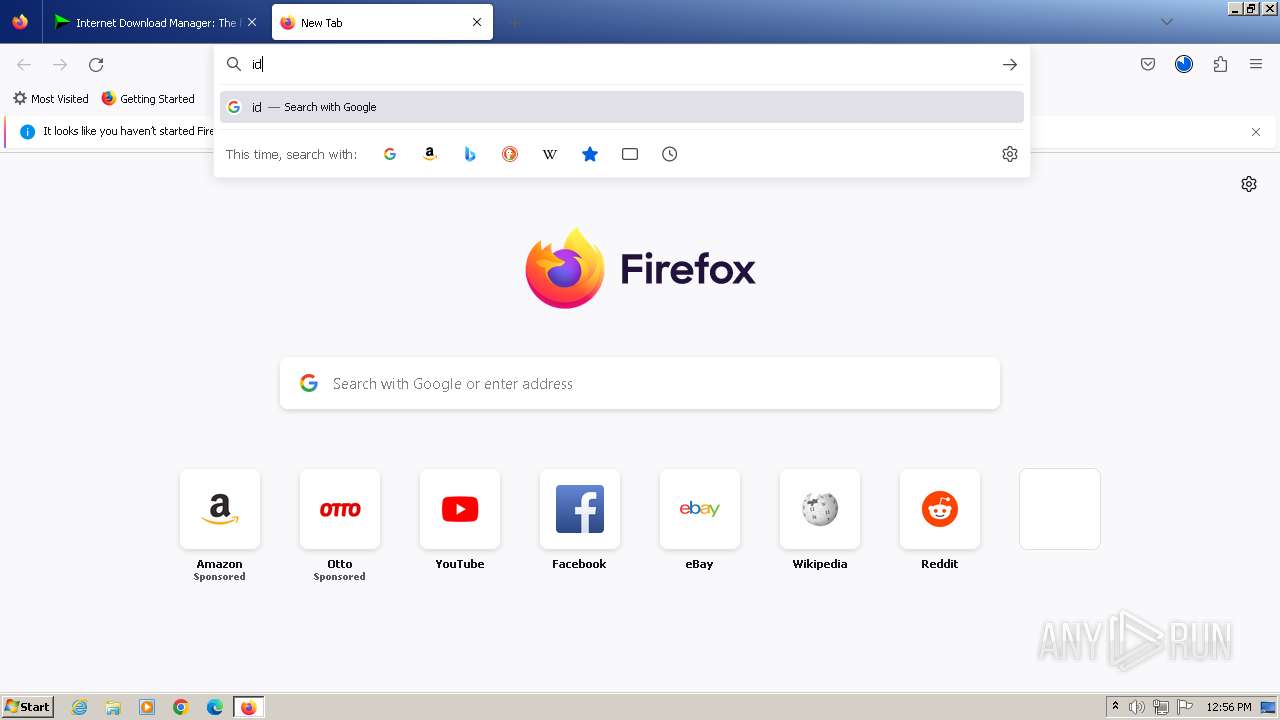
INFO
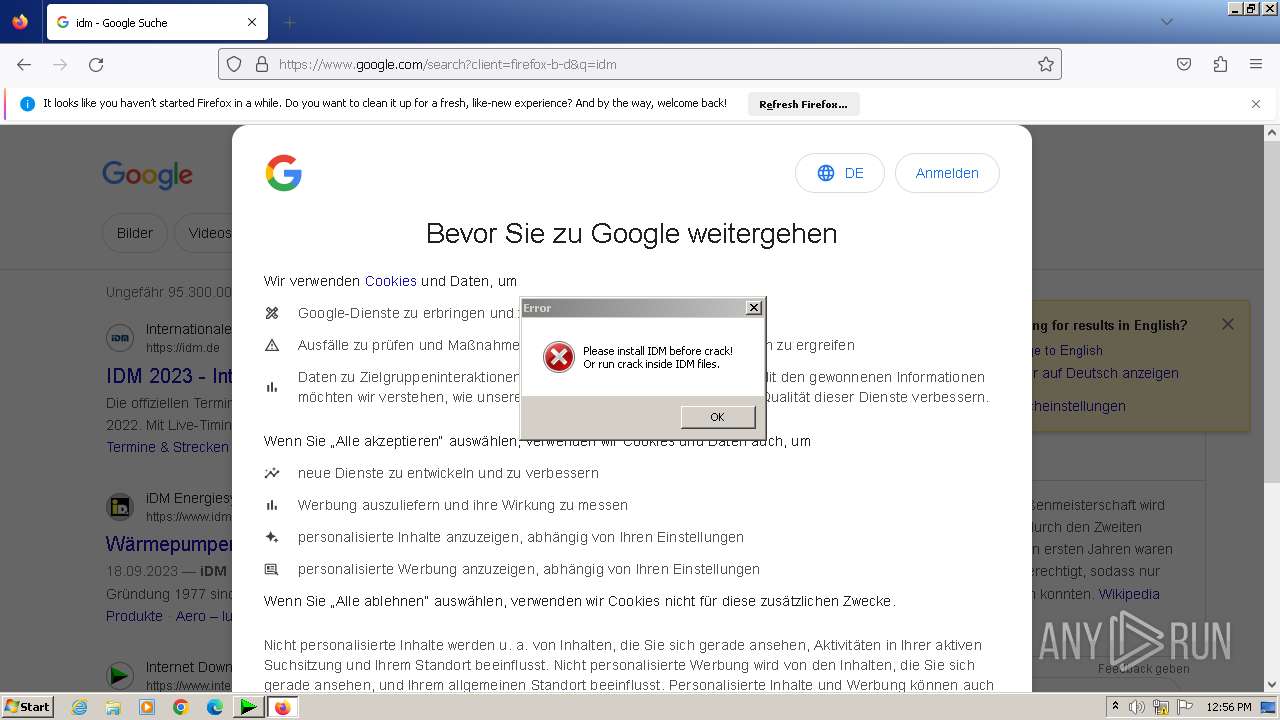
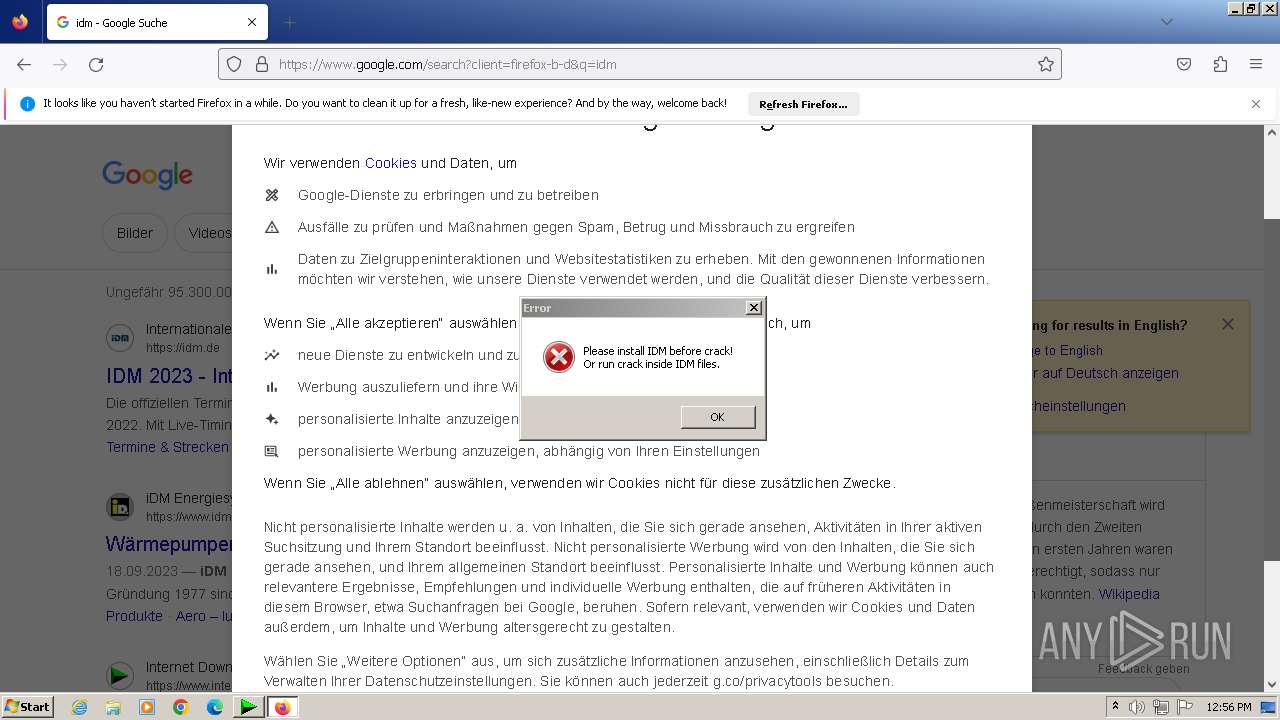
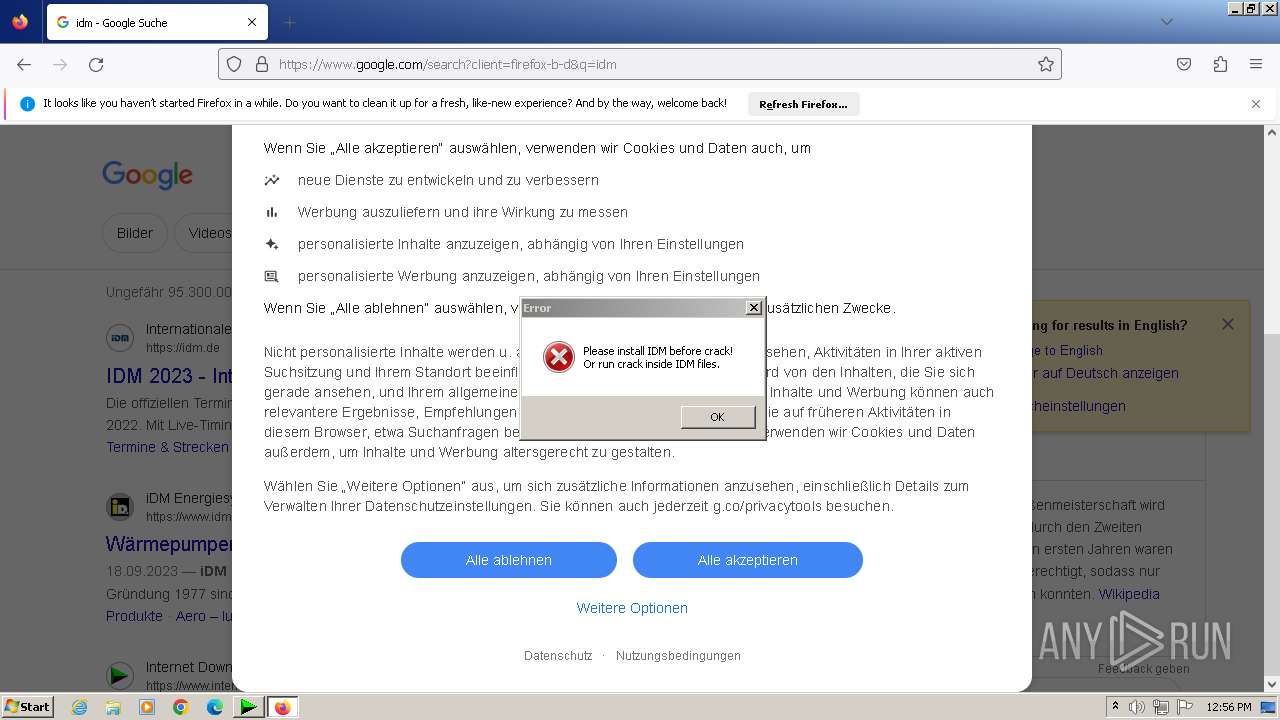
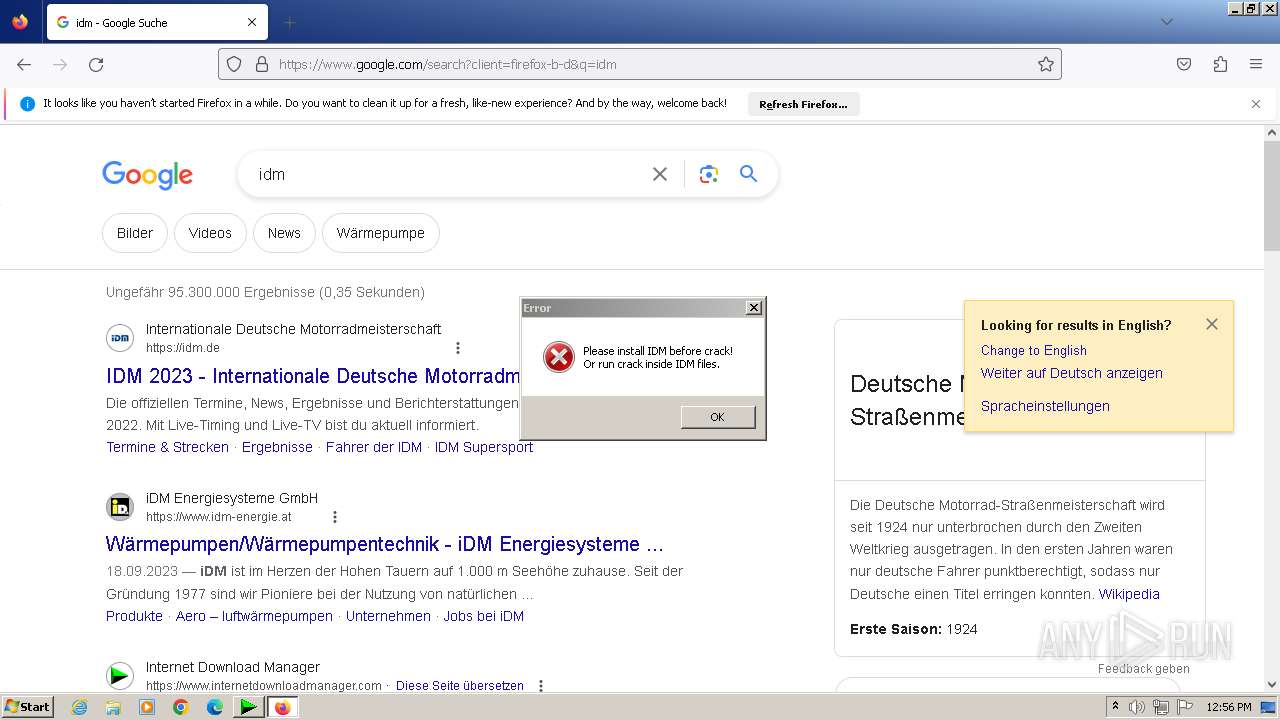
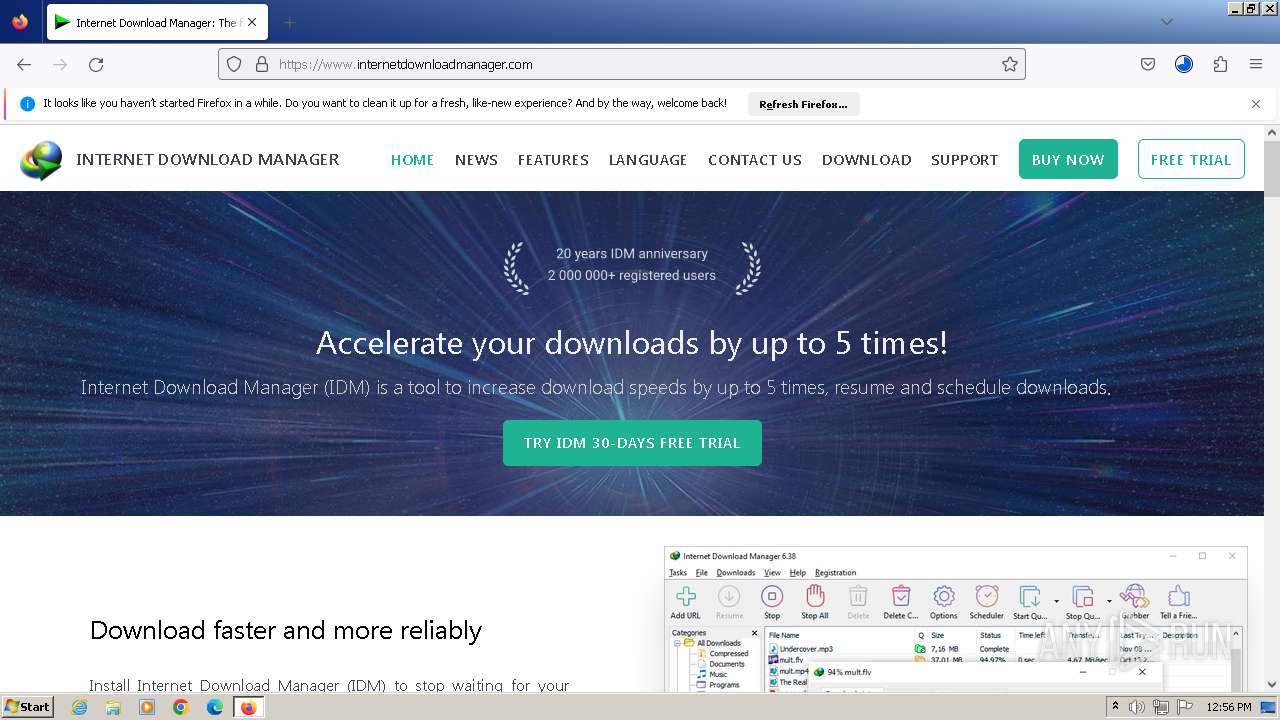
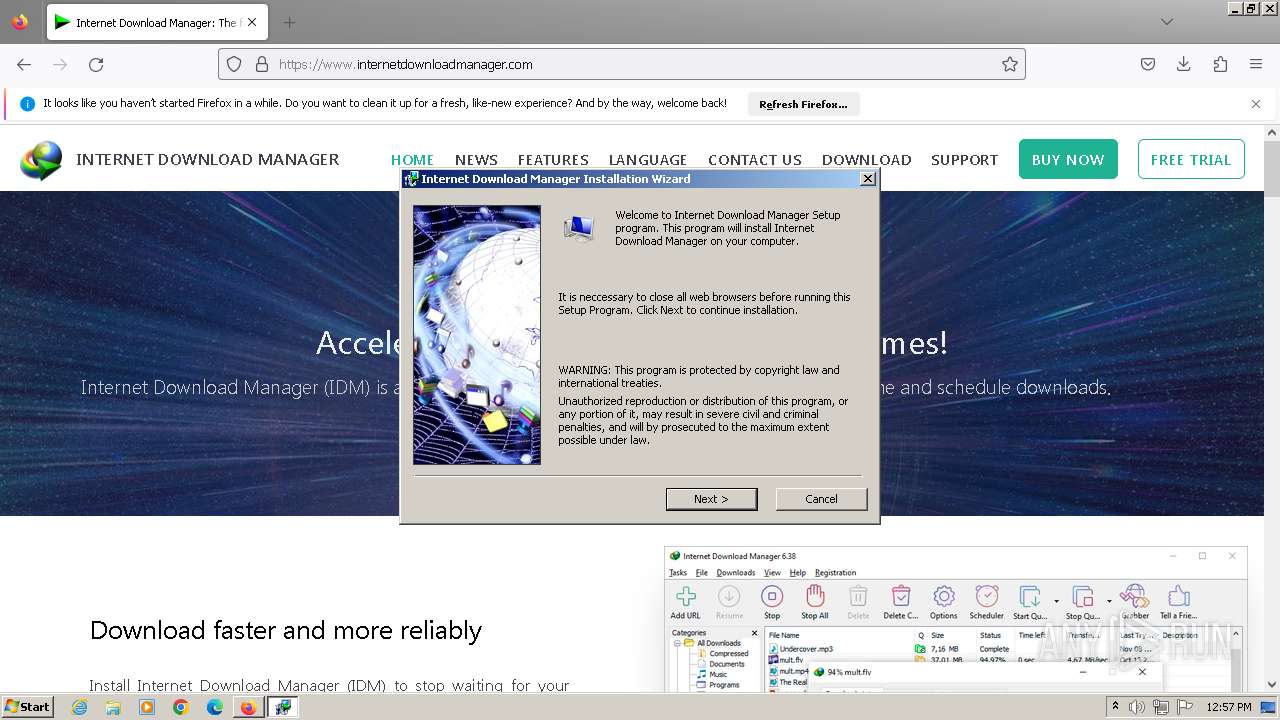
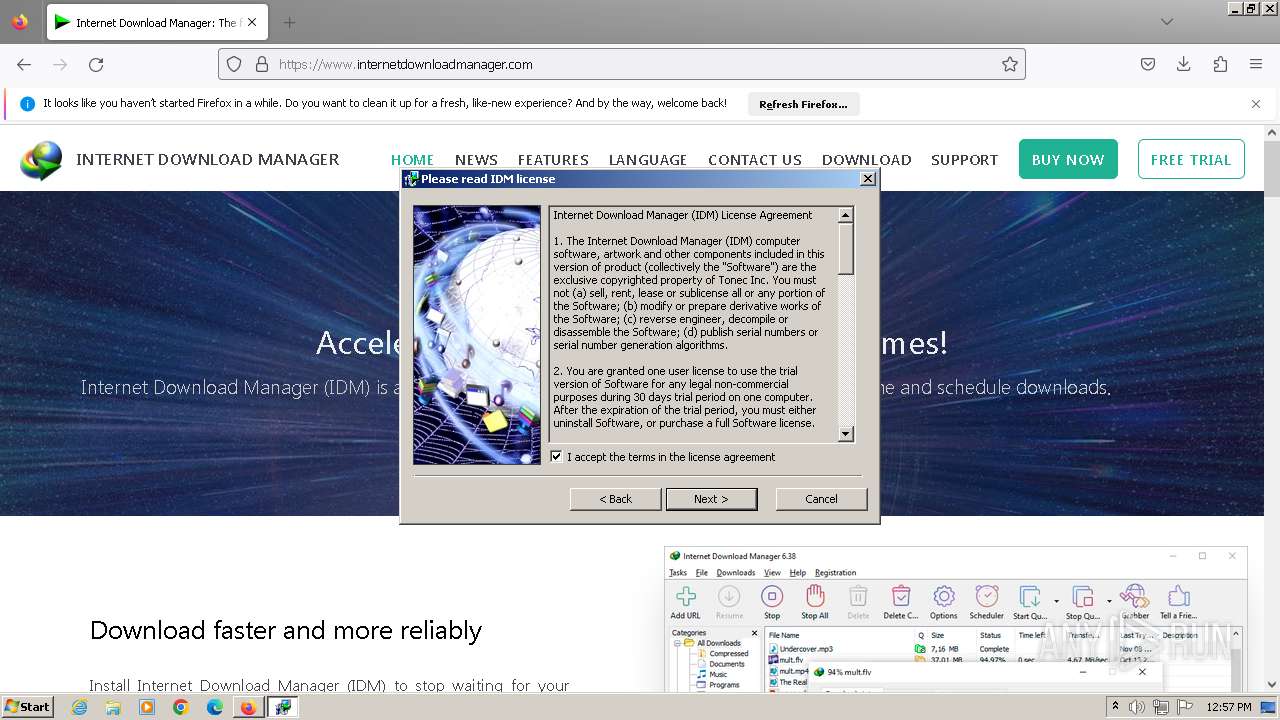
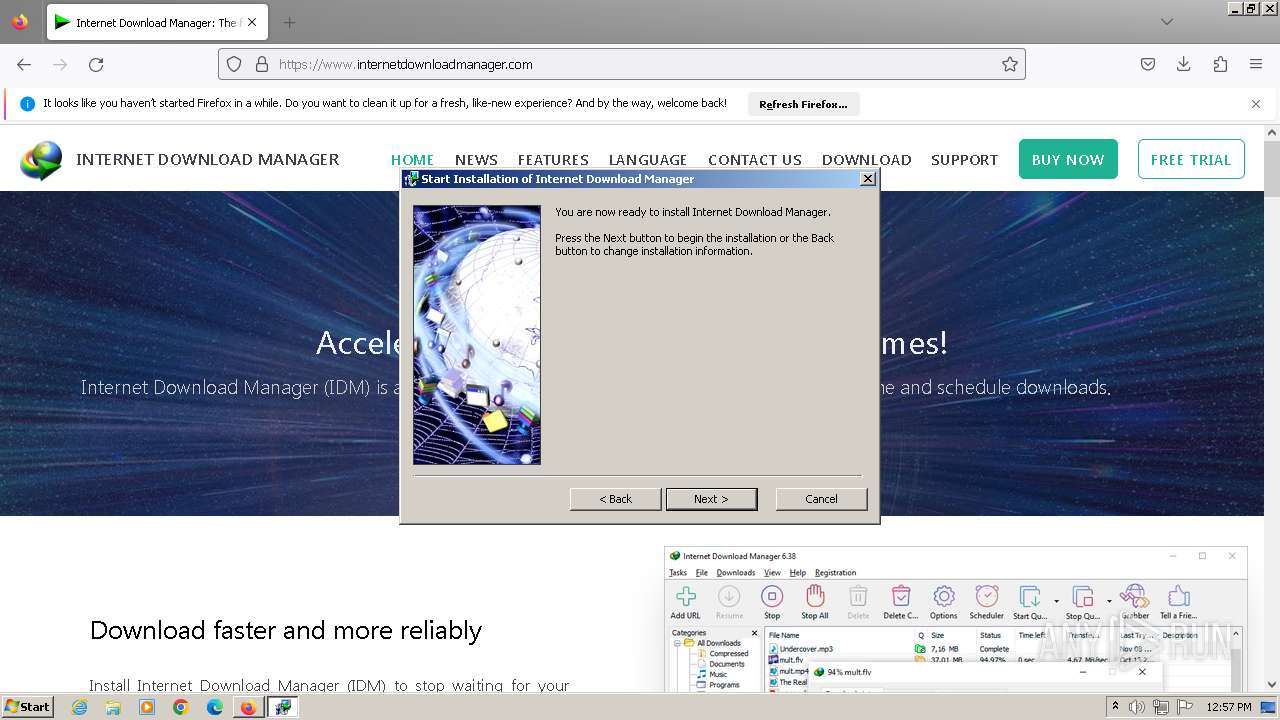
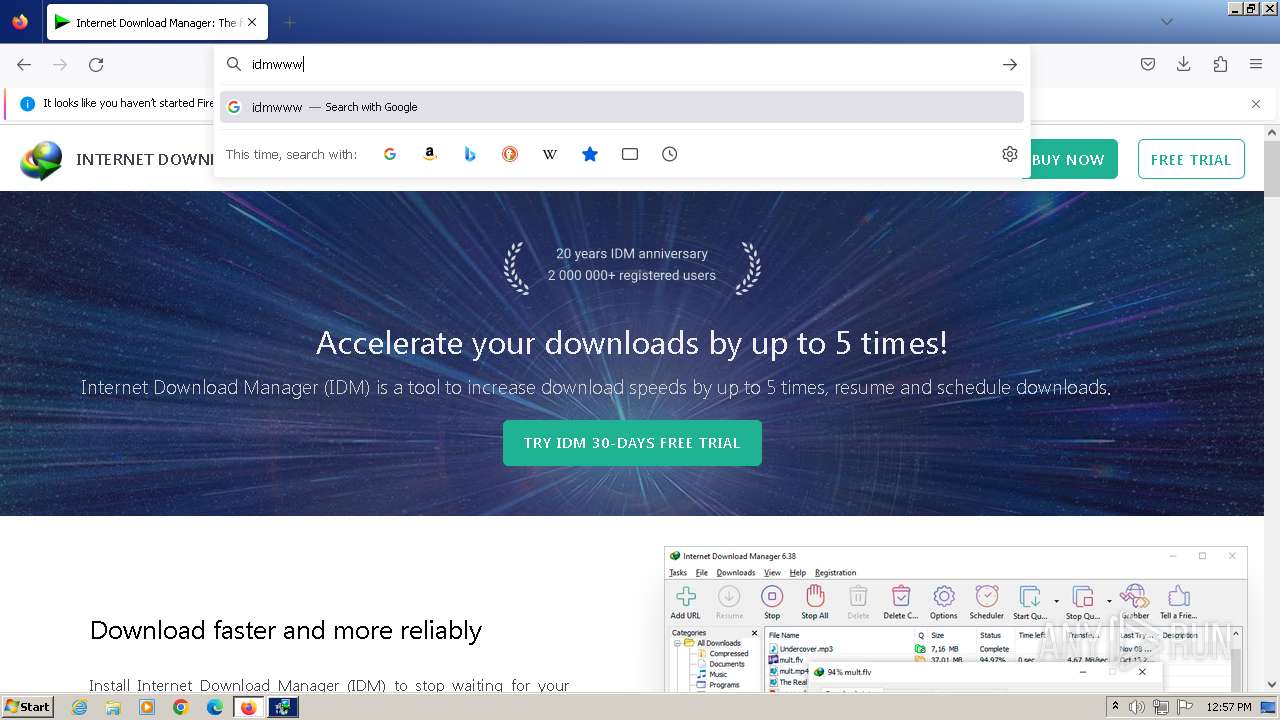
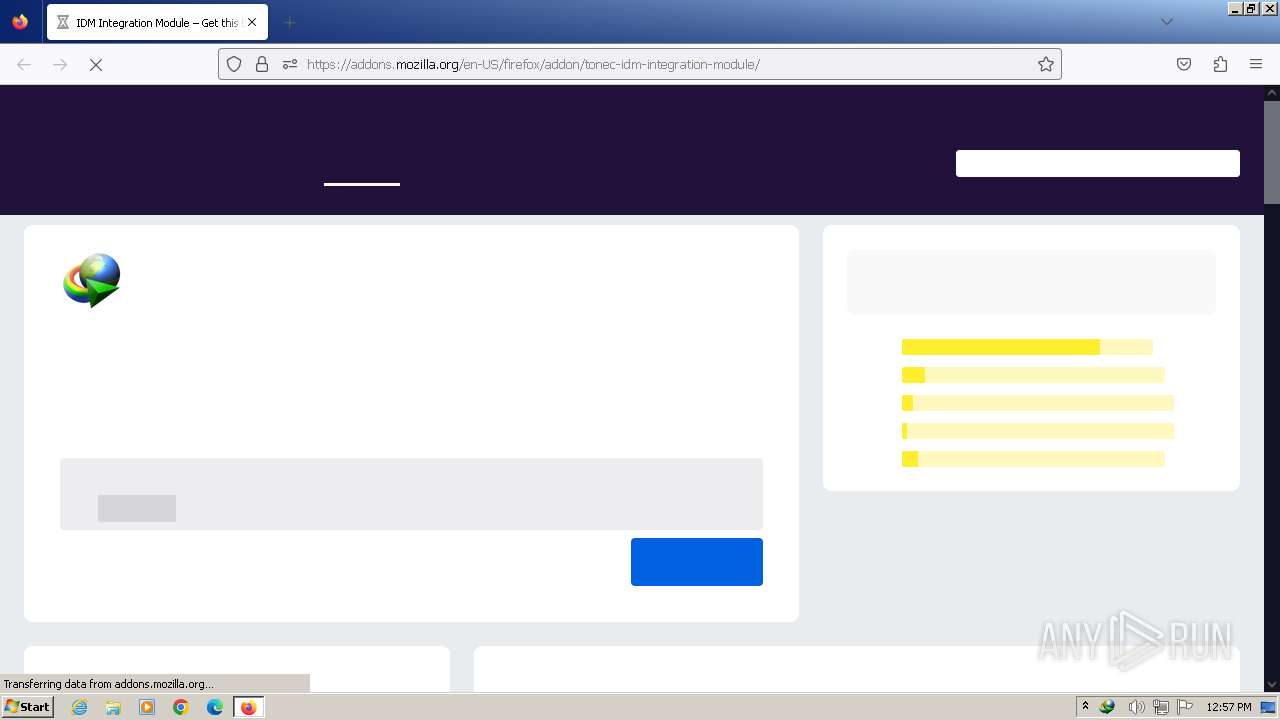
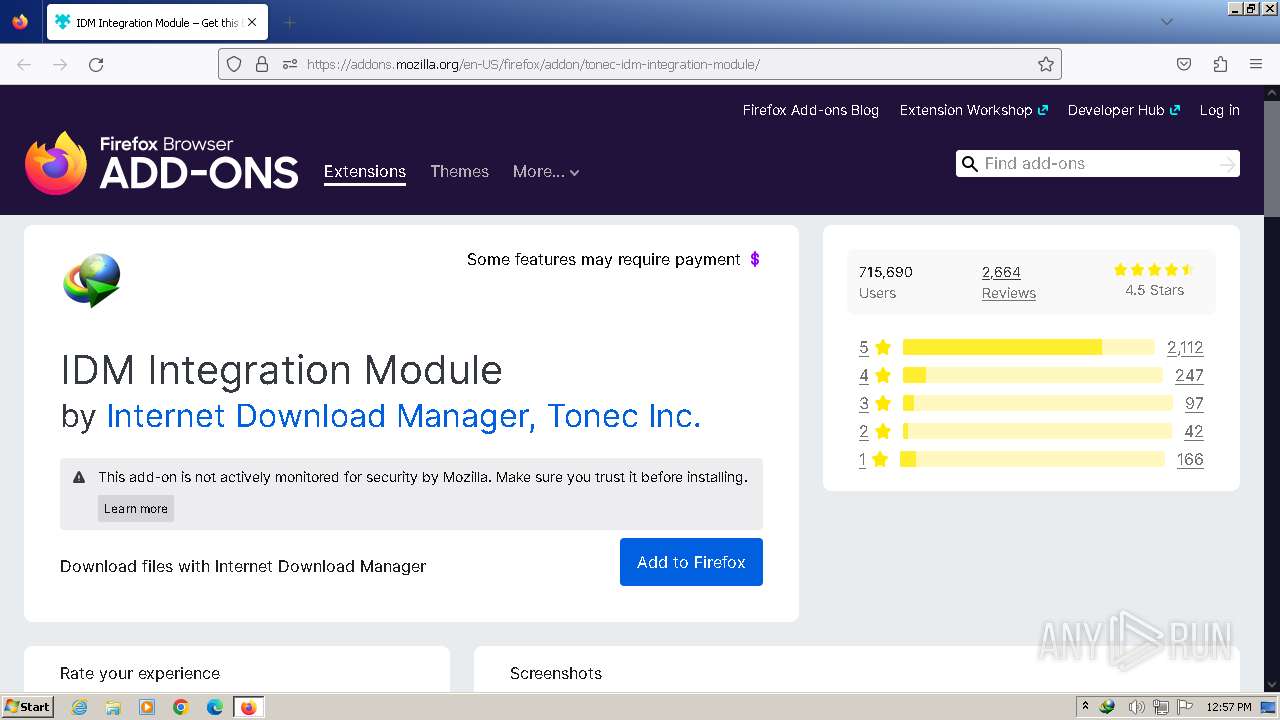
Manual execution by a user
- firefox.exe (PID: 3492)
- wmpnscfg.exe (PID: 2232)
- wmpnscfg.exe (PID: 1952)
- IDM_6.4x_Crack_v18.1.exe (PID: 1028)
- IDM_6.4x_Crack_v18.1.exe (PID: 1088)
- firefox.exe (PID: 2692)
- IDM_6.4x_Crack_v18.1.exe (PID: 2636)
- IDM_6.4x_Crack_v18.1.exe (PID: 4044)
- IDM_6.4x_Crack_v18.1.exe (PID: 3472)
- IDM_6.4x_Crack_v18.1.exe (PID: 1444)
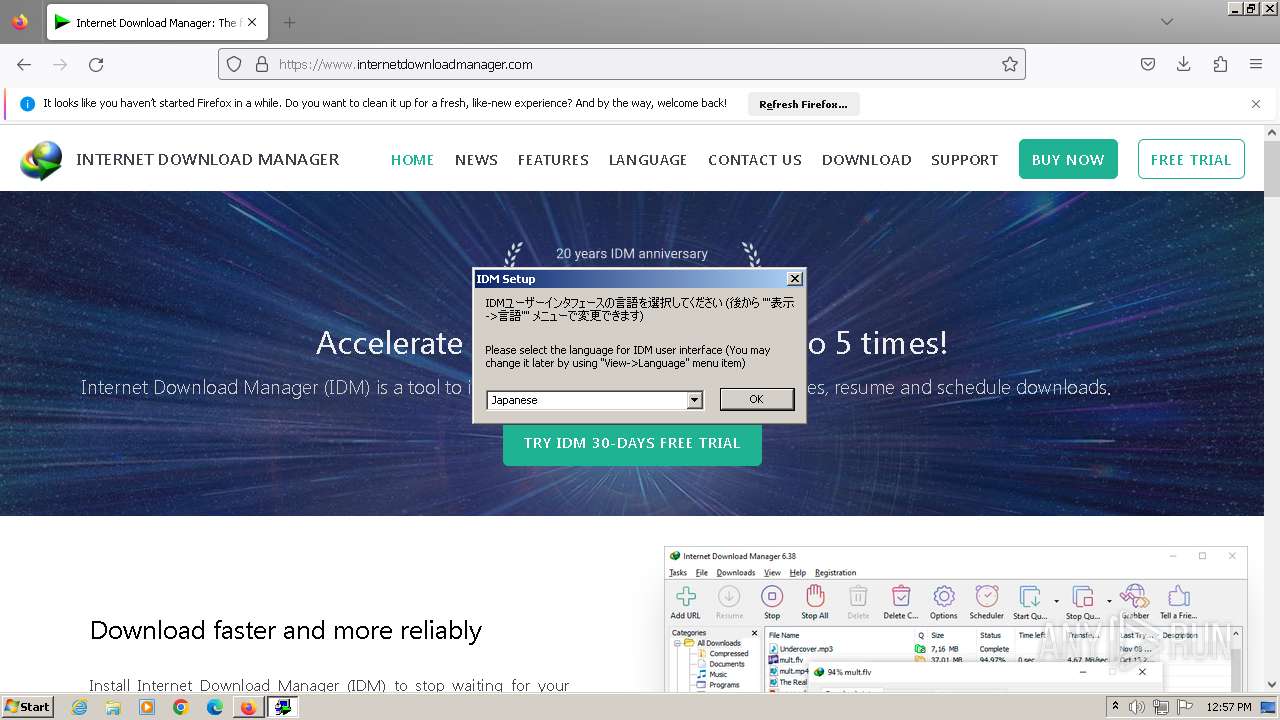
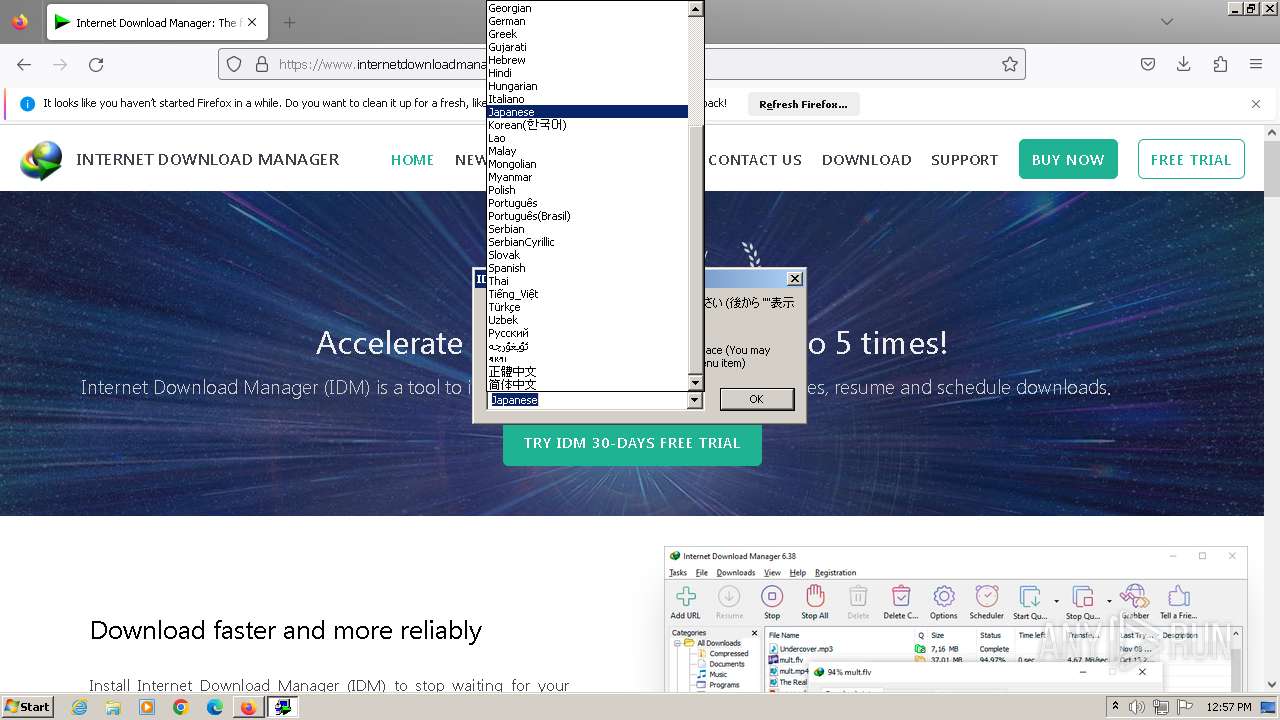
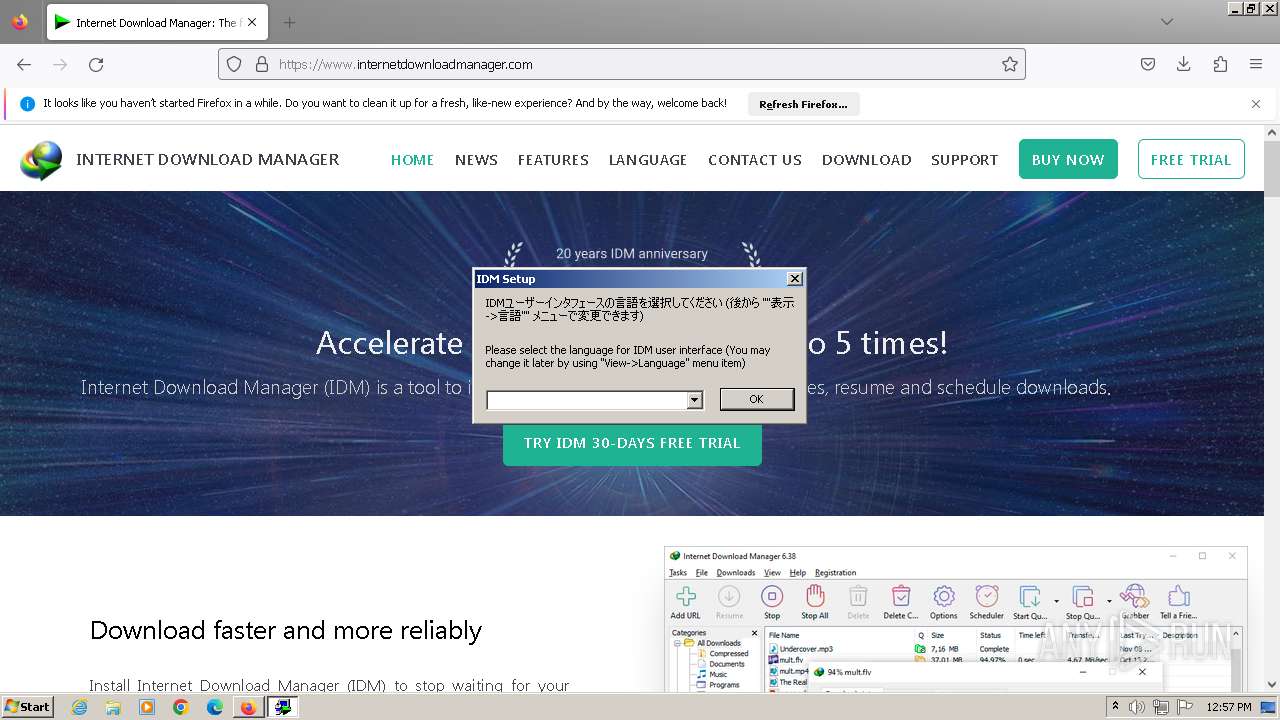
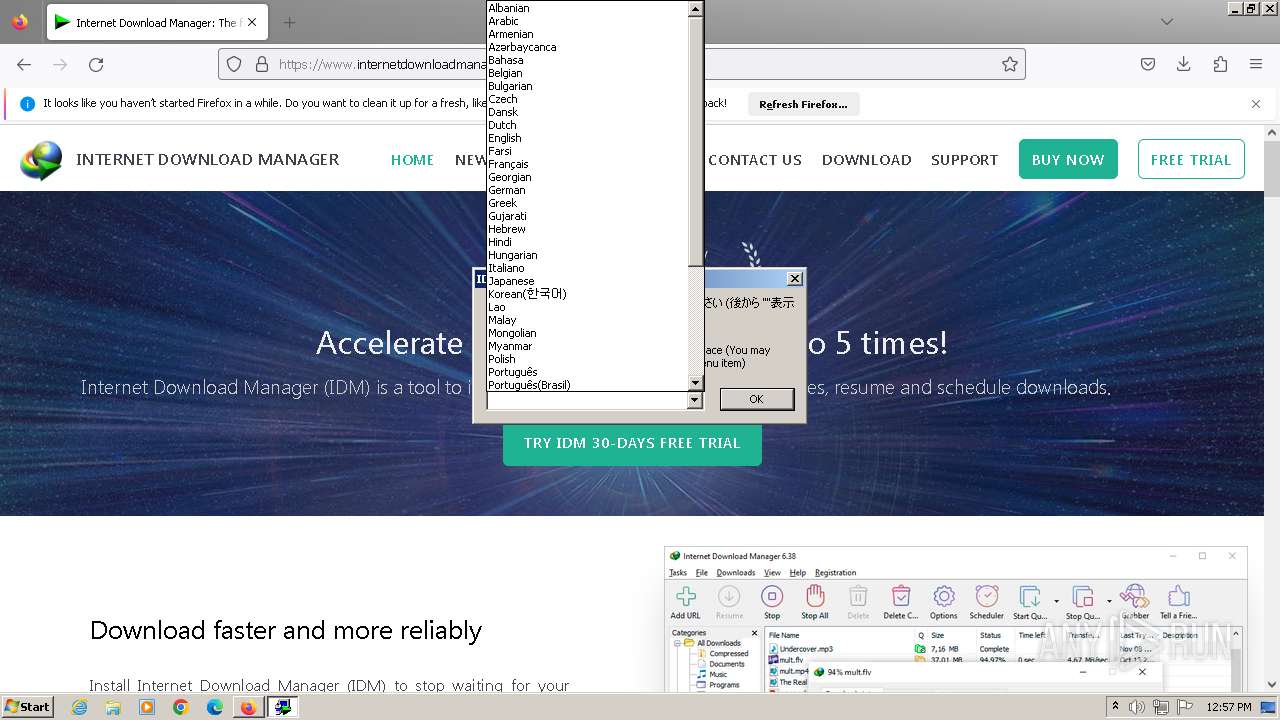
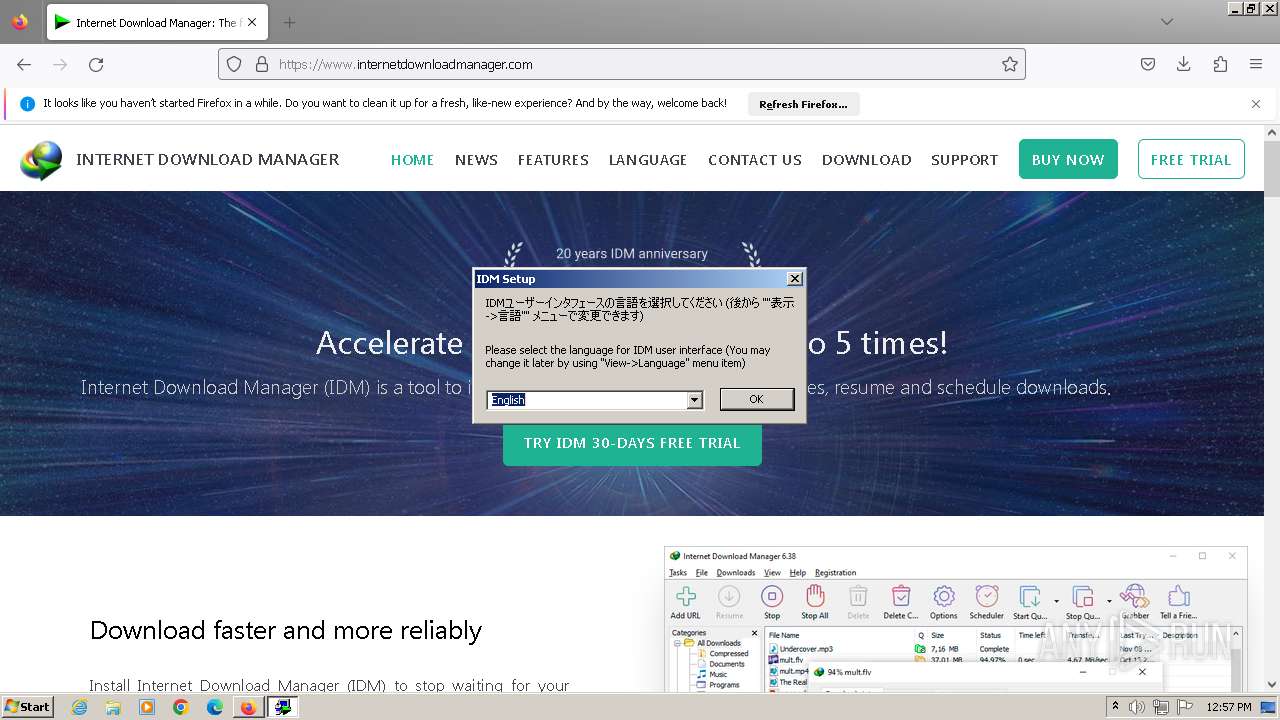
Checks supported languages
- IDM_6.4x_Crack_v18.1.exe (PID: 3228)
- wmpnscfg.exe (PID: 2232)
- idman641build22.exe (PID: 2396)
- IDM1.tmp (PID: 2708)
- wmpnscfg.exe (PID: 1952)
- idmBroker.exe (PID: 1348)
- IDMan.exe (PID: 2820)
- Uninstall.exe (PID: 3816)
- MediumILStart.exe (PID: 1376)
- IDMan.exe (PID: 3532)
- IEMonitor.exe (PID: 1752)
- IDM_6.4x_Crack_v18.1.exe (PID: 1028)
- UnSigner.exe (PID: 120)
- IDM_6.4x_Crack_v18.1.exe (PID: 4044)
- IDM_6.4x_Crack_v18.1.exe (PID: 1444)
Application launched itself
- firefox.exe (PID: 3492)
- firefox.exe (PID: 3580)
- firefox.exe (PID: 2692)
- firefox.exe (PID: 2724)
Reads the computer name
- wmpnscfg.exe (PID: 2232)
- wmpnscfg.exe (PID: 1952)
- IDM1.tmp (PID: 2708)
- IDMan.exe (PID: 2820)
- Uninstall.exe (PID: 3816)
- MediumILStart.exe (PID: 1376)
- IDMan.exe (PID: 3532)
- IEMonitor.exe (PID: 1752)
- IDM_6.4x_Crack_v18.1.exe (PID: 1028)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 2232)
- wmpnscfg.exe (PID: 1952)
- IDM1.tmp (PID: 2708)
- IDMan.exe (PID: 2820)
- MediumILStart.exe (PID: 1376)
- IDMan.exe (PID: 3532)
Drops the executable file immediately after the start
- firefox.exe (PID: 3580)
- rundll32.exe (PID: 1848)
The process uses the downloaded file
- firefox.exe (PID: 3580)
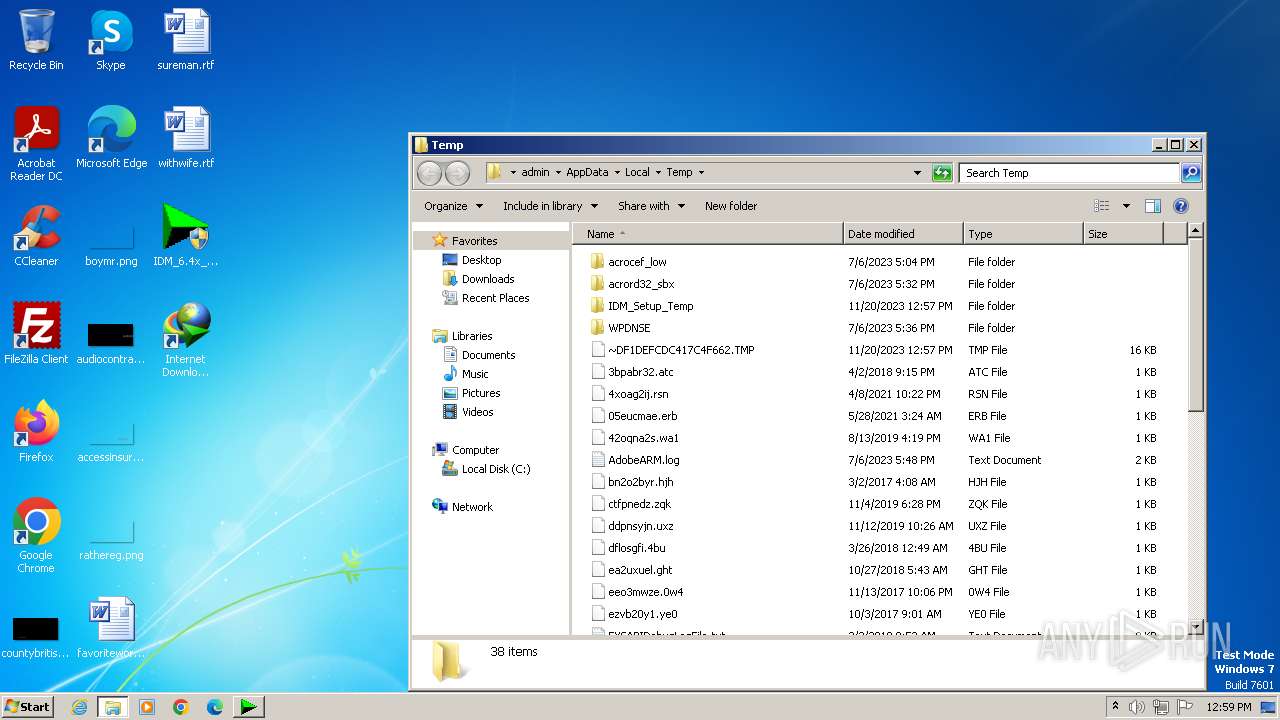
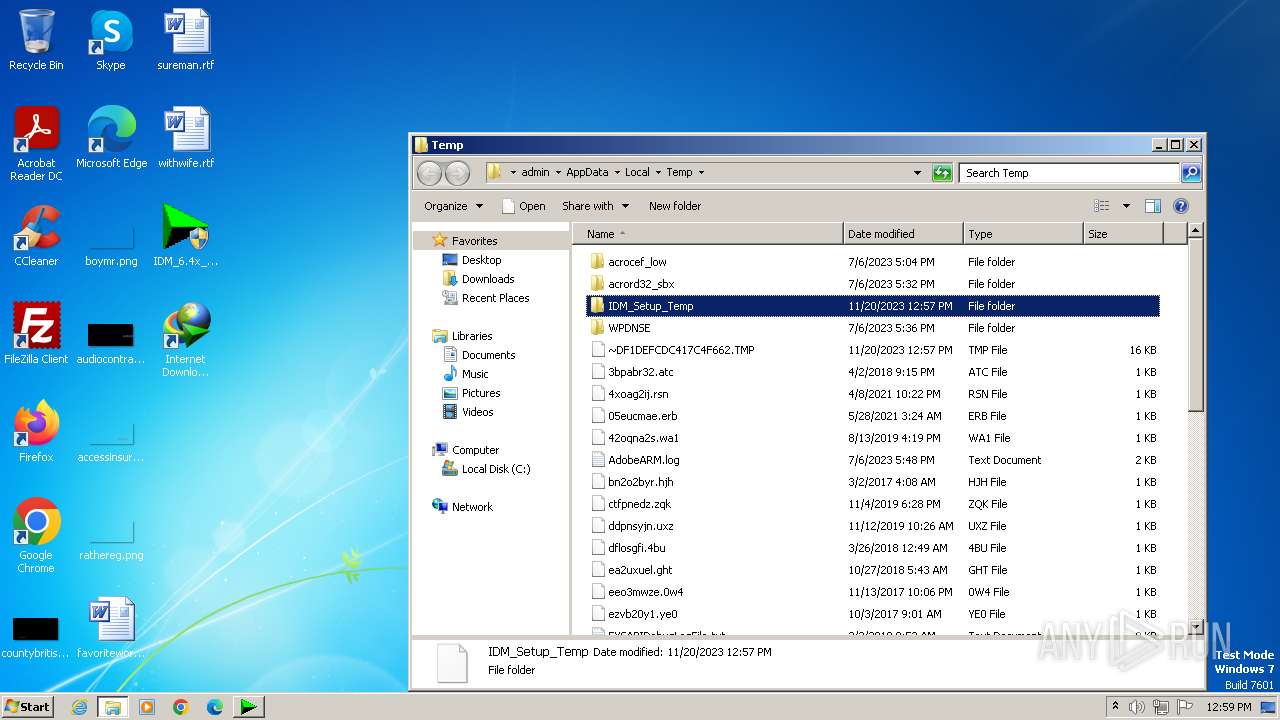
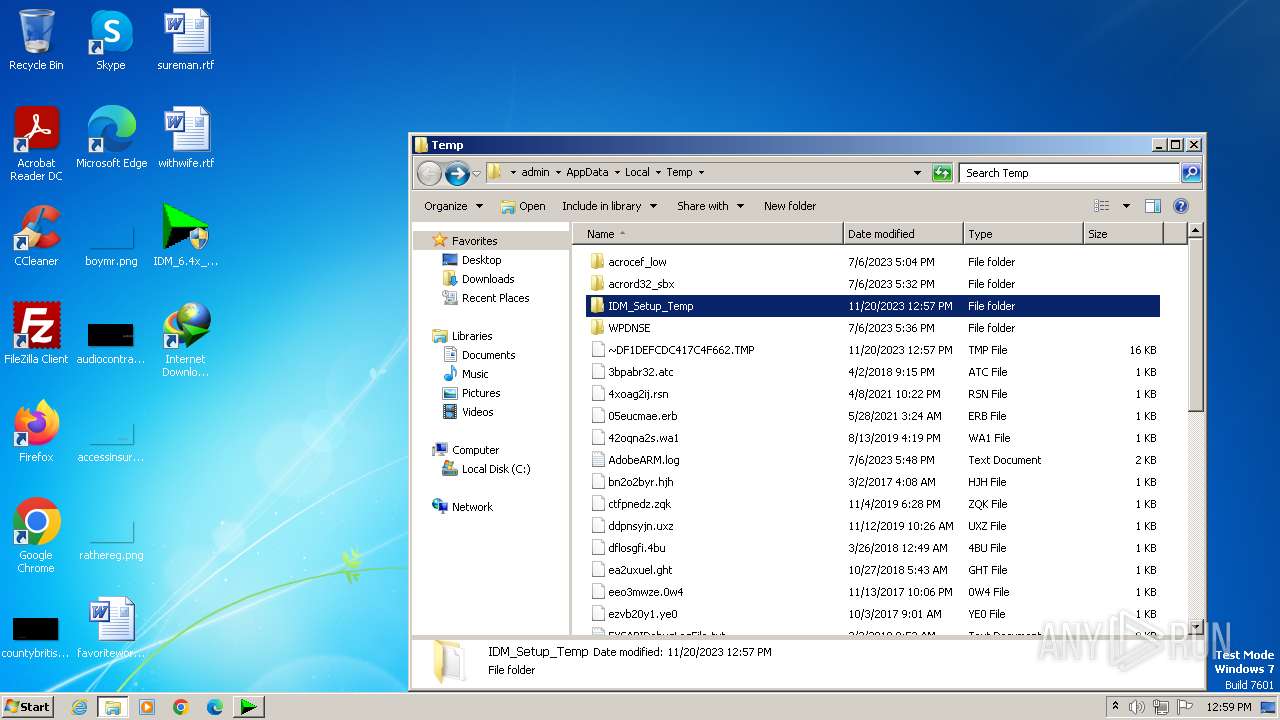
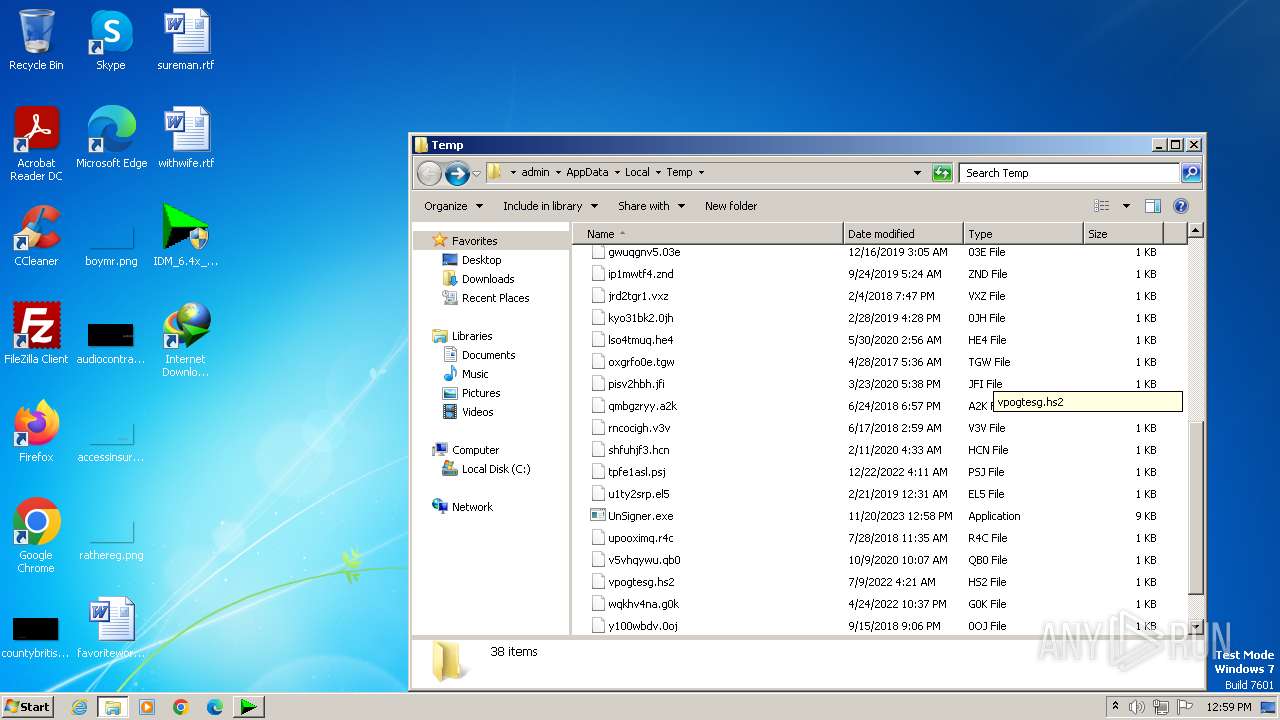
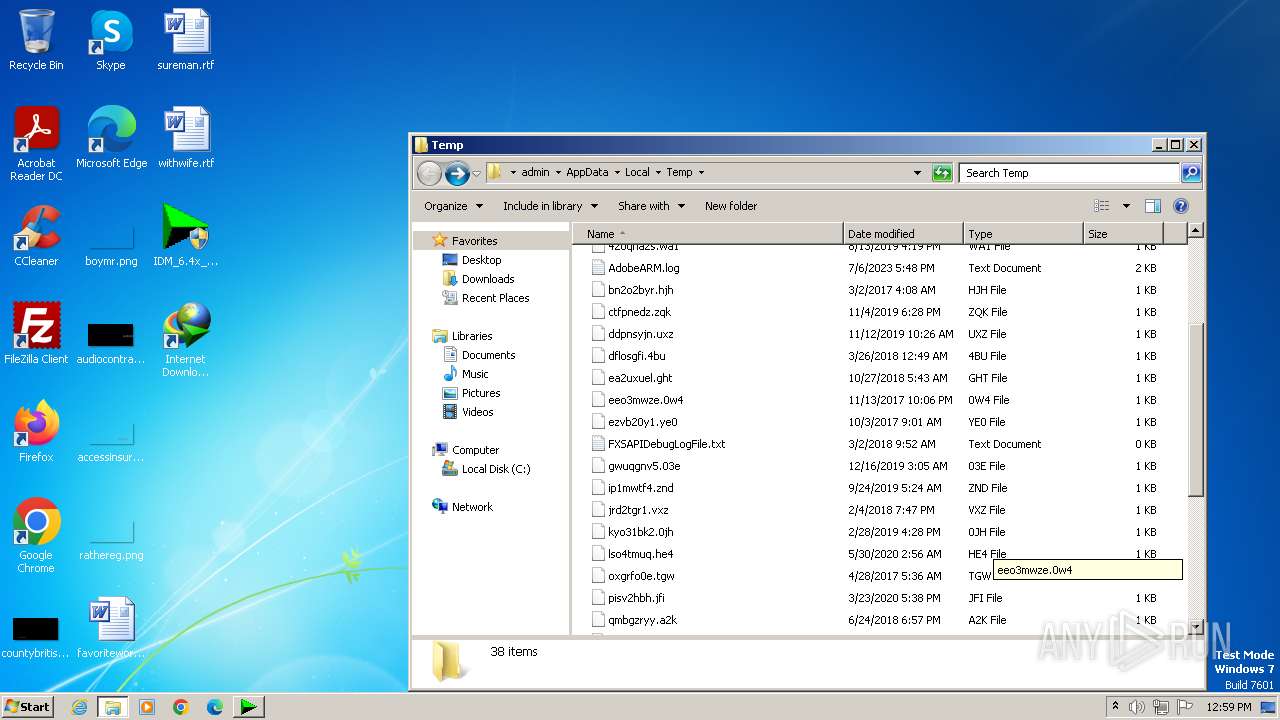
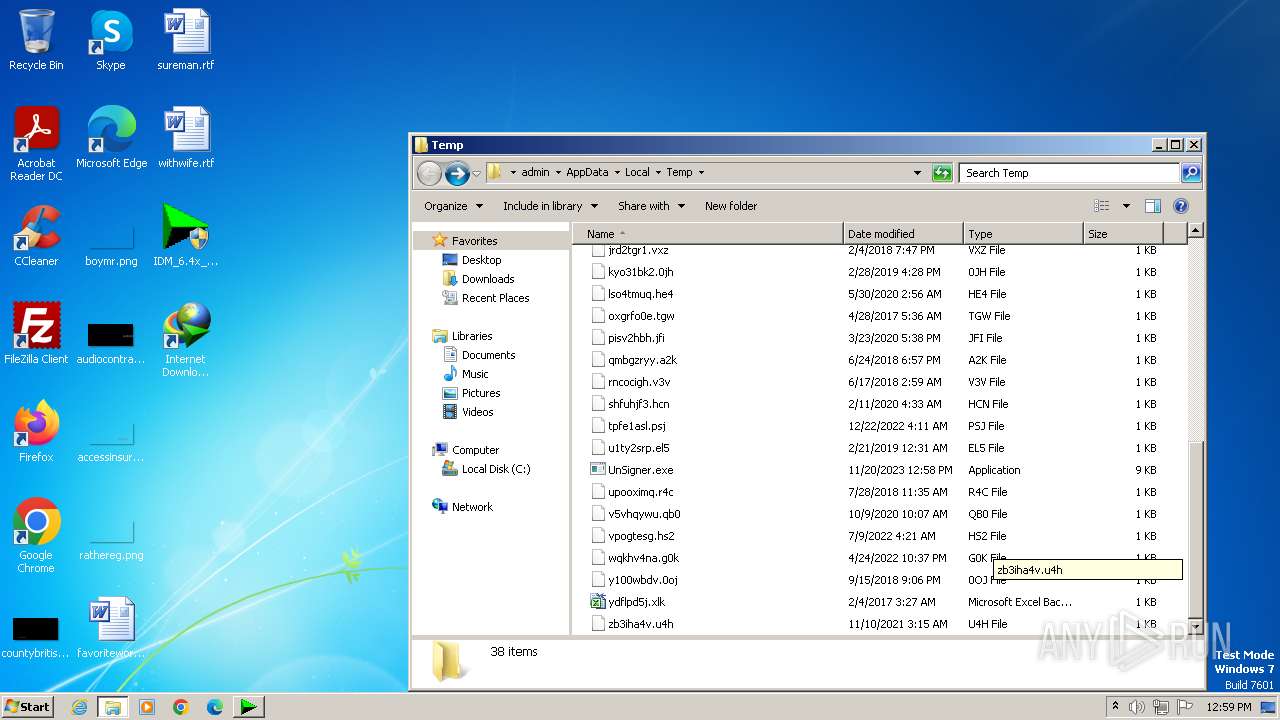
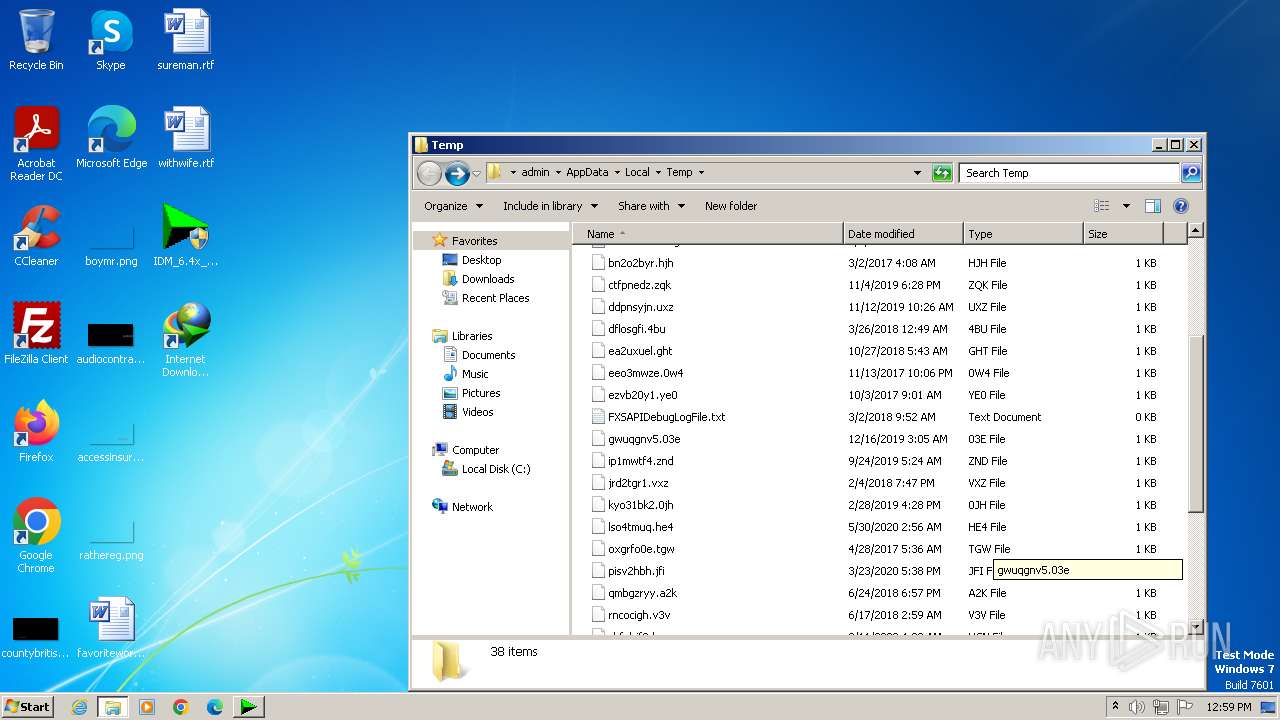
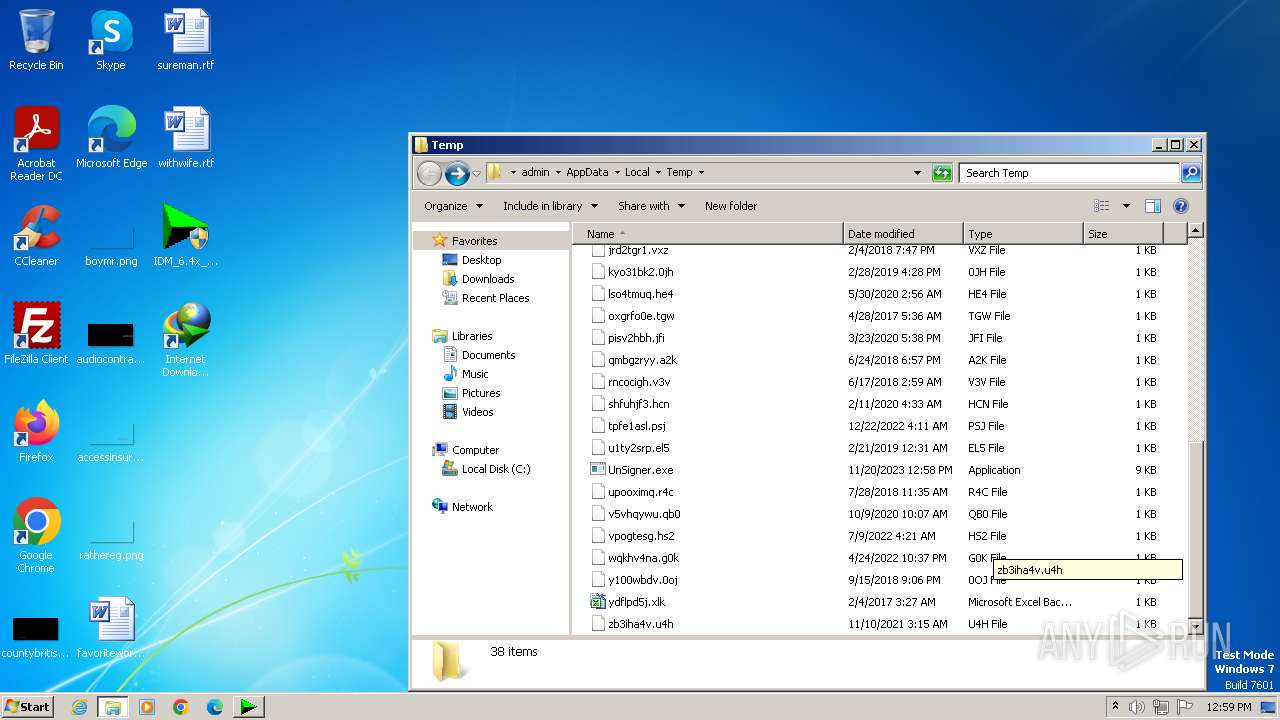
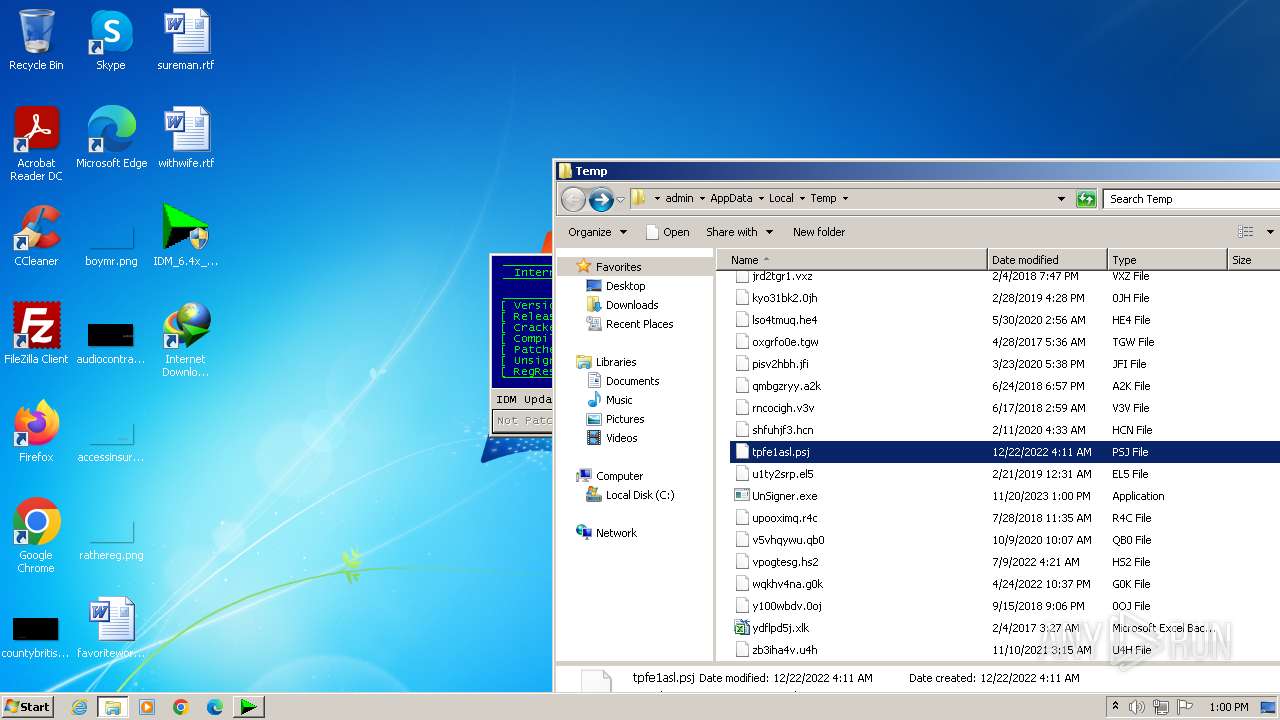
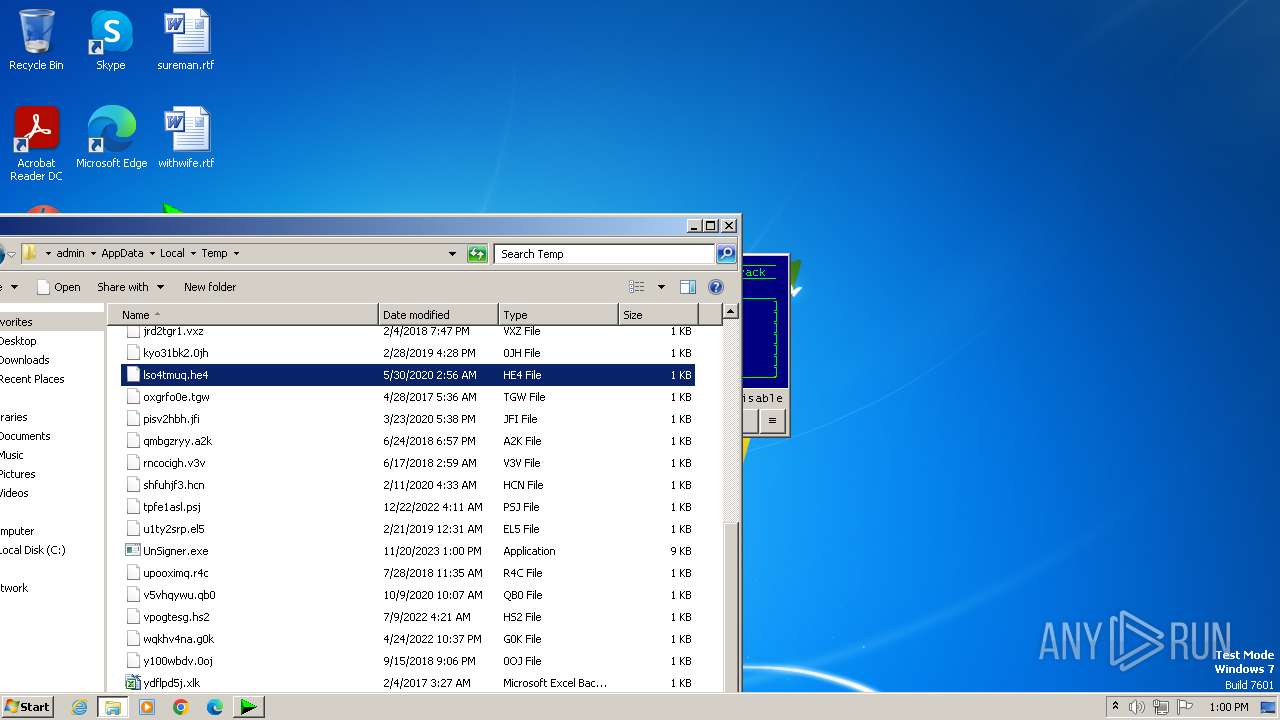
Create files in a temporary directory
- IDM1.tmp (PID: 2708)
- idman641build22.exe (PID: 2396)
- IDMan.exe (PID: 2820)
- IDMan.exe (PID: 3532)
- IDM_6.4x_Crack_v18.1.exe (PID: 1028)
- IDM_6.4x_Crack_v18.1.exe (PID: 4044)
Creates files in the program directory
- IDM1.tmp (PID: 2708)
- IDMan.exe (PID: 2820)
- wscript.exe (PID: 3388)
Creates files or folders in the user directory
- IDM1.tmp (PID: 2708)
- IDMan.exe (PID: 2820)
Reads the time zone
- runonce.exe (PID: 188)
Creates files in the driver directory
- rundll32.exe (PID: 1848)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (47.6) |
|---|---|---|
| .exe | | | Win32 Executable Borland Delphi 5 (32.3) |
| .exe | | | Win32 Executable Borland Delphi 6 (18.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.4) |
| .exe | | | Win32 Executable (generic) (0.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 32256 |
| InitializedDataSize: | 43008 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x89c4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
588
Monitored processes
521
Malicious processes
18
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Users\admin\AppData\Local\Temp\UnSigner.exe" -f -b "C:\Program Files\Internet Download Manager\IDMan.exe" | C:\Users\admin\AppData\Local\Temp\UnSigner.exe | — | IDM_6.4x_Crack_v18.1.exe | |||||||||||
User: admin Company: Pasi Ruokola Integrity Level: HIGH Description: PE file signature removal tool Exit code: 0 Version: 0.08 Modules
| |||||||||||||||
| 120 | reg query "HKU\.DEFAULT\Software\Classes\Wow6432Node\CLSID\{07999AC3-058B-40BF-984F-69EB1E554CA7}" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 120 | whoami /user /fo list | C:\Windows\System32\whoami.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: whoami - displays logged on user information Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 128 | REG DELETE "HKU\.DEFAULT\Software\Classes\CLSID\{D5B91409-A8CA-4973-9A0B-59F713D25671}" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 188 | "C:\Windows\system32\runonce.exe" -r | C:\Windows\System32\runonce.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 188 | reg query "HKU\.DEFAULT\Software\Classes\Wow6432Node\CLSID\{5ED60779-4DE2-4E07-B862-974CA4FF2E9C}" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 240 | reg query "HKU\.DEFAULT\Software\Classes\Wow6432Node\CLSID\{7B8E9164-324D-4A2E-A46D-0165FB2000EC}" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 240 | taskkill.exe /IM IDMan.exe /F | C:\Windows\System32\taskkill.exe | — | IDM_6.4x_Crack_v18.1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 280 | REG DELETE "HKLM\Software\Wow6432Node\Internet Download Manager" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 296 | REG DELETE "HKU\.DEFAULT\Software\Classes\Wow6432Node\CLSID\{E8CF4E59-B7A3-41F2-86C7-82B03334F22A}" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
51 965
Read events
51 212
Write events
636
Delete events
117
Modification events
| (PID) Process: | (3492) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 2166C0A101000000 | |||
| (PID) Process: | (3580) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 044CC1A101000000 | |||
| (PID) Process: | (3580) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (3580) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (3580) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Theme |
Value: 1 | |||
| (PID) Process: | (3580) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Enabled |
Value: 1 | |||
| (PID) Process: | (3580) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
| (PID) Process: | (3580) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableDefaultBrowserAgent |
Value: 0 | |||
| (PID) Process: | (3580) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|SetDefaultBrowserUserChoice |
Value: 1 | |||
| (PID) Process: | (3580) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|AppLastRunTime |
Value: D14E5F3C23B0D901 | |||
Executable files
19
Suspicious files
293
Text files
67
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3580 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3580 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | text | |
MD5:60E0DE9E05EC76C749D80F0D15A81B21 | SHA256:08252FA62CCCCD316474E20CC7317A6B5C932B2C972234318E8CCDA39EC2EF48 | |||
| 3580 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3580 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cert9.db-journal | binary | |
MD5:DEAE7ADACB727A3ACA3F791D85E88B8A | SHA256:5666F030D207BBED357AD146DF0525ED83AF5D9833E0E1155D22DE934F1FC969 | |||
| 3580 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\datareporting\glean\db\data.safe.bin | binary | |
MD5:1C3C58F7838DDE7F753614D170F110FC | SHA256:81C14432135B2A50DC505904E87781864CA561EFEF9E94BAECA3704D04E6DB3D | |||
| 3580 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\datareporting\glean\db\data.safe.tmp | binary | |
MD5:1C3C58F7838DDE7F753614D170F110FC | SHA256:81C14432135B2A50DC505904E87781864CA561EFEF9E94BAECA3704D04E6DB3D | |||
| 3580 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\protections.sqlite-journal | binary | |
MD5:3FEDCE714CB8251918C5E862F10630BC | SHA256:CE258752AF08FA3FC6F224A297BCF8CA931F3EA368B297C22A5364D0A4BD4FE1 | |||
| 3580 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\places.sqlite-wal | binary | |
MD5:BB064B0A21654B46BA9D2C419E39698A | SHA256:6B98375C5694DD4AA4725908E6BCA9A1B40B46751C3E17E43EEF5AC8441C07F2 | |||
| 3580 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cert9.db | binary | |
MD5:A39B8609CEC596880F7195D1C11506F3 | SHA256:F178819F9808B62CA8950CA99B4036C2192B3A4BE37D0BEE2CF16CD3C5435BFE | |||
| 3580 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\activity-stream.discovery_stream.json | binary | |
MD5:3D063636D30CD049829CDC32B9BFAE83 | SHA256:4CC54042B6EBAA814B5FA600FBA0EEFC09932CE3520B39556A58DCE5A0F12302 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
104
DNS requests
235
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3580 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | text | 8 b | unknown |
3580 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | text | 90 b | unknown |
3580 | firefox.exe | POST | 200 | 184.24.77.56:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
3580 | firefox.exe | POST | 200 | 184.24.77.56:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
3580 | firefox.exe | POST | 200 | 184.24.77.56:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
3580 | firefox.exe | POST | 200 | 184.24.77.45:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
3580 | firefox.exe | POST | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1c3 | unknown | binary | 472 b | unknown |
3580 | firefox.exe | POST | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1c3 | unknown | binary | 471 b | unknown |
3580 | firefox.exe | POST | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1c3 | unknown | binary | 471 b | unknown |
3580 | firefox.exe | POST | 200 | 108.138.16.27:80 | http://ocsp.r2m02.amazontrust.com/ | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
868 | svchost.exe | 184.30.20.134:80 | armmf.adobe.com | AKAMAI-AS | DE | unknown |
3580 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
3580 | firefox.exe | 34.117.237.239:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | unknown |
3580 | firefox.exe | 34.196.199.111:443 | spocs.getpocket.com | AMAZON-AES | US | unknown |
3580 | firefox.exe | 184.24.77.45:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
3580 | firefox.exe | 142.250.185.74:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
3580 | firefox.exe | 142.250.185.99:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
3580 | firefox.exe | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | unknown |
3580 | firefox.exe | 184.24.77.56:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
armmf.adobe.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| shared |
proxyserverecs-1736642167.us-east-1.elb.amazonaws.com |
| shared |
firefox.settings.services.mozilla.com |
| whitelisted |
r3.o.lencr.org |
| shared |