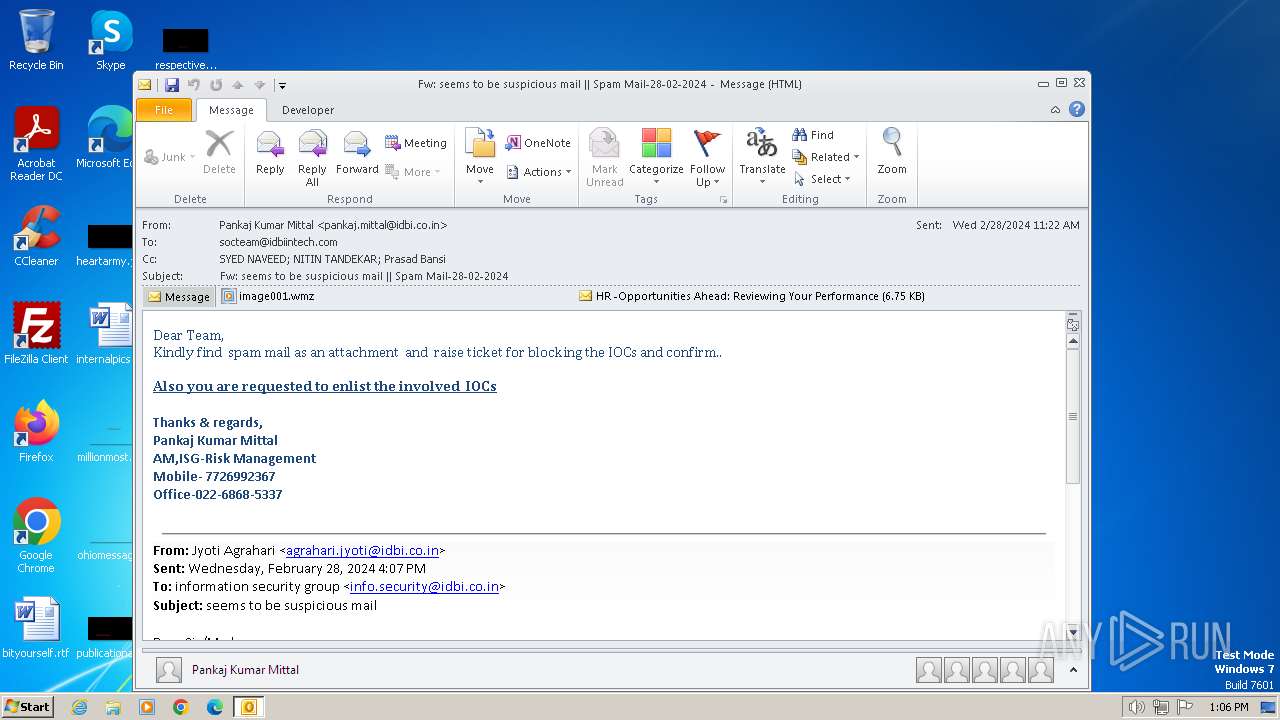
| File name: | Fw seems to be suspicious mail Spam Mail-28-02-2024.msg |
| Full analysis: | https://app.any.run/tasks/0e369ed5-2a00-4564-88e7-1ca97d594e6f |
| Verdict: | Malicious activity |
| Analysis date: | February 28, 2024, 13:05:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | AB822C82B1618598302728DDC7915A23 |
| SHA1: | 48EE2F5E5BC0BF928A9EB83858723FB9C037E58B |
| SHA256: | FE3EBB1C168E0644AA0416939A4F333020FD43383987530AD4B4C350A72E4E09 |
| SSDEEP: | 1536:ufGyG7WPEdlUntd/jPH+uN7MT1cUCPeelhUy48a0:uqWPEdKrGuMTuhUy481 |
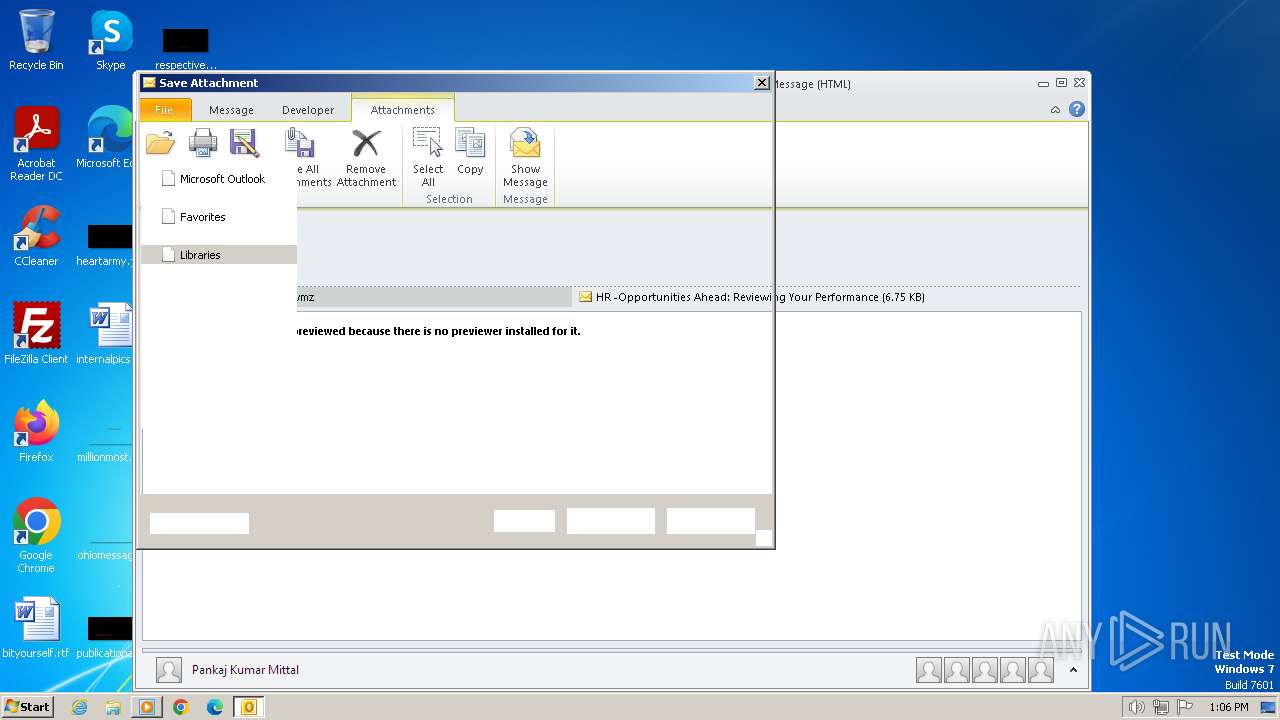
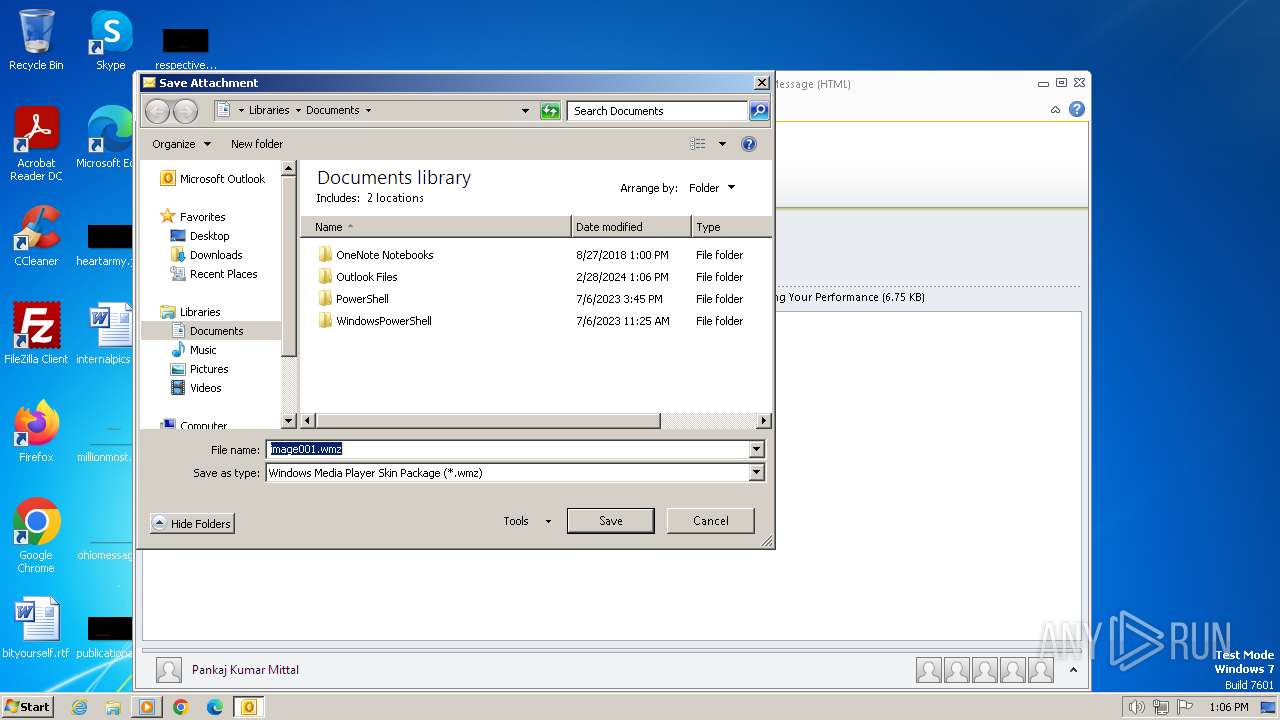
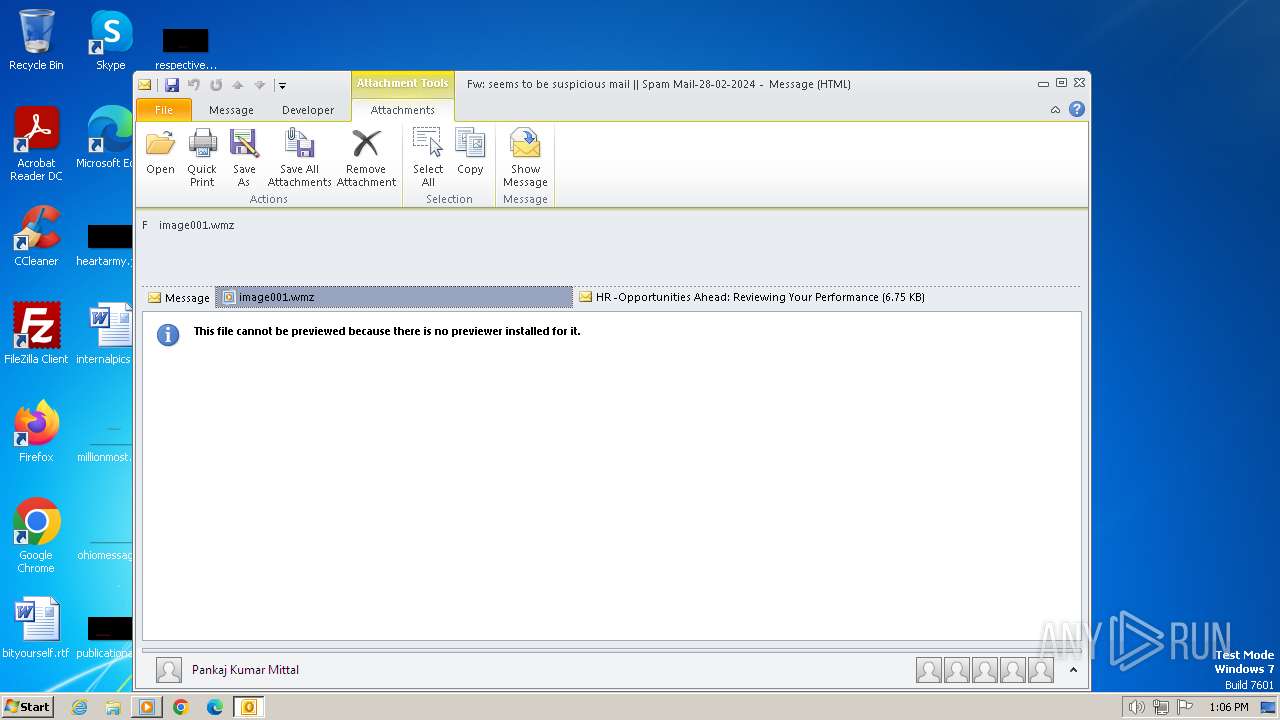
MALICIOUS
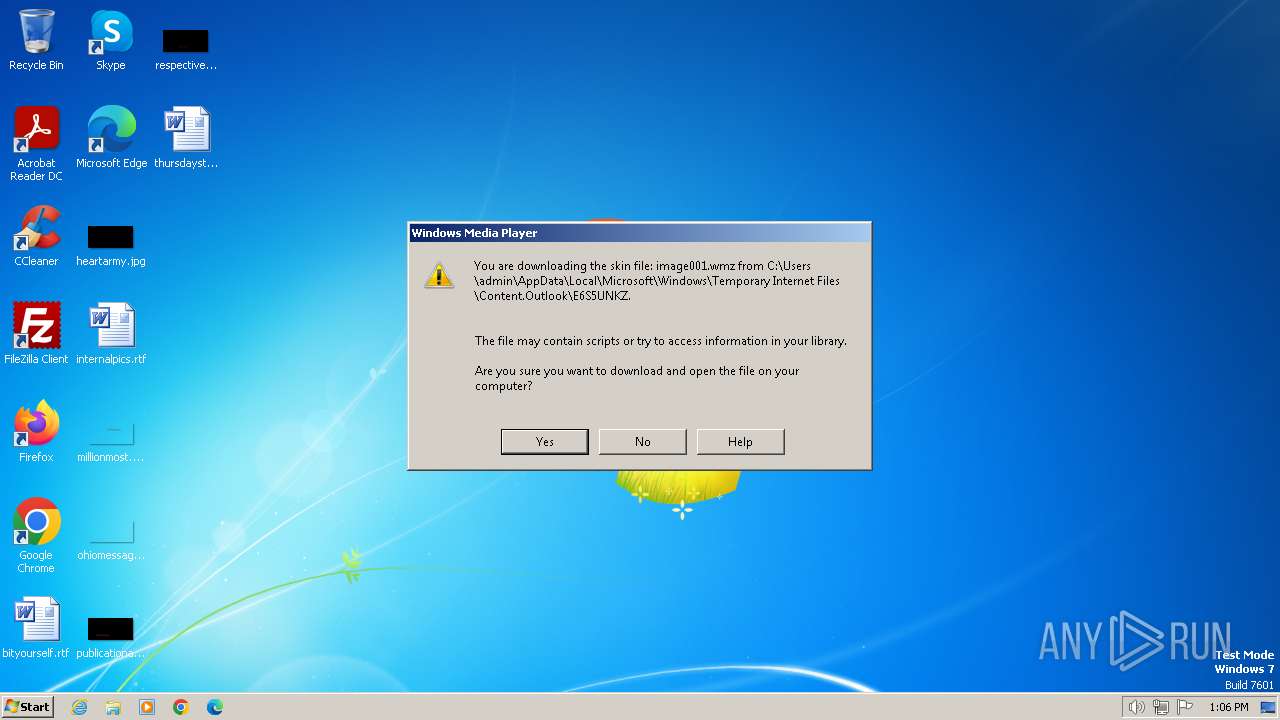
Unusual execution from MS Outlook
- OUTLOOK.EXE (PID: 3668)
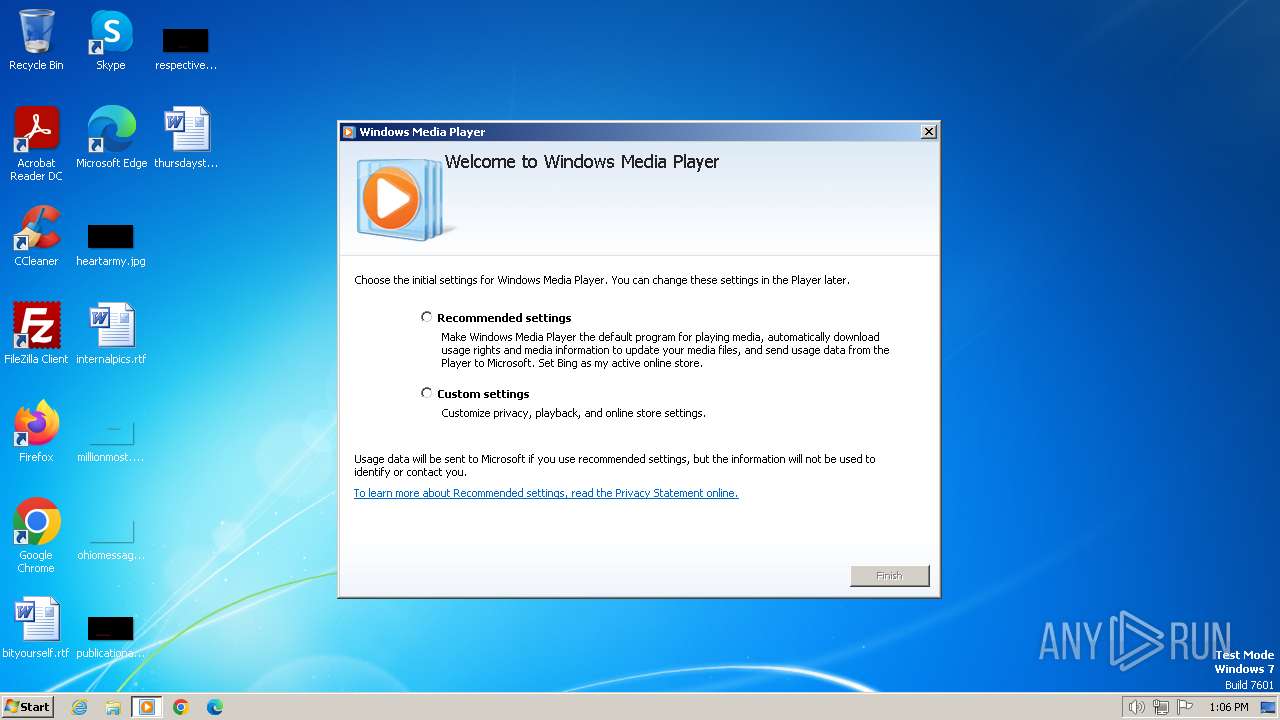
SUSPICIOUS
Reads the Internet Settings
- wmplayer.exe (PID: 3940)
- setup_wm.exe (PID: 3996)
- wmplayer.exe (PID: 2960)
- wmplayer.exe (PID: 3324)
Reads security settings of Internet Explorer
- wmplayer.exe (PID: 3940)
- setup_wm.exe (PID: 3996)
- wmplayer.exe (PID: 2960)
- wmplayer.exe (PID: 3324)
Reads Microsoft Outlook installation path
- wmplayer.exe (PID: 3324)
Reads Internet Explorer settings
- wmplayer.exe (PID: 3324)
INFO
Checks supported languages
- wmplayer.exe (PID: 3940)
- setup_wm.exe (PID: 3996)
- wmplayer.exe (PID: 2960)
- setup_wm.exe (PID: 3724)
- wmplayer.exe (PID: 3324)
The process uses the downloaded file
- OUTLOOK.EXE (PID: 3668)
Reads the computer name
- wmplayer.exe (PID: 3940)
- setup_wm.exe (PID: 3996)
- wmplayer.exe (PID: 2960)
- wmplayer.exe (PID: 3324)
- setup_wm.exe (PID: 3724)
Create files in a temporary directory
- setup_wm.exe (PID: 3996)
- wmplayer.exe (PID: 3324)
Reads the machine GUID from the registry
- setup_wm.exe (PID: 3996)
- wmplayer.exe (PID: 3324)
Reads Environment values
- setup_wm.exe (PID: 3996)
- wmplayer.exe (PID: 3324)
Process checks computer location settings
- setup_wm.exe (PID: 3996)
- wmplayer.exe (PID: 3324)
Checks proxy server information
- setup_wm.exe (PID: 3996)
- wmplayer.exe (PID: 3324)
Creates files or folders in the user directory
- wmplayer.exe (PID: 3324)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
49
Monitored processes
8
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1236 | "C:\Windows\system32\unregmp2.exe" /PerformIndivIfNeeded | C:\Windows\System32\unregmp2.exe | — | setup_wm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Media Player Setup Utility Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1572 | C:\Windows\system32\unregmp2.exe /ShowWMP /SetShowState /CreateMediaLibrary | C:\Windows\System32\unregmp2.exe | — | setup_wm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Media Player Setup Utility Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
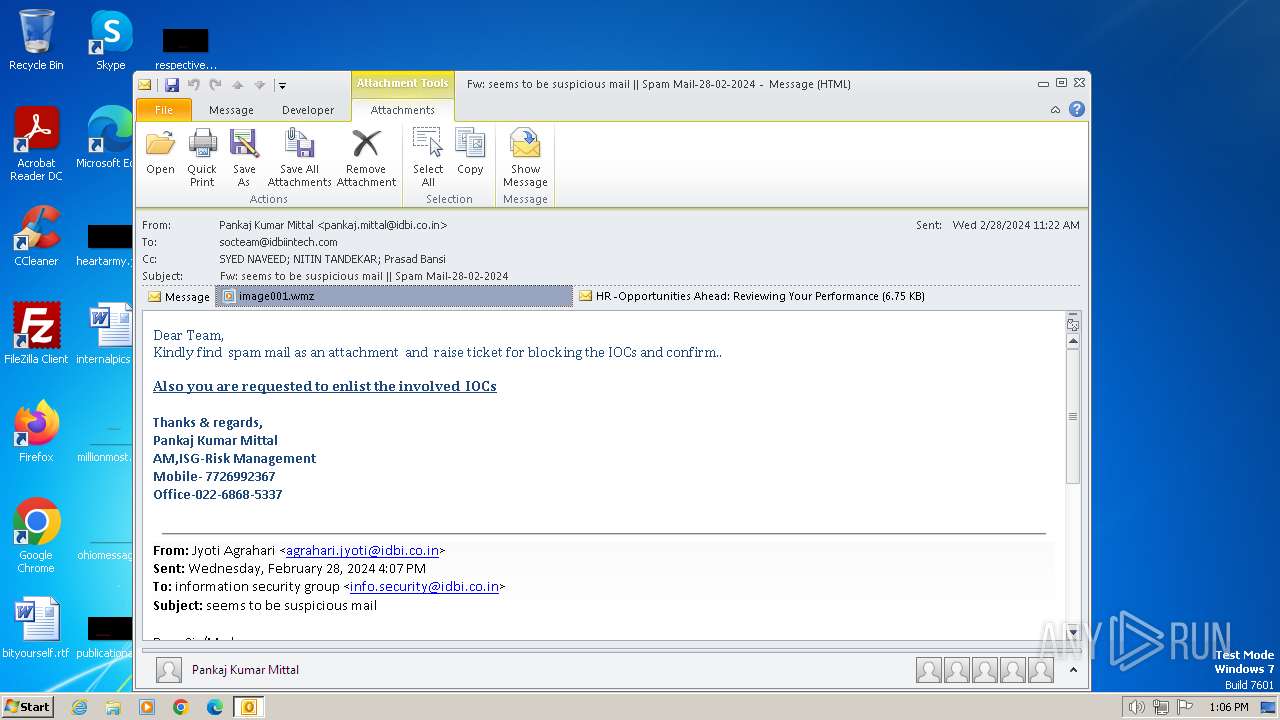
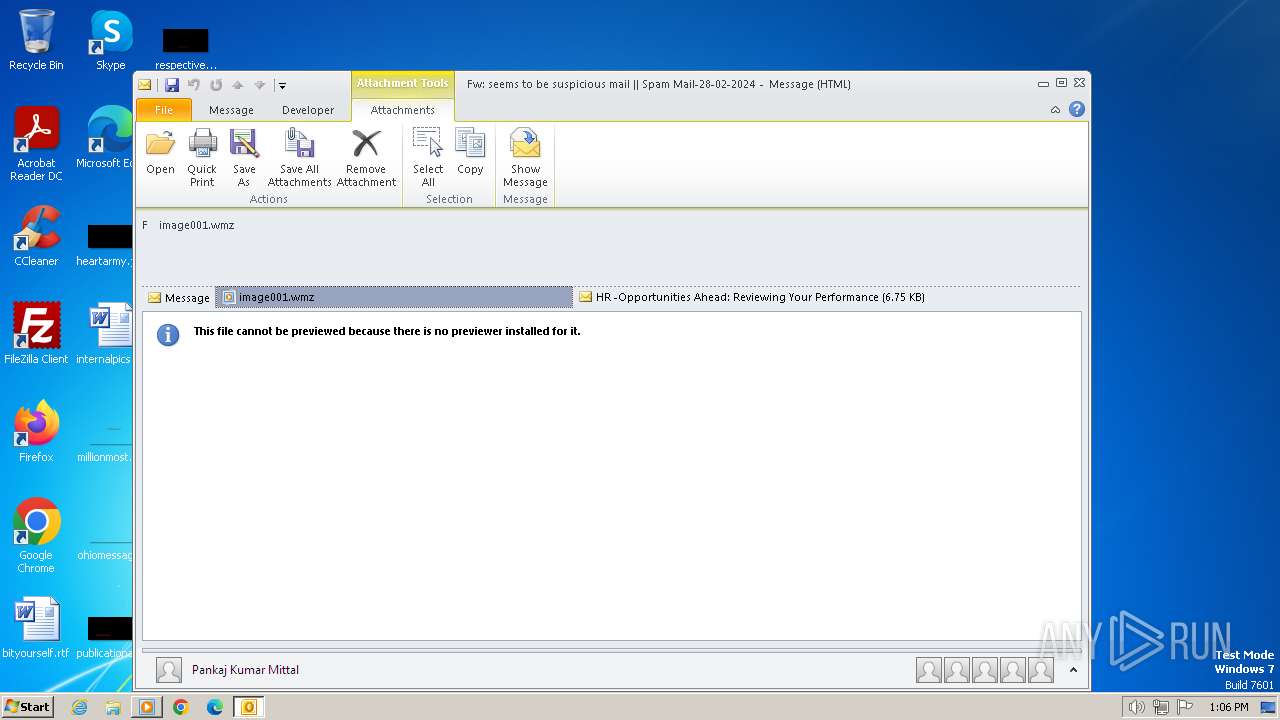
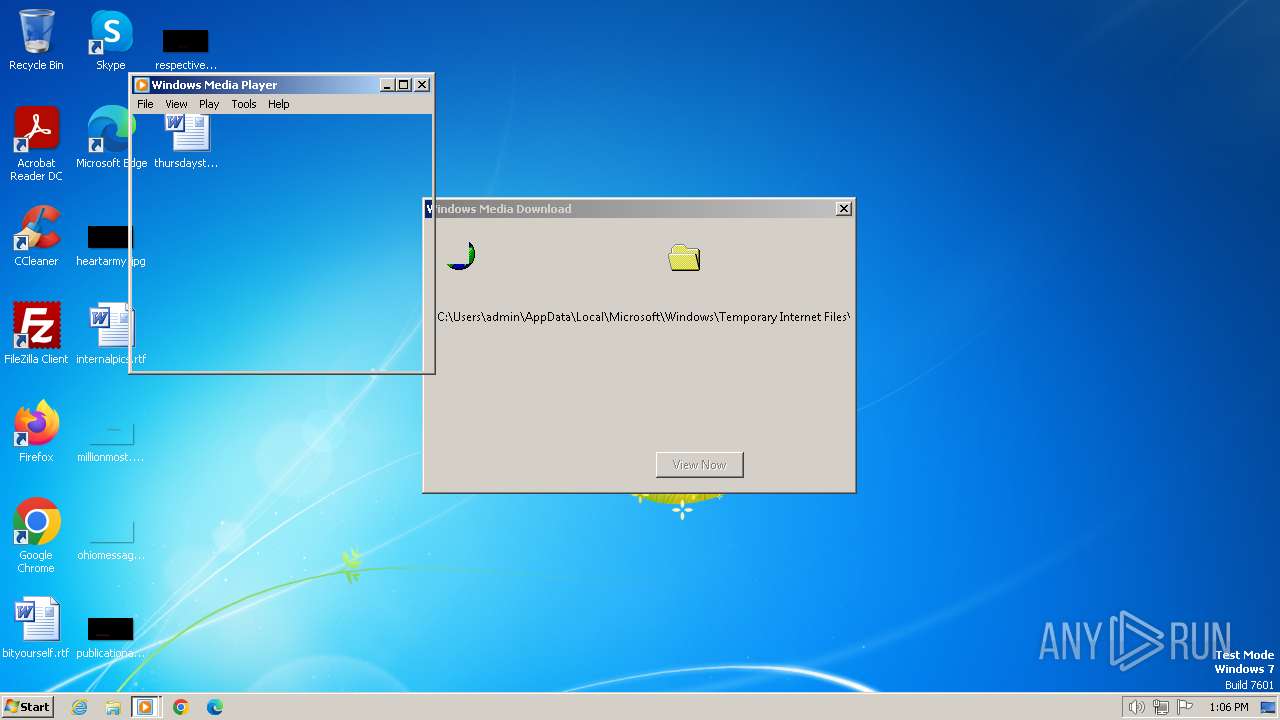
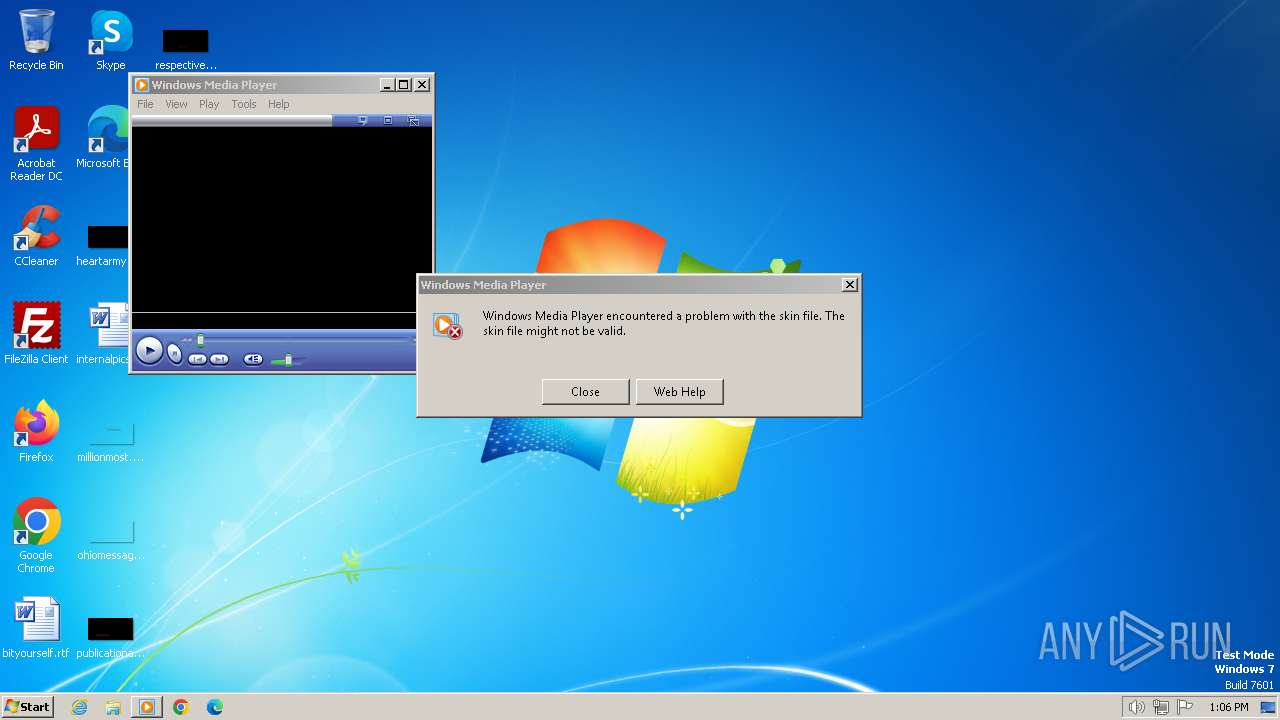
| 2960 | "C:\Program Files\Windows Media Player\wmplayer.exe" /layout:"C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\E6S5UNKZ\image001.wmz" | C:\Program Files\Windows Media Player\wmplayer.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Exit code: 0 Version: 12.0.7601.23517 (win7sp1_ldr.160812-0732) Modules
| |||||||||||||||
| 3324 | "C:\Program Files\Windows Media Player\wmplayer.exe" /Relaunch /layout:"C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\E6S5UNKZ\image001.wmz" | C:\Program Files\Windows Media Player\wmplayer.exe | setup_wm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Exit code: 0 Version: 12.0.7601.23517 (win7sp1_ldr.160812-0732) Modules
| |||||||||||||||
| 3668 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Fw seems to be suspicious mail Spam Mail-28-02-2024.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3724 | "C:\Program Files\Windows Media Player\setup_wm.exe" /RunOnce:"C:\Program Files\Windows Media Player\wmplayer.exe" /layout:"C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\E6S5UNKZ\image001.wmz" | C:\Program Files\Windows Media Player\setup_wm.exe | — | wmplayer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Media Configuration Utility Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3940 | "C:\Program Files\Windows Media Player\wmplayer.exe" /layout:"C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\E6S5UNKZ\image001.wmz" | C:\Program Files\Windows Media Player\wmplayer.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Exit code: 0 Version: 12.0.7601.23517 (win7sp1_ldr.160812-0732) Modules
| |||||||||||||||
| 3996 | "C:\Program Files\Windows Media Player\setup_wm.exe" /RunOnce:"C:\Program Files\Windows Media Player\wmplayer.exe" /layout:"C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\E6S5UNKZ\image001.wmz" | C:\Program Files\Windows Media Player\setup_wm.exe | wmplayer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Media Configuration Utility Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
25 941
Read events
24 897
Write events
921
Delete events
123
Modification events
| (PID) Process: | (3668) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3668) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3668) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3668) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3668) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3668) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3668) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3668) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3668) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (3668) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
12
Text files
25
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3668 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRF378.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3668 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 3668 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 3668 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\3229C6CF.dat | image | |
MD5:92C652B84E3391EE1920EC879F181B17 | SHA256:87ED476CD56E20250B84F4B857647E65D0E928FAC304CE4C0363DE7ADE7F14FA | |||
| 3668 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{30112F42-A90D-4F98-9C5B-90BC870D24CE}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
| 3668 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\E6S5UNKZ\image001 (2).wmz:Zone.Identifier:$DATA | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
| 3668 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\E6S5UNKZ\image001 (2).wmz | compressed | |
MD5:604EE5E3D30EA54CBD1166C0CBE65FF8 | SHA256:64209B36DF10985EC46ECF4D7AEFD4A6E2A4BEDA7A8789B63C528A6D224E42B9 | |||
| 3996 | setup_wm.exe | C:\Users\admin\AppData\Local\Temp\tmp77796.WMC\allservices.xml | xml | |
MD5:DF03E65B8E082F24DAB09C57BC9C6241 | SHA256:155B9C588061C71832AF329FAFA5678835D9153B8FBB7592195AE953D0C455BA | |||
| 3996 | setup_wm.exe | C:\Users\admin\AppData\Local\Temp\tmp79062.WMC\serviceinfo.xml | text | |
MD5:D58DA90D6DC51F97CB84DFBFFE2B2300 | SHA256:93ACDB79543D9248CA3FCA661F3AC287E6004E4B3DAFD79D4C4070794FFBF2AD | |||
| 3668 | OUTLOOK.EXE | C:\Users\admin\Downloads\image001.wmz:Zone.Identifier:$DATA | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
11
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3996 | setup_wm.exe | GET | 302 | 88.221.110.242:80 | http://redir.metaservices.microsoft.com/redir/allservices/?sv=5&version=12.0.7601.17514&locale=409&userlocale=409&geoid=f4&parch=x86&arch=x86 | unknown | — | — | unknown |
3996 | setup_wm.exe | GET | 200 | 88.221.110.104:80 | http://onlinestores.metaservices.microsoft.com/serviceswitching/AllServices.aspx?sv=5&version=12.0.7601.17514&locale=409&userlocale=409&geoid=f4&parch=x86&arch=x86 | unknown | xml | 546 b | unknown |
3324 | wmplayer.exe | GET | 302 | 88.221.110.242:80 | http://redir.metaservices.microsoft.com/redir/getmdrcdbackground/?locale=409&geoid=f4&version=12.0.7601.24499&userlocale=409&wmid=5FA05D35-A682-4AF6-96F7-0773E42D4D16 | unknown | — | — | unknown |
3996 | setup_wm.exe | GET | 200 | 88.221.110.104:80 | http://onlinestores.metaservices.microsoft.com/bing/bing.xml | unknown | text | 523 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3668 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3996 | setup_wm.exe | 88.221.110.242:80 | redir.metaservices.microsoft.com | Akamai International B.V. | DE | unknown |
3996 | setup_wm.exe | 88.221.110.104:80 | onlinestores.metaservices.microsoft.com | Akamai International B.V. | DE | unknown |
2260 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
3324 | wmplayer.exe | 88.221.110.242:80 | redir.metaservices.microsoft.com | Akamai International B.V. | DE | unknown |
3324 | wmplayer.exe | 49.13.77.253:80 | toc.music.metaservices.microsoft.com | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
redir.metaservices.microsoft.com |
| whitelisted |
onlinestores.metaservices.microsoft.com |
| whitelisted |
sqm.msn.com |
| unknown |
toc.music.metaservices.microsoft.com |
| whitelisted |