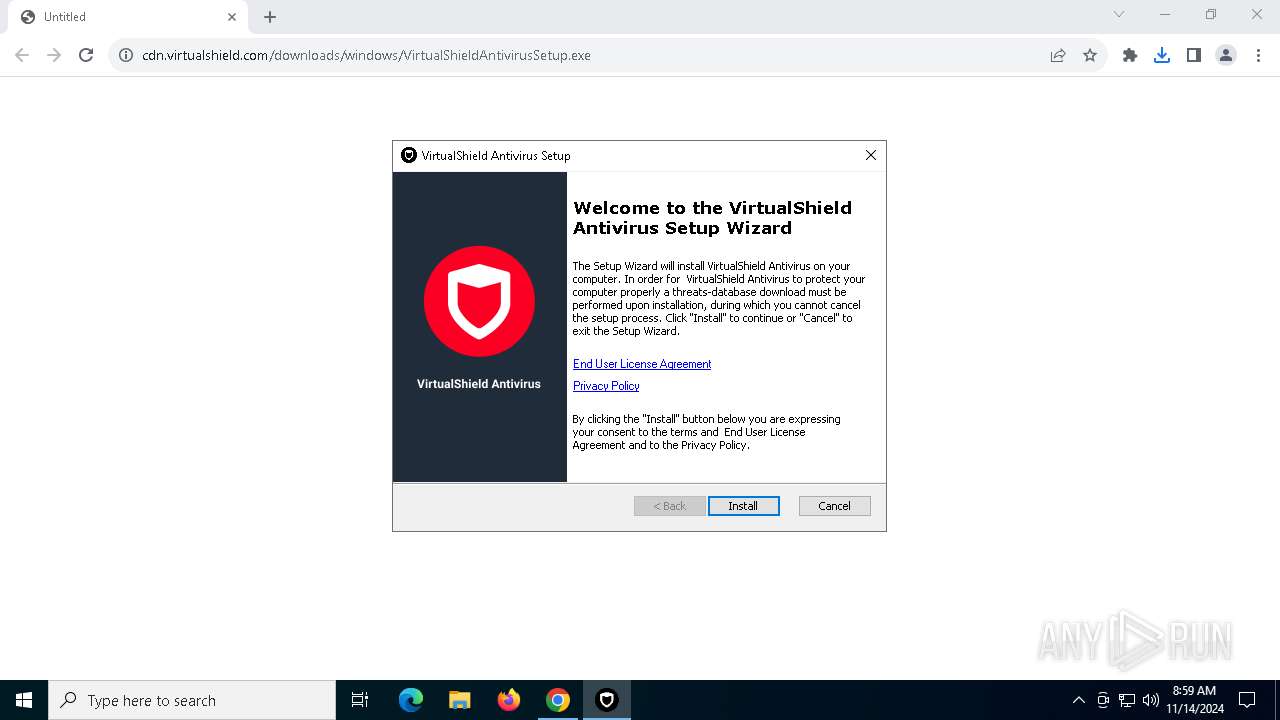
| URL: | https://cdn.virtualshield.com/downloads/windows/VirtualShieldAntivirusSetup.exe |
| Full analysis: | https://app.any.run/tasks/9961cee7-b5ff-46b5-8b5b-6b96cbbd3e65 |
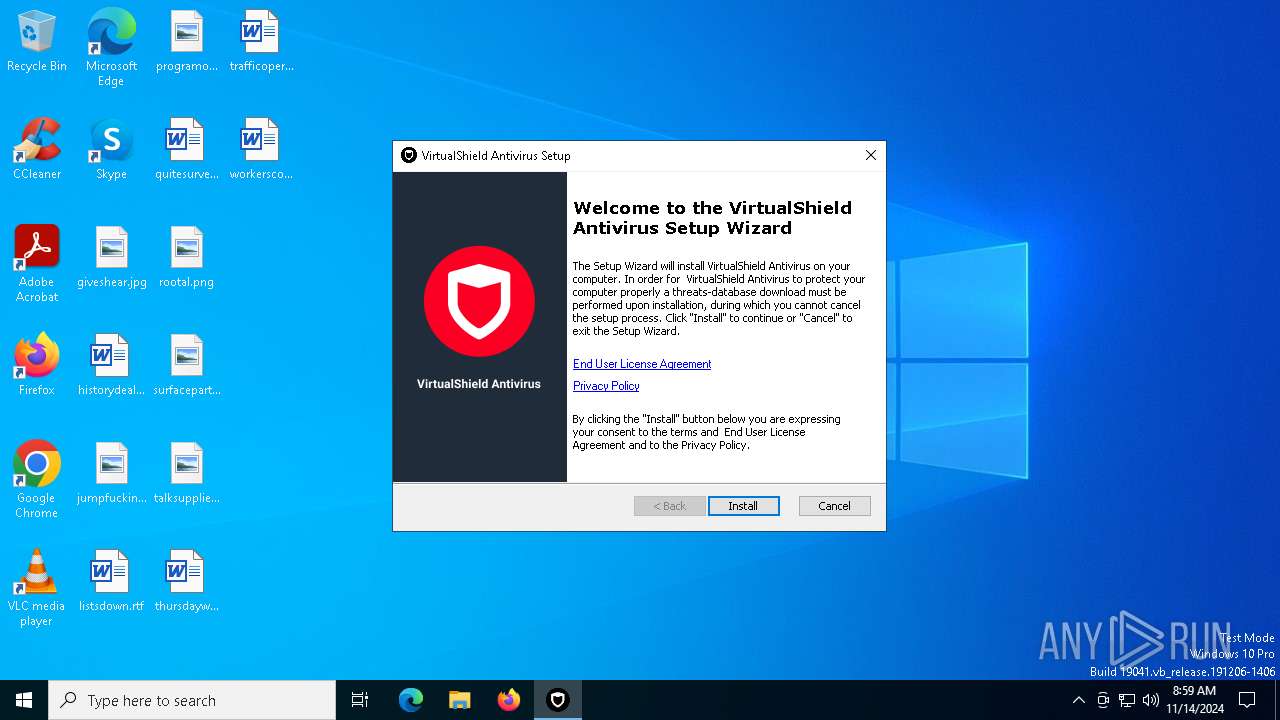
| Verdict: | Malicious activity |
| Analysis date: | November 14, 2024, 08:58:17 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 3913A7916E7B7EEC8801A76708488336 |
| SHA1: | 7A0B099FAAC27E8971E18CA4DDD6F61C025B645C |
| SHA256: | FE3C4BF1C5C1DEBFEC490AB9FC75D4452B0973F0F19774EF582C3D8D28B1BE6F |
| SSDEEP: | 3:N8cKQTfJBLR8XK/1K7zJ2edoX1kA:2cB9R8aI7MX1kA |
MALICIOUS
Starts NET.EXE for service management
- endpoint-protection-installer-x64.tmp (PID: 5700)
- net.exe (PID: 4500)
- net.exe (PID: 9112)
- net.exe (PID: 4260)
- net.exe (PID: 5068)
- net.exe (PID: 6024)
- net.exe (PID: 6336)
- net.exe (PID: 8888)
- net.exe (PID: 7156)
- net.exe (PID: 6260)
- net.exe (PID: 6316)
- net.exe (PID: 1952)
- net.exe (PID: 7328)
- net.exe (PID: 6160)
Executing a file with an untrusted certificate
- ACSSigned.exe (PID: 6736)
- endpoint-protection-installer-x64.exe (PID: 8116)
- endpointprotection.exe (PID: 8956)
- ACSSigned.exe (PID: 8464)
- rtp_setup.exe (PID: 9112)
- firewall.tools.exe (PID: 7160)
- endpointprotection.exe (PID: 6792)
- ACSSigned.exe (PID: 1084)
- ACSSigned.exe (PID: 8236)
- ACSSigned.exe (PID: 3744)
- ACSSigned.exe (PID: 7136)
- endpointprotection.exe (PID: 5080)
- wsc_agent.exe (PID: 5564)
- wsc_agent.exe (PID: 7536)
- SentryProtection.exe (PID: 8136)
- ACSSigned.exe (PID: 6708)
- SentryEye.exe (PID: 9212)
- firewall.tools.exe (PID: 7320)
SUSPICIOUS
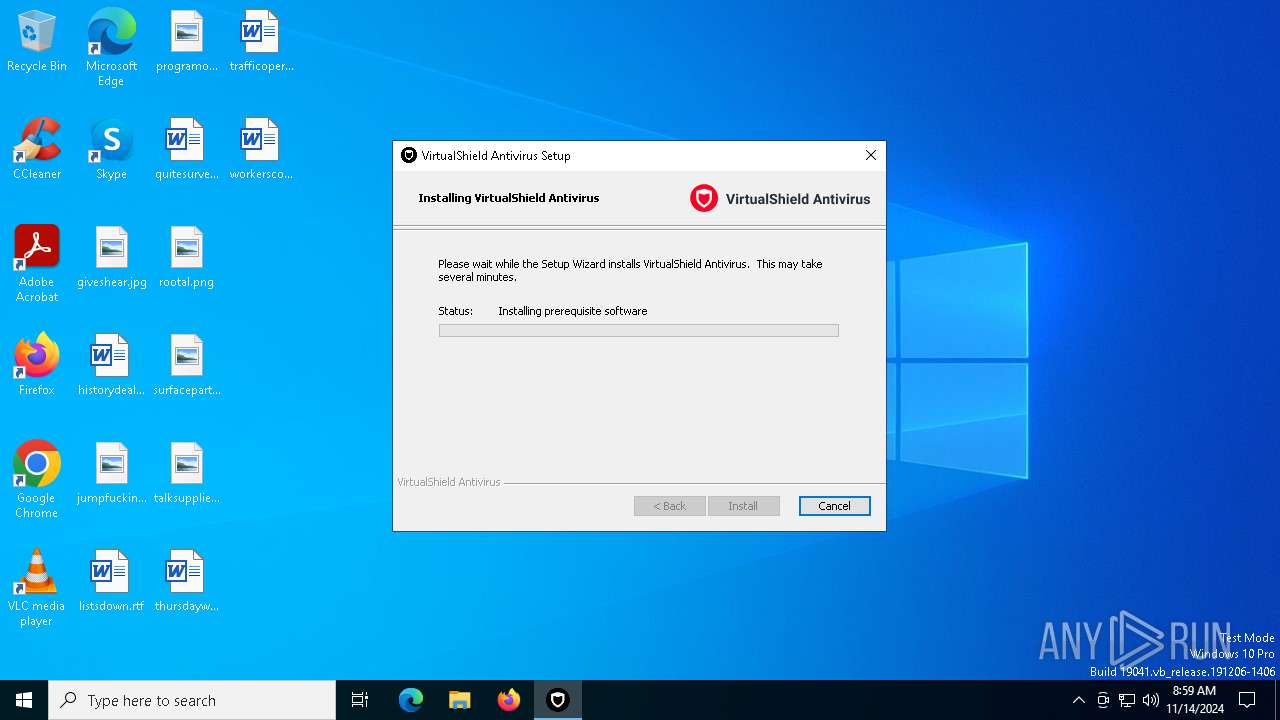
Executable content was dropped or overwritten
- VirtualShieldAntivirusSetup.exe (PID: 5068)
- VirtualShieldAntivirusSetup.exe (PID: 8104)
- endpoint-protection-installer-x64.exe (PID: 8116)
- endpoint-protection-installer-x64.tmp (PID: 5700)
- rtp_setup.exe (PID: 9112)
- SentryProtection.exe (PID: 8136)
- firewall.tools.exe (PID: 7160)
- endpointprotection.exe (PID: 5080)
Process drops legitimate windows executable
- VirtualShieldAntivirusSetup.exe (PID: 5068)
- VirtualShieldAntivirusSetup.exe (PID: 8104)
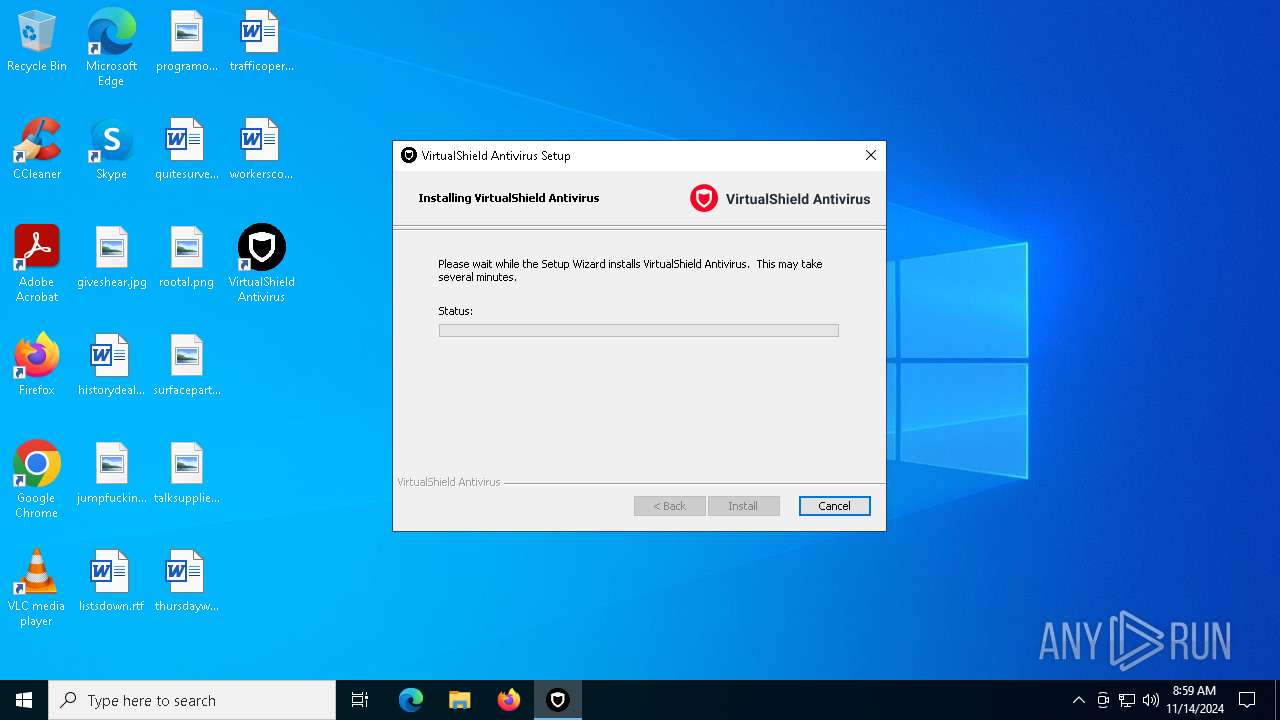
Application launched itself
- VirtualShieldAntivirusSetup.exe (PID: 8104)
Starts SC.EXE for service management
- endpoint-protection-installer-x64.tmp (PID: 5700)
Executes as Windows Service
- VSSVC.exe (PID: 7672)
- endpointprotection.exe (PID: 5080)
Drops a system driver (possible attempt to evade defenses)
- rtp_setup.exe (PID: 9112)
- endpoint-protection-installer-x64.tmp (PID: 5700)
- firewall.tools.exe (PID: 7160)
- SentryProtection.exe (PID: 8136)
INFO
Application launched itself
- chrome.exe (PID: 7092)
- msedge.exe (PID: 7936)
- msedge.exe (PID: 4956)
- msedge.exe (PID: 6208)
Executable content was dropped or overwritten
- chrome.exe (PID: 7092)
- msiexec.exe (PID: 7408)
- msedge.exe (PID: 3076)
Manages system restore points
- SrTasks.exe (PID: 1160)
Sends debugging messages
- msiexec.exe (PID: 4896)
- msiexec.exe (PID: 4448)
Manual execution by a user
- msedge.exe (PID: 4956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
342
Monitored processes
200
Malicious processes
10
Suspicious processes
13
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 696 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3208 --field-trial-handle=2300,i,7857203924050384469,860010061826189114,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 780 | "sc.exe" delete rtp_elam | C:\Windows\System32\sc.exe | — | endpoint-protection-installer-x64.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1804 --field-trial-handle=1896,i,15375128421326877144,18083974601975220090,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 864 | "sc.exe" delete BdSentry | C:\Windows\System32\sc.exe | — | endpoint-protection-installer-x64.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1008 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7540 --field-trial-handle=2596,i,15521433479206650218,17097005924680218392,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1084 | "ACSSigned.exe" | C:\Program Files\Endpoint Protection SDK\ACSSigned.exe | — | endpointprotection.exe | |||||||||||
User: admin Company: Avira Operations GmbH Integrity Level: HIGH Description: ASCSigned Exit code: 0 Version: 255.255.255.255 Modules
| |||||||||||||||
| 1160 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1200 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x294,0x298,0x29c,0x28c,0x2a4,0x7ffbc7595fd8,0x7ffbc7595fe4,0x7ffbc7595ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1252 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x288,0x294,0x298,0x28c,0x2a4,0x7ffbc7595fd8,0x7ffbc7595fe4,0x7ffbc7595ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1332 | "C:\Program Files (x86)\VirtualShield Antivirus\VirtualShieldAntivirus.exe" afterinstallrun "C:\Users\admin\Downloads\VirtualShieldAntivirusSetup.exe" | C:\Program Files (x86)\VirtualShield Antivirus\VirtualShieldAntivirus.exe | msiexec.exe | ||||||||||||
User: admin Company: VirtualShield LLC Integrity Level: HIGH Description: VirtualShield Antivirus Version: 5.4.8.0 Modules
| |||||||||||||||
Total events
110 740
Read events
110 107
Write events
585
Delete events
48
Modification events
| (PID) Process: | (7092) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7092) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7092) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7092) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7092) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7948) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000EC6291707336DB01 | |||
| (PID) Process: | (7092) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (7092) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | GoogleChromeAutoLaunch_A822CA3D40D4B8944864CFEA751D8D57 |
Value: | |||
| (PID) Process: | (7408) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000DB4BD1777336DB01F01C0000E81E0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7408) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000DB4BD1777336DB01F01C0000E81E0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
343
Suspicious files
1 687
Text files
825
Unknown types
94
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF8fbfc.TMP | — | |
MD5:— | SHA256:— | |||
| 7092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF8fbfc.TMP | — | |
MD5:— | SHA256:— | |||
| 7092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF8fc0c.TMP | — | |
MD5:— | SHA256:— | |||
| 7092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF8fbfc.TMP | — | |
MD5:— | SHA256:— | |||
| 7092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF8fc0c.TMP | — | |
MD5:— | SHA256:— | |||
| 7092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
81
TCP/UDP connections
150
DNS requests
160
Threats
30
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3948 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
8104 | VirtualShieldAntivirusSetup.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
7700 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7700 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8104 | VirtualShieldAntivirusSetup.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
8104 | VirtualShieldAntivirusSetup.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEArQhA8sIa9U0BELas9d8eM%3D | unknown | — | — | whitelisted |
3824 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.216.77.25:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6944 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3948 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3948 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
780 | svchost.exe | 23.218.210.69:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
cdn.virtualshield.com |
| whitelisted |
accounts.google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5900 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
5900 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
5900 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Possible Abuse Customer Service with Ticketing (.freshdesk .com) |
5900 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Possible Abuse Customer Service with Ticketing (.freshdesk .com) |
5900 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Possible Abuse Customer Service with Ticketing (.freshdesk .com) |
5900 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Possible Abuse Customer Service with Ticketing (.freshdesk .com) |
5900 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Possible Abuse Customer Service with Ticketing (.freshdesk .com) |
5900 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Possible Abuse Customer Service with Ticketing (.freshdesk .com) |
5900 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5900 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
Process | Message |
|---|---|
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |