| File name: | Test.jar |
| Full analysis: | https://app.any.run/tasks/982bd9dd-b208-4847-aeed-ae0e5d8ab6a6 |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2023, 09:34:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | application/java-archive |
| File info: | Java archive data (JAR) |
| MD5: | 541319AA9638C234524FF42D8112F699 |
| SHA1: | 281899B7D51CF6922D4301027FC4D18A7E869812 |
| SHA256: | FE17D97137655583BC1E32136E3A5A94CB1E7F3C0D415CFD981E8856DFFB8C3D |
| SSDEEP: | 24:9kf4tkI/pGA7kSpeebM0p38gr/gBauQY7r0Ket33Yi5iUxgbRX:9jt7/Lj7R8gr/gBauQY7ort33YMVxK5 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- javaw.exe (PID: 2928)
INFO
Create files in a temporary directory
- javaw.exe (PID: 2928)
Checks supported languages
- javaw.exe (PID: 2928)
Reads the computer name
- javaw.exe (PID: 2928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jar | | | Java Archive (78.3) |
|---|---|---|
| .zip | | | ZIP compressed archive (21.6) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:08:14 15:43:28 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 2 |
| ZipUncompressedSize: | - |
| ZipFileName: | META-INF/ |
Total processes
32
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
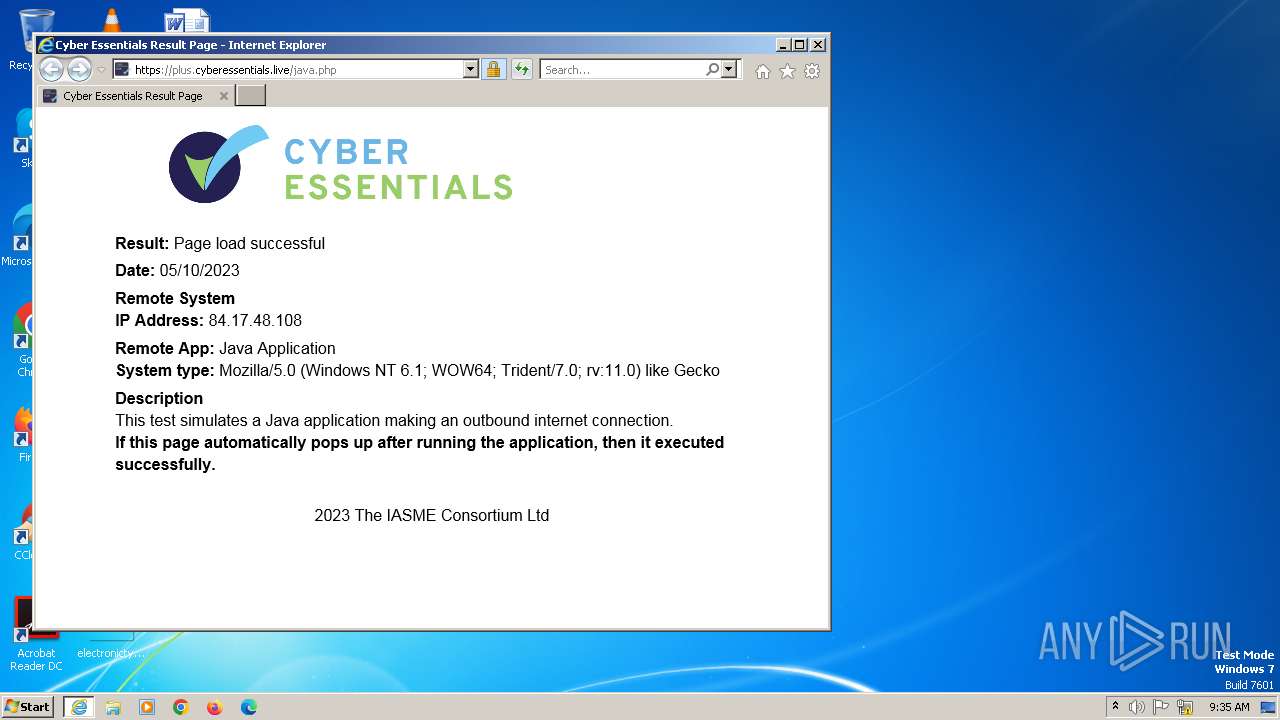
| 2216 | "C:\Program Files\Internet Explorer\iexplore.exe" https://plus.cyberessentials.live/java.php | C:\Program Files\Internet Explorer\iexplore.exe | javaw.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2552 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:2216 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2928 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Temp\Test.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | explorer.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
3 794
Read events
3 732
Write events
61
Delete events
1
Modification events
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 5 | |||
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 91676960 | |||
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31049115 | |||
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31049165 | |||
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000BD000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
10
Text files
22
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2552 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab3B11.tmp | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 2552 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 2928 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:C7B516583C4F694504E6170E824A0FD8 | SHA256:F1ABDB56A3DC4A0F117AA3D9005C4349BCCB8B620310C5E43AD059D8AA72B871 | |||
| 2552 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:7D5C827E808CBD99C6CEA1E8A999D039 | SHA256:68791CCDAEF9F5C81C37B6F120DCAAA7B4EF54A634F51C340B398AE6A2D8405A | |||
| 2552 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar3B00.tmp | binary | |
MD5:9441737383D21192400ECA82FDA910EC | SHA256:BC3A6E84E41FAEB57E7C21AA3B60C2A64777107009727C5B7C0ED8FE658909E5 | |||
| 2552 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab3AFF.tmp | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 2552 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar3B12.tmp | binary | |
MD5:9441737383D21192400ECA82FDA910EC | SHA256:BC3A6E84E41FAEB57E7C21AA3B60C2A64777107009727C5B7C0ED8FE658909E5 | |||
| 2552 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\UJFUX3OG\java[1].htm | html | |
MD5:999CAE9BAE2A11DD006A0EC6051937E8 | SHA256:CE6E9332482151C77C86B777A40D26293A07AB11A1DFA44BEE1BB110D9ECBDAB | |||
| 2552 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\XLWA6BPE\index-grid[1].css | text | |
MD5:8C31E76E4BF8C8C1A9E66C7ED2E9F0DD | SHA256:D84DAF30AA7378AC95D80AE8438E1F9E26EE5DEBCA23C2E0E92B238A6215CD22 | |||
| 2552 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\XLWA6BPE\standardize[1].css | text | |
MD5:AD8C1B672A48B0B64B52BB31C5642DC3 | SHA256:4BC28DB07851FC4282C47161DA018B40AA4D9F688886E8DC20E623452AEE9C9F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
24
DNS requests
14
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2552 | iexplore.exe | GET | 200 | 67.27.157.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?255d4ee536c94982 | unknown | compressed | 61.6 Kb | unknown |
2552 | iexplore.exe | GET | 200 | 67.27.157.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?7c4d3f1160e5ef0a | unknown | compressed | 61.6 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2552 | iexplore.exe | 5.28.62.61:443 | plus.cyberessentials.live | Iomart Hosting Limited | GB | unknown |
324 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2552 | iexplore.exe | 67.27.157.126:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
2216 | iexplore.exe | 5.28.62.61:443 | plus.cyberessentials.live | Iomart Hosting Limited | GB | unknown |
2216 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
2216 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2216 | iexplore.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
plus.cyberessentials.live |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.msn.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report