| File name: | XYplorer.exe |
| Full analysis: | https://app.any.run/tasks/194f8448-bf74-4eb2-8886-4d644a188353 |
| Verdict: | No threats detected |
| Analysis date: | September 27, 2018, 22:33:59 |
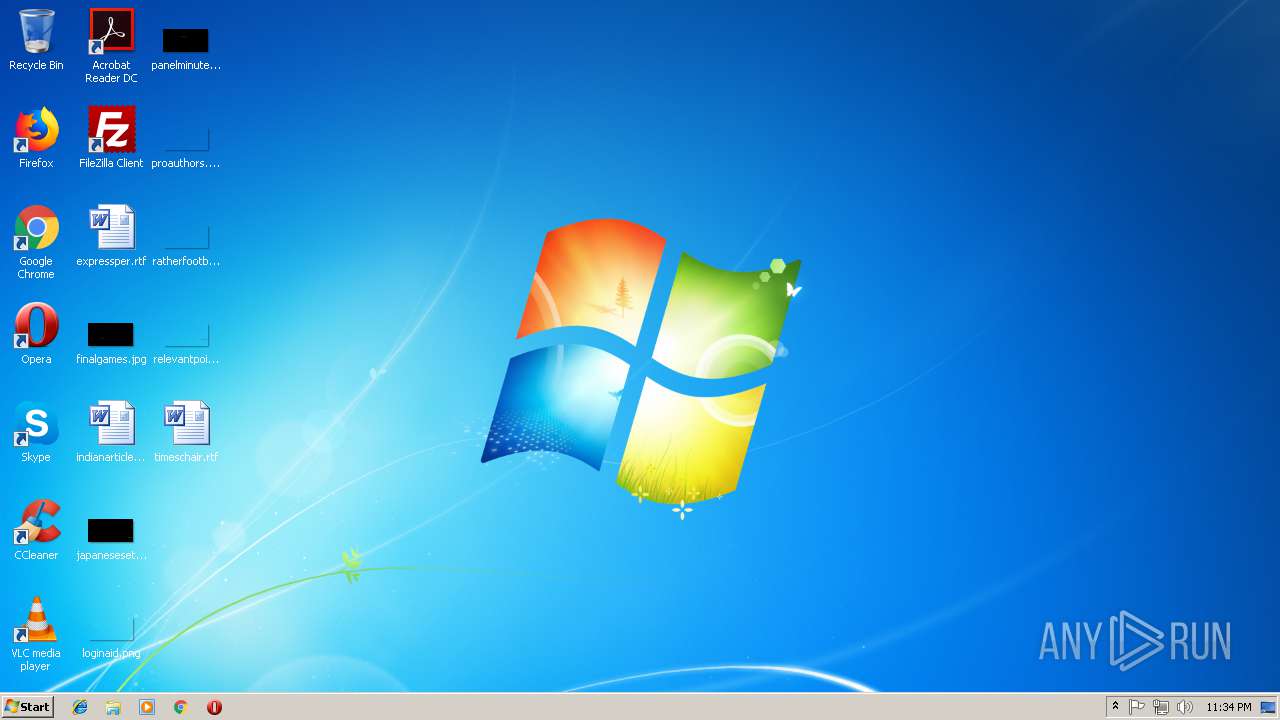
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 991B76100D74536DE54F211A05F75F50 |
| SHA1: | F259C577DCA524ADD05C1C0AF5D5D712BEFB8445 |
| SHA256: | FE0C71EC8B56C42876068474A8DB2980D5DF683EB236EFC0615F8769499C2197 |
| SSDEEP: | 393216:iJfQsRj29QyLX68PF/U/N1mmurNBcecCCiXQKYcNCeZlYnMINS0T/tSDXXINbJLN:iJpk1lPNU/N1mmurNBHX/YcNZunG0T/Z |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (59.5) |
|---|---|---|
| .ax | | | DirectShow filter (14.1) |
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (5.7) |
| .exe | | | InstallShield setup (3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:24 15:13:13+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 20480 |
| InitializedDataSize: | 69632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x287a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 19.20.0.0 |
| ProductVersionNumber: | 19.20.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | German |
| CharacterSet: | Unicode |
| Comments: | www.xyplorer.com |
| CompanyName: | Cologne Code Company |
| FileDescription: | XYplorer |
| LegalCopyright: | Copyright © 1997-2018 Cologne Code Company |
| LegalTrademarks: | XYplorer |
| ProductName: | XYplorer |
| FileVersion: | 19.2 |
| ProductVersion: | 19.2 |
| InternalName: | XYplorer |
| OriginalFileName: | XYplorer.exe |
| Packager: | Turbo Studio 18 |
| PackagerVersion: | 18.4.1080 |
| VmVersion: | 18.4.1281.3 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Sep-2018 13:13:13 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 24-Sep-2018 13:13:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00004574 | 0x00004600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.34361 |
.data | 0x00006000 | 0x00000460 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.xcpad | 0x00007000 | 0x00759000 | 0x00000000 | 0 | |
.idata | 0x00760000 | 0x0000036C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.26314 |
.reloc | 0x00761000 | 0x00000248 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.38687 |
.rsrc | 0x00762000 | 0x0000E4ED | 0x0000E600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.98143 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21611 | 1538 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 4.55292 | 3752 | Unicode (UTF 16LE) | English - United States | RT_ICON |
3 | 4.79821 | 2216 | Unicode (UTF 16LE) | English - United States | RT_ICON |
4 | 4.87455 | 1384 | Unicode (UTF 16LE) | English - United States | RT_ICON |
5 | 7.83037 | 6437 | Unicode (UTF 16LE) | English - United States | RT_ICON |
6 | 2.86748 | 16936 | Unicode (UTF 16LE) | English - United States | RT_ICON |
7 | 3.13652 | 9640 | Unicode (UTF 16LE) | English - United States | RT_ICON |
8 | 2.99942 | 4264 | Unicode (UTF 16LE) | English - United States | RT_ICON |
9 | 3.78764 | 1128 | Unicode (UTF 16LE) | English - United States | RT_ICON |
30001 | 4.79821 | 2216 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
Imports
KERNEL32.dll |
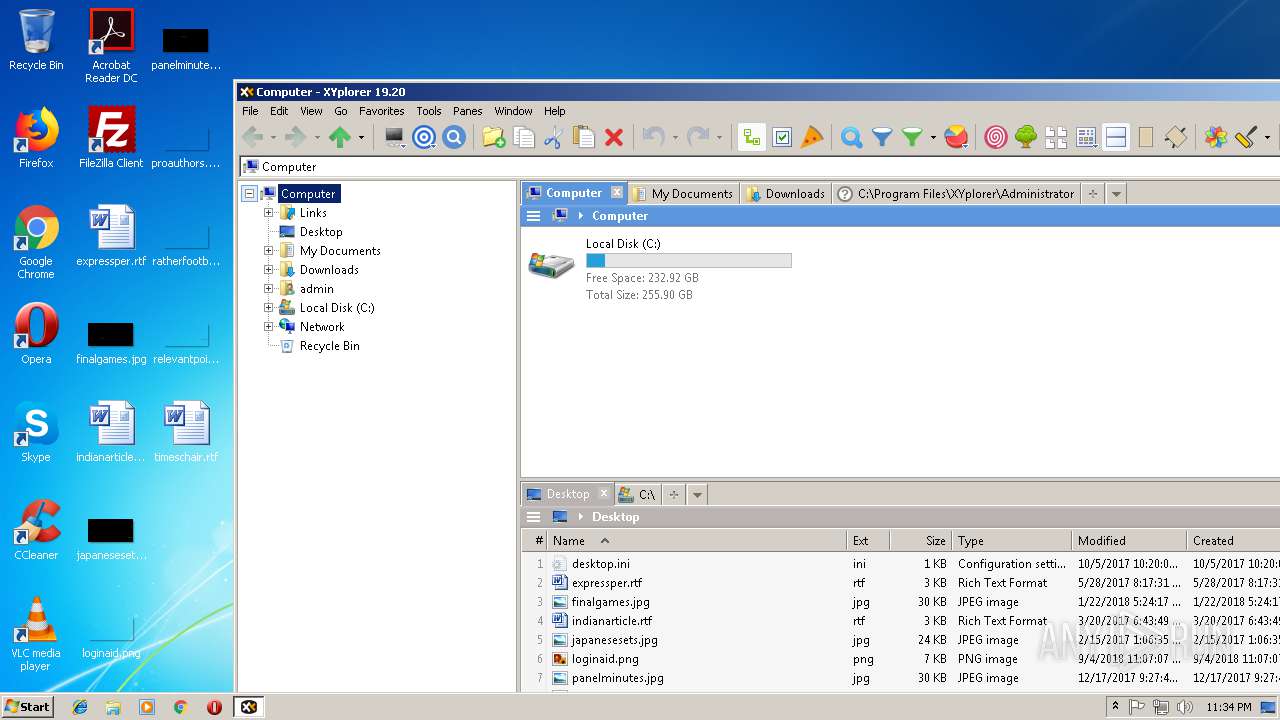
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
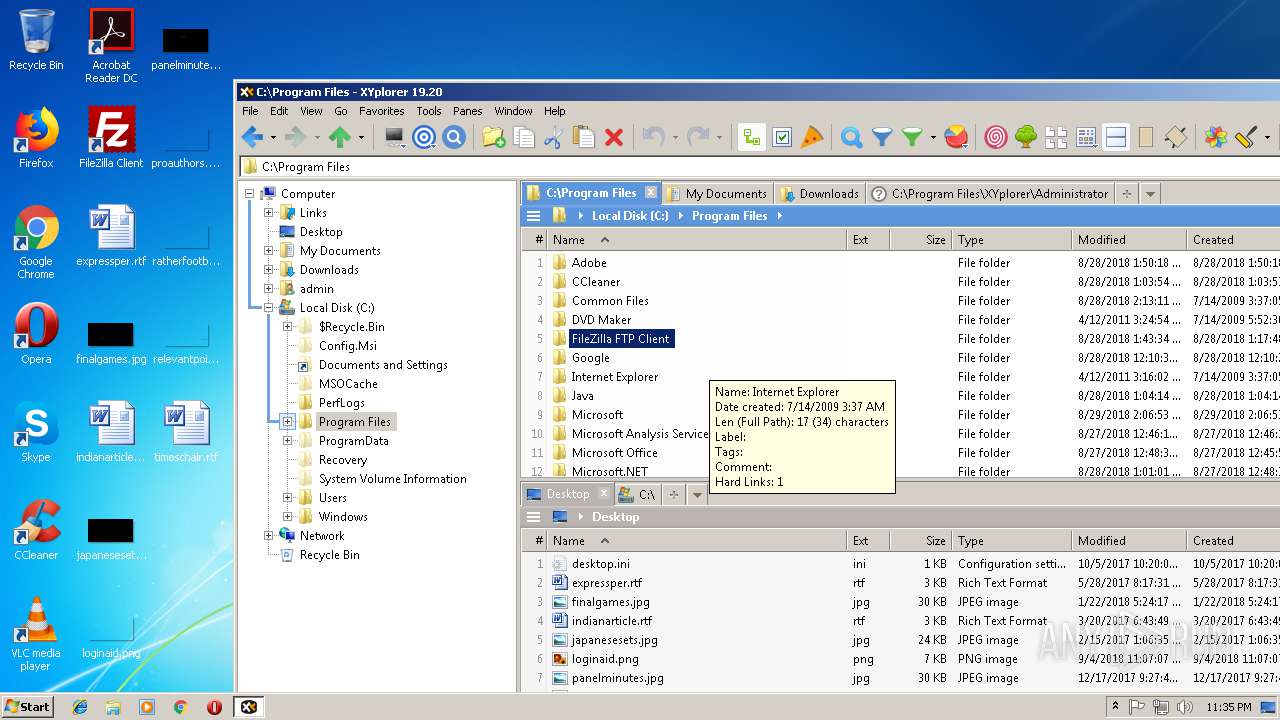
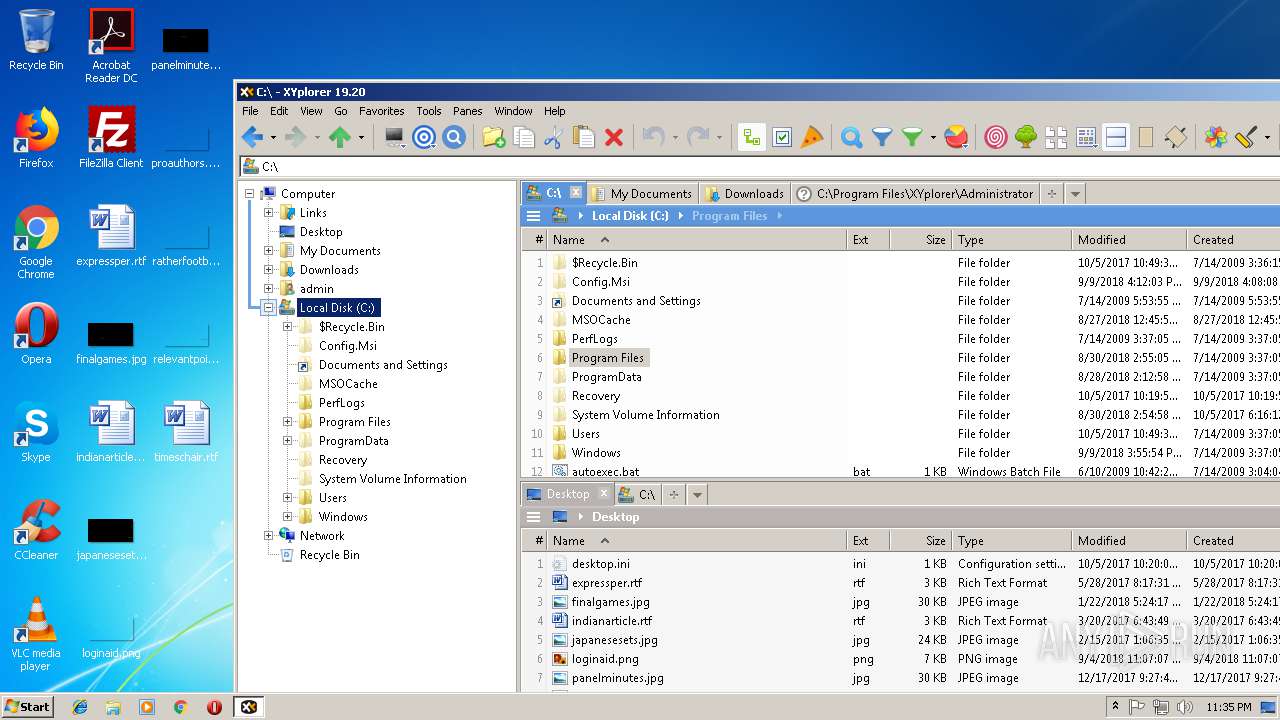
| 2424 | "C:\Users\admin\AppData\Local\Temp\XYplorer\local\stubexe\0x48B9B4DAFAC51033\XYplorer.exe" /864A627C-C6B2-464A-AA13-25D62F282BD8 | C:\Program Files\XYplorer\XYplorer.exe | — | XYplorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3120 | "C:\Users\admin\AppData\Local\Temp\XYplorer.exe" | C:\Users\admin\AppData\Local\Temp\XYplorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Cologne Code Company Integrity Level: MEDIUM Description: XYplorer Exit code: 0 Version: 19.20 Modules
| |||||||||||||||
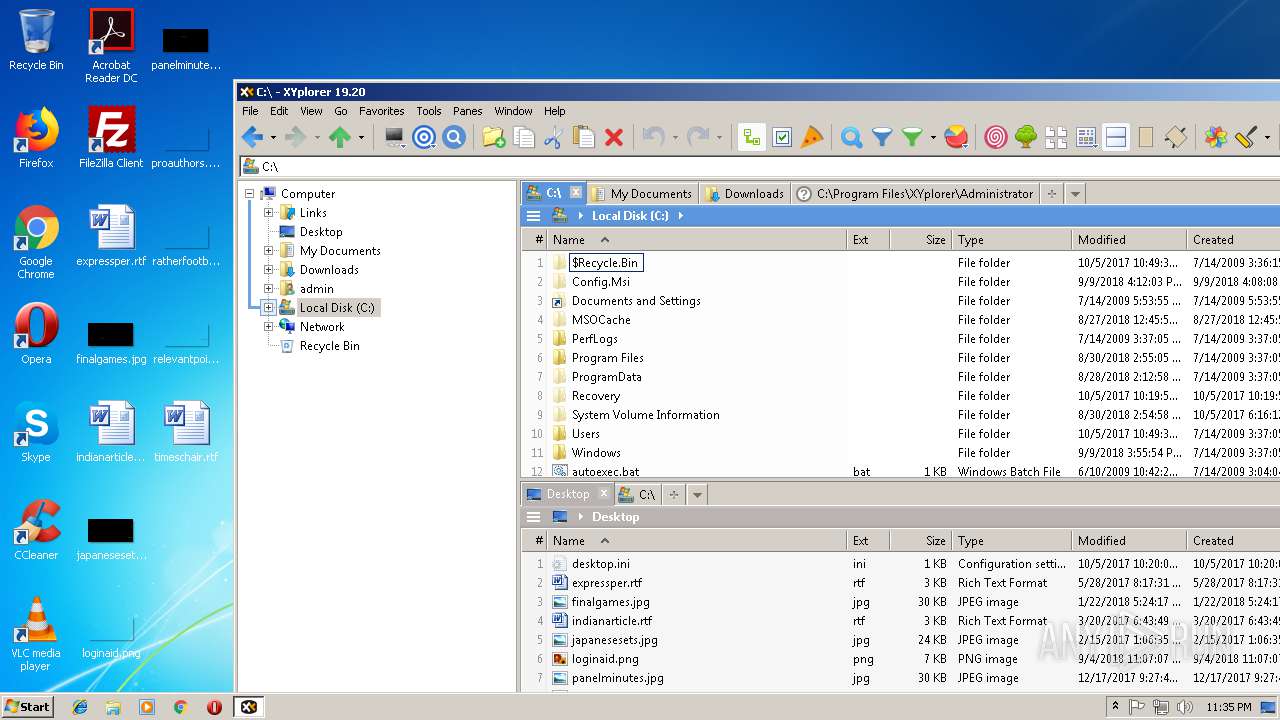
Total events
383
Read events
380
Write events
3
Delete events
0
Modification events
| (PID) Process: | (2424) XYplorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2424) XYplorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\acppage.dll,-6002 |
Value: Windows Batch File | |||
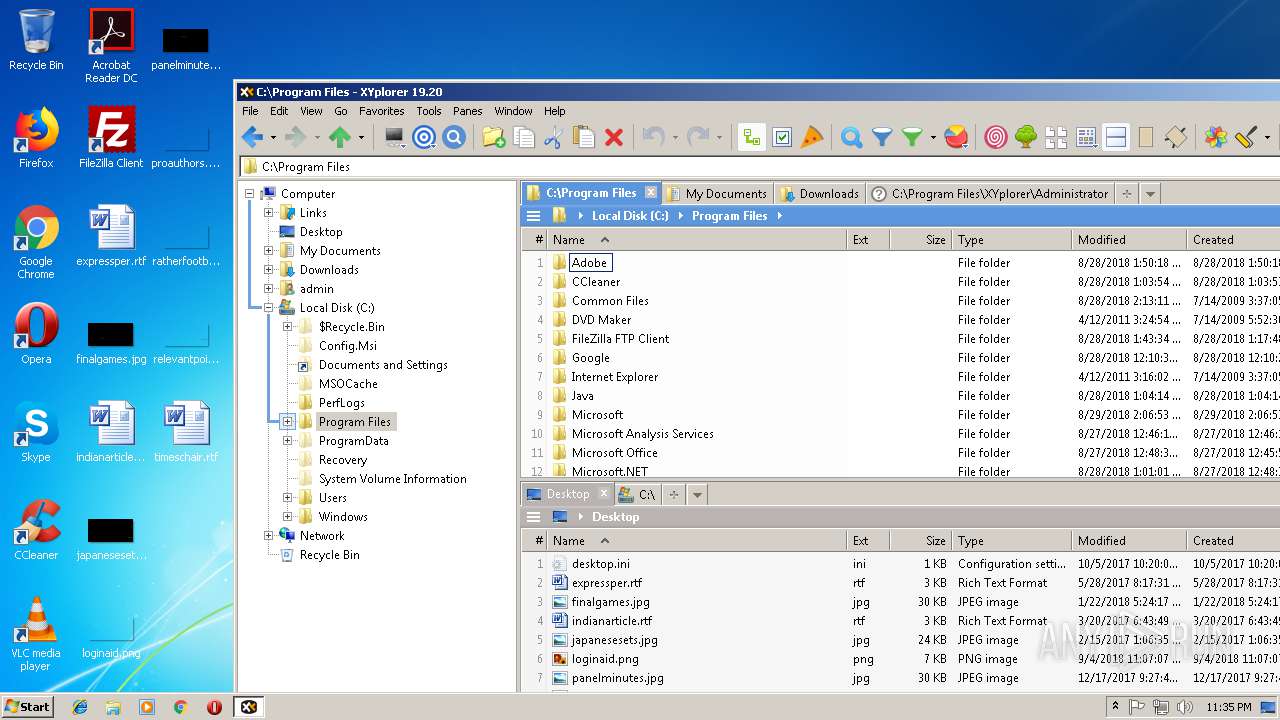
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3120 | XYplorer.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\Temp\XYplorer\xsandbox.bin | — | |
MD5:— | SHA256:— | |||
| 3120 | XYplorer.exe | C:\Users\admin\AppData\Local\Temp\XYplorer\xsandbox.bin.__tmp__ | — | |
MD5:— | SHA256:— | |||
| 3120 | XYplorer.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\Temp\SPOON\CACHE\0xDD51C1B7AFD61565\sxs\_AutoHotkey@1.1.00.00\_AutoHotkey@1.1.00.00.manifest | — | |
MD5:— | SHA256:— | |||
| 3120 | XYplorer.exe | C:\Users\admin\AppData\Local\Temp\SPOON\CACHE\0xDD51C1B7AFD61565\sxs\_AutoHotkey@1.1.00.00\_AutoHotkey@1.1.00.00.manifest.__tmp__ | — | |
MD5:— | SHA256:— | |||
| 3120 | XYplorer.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\Temp\SPOON\CACHE\0xDD51C1B7AFD61565\sxs\_AutoHotkey@1.1.00.00\AutoHotkey.manifest | — | |
MD5:— | SHA256:— | |||
| 3120 | XYplorer.exe | C:\Users\admin\AppData\Local\Temp\SPOON\CACHE\0xDD51C1B7AFD61565\sxs\_AutoHotkey@1.1.00.00\AutoHotkey.manifest.__tmp__ | — | |
MD5:— | SHA256:— | |||
| 3120 | XYplorer.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\Temp\SPOON\CACHE\0xDD51C1B7AFD61565\sxs\_Nullsoft.NSIS.exehead@1.0.0.0\_Nullsoft.NSIS.exehead@1.0.0.0.manifest | — | |
MD5:— | SHA256:— | |||
| 3120 | XYplorer.exe | C:\Users\admin\AppData\Local\Temp\SPOON\CACHE\0xDD51C1B7AFD61565\sxs\_Nullsoft.NSIS.exehead@1.0.0.0\_Nullsoft.NSIS.exehead@1.0.0.0.manifest.__tmp__ | — | |
MD5:— | SHA256:— | |||
| 3120 | XYplorer.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\Temp\SPOON\CACHE\0xDD51C1B7AFD61565\sxs\_Nullsoft.NSIS.exehead@1.0.0.0\Nullsoft.NSIS.exehead.manifest | — | |
MD5:— | SHA256:— | |||
| 3120 | XYplorer.exe | C:\Users\admin\AppData\Local\Temp\SPOON\CACHE\0xDD51C1B7AFD61565\sxs\_Nullsoft.NSIS.exehead@1.0.0.0\Nullsoft.NSIS.exehead.manifest.__tmp__ | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report