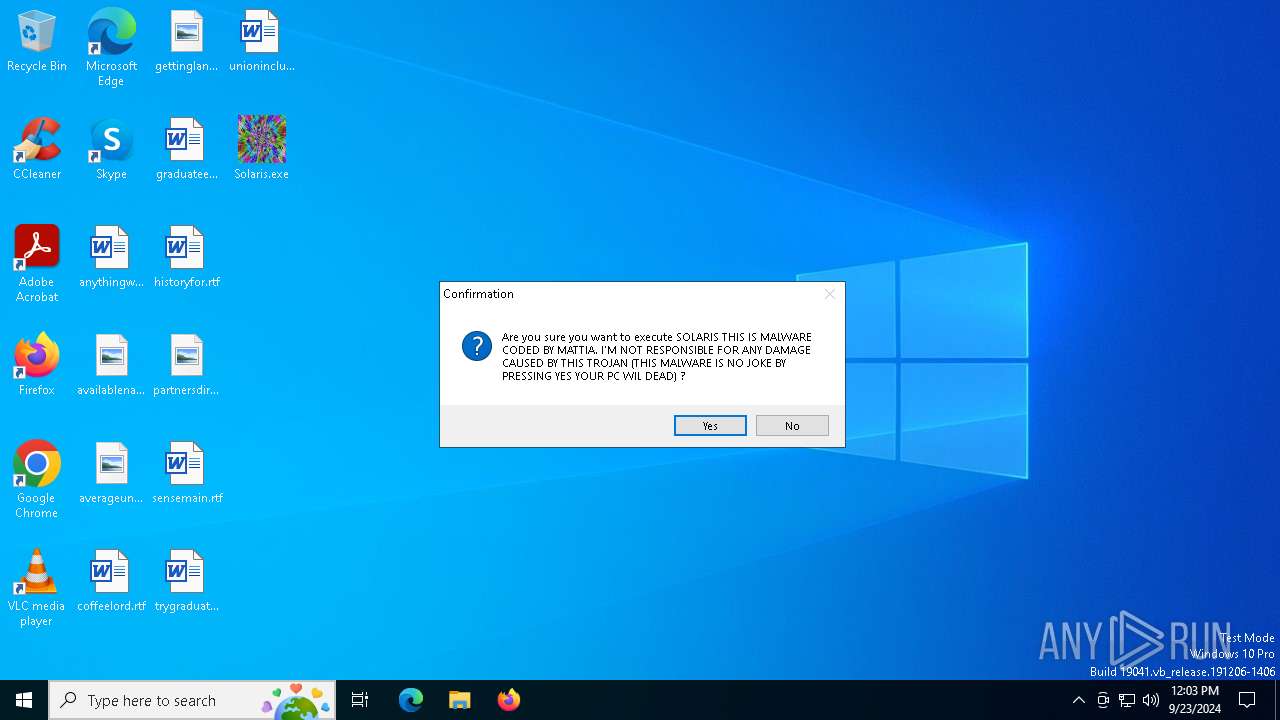
| File name: | Solaris.exe |
| Full analysis: | https://app.any.run/tasks/d53a4264-28ac-423f-b04c-fa05e65e72c6 |
| Verdict: | Malicious activity |
| Analysis date: | September 23, 2024, 12:02:59 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | 14FC8CFEDCB09DF821C93BB735F91065 |
| SHA1: | CEC32143E7D69D3870F092D72B8EF561D2FD4B7B |
| SHA256: | FE0AEFC67036A3A060F636658C16159CA4B13E5C33FA6F2BD3984E73CF9006C0 |
| SSDEEP: | 98304:Alejqw5s7IoEQvI7bnrkt+TllEa1IuBAgKIcTpfQob+tyn99uu4I+aO9z6c+6tX0:RwXPu7JWQyreqdcq0YlBa8a/JSC/gT |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- Solaris.exe (PID: 752)
Application launched itself
- Solaris.exe (PID: 752)
The process drops C-runtime libraries
- Solaris.exe (PID: 752)
Executable content was dropped or overwritten
- Solaris.exe (PID: 752)
Process drops python dynamic module
- Solaris.exe (PID: 752)
INFO
Checks supported languages
- Solaris.exe (PID: 752)
PyInstaller has been detected (YARA)
- Solaris.exe (PID: 3880)
- Solaris.exe (PID: 752)
Create files in a temporary directory
- Solaris.exe (PID: 752)
Reads the computer name
- Solaris.exe (PID: 752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:04:15 15:47:28+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.38 |
| CodeSize: | 175616 |
| InitializedDataSize: | 271360 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc330 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
Total processes
121
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 752 | "C:\Users\admin\Desktop\Solaris.exe" | C:\Users\admin\Desktop\Solaris.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 3880 | "C:\Users\admin\Desktop\Solaris.exe" | C:\Users\admin\Desktop\Solaris.exe | Solaris.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
290
Read events
290
Write events
0
Delete events
0
Modification events
Executable files
41
Suspicious files
3
Text files
921
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 752 | Solaris.exe | C:\Users\admin\AppData\Local\Temp\_MEI7522\Pythonwin\win32ui.pyd | executable | |
MD5:D335339C3508604925016C1F3EE0600D | SHA256:8B992A0333990A255C6DF4395AE2E4153300596D75C7FBD17780214FB359B6A7 | |||
| 752 | Solaris.exe | C:\Users\admin\AppData\Local\Temp\_MEI7522\PIL\_imagingmath.cp312-win_amd64.pyd | executable | |
MD5:3FF6DD84E279E61656DB569E9A7689FA | SHA256:7F3530E6CE99582CB275BE15BBC7BE5E0BC3C1AEEABF1B6C3AF09F9668F65284 | |||
| 752 | Solaris.exe | C:\Users\admin\AppData\Local\Temp\_MEI7522\PIL\_imaging.cp312-win_amd64.pyd | executable | |
MD5:FF0F2E5A156A73C3759FE19AF09A18EF | SHA256:B9E41E7137CFC7B873E96ADA1C473BABFD616D0AD7878221BB68C43B70190067 | |||
| 752 | Solaris.exe | C:\Users\admin\AppData\Local\Temp\_MEI7522\PIL\_imagingcms.cp312-win_amd64.pyd | executable | |
MD5:6A141B845C2B4144ED0DBC7F53FF6803 | SHA256:A0BB33298DCC52DA966F7A934C4838E32E20438EB8DB929D4AD12FD042FD0922 | |||
| 752 | Solaris.exe | C:\Users\admin\AppData\Local\Temp\_MEI7522\_decimal.pyd | executable | |
MD5:F930B7550574446A015BC602D59B0948 | SHA256:3B9AD1D2BC9EC03D37DA86135853DAC73B3FE851B164FE52265564A81EB8C544 | |||
| 752 | Solaris.exe | C:\Users\admin\AppData\Local\Temp\_MEI7522\Pythonwin\mfc140u.dll | executable | |
MD5:03A161718F1D5E41897236D48C91AE3C | SHA256:E06C4BD078F4690AA8874A3DEB38E802B2A16CCB602A7EDC2E077E98C05B5807 | |||
| 752 | Solaris.exe | C:\Users\admin\AppData\Local\Temp\_MEI7522\PIL\_webp.cp312-win_amd64.pyd | executable | |
MD5:89FB0BCC6336A7F70371F6780676C78D | SHA256:D35B0433B128E9DBF900CAC0F8F73E78735DE717B46C8CA3BD15A94DA135620D | |||
| 752 | Solaris.exe | C:\Users\admin\AppData\Local\Temp\_MEI7522\_bz2.pyd | executable | |
MD5:59D60A559C23202BEB622021AF29E8A9 | SHA256:706D4A0C26DD454538926CBB2FF6C64257C3D9BD48C956F7CABD6DEF36FFD13E | |||
| 752 | Solaris.exe | C:\Users\admin\AppData\Local\Temp\_MEI7522\VCRUNTIME140.dll | executable | |
MD5:BE8DBE2DC77EBE7F88F910C61AEC691A | SHA256:4D292623516F65C80482081E62D5DADB759DC16E851DE5DB24C3CBB57B87DB83 | |||
| 752 | Solaris.exe | C:\Users\admin\AppData\Local\Temp\_MEI7522\PIL\_imagingtk.cp312-win_amd64.pyd | executable | |
MD5:32C5EE4D2A957D99319ADA53862EB0B1 | SHA256:1AFA30DEE9788E83C0D45678C921E1AB9F45BA7DFF3E84533D18E62928FAF756 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
15
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6176 | RUXIMICS.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
6604 | svchost.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
6176 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6604 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 104.208.16.92:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6176 | RUXIMICS.exe | 23.218.209.163:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6604 | svchost.exe | 23.218.209.163:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |