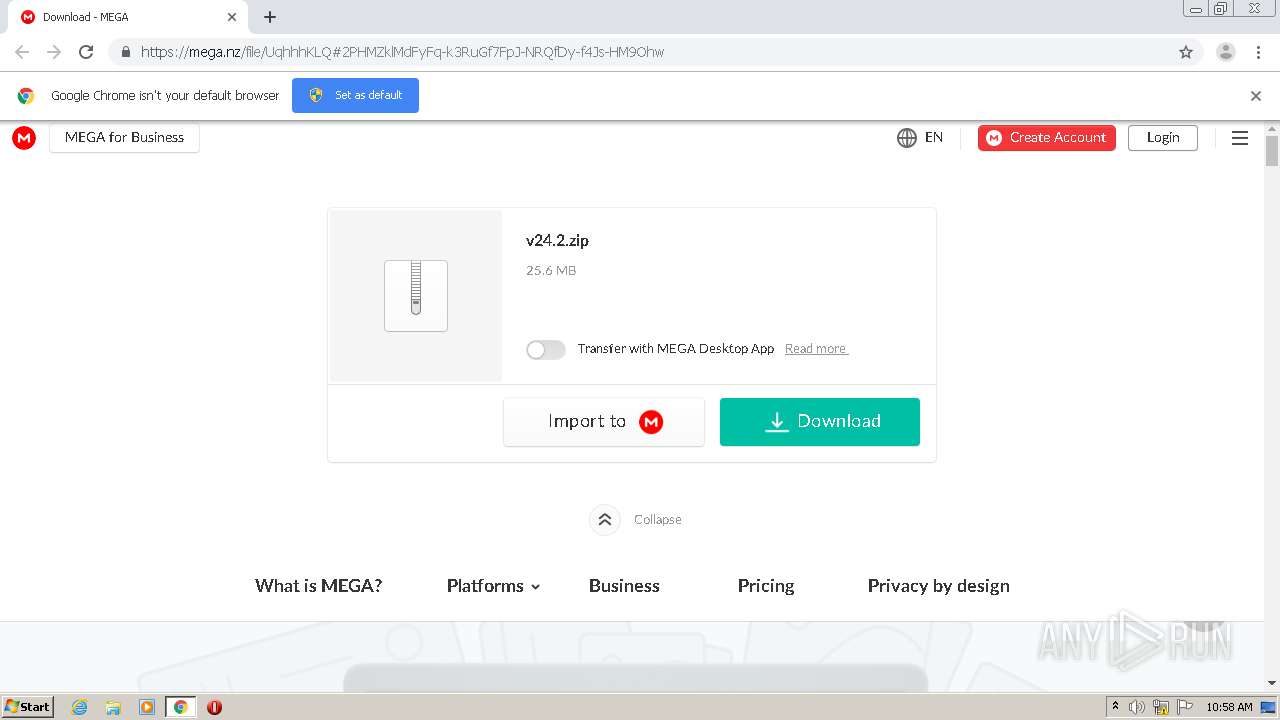
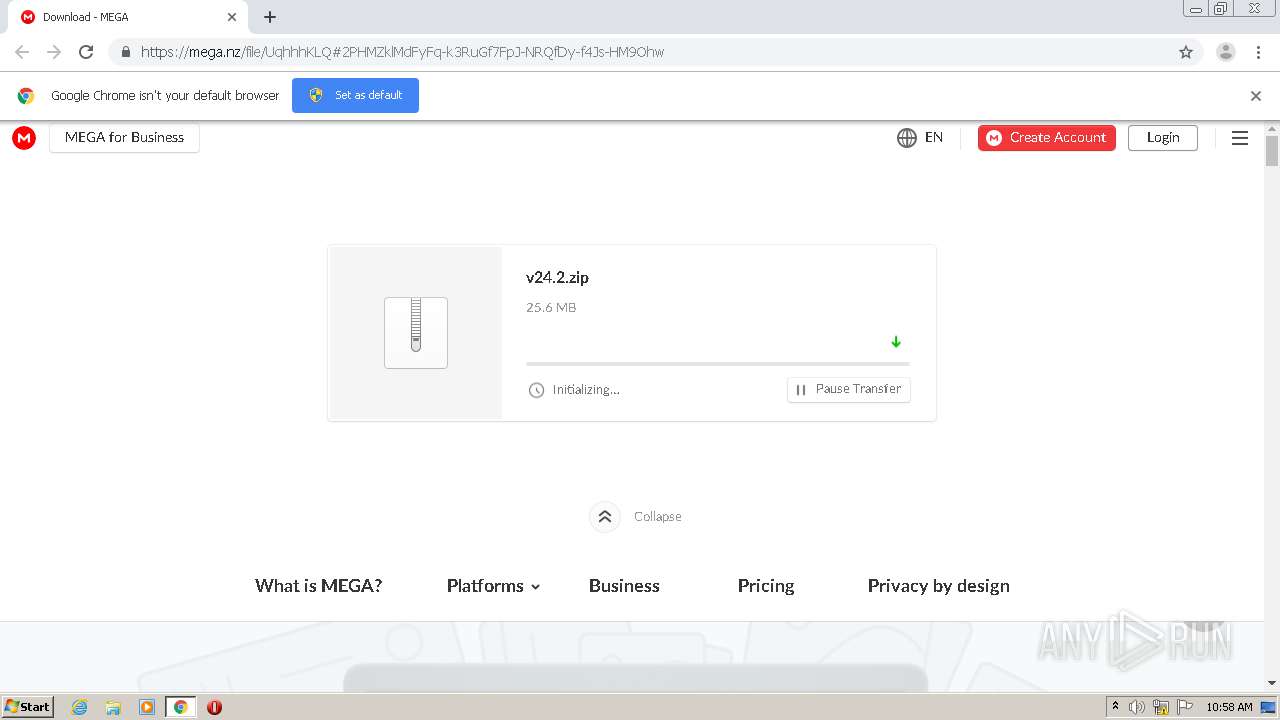
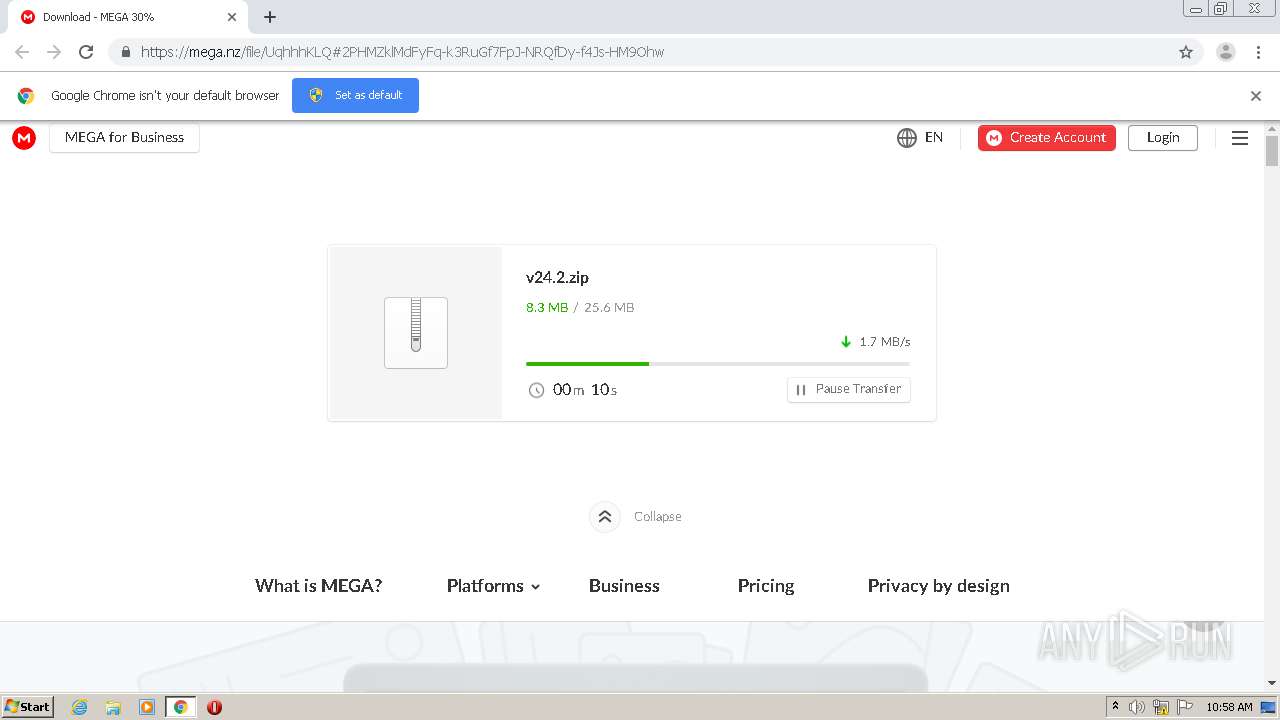
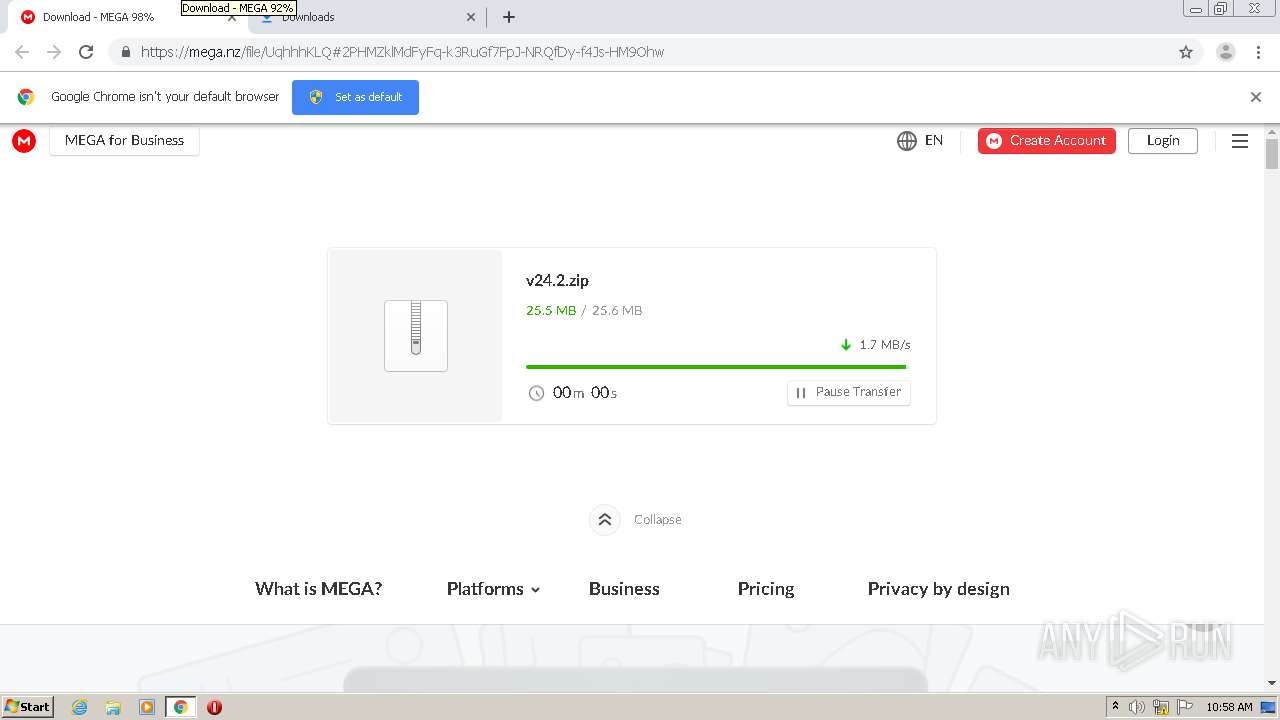
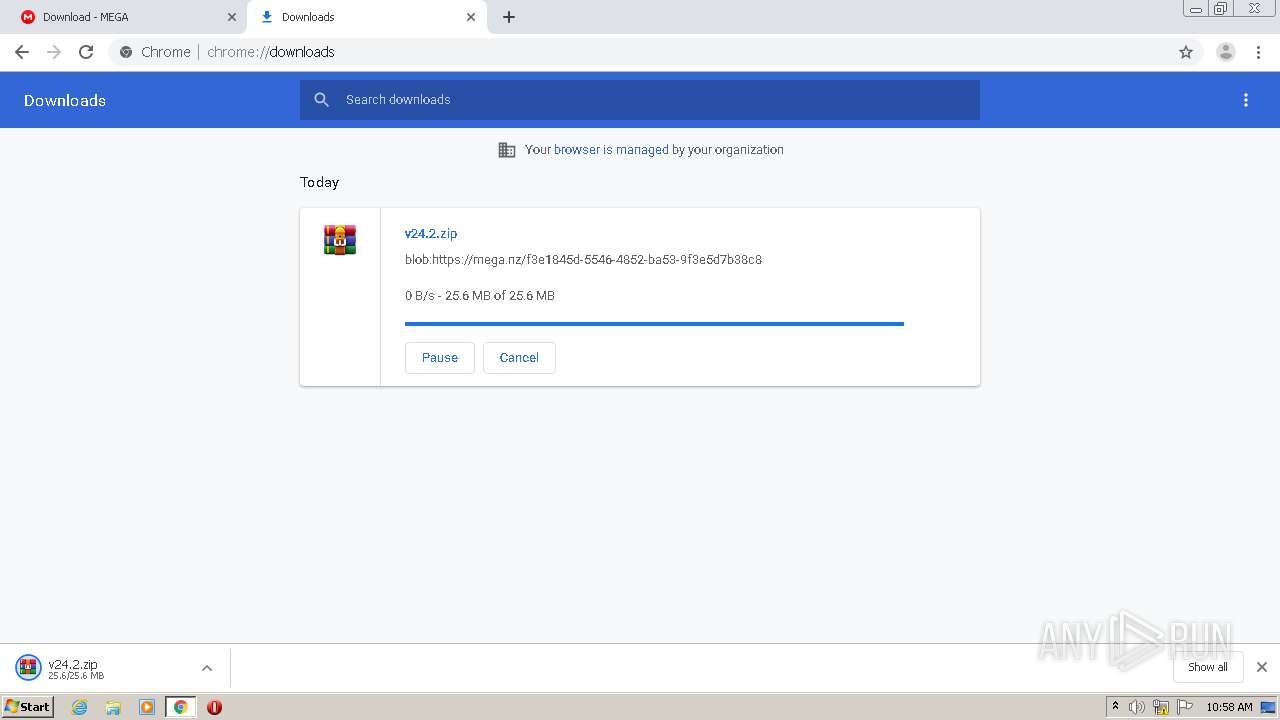
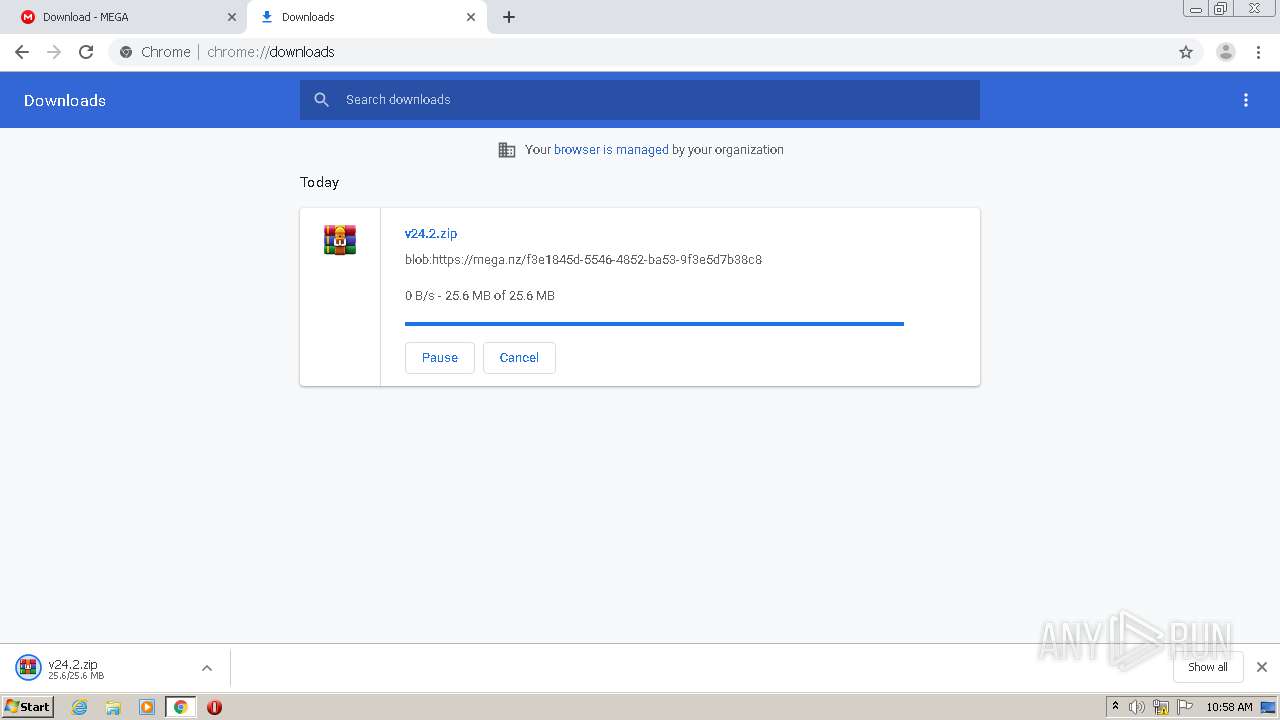
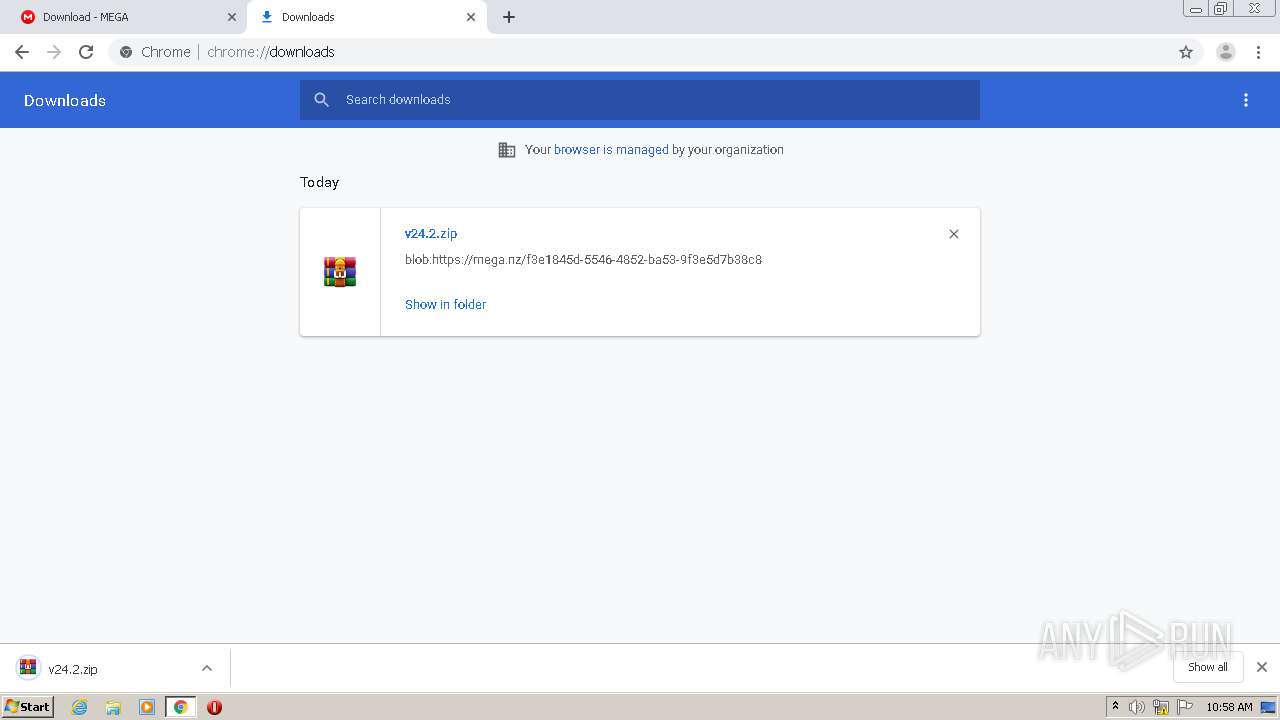
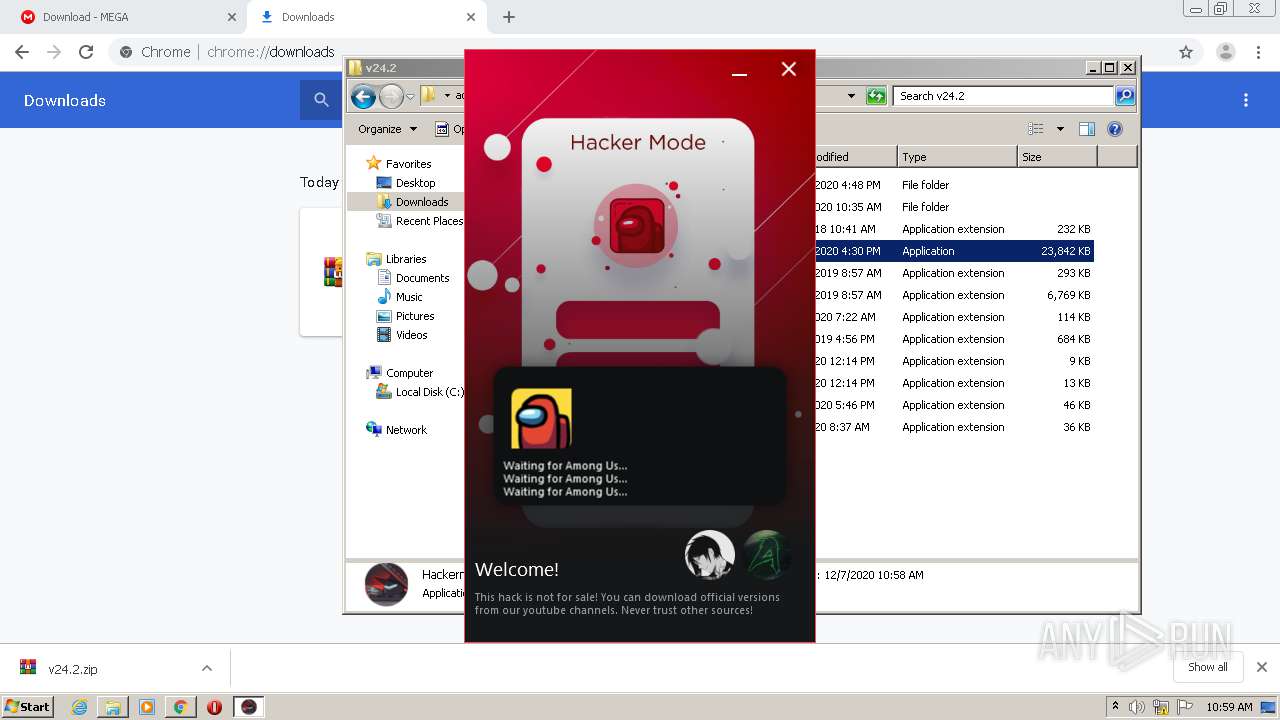
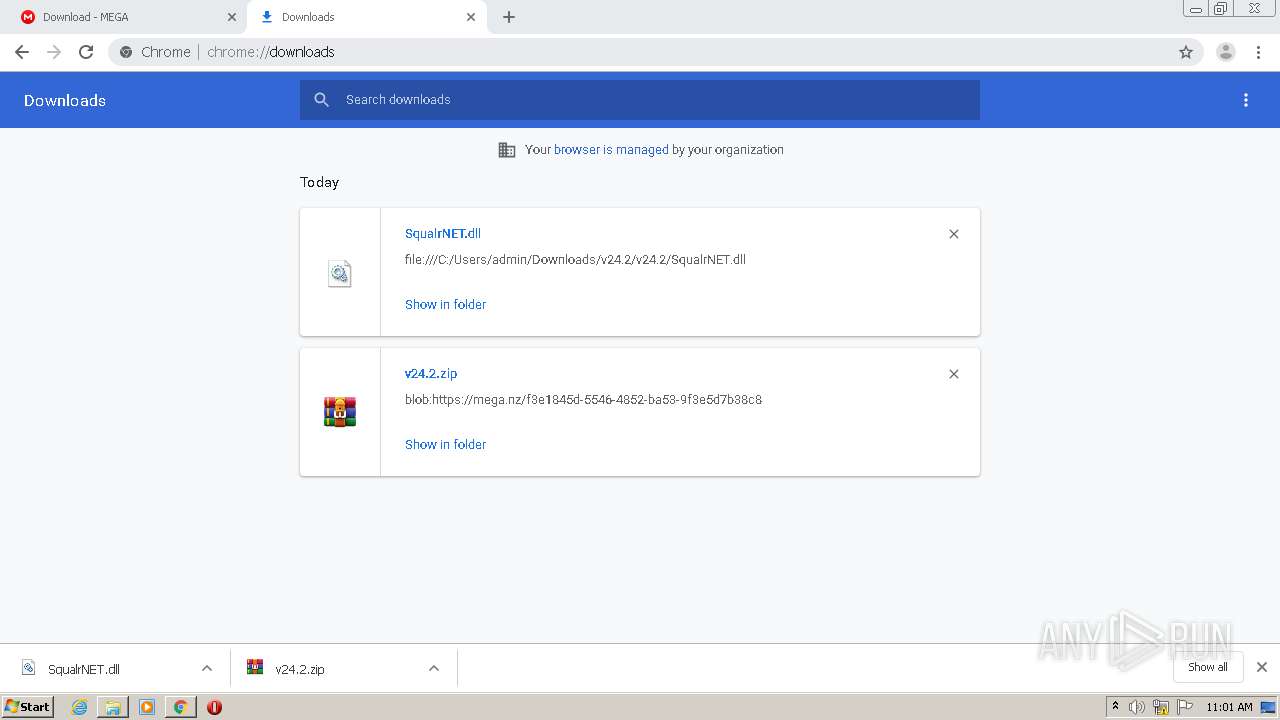
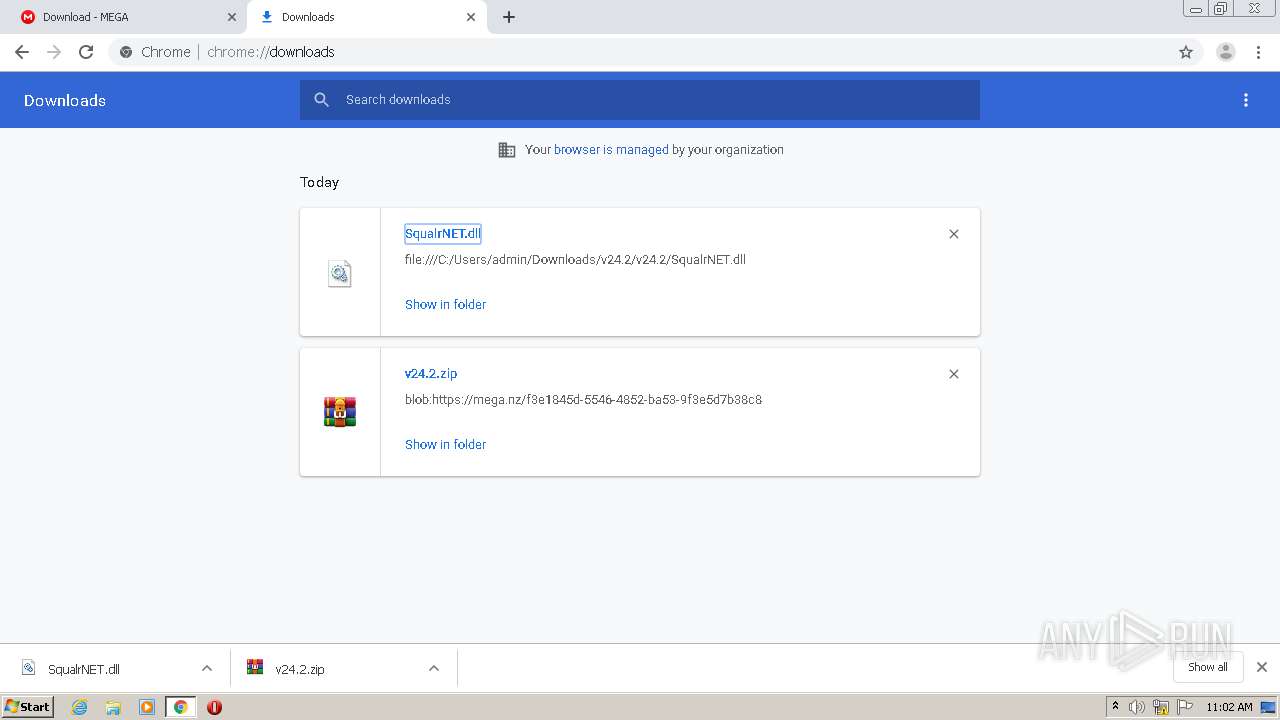
| URL: | https://mega.nz/file/UqhhhKLQ#2PHMZklMdFyFq-k3RuGf7FpJ-NRQfDy-f4Js-HM9Ohw |
| Full analysis: | https://app.any.run/tasks/66631360-8e42-4186-b4d9-a9870b10ee49 |
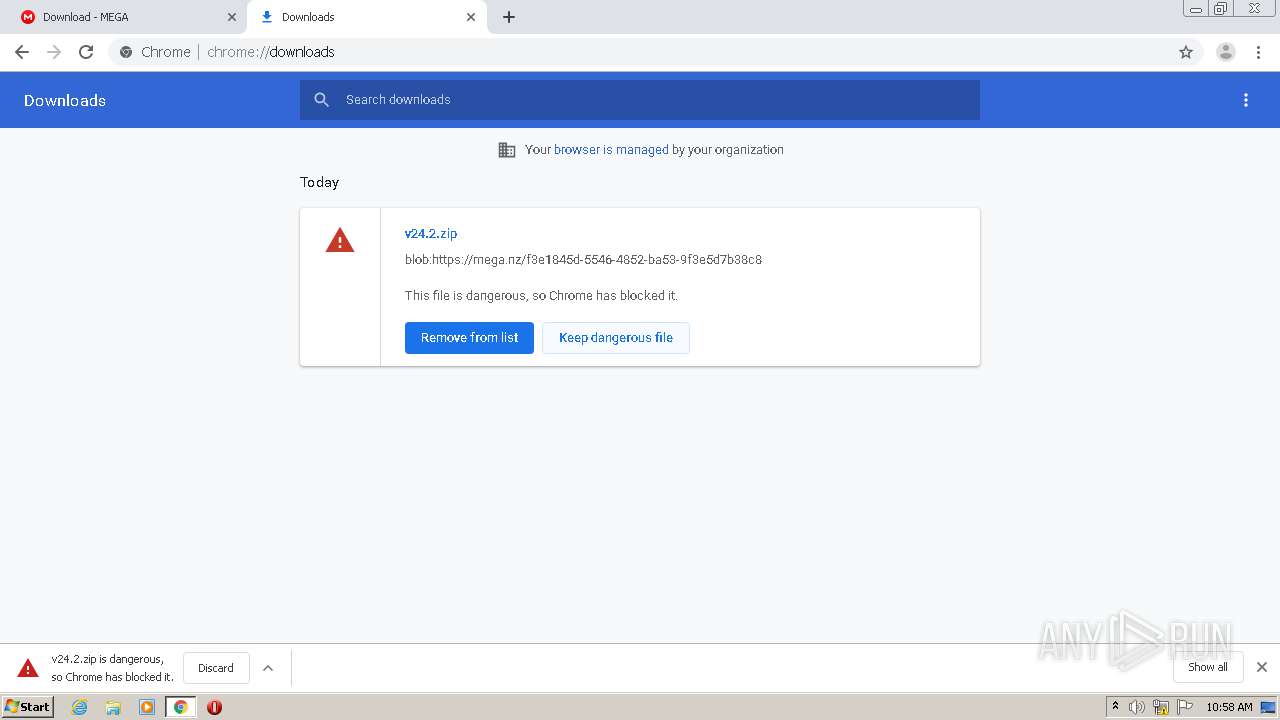
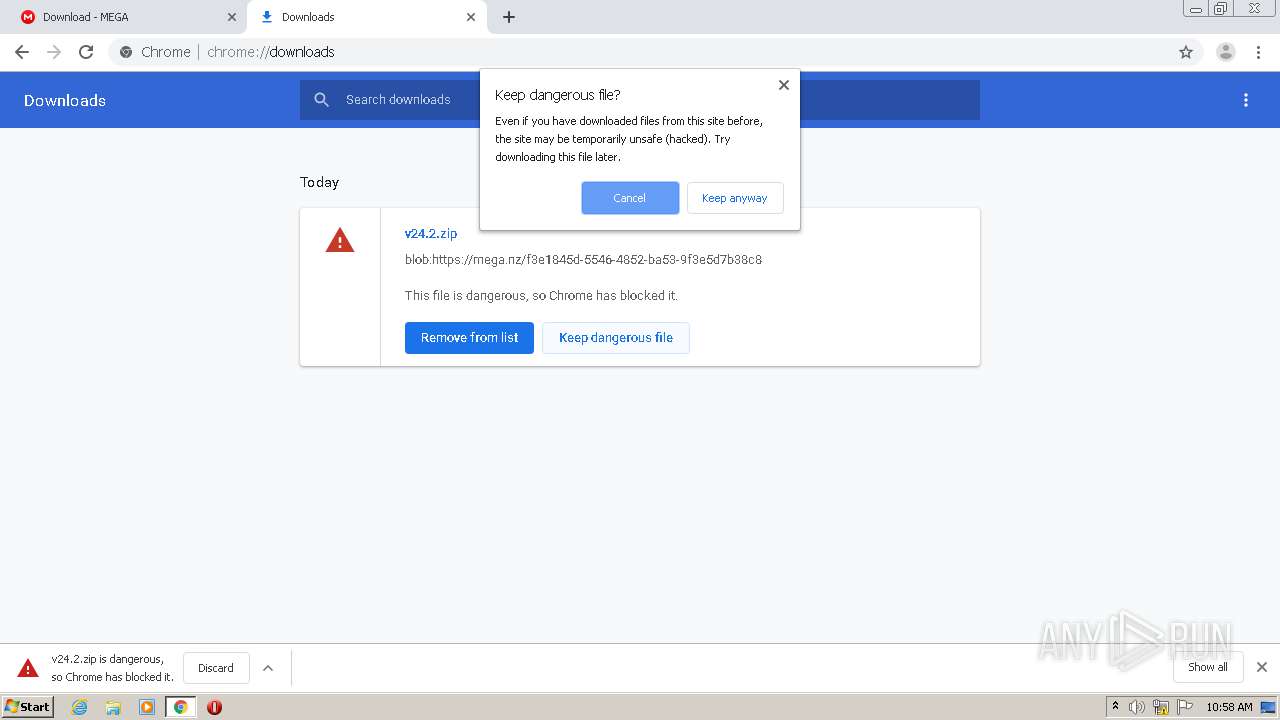
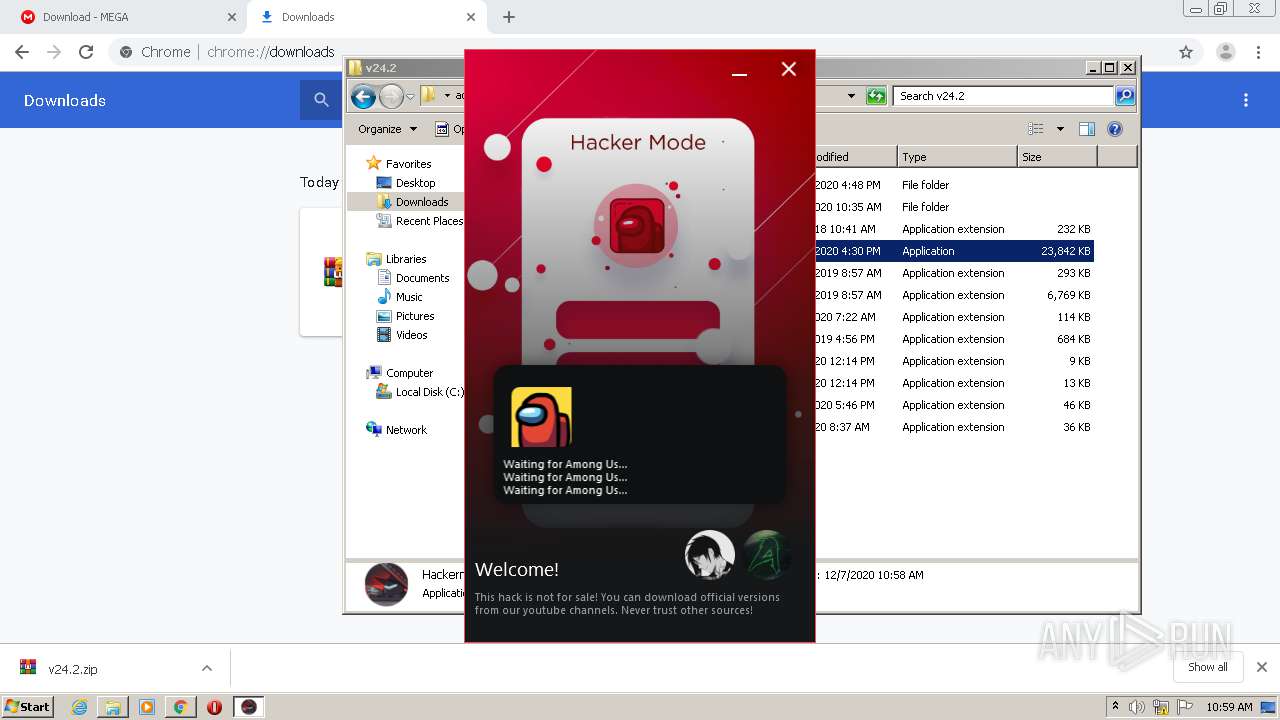
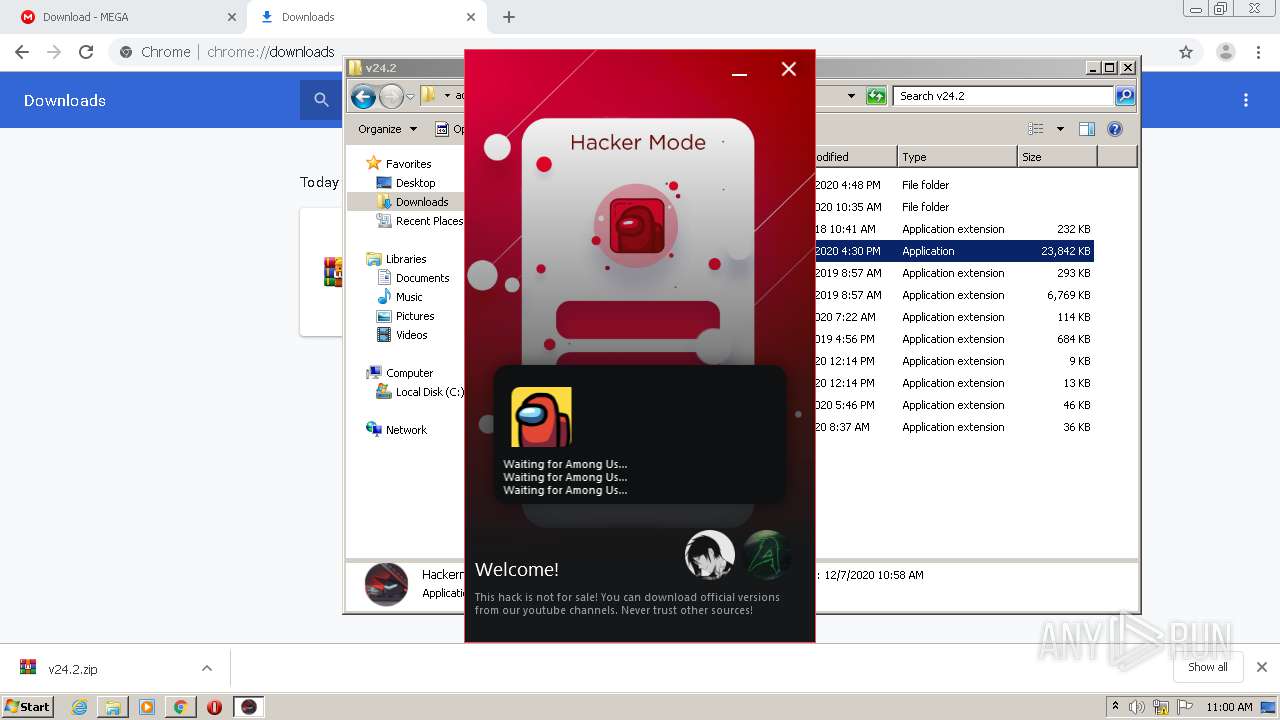
| Verdict: | Malicious activity |
| Analysis date: | December 07, 2020, 10:57:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6D385A6752EF0B4282066E5F48B9CA1E |
| SHA1: | 6299F1A4BF21F59726BA74F40EFD9A3DE855014E |
| SHA256: | FE003803525DD5D094C9150AB75724732D6C284E53A9FC52CC477DA0EFD18928 |
| SSDEEP: | 3:N8X/i+fcoGm2kwQiMVQaOS:2Itm245Qal |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3540)
- Hackermode v24.exe (PID: 2204)
- explorer.exe (PID: 372)
- SearchProtocolHost.exe (PID: 2120)
- Hackermode v24.exe (PID: 1440)
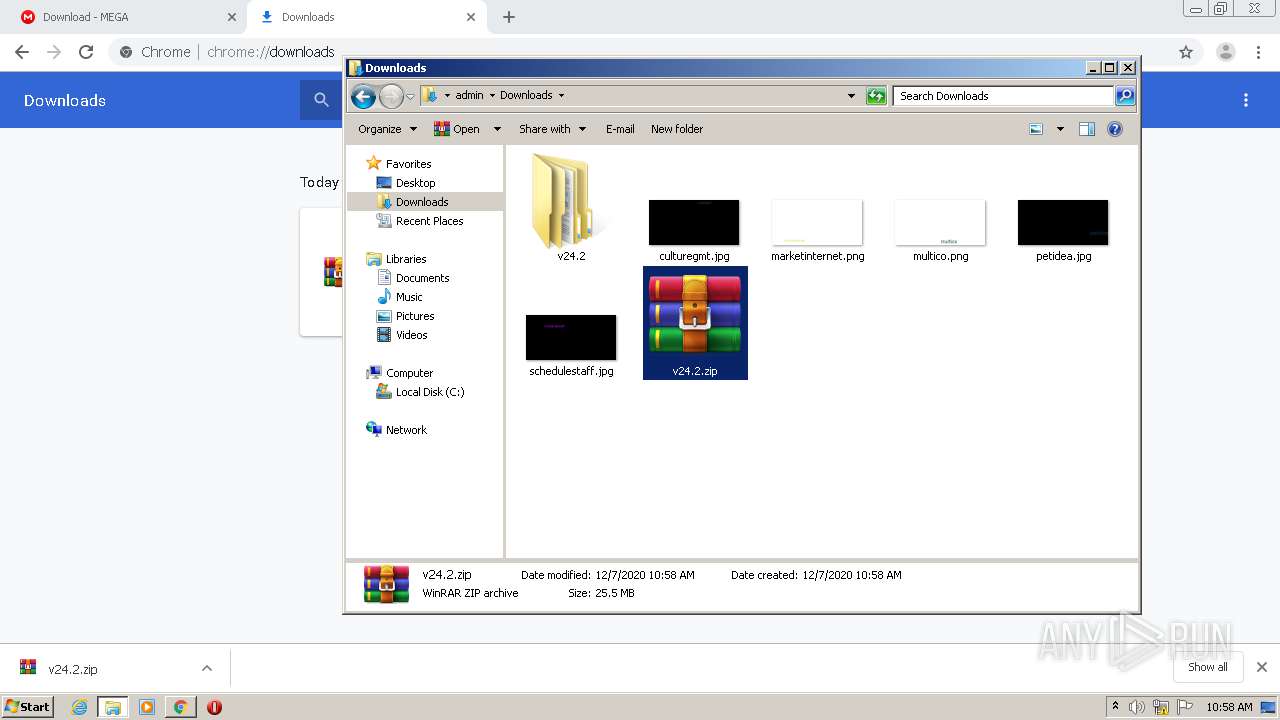
Application was dropped or rewritten from another process
- Hackermode v24.exe (PID: 2204)
- Hackermode v24.exe (PID: 1440)
SUSPICIOUS
Creates files in the user directory
- explorer.exe (PID: 372)
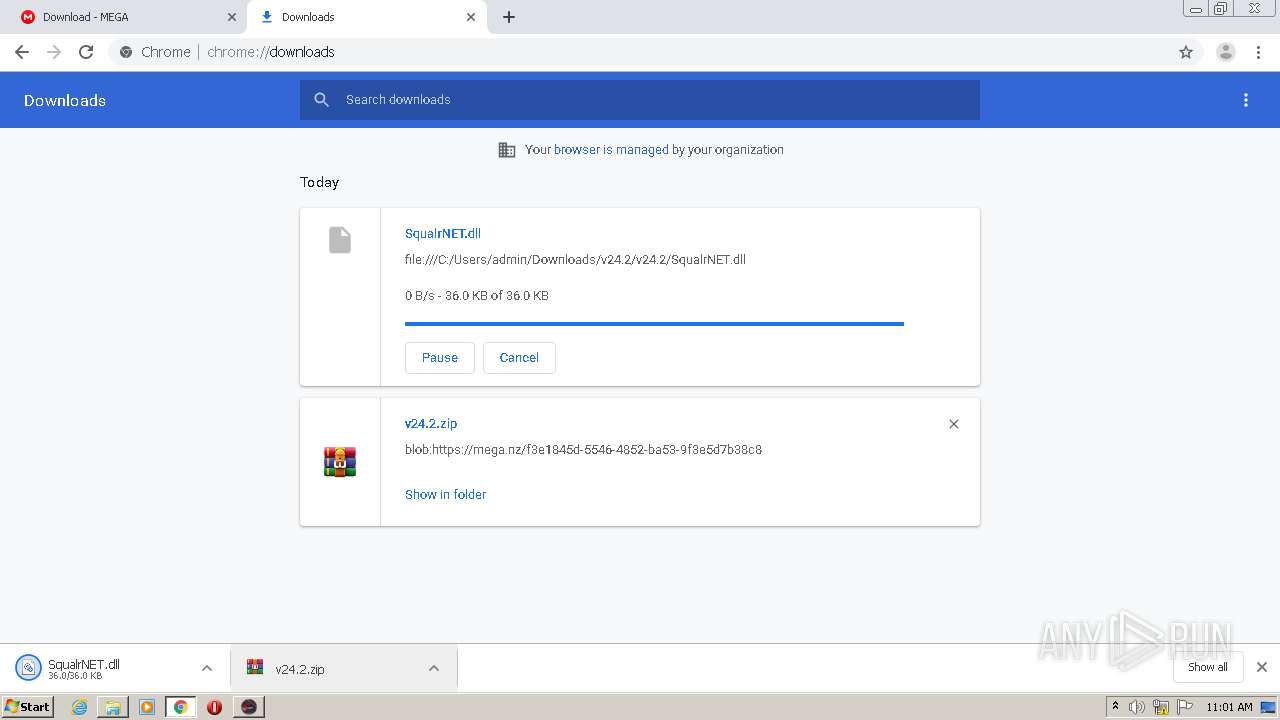
Drops a file with a compile date too recent
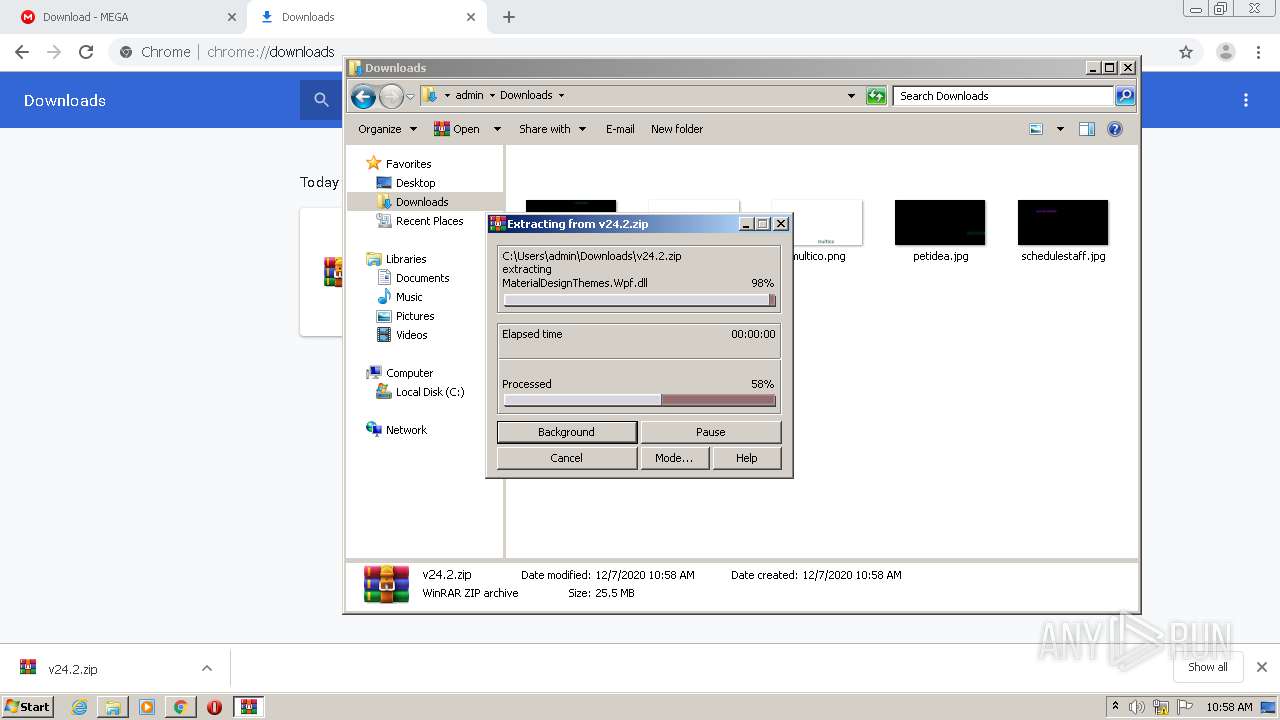
- WinRAR.exe (PID: 780)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 780)
- chrome.exe (PID: 2408)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 780)
- chrome.exe (PID: 2408)
Executed via COM
- MsSpellCheckingFacility.exe (PID: 3808)
Reads Environment values
- Hackermode v24.exe (PID: 2204)
Drops a file with too old compile date
- WinRAR.exe (PID: 780)
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 372)
INFO
Reads the hosts file
- chrome.exe (PID: 2408)
- chrome.exe (PID: 1036)
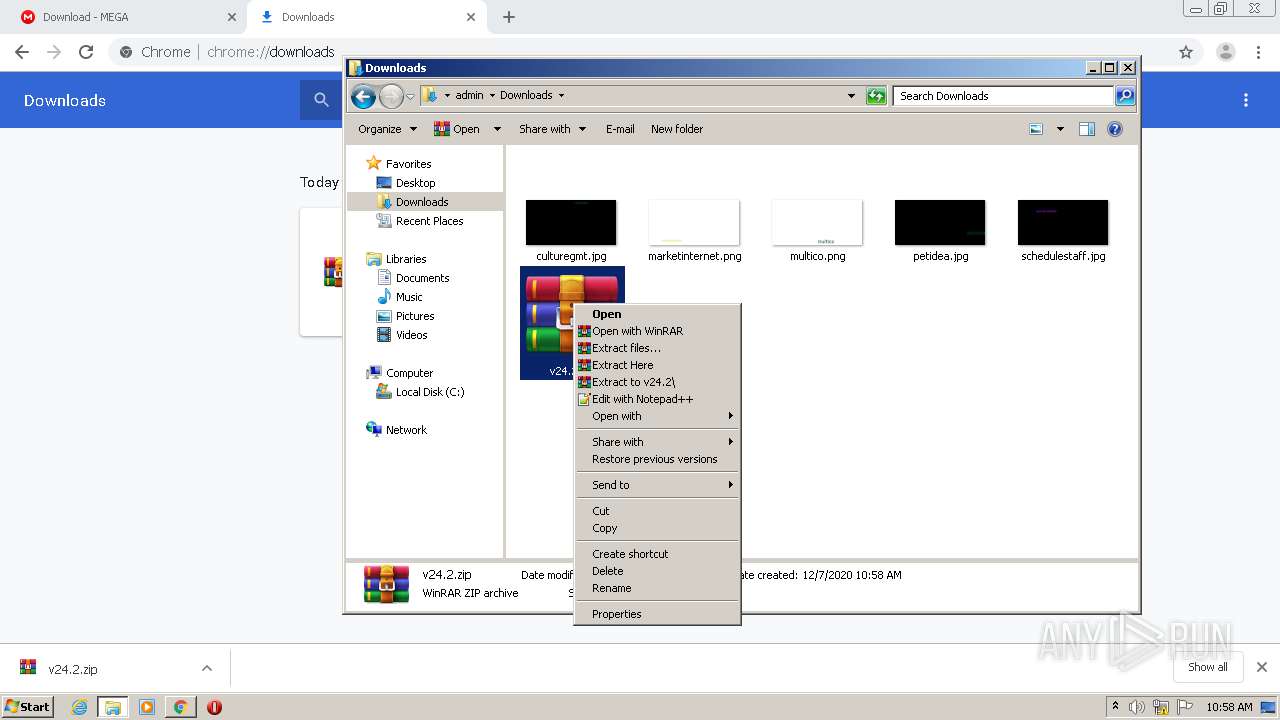
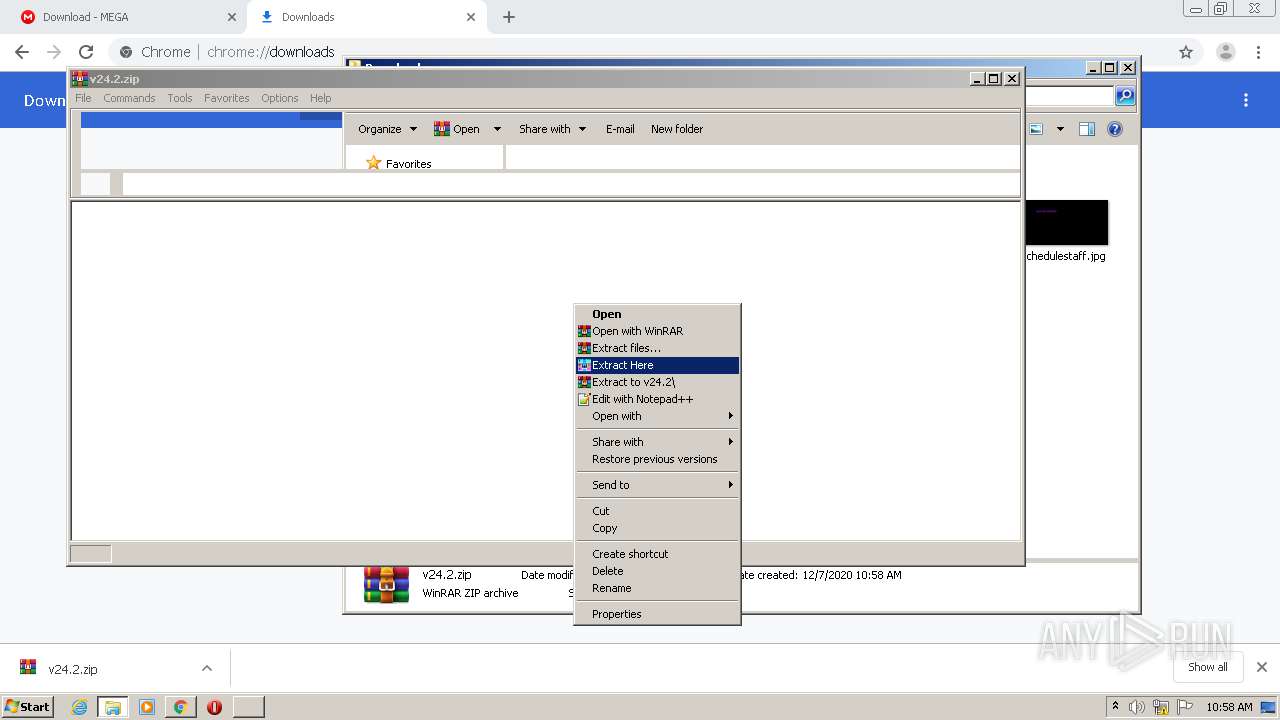
Manual execution by user
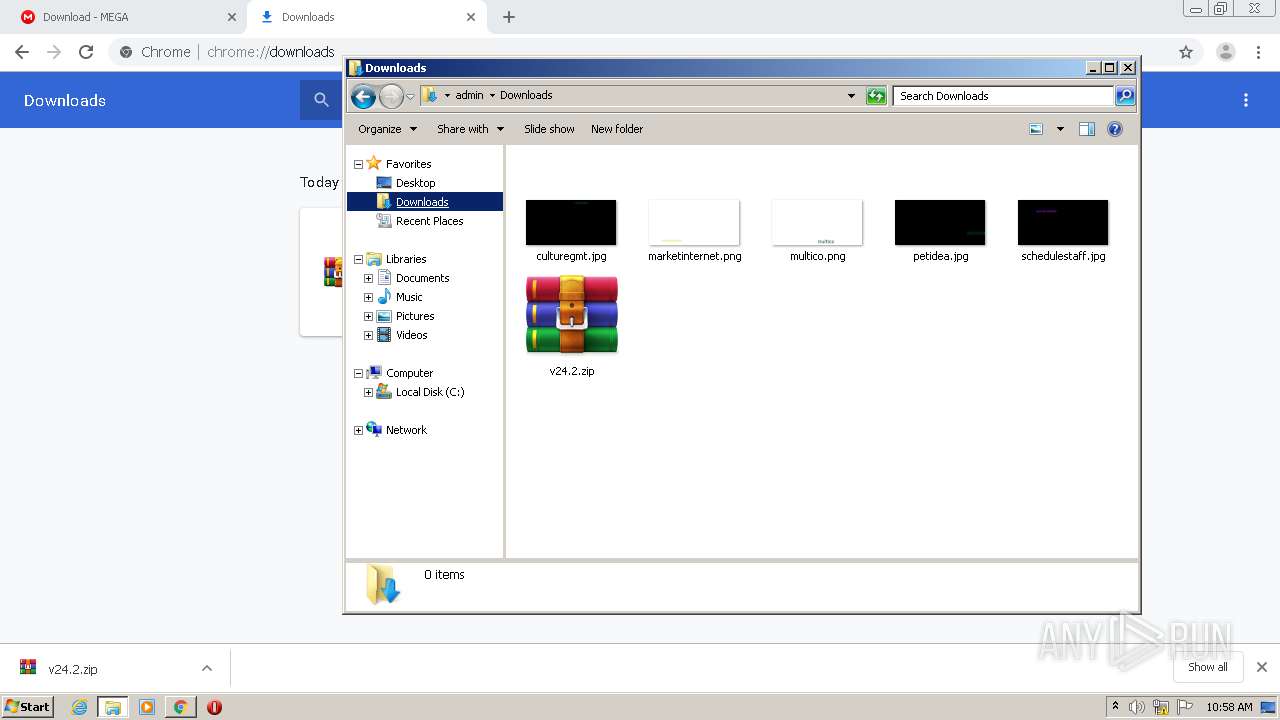
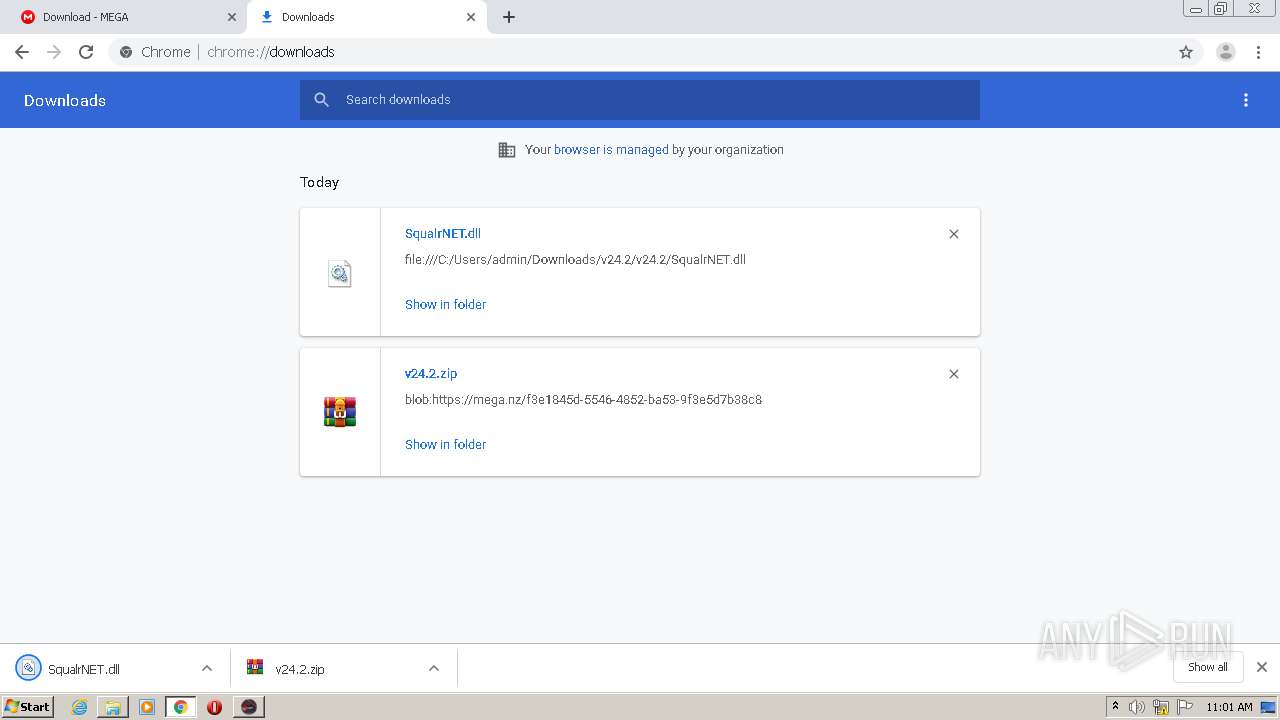
- WinRAR.exe (PID: 2452)
- WinRAR.exe (PID: 780)
- Hackermode v24.exe (PID: 2204)
- rundll32.exe (PID: 1200)
Application launched itself
- chrome.exe (PID: 2408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
26
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
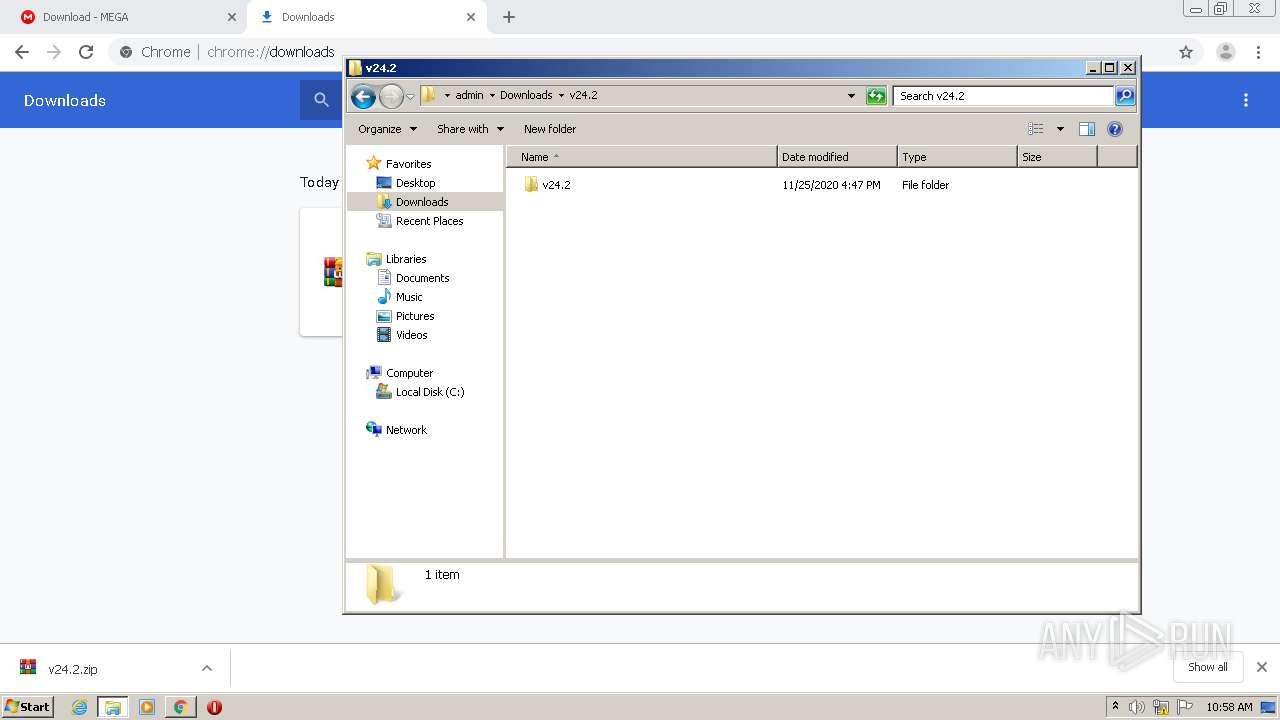
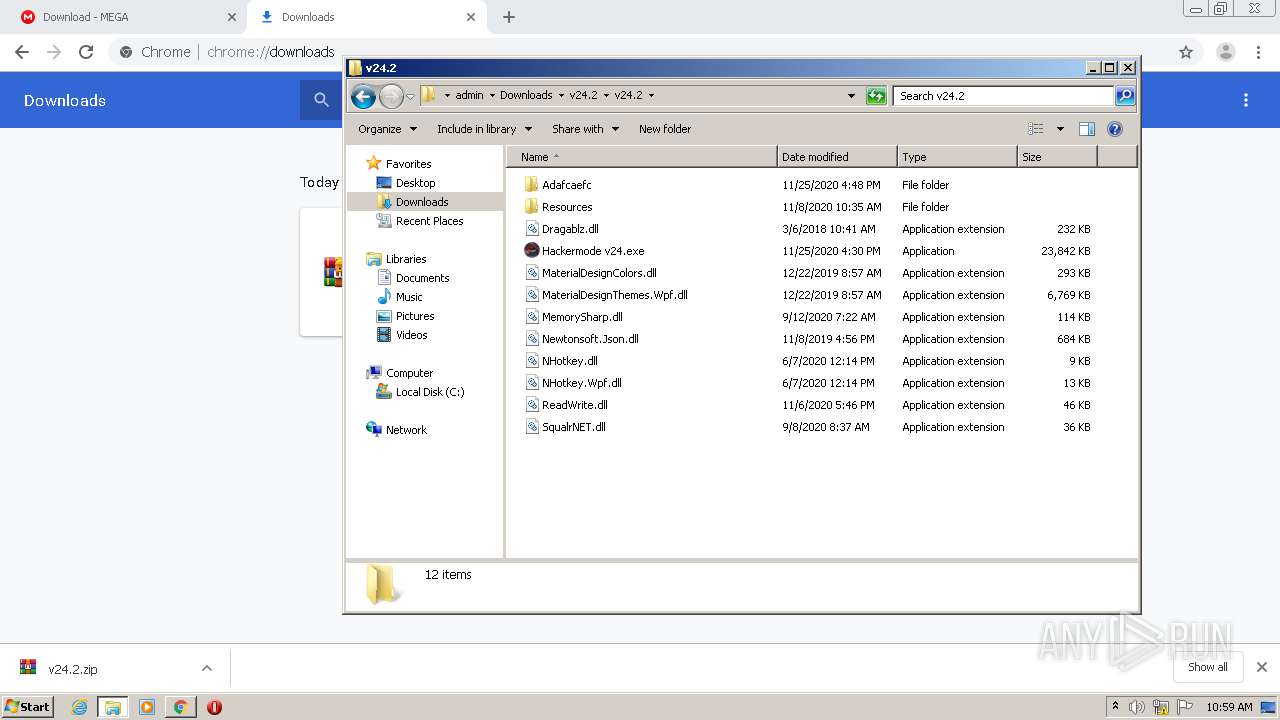
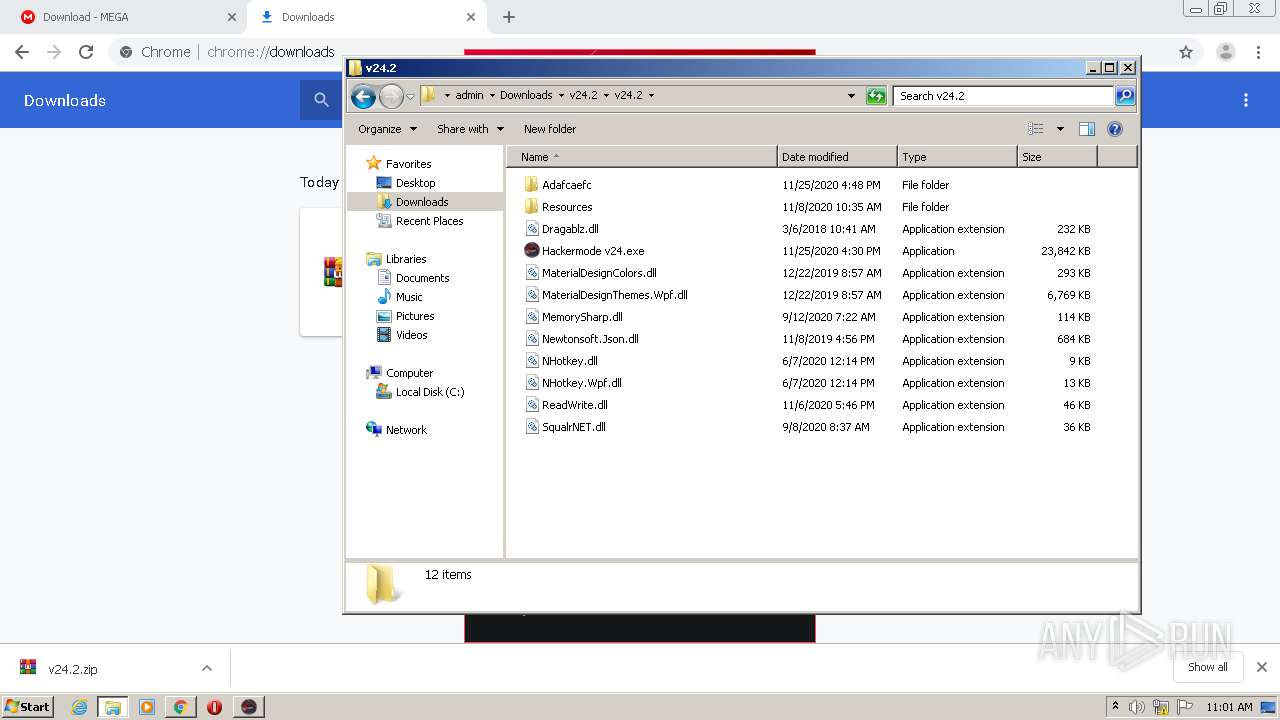
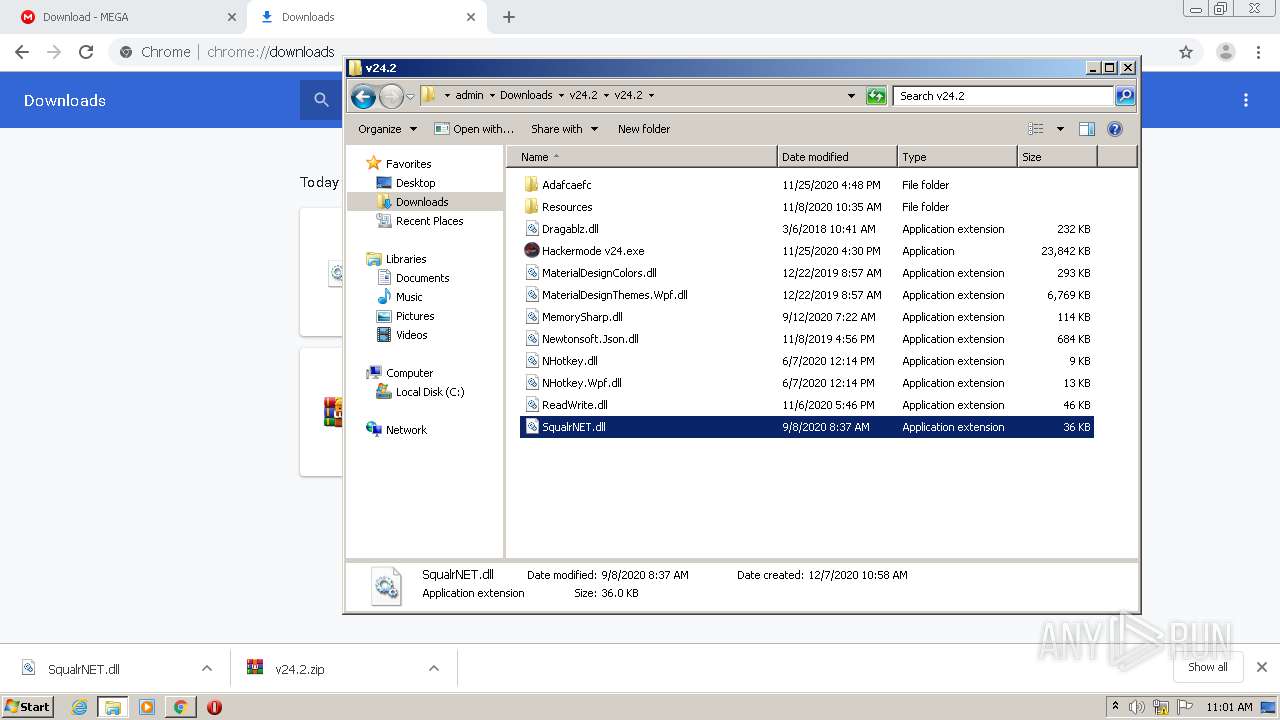
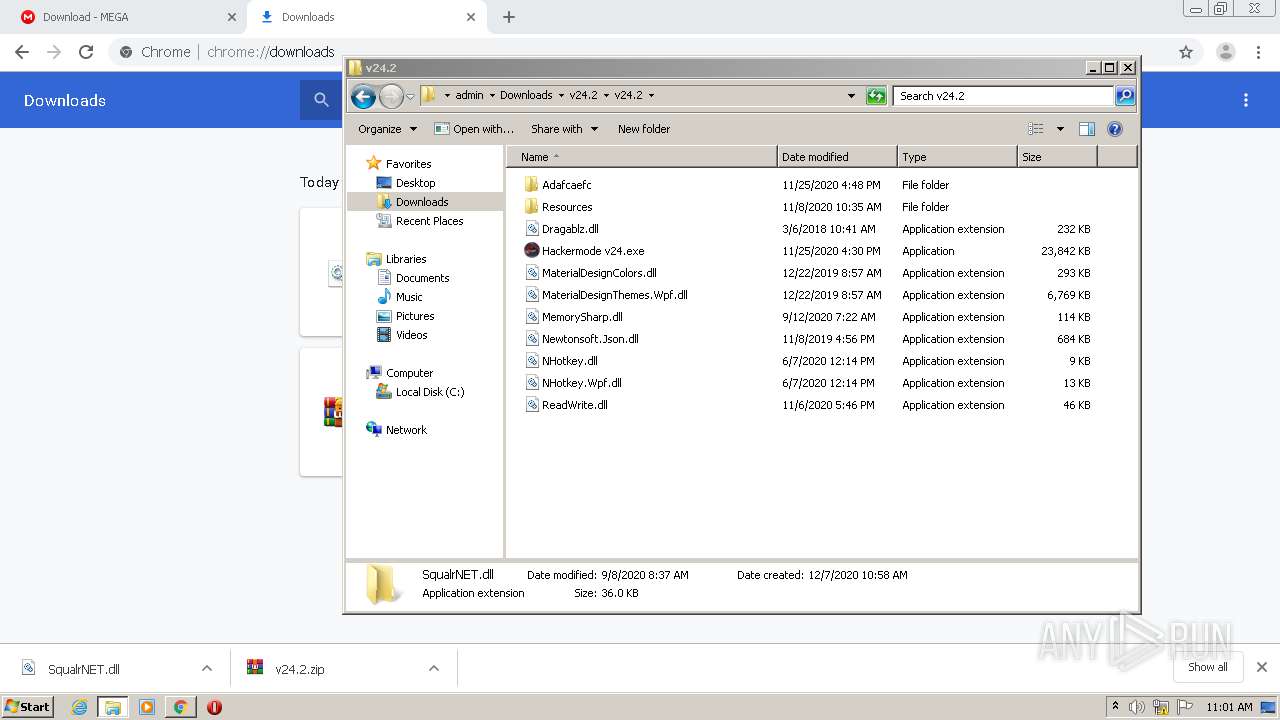
| 780 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\v24.2.zip" C:\Users\admin\Downloads\v24.2\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,11990083863609055818,14441007995725170630,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=12778446427105084577 --mojo-platform-channel-handle=1544 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
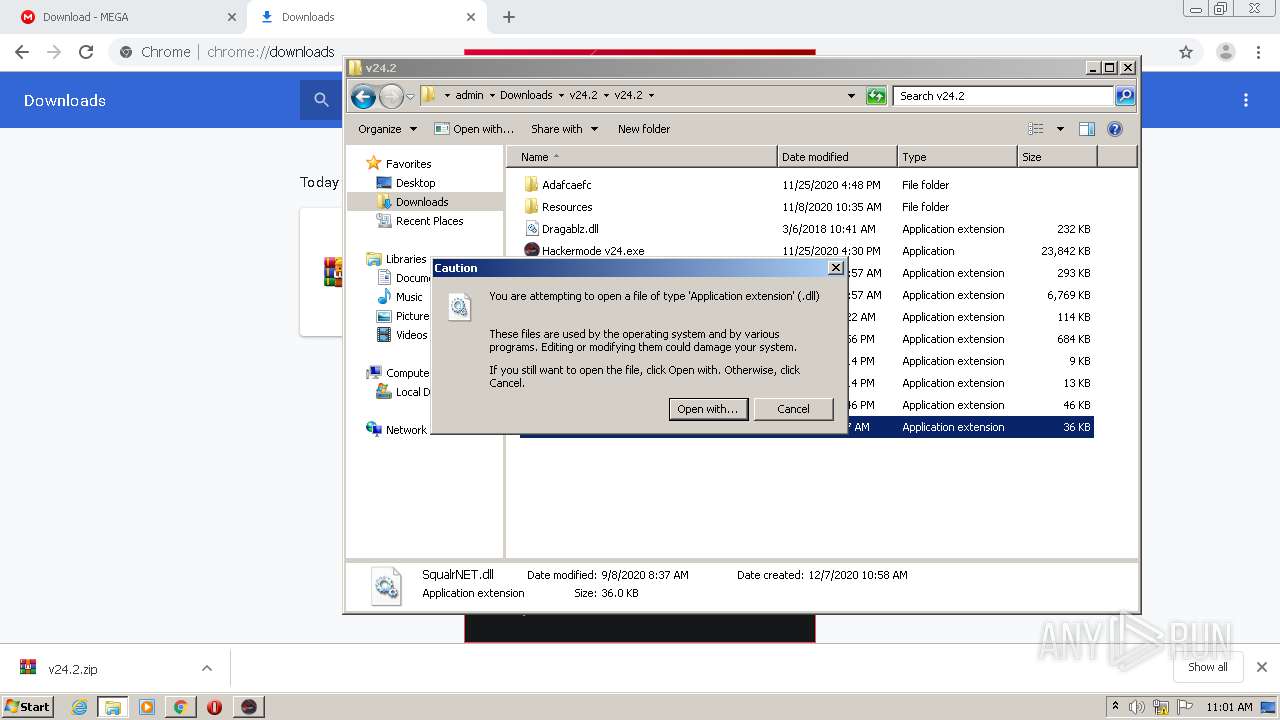
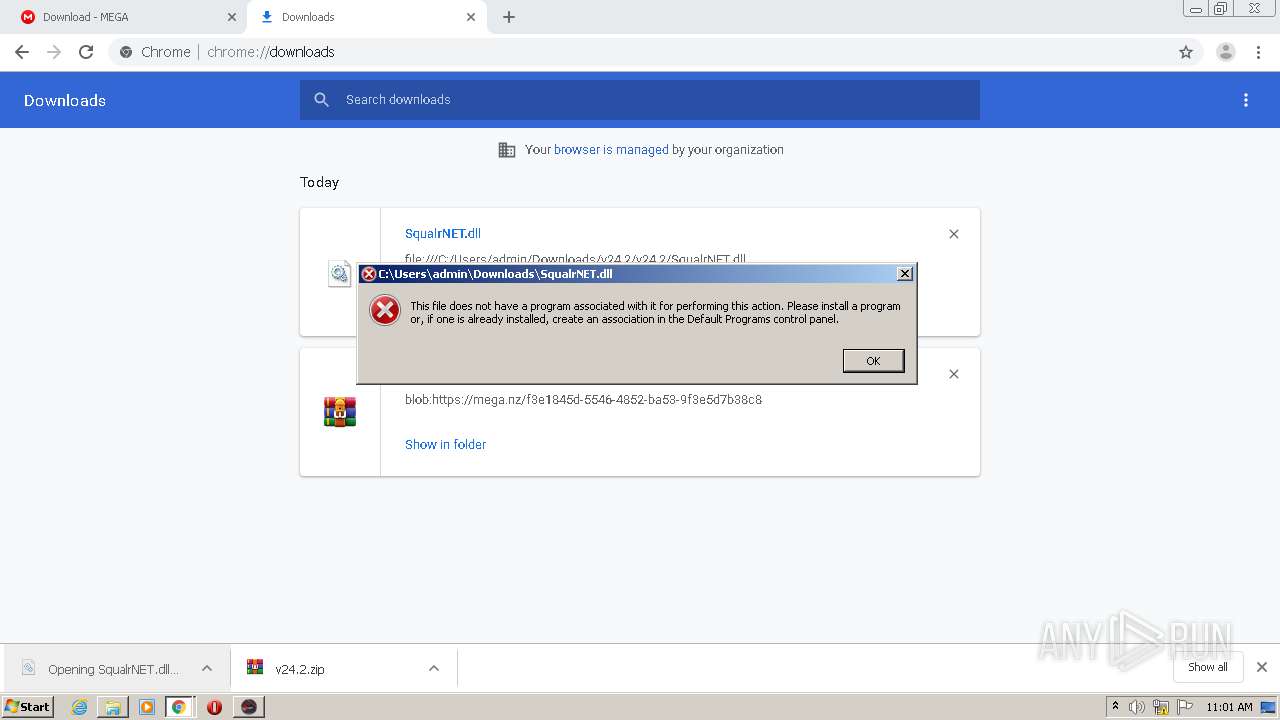
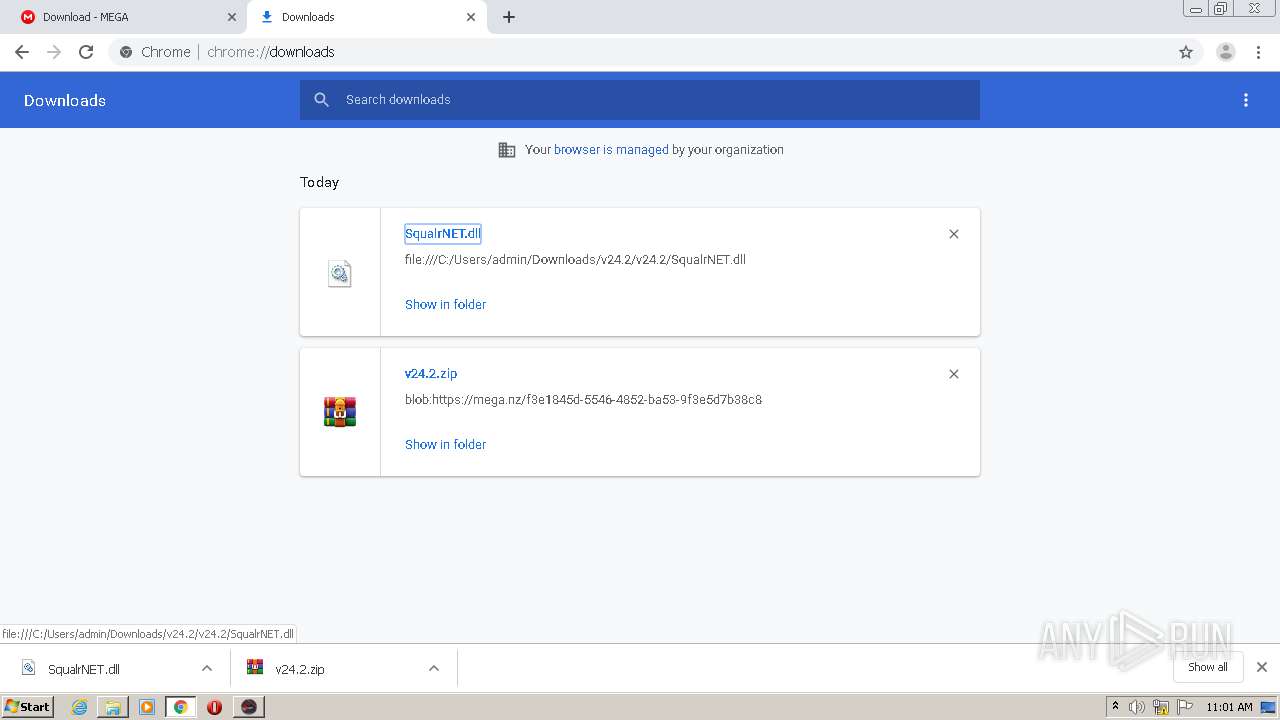
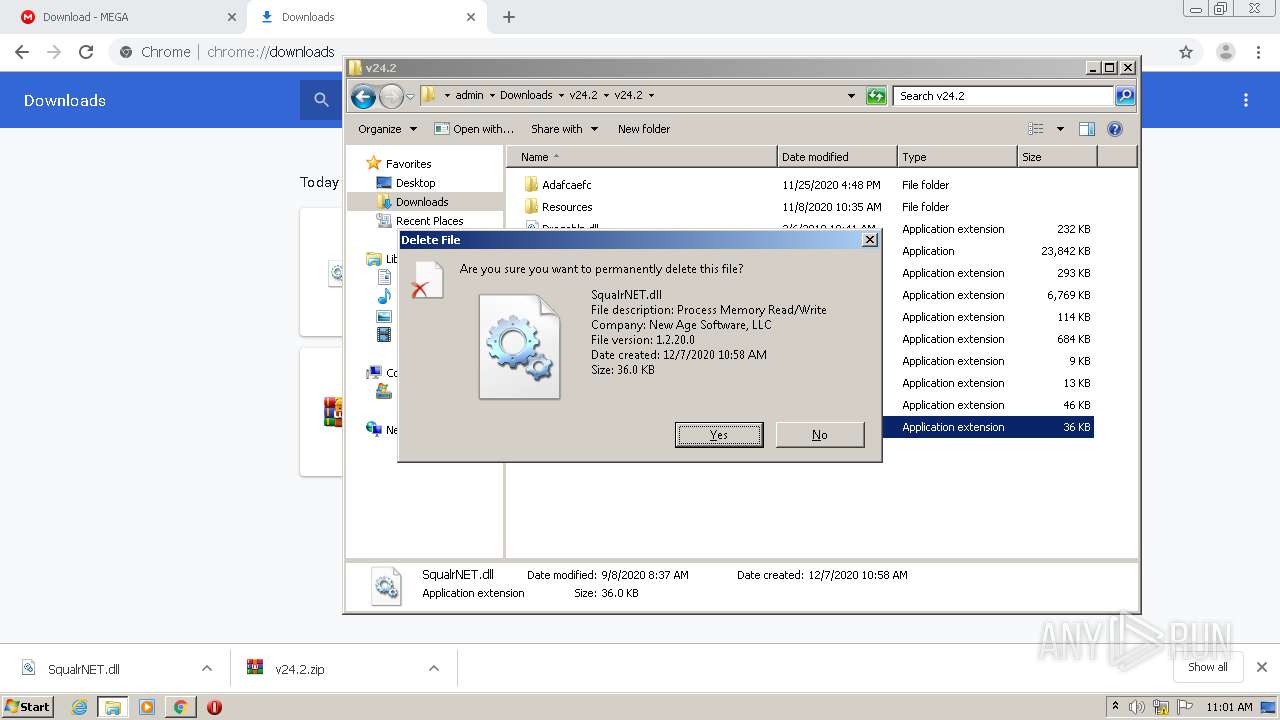
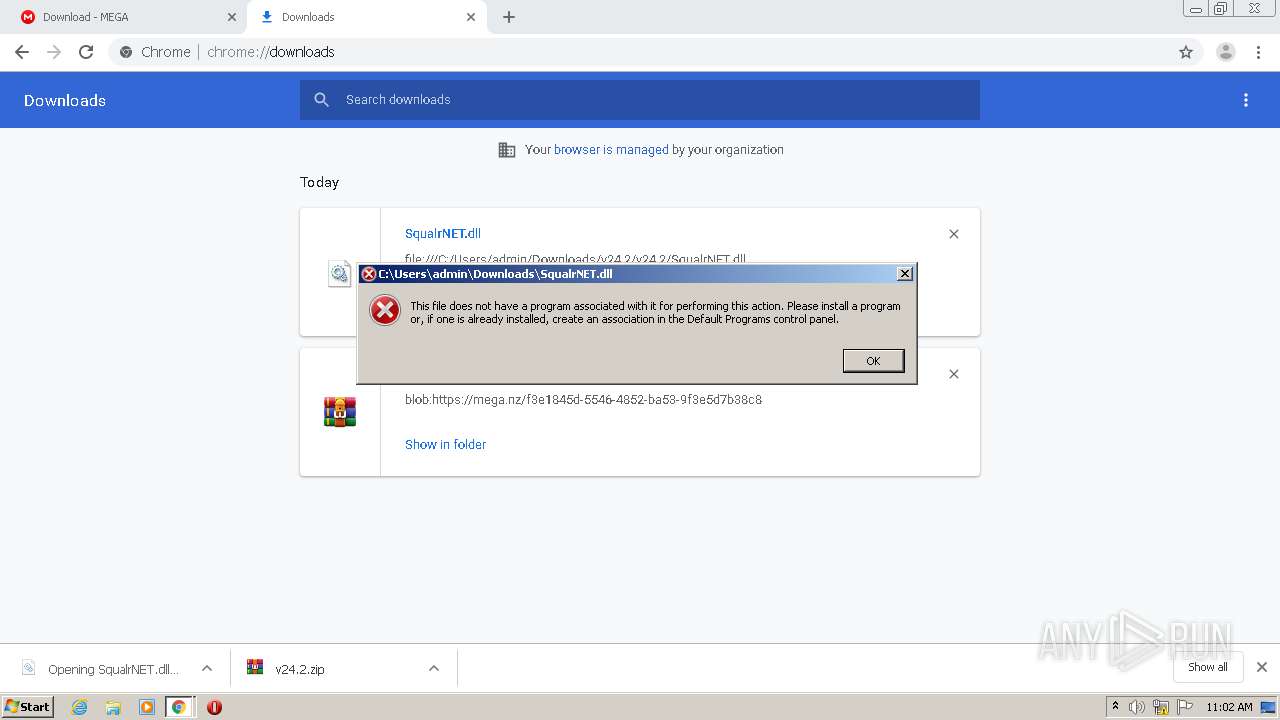
| 1200 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Downloads\v24.2\v24.2\SqualrNET.dll | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
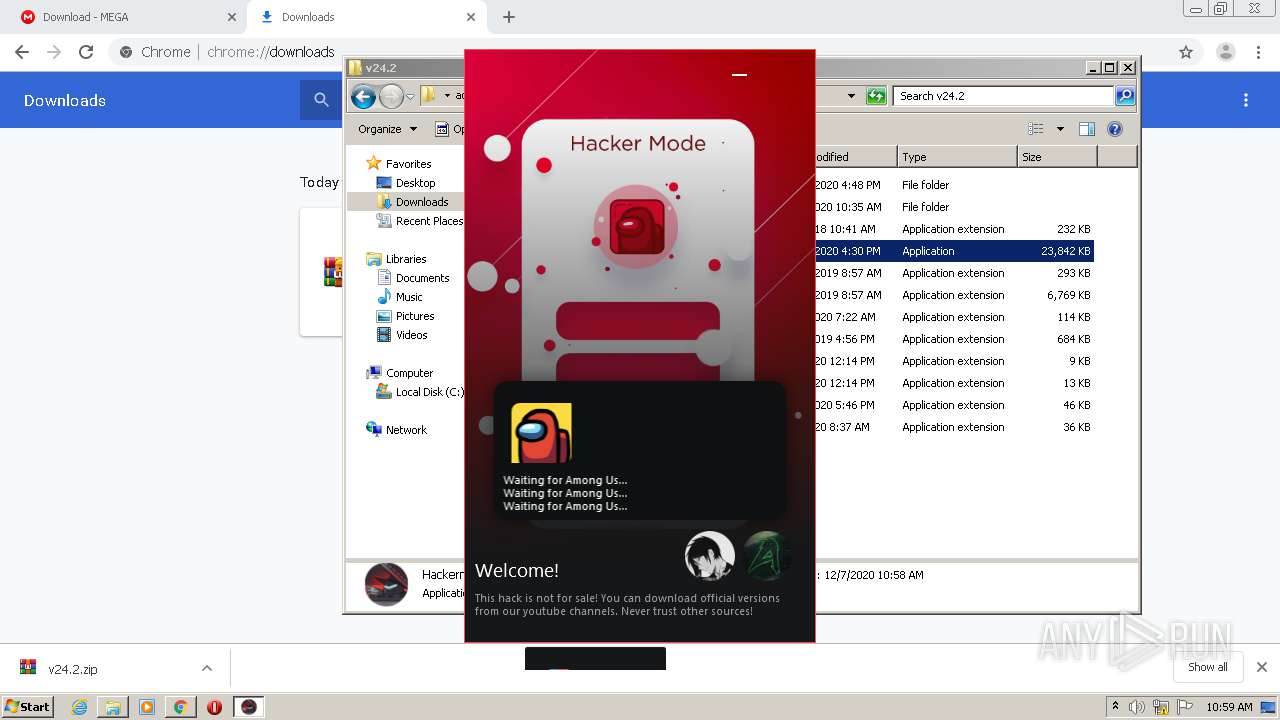
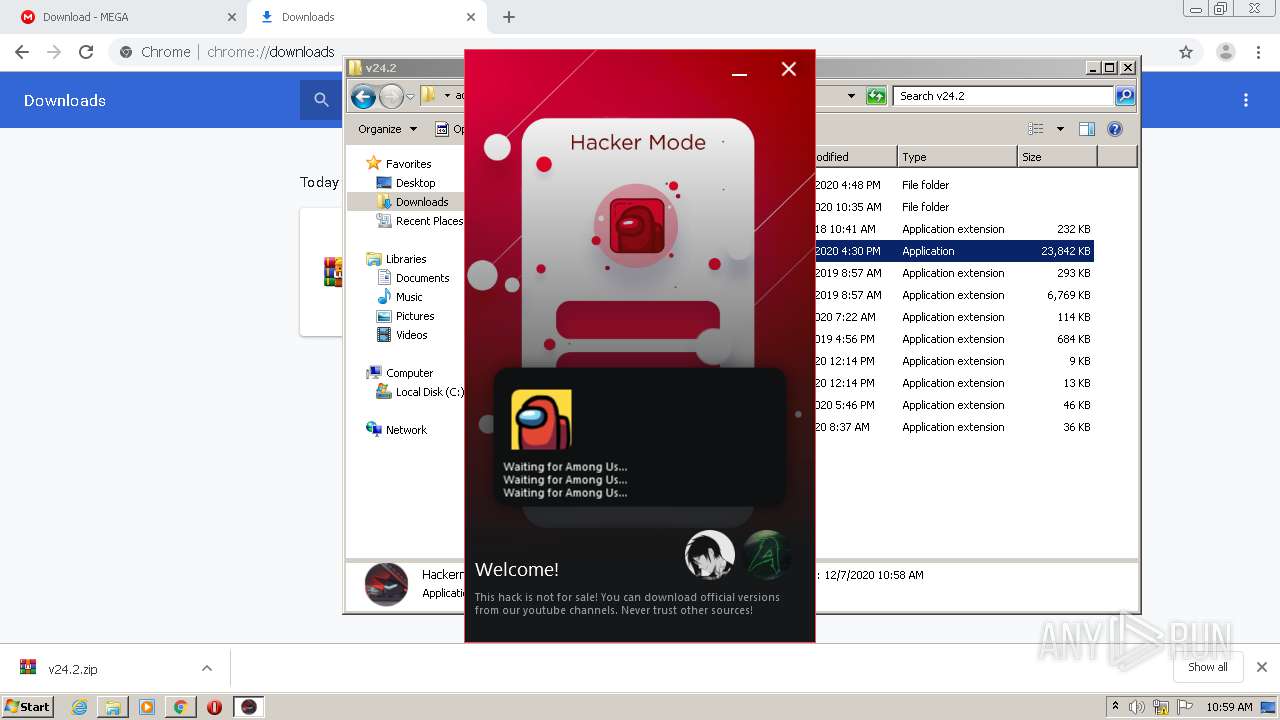
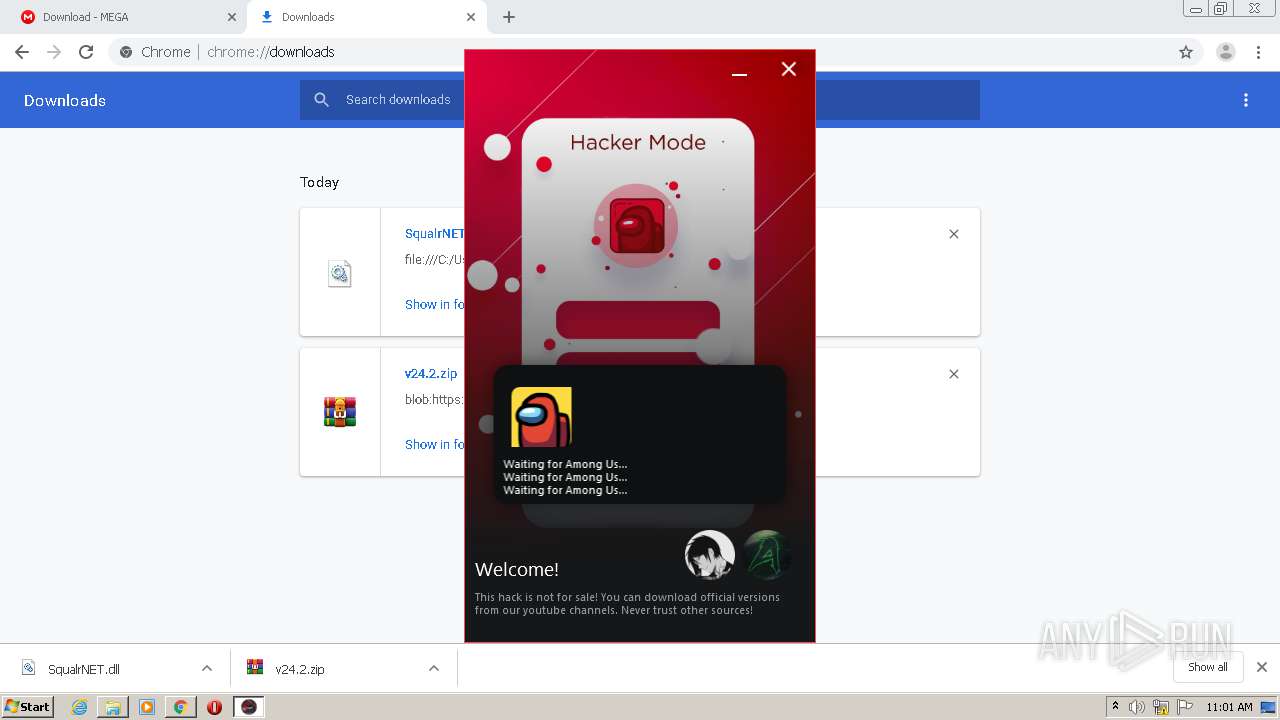
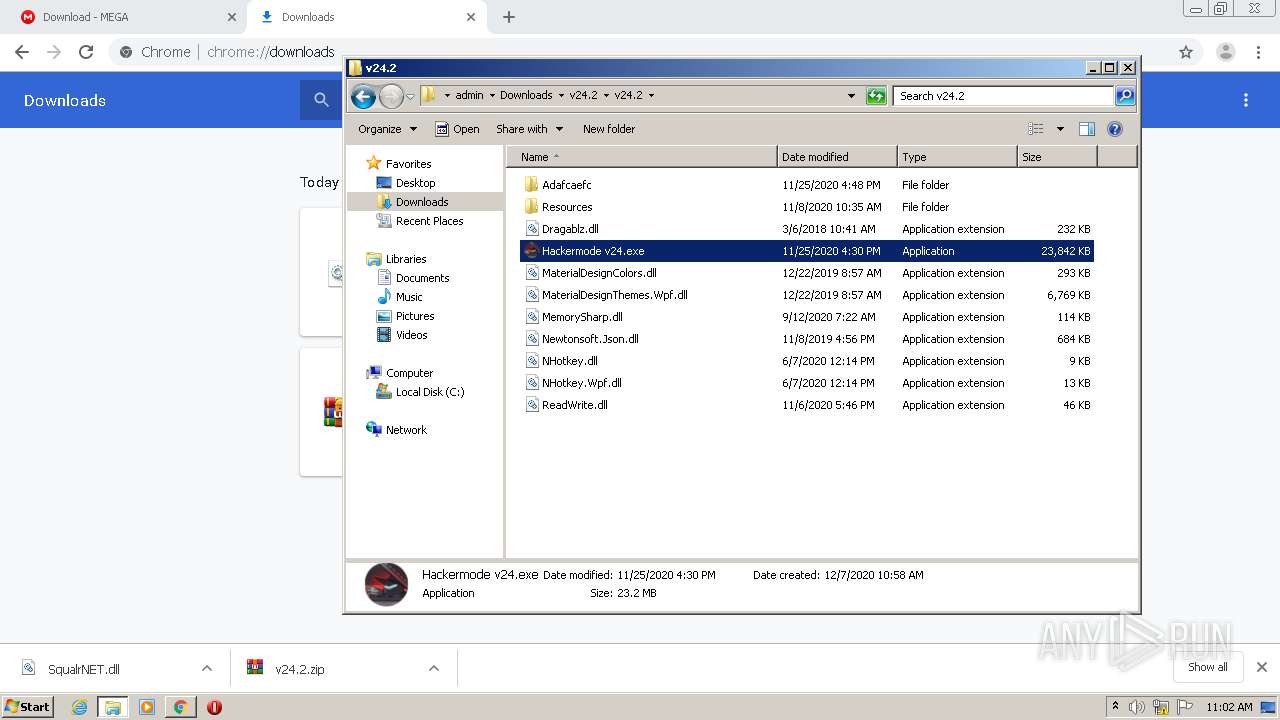
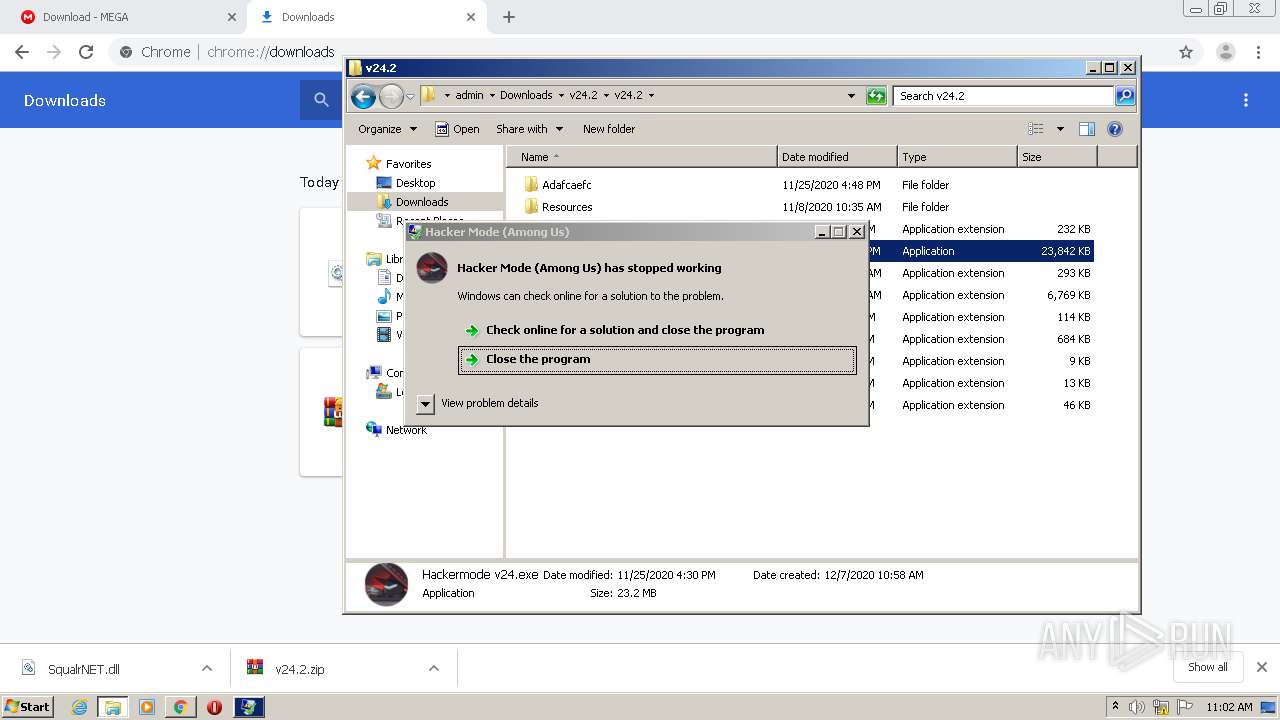
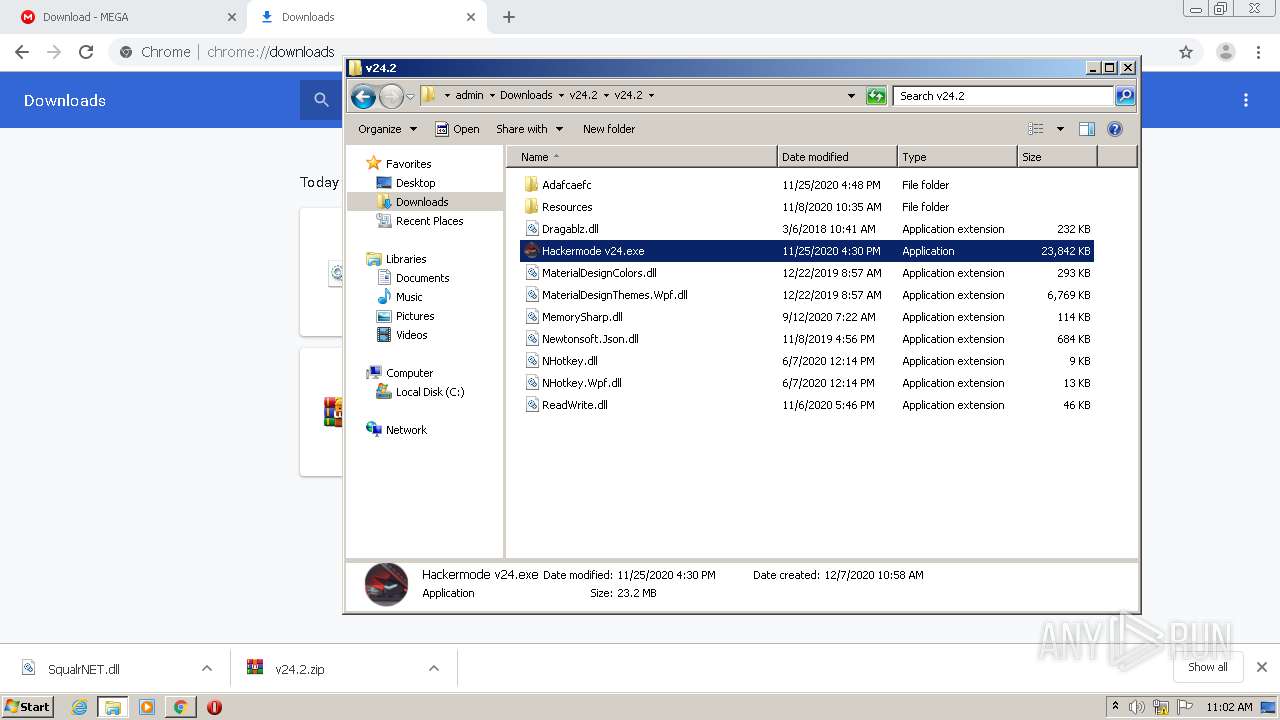
| 1440 | "C:\Users\admin\Downloads\v24.2\v24.2\Hackermode v24.exe" | C:\Users\admin\Downloads\v24.2\v24.2\Hackermode v24.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Hacker Mode (Among Us) Exit code: 3762504530 Version: 1.0.9.0 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,11990083863609055818,14441007995725170630,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2130991483507276803 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2412 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,11990083863609055818,14441007995725170630,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10011085835323571013 --mojo-platform-channel-handle=2428 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,11990083863609055818,14441007995725170630,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9225037607575693080 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3680 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2120 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe3_ Global\UsGthrCtrlFltPipeMssGthrPipe3 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 442
Read events
2 978
Write events
459
Delete events
5
Modification events
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2408-13251812284214125 |
Value: 259 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
14
Suspicious files
17
Text files
93
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FCE0ABD-968.pma | — | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6c426e47-0cd6-4039-a2a3-0b19bc6546e3.tmp | — | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF14367f.TMP | text | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF14367f.TMP | text | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF143670.TMP | text | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF143900.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
34
DNS requests
15
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1036 | chrome.exe | 66.203.127.12:443 | mega.nz | RealNetworks, Inc. | US | unknown |
1036 | chrome.exe | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
1036 | chrome.exe | 172.217.23.106:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1036 | chrome.exe | 216.58.207.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
1036 | chrome.exe | 66.203.127.11:443 | eu.static.mega.co.nz | RealNetworks, Inc. | US | suspicious |
— | — | 66.203.127.12:443 | mega.nz | RealNetworks, Inc. | US | unknown |
2204 | Hackermode v24.exe | 104.23.99.190:443 | pastebin.com | Cloudflare Inc | US | malicious |
1036 | chrome.exe | 216.58.212.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1036 | chrome.exe | 173.194.222.93:443 | sb-ssl.google.com | Google Inc. | US | unknown |
1036 | chrome.exe | 172.217.23.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mega.nz |
| whitelisted |
accounts.google.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
clients1.google.com |
| whitelisted |
eu.static.mega.co.nz |
| shared |
g.api.mega.co.nz |
| shared |
ssl.gstatic.com |
| whitelisted |
gfs204n114.userstorage.mega.co.nz |
| suspicious |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |