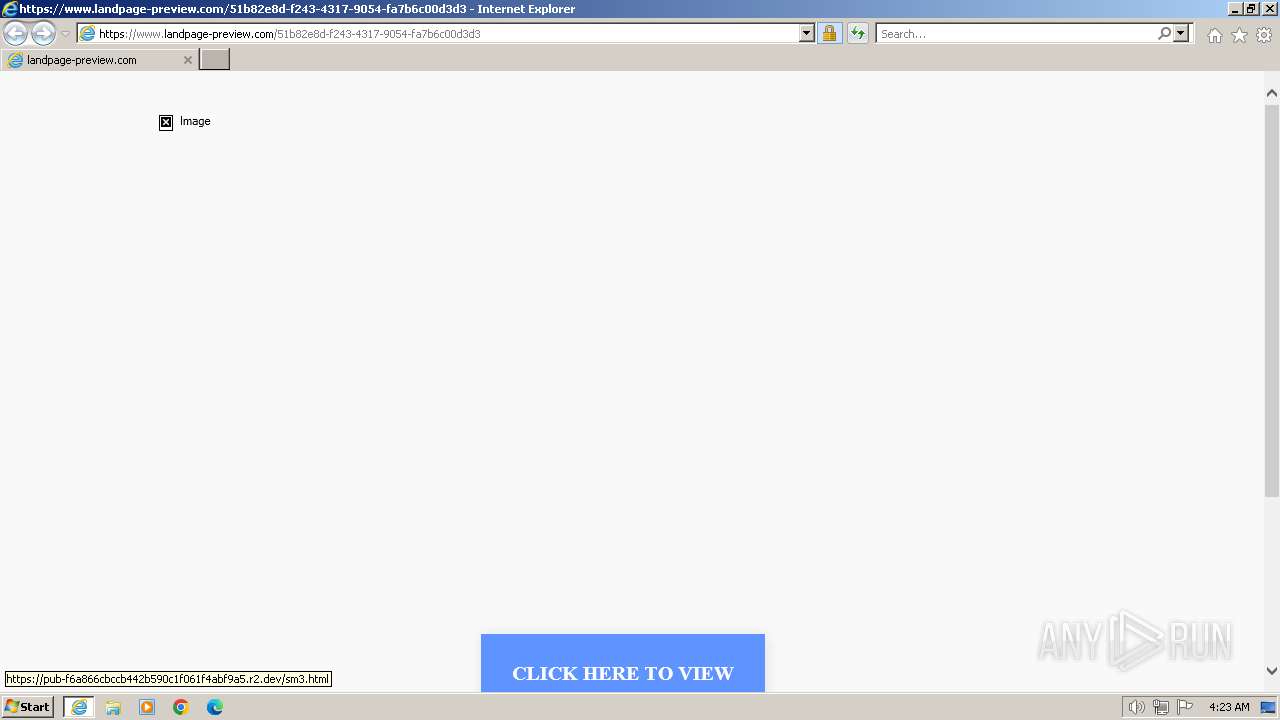
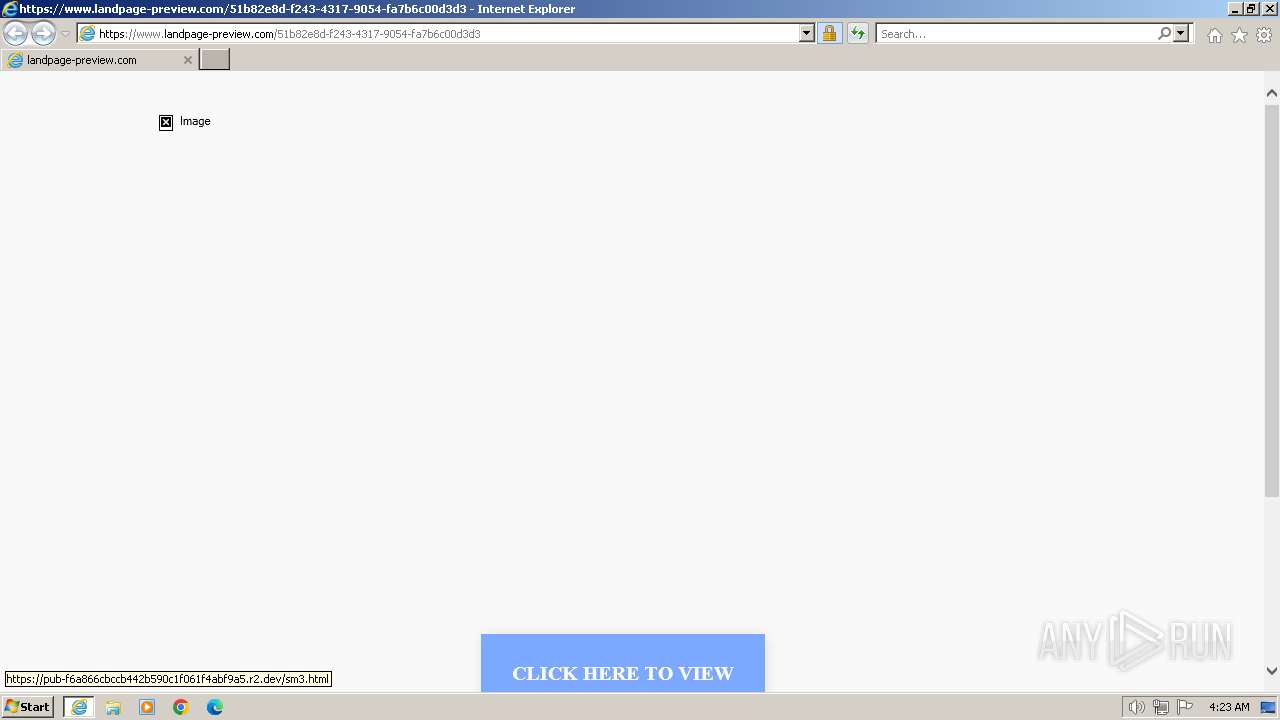
| URL: | https://www.landpage-preview.com/51b82e8d-f243-4317-9054-fa7b6c00d3d3 |
| Full analysis: | https://app.any.run/tasks/4d9a75e5-750c-4c5a-9727-5cd53cd7ab07 |
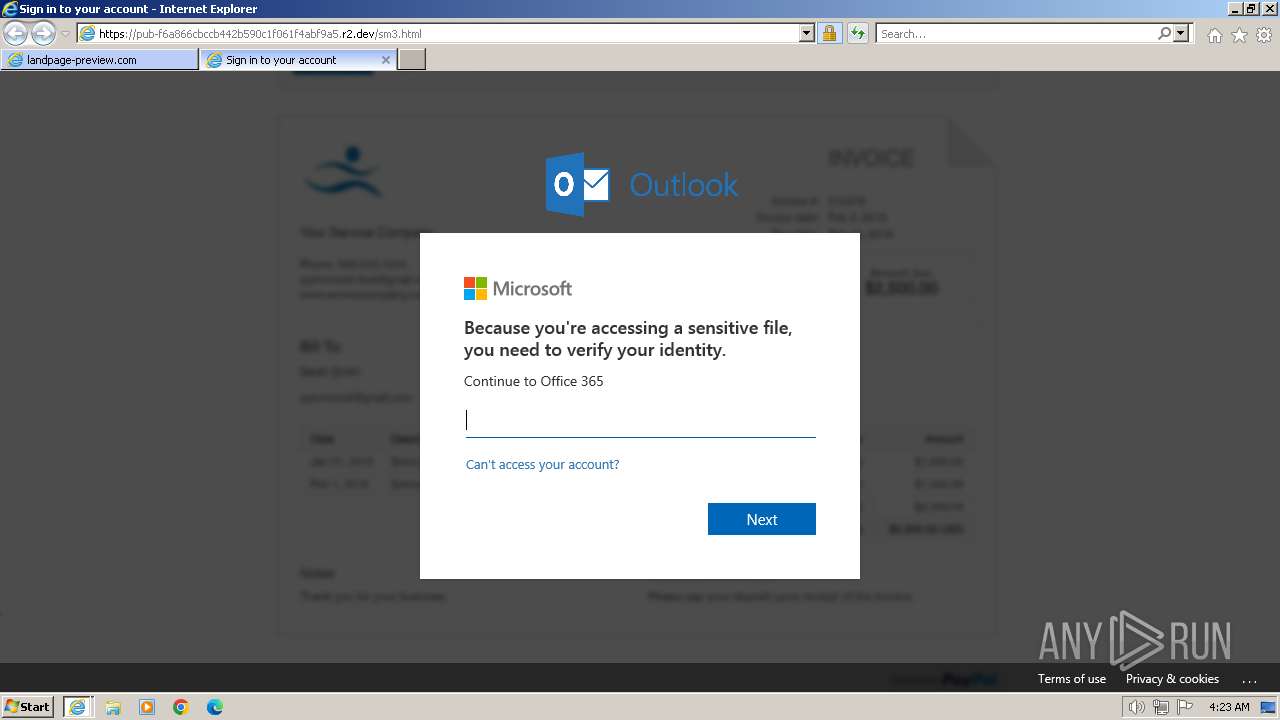
| Verdict: | Malicious activity |
| Analysis date: | April 11, 2024, 03:23:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CBAB90E838A37495CB9941D19C4BE6B2 |
| SHA1: | 10279B48D56FAA3445CD685D882346F89300F4A1 |
| SHA256: | FDEF75000D09C96335079FEE41F31034692E43DA1C69753640F3D4F82DD2BFAB |
| SSDEEP: | 3:N8DSLQBNA3wR1FR4U7ZM7Ngn:2OLUN/RZdM5gn |
MALICIOUS
PHISHING has been detected (SURICATA)
- iexplore.exe (PID: 3540)
SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 1696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1696 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.landpage-preview.com/51b82e8d-f243-4317-9054-fa7b6c00d3d3" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2692 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1696 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3540 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1696 CREDAT:2168076 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
31 069
Read events
30 924
Write events
101
Delete events
44
Modification events
| (PID) Process: | (1696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31099839 | |||
| (PID) Process: | (1696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31099839 | |||
| (PID) Process: | (1696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
31
Text files
23
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab2AA5.tmp | compressed | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar2AA6.tmp | cat | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab2AB6.tmp | compressed | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar2AB7.tmp | cat | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | der | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 2692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\FBE08748712A0225485E3E06A0C8581A | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
73
DNS requests
35
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2692 | iexplore.exe | GET | 304 | 95.101.54.113:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7f30423e8f7249ff | unknown | — | — | unknown |
2692 | iexplore.exe | GET | 304 | 95.101.54.120:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5259f1aa84763c8c | unknown | — | — | unknown |
2692 | iexplore.exe | GET | 200 | 95.101.54.120:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?22f3adc483c3ba5b | unknown | — | — | unknown |
2692 | iexplore.exe | GET | 200 | 95.101.54.113:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?9df0723acf4b4299 | unknown | — | — | unknown |
2692 | iexplore.exe | GET | 200 | 92.123.17.153:80 | http://x1.c.lencr.org/ | unknown | — | — | unknown |
2692 | iexplore.exe | GET | 200 | 95.101.54.107:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgMzEjgGgMBncd3SyQSHHB1qsw%3D%3D | unknown | — | — | unknown |
2692 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | unknown |
2692 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | — | — | unknown |
2692 | iexplore.exe | GET | 200 | 2.19.96.160:80 | http://subca.ocsp-certum.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTYOkzrrCGQj08njZXbUQQpkoUmuQQUCHbNywf%2FJPbFze27kLzihDdGdfcCECbd0itGycRNWmlNOYB%2Bcq0%3D | unknown | — | — | unknown |
2692 | iexplore.exe | GET | 200 | 2.19.96.160:80 | http://dvcasha2.ocsp-certum.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNcCPjJ499lHmfPUvPsRjzr1YchwQU5TGtvzoRlvSDvFA81LeQm5Du3iUCEEtzQkzDX0itkG9w0gGJ9E4%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2692 | iexplore.exe | 157.53.227.1:443 | www.landpage-preview.com | NetActuate, Inc | US | unknown |
2692 | iexplore.exe | 95.101.54.120:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2692 | iexplore.exe | 95.101.54.113:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2692 | iexplore.exe | 92.123.17.153:80 | x1.c.lencr.org | AKAMAI-AS | AT | unknown |
2692 | iexplore.exe | 95.101.54.107:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
2692 | iexplore.exe | 18.202.162.134:443 | popups.landingi.com | AMAZON-02 | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.landpage-preview.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
styles.assets-landingi.com |
| whitelisted |
popups.landingi.com |
| unknown |
scripts.assets-landingi.com |
| unknown |
images.assets-landingi.com |
| unknown |
cdn.lugc.link |
| unknown |
assetslp.link |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
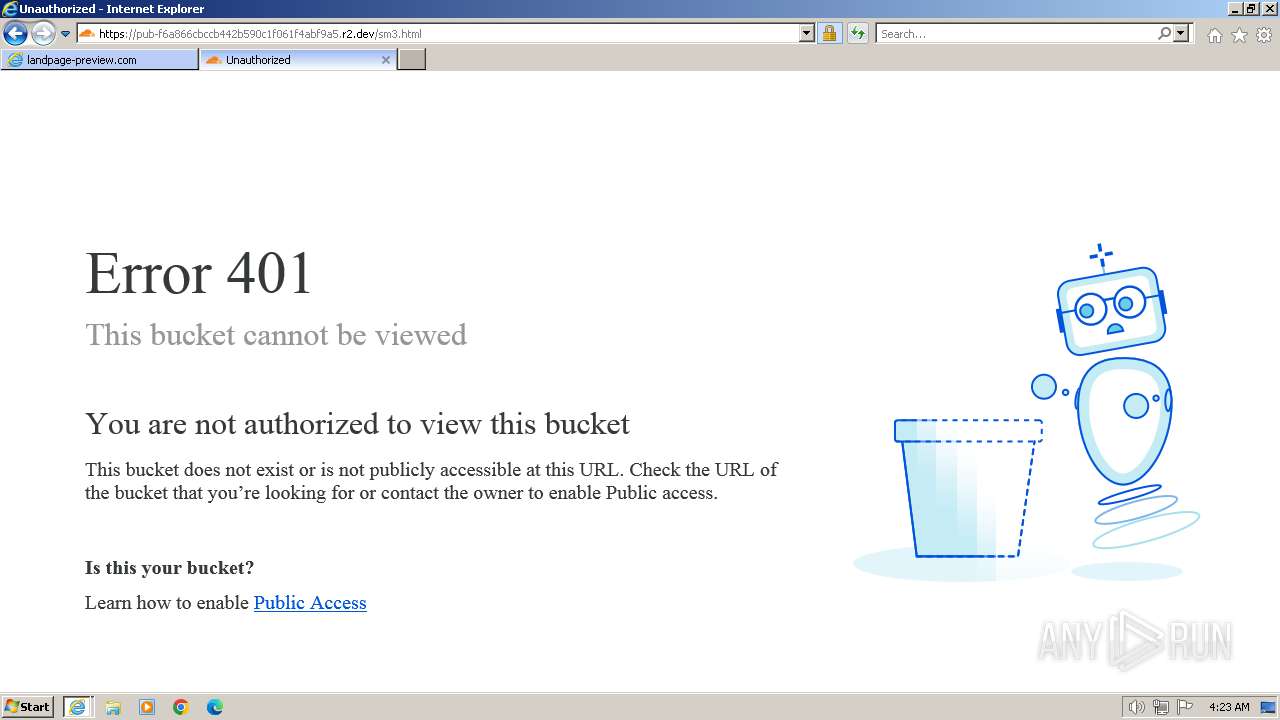
3540 | iexplore.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Possible Public R2.dev Bucket Abuse to Phishing in TLS (Greatness) |
3540 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code.jquery .com) |