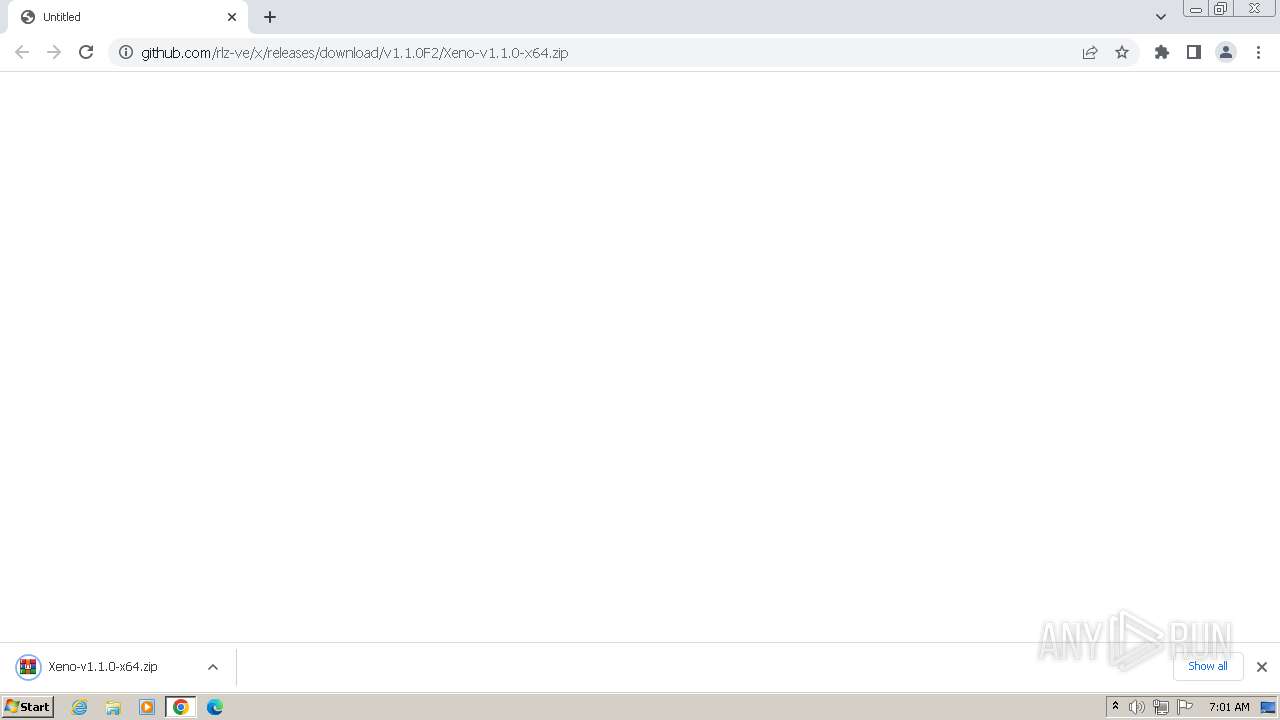
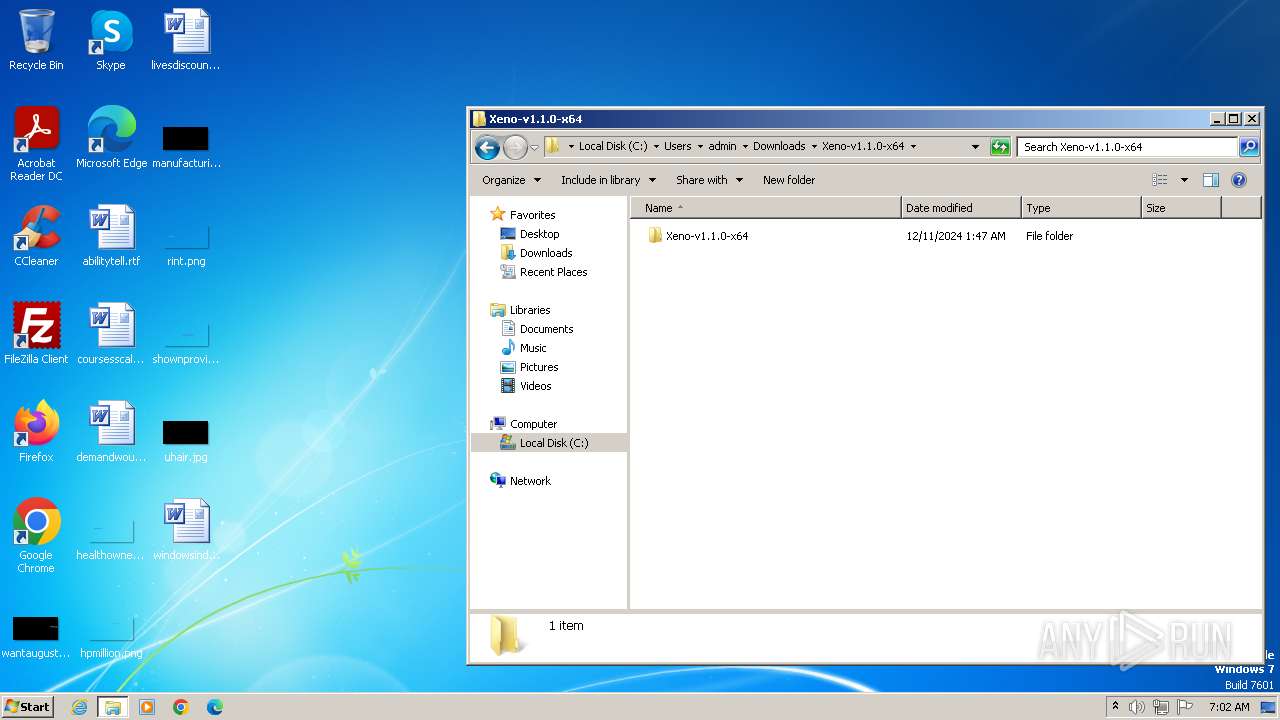
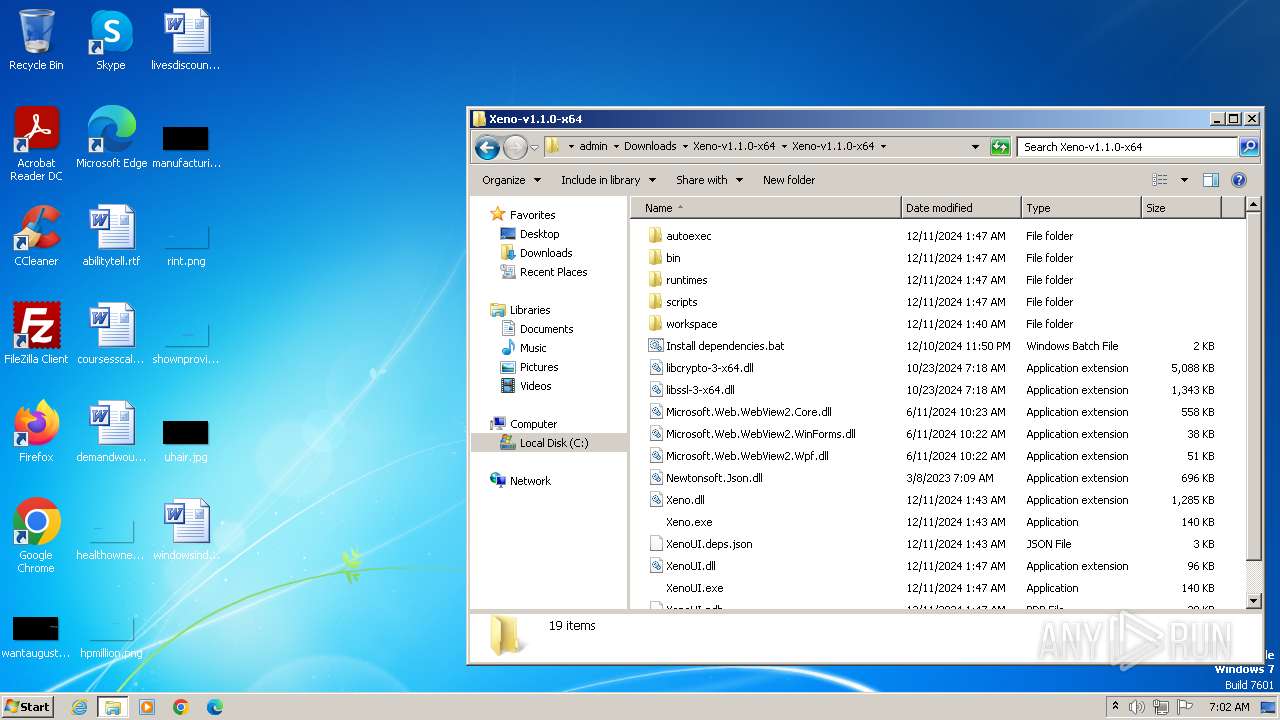
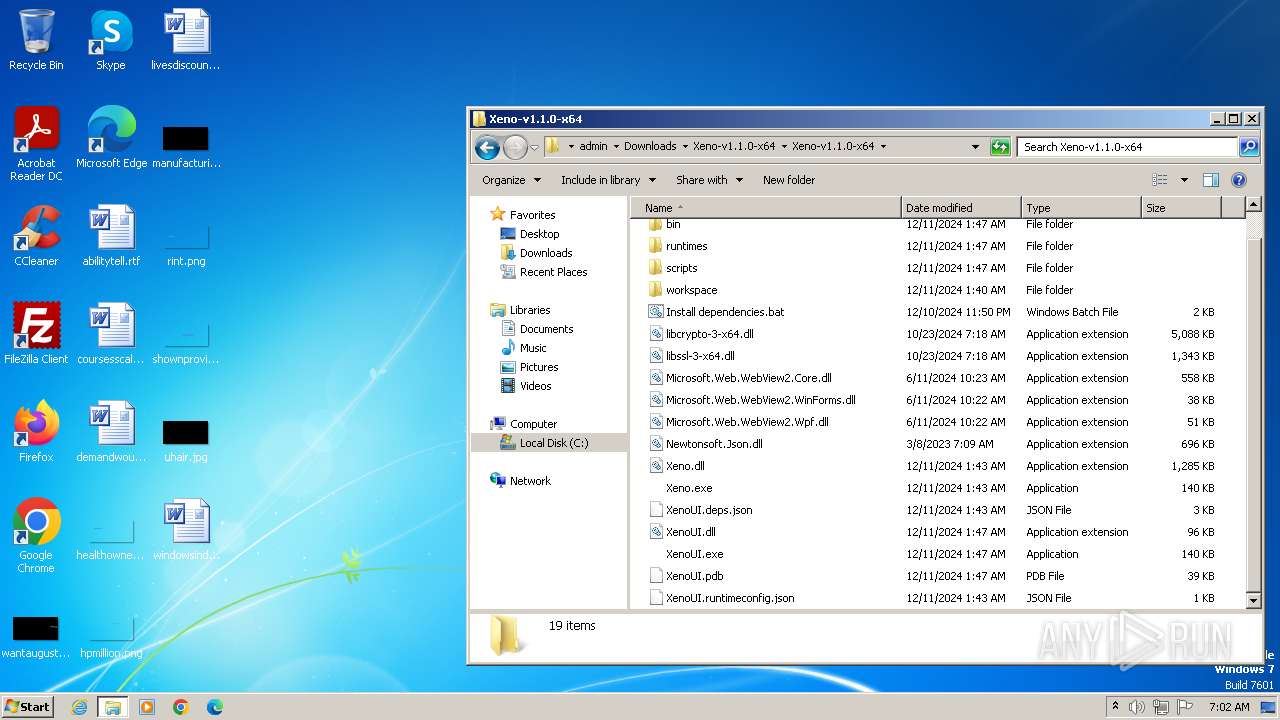
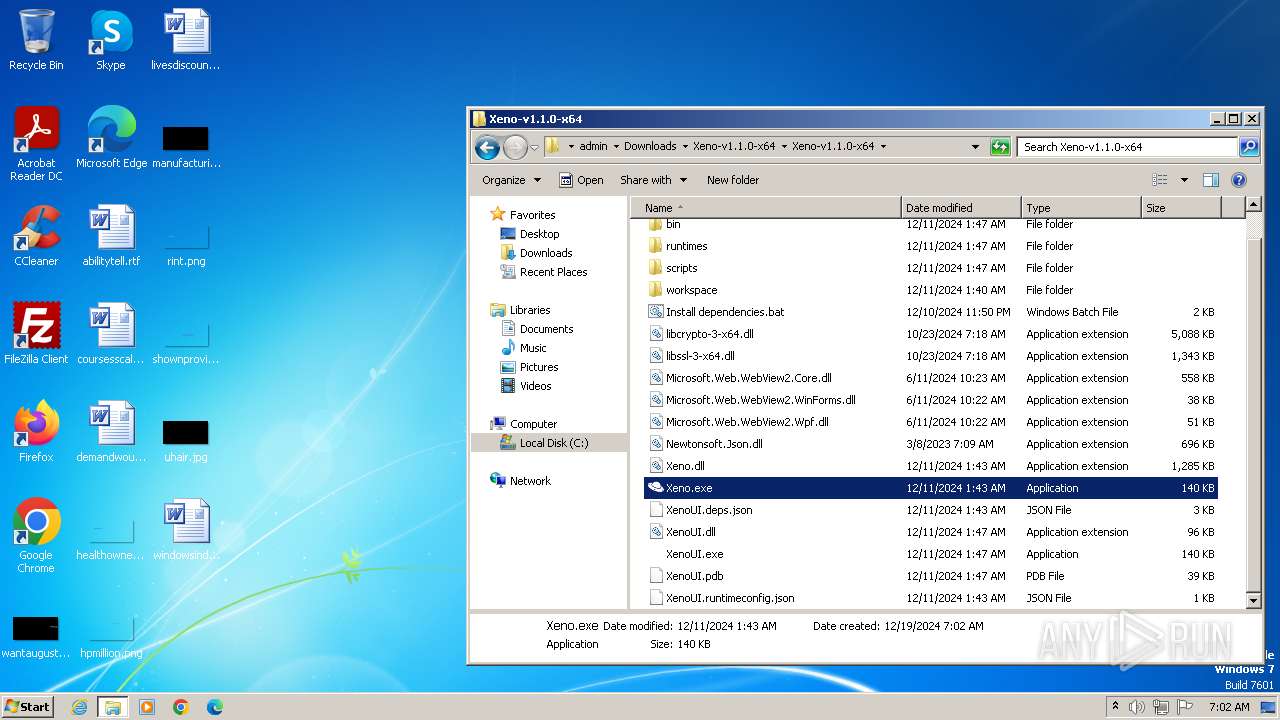
| URL: | https://github.com/rlz-ve/x/releases/download/v1.1.0F2/Xeno-v1.1.0-x64.zip |
| Full analysis: | https://app.any.run/tasks/995f81f4-2548-4f9d-b2f3-76260451145e |
| Verdict: | Malicious activity |
| Analysis date: | December 19, 2024, 07:01:42 |
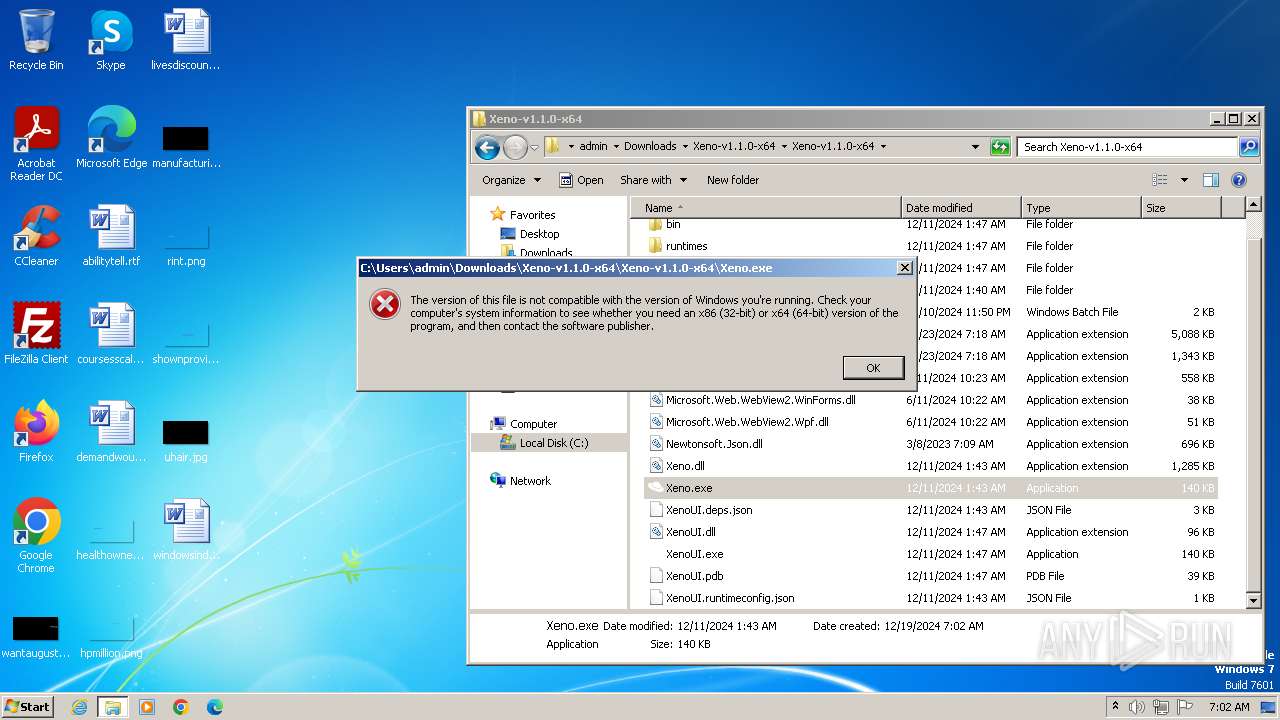
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0D1B15DD124A4CC07624AEEF2DEA94F3 |
| SHA1: | 504DFF340A611D74DC7097659A333EA29828F331 |
| SHA256: | FDEF45577F81754EBF312D8D4354A07773B003EF12F9B1D7AD2474B8EAFE83FB |
| SSDEEP: | 3:N8tEdncekCmSJaYYLULiRRLc:2unsSyOiRR4 |
MALICIOUS
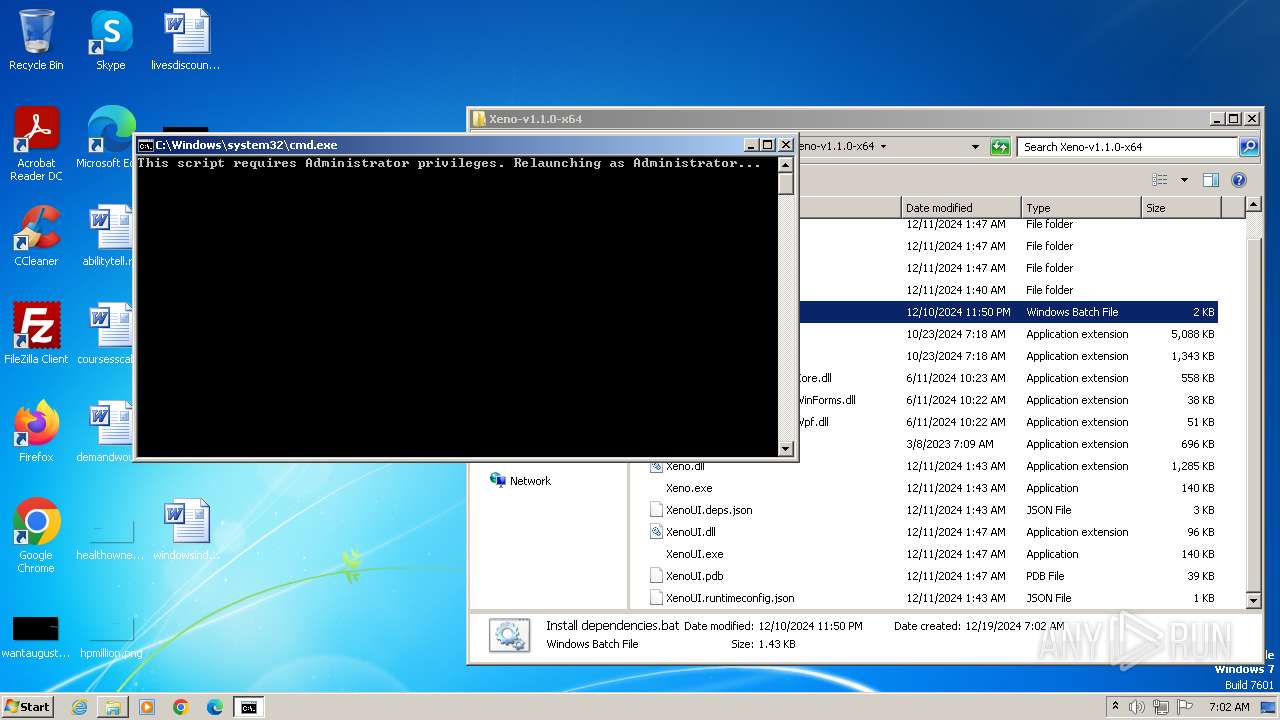
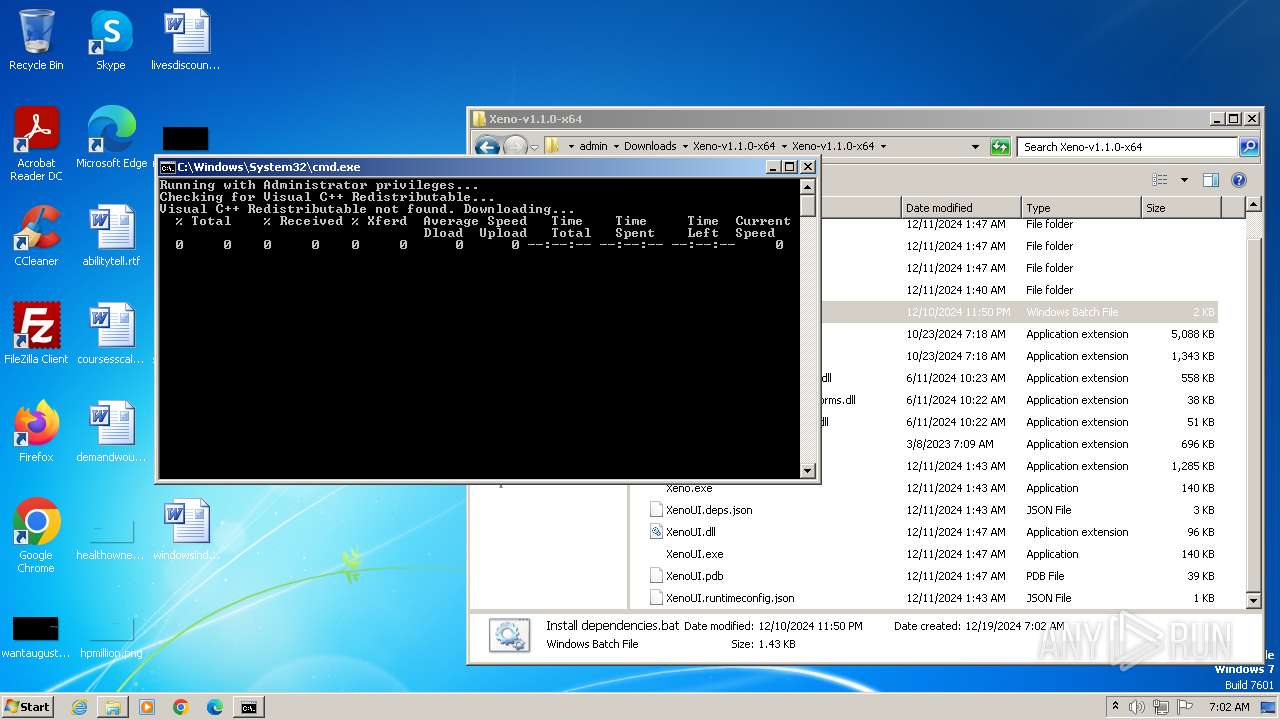
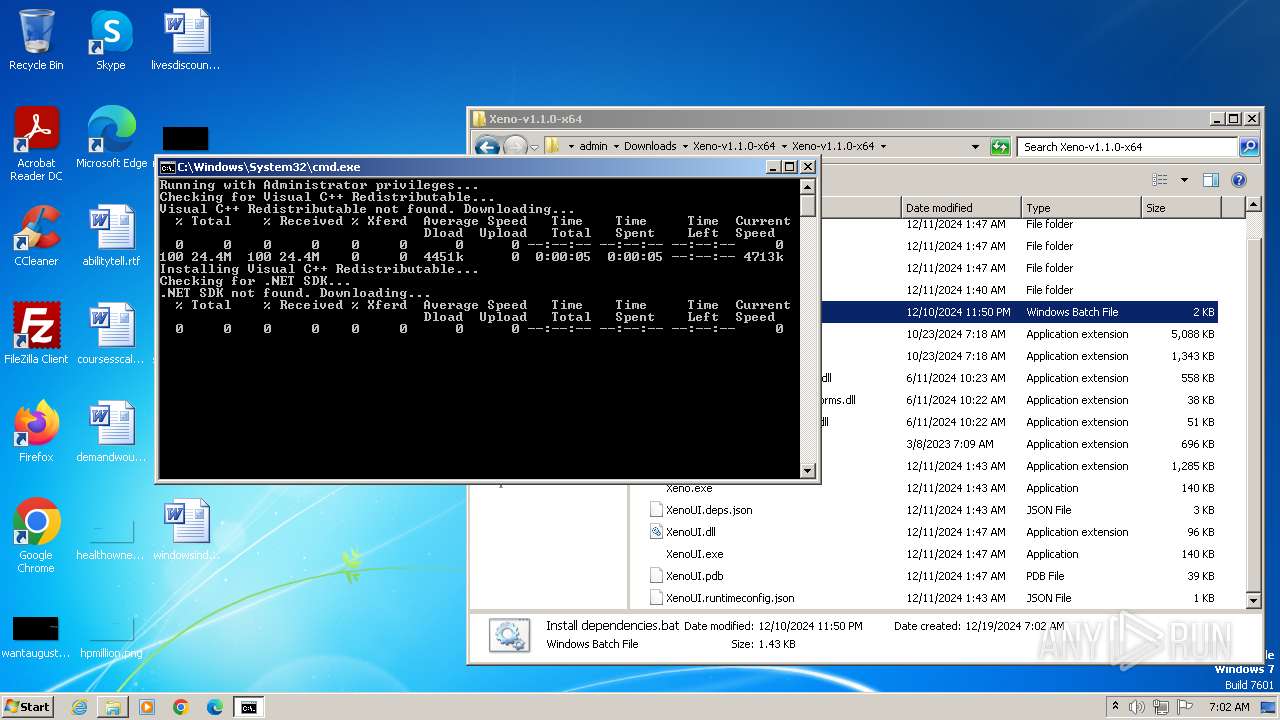
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 3096)
Bypass execution policy to execute commands
- powershell.exe (PID: 3428)
Executing a file with an untrusted certificate
- curl.exe (PID: 1584)
- curl.exe (PID: 2860)
Changes the autorun value in the registry
- VC_redist.x64.exe (PID: 2656)
SUSPICIOUS
Process drops legitimate windows executable
- chrome.exe (PID: 1252)
- WinRAR.exe (PID: 3440)
- curl.exe (PID: 1584)
- vc_redist.x64.exe (PID: 1088)
- VC_redist.x64.exe (PID: 2656)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 3096)
- net.exe (PID: 3728)
- cmd.exe (PID: 3928)
- net.exe (PID: 1096)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3096)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 3096)
Starts process via Powershell
- powershell.exe (PID: 3428)
Reads the Internet Settings
- powershell.exe (PID: 3428)
- vc_redist.x64.exe (PID: 1088)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 3428)
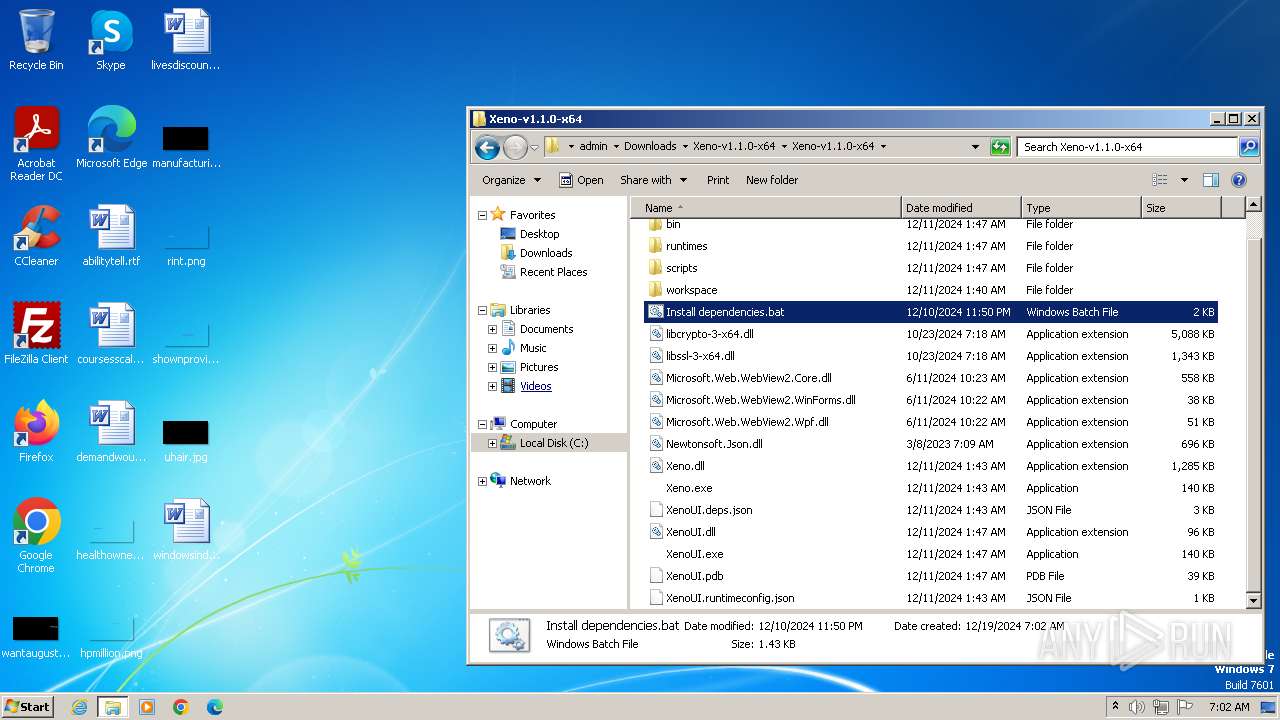
Executable content was dropped or overwritten
- curl.exe (PID: 1584)
- vc_redist.x64.exe (PID: 652)
- vc_redist.x64.exe (PID: 1088)
- VC_redist.x64.exe (PID: 2656)
Executing commands from a ".bat" file
- powershell.exe (PID: 3428)
Starts a Microsoft application from unusual location
- vc_redist.x64.exe (PID: 1088)
- VC_redist.x64.exe (PID: 2656)
Searches for installed software
- VC_redist.x64.exe (PID: 2656)
- vc_redist.x64.exe (PID: 1088)
Starts itself from another location
- vc_redist.x64.exe (PID: 1088)
Reads security settings of Internet Explorer
- vc_redist.x64.exe (PID: 1088)
Executes as Windows Service
- VSSVC.exe (PID: 2728)
Creates a software uninstall entry
- VC_redist.x64.exe (PID: 2656)
Creates file in the systems drive root
- ntvdm.exe (PID: 3016)
INFO
Reads the computer name
- wmpnscfg.exe (PID: 3284)
- curl.exe (PID: 1584)
- vc_redist.x64.exe (PID: 1088)
- VC_redist.x64.exe (PID: 2656)
- curl.exe (PID: 2860)
Checks supported languages
- wmpnscfg.exe (PID: 3284)
- curl.exe (PID: 1584)
- vc_redist.x64.exe (PID: 1088)
- VC_redist.x64.exe (PID: 2656)
- curl.exe (PID: 2860)
The sample compiled with english language support
- chrome.exe (PID: 1252)
- WinRAR.exe (PID: 3440)
- vc_redist.x64.exe (PID: 652)
- curl.exe (PID: 1584)
- VC_redist.x64.exe (PID: 2656)
- vc_redist.x64.exe (PID: 1088)
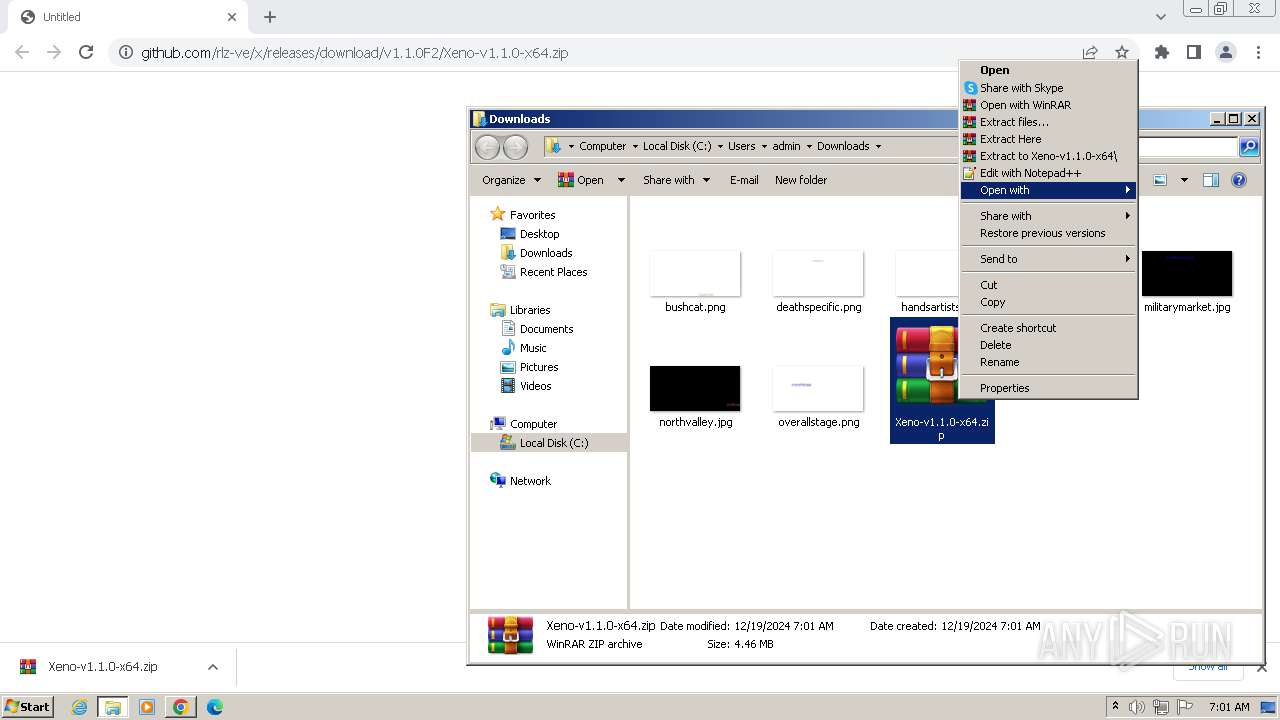
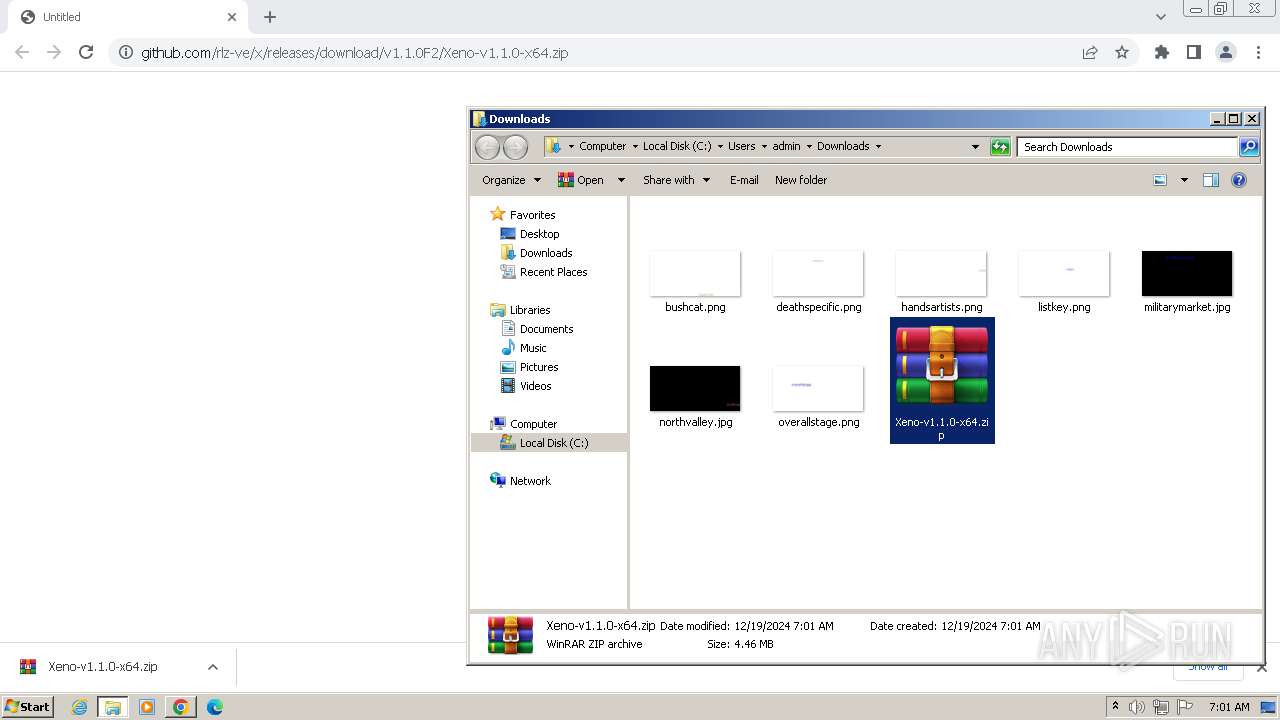
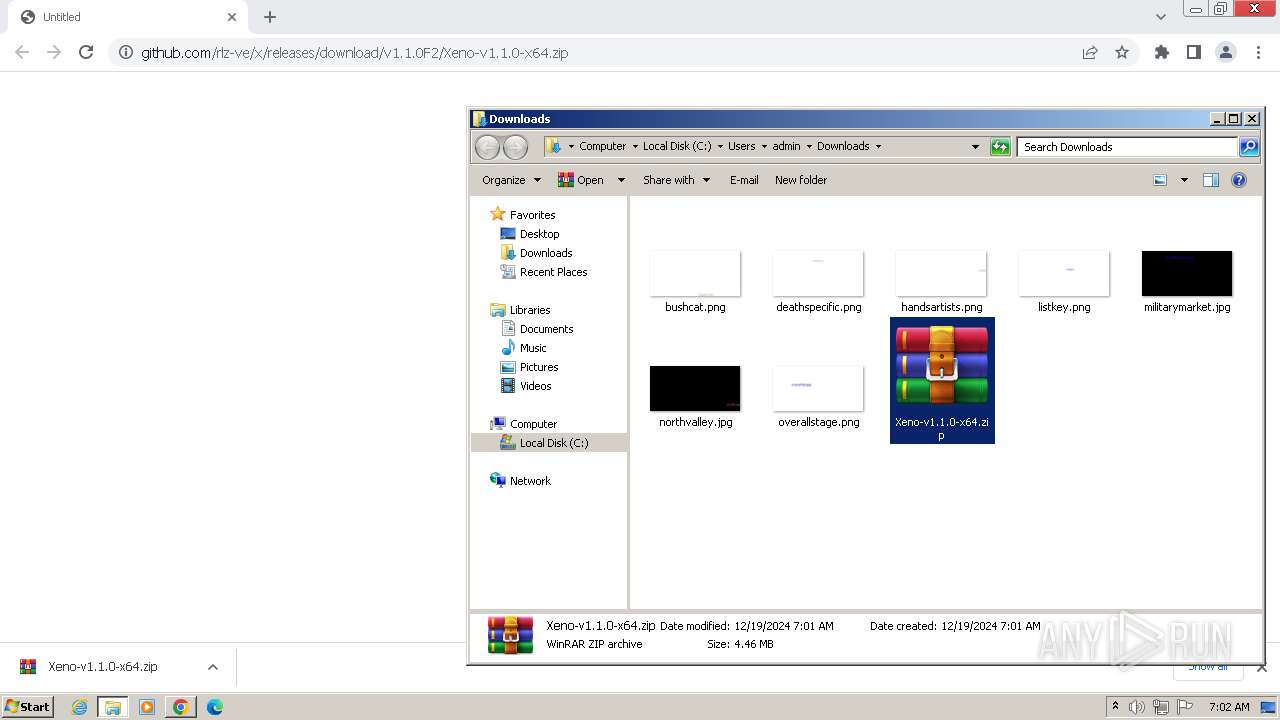
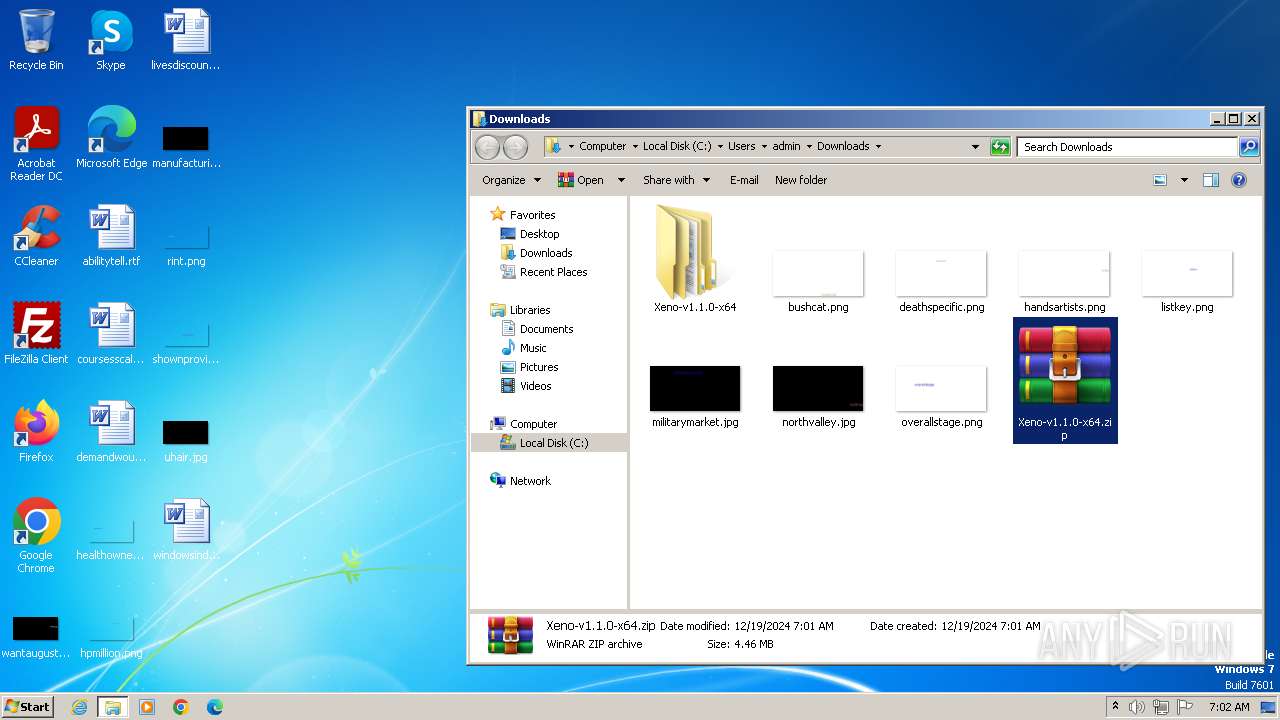
Manual execution by a user
- wmpnscfg.exe (PID: 3284)
- WinRAR.exe (PID: 3440)
- cmd.exe (PID: 3096)
Application launched itself
- chrome.exe (PID: 1252)
The process uses the downloaded file
- chrome.exe (PID: 3036)
- powershell.exe (PID: 3428)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3440)
Execution of CURL command
- cmd.exe (PID: 3928)
Reads the machine GUID from the registry
- vc_redist.x64.exe (PID: 1088)
- VC_redist.x64.exe (PID: 2656)
Create files in a temporary directory
- vc_redist.x64.exe (PID: 1088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
69
Monitored processes
29
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=2852 --field-trial-handle=1120,i,6889208691954434176,2081306673601018373,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 652 | vc_redist.x64.exe /quiet /norestart | C:\Windows\System32\vc_redist.x64.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.42.34433 Exit code: 0 Version: 14.42.34433.0 Modules
| |||||||||||||||
| 924 | C:\Windows\system32\net1 session | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1088 | "C:\Windows\Temp\{481553A3-5B99-47F0-BFF2-DF64EECEAFDD}\.cr\vc_redist.x64.exe" -burn.clean.room="C:\Windows\system32\vc_redist.x64.exe" -burn.filehandle.attached=288 -burn.filehandle.self=292 /quiet /norestart | C:\Windows\Temp\{481553A3-5B99-47F0-BFF2-DF64EECEAFDD}\.cr\vc_redist.x64.exe | vc_redist.x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.42.34433 Exit code: 0 Version: 14.42.34433.0 Modules
| |||||||||||||||
| 1096 | net session | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://github.com/rlz-ve/x/releases/download/v1.1.0F2/Xeno-v1.1.0-x64.zip" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6cb68b38,0x6cb68b48,0x6cb68b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1584 | curl -L -o vc_redist.x64.exe "https://aka.ms/vs/17/release/vc_redist.x64.exe" | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: HIGH Description: The curl executable Exit code: 0 Version: 8.5.0 Modules
| |||||||||||||||
| 1868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=1988 --field-trial-handle=1120,i,6889208691954434176,2081306673601018373,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1140 --field-trial-handle=1120,i,6889208691954434176,2081306673601018373,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
7 905
Read events
7 664
Write events
232
Delete events
9
Modification events
| (PID) Process: | (1252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1252) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
18
Suspicious files
64
Text files
82
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10882d.TMP | — | |
MD5:— | SHA256:— | |||
| 1252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF10882d.TMP | text | |
MD5:825B582C78EC88D54C215EFDF1EAD639 | SHA256:367995D01A8F13E5C30C79499F86B034775BFD009D83DC97635DE438D47DFA37 | |||
| 1252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:1C6BD9993E8ECB91342E78927D81DCA3 | SHA256:76BE6BB39D2B3287BCBBCF6465599F0CF66FE5B9F4F55D10ED38B0BCF1A4BEC3 | |||
| 1252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 1252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF10881d.TMP | text | |
MD5:456D3EF989973A7C218E338A6CFFAD25 | SHA256:75631D994431F254B94255C50038A3657BFC45D76FCE9D794D514E57CA678872 | |||
| 1252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF108b0b.TMP | text | |
MD5:FF6BABA737D50E515029C3F3A1305BBC | SHA256:670EED15EAA8E3F1A4F8612B229654EB0C64107AEAF0B1017E4BD45E3F7EED83 | |||
| 1252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF108e86.TMP | — | |
MD5:— | SHA256:— | |||
| 1252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF108a40.TMP | text | |
MD5:FA25AF7098FC1571F24F200A9D105D58 | SHA256:4F40C87070B7A151FB241CCF36E7027AA703C15CA0ACB0A1759DA07B2C318574 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
15
DNS requests
14
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1108 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
1252 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2280 | chrome.exe | 140.82.121.4:443 | github.com | GITHUB | US | shared |
2280 | chrome.exe | 142.251.173.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
2280 | chrome.exe | 185.199.111.133:443 | objects.githubusercontent.com | FASTLY | US | shared |
1252 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
2280 | chrome.exe | 216.58.206.78:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
github.com |
| shared |
accounts.google.com |
| whitelisted |
objects.githubusercontent.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| whitelisted |
aka.ms |
| whitelisted |
download.visualstudio.microsoft.com |
| whitelisted |
dotnet.microsoft.com |
| whitelisted |