| File name: | sample.exe |
| Full analysis: | https://app.any.run/tasks/f1fd17b4-85c7-45b3-b4d7-9e3c72e1cb02 |
| Verdict: | Malicious activity |
| Analysis date: | May 09, 2019, 07:05:12 |
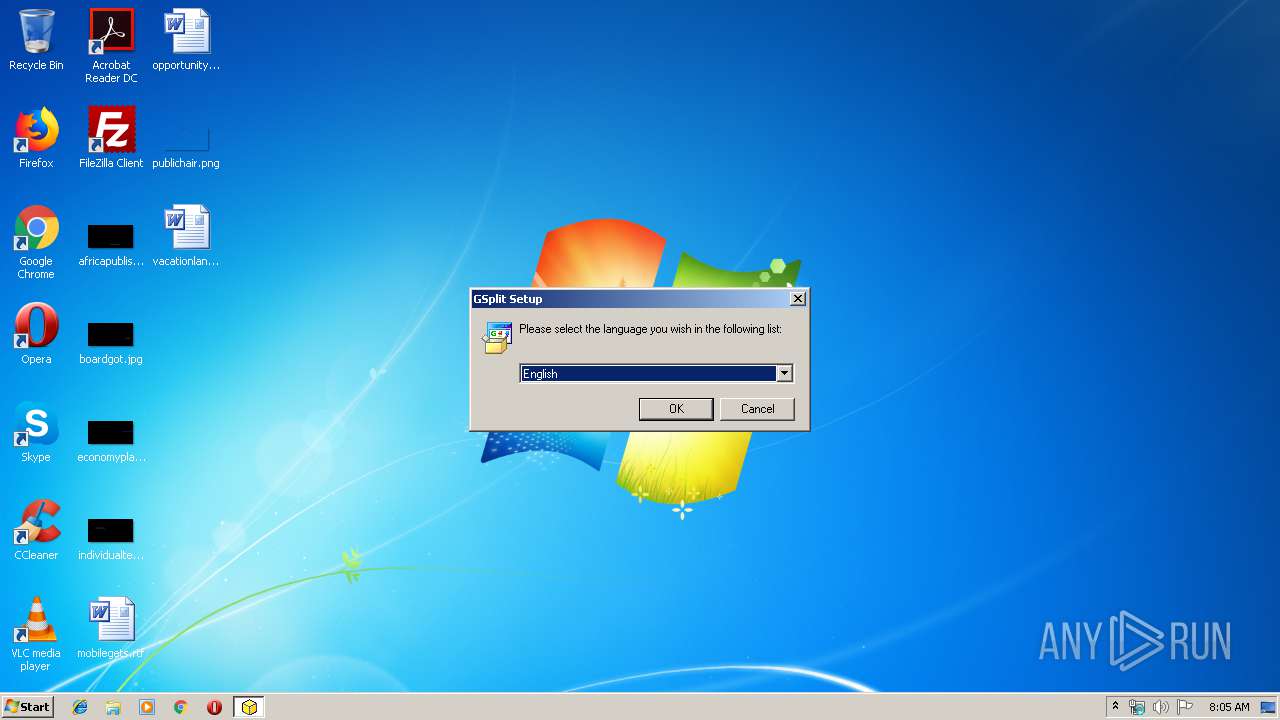
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DE1726040A5232BD5A670A749CCEC2A4 |
| SHA1: | 0AD5BA1390310214924B38B2E273424CBDB3143C |
| SHA256: | FDEDE876D7E64EFB35AAC18E18B27046E5F7C5139D6547FD385383F6838E4C11 |
| SSDEEP: | 24576:nXiUj+K7sRPdGGcypjeF/7fPyvmuYUYVxT+MNxEDF8rUoLP4GvexMv1RZuPHDG5b:HSKQhd+ypMfarPQ7PEDFCNTVv1RZcD2b |
MALICIOUS
Loads dropped or rewritten executable
- sample.exe (PID: 2108)
Application was dropped or rewritten from another process
- Uninst.exe (PID: 3392)
- GSplit.exe (PID: 2676)
SUSPICIOUS
Executable content was dropped or overwritten
- sample.exe (PID: 2108)
- Uninst.exe (PID: 3392)
- GSplit.exe (PID: 2676)
Creates COM task schedule object
- sample.exe (PID: 2108)
Creates files in the program directory
- Uninst.exe (PID: 3392)
- sample.exe (PID: 2108)
Creates a software uninstall entry
- sample.exe (PID: 2108)
Creates files in the user directory
- GSplit.exe (PID: 2676)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 9216 |
| InitializedDataSize: | 199680 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3274 |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.1.0 |
| ProductVersionNumber: | 3.0.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
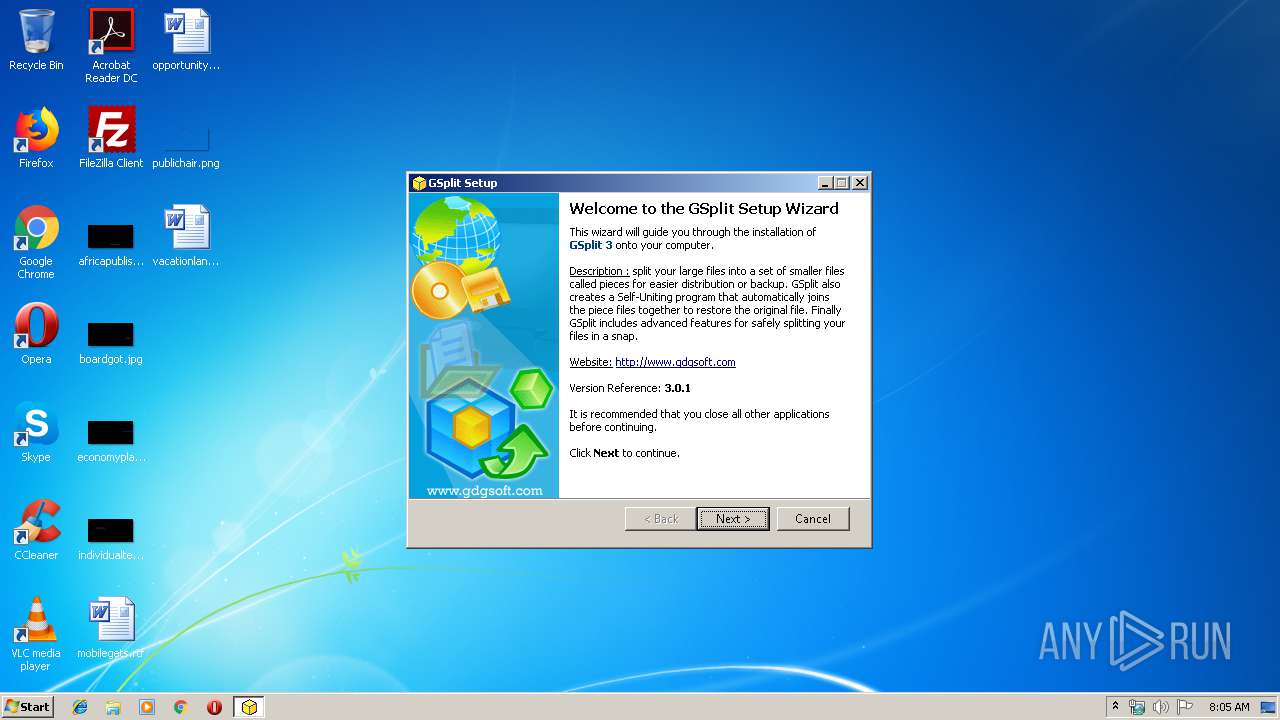
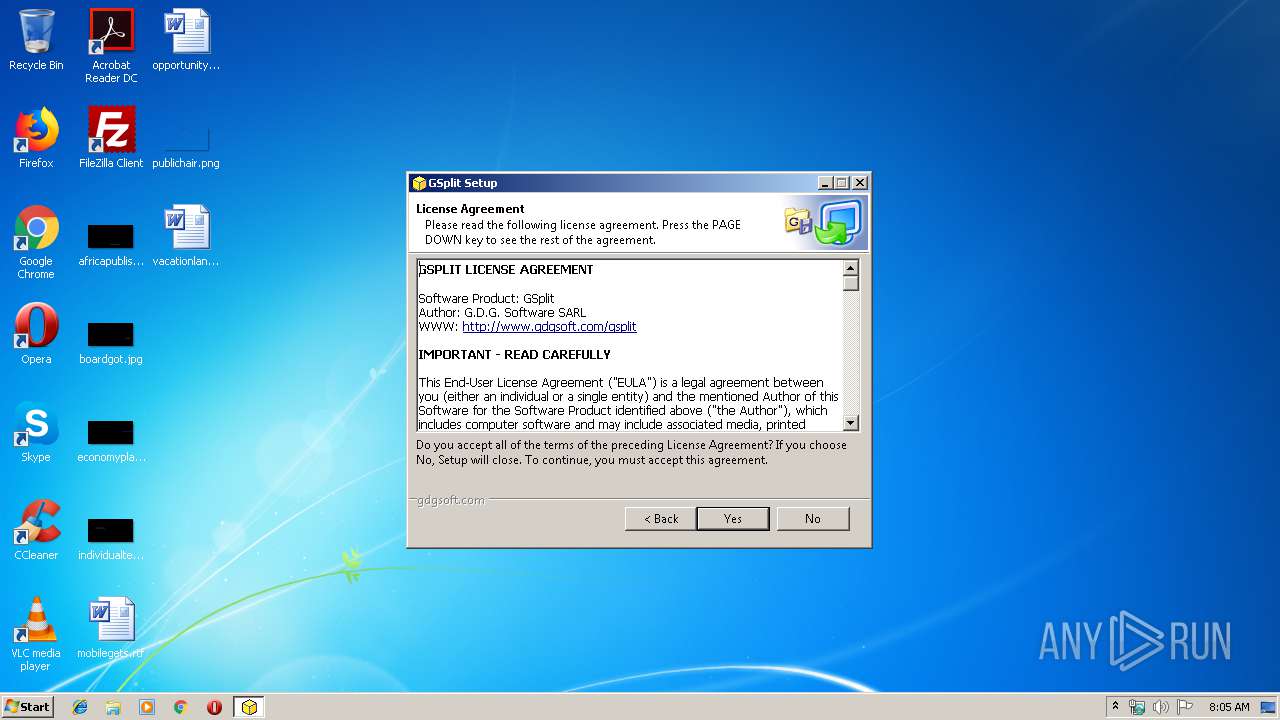
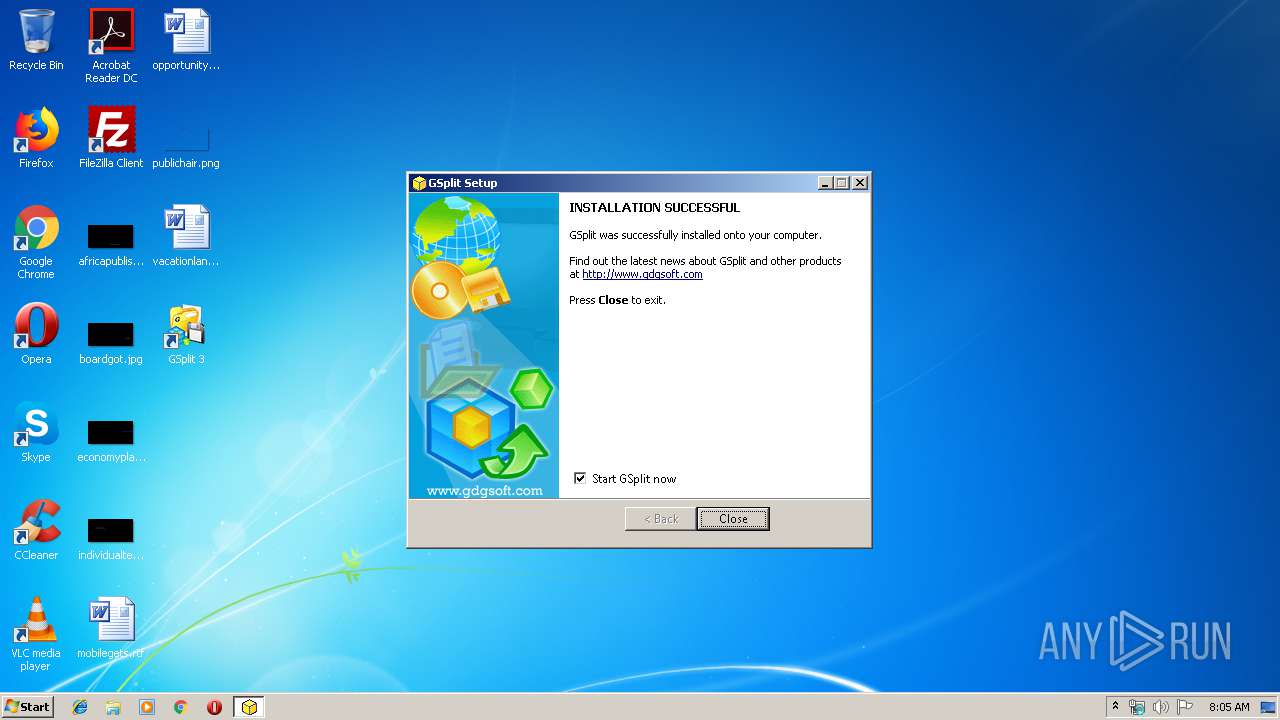
| FileDescription: | GSplit Self-Installing Package |
| FileVersion: | 2.0.1.0 |
| LegalCopyright: | Copyright © G.D.G Software 2006-2009. All rights reserved. |
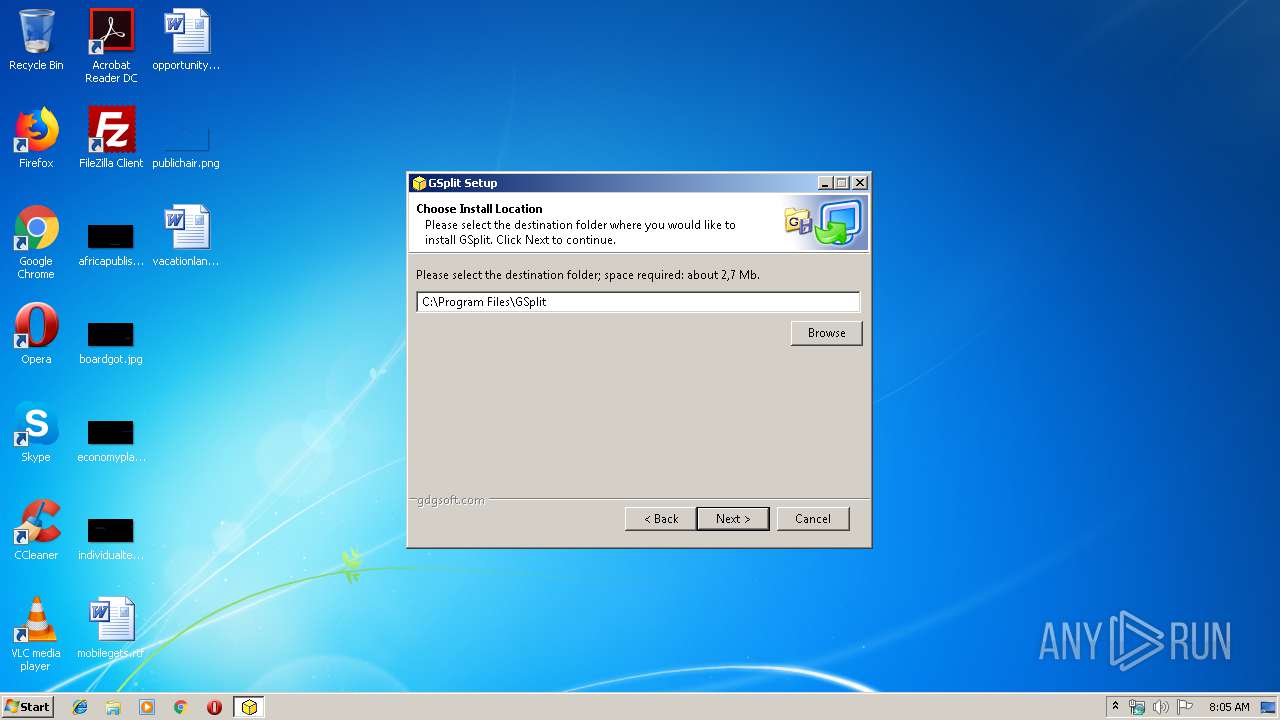
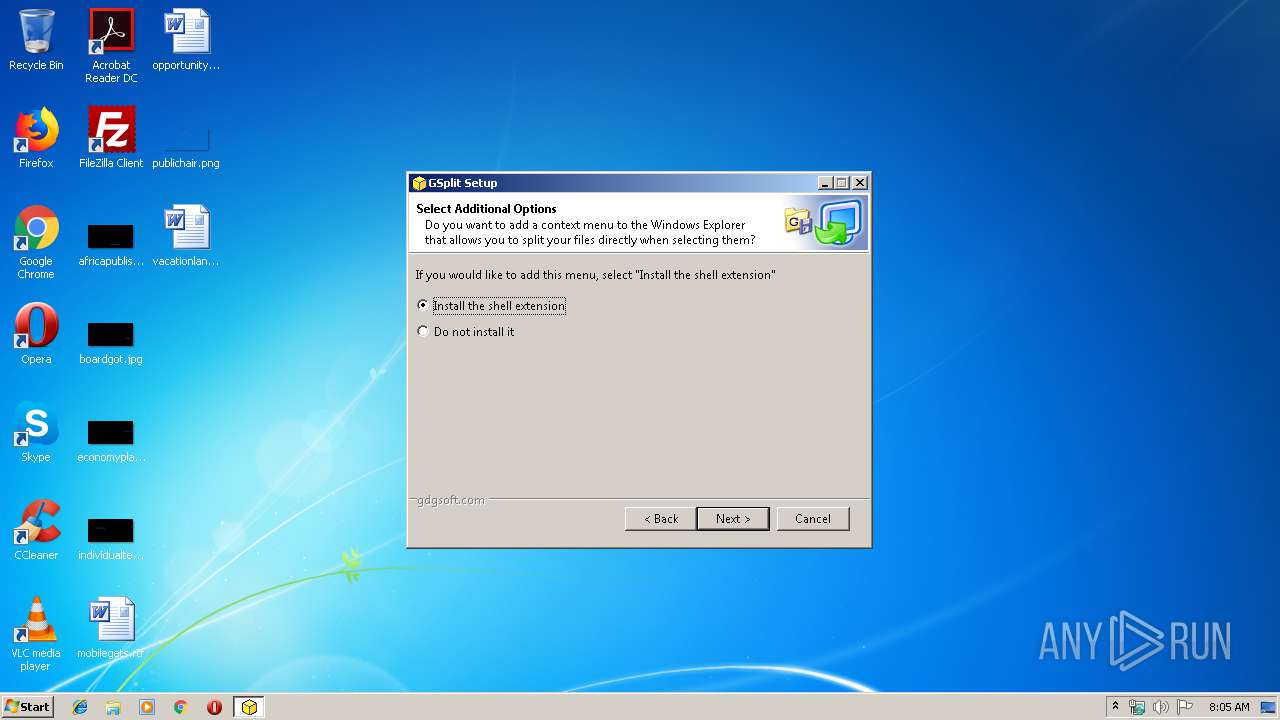
| ProductName: | GSplit Setup |
| ProductVersion: | 3.0.1.0 |
| Web: | http://www.gdgsoft.com |
| CompanyName: | G.D.G. Software, info@gdgsoft.com |
| Comments: | This program will install GSplit 3, file splitter for Windows. |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| FileDescription: | GSplit Self-Installing Package |
| FileVersion: | 2.0.1.0 |
| LegalCopyright: | Copyright © G.D.G Software 2006-2009. All rights reserved. |
| ProductName: | GSplit Setup |
| ProductVersion: | 3.0.1.0 |
| Web: | http://www.gdgsoft.com |
| CompanyName: | G.D.G. Software, info@gdgsoft.com |
| Comments: | This program will install GSplit 3, file splitter for Windows. |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00002298 | 0x00002400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37966 |
DATA | 0x00004000 | 0x0000007C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.936741 |
BSS | 0x00005000 | 0x00000085 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00006000 | 0x0000038C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.93619 |
.tls | 0x00007000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00008000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00009000 | 0x00000214 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 3.93882 |
.rsrc | 0x0000A000 | 0x0002FFB8 | 0x00030000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 7.97459 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.12097 | 709 | UNKNOWN | English - United States | RT_MANIFEST |
50 | 3.07064 | 296 | UNKNOWN | UNKNOWN | RT_ICON |
51 | 3.81154 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
52 | 3.71558 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
53 | 3.52223 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
ENG | 7.99904 | 189604 | UNKNOWN | English - United States | RT_RCDATA |
MAINICON | 2.79716 | 62 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
comctl32.dll |
kernel32.dll |
user32.dll |
Total processes
37
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
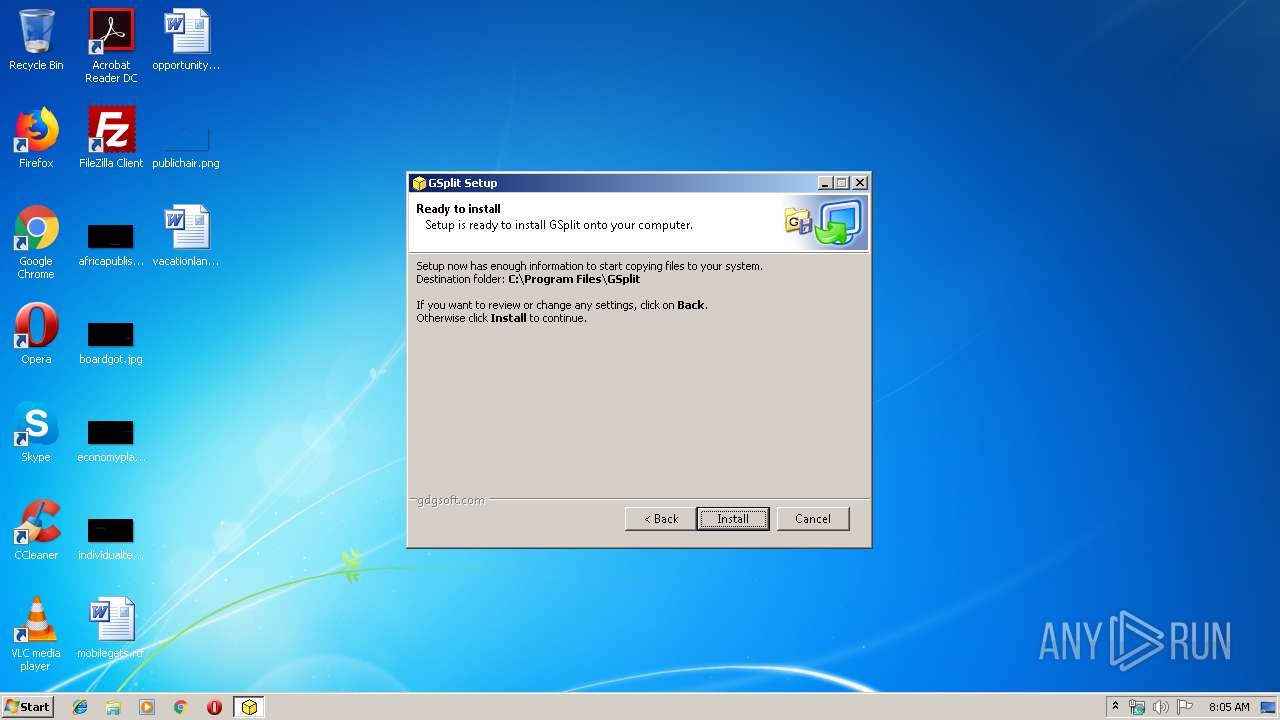
| 2108 | "C:\Users\admin\AppData\Local\Temp\sample.exe" | C:\Users\admin\AppData\Local\Temp\sample.exe | explorer.exe | ||||||||||||
User: admin Company: G.D.G. Software, info@gdgsoft.com Integrity Level: HIGH Description: GSplit Self-Installing Package Exit code: 0 Version: 2.0.1.0 Modules
| |||||||||||||||
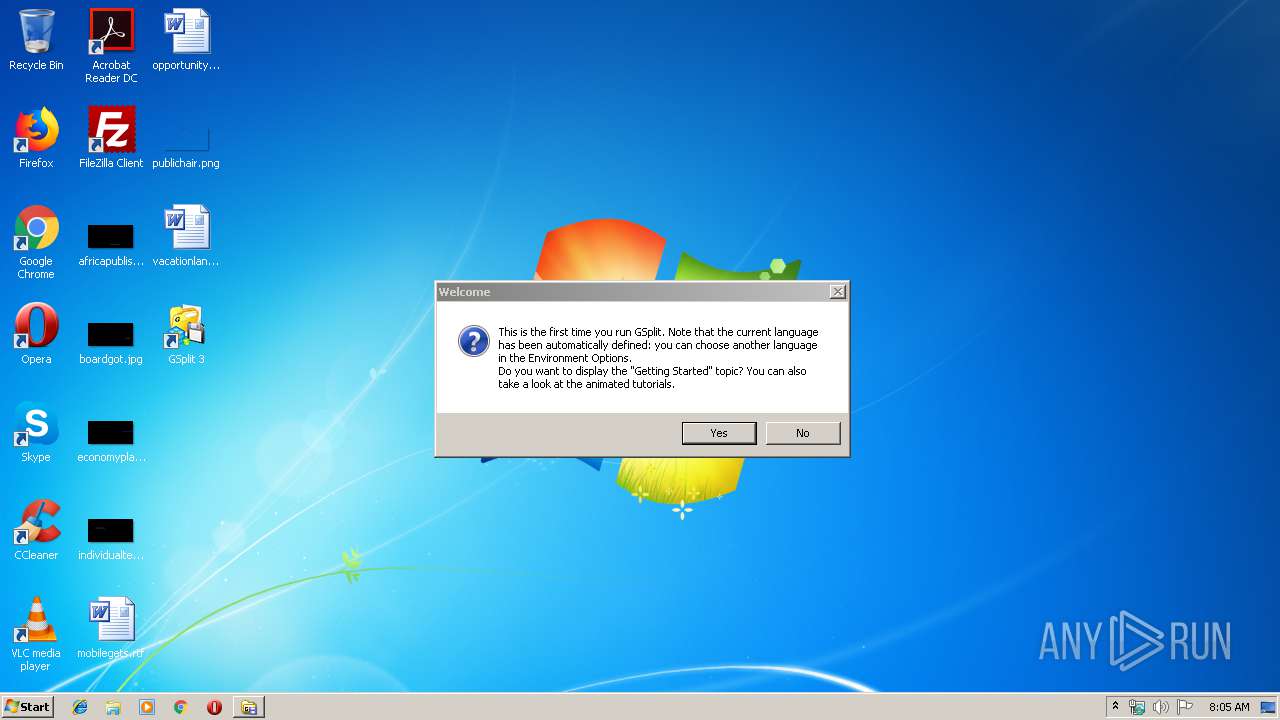
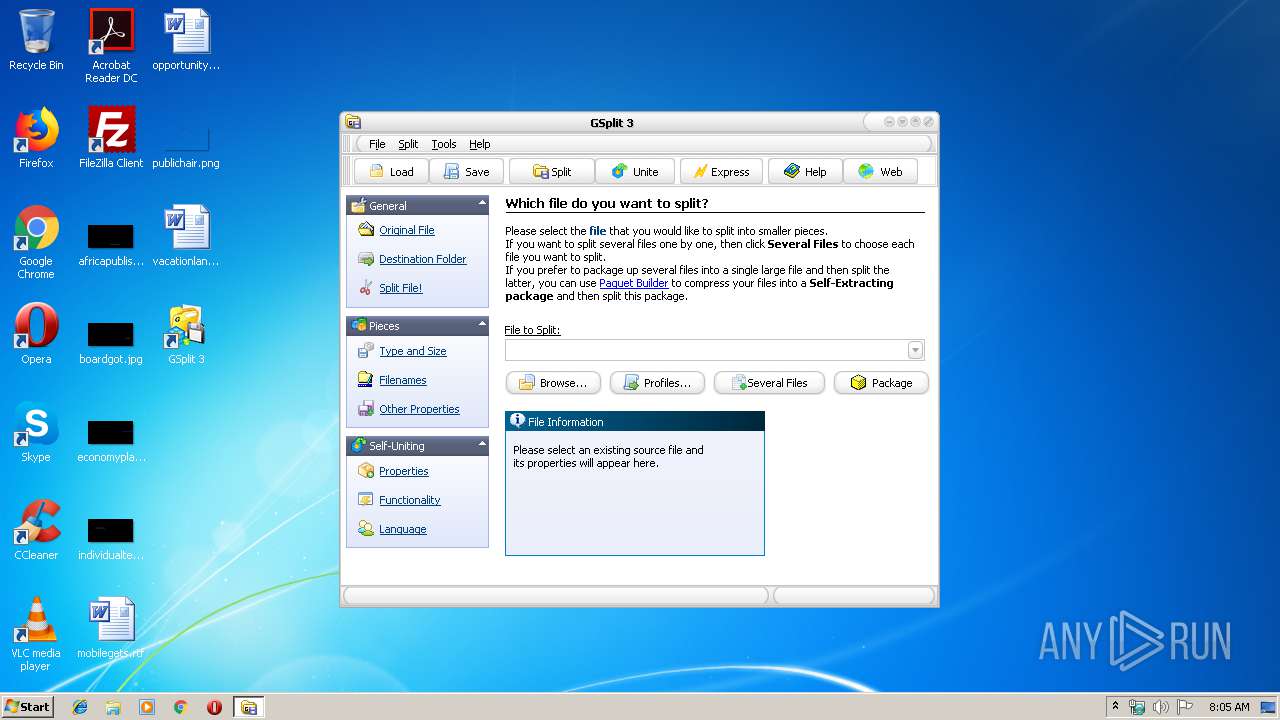
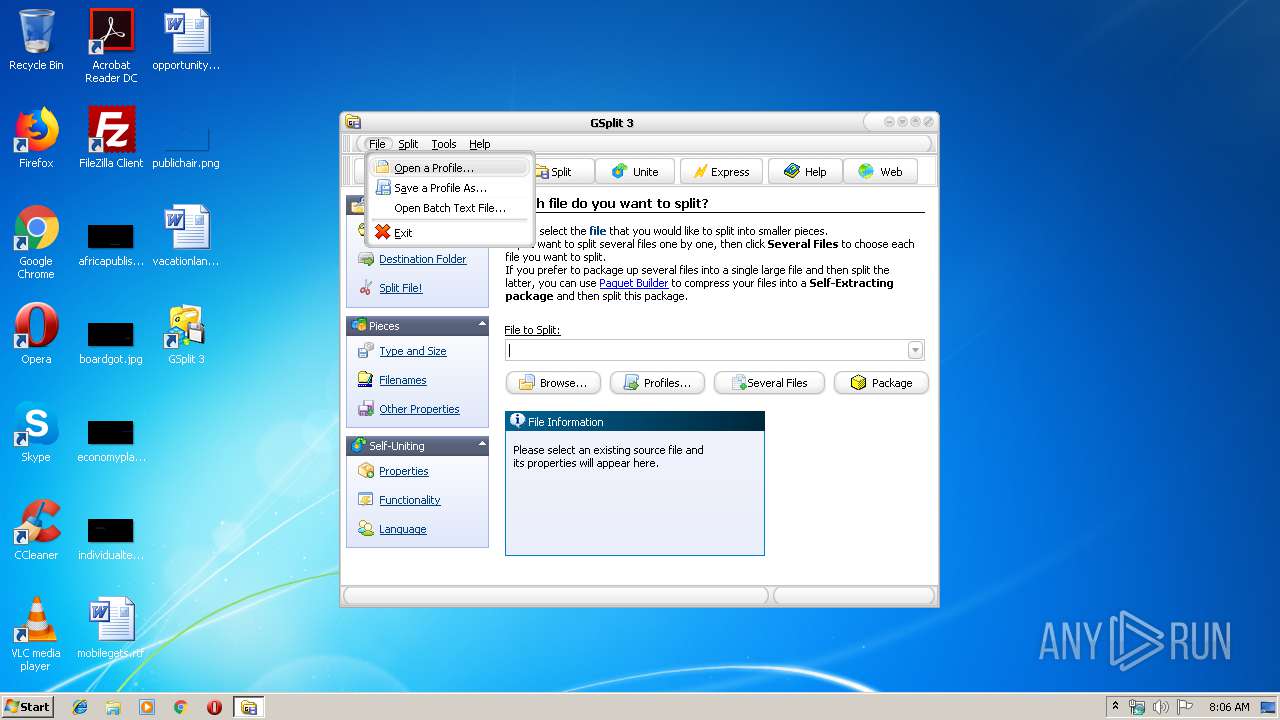
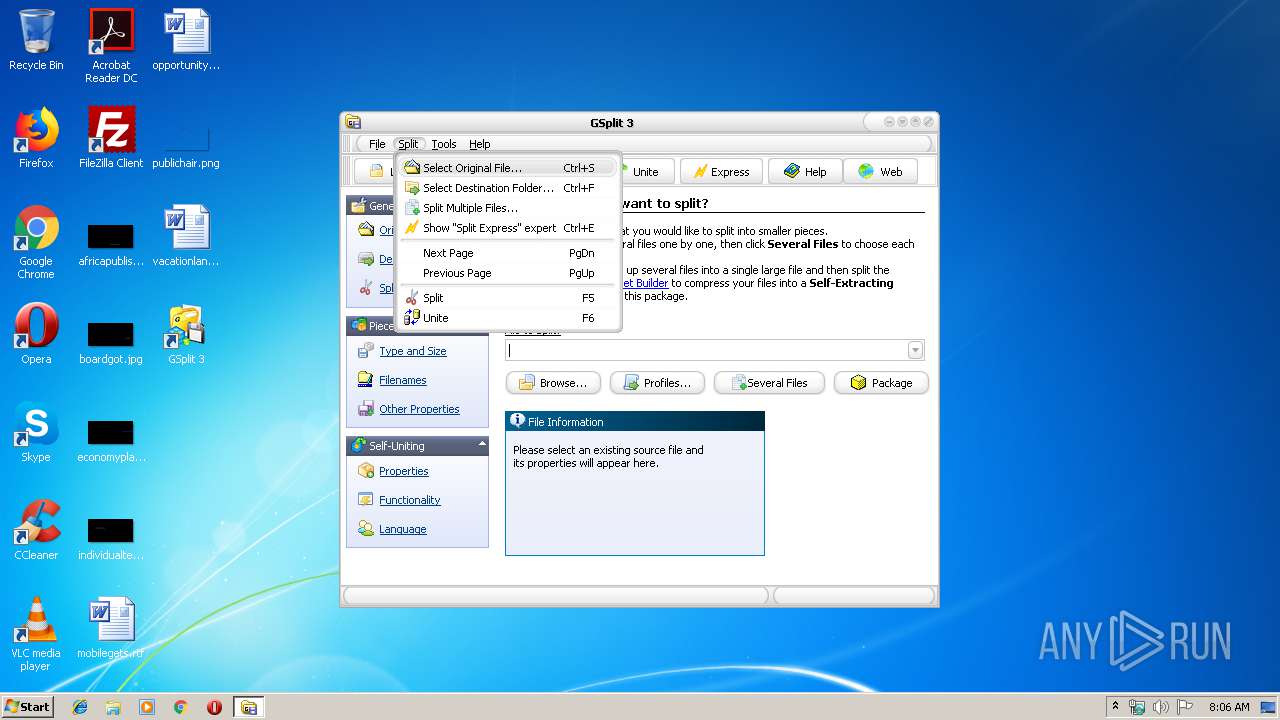
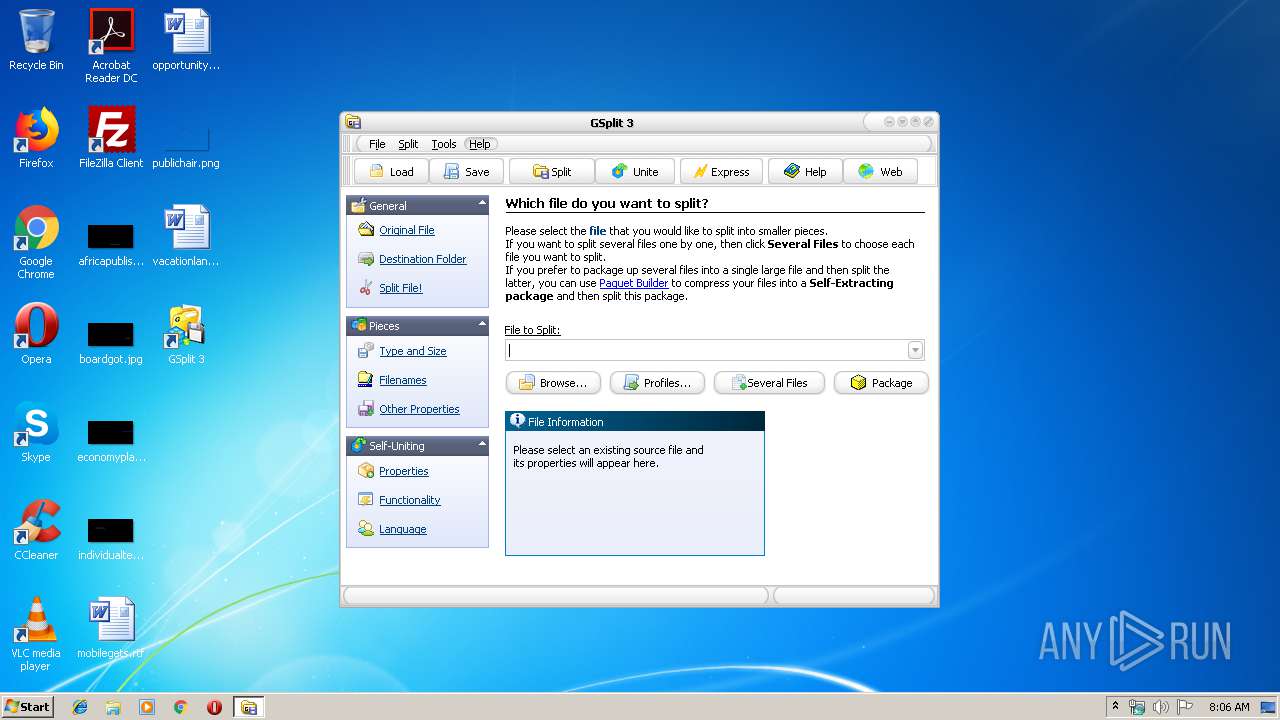
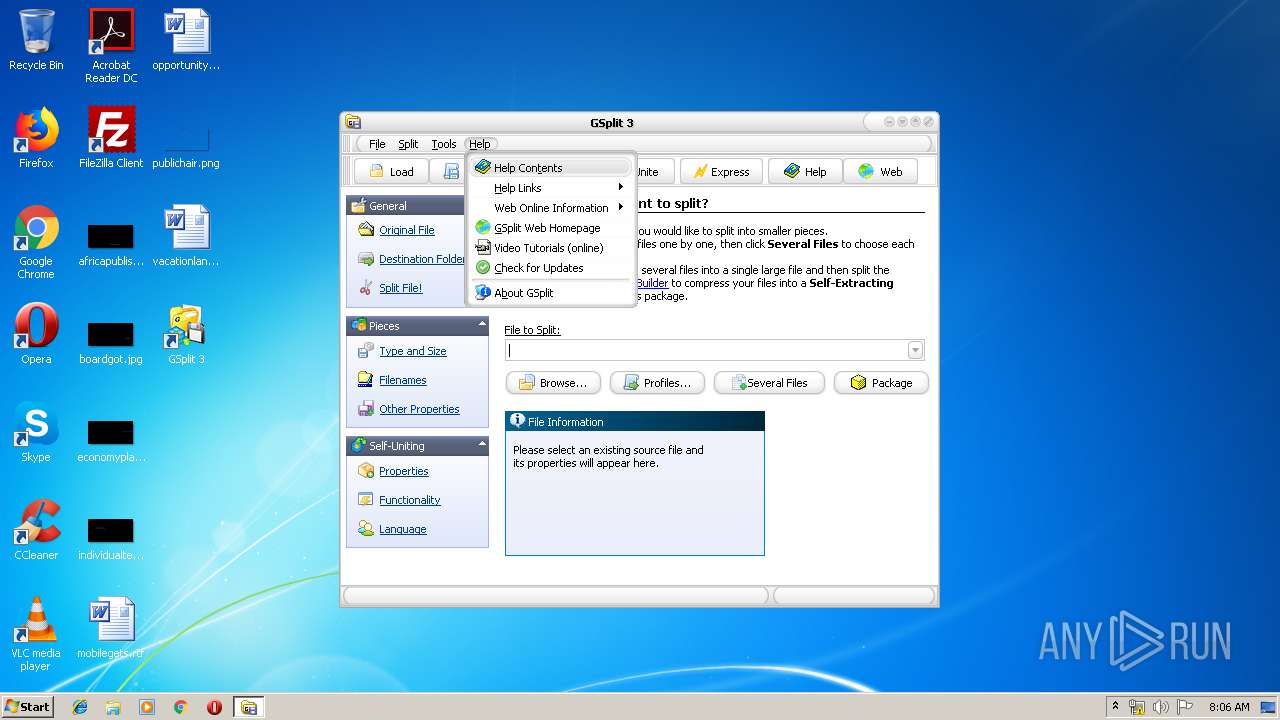
| 2676 | "C:\Program Files\GSplit\GSplit.exe" | C:\Program Files\GSplit\GSplit.exe | sample.exe | ||||||||||||
User: admin Company: G.D.G. Software Integrity Level: HIGH Description: GSplit: file splitter Exit code: 5 Version: 3.0.1.0 Modules
| |||||||||||||||
| 2960 | "C:\Users\admin\AppData\Local\Temp\sample.exe" | C:\Users\admin\AppData\Local\Temp\sample.exe | — | explorer.exe | |||||||||||
User: admin Company: G.D.G. Software, info@gdgsoft.com Integrity Level: MEDIUM Description: GSplit Self-Installing Package Exit code: 3221226540 Version: 2.0.1.0 Modules
| |||||||||||||||
| 3392 | "C:\Program Files\GSplit\Uninst.exe" /RUNP | C:\Program Files\GSplit\Uninst.exe | sample.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Paquet Builder - Package Uninstaller Exit code: 0 Version: 1, 6, 0, 0 Modules
| |||||||||||||||
Total events
294
Read events
270
Write events
24
Delete events
0
Modification events
| (PID) Process: | (2108) sample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\GSplit.exe |
| Operation: | write | Name: | |
Value: C:\Program Files\GSplit\GSplit.exe | |||
| (PID) Process: | (2108) sample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\GSplit.exe |
| Operation: | write | Name: | Path |
Value: C:\Program Files\GSplit | |||
| (PID) Process: | (2108) sample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GSplit |
| Operation: | write | Name: | Path |
Value: C:\Program Files\GSplit\GSplit.exe | |||
| (PID) Process: | (2108) sample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GSplit |
| Operation: | write | Name: | InstallPath |
Value: C:\Program Files\GSplit | |||
| (PID) Process: | (2108) sample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GSplit |
| Operation: | write | Name: | Version |
Value: 3.0.1 | |||
| (PID) Process: | (2108) sample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GSplit |
| Operation: | write | Name: | Vernum |
Value: 30010 | |||
| (PID) Process: | (2108) sample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Program Files\Common Files\GSplit\gspshell.dll |
Value: 1 | |||
| (PID) Process: | (2108) sample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{B46C1E0F-F61D-4B19-BC55-B68D8BB3CAFE} |
| Operation: | write | Name: | |
Value: GSplit Context Menu Shell Extension | |||
| (PID) Process: | (2108) sample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{B46C1E0F-F61D-4B19-BC55-B68D8BB3CAFE}\InprocServer32 |
| Operation: | write | Name: | |
Value: C:\Program Files\Common Files\GSplit\gspshell.dll | |||
| (PID) Process: | (2108) sample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{B46C1E0F-F61D-4B19-BC55-B68D8BB3CAFE}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
Executable files
8
Suspicious files
1
Text files
4
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2108 | sample.exe | C:\Users\admin\AppData\Local\Temp\pb3F8E.tmp | — | |
MD5:— | SHA256:— | |||
| 2108 | sample.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\GSplit 3\Web Homepage.lnk | lnk | |
MD5:— | SHA256:— | |||
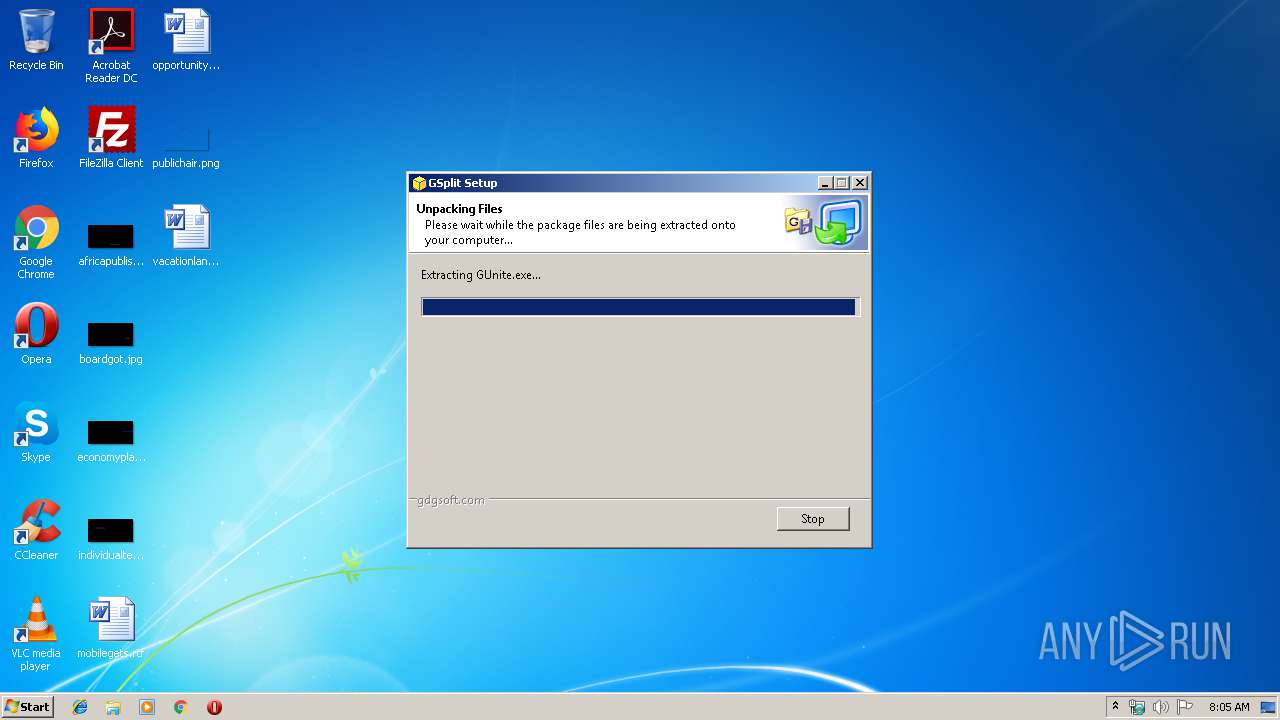
| 2108 | sample.exe | C:\Program Files\GSplit\GUnite.exe | executable | |
MD5:0910FB5A36662CCD6586AA16F9FA6A88 | SHA256:48D7BD4ECD376DDFF9C8579DCD0B7C70A5D80EF2841818338237157E0C1C23D5 | |||
| 2108 | sample.exe | C:\Program Files\GSplit\GSplit.exe | executable | |
MD5:BC2C0ABA76B32F90F9FFB00DBCDDC7AC | SHA256:2248E9C4D68851D38B9C219029CE82E0BCD54BAEB435E1C3044BDF33A2BC24BD | |||
| 2108 | sample.exe | C:\Program Files\Common Files\GSplit\gspshell.dll | executable | |
MD5:5F694D247A12D61A6BAF60F80D92CCE2 | SHA256:056B716B1E104142D0E125EEA7142DE0B889D15F0CBB4A1F5CA7FD6D6482898B | |||
| 2108 | sample.exe | C:\Program Files\GSplit\Skins\WinXPBlue.skn | binary | |
MD5:6C65344F2E750B7EC2A92ABCD1E98A16 | SHA256:2DD83579EFDD1A0ABC1DE440B72E2AC685DA77A2F8EA9B347DD9E381D1DE372E | |||
| 2108 | sample.exe | C:\Program Files\GSplit\Uninst.log | bs | |
MD5:— | SHA256:— | |||
| 2108 | sample.exe | C:\Program Files\GSplit\gdefval.inf | text | |
MD5:EE42B5479165D8B813BC58BFCAA262B7 | SHA256:8472D64A8E9DA79625B355448CF2BB411F6C90024E9427AA56EBA26F1C3425DC | |||
| 2108 | sample.exe | C:\Program Files\GSplit\homepage.url | text | |
MD5:7BC2428202AD440151DBF6EB3622E7BC | SHA256:8891398F7E6DBED305E4B41B8392FCC71030ABC08CBCB44444EC011FFF7DB4F0 | |||
| 2108 | sample.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\GSplit 3\Documentation.lnk | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report