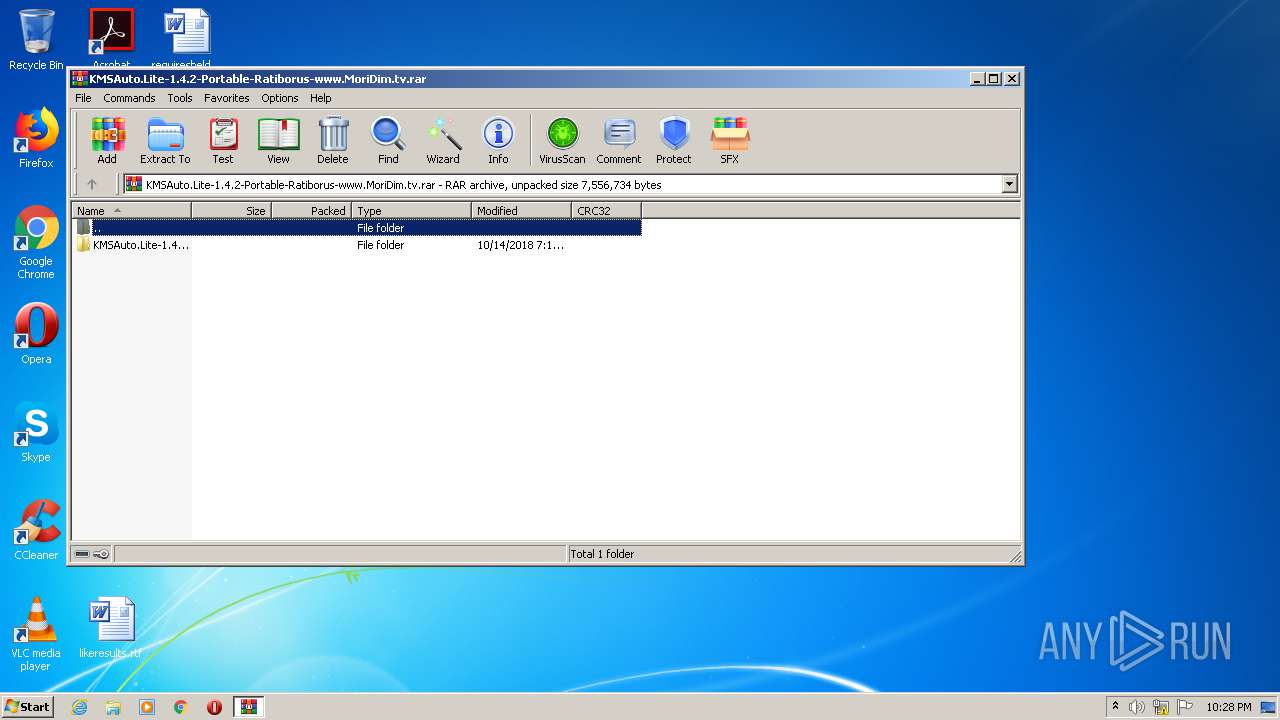
| File name: | KMSAuto.Lite-1.4.2-Portable-Ratiborus-www.MoriDim.tv.rar |
| Full analysis: | https://app.any.run/tasks/0912c6da-0340-4580-952c-b245b8ae0305 |
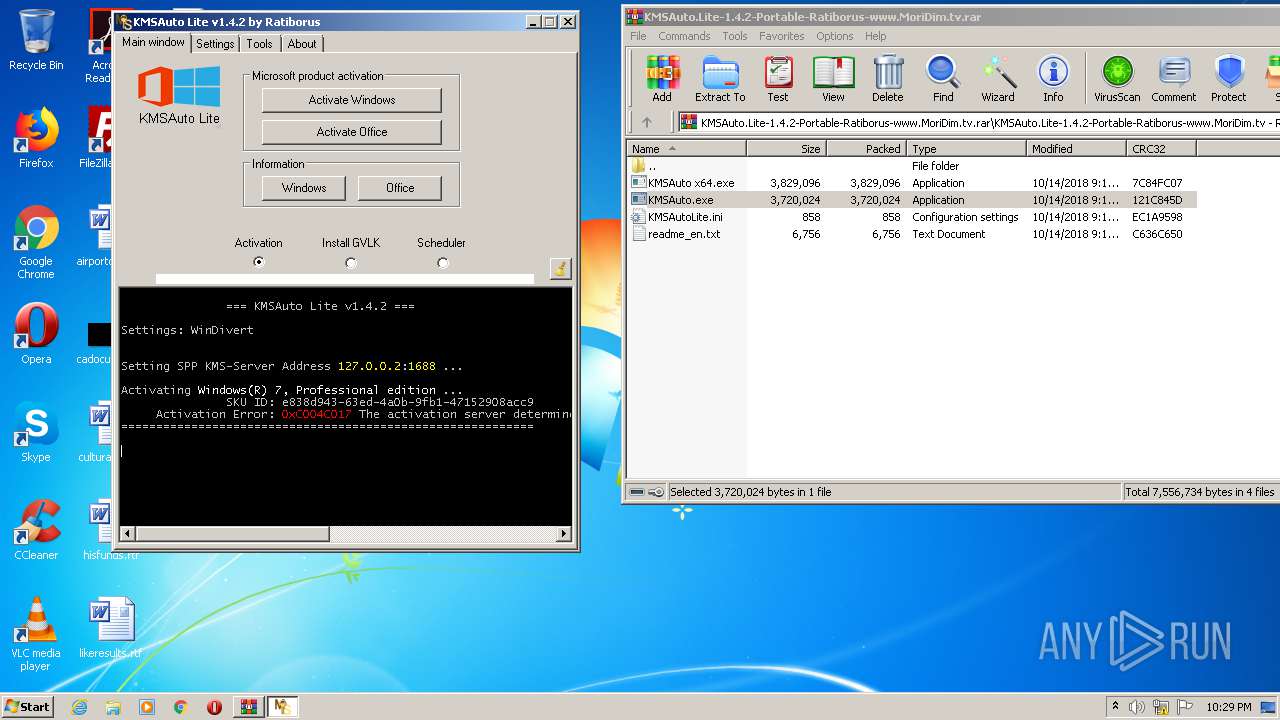
| Verdict: | Malicious activity |
| Analysis date: | November 19, 2020, 22:28:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 27ADD1B5EE51365728DF592D1CD2019A |
| SHA1: | A179A84B931DF98547A2859A93C1A05A1986BF54 |
| SHA256: | FDEBB44A4F6730EA09C68E523857E3B14F7F55DD9CD897FC4AD60BE90F74448B |
| SSDEEP: | 196608:ekF1T9H3knif1tQzy8mCeGhmb1D4VOyJAUF1v6b+xMG:ekFVQ2x8te/1DCF1vRMG |
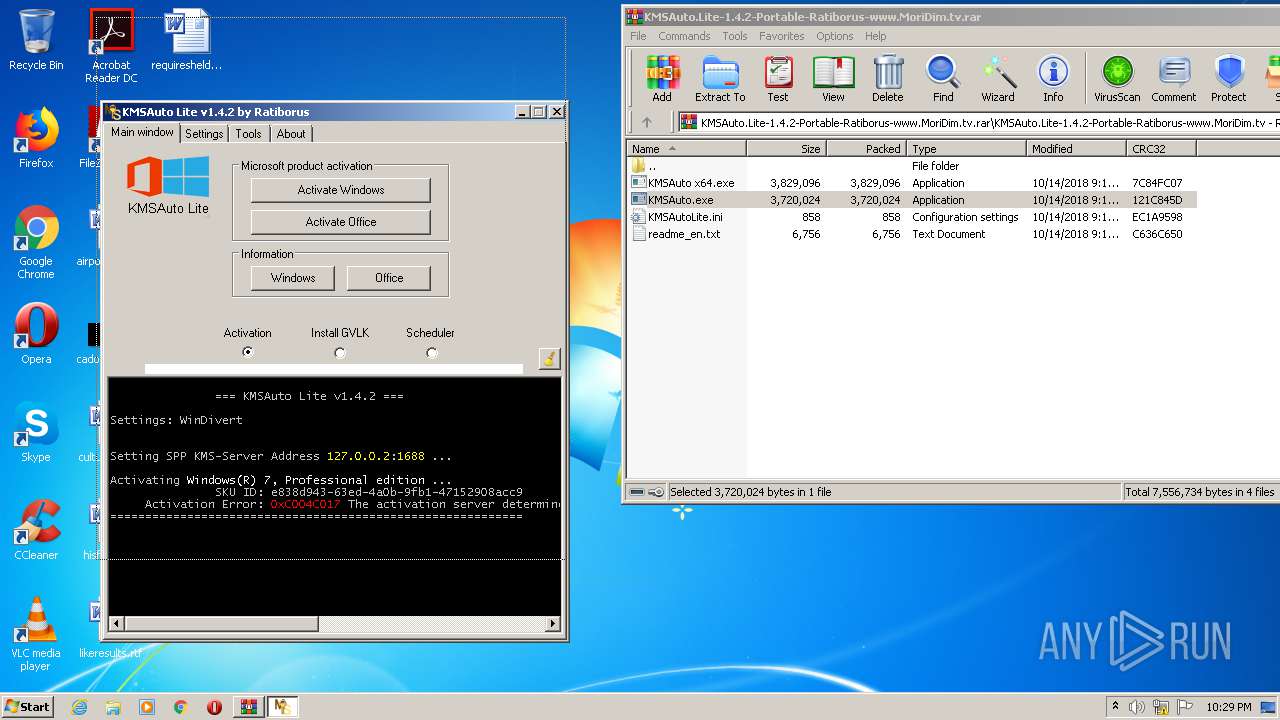
MALICIOUS
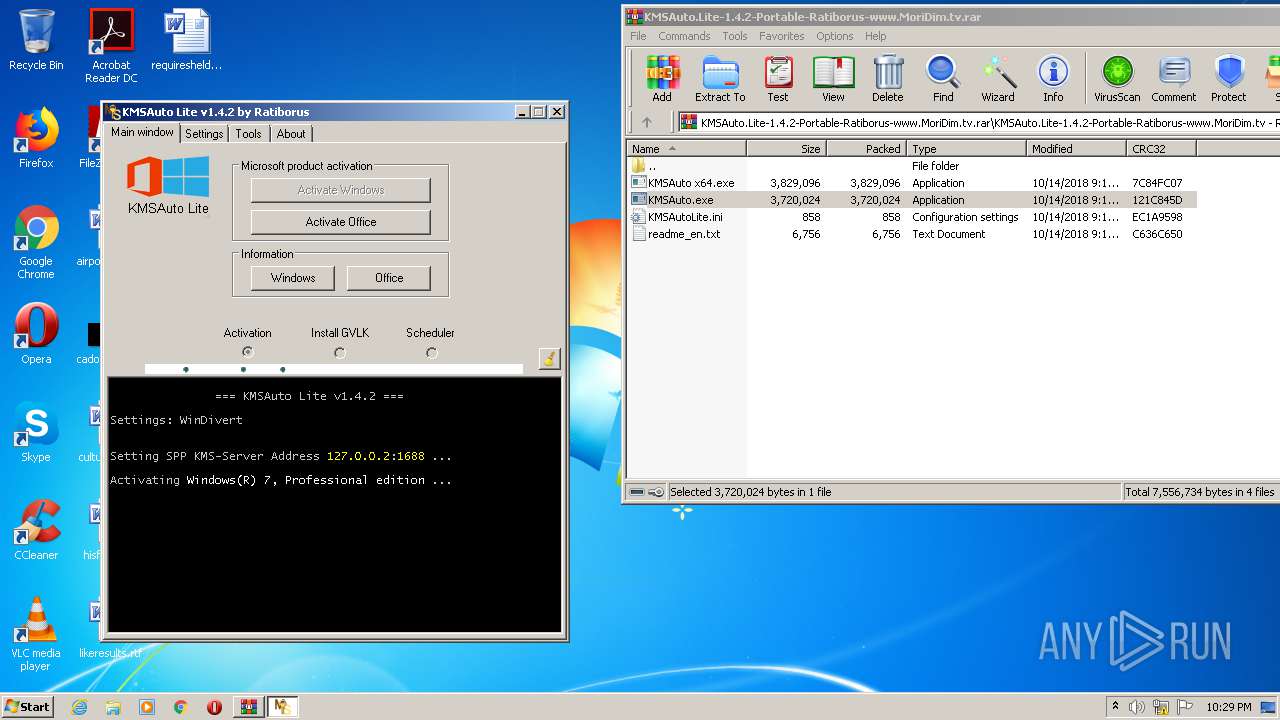
Application was dropped or rewritten from another process
- KMSAuto.exe (PID: 2868)
- KMSAuto.exe (PID: 1868)
- KMSSS.exe (PID: 2144)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1252)
- KMSAuto.exe (PID: 2868)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 748)
- KMSAuto.exe (PID: 2868)
- cmd.exe (PID: 2600)
- cmd.exe (PID: 3456)
- cmd.exe (PID: 620)
Starts SC.EXE for service management
- cmd.exe (PID: 2840)
- cmd.exe (PID: 2980)
- cmd.exe (PID: 4032)
- cmd.exe (PID: 2956)
Creates files in the Windows directory
- KMSAuto.exe (PID: 2868)
- KMSSS.exe (PID: 2144)
Starts CMD.EXE for commands execution
- KMSAuto.exe (PID: 2868)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 2828)
- cmd.exe (PID: 308)
- cmd.exe (PID: 4092)
- cmd.exe (PID: 2036)
- cmd.exe (PID: 2232)
- cmd.exe (PID: 976)
Executes scripts
- cmd.exe (PID: 1932)
- cmd.exe (PID: 2160)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 1332)
Creates or modifies windows services
- KMSAuto.exe (PID: 2868)
Removes files from Windows directory
- KMSAuto.exe (PID: 2868)
Executed as Windows Service
- KMSSS.exe (PID: 2144)
INFO
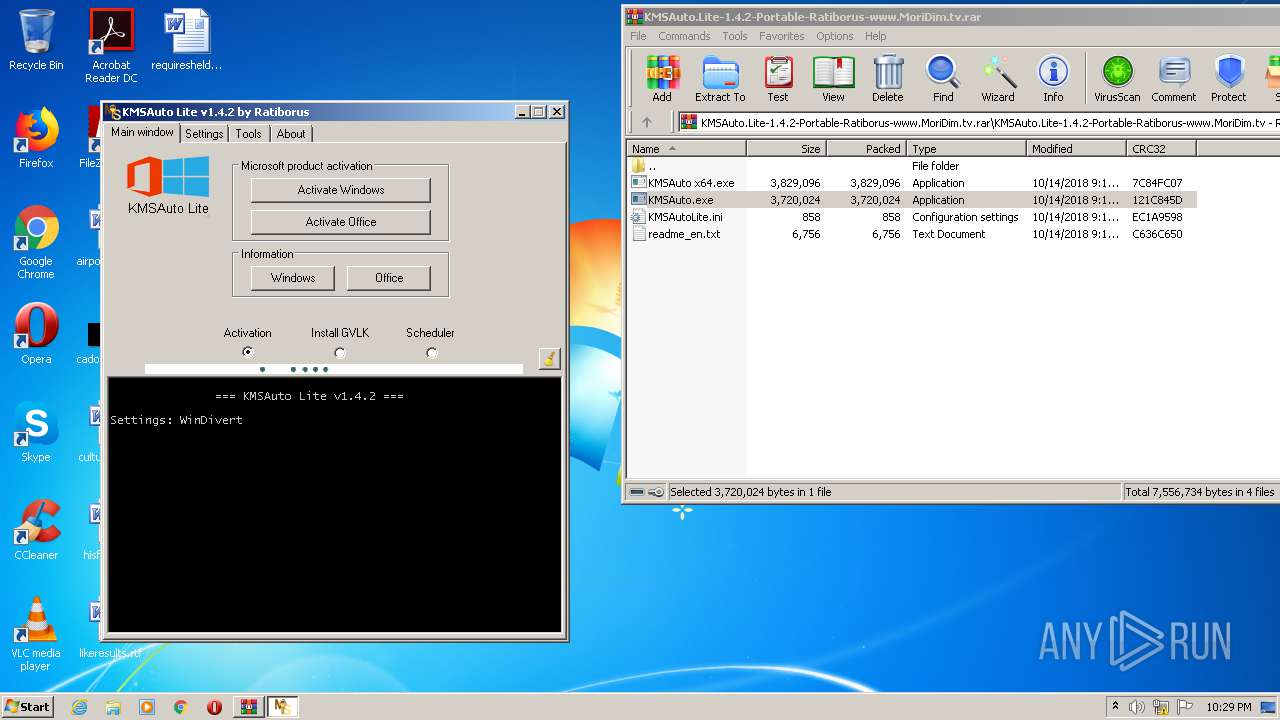
Manual execution by user
- KMSAuto.exe (PID: 1868)
- KMSAuto.exe (PID: 2868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
98
Monitored processes
40
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Windows\System32\cmd.exe" /c Netsh.exe Advfirewall Firewall delete rule name=0pen_Port_KMS protocol=TCP | C:\Windows\System32\cmd.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 620 | "C:\Windows\System32\cmd.exe" /c reg.exe add "HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform" /f /v KeyManagementServicePort /d 1688 /t REG_SZ /reg:64 | C:\Windows\System32\cmd.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 748 | "C:\Windows\System32\cmd.exe" /c reg.exe add "HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform" /f /v KeyManagementServiceName /d 127.0.0.2 /t REG_SZ /reg:32 | C:\Windows\System32\cmd.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 976 | "C:\Windows\System32\cmd.exe" /c Netsh.exe Advfirewall Firewall add rule name=0pen_Port_KMS dir=in action=allow protocol=TCP localport=1688 | C:\Windows\System32\cmd.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1032 | cscript //nologo "C:\Users\admin\AppData\Local\Temp\slmgr.vbs" /ato | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 3221536791 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1240 | reg.exe add "HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform" /f /v KeyManagementServicePort /d 1688 /t REG_SZ /reg:32 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1252 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\KMSAuto.Lite-1.4.2-Portable-Ratiborus-www.MoriDim.tv.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1256 | sc.exe start KMSEmulator | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1332 | "C:\Windows\System32\cmd.exe" /c wmic path SoftwareLicensingProduct where (Name LIKE 'Windows%%' And PartialProductKey is Not NULL) get Name /FORMAT:List | C:\Windows\System32\cmd.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1688 | sc.exe create KMSEmulator binpath= temp.exe type= own start= auto | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
913
Read events
625
Write events
288
Delete events
0
Modification events
| (PID) Process: | (1252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1252) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\KMSAuto.Lite-1.4.2-Portable-Ratiborus-www.MoriDim.tv.rar | |||
| (PID) Process: | (1252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
3
Suspicious files
0
Text files
36
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1252 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1252.26989\KMSAuto.Lite-1.4.2-Portable-Ratiborus-www.MoriDim.tv\KMSAuto.exe | — | |
MD5:— | SHA256:— | |||
| 1252 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1252.25250\KMSAuto.Lite-1.4.2-Portable-Ratiborus-www.MoriDim.tv\KMSAutoLite.ini | text | |
MD5:— | SHA256:— | |||
| 1252 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1252.25250\KMSAuto.Lite-1.4.2-Portable-Ratiborus-www.MoriDim.tv\KMSAuto.exe | executable | |
MD5:— | SHA256:— | |||
| 1252 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1252.25250\KMSAuto.Lite-1.4.2-Portable-Ratiborus-www.MoriDim.tv\KMSAuto x64.exe | executable | |
MD5:E05622435A55ABABCE265FB350F65161 | SHA256:BD50F0235EE8D6B5477218CAA989DF5D15565E56D7713B9AFBD04960E0201002 | |||
| 2144 | KMSSS.exe | C:\Windows\Temp\KMSAuto_Files\bin\KMSSS.log | text | |
MD5:— | SHA256:— | |||
| 1252 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1252.25250\KMSAuto.Lite-1.4.2-Portable-Ratiborus-www.MoriDim.tv\readme_en.txt | text | |
MD5:2A01203D3B992EC17E7F66B32A4D1B19 | SHA256:1253031B338654889A122460AA5410847C8D93B6E447239B60B4BF731C44B789 | |||
| 2868 | KMSAuto.exe | C:\Users\admin\AppData\Local\Temp\slmgr.vbs | text | |
MD5:38482A5013D8AB40DF0FB15EAE022C57 | SHA256:AC5C46B97345465A96E9AE1EDAFF44B191A39BF3D03DC1128090B8FFA92A16F8 | |||
| 2868 | KMSAuto.exe | C:\Windows\Temp\KMSAuto_Files\bin\KMSSS.exe | executable | |
MD5:01A80AAD5DABED1C1580F7E00213CF9D | SHA256:FD7499214ABAA13BF56D006AB7DE78EB8D6ADF17926C24ACE024D067049BC81D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
2
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3380 | wmiprvse.exe | POST | 302 | 23.43.214.226:80 | http://go.microsoft.com/fwlink/?LinkID=88339 | US | — | — | whitelisted |
3380 | wmiprvse.exe | POST | 302 | 23.43.214.226:80 | http://go.microsoft.com/fwlink/?LinkID=88340 | US | — | — | whitelisted |
3380 | wmiprvse.exe | POST | 302 | 23.43.214.226:80 | http://go.microsoft.com/fwlink/?LinkID=88341 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3380 | wmiprvse.exe | 23.43.214.226:80 | go.microsoft.com | Akamai International B.V. | US | malicious |
3380 | wmiprvse.exe | 40.91.72.206:443 | activation.sls.microsoft.com | Microsoft Corporation | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
activation.sls.microsoft.com |
| whitelisted |