| File name: | Flexer.exe |
| Full analysis: | https://app.any.run/tasks/b722667e-0934-4806-9932-a71004da11f7 |
| Verdict: | Malicious activity |
| Analysis date: | November 26, 2024, 13:28:40 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | FC4CD4BE96C610321FFD4702AF38995A |
| SHA1: | 5B108A03642AB855D3CF541F540BD5AE147155A6 |
| SHA256: | FDDBF31C5C1996B42B50C381EA5F284F85D8F69C89C18AA8E2514F7B1FAD8F8B |
| SSDEEP: | 98304:3c8oaYNAg/Yk981g1HUsYkV2R5LYZEHrDz3JhZEfvJGqSPgVNlm2d4ApzGWFR5sK:5gvt7qGXDbfK5HYfF5 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- Flexer.exe (PID: 6624)
The process drops C-runtime libraries
- Flexer.exe (PID: 6624)
Process drops python dynamic module
- Flexer.exe (PID: 6624)
Process drops legitimate windows executable
- Flexer.exe (PID: 6624)
INFO
Checks supported languages
- Flexer.exe (PID: 6624)
Create files in a temporary directory
- Flexer.exe (PID: 6624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:11:26 06:51:00+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.42 |
| CodeSize: | 131072 |
| InitializedDataSize: | 11226112 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc88c |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
119
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
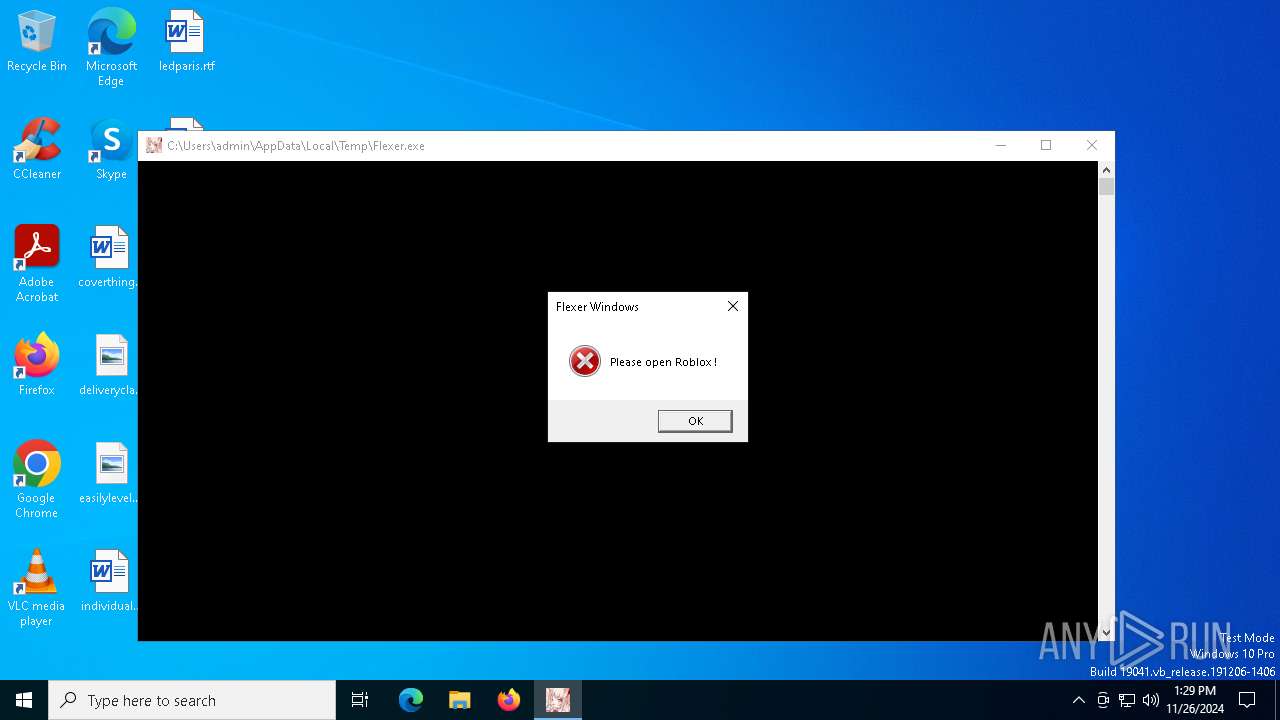
| 6624 | "C:\Users\admin\AppData\Local\Temp\Flexer.exe" | C:\Users\admin\AppData\Local\Temp\Flexer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 6632 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Flexer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6992 | C:\Users\admin\AppData\Local\Temp\Flexer.exe | C:\Users\admin\AppData\Local\Temp\onefile_6624_133771013366053043\Loader.exe | — | Flexer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
Total events
646
Read events
646
Write events
0
Delete events
0
Modification events
Executable files
30
Suspicious files
2
Text files
923
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6624 | Flexer.exe | C:\Users\admin\AppData\Local\Temp\onefile_6624_133771013366053043\_ctypes.pyd | executable | |
MD5:A55E57D7594303C89B5F7A1D1D6F2B67 | SHA256:F63C6C7E71C342084D8F1A108786CA6975A52CEFEF8BE32CC2589E6E2FE060C8 | |||
| 6624 | Flexer.exe | C:\Users\admin\AppData\Local\Temp\onefile_6624_133771013366053043\_queue.pyd | executable | |
MD5:1C03CAA59B5E4A7FB9B998D8C1DA165A | SHA256:B9CF502DADCB124F693BF69ECD7077971E37174104DBDA563022D74961A67E1E | |||
| 6624 | Flexer.exe | C:\Users\admin\AppData\Local\Temp\onefile_6624_133771013366053043\Loader.exe | executable | |
MD5:4B482ADEA16A69F93E6F562B32D041B0 | SHA256:8CF9B87D20DBF123AC018C30D66F02D0082469B964A6458A13BDD2FB35F60FAC | |||
| 6624 | Flexer.exe | C:\Users\admin\AppData\Local\Temp\onefile_6624_133771013366053043\libssl-3.dll | executable | |
MD5:4FF168AAA6A1D68E7957175C8513F3A2 | SHA256:2E4D35B681A172D3298CAF7DC670451BE7A8BA27C26446EFC67470742497A950 | |||
| 6624 | Flexer.exe | C:\Users\admin\AppData\Local\Temp\onefile_6624_133771013366053043\libffi-8.dll | executable | |
MD5:0F8E4992CA92BAAF54CC0B43AACCCE21 | SHA256:EFF52743773EB550FCC6CE3EFC37C85724502233B6B002A35496D828BD7B280A | |||
| 6624 | Flexer.exe | C:\Users\admin\AppData\Local\Temp\onefile_6624_133771013366053043\libcrypto-3.dll | executable | |
MD5:123AD0908C76CCBA4789C084F7A6B8D0 | SHA256:4E5D5D20D6D31E72AB341C81E97B89E514326C4C861B48638243BDF0918CFA43 | |||
| 6624 | Flexer.exe | C:\Users\admin\AppData\Local\Temp\onefile_6624_133771013366053043\_lzma.pyd | executable | |
MD5:1BA022D42024A655CF289544AE461FB8 | SHA256:D080EABD015A3569813A220FD4EA74DFF34ED2A8519A10473EB37E22B1118A06 | |||
| 6624 | Flexer.exe | C:\Users\admin\AppData\Local\Temp\onefile_6624_133771013366053043\_decimal.pyd | executable | |
MD5:F3377F3DE29579140E2BBAEEFD334D4F | SHA256:B715D1C18E9A9C1531F21C02003B4C6726742D1A2441A1893BC3D79D7BB50E91 | |||
| 6624 | Flexer.exe | C:\Users\admin\AppData\Local\Temp\onefile_6624_133771013366053043\_socket.pyd | executable | |
MD5:FE896371430BD9551717EF12A3E7E818 | SHA256:35246B04C6C7001CA448554246445A845CE116814A29B18B617EA38752E4659B | |||
| 6624 | Flexer.exe | C:\Users\admin\AppData\Local\Temp\onefile_6624_133771013366053043\_wmi.pyd | executable | |
MD5:1C30CC7DF3BD168D883E93C593890B43 | SHA256:6435C679A3A3FF4F16708EBC43F7CA62456C110AC1EA94F617D8052C90C143C7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
33
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1468 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1468 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6748 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6748 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5720 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
1468 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1468 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 2.23.209.177:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |