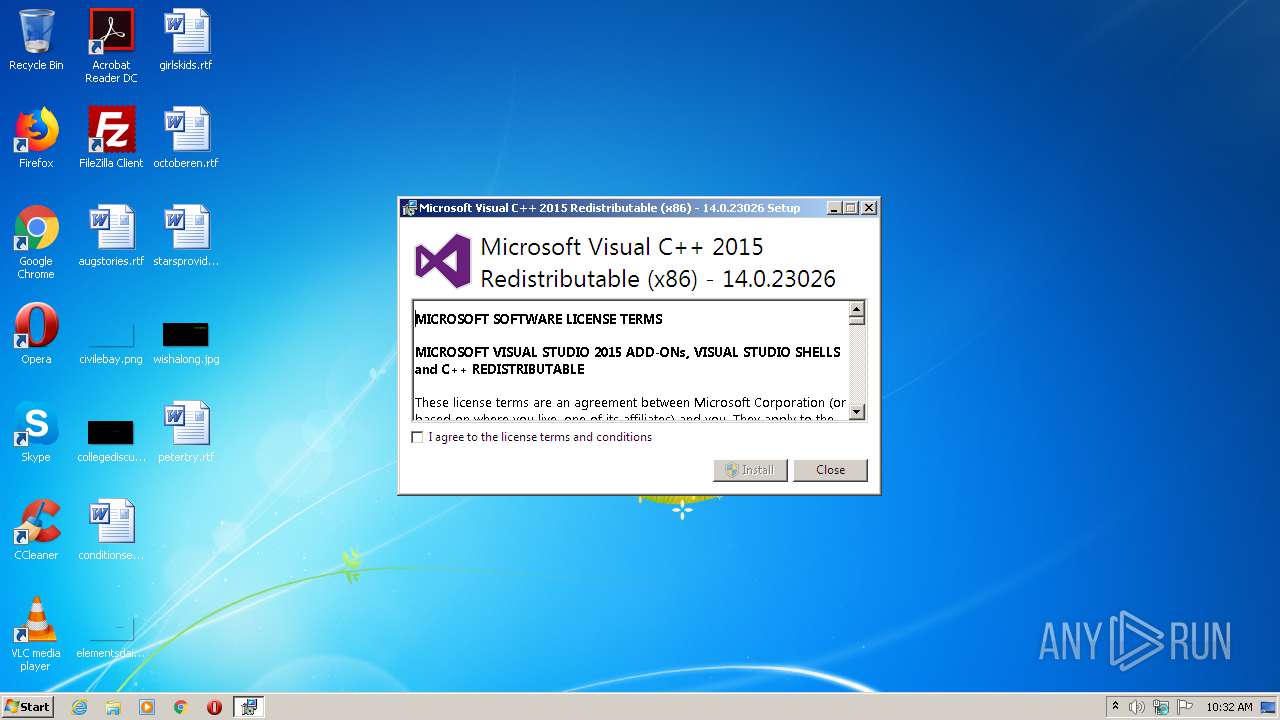
| File name: | vc_redist.x86.exe |
| Full analysis: | https://app.any.run/tasks/99aae685-19a5-455b-af05-a3c13c407130 |
| Verdict: | Malicious activity |
| Analysis date: | June 25, 2020, 09:32:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1A15E6606BAC9647E7AD3CAA543377CF |
| SHA1: | BFB74E498C44D3A103CA3AA2831763FB417134D1 |
| SHA256: | FDD1E1F0DCAE2D0AA0720895EFF33B927D13076E64464BB7C7E5843B7667CD14 |
| SSDEEP: | 393216:S1RPq5dCsKSR65cX7Eyd/qnejOFxP7OEnl4L/Vvc:yP5iw56oyleej2OEnlwc |
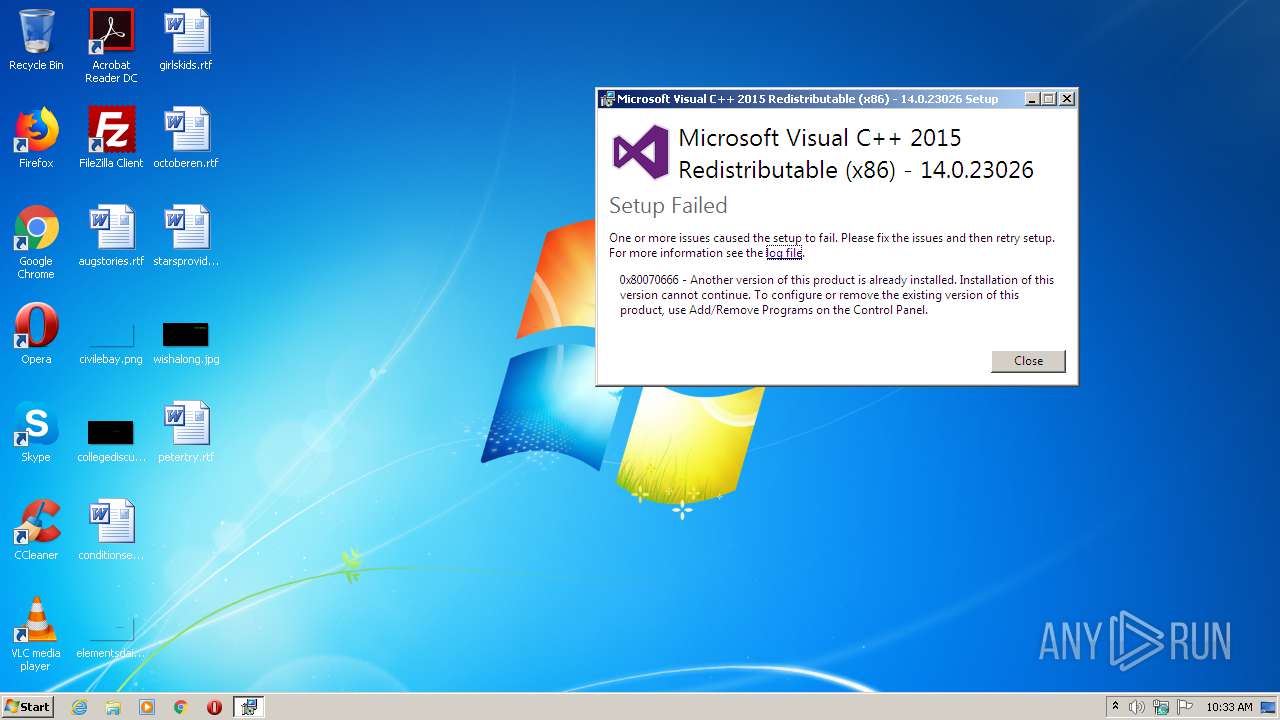
MALICIOUS
Loads dropped or rewritten executable
- vc_redist.x86.exe (PID: 1548)
SUSPICIOUS
Searches for installed software
- vc_redist.x86.exe (PID: 1548)
Executable content was dropped or overwritten
- vc_redist.x86.exe (PID: 1548)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2016)
INFO
Reads the hosts file
- chrome.exe (PID: 2016)
- chrome.exe (PID: 288)
Manual execution by user
- chrome.exe (PID: 2016)
Application launched itself
- chrome.exe (PID: 2016)
Reads settings of System Certificates
- chrome.exe (PID: 288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:02:13 20:42:32+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 234496 |
| InitializedDataSize: | 144896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x28494 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 14.0.23026.0 |
| ProductVersionNumber: | 14.0.23026.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft Visual C++ 2015 Redistributable (x86) - 14.0.23026 |
| FileVersion: | 14.0.23026.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| OriginalFileName: | VC_redist.x86.exe |
| ProductName: | Microsoft Visual C++ 2015 Redistributable (x86) - 14.0.23026 |
| ProductVersion: | 14.0.23026.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Feb-2015 19:42:32 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft Visual C++ 2015 Redistributable (x86) - 14.0.23026 |
| FileVersion: | 14.0.23026.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| OriginalFilename: | VC_redist.x86.exe |
| ProductName: | Microsoft Visual C++ 2015 Redistributable (x86) - 14.0.23026 |
| ProductVersion: | 14.0.23026.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 13-Feb-2015 19:42:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00039384 | 0x00039400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50787 |
.rdata | 0x0003B000 | 0x0001A0EC | 0x0001A200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.96038 |
.data | 0x00056000 | 0x000030C0 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.78852 |
.wixburn8 | 0x0005A000 | 0x00000038 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.7415 |
.tls | 0x0005B000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0005C000 | 0x00003910 | 0x00003A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.50792 |
.reloc | 0x00060000 | 0x00004482 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.65822 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25503 | 1332 | Latin 1 / Western European | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
CRYPT32.dll |
Cabinet.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
Total processes
70
Monitored processes
35
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,10979821978468912240,14738958466476529115,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=13904716799725655652 --mojo-platform-channel-handle=1564 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,10979821978468912240,14738958466476529115,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3385528692952461873 --mojo-platform-channel-handle=4564 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,10979821978468912240,14738958466476529115,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9932699265741941074 --mojo-platform-channel-handle=3600 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,10979821978468912240,14738958466476529115,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3311100866139150812 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,10979821978468912240,14738958466476529115,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3173244746301806149 --mojo-platform-channel-handle=3748 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,10979821978468912240,14738958466476529115,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7771905681535744133 --mojo-platform-channel-handle=3648 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,10979821978468912240,14738958466476529115,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5553244199478600728 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2528 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1548 | "C:\Users\admin\AppData\Local\Temp\vc_redist.x86.exe" | C:\Users\admin\AppData\Local\Temp\vc_redist.x86.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2015 Redistributable (x86) - 14.0.23026 Exit code: 1638 Version: 14.0.23026.0 Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,10979821978468912240,14738958466476529115,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1009778155052839512 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,10979821978468912240,14738958466476529115,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7546681548164912384 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2020 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
838
Read events
744
Write events
89
Delete events
5
Modification events
| (PID) Process: | (2016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3360) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2016-13237551200086375 |
Value: 259 | |||
| (PID) Process: | (2016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2016) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
1
Suspicious files
61
Text files
303
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1548 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1040\license.rtf | text | |
MD5:1D07E27F97CE22A58780A04227BE6465 | SHA256:F1214784C57AA3323426AF64D132045970717994EBA500B25283684DC1ADEBAA | |||
| 1548 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1029\license.rtf | text | |
MD5:FD8353F3BC88A47B8880B59A5DAD3F03 | SHA256:2428E8BA8FC9648422333B6B4B92FB476741FC1022DE7CB59D030EC35CC21AC7 | |||
| 1548 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1028\license.rtf | text | |
MD5:EFA0E0316DBE1D01B04DB8AE55216E89 | SHA256:D5147EE2BA7826D5B68E0DC10FC2AC95079F89C38264C5648D924DEC9290D085 | |||
| 1548 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1036\license.rtf | text | |
MD5:6F70759DF32F212DBB65464258ECEEAF | SHA256:C7F03DA5D9A7F689B8DCBD507FF0B3FA98DABA55616F902E5E47E9839B753E1F | |||
| 1548 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1031\license.rtf | text | |
MD5:B4A1F60A329E18DD44C19F91E19E9A0D | SHA256:C017EDFE3B0D308E20FBF3DE8795FD4451A530475A2D0EE0824E166045EADFB7 | |||
| 1548 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1055\license.rtf | text | |
MD5:362F60F539B629BF59021003F426583C | SHA256:1E602773F3071636E0F9C6B27037B7B4094DC26F7C2FABCDF3287BC9BCAA8652 | |||
| 1548 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\2052\license.rtf | text | |
MD5:31AFEC54446E496CE2A1D1CD3B257738 | SHA256:63F463F0ACE41FA088ACFB70F501DB47E3B83600DB31538D8DABA010E6B83D42 | |||
| 1548 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1042\license.rtf | text | |
MD5:F6E7A2A05EFB4413295C156A179578A3 | SHA256:DCEFD9B37D78F37ED8AAEF70AC2BFCDE441DCFB97469A6AA6AF89C1FFADBF814 | |||
| 1548 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1045\license.rtf | text | |
MD5:A0D88589A339E57E412AB01E763D6A27 | SHA256:898D5CA01A3271D97350D06A6CCDB8803A176BB42BAF7E2C8F76C9037235CA8E | |||
| 1548 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1046\license.rtf | text | |
MD5:137A9579BA2E02EBB87817440FCBDCB9 | SHA256:42DC678EF9D5E4E147BF178FFE2FA3CD4BBBF9C904872B4E344D8BB22C473ED5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
43
DNS requests
43
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
288 | chrome.exe | GET | 302 | 172.217.23.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 539 b | whitelisted |
288 | chrome.exe | GET | 200 | 185.180.12.142:80 | http://r3---sn-n02xgoxufvg3-8pxe.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.183.107.236&mm=28&mn=sn-n02xgoxufvg3-8pxe&ms=nvh&mt=1593077535&mv=m&mvi=2&pl=24&shardbypass=yes | AT | crx | 293 Kb | whitelisted |
288 | chrome.exe | GET | 302 | 172.217.23.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 544 b | whitelisted |
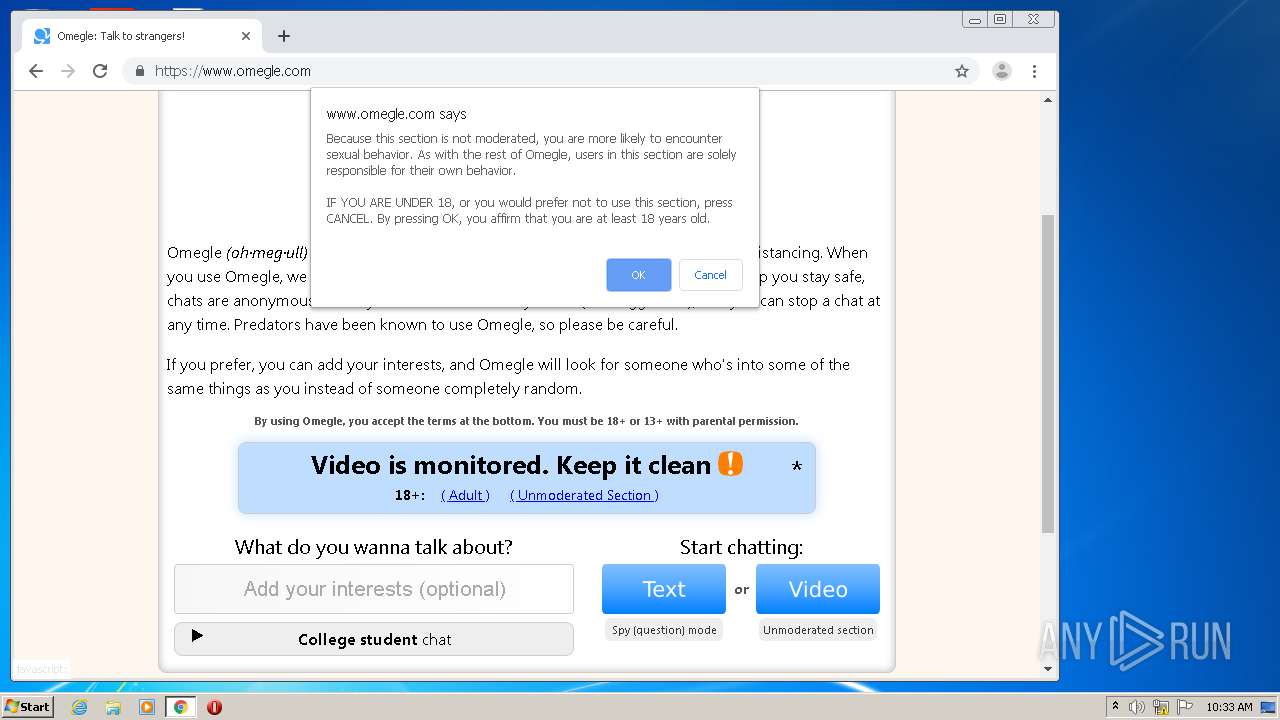
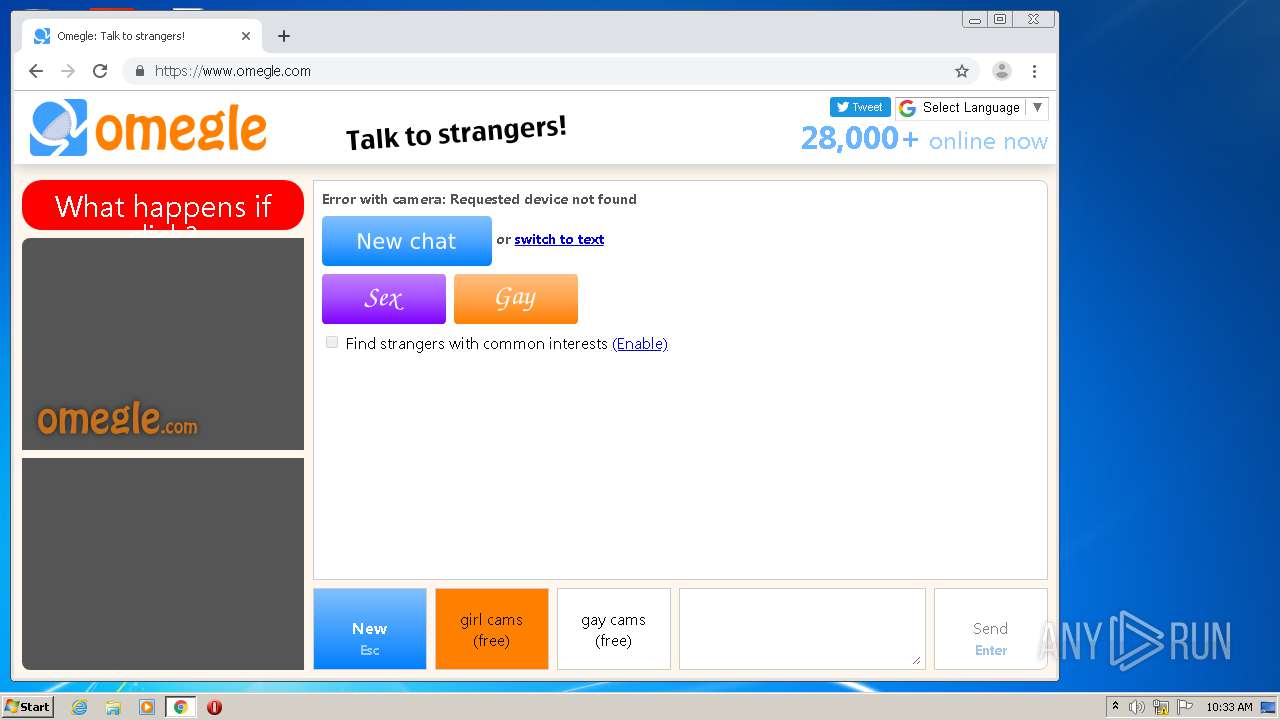
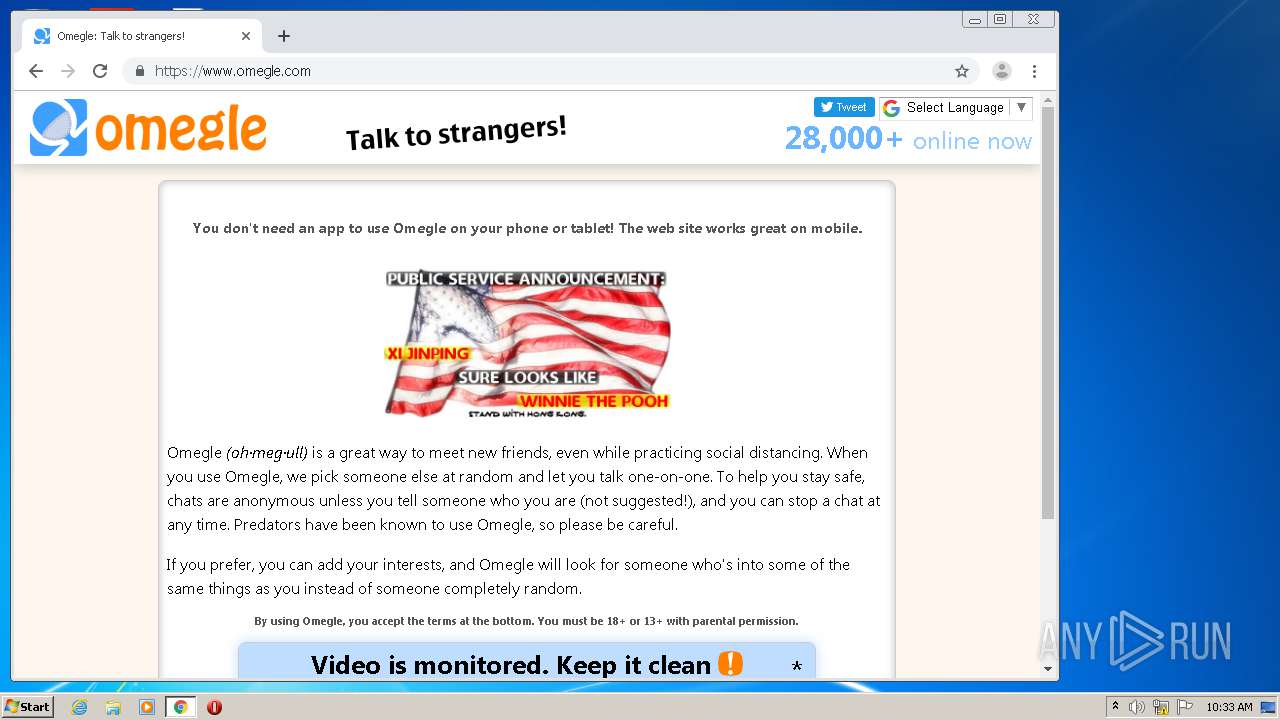
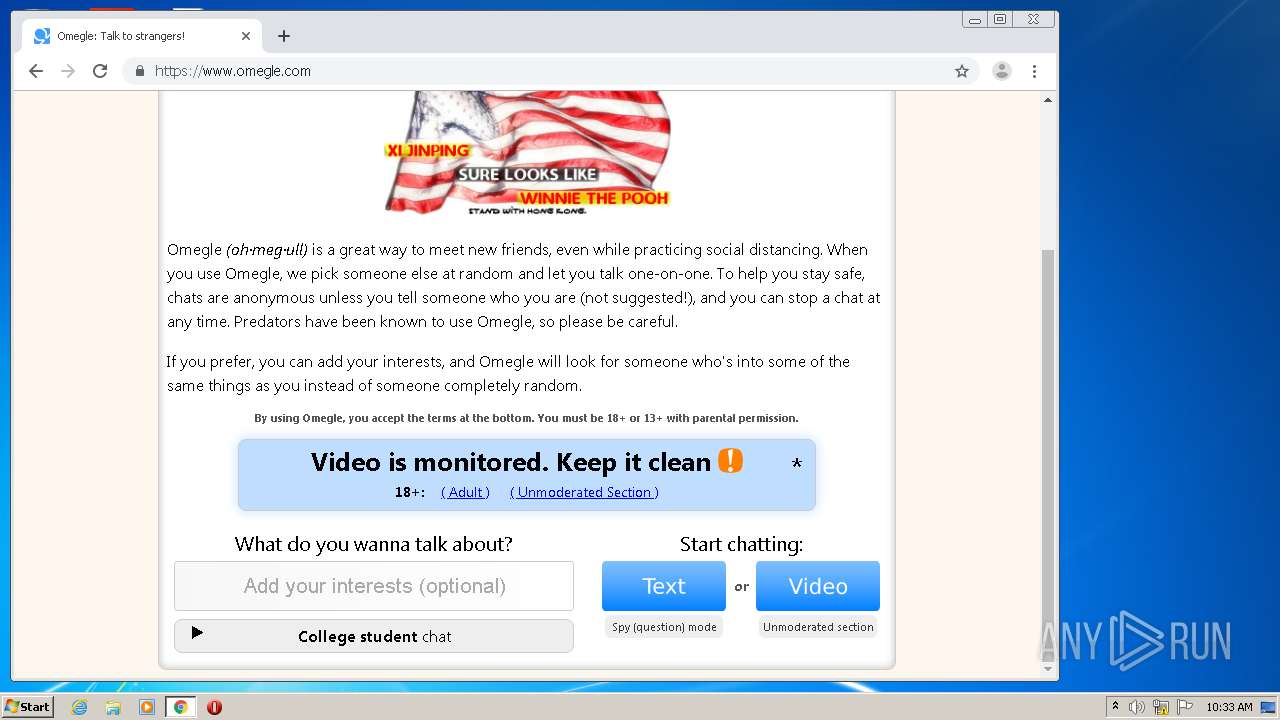
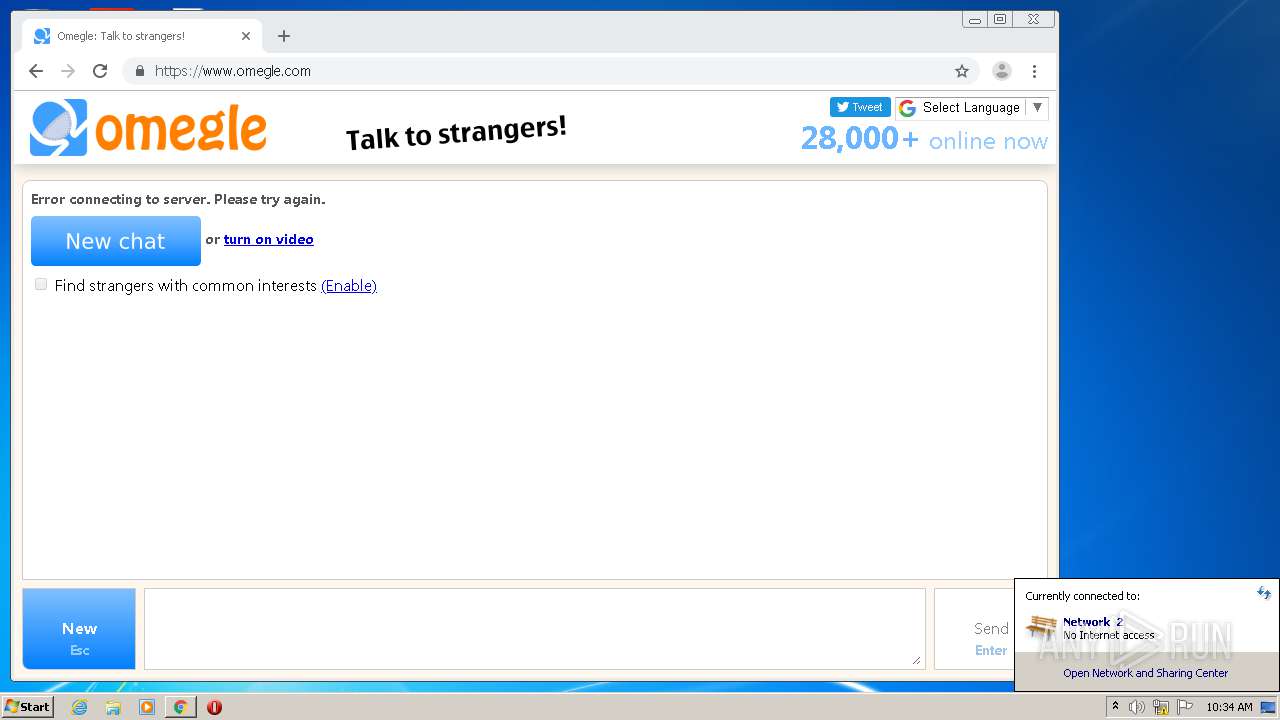
288 | chrome.exe | GET | 301 | 104.23.143.25:80 | http://omegle.com/ | US | — | — | suspicious |
288 | chrome.exe | GET | 200 | 185.180.12.141:80 | http://r2---sn-n02xgoxufvg3-8pxe.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=185.183.107.236&mm=28&mn=sn-n02xgoxufvg3-8pxe&ms=nvh&mt=1593077535&mv=m&mvi=1&pl=24&shardbypass=yes | AT | crx | 823 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
288 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
288 | chrome.exe | 172.217.18.163:443 | www.google.com.ua | Google Inc. | US | whitelisted |
288 | chrome.exe | 172.217.21.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
288 | chrome.exe | 172.217.23.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
288 | chrome.exe | 172.217.16.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
288 | chrome.exe | 216.58.207.46:443 | apis.google.com | Google Inc. | US | whitelisted |
288 | chrome.exe | 172.217.21.238:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
288 | chrome.exe | 172.217.16.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
288 | chrome.exe | 172.217.23.174:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
288 | chrome.exe | 216.58.207.33:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |