| File name: | spirthack.mestaticvc_redist.exe |
| Full analysis: | https://app.any.run/tasks/67a34e5d-6ad2-4fee-87dd-a2bd611f8787 |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 08:17:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1A15E6606BAC9647E7AD3CAA543377CF |
| SHA1: | BFB74E498C44D3A103CA3AA2831763FB417134D1 |
| SHA256: | FDD1E1F0DCAE2D0AA0720895EFF33B927D13076E64464BB7C7E5843B7667CD14 |
| SSDEEP: | 393216:S1RPq5dCsKSR65cX7Eyd/qnejOFxP7OEnl4L/Vvc:yP5iw56oyleej2OEnlwc |
MALICIOUS
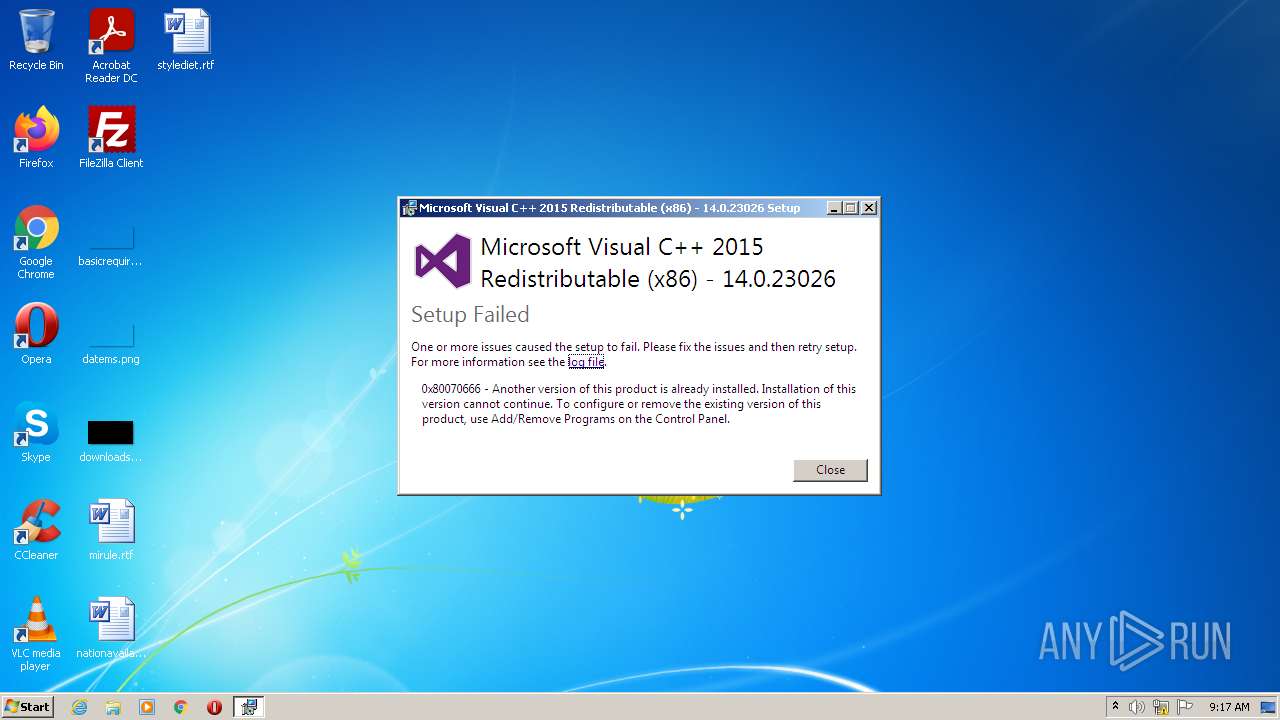
Drops executable file immediately after starts
- spirthack.mestaticvc_redist.exe (PID: 3216)
Loads dropped or rewritten executable
- spirthack.mestaticvc_redist.exe (PID: 3216)
SUSPICIOUS
Checks supported languages
- spirthack.mestaticvc_redist.exe (PID: 3216)
Reads the computer name
- spirthack.mestaticvc_redist.exe (PID: 3216)
Executable content was dropped or overwritten
- spirthack.mestaticvc_redist.exe (PID: 3216)
Searches for installed software
- spirthack.mestaticvc_redist.exe (PID: 3216)
Drops a file with a compile date too recent
- spirthack.mestaticvc_redist.exe (PID: 3216)
Executed via COM
- DllHost.exe (PID: 3780)
INFO
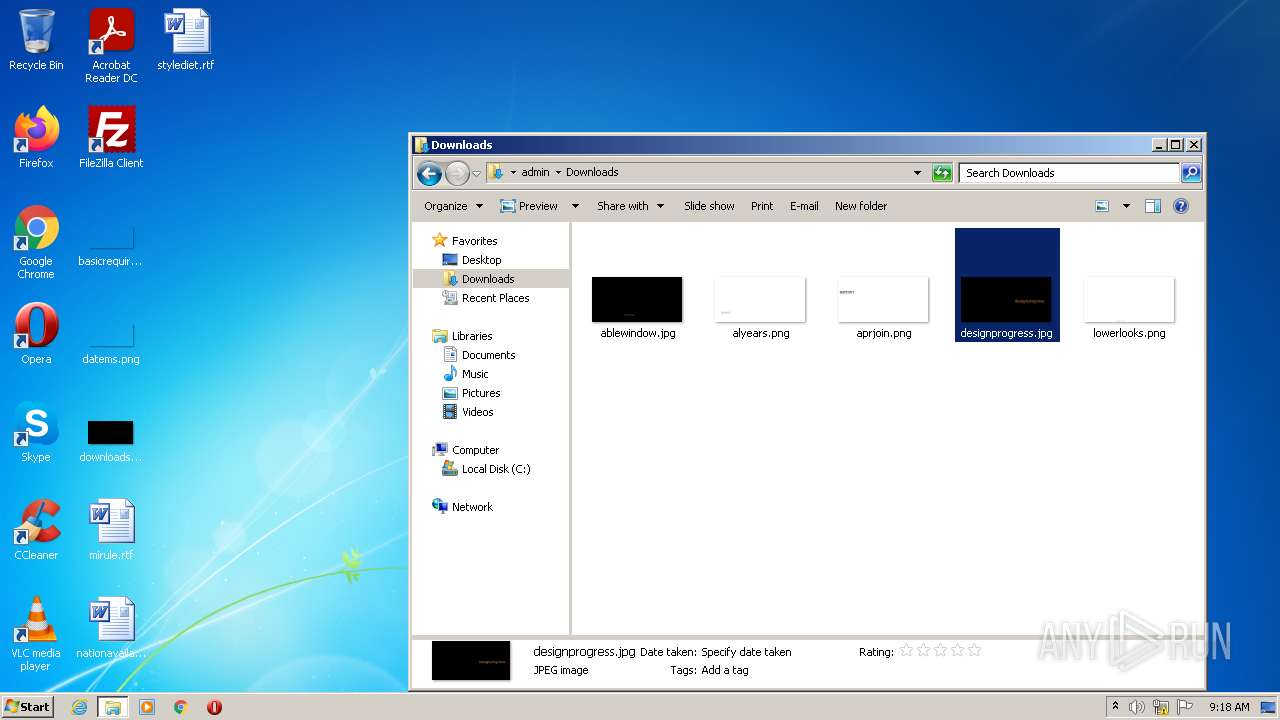
Manual execution by user
- explorer.exe (PID: 3212)
Reads the computer name
- explorer.exe (PID: 3212)
- DllHost.exe (PID: 3780)
Checks supported languages
- DllHost.exe (PID: 3780)
- explorer.exe (PID: 3212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
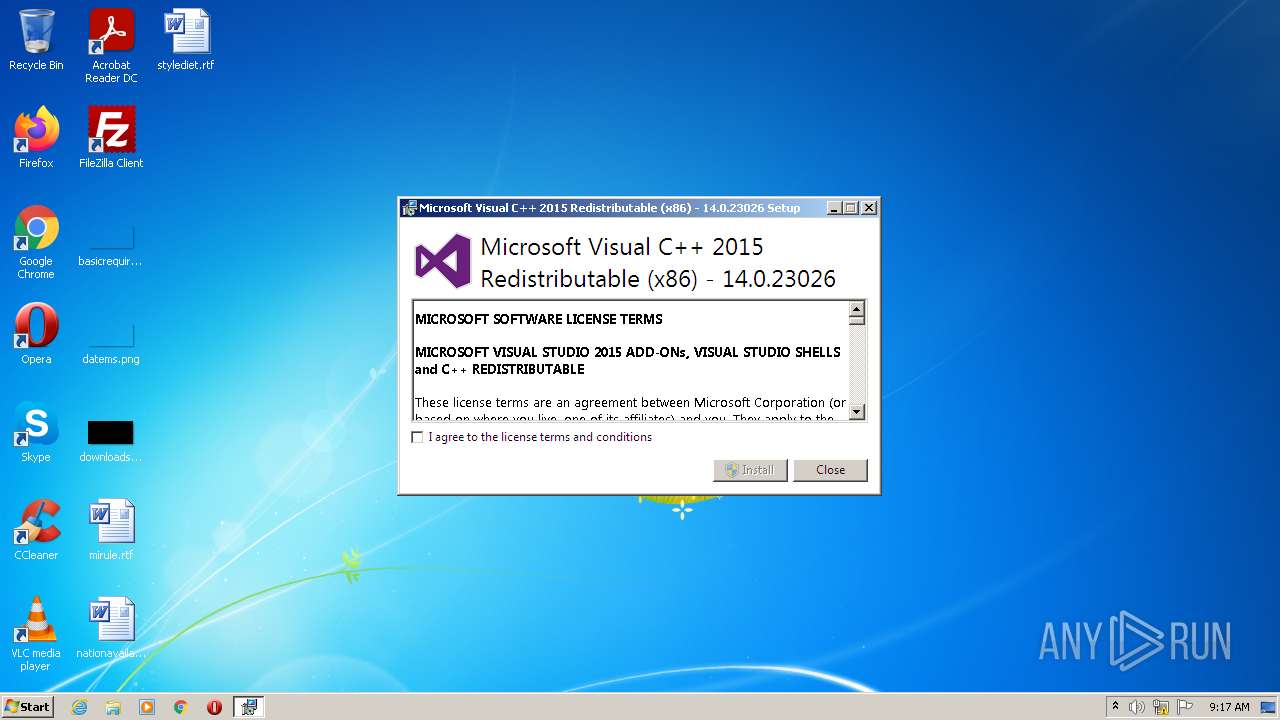
| ProductVersion: | 14.0.23026.0 |
|---|---|
| ProductName: | Microsoft Visual C++ 2015 Redistributable (x86) - 14.0.23026 |
| OriginalFileName: | VC_redist.x86.exe |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| InternalName: | setup |
| FileVersion: | 14.0.23026.0 |
| FileDescription: | Microsoft Visual C++ 2015 Redistributable (x86) - 14.0.23026 |
| CompanyName: | Microsoft Corporation |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 14.0.23026.0 |
| FileVersionNumber: | 14.0.23026.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x28494 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 144896 |
| CodeSize: | 234496 |
| LinkerVersion: | 10 |
| PEType: | PE32 |
| TimeStamp: | 2015:02:13 20:42:32+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Feb-2015 19:42:32 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft Visual C++ 2015 Redistributable (x86) - 14.0.23026 |
| FileVersion: | 14.0.23026.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| OriginalFilename: | VC_redist.x86.exe |
| ProductName: | Microsoft Visual C++ 2015 Redistributable (x86) - 14.0.23026 |
| ProductVersion: | 14.0.23026.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 13-Feb-2015 19:42:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00039384 | 0x00039400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50787 |
.rdata | 0x0003B000 | 0x0001A0EC | 0x0001A200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.96038 |
.data | 0x00056000 | 0x000030C0 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.78852 |
.wixburn8 | 0x0005A000 | 0x00000038 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.7415 |
.tls | 0x0005B000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0005C000 | 0x00003910 | 0x00003A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.50792 |
.reloc | 0x00060000 | 0x00004482 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.65822 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25503 | 1332 | Latin 1 / Western European | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
CRYPT32.dll |
Cabinet.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
Total processes
37
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3212 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3216 | "C:\Users\admin\AppData\Local\Temp\spirthack.mestaticvc_redist.exe" | C:\Users\admin\AppData\Local\Temp\spirthack.mestaticvc_redist.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2015 Redistributable (x86) - 14.0.23026 Exit code: 1638 Version: 14.0.23026.0 Modules
| |||||||||||||||
| 3780 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
937
Read events
935
Write events
2
Delete events
0
Modification events
| (PID) Process: | (3780) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
| (PID) Process: | (3780) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Photo Viewer\Viewer |
| Operation: | write | Name: | MainWndPos |
Value: 6000000034000000A00400008002000000000000 | |||
Executable files
1
Suspicious files
0
Text files
32
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3216 | spirthack.mestaticvc_redist.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1031\license.rtf | text | |
MD5:B4A1F60A329E18DD44C19F91E19E9A0D | SHA256:C017EDFE3B0D308E20FBF3DE8795FD4451A530475A2D0EE0824E166045EADFB7 | |||
| 3216 | spirthack.mestaticvc_redist.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\wixstdba.dll | executable | |
MD5:4D20A950A3571D11236482754B4A8E76 | SHA256:A9295AD4E909F979E2B6CB2B2495C3D35C8517E689CD64A918C690E17B49078B | |||
| 3216 | spirthack.mestaticvc_redist.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1036\license.rtf | text | |
MD5:6F70759DF32F212DBB65464258ECEEAF | SHA256:C7F03DA5D9A7F689B8DCBD507FF0B3FA98DABA55616F902E5E47E9839B753E1F | |||
| 3216 | spirthack.mestaticvc_redist.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1029\license.rtf | text | |
MD5:FD8353F3BC88A47B8880B59A5DAD3F03 | SHA256:2428E8BA8FC9648422333B6B4B92FB476741FC1022DE7CB59D030EC35CC21AC7 | |||
| 3216 | spirthack.mestaticvc_redist.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1041\license.rtf | text | |
MD5:0D9DD57746D5609494B35314FA88FD93 | SHA256:AC0D8E0EAAB1875909A6A6F106A37CD7468F87F71887A44263F5F0178F99C40B | |||
| 3216 | spirthack.mestaticvc_redist.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1049\license.rtf | text | |
MD5:EFF73C35DB2D6AC9F29D1B633C984A95 | SHA256:F00A2A67106CA3BADB4C233951A262EC0A9BBA3151E1D8DA0362DCADA7928DCD | |||
| 3216 | spirthack.mestaticvc_redist.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1045\license.rtf | text | |
MD5:A0D88589A339E57E412AB01E763D6A27 | SHA256:898D5CA01A3271D97350D06A6CCDB8803A176BB42BAF7E2C8F76C9037235CA8E | |||
| 3216 | spirthack.mestaticvc_redist.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1040\license.rtf | text | |
MD5:1D07E27F97CE22A58780A04227BE6465 | SHA256:F1214784C57AA3323426AF64D132045970717994EBA500B25283684DC1ADEBAA | |||
| 3216 | spirthack.mestaticvc_redist.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\3082\license.rtf | text | |
MD5:64F1444D27E3F3489F057E7280E9C973 | SHA256:55929413B6A530F8C4ACBB1E7EEE81FB9ED0BD64AF5CD26D6F5637CEDFAF0A2D | |||
| 3216 | spirthack.mestaticvc_redist.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1042\license.rtf | text | |
MD5:F6E7A2A05EFB4413295C156A179578A3 | SHA256:DCEFD9B37D78F37ED8AAEF70AC2BFCDE441DCFB97469A6AA6AF89C1FFADBF814 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report