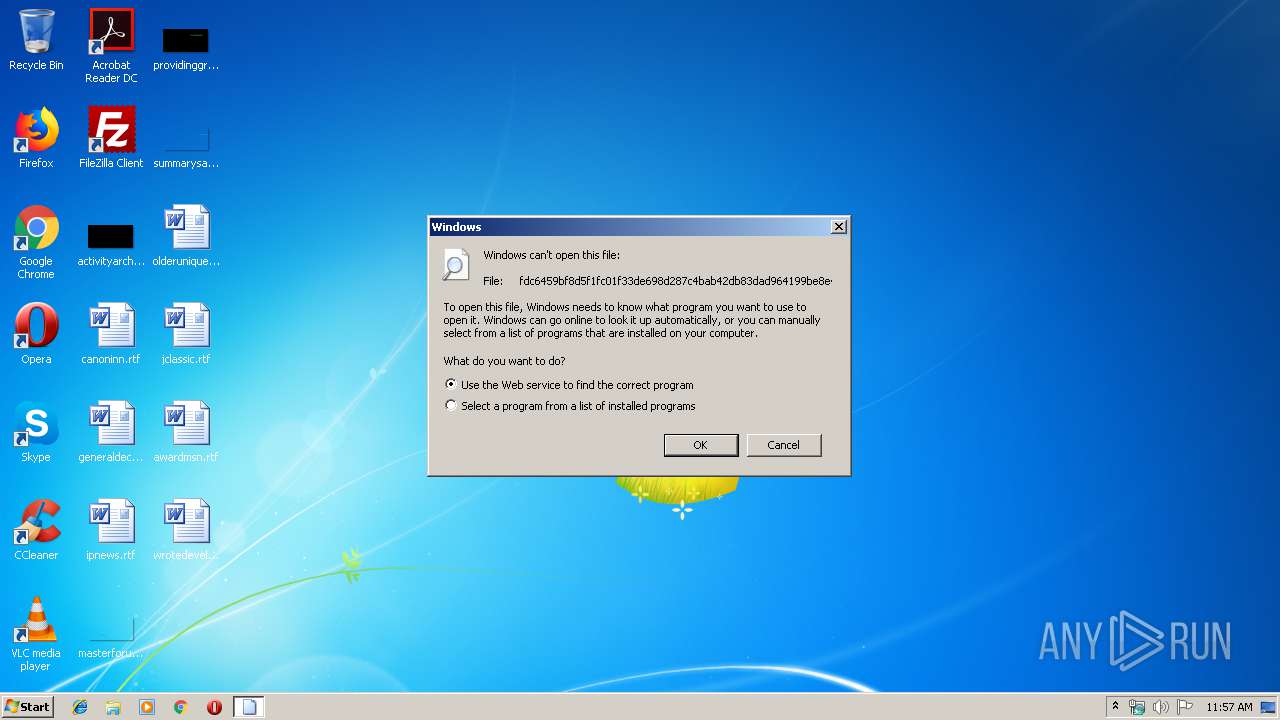
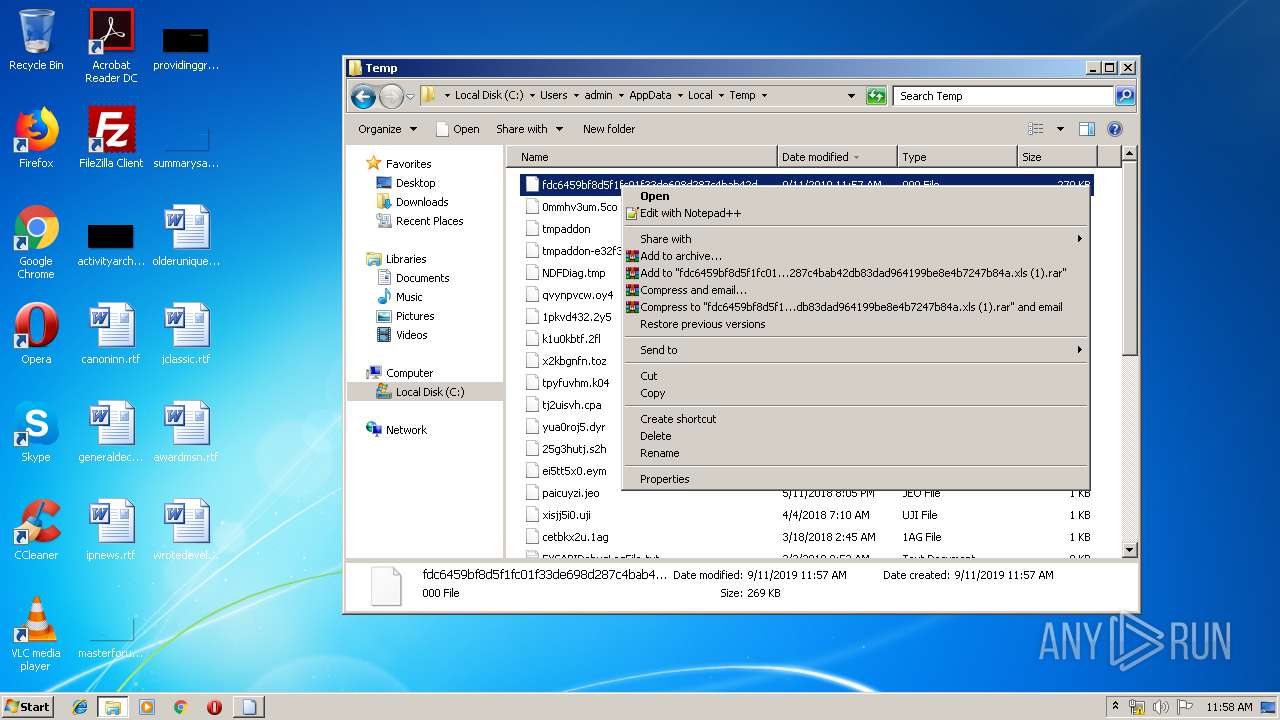
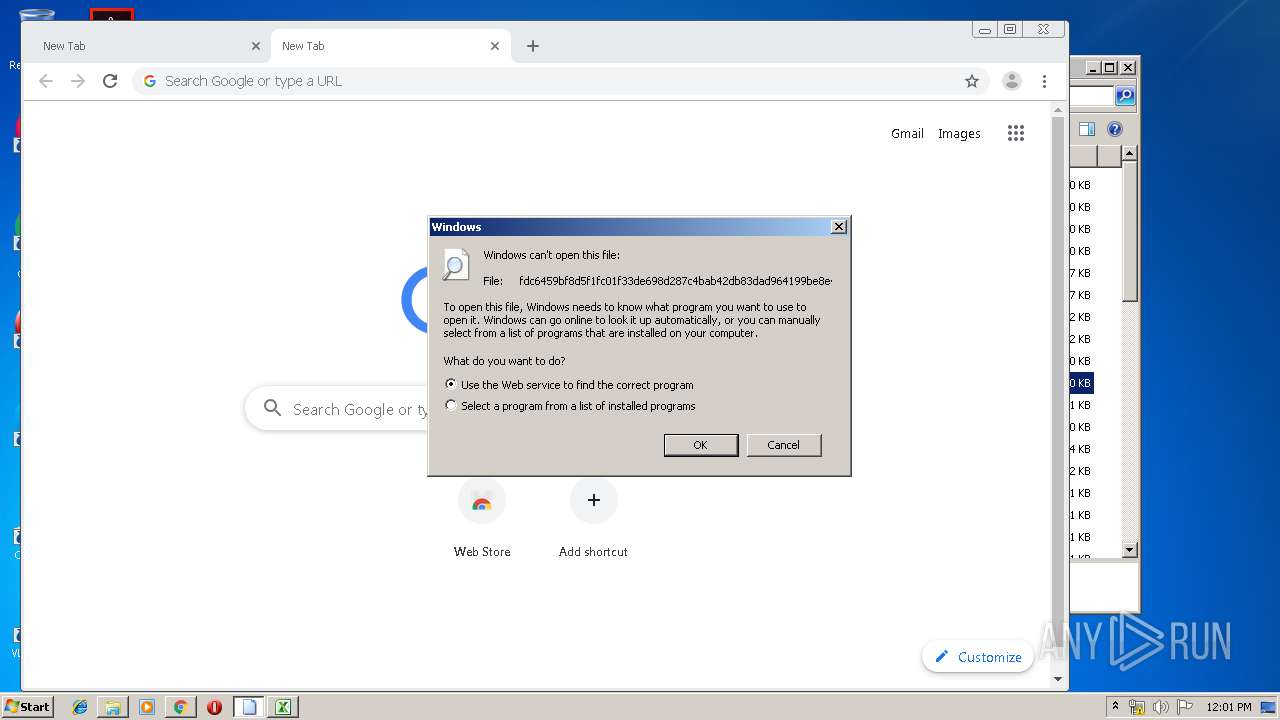
| File name: | fdc6459bf8d5f1fc01f33de698d287c4bab42db83dad964199be8e4b7247b84a.xls (1).000 |
| Full analysis: | https://app.any.run/tasks/c2e652c4-efb1-4837-8a74-9bf57b4428d8 |
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2019, 10:57:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
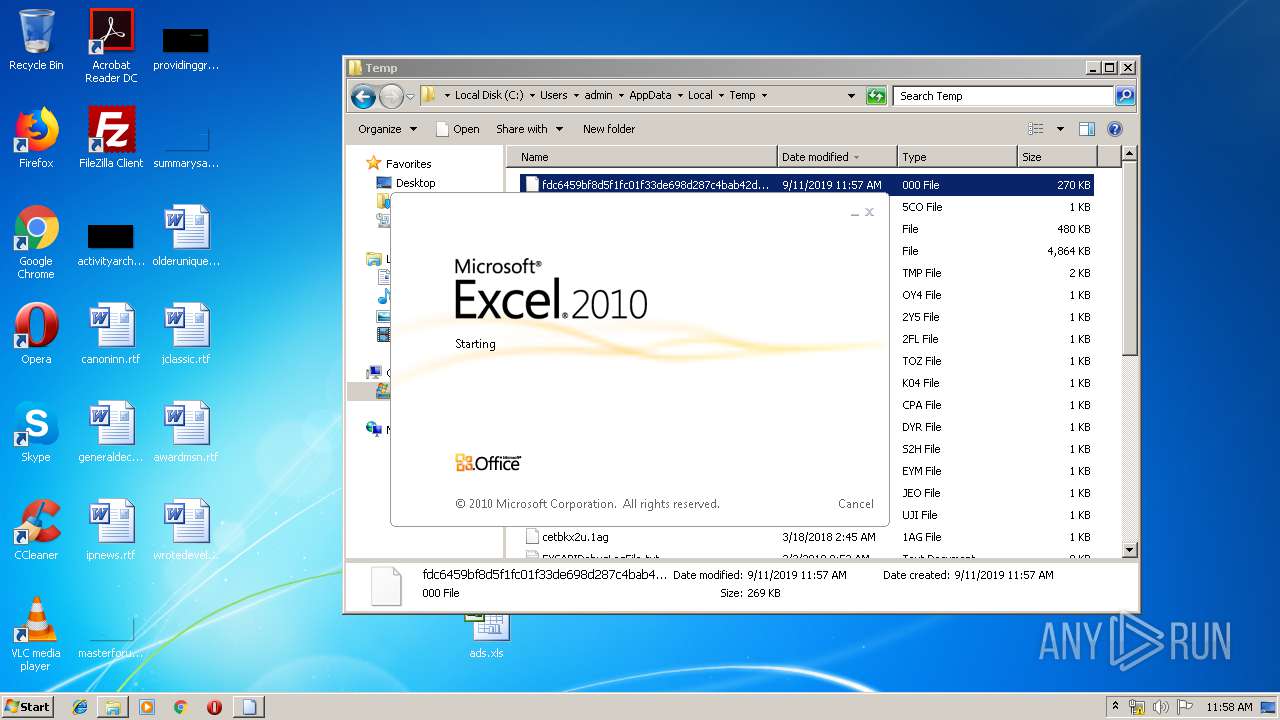
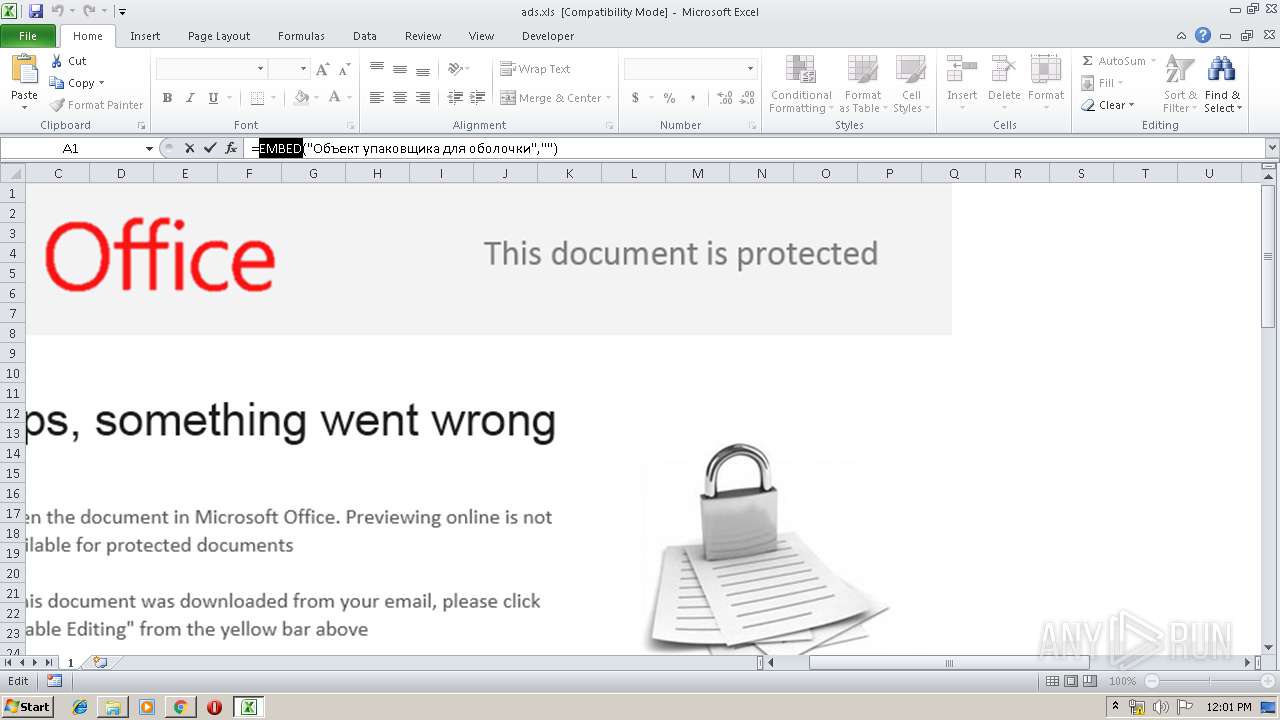
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1251, Title: kTS, Subject: T, Author: L, Last Saved By: Microsoft Office, Revision Number: 105, Name of Creating Application: Microsoft Excel, Total Editing Time: 1d+03:06:00, Create Time/Date: Fri Aug 30 10:14:50 2019, Last Saved Time/Date: Mon Sep 9 12:37:42 2019, Number of Pages: 4, Number of Words: 3365, Number of Characters: 1235, Security: 0 |
| MD5: | FEDF09D11D86E5C554DA907E60A599AB |
| SHA1: | 020CCF8D0C847AF9F539982E015EB9E261816C68 |
| SHA256: | FDC6459BF8D5F1FC01F33DE698D287C4BAB42DB83DAD964199BE8E4B7247B84A |
| SSDEEP: | 3072:f8KsaWCp3C2ENU59tF2wassbcIn5MvST1Irjgbsf5dxt5fADY5kJs/DcoWa1Sc4G:f8nC1r9arbVnSvt4sfDxAIkJIWa1Sc |
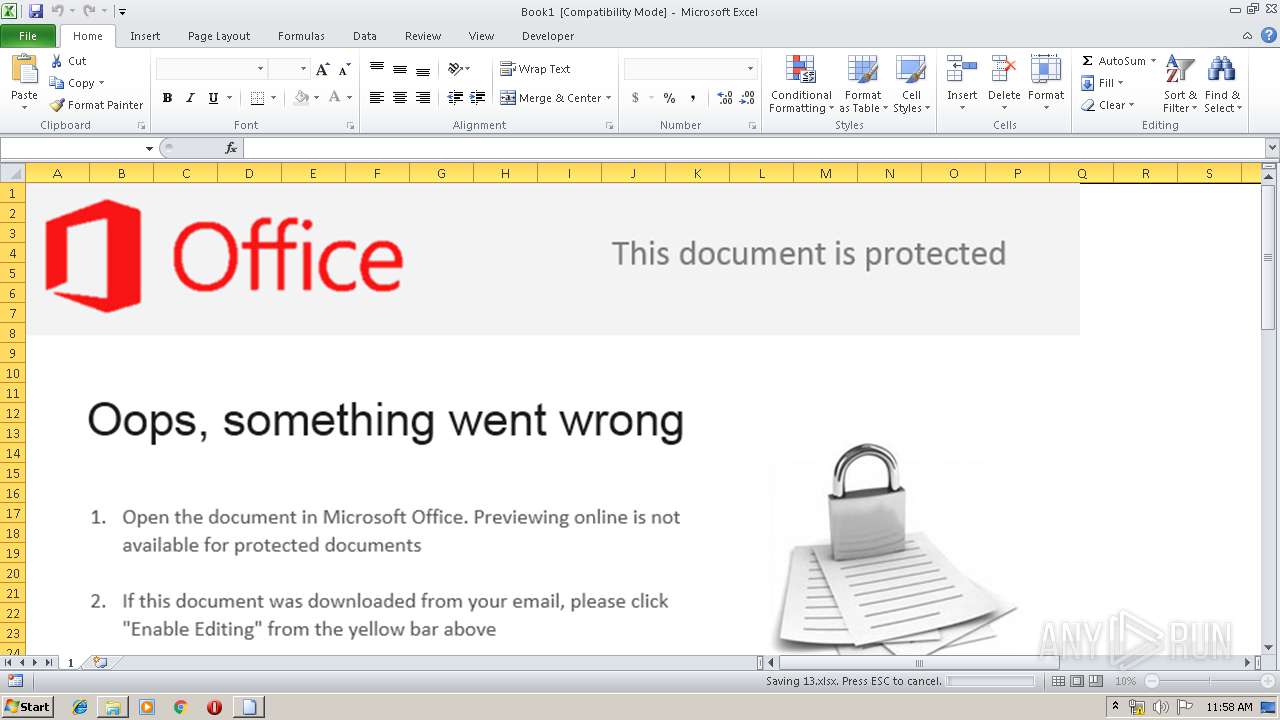
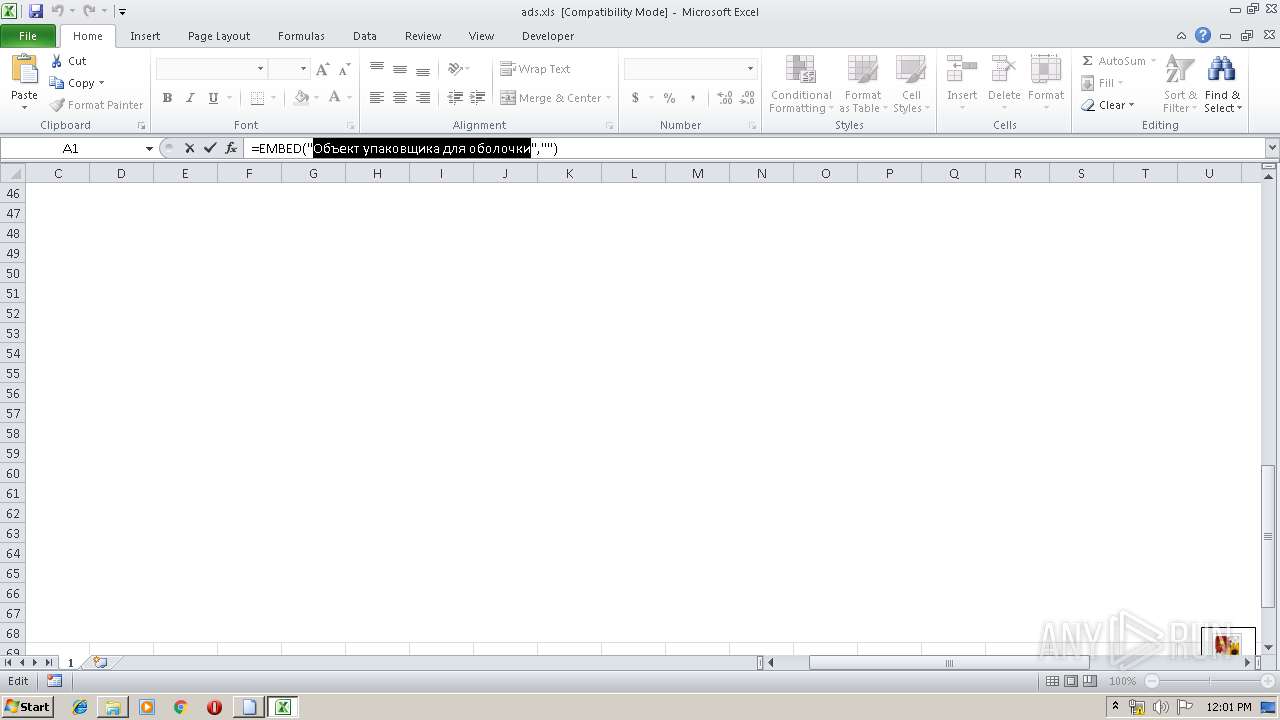
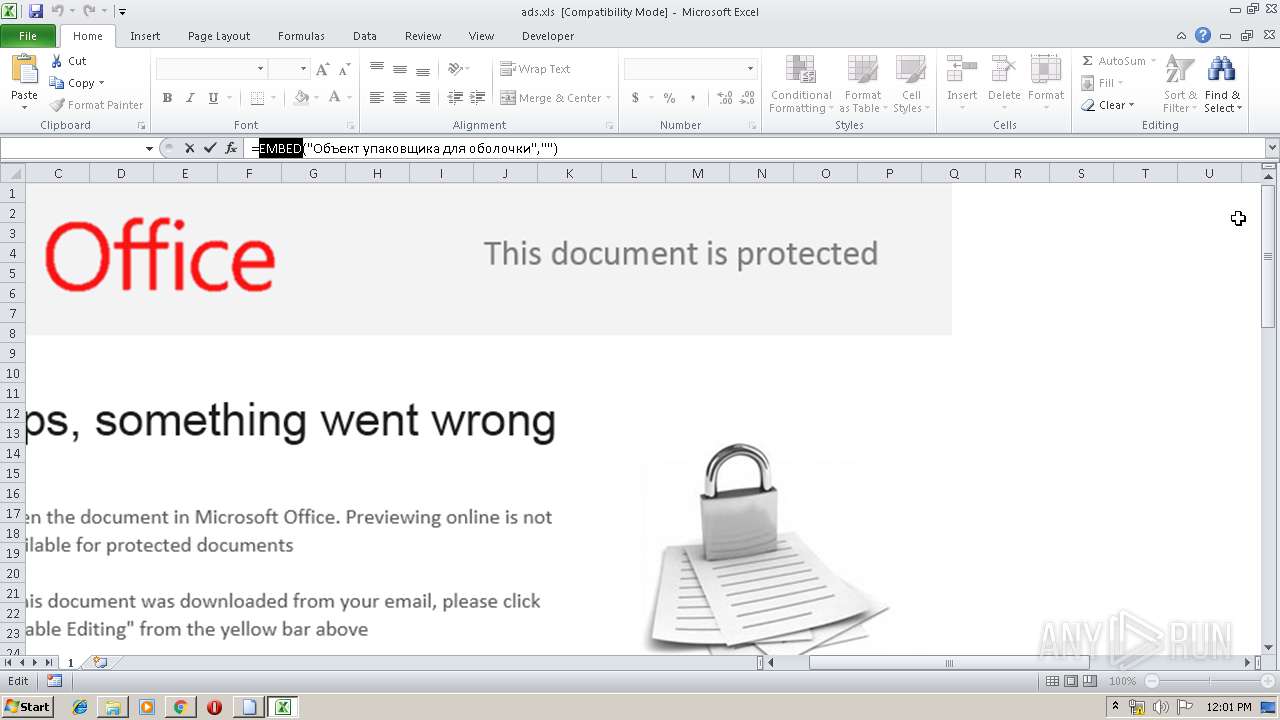
MALICIOUS
Loads dropped or rewritten executable
- EXCEL.EXE (PID: 2056)
Executable content was dropped or overwritten
- EXCEL.EXE (PID: 2056)
SUSPICIOUS
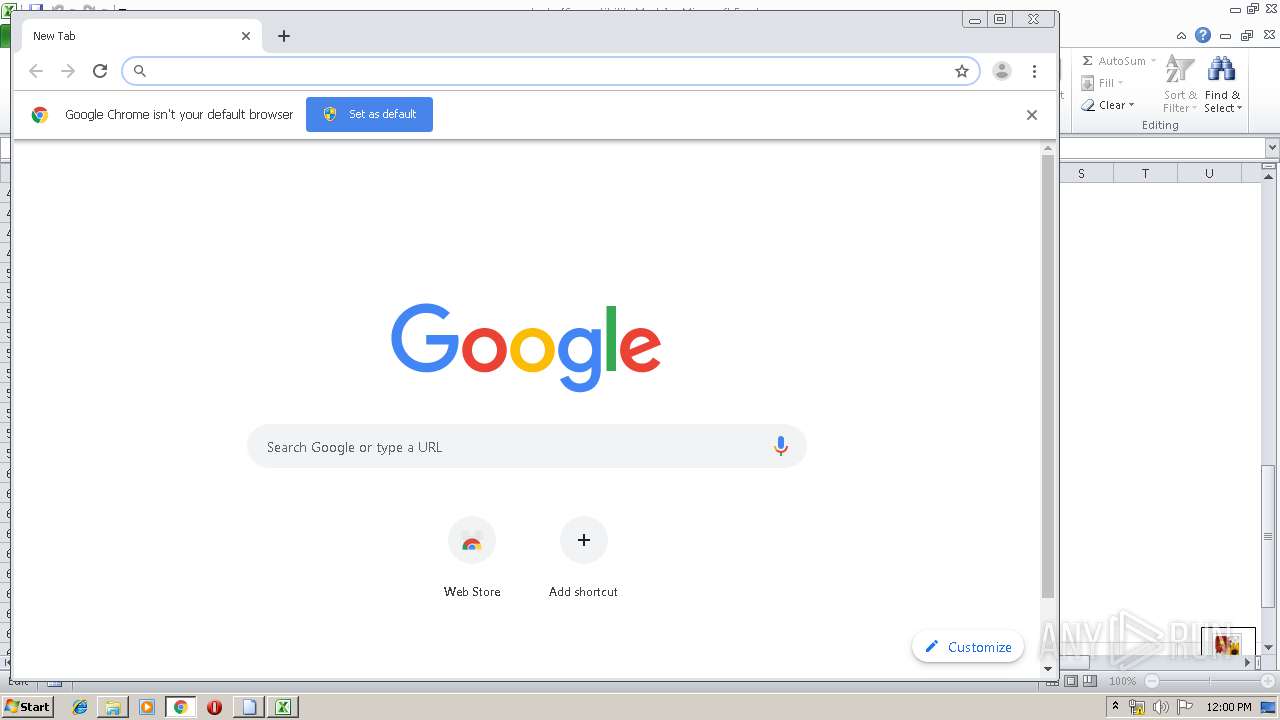
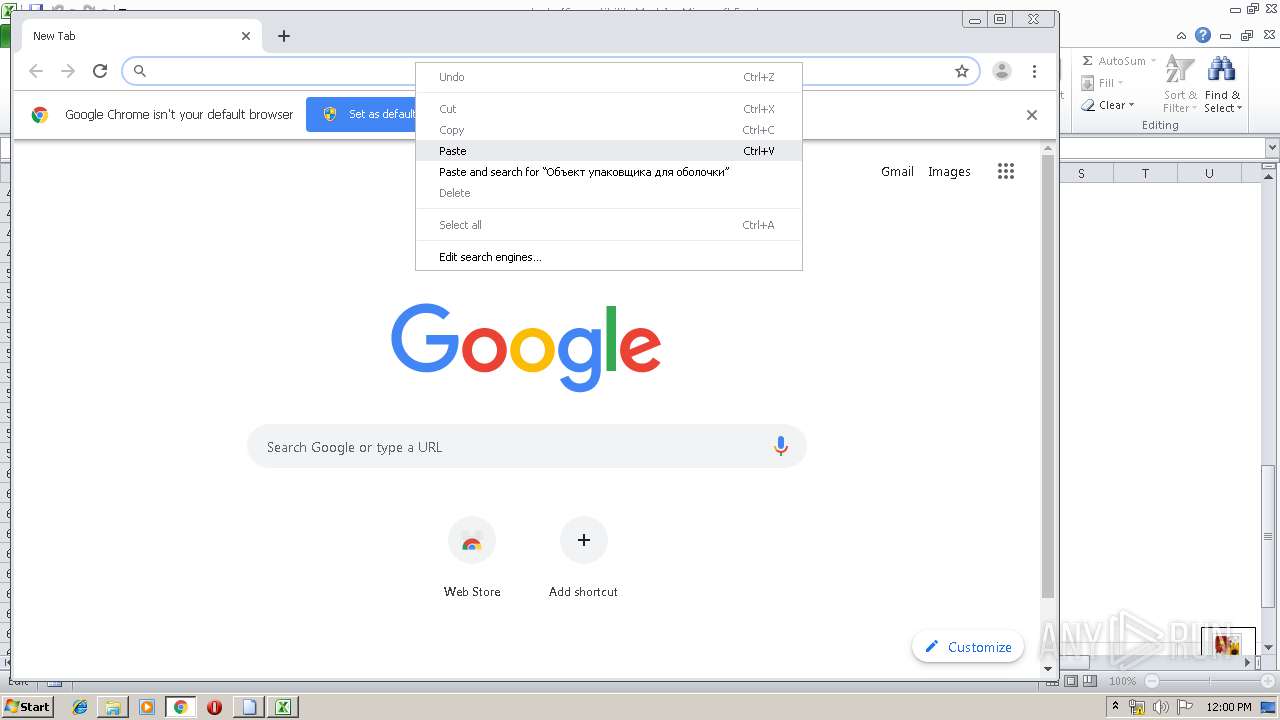
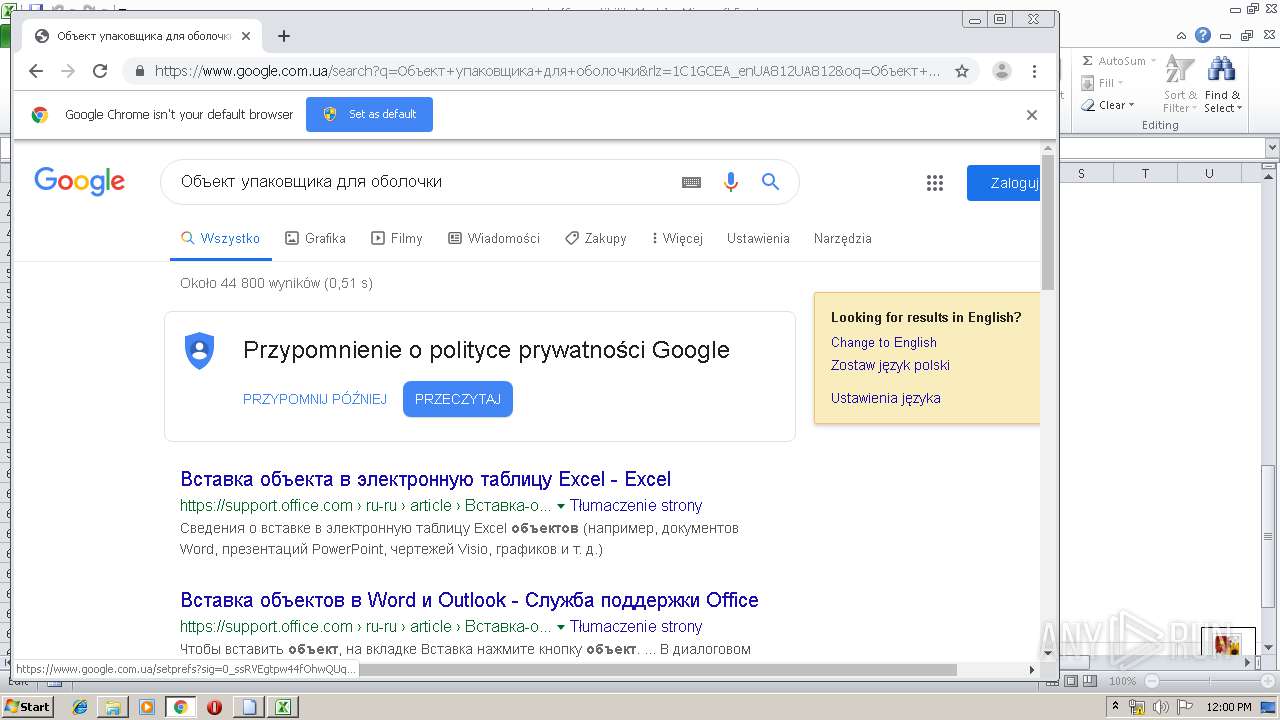
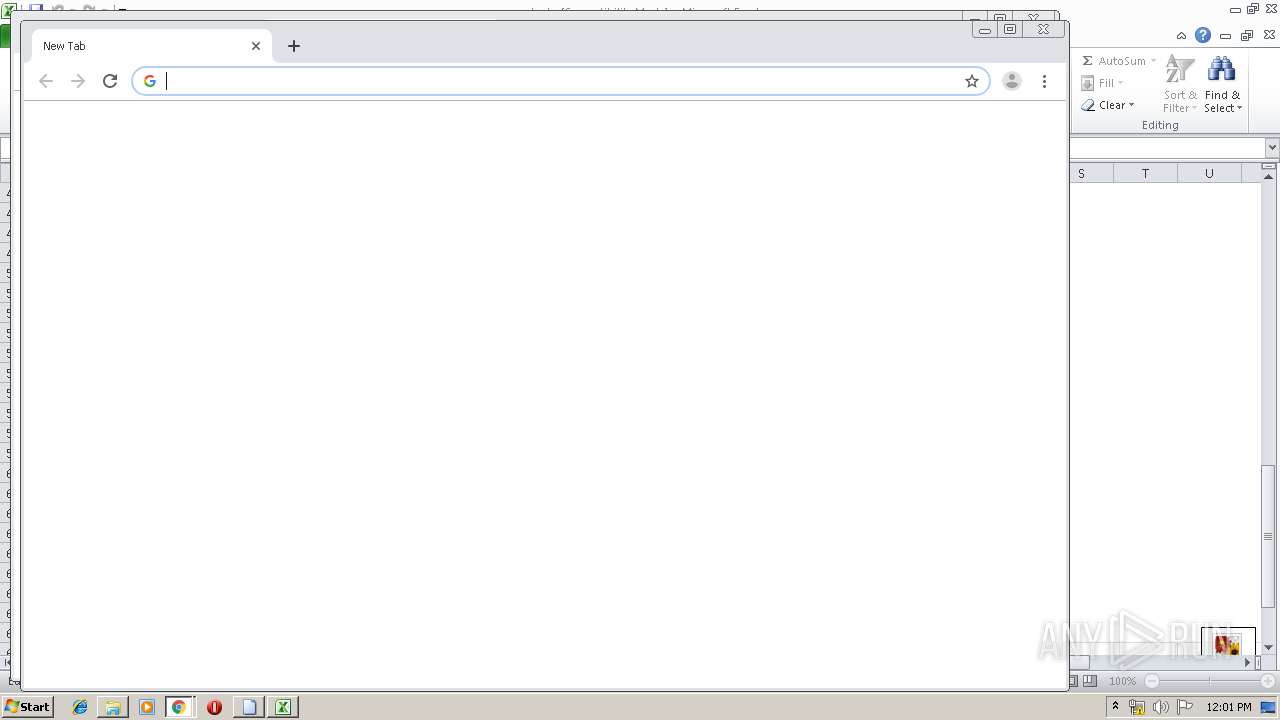
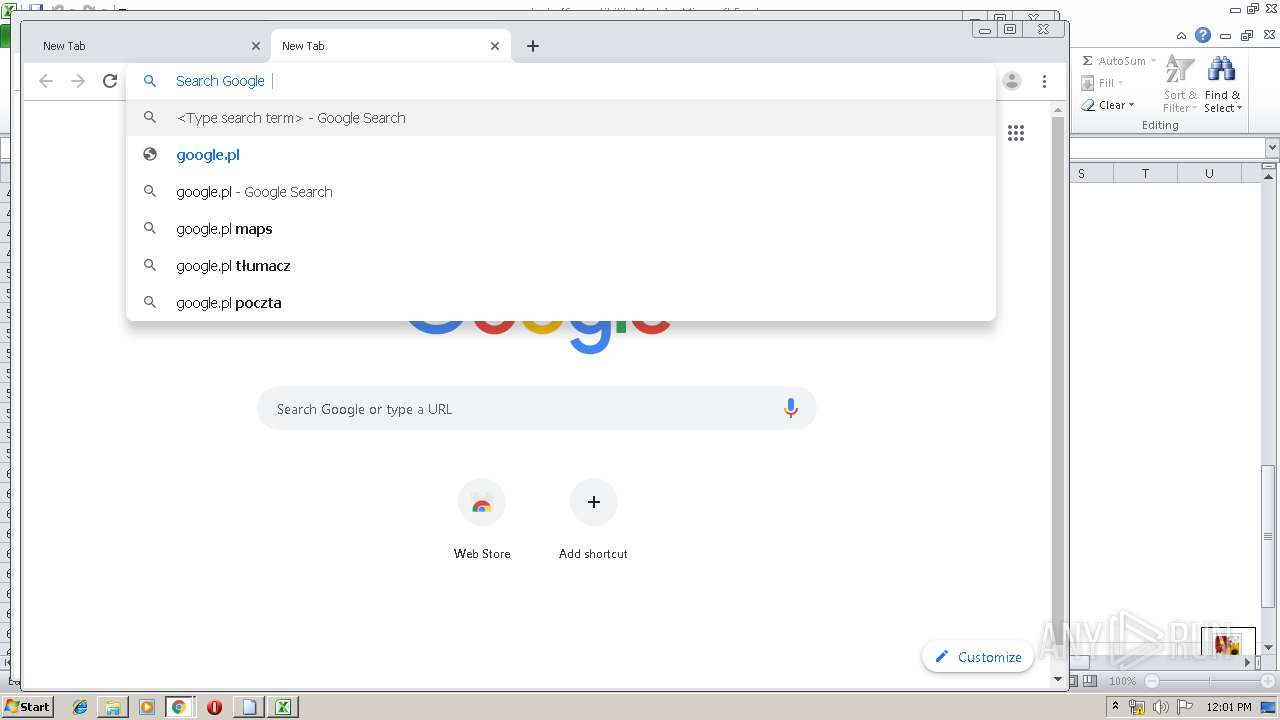
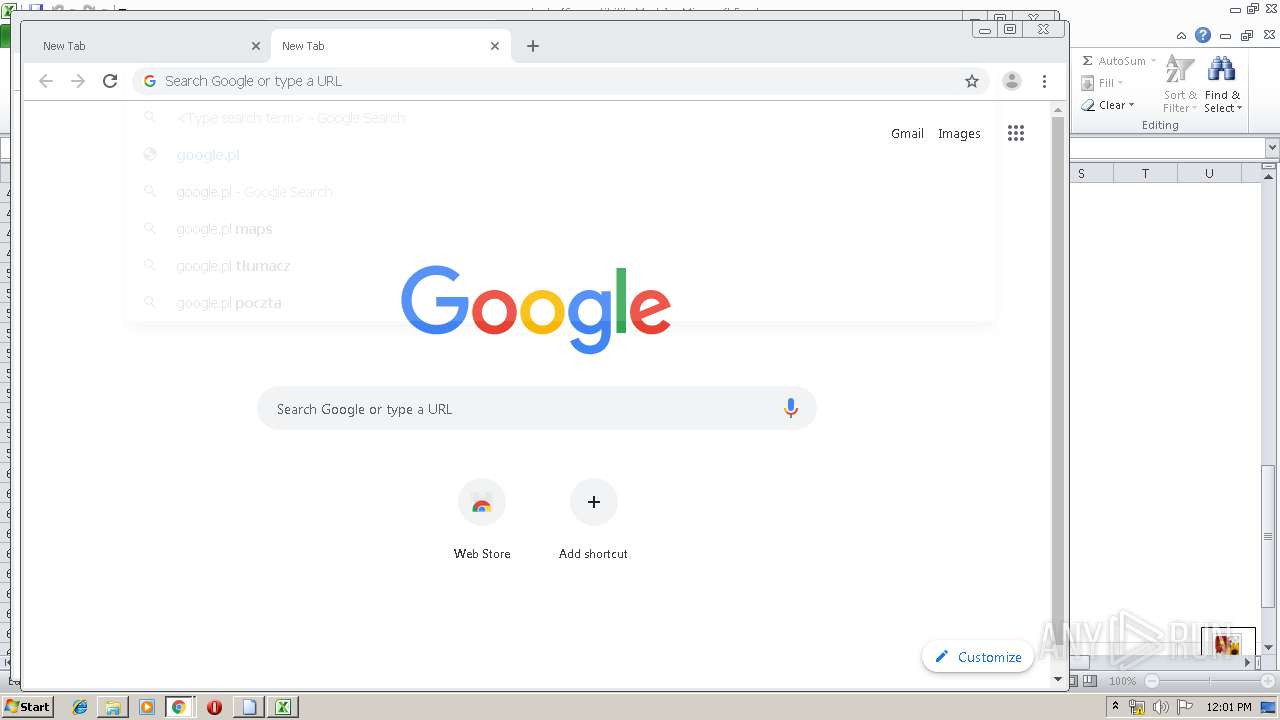
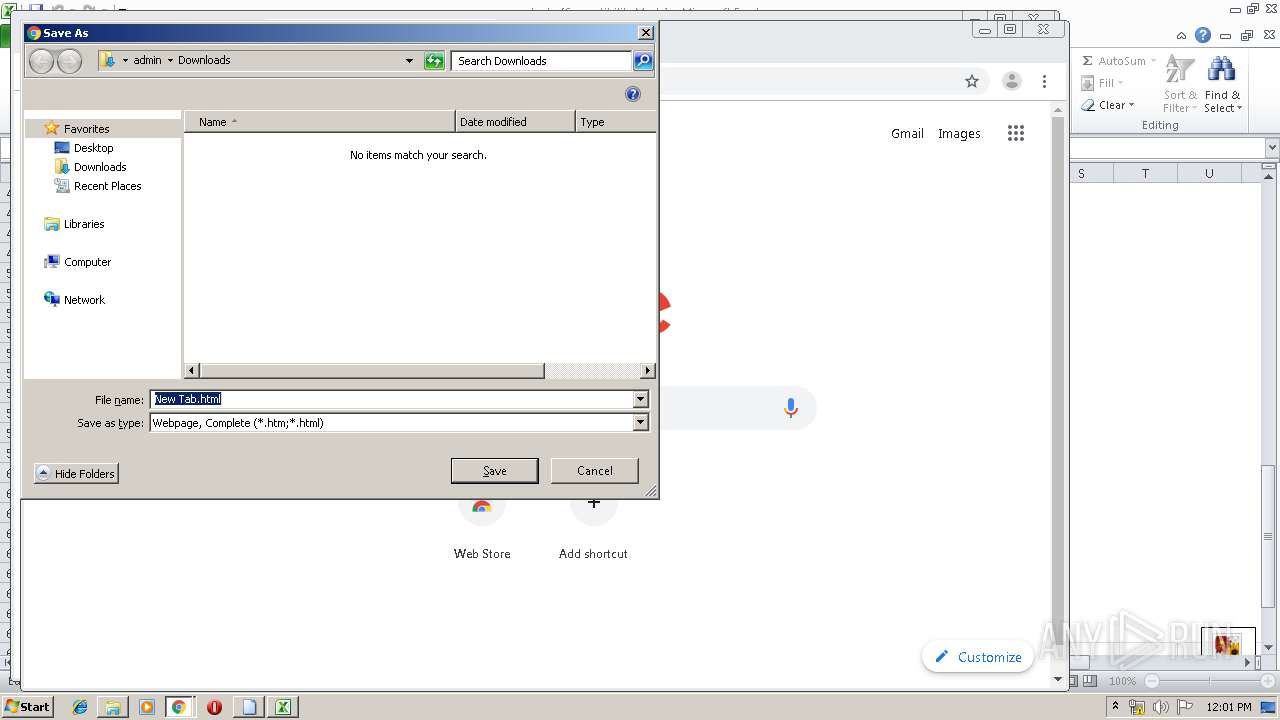
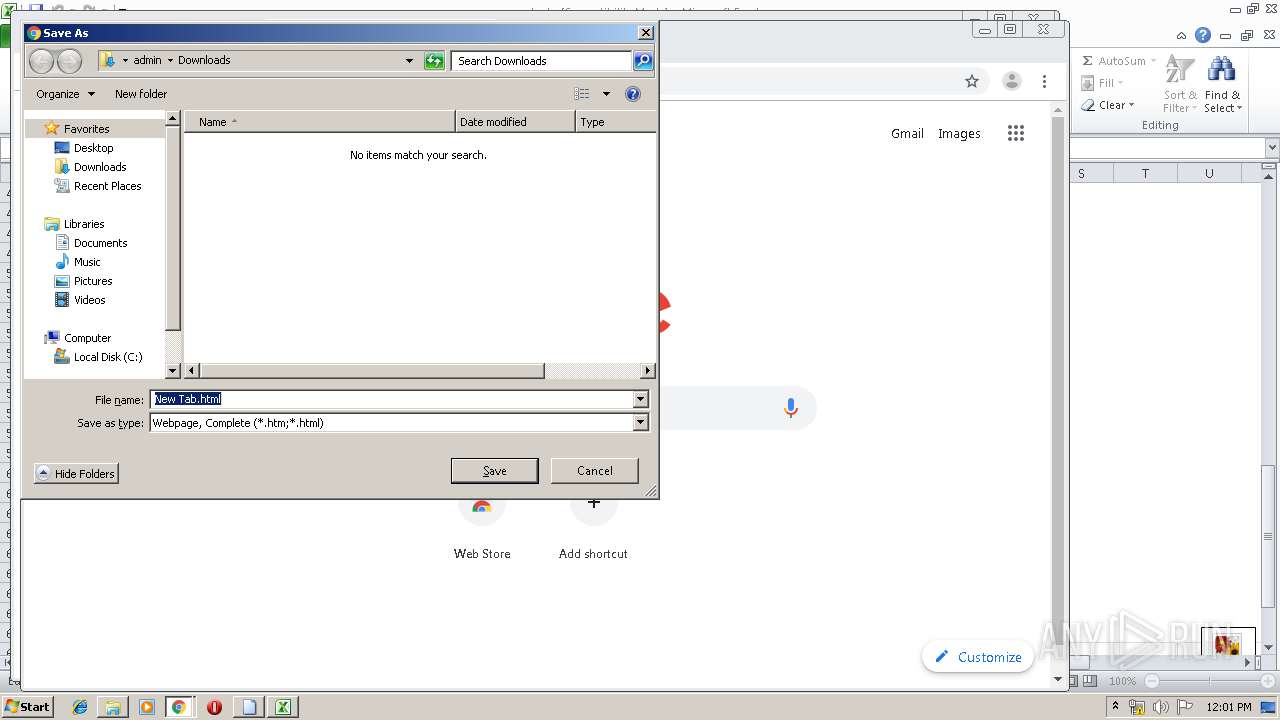
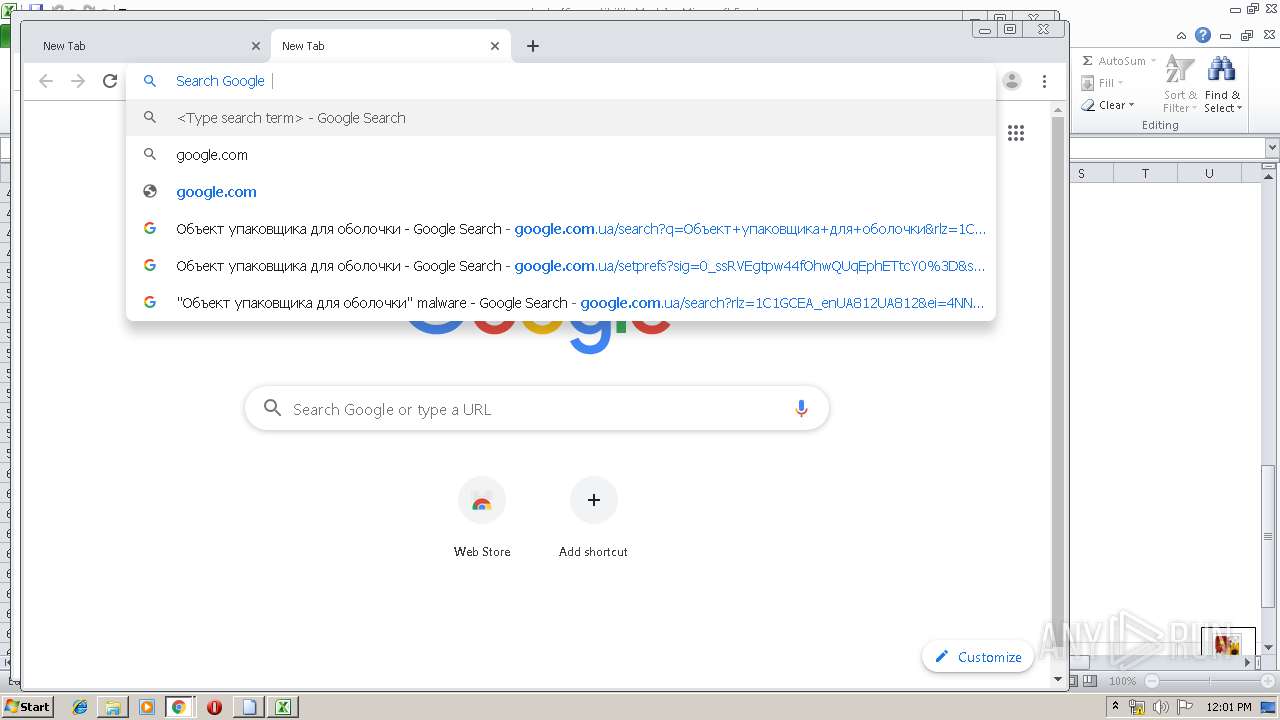
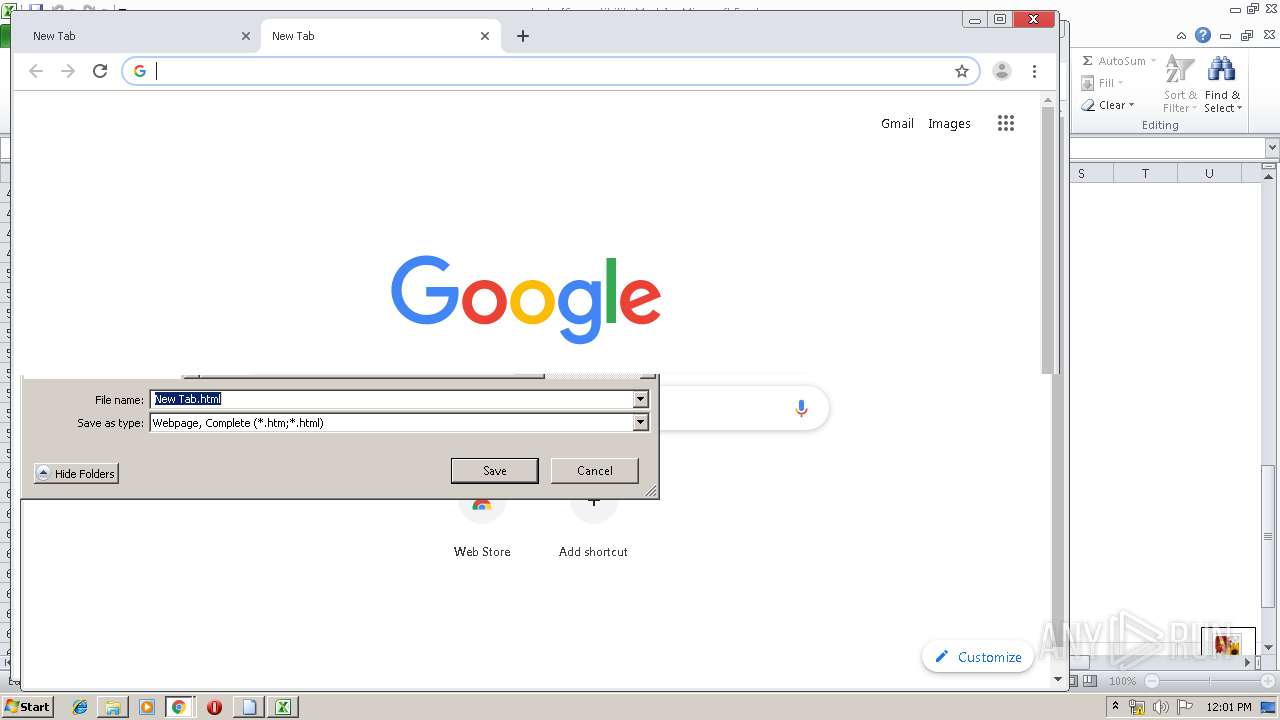
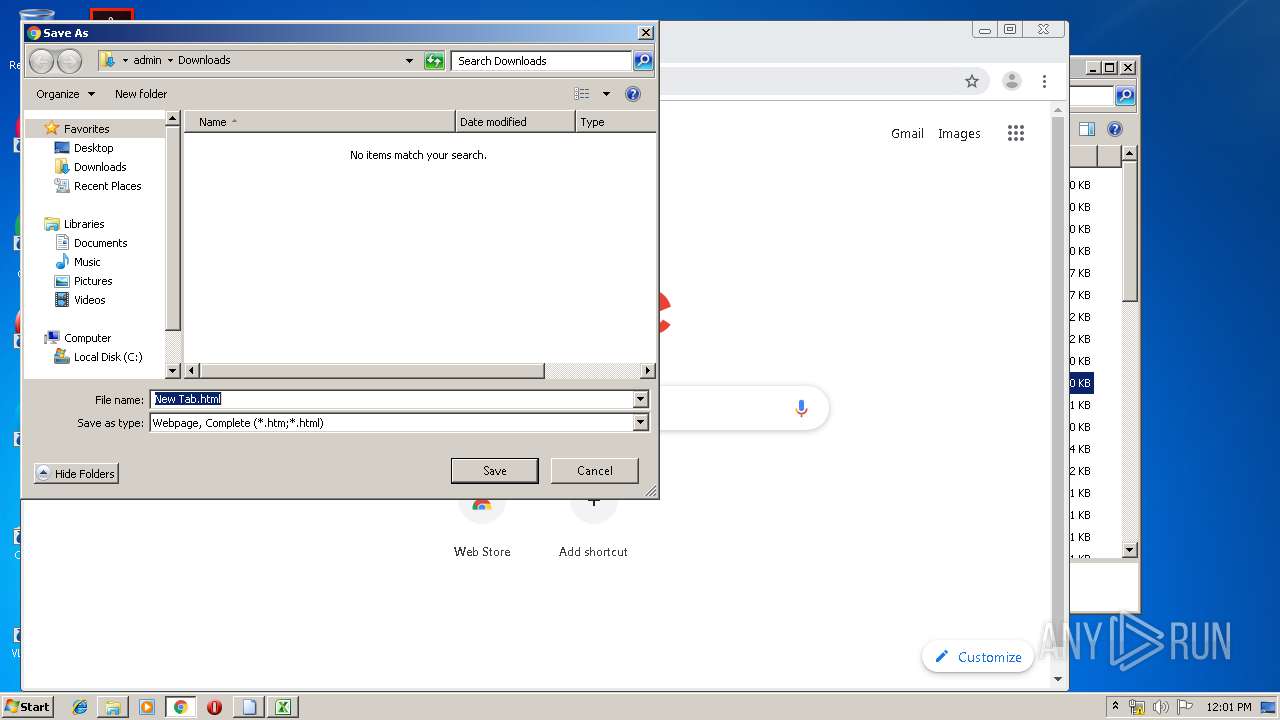
Modifies files in Chrome extension folder
- chrome.exe (PID: 2160)
INFO
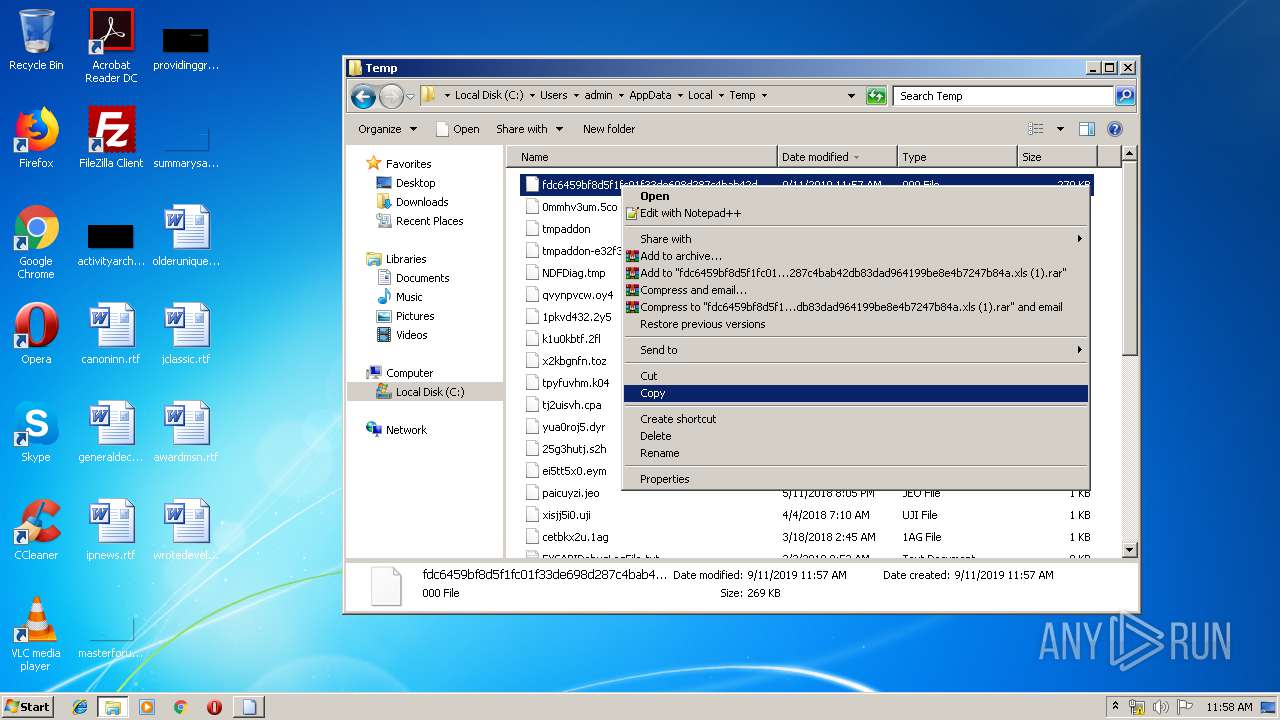
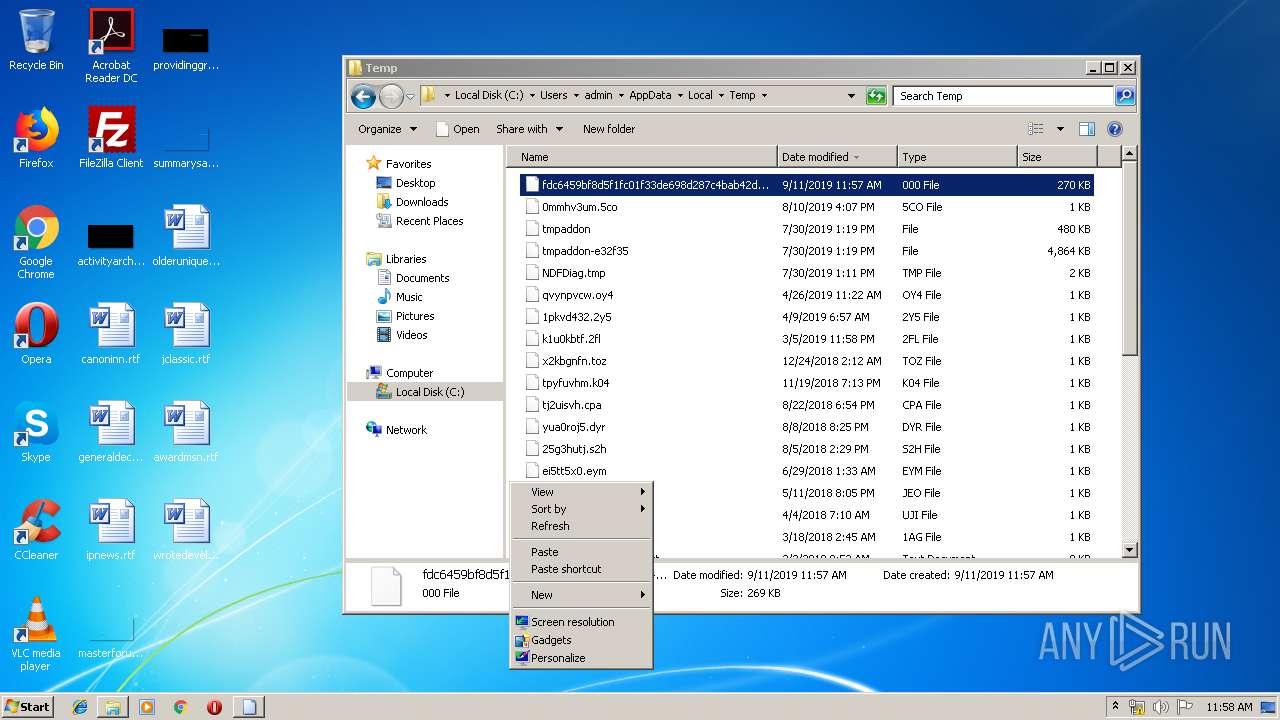
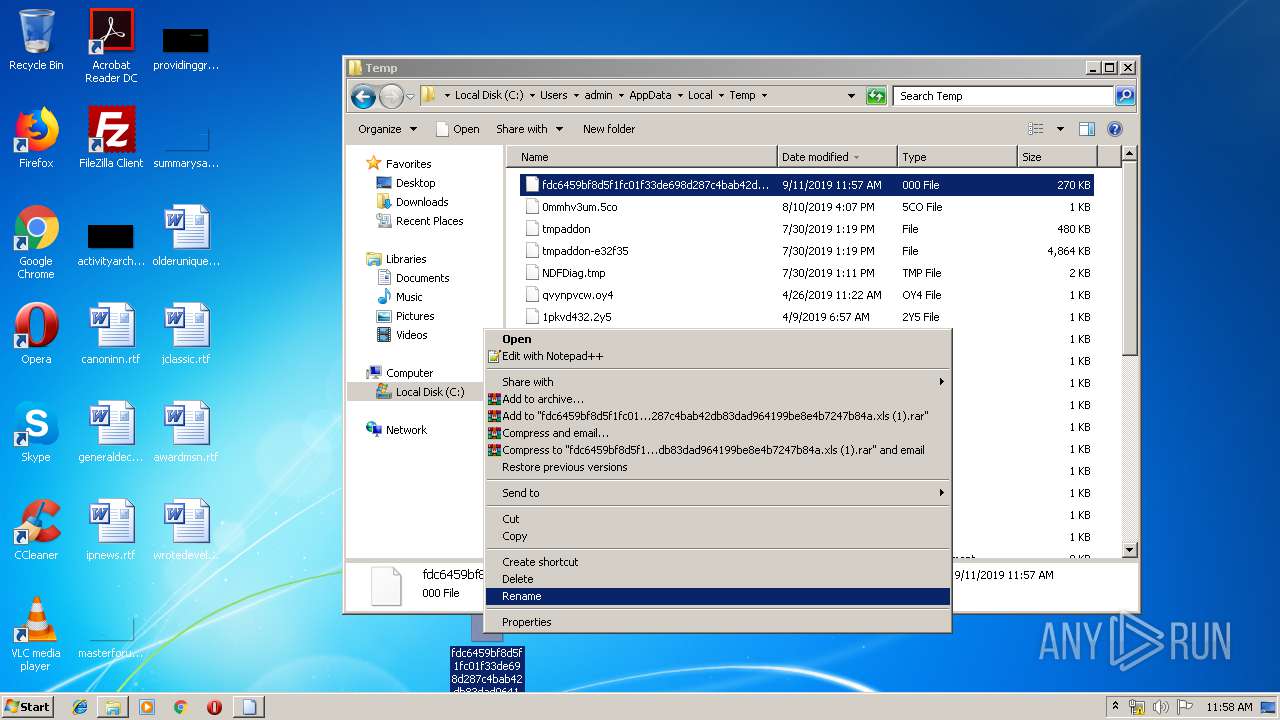
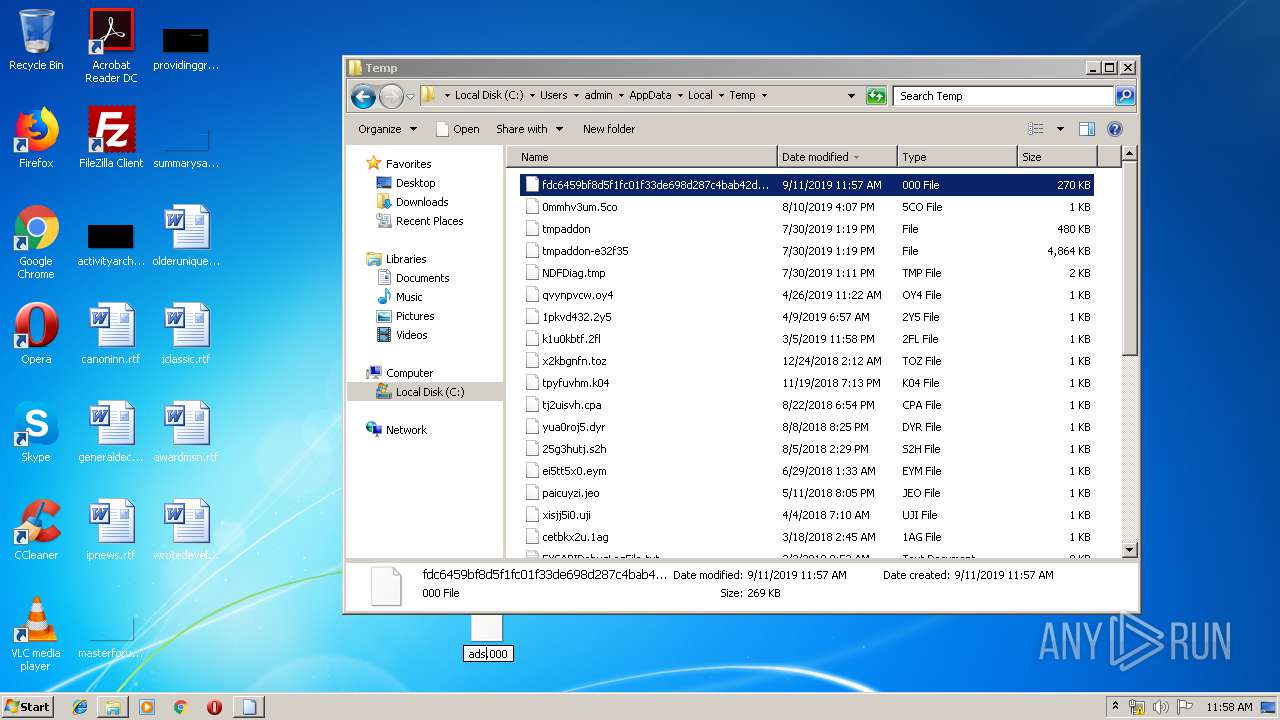
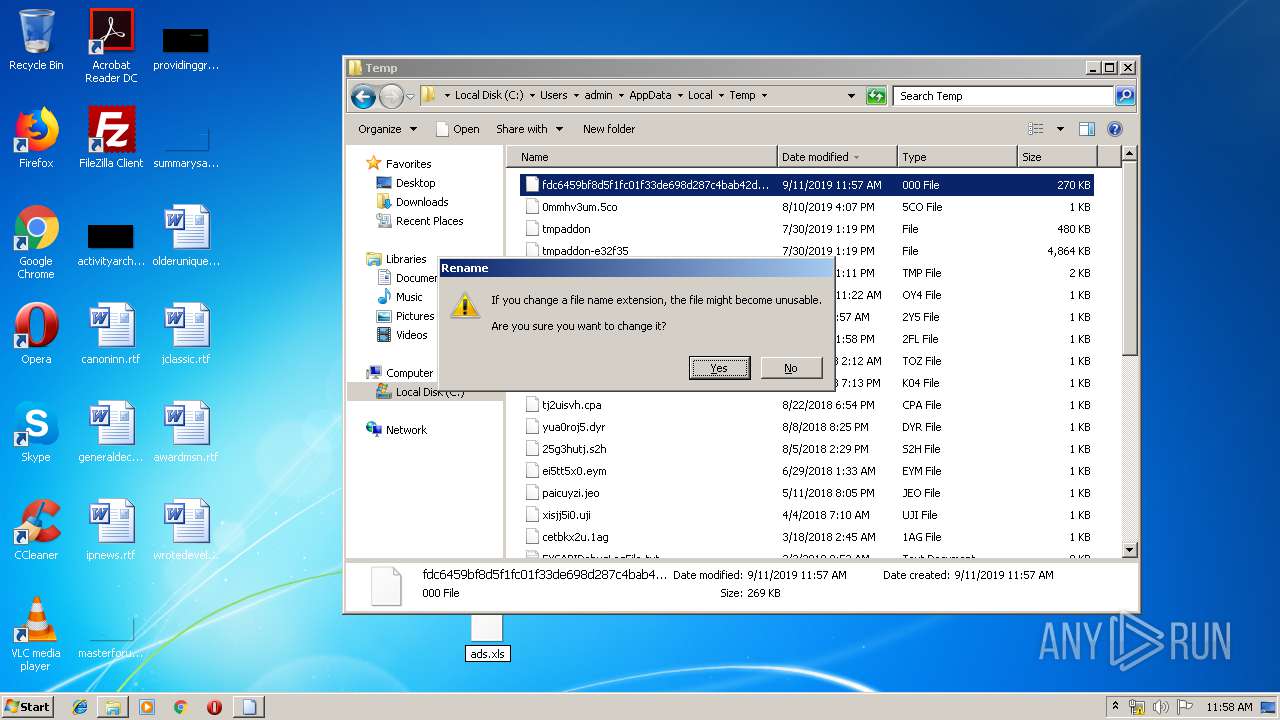
Manual execution by user
- explorer.exe (PID: 2428)
- chrome.exe (PID: 2860)
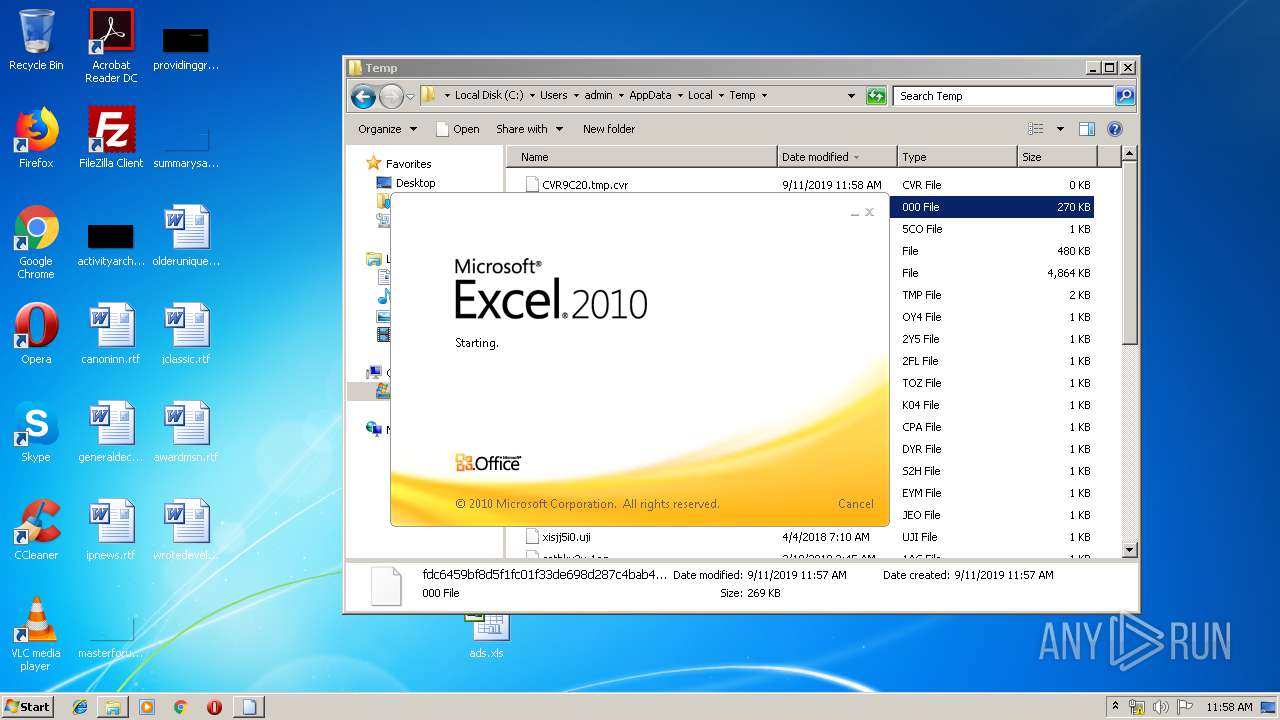
- EXCEL.EXE (PID: 2056)
- chrome.exe (PID: 2160)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2056)
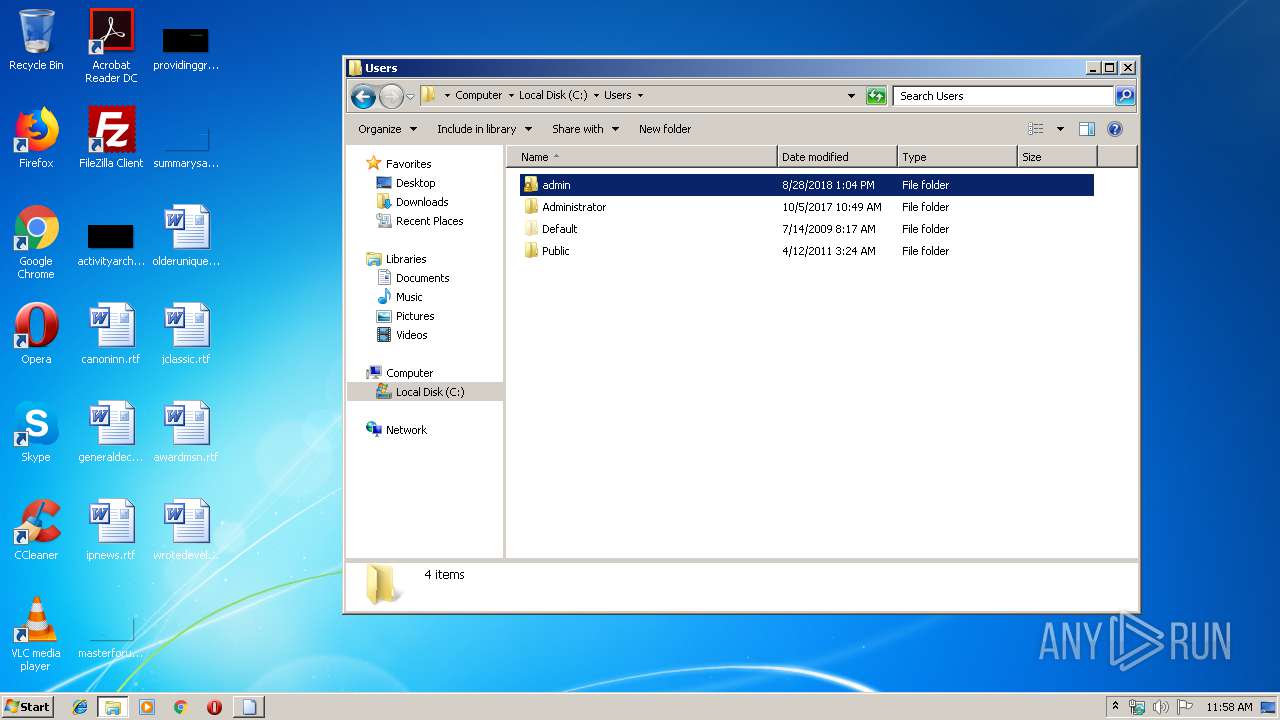
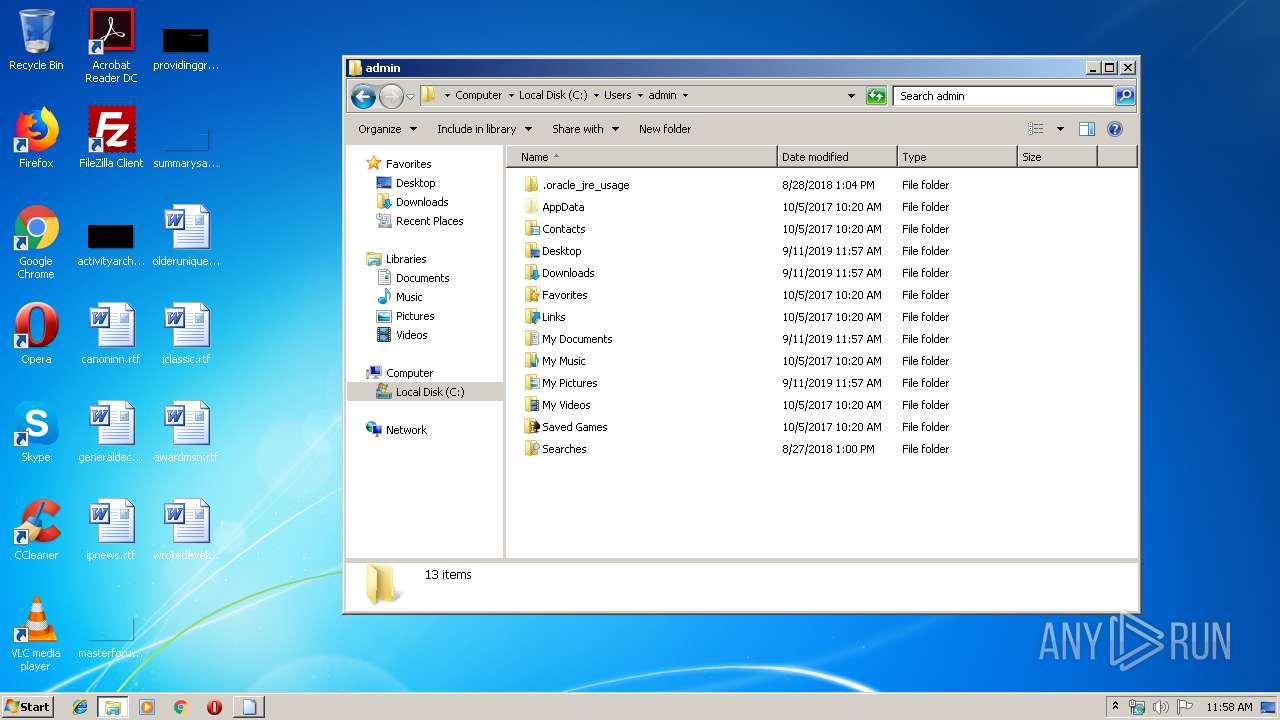
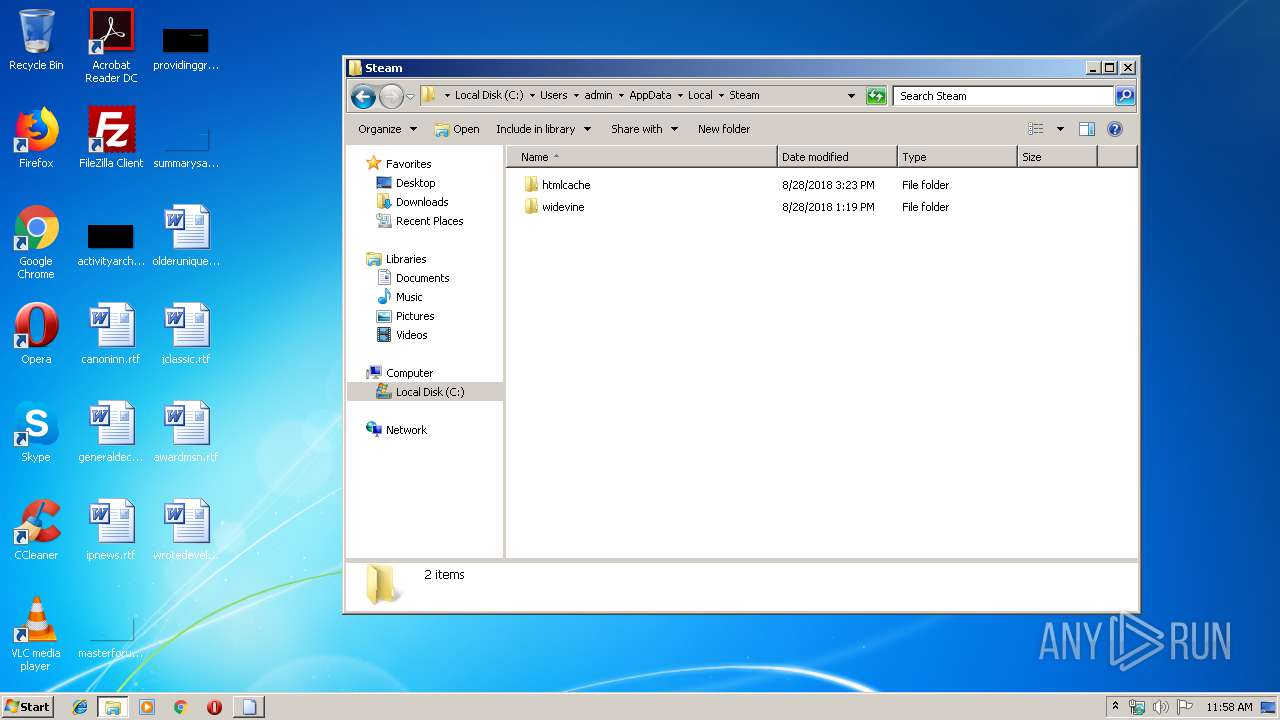
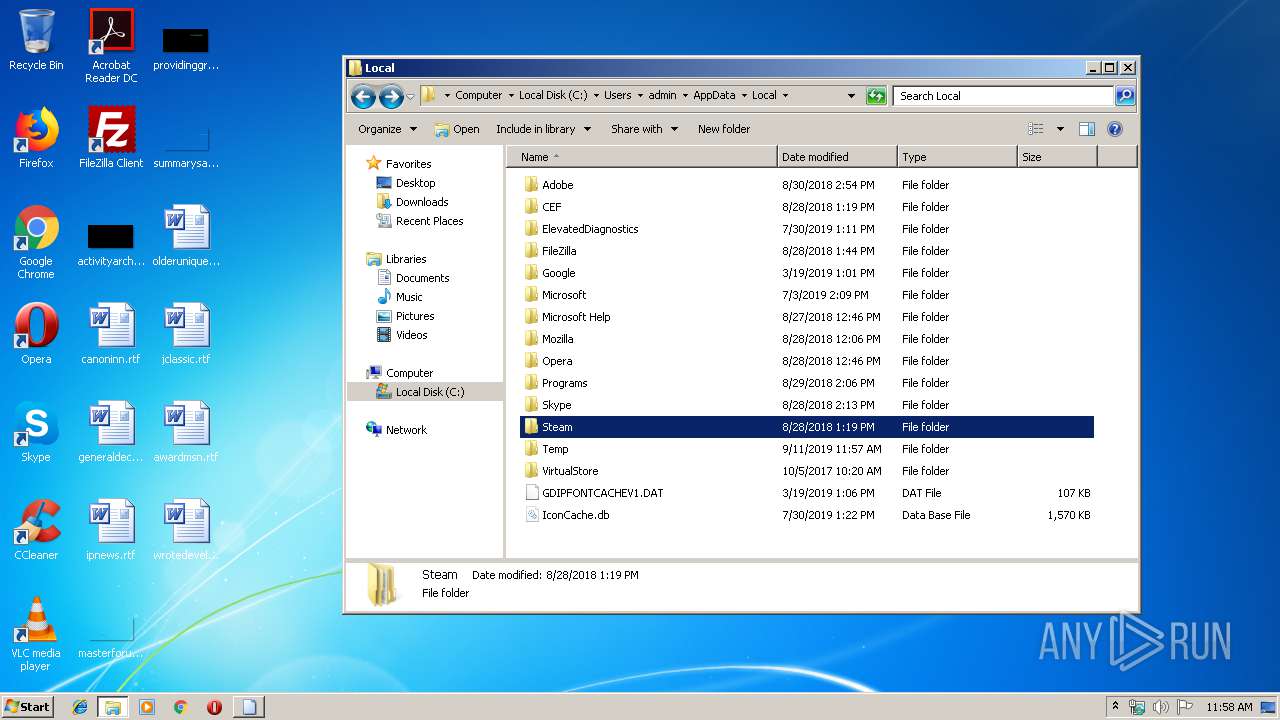
Creates files in the user directory
- EXCEL.EXE (PID: 2056)
Application launched itself
- chrome.exe (PID: 2160)
- chrome.exe (PID: 2860)
Reads settings of System Certificates
- chrome.exe (PID: 3344)
Reads the hosts file
- chrome.exe (PID: 2160)
- chrome.exe (PID: 2860)
- chrome.exe (PID: 3984)
- chrome.exe (PID: 3344)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (48) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (alternate) (39.2) |
EXIF
FlashPix
| CompObjUserTypeLen: | 12 |
|---|---|
| CompObjUserType: | OLE Package |
| Title: | kTS |
| Subject: | T |
| Author: | L |
| LastModifiedBy: | Microsoft Office |
| RevisionNumber: | 105 |
| Software: | Microsoft Excel |
| TotalEditTime: | 1.1 days |
| CreateDate: | 2019:08:30 09:14:50 |
| ModifyDate: | 2019:09:09 11:37:42 |
| Pages: | 4 |
| Words: | 3365 |
| Characters: | 1235 |
| Security: | None |
| CodePage: | Windows Cyrillic |
| Company: | - |
| Bytes: | 56685 |
| Lines: | 126 |
| Paragraphs: | 93 |
| AppVersion: | 11.9999 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | 1 |
| HeadingPairs: |
|
Total processes
96
Monitored processes
57
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,13755882730066501012,1763367571929961625,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5533513746603728580 --mojo-platform-channel-handle=4124 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,13755882730066501012,1763367571929961625,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11269658511575966616 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3556 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,5958008921734103568,2600065924069931565,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6303335861450000975 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,5958008921734103568,2600065924069931565,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14338317749951537496 --mojo-platform-channel-handle=3496 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,13755882730066501012,1763367571929961625,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1328987036788615596 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,5958008921734103568,2600065924069931565,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11904633476804508980 --mojo-platform-channel-handle=3012 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,5958008921734103568,2600065924069931565,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10656199583970209907 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2464 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,13755882730066501012,1763367571929961625,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2759356380499644693 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3724 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,13755882730066501012,1763367571929961625,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13274686176326593348 --mojo-platform-channel-handle=4272 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=984,13755882730066501012,1763367571929961625,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2030282325280723391 --mojo-platform-channel-handle=1028 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 622
Read events
2 365
Write events
230
Delete events
27
Modification events
| (PID) Process: | (2056) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | <; |
Value: 203C3B0008080000010000000000000000000000 | |||
| (PID) Process: | (2056) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2056) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2056) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 080800008228D3DA8F68D50100000000 | |||
| (PID) Process: | (2056) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | <; |
Value: 203C3B0008080000010000000000000000000000 | |||
| (PID) Process: | (2056) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2056) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2056) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2056) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2056) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\17A1A0 |
| Operation: | write | Name: | 17A1A0 |
Value: 04000000080800001E00000043003A005C00550073006500720073005C00610064006D0069006E005C004400650073006B0074006F0070005C006100640073002E0078006C007300000000001700000043003A005C00550073006500720073005C00610064006D0069006E005C004400650073006B0074006F0070005C00010000000000000010FFD6DB8F68D501A0A11700A0A1170000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
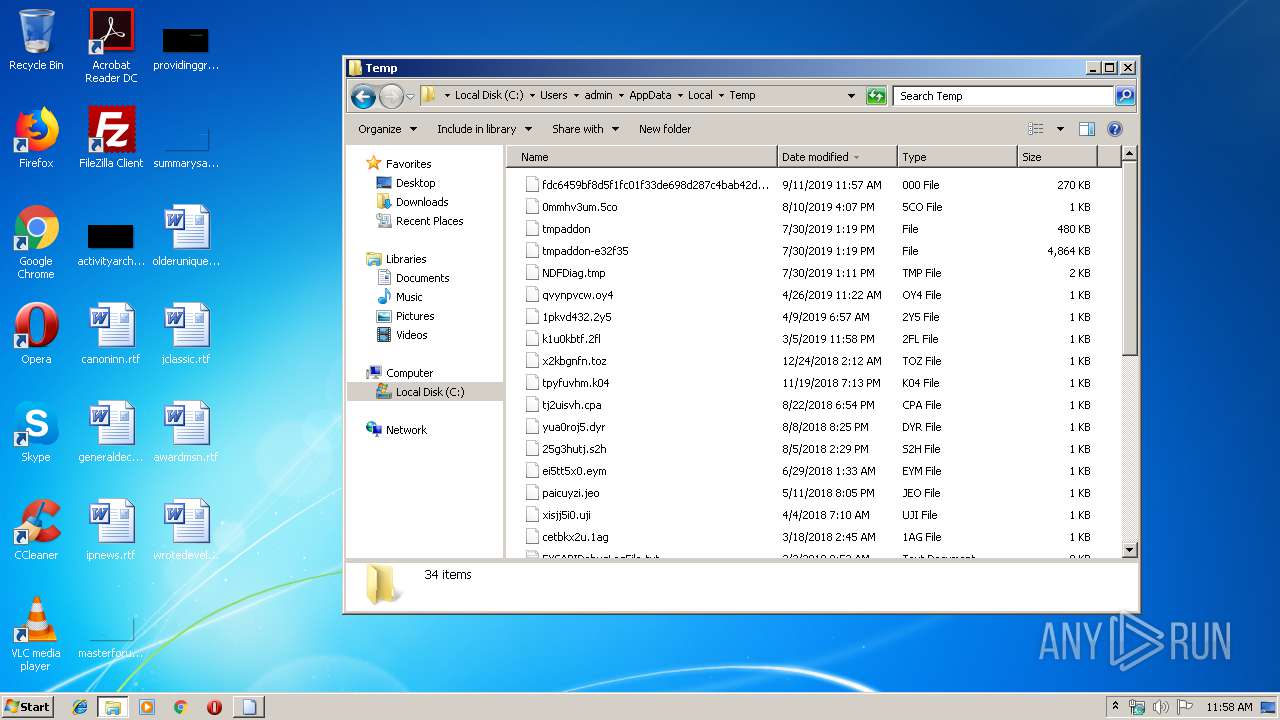
Executable files
1
Suspicious files
80
Text files
288
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
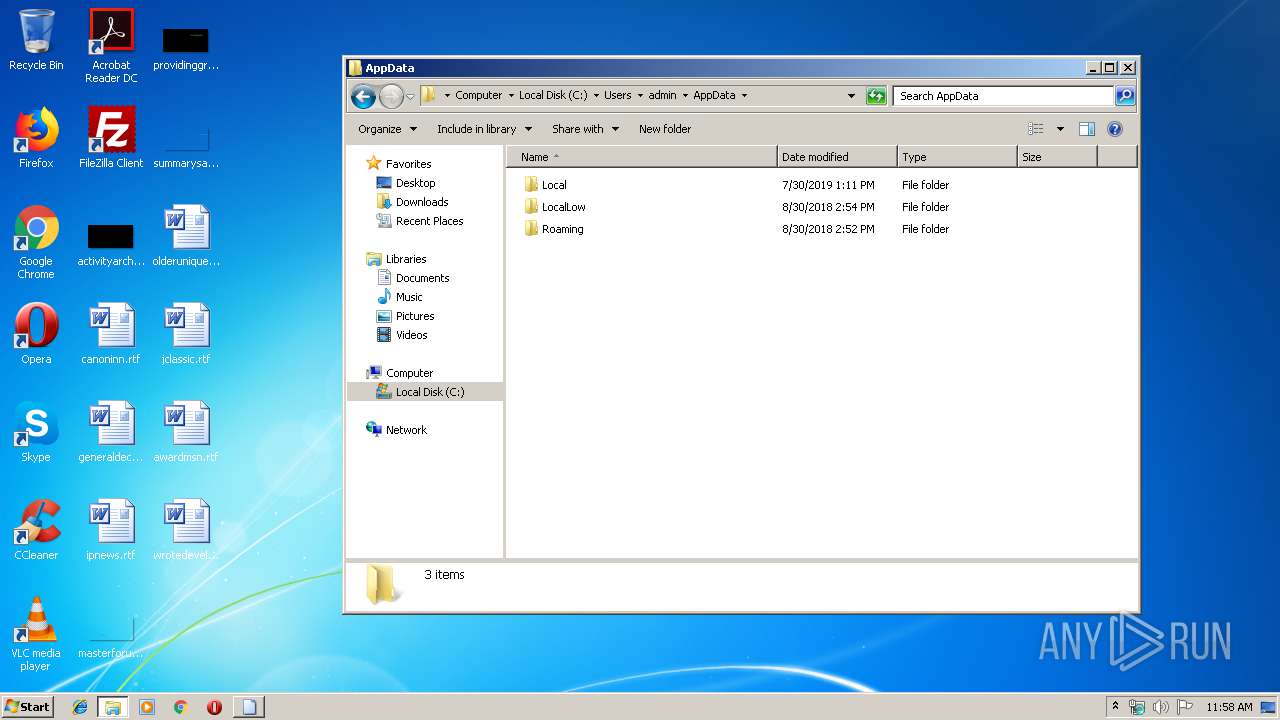
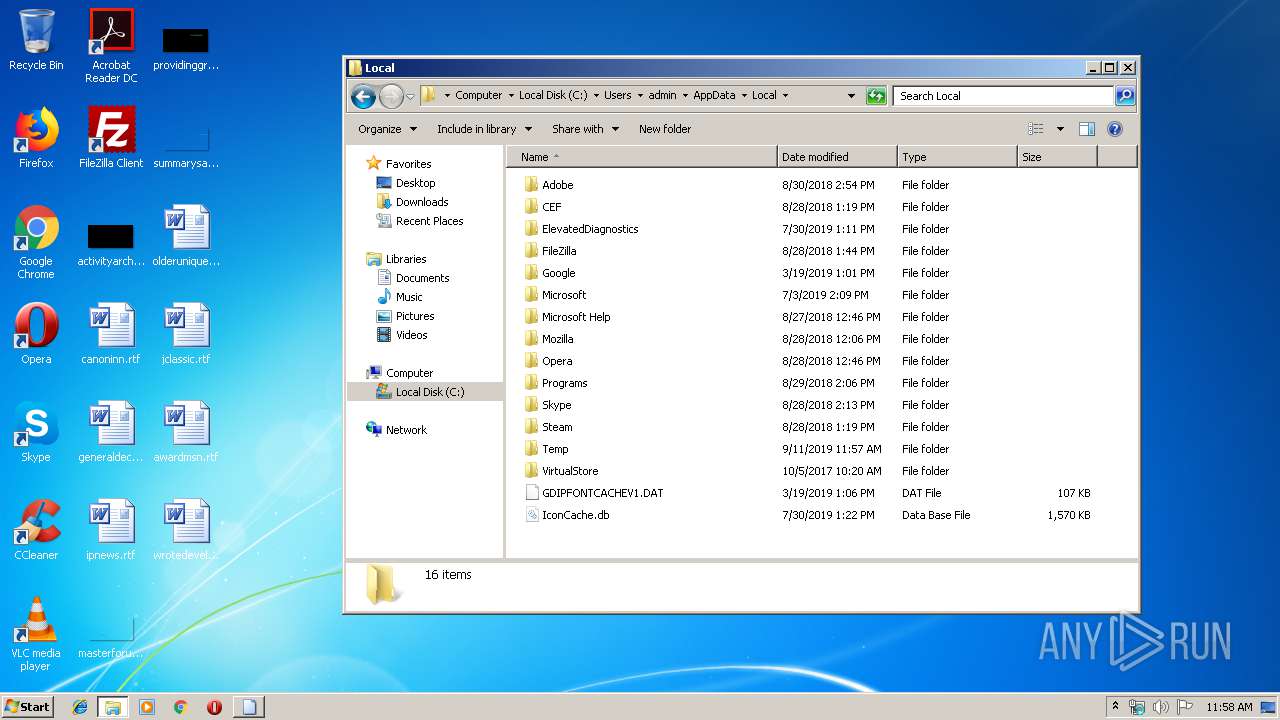
| 2056 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR9C20.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2056 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\VBA54B.tmp | — | |
MD5:— | SHA256:— | |||
| 2056 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\VBA54A.tmp | — | |
MD5:— | SHA256:— | |||
| 2056 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DFE54960E9E300120B.TMP | — | |
MD5:— | SHA256:— | |||
| 2056 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\D5A71000 | — | |
MD5:— | SHA256:— | |||
| 2056 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF521621D909FEA466.TMP | — | |
MD5:— | SHA256:— | |||
| 2056 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~$13.xlsx | — | |
MD5:— | SHA256:— | |||
| 2056 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF53BF1A3829C6A58F.TMP | — | |
MD5:— | SHA256:— | |||
| 2056 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\13.xlsx | document | |
MD5:— | SHA256:— | |||
| 2056 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\ads.xls.LNK | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
35
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3984 | chrome.exe | GET | 204 | 172.217.9.163:80 | http://csi.gstatic.com/csi?v=3&s=gapi_module&action=gapi_iframes__googleapis_cli12&it=mli.291,mei.21&srt=31&tbsrt=2514&tran=15&e=abc_l0,abc_m0,abc_pgapi_iframes__googleapis_cli12,abc_u0&rt= | US | — | — | whitelisted |
3984 | chrome.exe | GET | 302 | 172.217.22.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
3984 | chrome.exe | GET | 200 | 173.194.150.135:80 | http://r1---sn-f5f7ln7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=212.7.222.142&mm=28&mn=sn-f5f7ln7s&ms=nvh&mt=1568198783&mv=u&mvi=0&pl=23&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3984 | chrome.exe | 216.58.208.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3984 | chrome.exe | 172.217.22.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
3984 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
3984 | chrome.exe | 172.217.16.131:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2056 | EXCEL.EXE | 212.80.216.172:443 | update365-office-ens.com | — | — | unknown |
3984 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3984 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3984 | chrome.exe | 216.58.208.33:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3984 | chrome.exe | 172.217.22.14:443 | apis.google.com | Google Inc. | US | whitelisted |
3984 | chrome.exe | 173.194.150.135:80 | r1---sn-f5f7ln7s.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
update365-office-ens.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
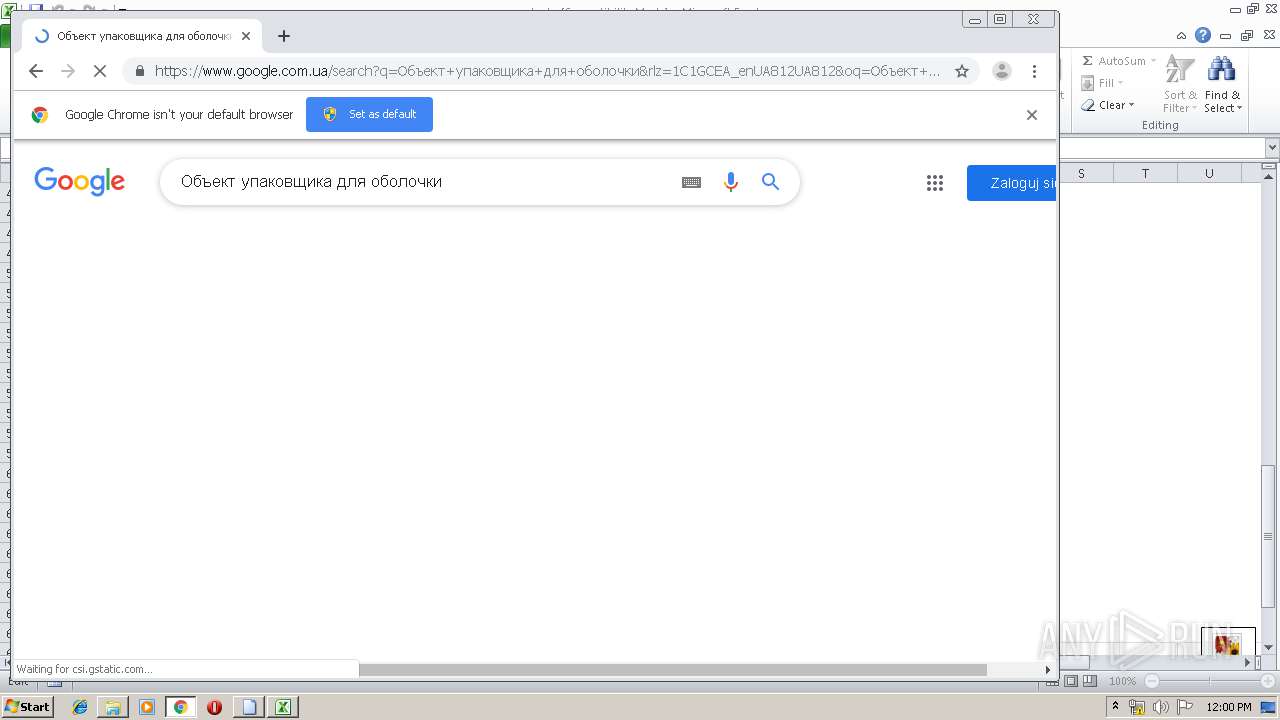
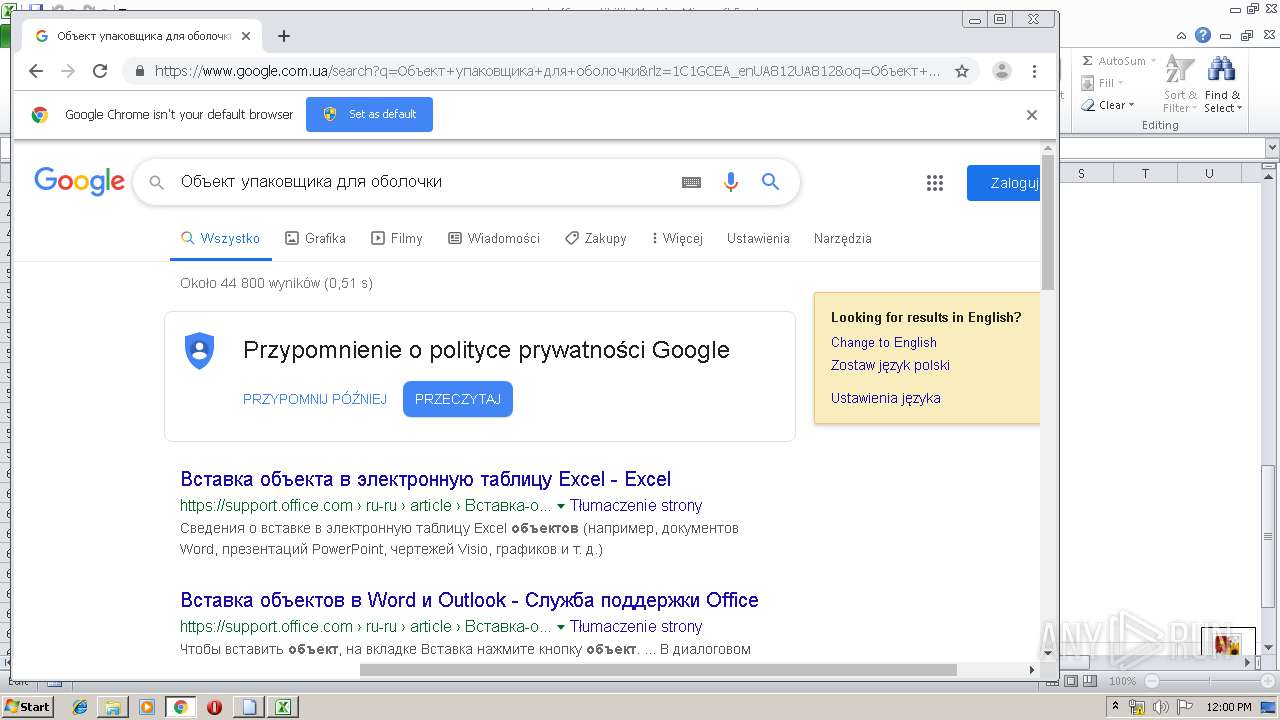
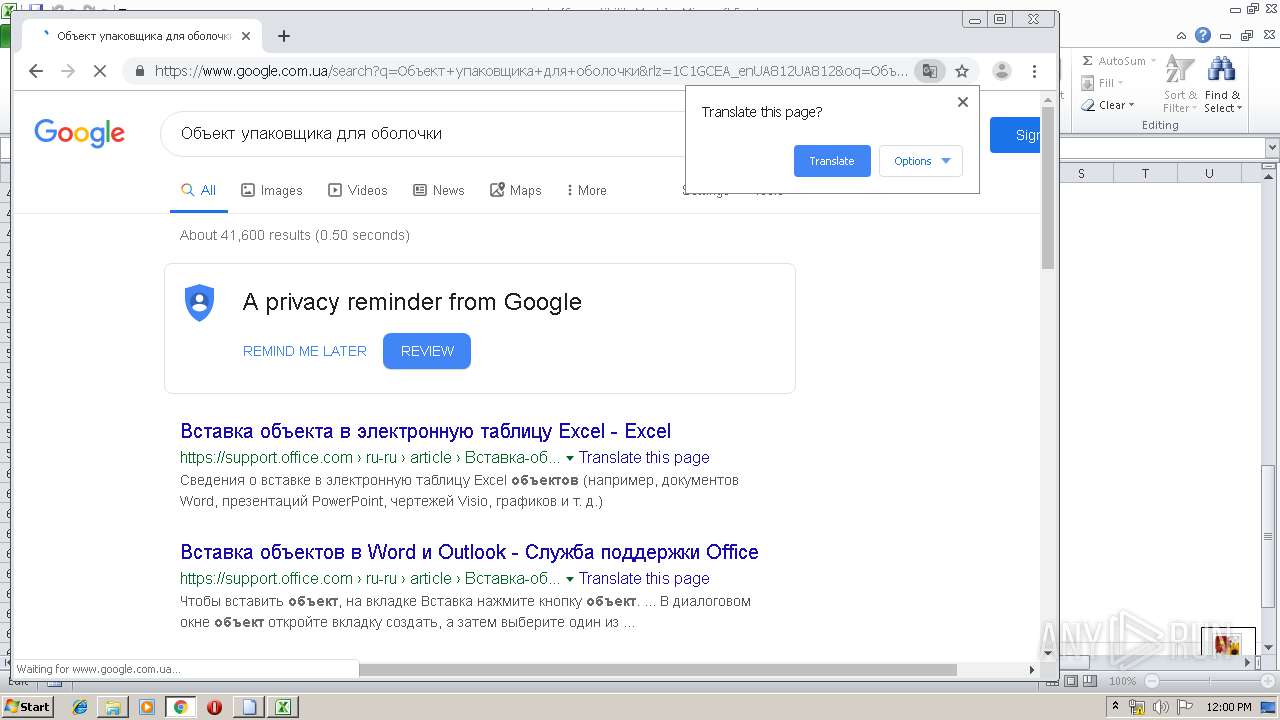
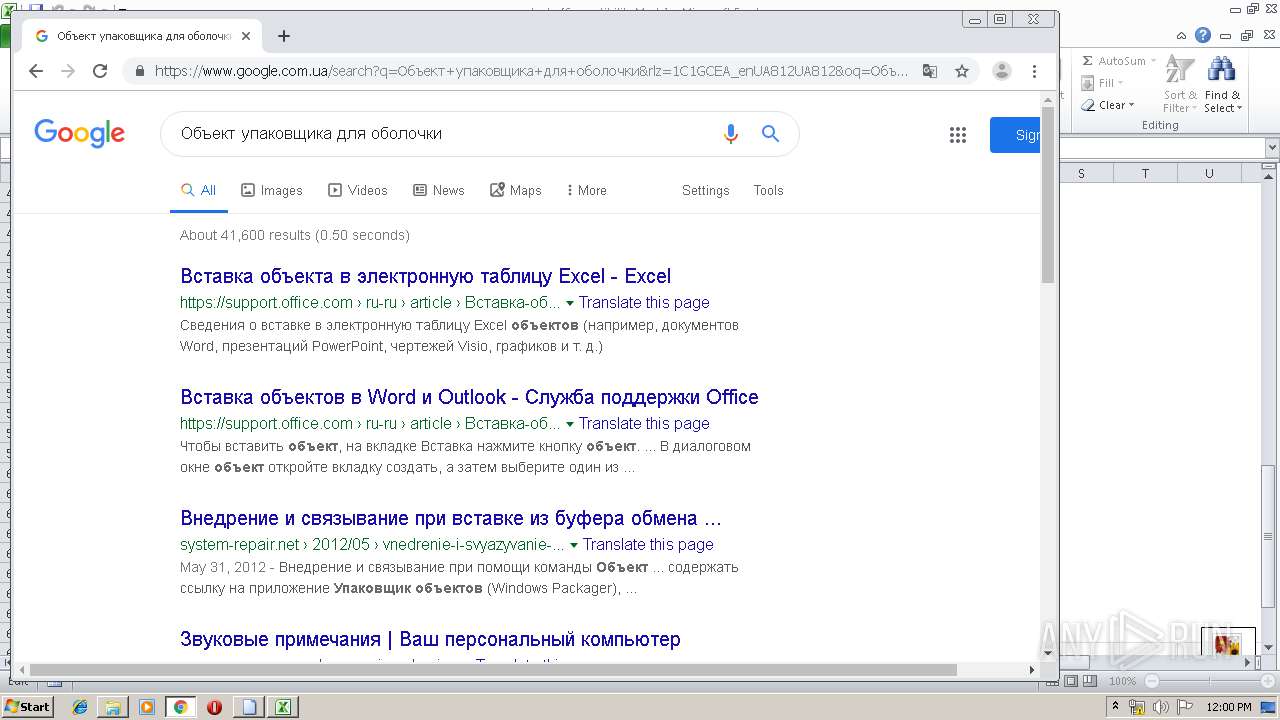
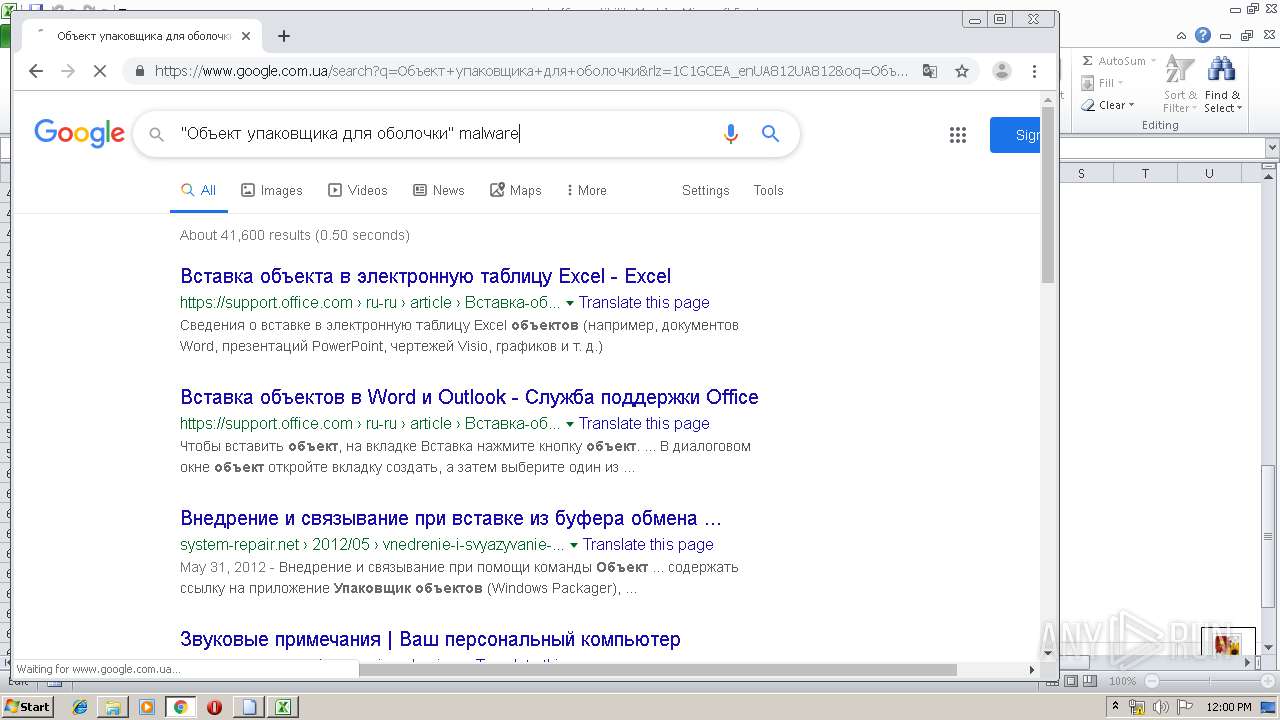
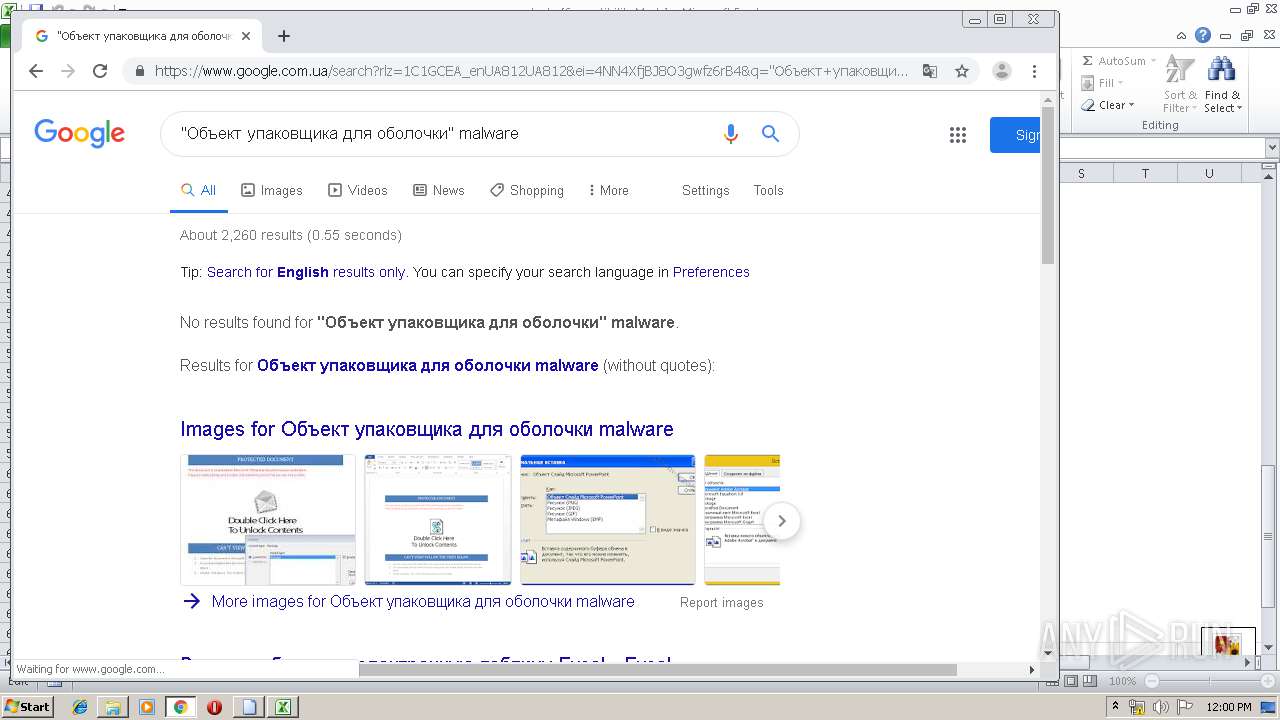
www.google.com.ua |
| whitelisted |
clients2.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |