| URL: | https://guipleaderspif1986.blogspot.qa/ |
| Full analysis: | https://app.any.run/tasks/5e77cf00-ca0c-4f06-9bf2-d802821e12c2 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 06:42:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B7AEFEB2685AACA0B21EF3EF3C01180F |
| SHA1: | 7112E68D36822B85813B39581A62ADF5AD65F8A2 |
| SHA256: | FDC3AB911E3269294F41B8480E7FB8666BDD45494664048E74BC5ECF28ED3D45 |
| SSDEEP: | 3:N8xQhBF0UylZWSdK:20gUydI |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3116)
INFO
Application launched itself
- chrome.exe (PID: 3116)
Reads settings of System Certificates
- chrome.exe (PID: 3116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
22
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15884298534115738913 --mojo-platform-channel-handle=4476 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2936568141177952911 --mojo-platform-channel-handle=4512 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=964,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11161462533740338159 --mojo-platform-channel-handle=4536 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=964,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15920027177994419801 --mojo-platform-channel-handle=968 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --service-pipe-token=5535311646725513885 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5535311646725513885 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2064 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1288736416179745579 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1288736416179745579 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3752 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4876899859774469093 --mojo-platform-channel-handle=2912 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17930058137258295203 --mojo-platform-channel-handle=4172 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=17832965554738040658 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17832965554738040658 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3440 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7690459794457750617 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7690459794457750617 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
551
Read events
462
Write events
84
Delete events
5
Modification events
| (PID) Process: | (3116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3116-13205400191482250 |
Value: 259 | |||
| (PID) Process: | (3116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3116-13205400191482250 |
Value: 259 | |||
Executable files
0
Suspicious files
21
Text files
172
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9ff35f5d-3ee7-476a-8a5b-6ac34ab0bca0.tmp | — | |
MD5:— | SHA256:— | |||
| 3116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
30
DNS requests
20
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3116 | chrome.exe | GET | — | 47.88.103.239:80 | http://finanso.top/favicon.ico | US | — | — | suspicious |
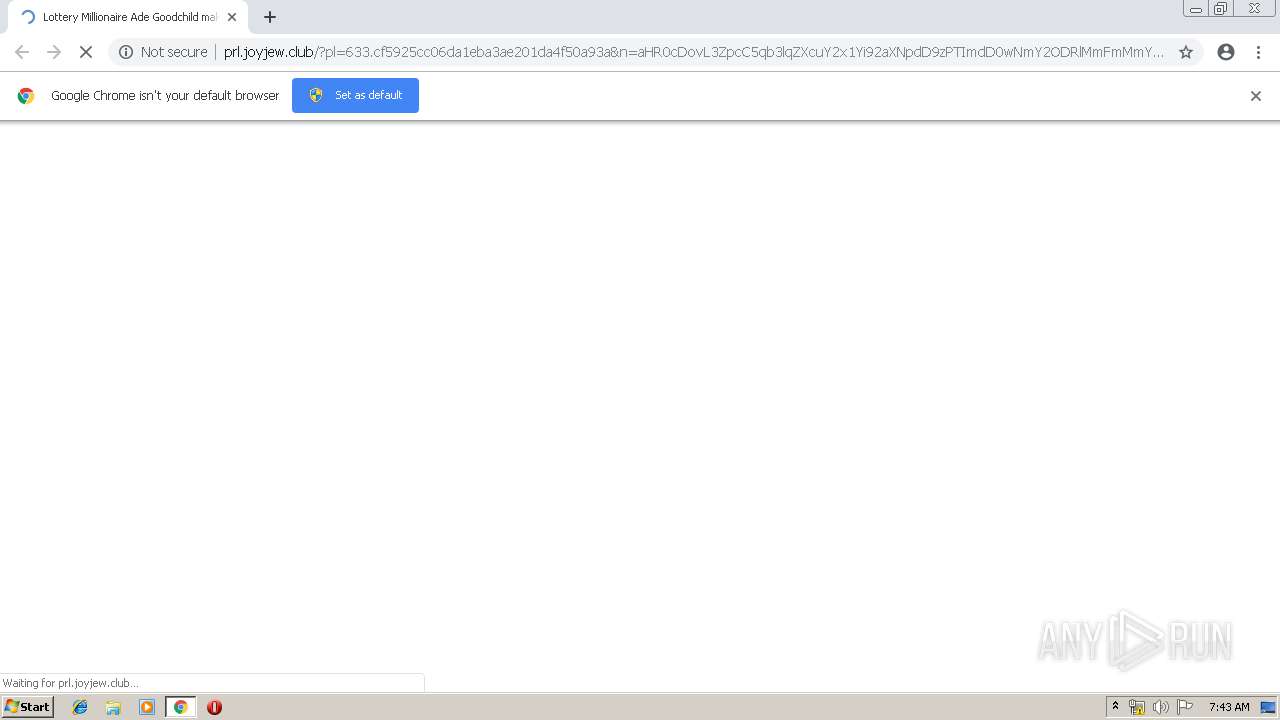
3116 | chrome.exe | GET | 302 | 104.31.86.46:80 | http://vip.joyjew.club/tracker?offer_id=2164&aff_id=225&u=1197:100&pl=633:100 | US | — | — | malicious |
3116 | chrome.exe | GET | 200 | 47.88.103.239:80 | http://finanso.top/eng.html | US | html | 154 b | suspicious |
3116 | chrome.exe | GET | 200 | 104.31.87.46:80 | http://prl.joyjew.club/prelands/633/css/tidyx-v2.css | US | text | 8.27 Kb | malicious |
3116 | chrome.exe | GET | 200 | 104.31.87.46:80 | http://prl.joyjew.club/?pl=633.cf5925cc06da1eba3ae201da4f50a93a&n=aHR0cDovL3ZpcC5qb3lqZXcuY2x1Yi92aXNpdD9zPTImdD0wNmY2ODRlMmFmMmY0OWZmOWQ3YjMwZjQ0MDNiYzY1OCZuPWFIUjBjRG92TDJOaExtTnllWEIwYjJkeWIzVndMV0Z3Y0M1MmFYQXVhbTk1YW1WM0xtTnNkV0l2UDNObGMzTnBiMjQ5TURabU5qZzBaVEpoWmpKbU5EbG1aamxrTjJJek1HWTBOREF6WW1NMk5UZ21ZV1ptWDJsa1BUSXlOU1ptY0hBOU1RPT0= | US | html | 10.1 Kb | malicious |
3116 | chrome.exe | GET | 200 | 104.31.87.46:80 | http://prl.joyjew.club/prelands/633/images/espic1.jpg | US | image | 37.1 Kb | malicious |
3116 | chrome.exe | GET | 200 | 104.31.87.46:80 | http://prl.joyjew.club/prelands/633/css/css.css | US | text | 761 b | malicious |
3116 | chrome.exe | GET | 200 | 104.31.87.46:80 | http://prl.joyjew.club/prelands/633/images/sharedesk.png | US | image | 2.66 Kb | malicious |
3116 | chrome.exe | GET | 200 | 104.31.87.46:80 | http://prl.joyjew.club/prelands/633/images/Sergi.jpg | US | image | 53.0 Kb | malicious |
3116 | chrome.exe | GET | 200 | 104.31.87.46:80 | http://prl.joyjew.club/prelands/633/images/18119267_10155363709609924_958378663814436125_n.jpg | US | image | 1.28 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3116 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3116 | chrome.exe | 216.58.206.1:443 | guipleaderspif1986.blogspot.qa | Google Inc. | US | whitelisted |
3116 | chrome.exe | 216.58.210.1:443 | guipleaderspif1986.blogspot.com | Google Inc. | US | whitelisted |
3116 | chrome.exe | 172.217.21.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3116 | chrome.exe | 172.217.16.201:443 | resources.blogblog.com | Google Inc. | US | whitelisted |
3116 | chrome.exe | 172.217.16.193:443 | themes.googleusercontent.com | Google Inc. | US | whitelisted |
3116 | chrome.exe | 172.217.18.161:443 | lh3.googleusercontent.com | Google Inc. | US | whitelisted |
3116 | chrome.exe | 104.31.87.46:80 | vip.joyjew.club | Cloudflare Inc | US | shared |
3116 | chrome.exe | 104.31.86.46:80 | vip.joyjew.club | Cloudflare Inc | US | shared |
3116 | chrome.exe | 172.217.22.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
guipleaderspif1986.blogspot.qa |
| whitelisted |
accounts.google.com |
| shared |
guipleaderspif1986.blogspot.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
resources.blogblog.com |
| whitelisted |
www.blogger.com |
| shared |
themes.googleusercontent.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
lh3.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
3116 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |