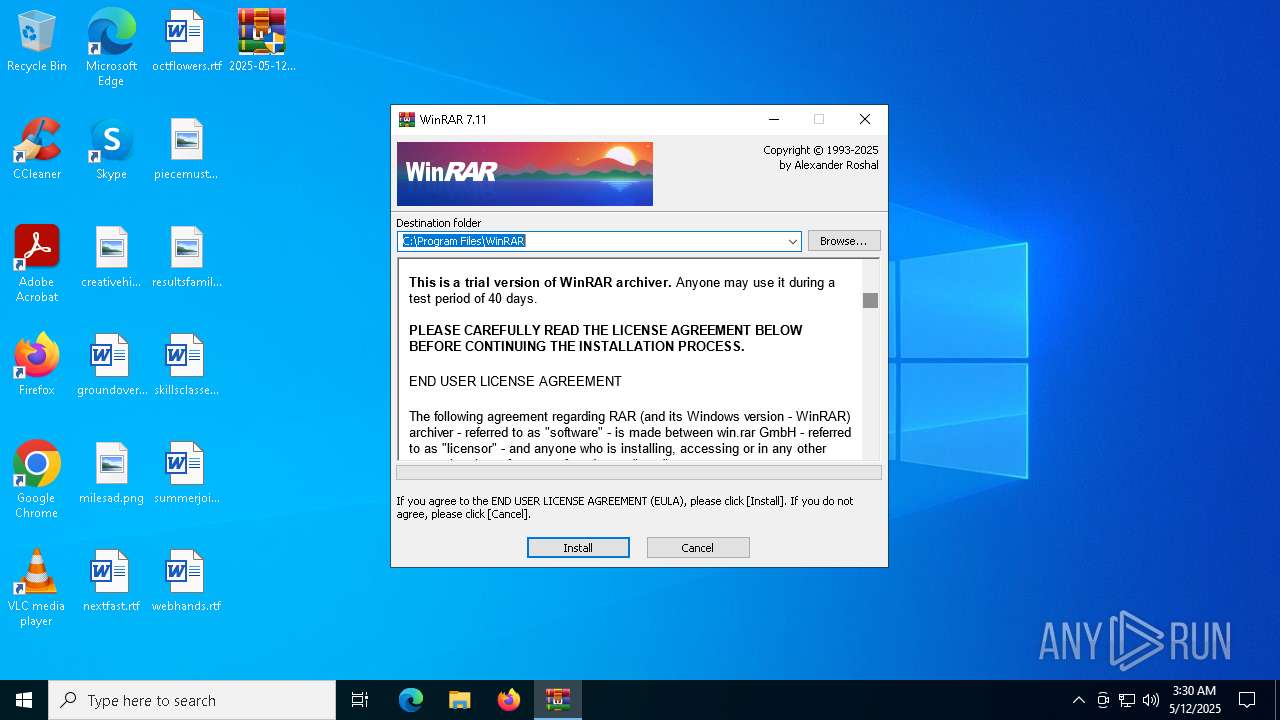
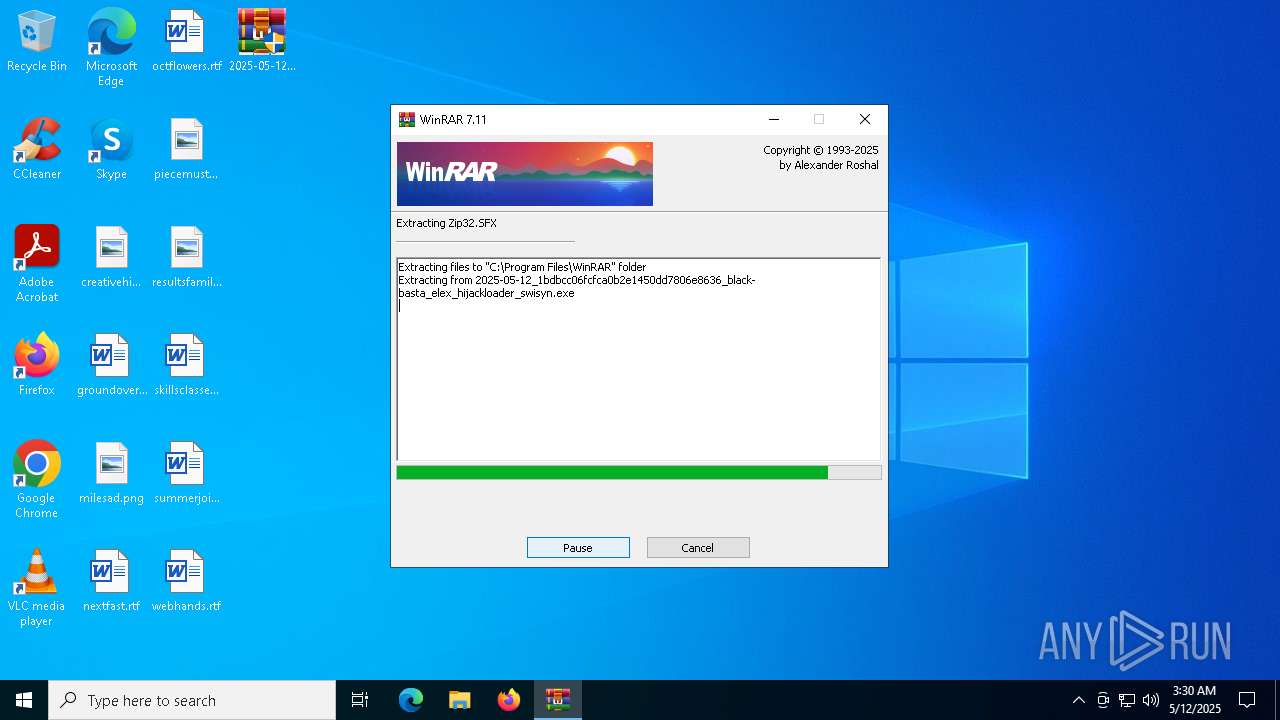
| File name: | 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn |
| Full analysis: | https://app.any.run/tasks/392b0ccb-dfbe-499d-9a27-357306fbeedd |
| Verdict: | Malicious activity |
| Analysis date: | May 12, 2025, 03:30:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 1BDBCC06FCFCA0B2E1450DD7806E8636 |
| SHA1: | F3211C046902368AAD21A8A6C88E6A97963A8BEA |
| SHA256: | FDBD5EC0B1E92DFB693DB9B4B2E6C8EC751A9450D53379F6C413A67A6125EE25 |
| SSDEEP: | 98304:5cC2d240HRy5S6g/LzM1DXbTRe0hBSLyoovRWf6Sz1i0hAVUlGisxod1lifQ+keV:nWUuQmcJ2J |
MALICIOUS
JEEFO has been detected
- 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe (PID: 5680)
- icsys.icn.exe (PID: 5988)
- svchost.exe (PID: 1324)
- explorer.exe (PID: 4040)
Changes the autorun value in the registry
- explorer.exe (PID: 4040)
- svchost.exe (PID: 1324)
SUSPICIOUS
Executable content was dropped or overwritten
- 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe (PID: 5680)
- icsys.icn.exe (PID: 5988)
- explorer.exe (PID: 4040)
- spoolsv.exe (PID: 1228)
- 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe (PID: 5156)
Starts application with an unusual extension
- 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe (PID: 5680)
Starts itself from another location
- 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe (PID: 5680)
- icsys.icn.exe (PID: 5988)
- explorer.exe (PID: 4040)
- svchost.exe (PID: 1324)
- spoolsv.exe (PID: 1228)
The process creates files with name similar to system file names
- icsys.icn.exe (PID: 5988)
- spoolsv.exe (PID: 1228)
Reads Microsoft Outlook installation path
- 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe (PID: 5156)
Reads Internet Explorer settings
- 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe (PID: 5156)
Drops 7-zip archiver for unpacking
- 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe (PID: 5156)
Reads the date of Windows installation
- 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe (PID: 5156)
- Uninstall.exe (PID: 2616)
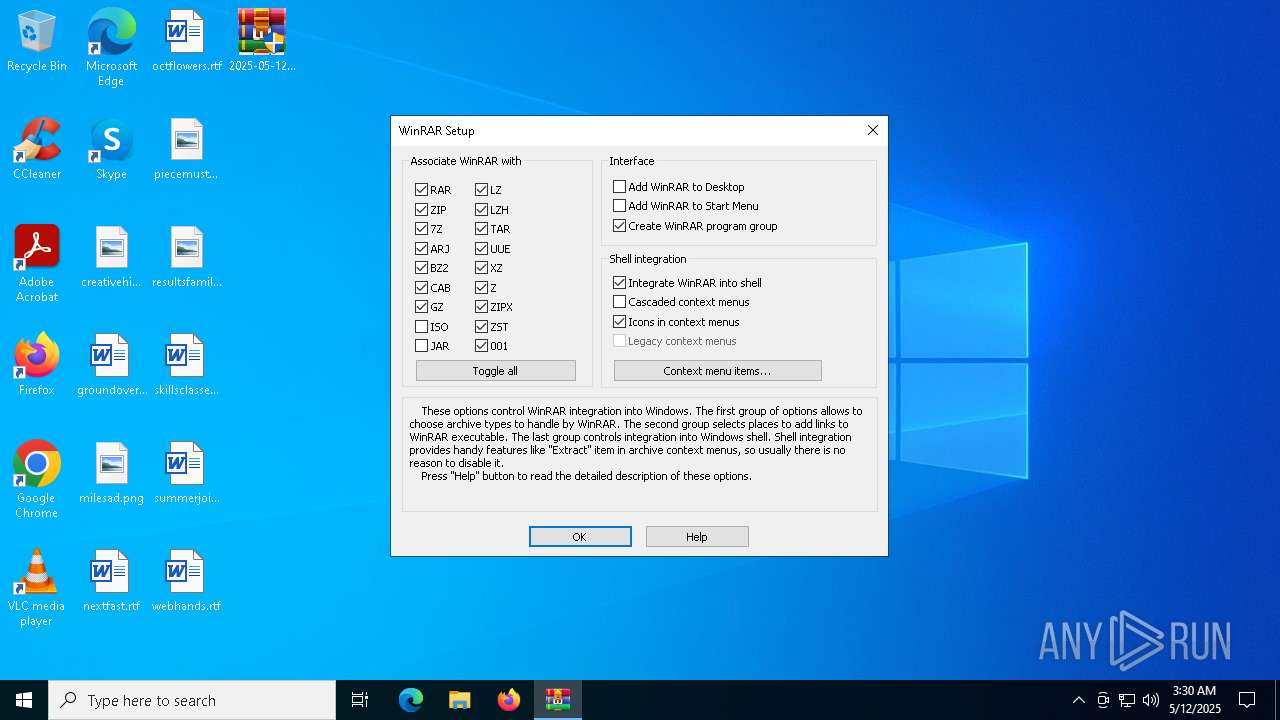
Searches for installed software
- Uninstall.exe (PID: 2616)
Creates/Modifies COM task schedule object
- Uninstall.exe (PID: 2616)
Creates a software uninstall entry
- Uninstall.exe (PID: 2616)
Reads security settings of Internet Explorer
- 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe (PID: 5156)
- Uninstall.exe (PID: 2616)
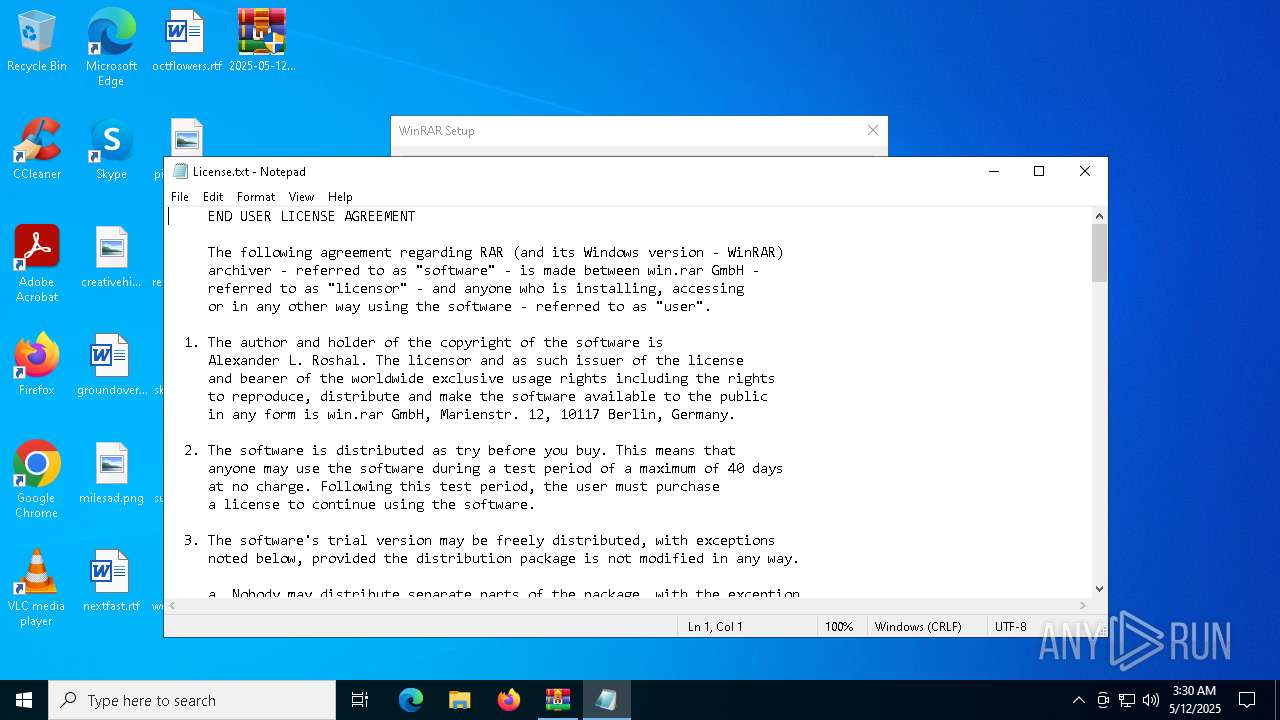
Start notepad (likely ransomware note)
- Uninstall.exe (PID: 2616)
Creates or modifies Windows services
- svchost.exe (PID: 1324)
There is functionality for taking screenshot (YARA)
- Uninstall.exe (PID: 2616)
INFO
Checks supported languages
- 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe (PID: 5680)
- 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe (PID: 5156)
- icsys.icn.exe (PID: 5988)
- explorer.exe (PID: 4040)
- spoolsv.exe (PID: 1228)
- svchost.exe (PID: 1324)
- spoolsv.exe (PID: 6272)
- Uninstall.exe (PID: 2616)
Create files in a temporary directory
- 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe (PID: 5680)
- icsys.icn.exe (PID: 5988)
- explorer.exe (PID: 4040)
- spoolsv.exe (PID: 1228)
- svchost.exe (PID: 1324)
- spoolsv.exe (PID: 6272)
The sample compiled with english language support
- 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe (PID: 5680)
- 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe (PID: 5156)
Reads the computer name
- 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe (PID: 5156)
- svchost.exe (PID: 1324)
- Uninstall.exe (PID: 2616)
Checks proxy server information
- 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe (PID: 5156)
- slui.exe (PID: 6148)
Auto-launch of the file from Registry key
- explorer.exe (PID: 4040)
- svchost.exe (PID: 1324)
The sample compiled with russian language support
- 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe (PID: 5156)
Creates files in the program directory
- 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe (PID: 5156)
- Uninstall.exe (PID: 2616)
Process checks computer location settings
- 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe (PID: 5156)
- Uninstall.exe (PID: 2616)
Manual execution by a user
- svchost.exe (PID: 1532)
- explorer.exe (PID: 6032)
Creates files or folders in the user directory
- Uninstall.exe (PID: 2616)
Reads Microsoft Office registry keys
- Uninstall.exe (PID: 2616)
Reads the software policy settings
- slui.exe (PID: 6148)
Reads security settings of Internet Explorer
- notepad.exe (PID: 5720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:04:01 07:08:22+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 106496 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x290c |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| ProductName: | Project1 |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | TJprojMain |
| OriginalFileName: | TJprojMain.exe |
Total processes
140
Monitored processes
13
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1228 | c:\windows\resources\spoolsv.exe SE | C:\Windows\Resources\spoolsv.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 1324 | c:\windows\resources\svchost.exe | C:\Windows\Resources\svchost.exe | spoolsv.exe | ||||||||||||
User: admin Integrity Level: HIGH Version: 1.00 Modules
| |||||||||||||||
| 1532 | c:\windows\resources\svchost.exe RO | C:\Windows\Resources\svchost.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.00 Modules
| |||||||||||||||
| 2616 | "C:\Program Files\WinRAR\uninstall.exe" /setup | C:\Program Files\WinRAR\Uninstall.exe | — | 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: Uninstall WinRAR Version: 7.11.0 Modules
| |||||||||||||||
| 4040 | c:\windows\resources\themes\explorer.exe | C:\Windows\Resources\Themes\explorer.exe | icsys.icn.exe | ||||||||||||
User: admin Integrity Level: HIGH Version: 1.00 Modules
| |||||||||||||||
| 5156 | c:\users\admin\desktop\2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe | C:\Users\admin\Desktop\2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe | 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: WinRAR Exit code: 0 Version: 7.11.0 Modules
| |||||||||||||||
| 5680 | "C:\Users\admin\Desktop\2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe" | C:\Users\admin\Desktop\2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 5720 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Program Files\WinRAR\License.txt | C:\Windows\System32\notepad.exe | — | Uninstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5988 | C:\Windows\Resources\Themes\icsys.icn.exe | C:\Windows\Resources\Themes\icsys.icn.exe | 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 6032 | c:\windows\resources\themes\explorer.exe RO | C:\Windows\Resources\Themes\explorer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.00 Modules
| |||||||||||||||
Total events
5 435
Read events
5 329
Write events
98
Delete events
8
Modification events
| (PID) Process: | (5680) 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (5988) icsys.icn.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (4040) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Explorer |
Value: c:\windows\resources\themes\explorer.exe RO | |||
| (PID) Process: | (4040) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Svchost |
Value: c:\windows\resources\svchost.exe RO | |||
| (PID) Process: | (4040) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Explorer |
Value: | |||
| (PID) Process: | (4040) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Svchost |
Value: | |||
| (PID) Process: | (1324) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Explorer |
Value: c:\windows\resources\themes\explorer.exe RO | |||
| (PID) Process: | (1324) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Svchost |
Value: c:\windows\resources\svchost.exe RO | |||
| (PID) Process: | (1324) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Explorer |
Value: | |||
| (PID) Process: | (1324) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Svchost |
Value: | |||
Executable files
18
Suspicious files
15
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1228 | spoolsv.exe | C:\Windows\Resources\svchost.exe | executable | |
MD5:D7CD8FD1B43D7B05737458EA5B9726AC | SHA256:F034E0547BC8B60AF820E00790035B85893CCF6821B3EA530E736DC4367B38F9 | |||
| 5156 | 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe | — | ||
MD5:— | SHA256:— | |||
| 5988 | icsys.icn.exe | C:\Windows\Resources\Themes\explorer.exe | executable | |
MD5:7761B3993DFFE8ED3B1640EAB5E0CC58 | SHA256:D994A2BD26857F052B5DAAF61032234EBE3A11AB0643F0E3895CFCFFF7AD2C6E | |||
| 4040 | explorer.exe | C:\Windows\Resources\spoolsv.exe | executable | |
MD5:3725C4EEC512375F87B4A2F6EB3179F1 | SHA256:8F2F69FA434AB808EC6DC2751D0810F33C7D9F23731135424AC8F3D963D1977E | |||
| 5988 | icsys.icn.exe | C:\Users\admin\AppData\Local\Temp\~DF201FD072810B684C.TMP | binary | |
MD5:CB396E899FBC2CD2DDAA6E56DAFC7F4A | SHA256:4DFCCE5F3C7E429B7027ED49C52FF56A72C8C16DD43C7E15A8A81DE8F2C4A7F3 | |||
| 1228 | spoolsv.exe | C:\Users\admin\AppData\Local\Temp\~DFFEB14E23580088BB.TMP | binary | |
MD5:327FC278B47DFE2AA3EEDF51479B534D | SHA256:BEA0186364AE6CB0FA5BA17F885F3BEC4800435CC4CA32FA828700330687C0F9 | |||
| 5680 | 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe | C:\Users\admin\Desktop\2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe | executable | |
MD5:F033A919F2F6C705FC986CA56C502E8B | SHA256:4E447DD3A885340845DD89E748A4CB566E19C4DA7AE2939F9F26BDA067623A25 | |||
| 5680 | 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe | C:\Windows\Resources\Themes\icsys.icn.exe | executable | |
MD5:ACFC95999E39D3FA63FC63B48FA2B8FE | SHA256:B01AC43B391E267AEC85E1695C24DF982C10AA36B4998803FB9D9B41B80B9066 | |||
| 5156 | 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe | C:\Program Files\WinRAR\Uninstall.lst | text | |
MD5:6EEEFCB85673C14201D024B6E6AC6258 | SHA256:B75FDEE208D2834AB147DACB51F4E7D70E44457C8B639048FE67B252B8D61F1F | |||
| 5156 | 2025-05-12_1bdbcc06fcfca0b2e1450dd7806e8636_black-basta_elex_hijackloader_swisyn.exe | C:\Program Files\WinRAR\Rar.exe | executable | |
MD5:18DC8BFF47CC282508354771D0C8CF8C | SHA256:CFB7930F778FC1C56919DA5A83A83FCF2509A0D2126F6644E5C972111E14AF68 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
22
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4172 | RUXIMICS.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4172 | RUXIMICS.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4172 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4172 | RUXIMICS.exe | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
4172 | RUXIMICS.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
2104 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
896 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |