analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
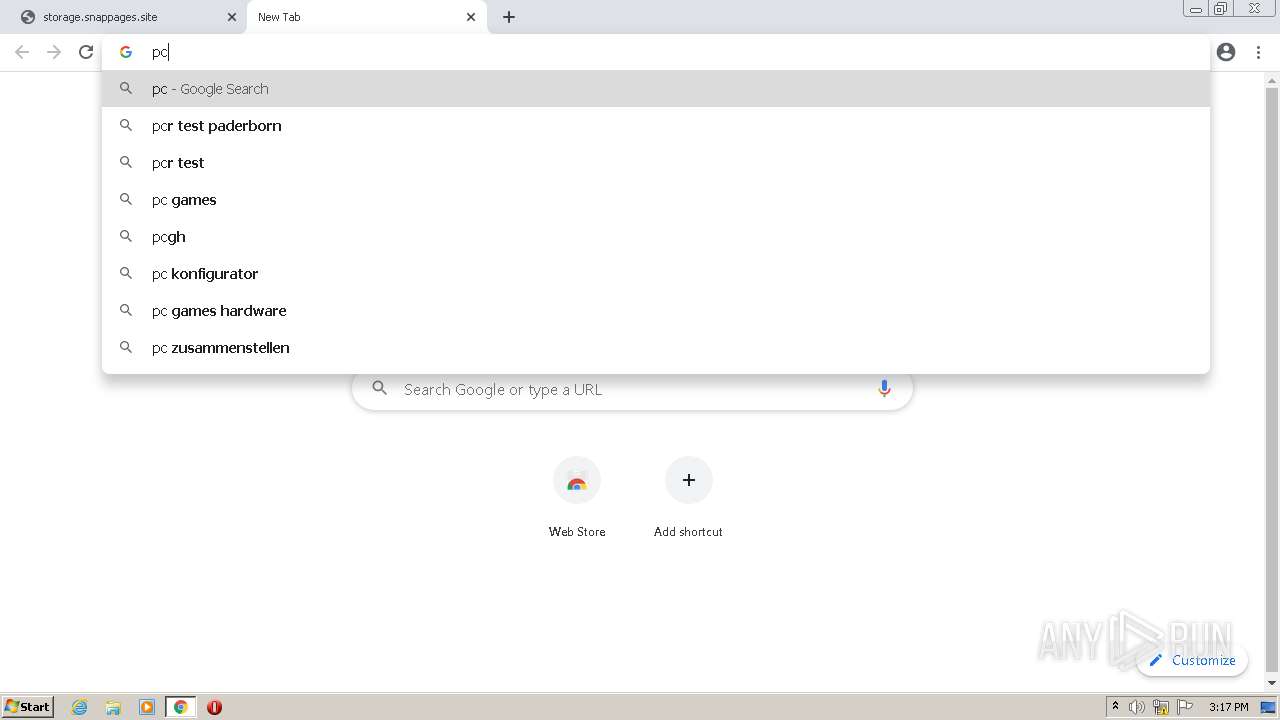
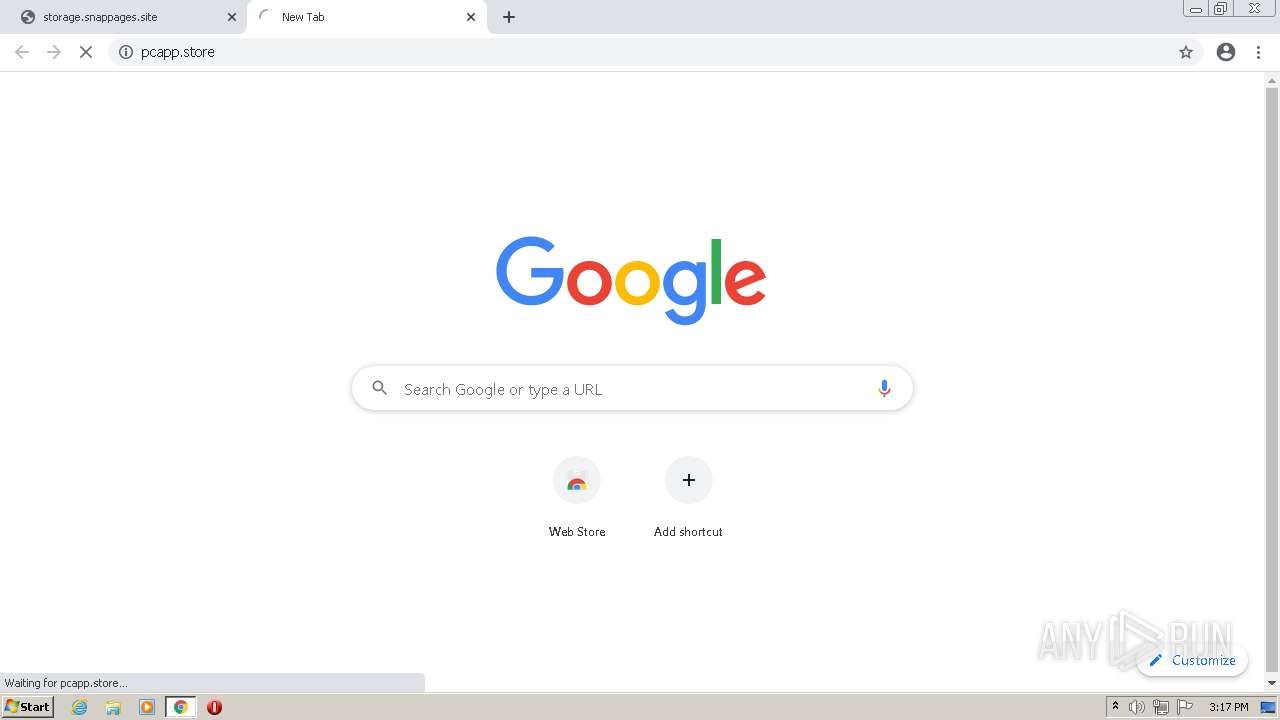
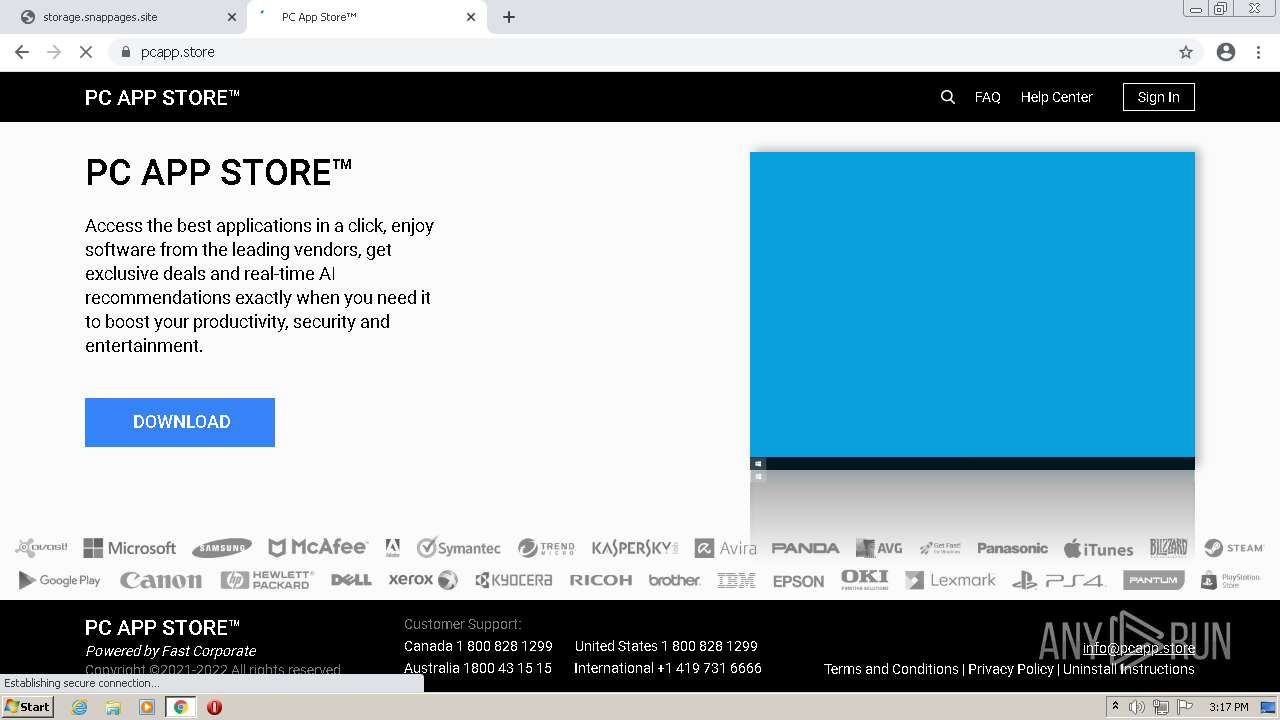
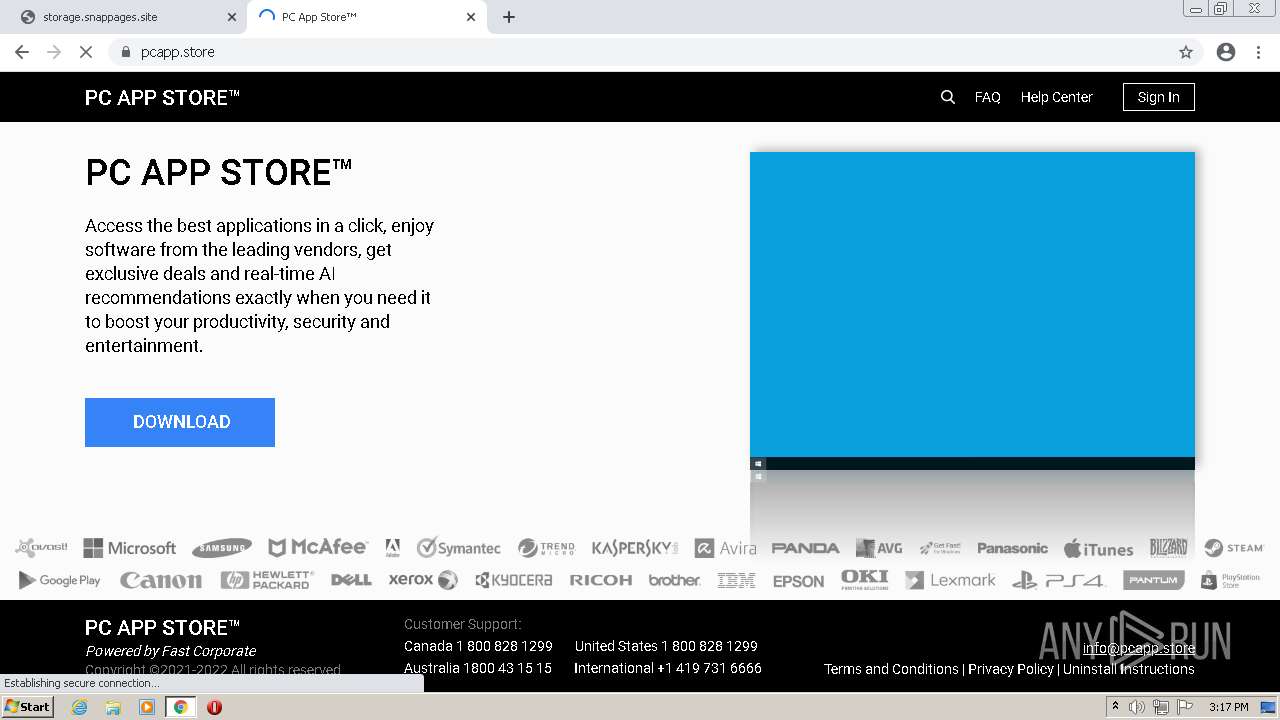
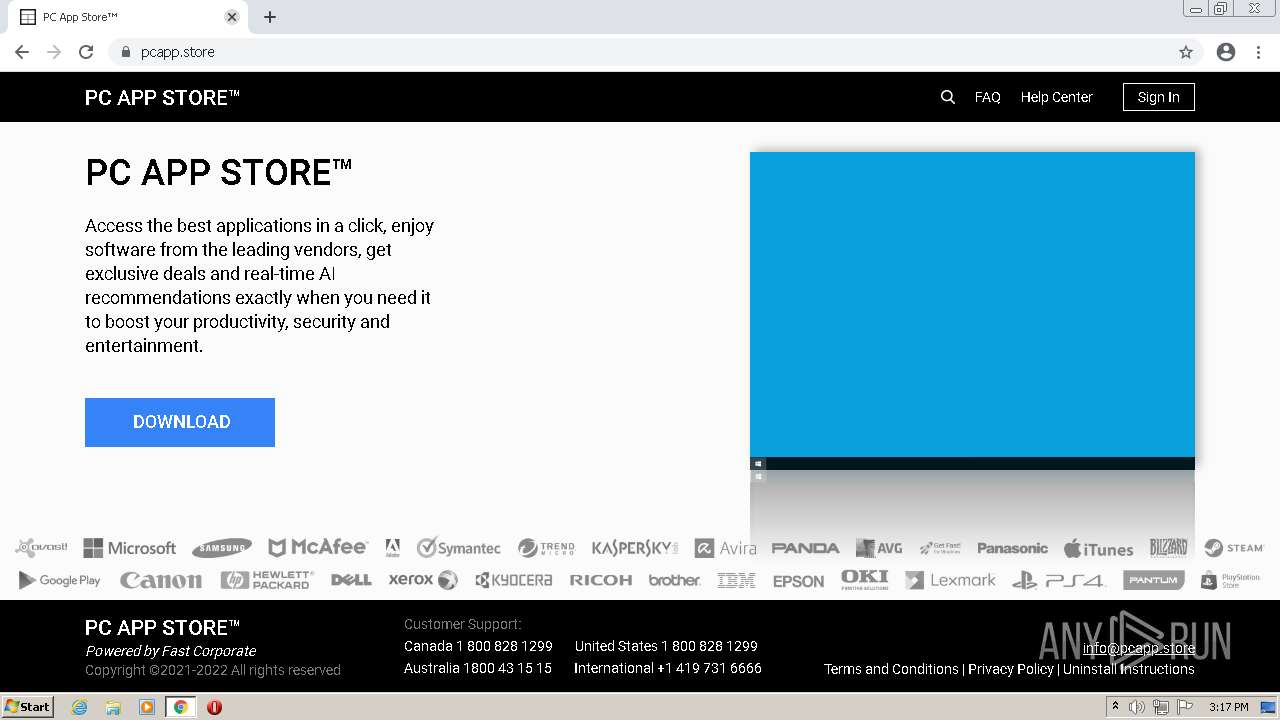
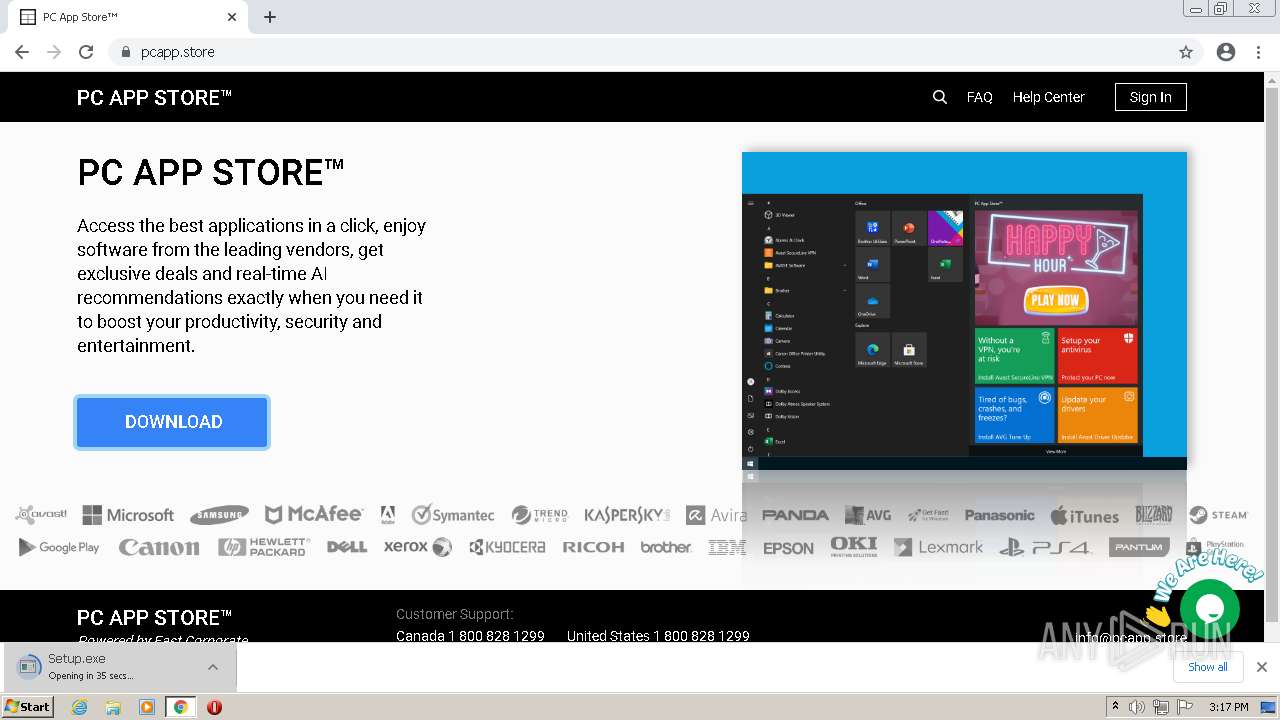
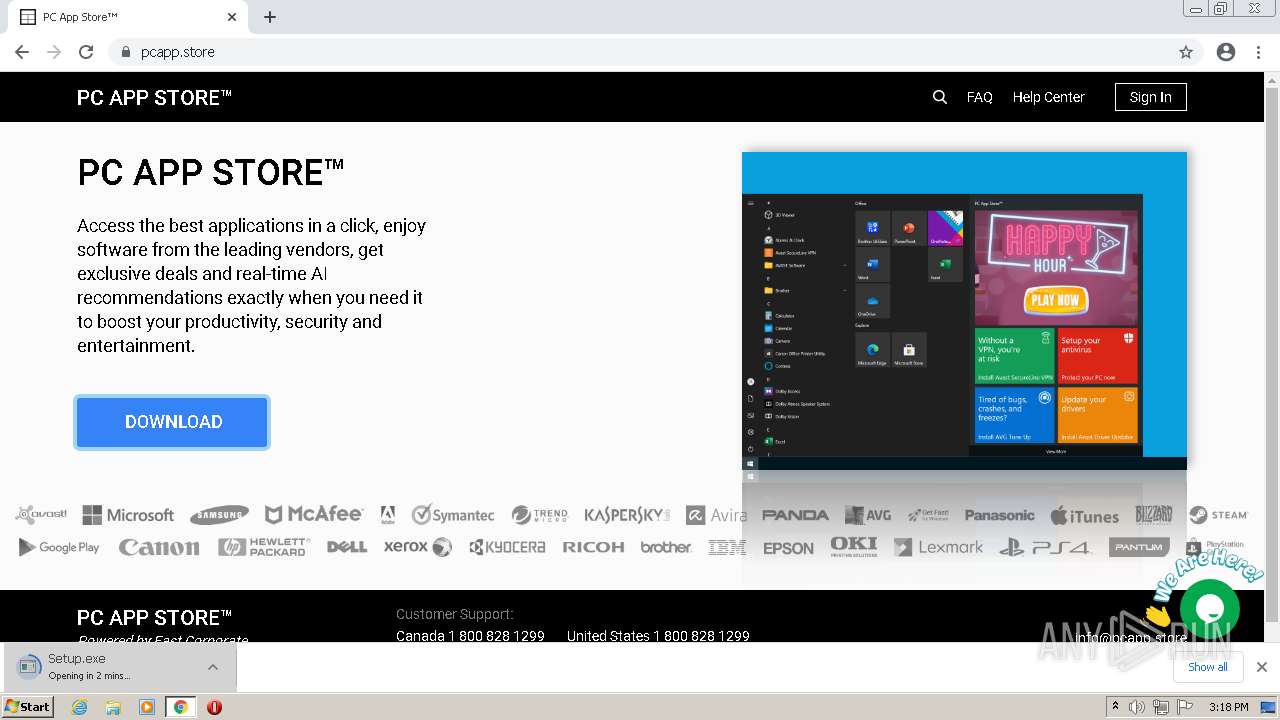
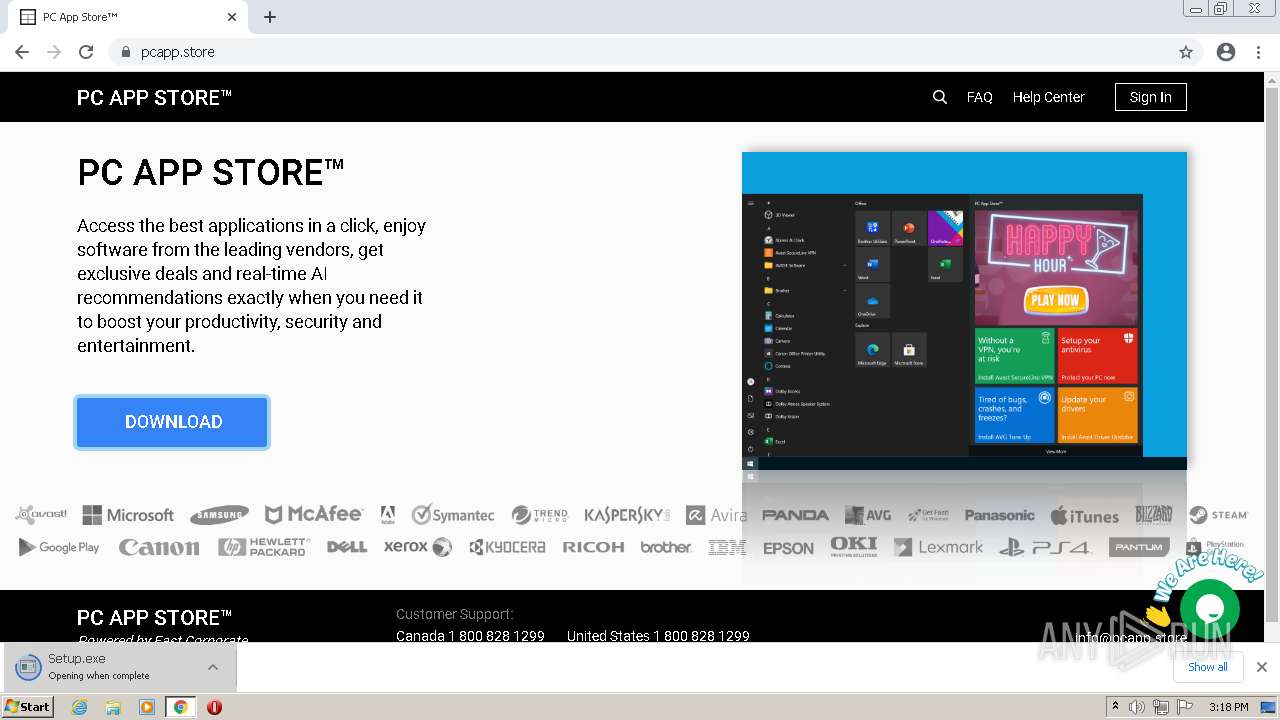
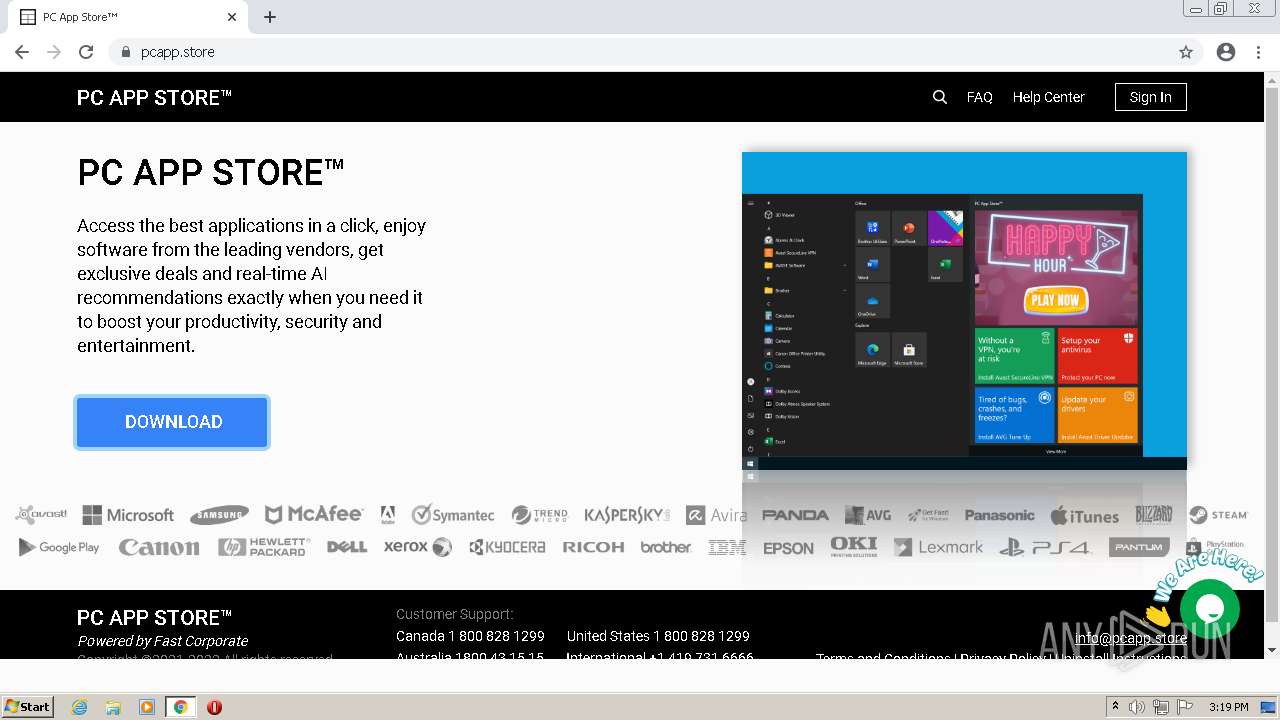
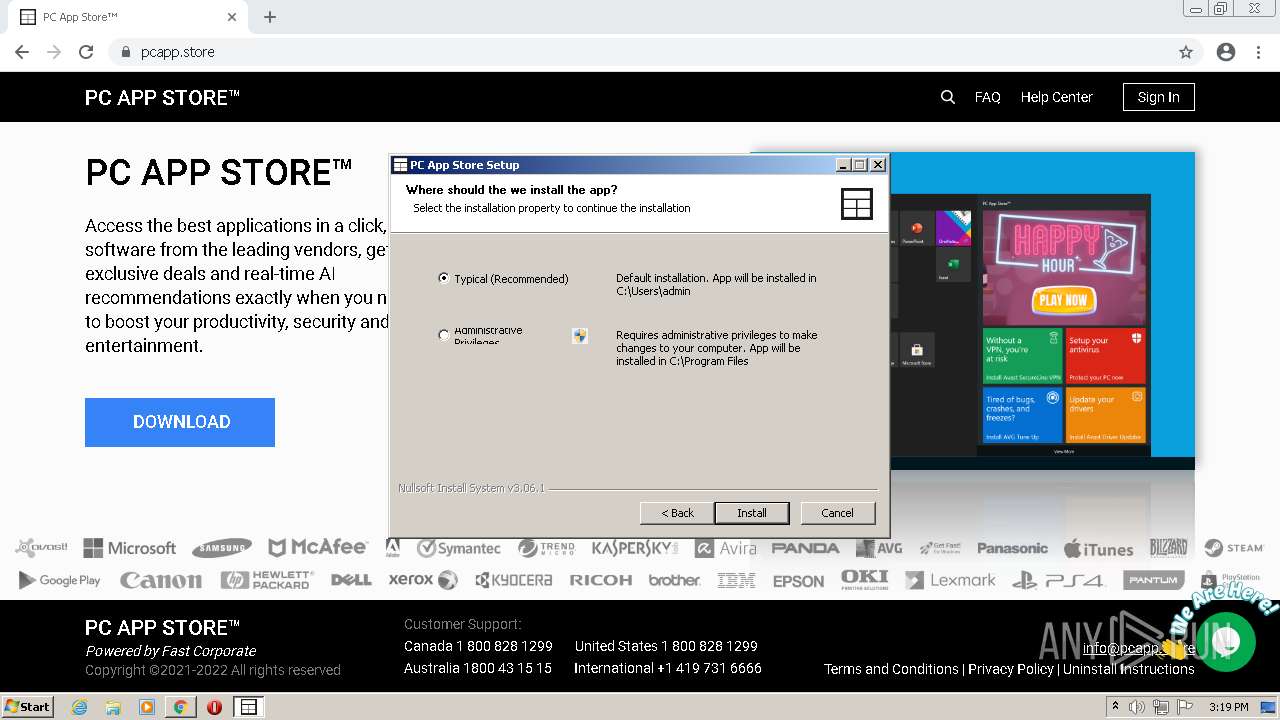
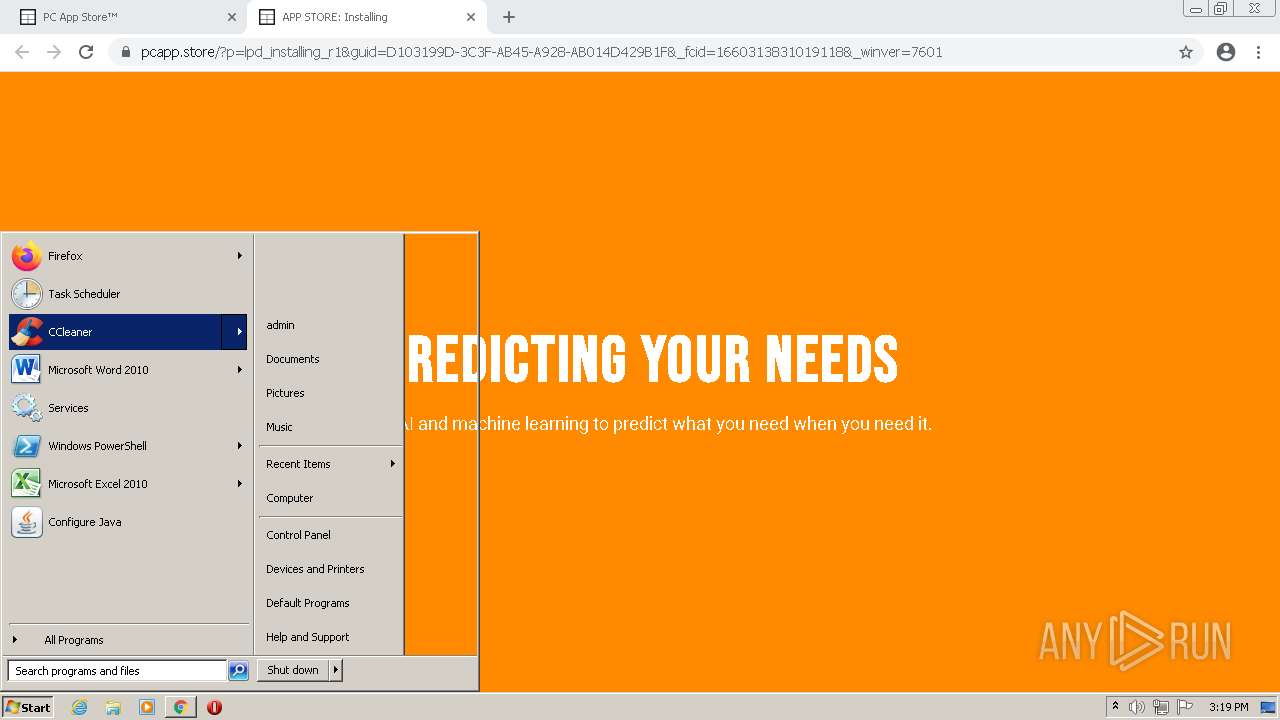
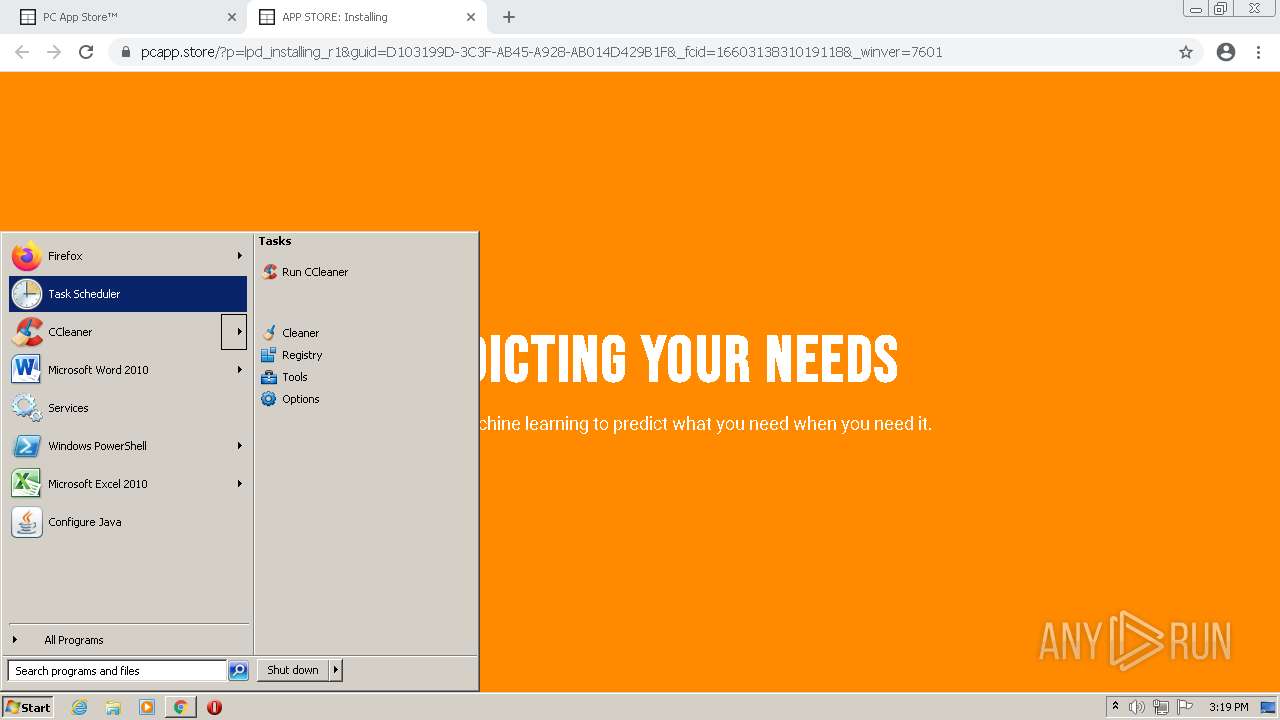
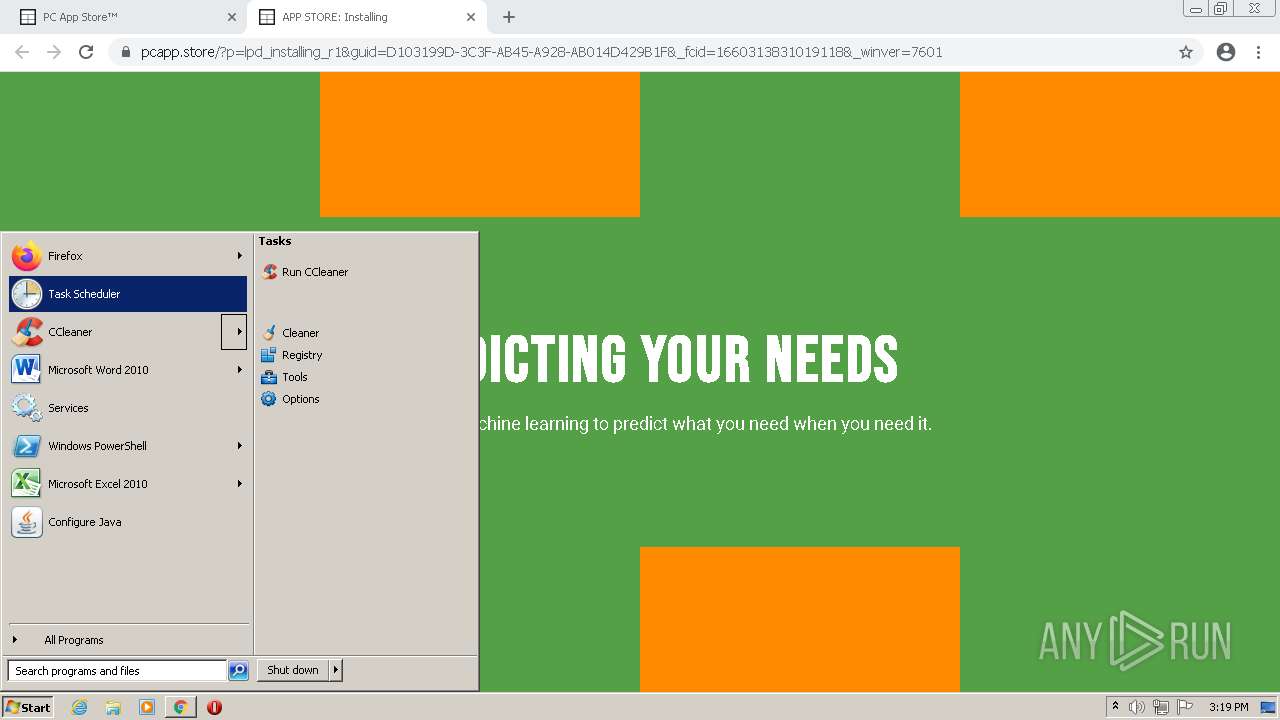
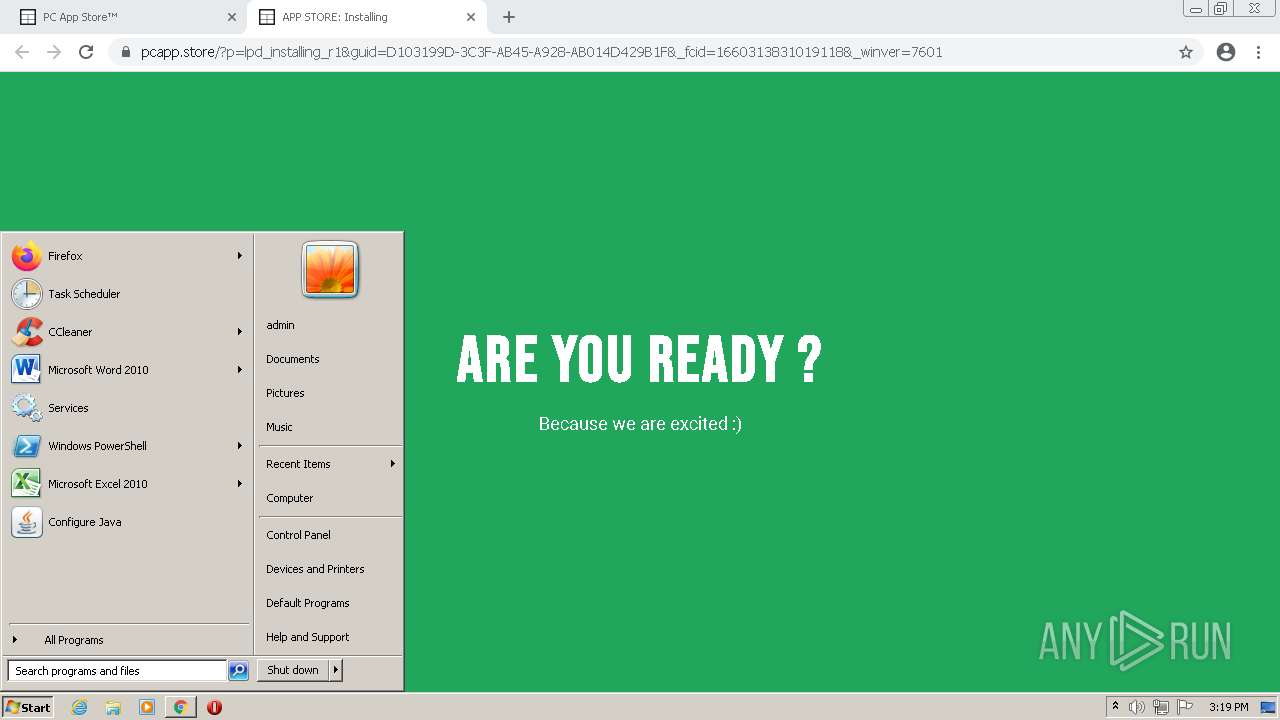
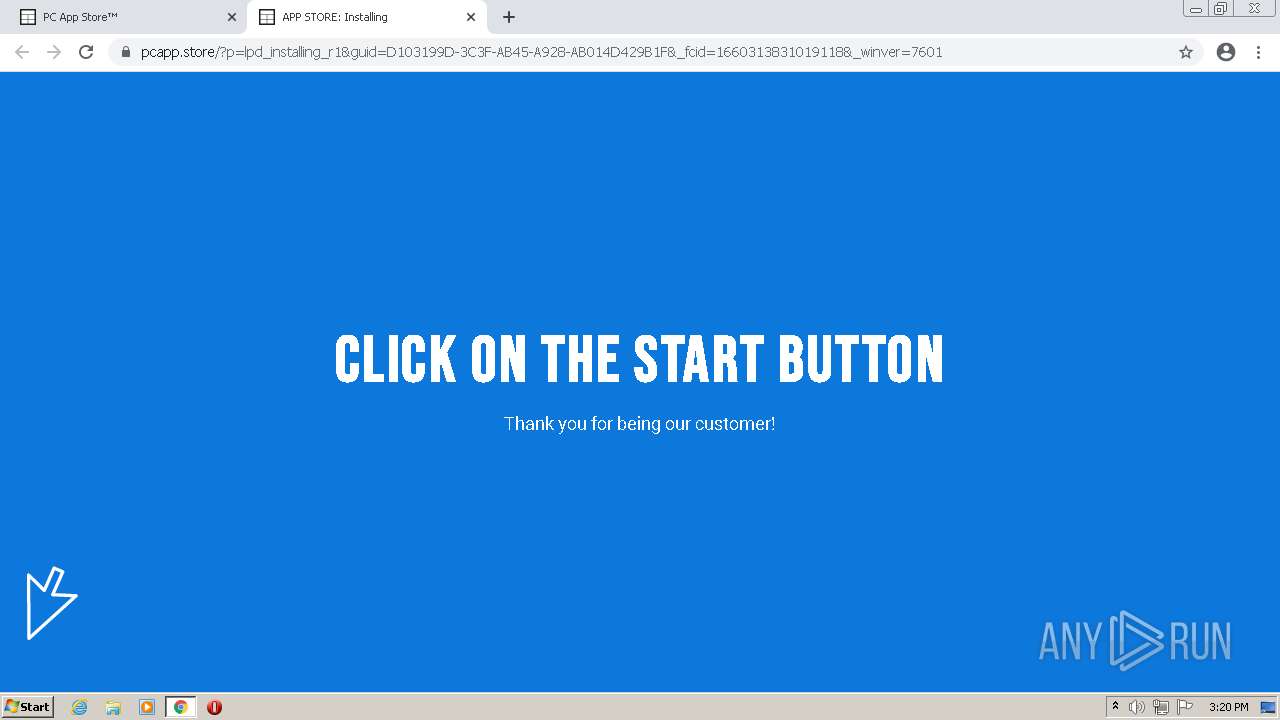
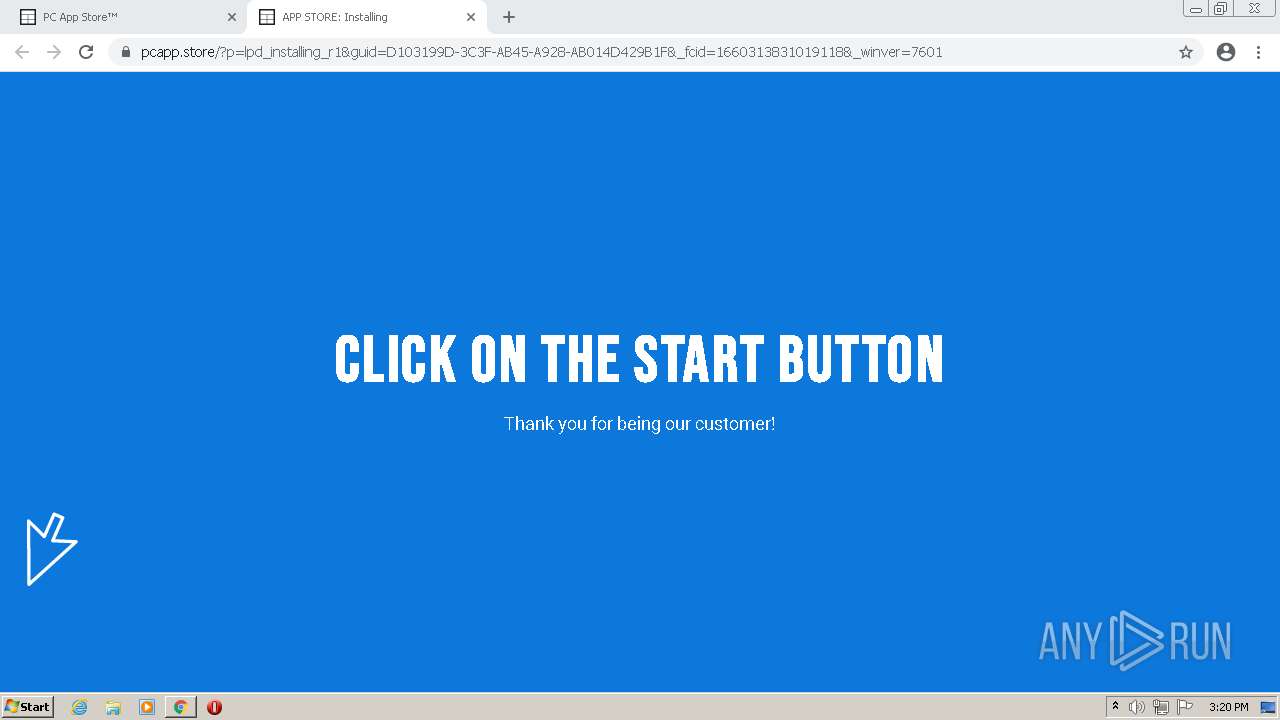
| URL: | http://storage.snappages.site |
| Full analysis: | https://app.any.run/tasks/cef1d02d-29e2-4a53-84eb-0ed87e593634 |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 14:16:57 |
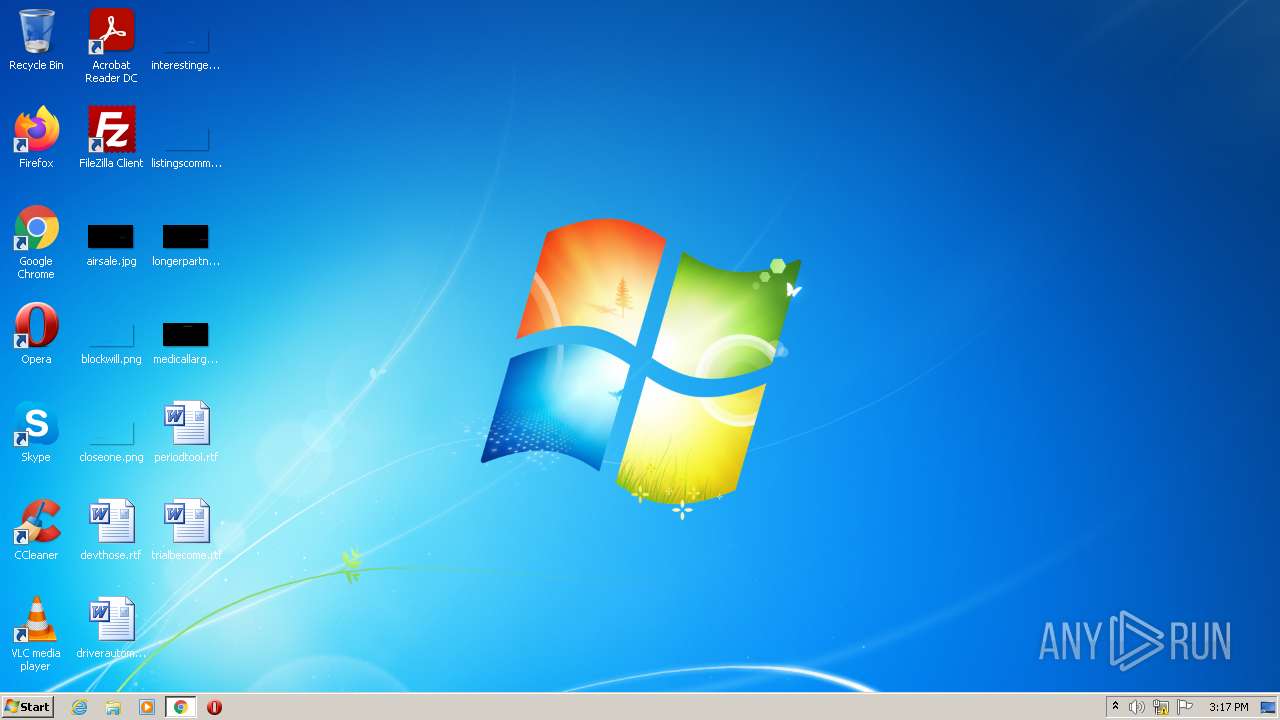
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 2E1A2C77B055B6718D12010EF9DF95DF |
| SHA1: | DB25566D4DC74ED2584C3005FAEB69DF0CC1F4FC |
| SHA256: | FDA730241F6616F071C42F712EFFEC4F95FE51C194FB0A48B9CF9A649D9DED62 |
| SSDEEP: | 3:N1KNRMEC1wAWvm:CQR1WO |
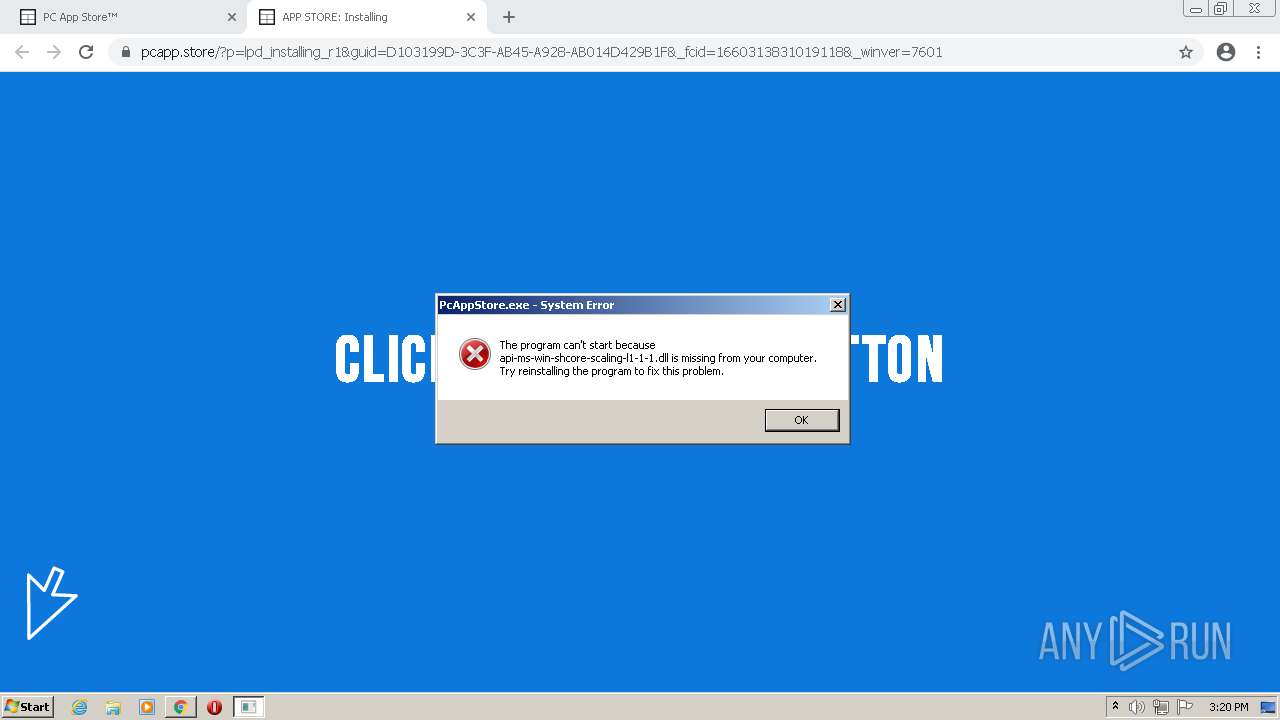
MALICIOUS
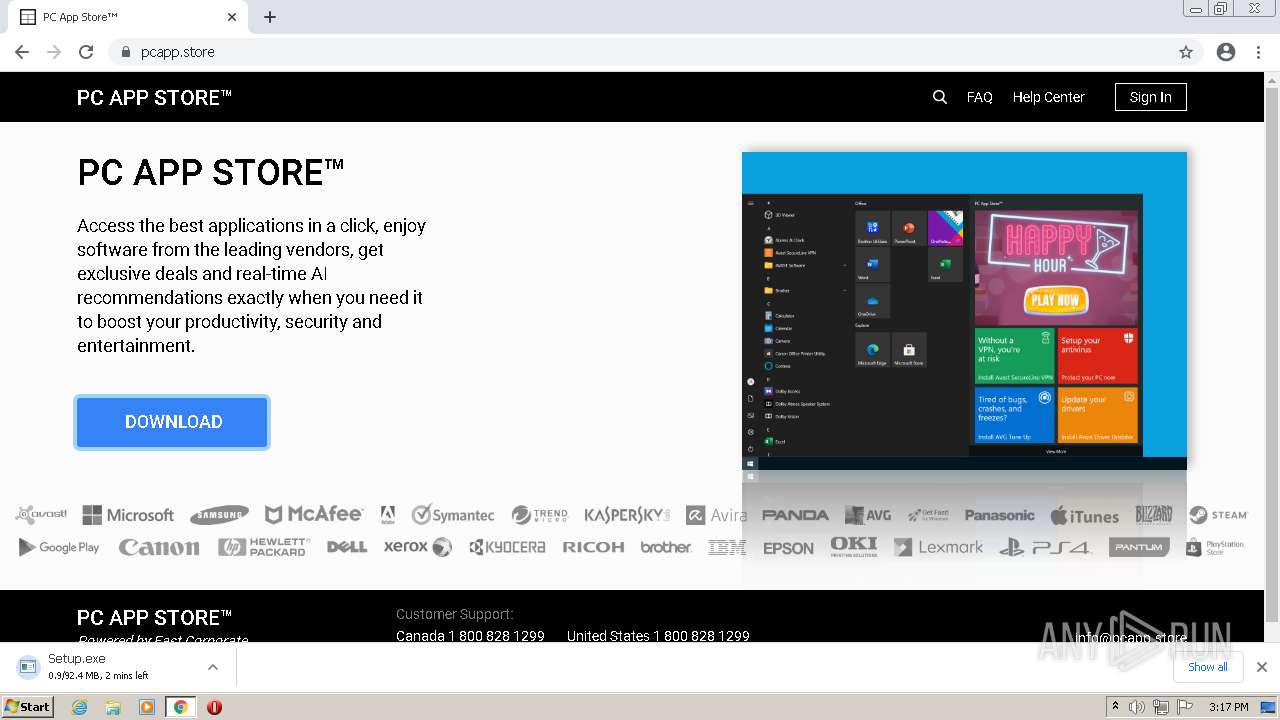
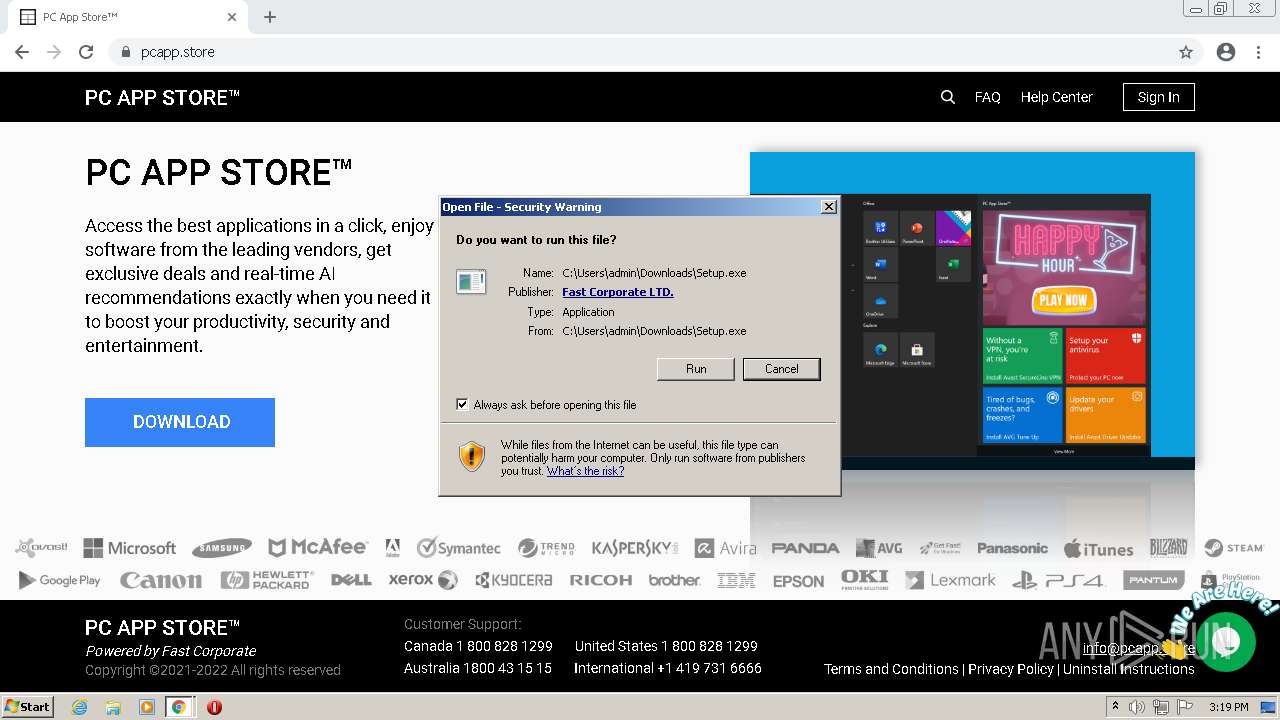
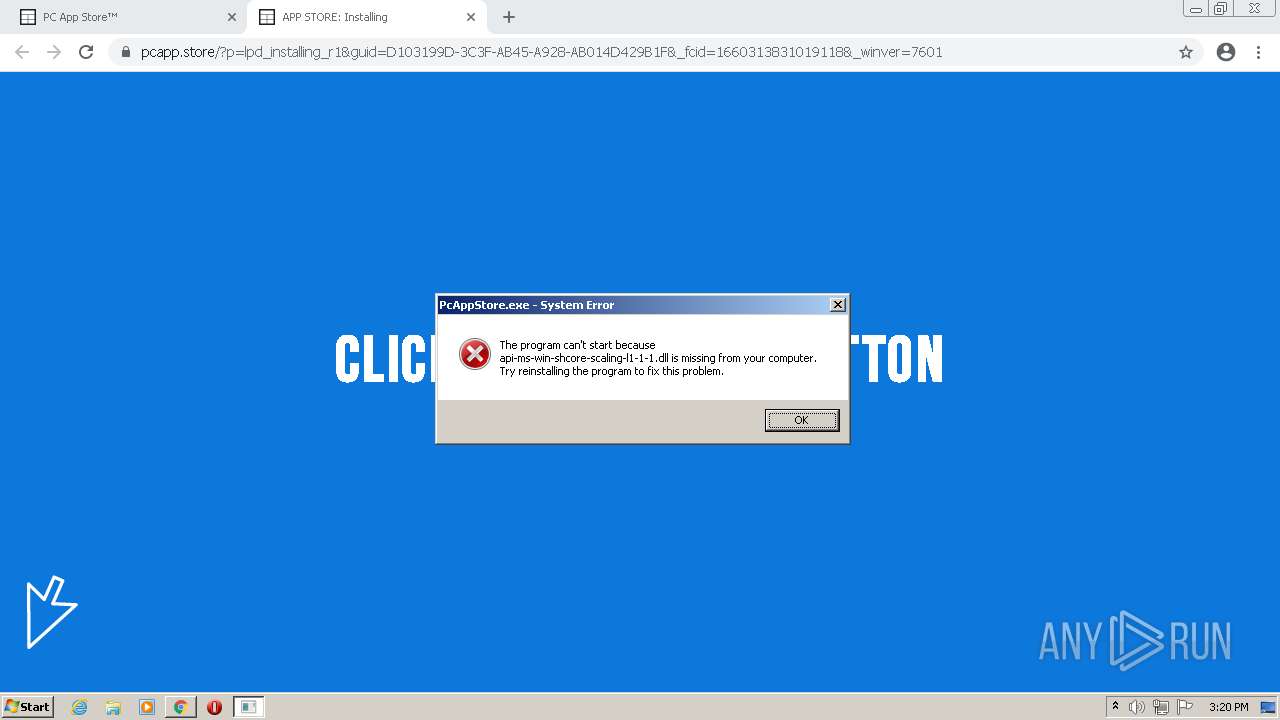
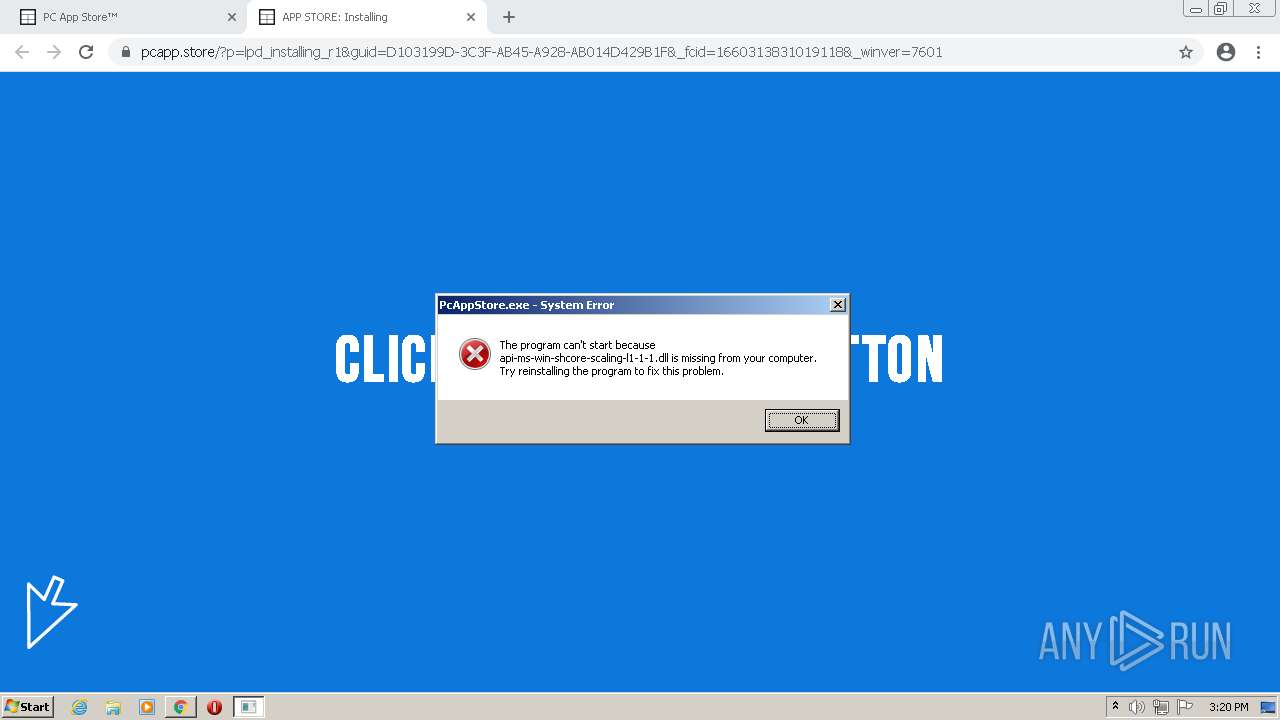
Drops executable file immediately after starts
- chrome.exe (PID: 2964)
- chrome.exe (PID: 2820)
- Setup.exe (PID: 3416)
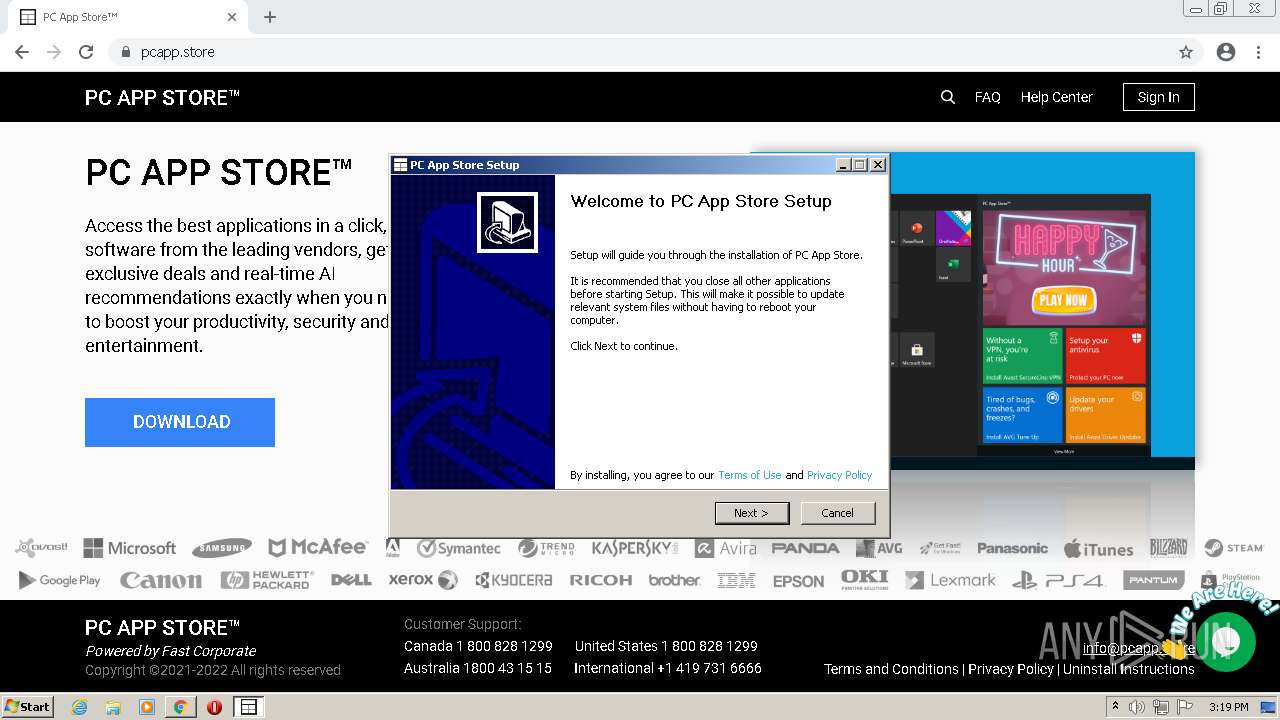
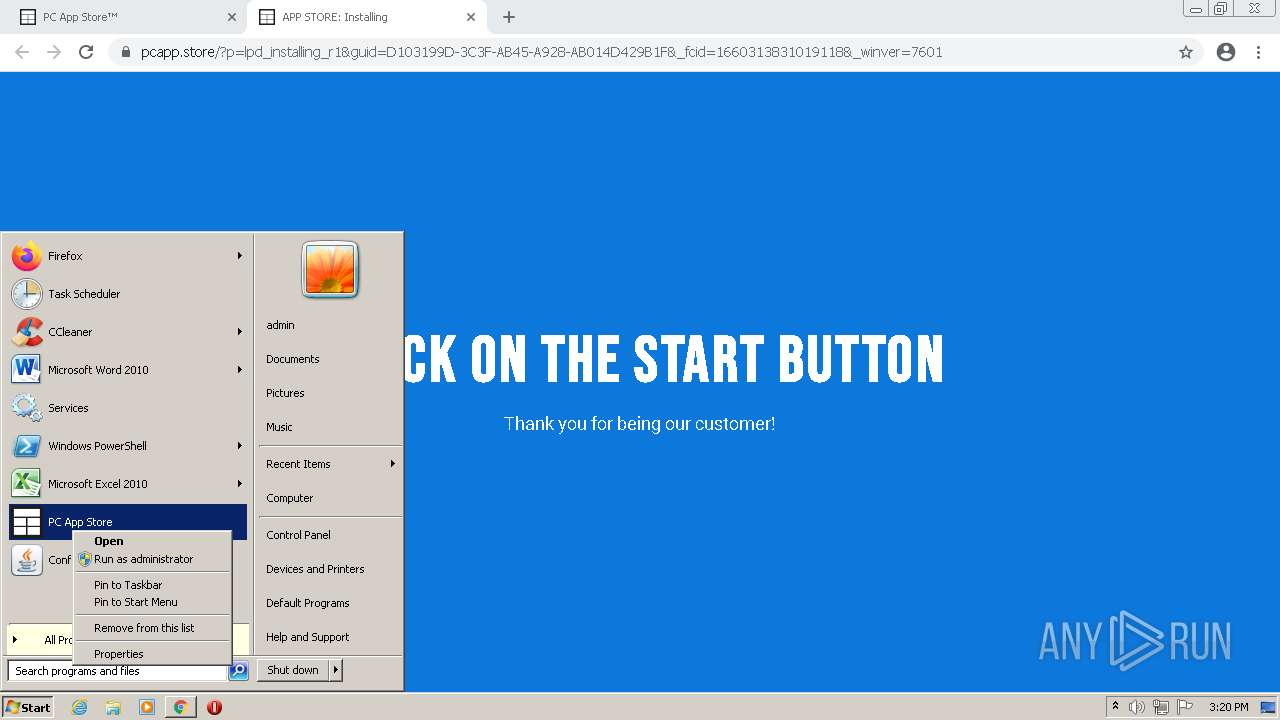
Application was dropped or rewritten from another process
- Setup.exe (PID: 3416)
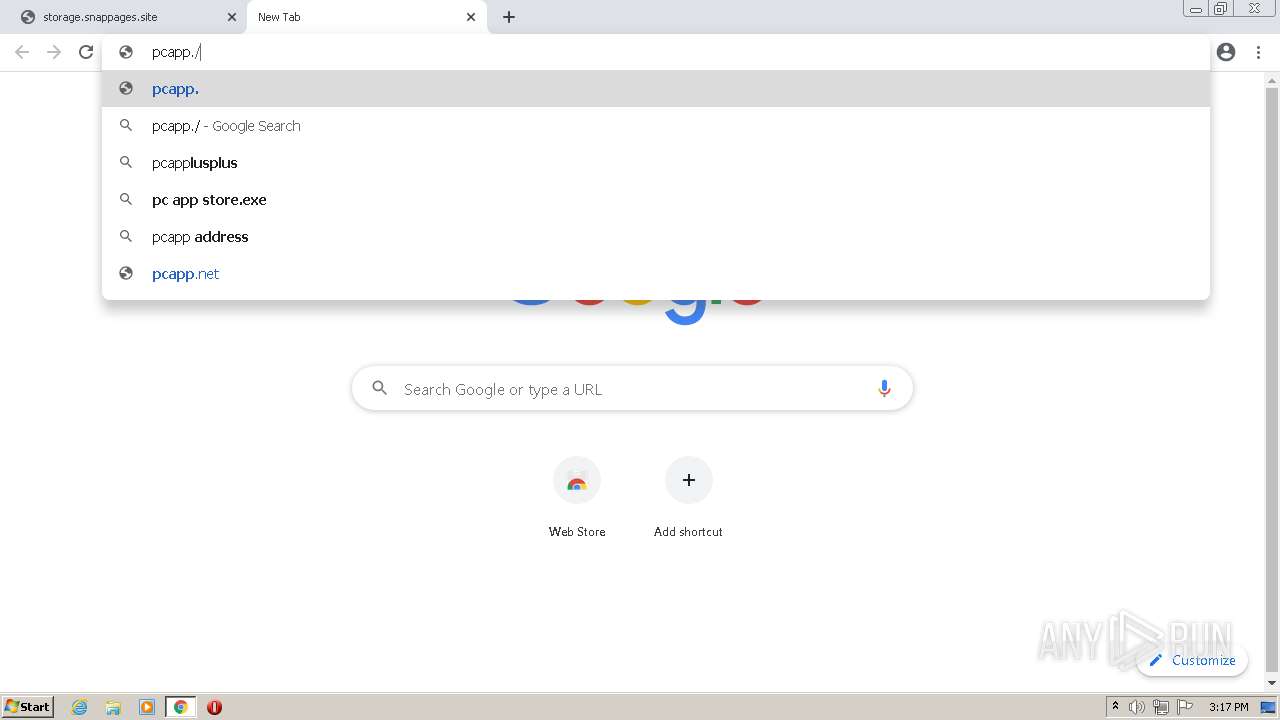
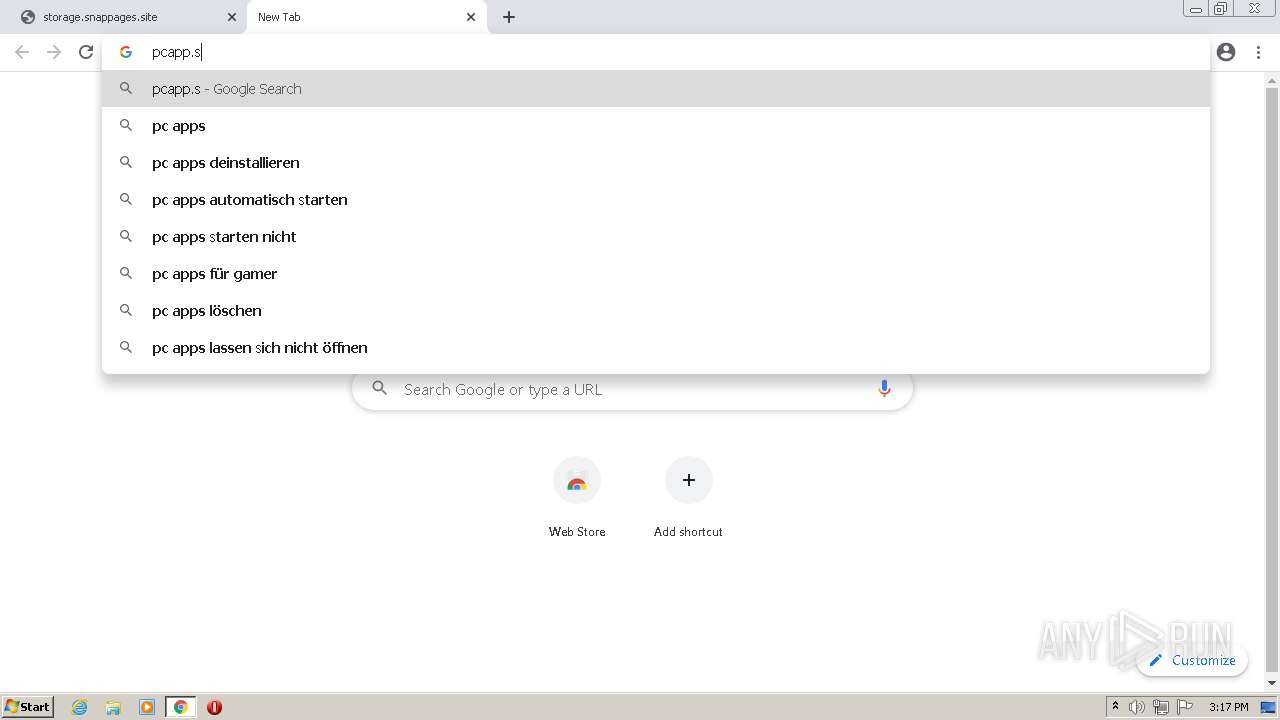
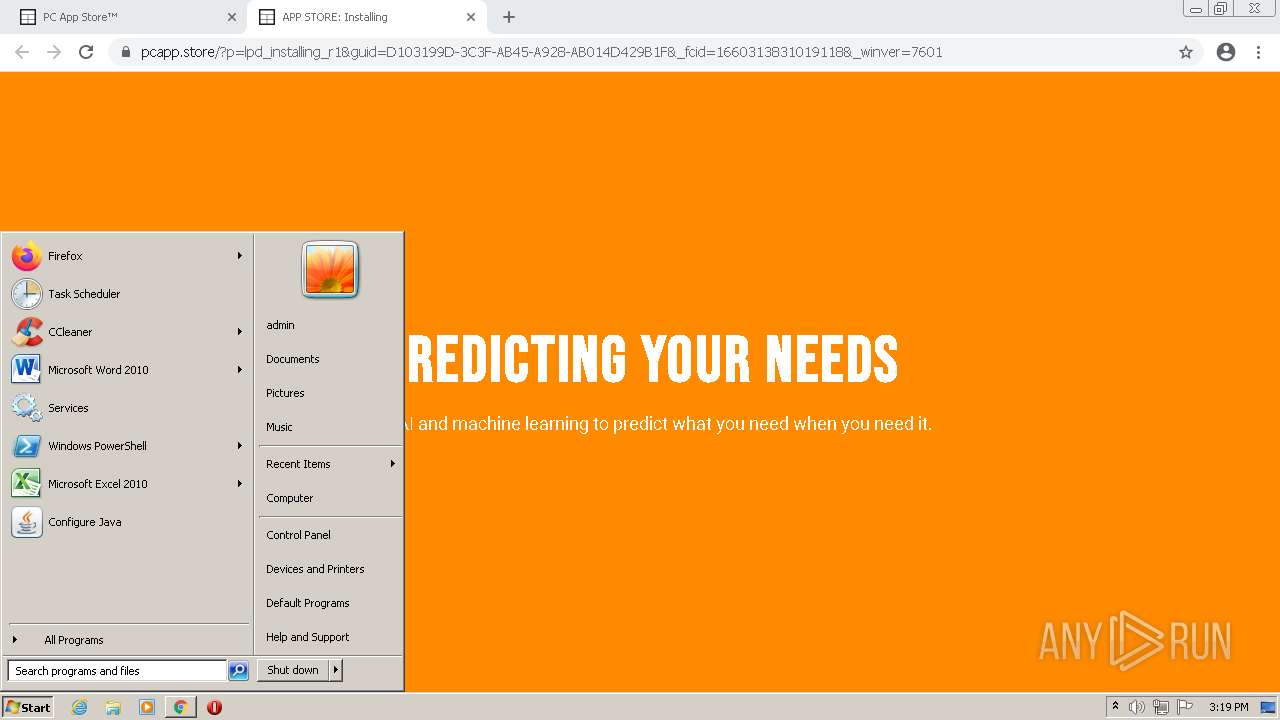
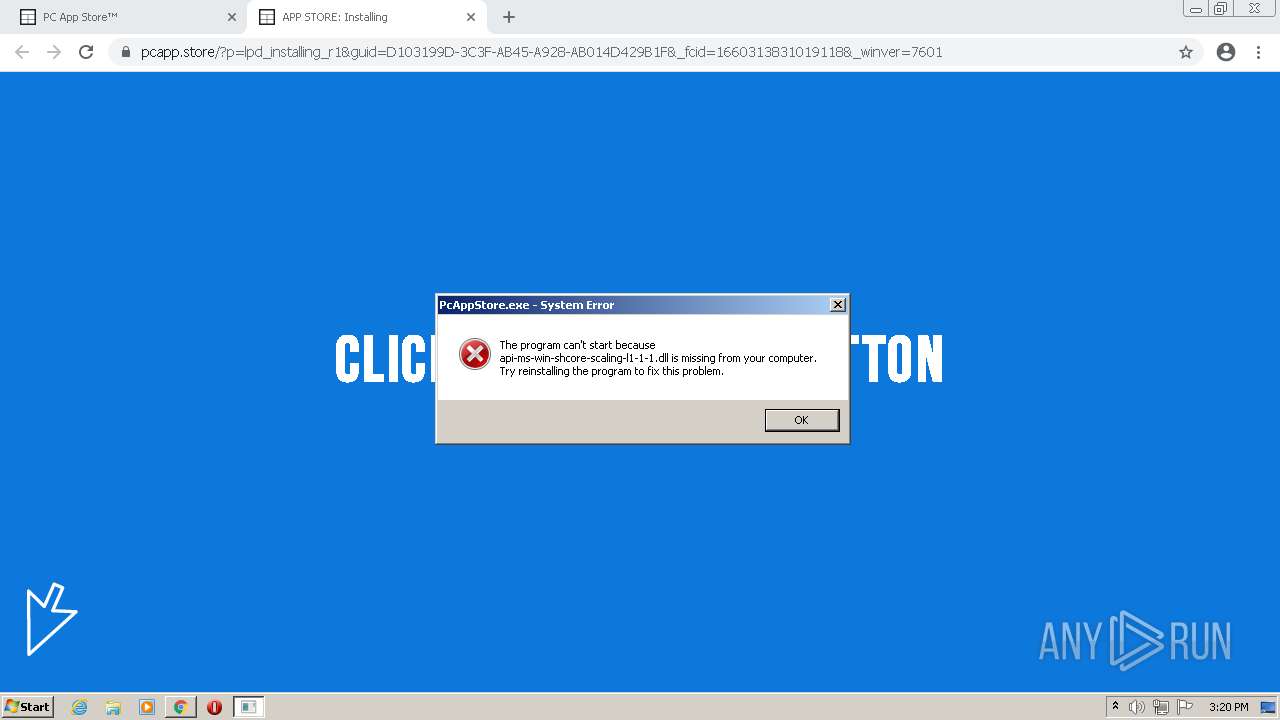
- PcAppStore.exe (PID: 3448)
- PcAppStore.exe (PID: 2984)
- PcAppStore.exe (PID: 2332)
Loads dropped or rewritten executable
- Setup.exe (PID: 3416)
- SearchProtocolHost.exe (PID: 2096)
Changes the autorun value in the registry
- Setup.exe (PID: 3416)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2964)
- chrome.exe (PID: 2820)
- Setup.exe (PID: 3416)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2964)
Drops a file with a compile date too recent
- chrome.exe (PID: 2964)
- chrome.exe (PID: 2820)
- Setup.exe (PID: 3416)
Checks supported languages
- Setup.exe (PID: 3416)
- ns7AB3.tmp (PID: 2080)
Reads the computer name
- Setup.exe (PID: 3416)
Reads Environment values
- Setup.exe (PID: 3416)
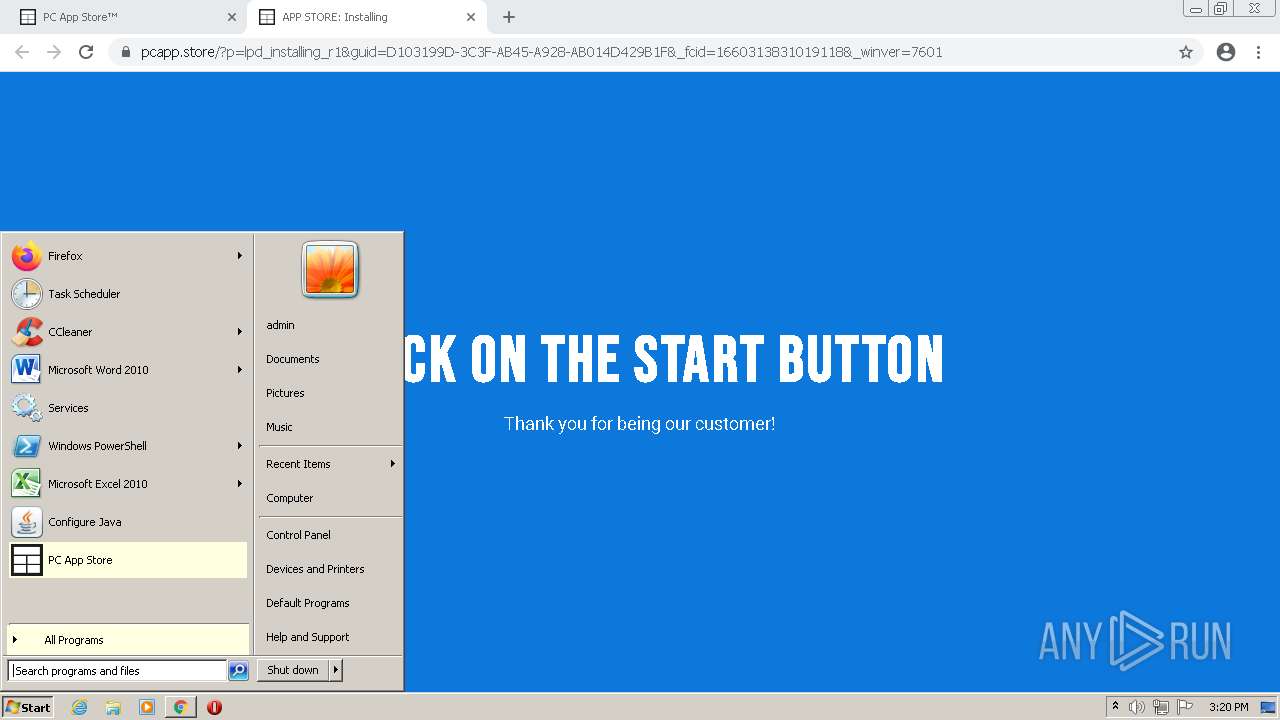
Creates a software uninstall entry
- Setup.exe (PID: 3416)
Starts application with an unusual extension
- Setup.exe (PID: 3416)
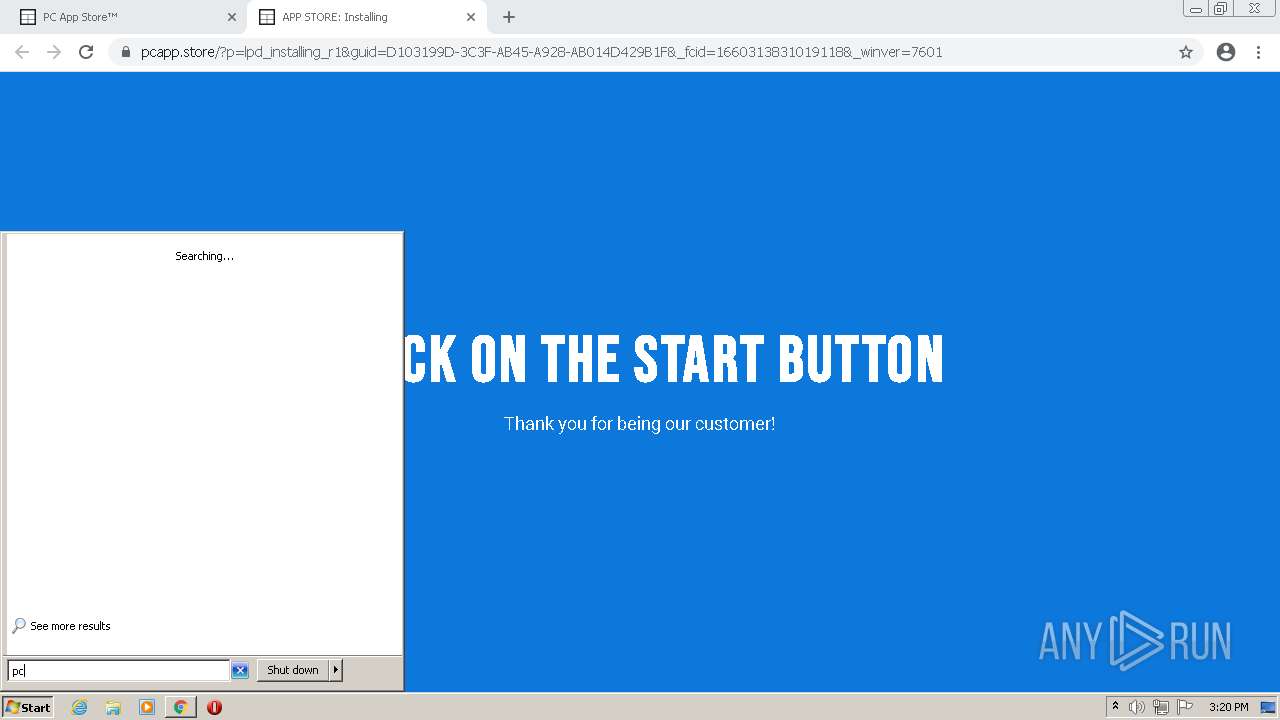
Searches for installed software
- Setup.exe (PID: 3416)
INFO
Checks supported languages
- chrome.exe (PID: 3624)
- chrome.exe (PID: 2964)
- chrome.exe (PID: 392)
- chrome.exe (PID: 420)
- chrome.exe (PID: 3804)
- chrome.exe (PID: 900)
- chrome.exe (PID: 1192)
- chrome.exe (PID: 3464)
- chrome.exe (PID: 2164)
- chrome.exe (PID: 2736)
- chrome.exe (PID: 2648)
- chrome.exe (PID: 3232)
- chrome.exe (PID: 2832)
- chrome.exe (PID: 2836)
- chrome.exe (PID: 1160)
- chrome.exe (PID: 4028)
- chrome.exe (PID: 3340)
- chrome.exe (PID: 2824)
- chrome.exe (PID: 1240)
- chrome.exe (PID: 1664)
- chrome.exe (PID: 1408)
- chrome.exe (PID: 2856)
- chrome.exe (PID: 2884)
- chrome.exe (PID: 1344)
- chrome.exe (PID: 2820)
- chrome.exe (PID: 900)
- SearchProtocolHost.exe (PID: 2096)
- chrome.exe (PID: 2044)
- chrome.exe (PID: 3632)
- chrome.exe (PID: 3300)
- chrome.exe (PID: 3820)
- chrome.exe (PID: 2484)
- chrome.exe (PID: 1880)
- chrome.exe (PID: 2072)
- chrome.exe (PID: 2792)
- chrome.exe (PID: 1716)
- SCHTASKS.exe (PID: 288)
- chrome.exe (PID: 2516)
Reads the computer name
- chrome.exe (PID: 3624)
- chrome.exe (PID: 2964)
- chrome.exe (PID: 1192)
- chrome.exe (PID: 3232)
- chrome.exe (PID: 1160)
- chrome.exe (PID: 3804)
- chrome.exe (PID: 2836)
- chrome.exe (PID: 1408)
- chrome.exe (PID: 1344)
- chrome.exe (PID: 1664)
- chrome.exe (PID: 2824)
- chrome.exe (PID: 3300)
- SearchProtocolHost.exe (PID: 2096)
- chrome.exe (PID: 900)
- chrome.exe (PID: 2484)
- SCHTASKS.exe (PID: 288)
Reads settings of System Certificates
- chrome.exe (PID: 1192)
- chrome.exe (PID: 2964)
- Setup.exe (PID: 3416)
Application launched itself
- chrome.exe (PID: 2964)
- chrome.exe (PID: 2484)
Reads the date of Windows installation
- chrome.exe (PID: 1344)
Checks Windows Trust Settings
- chrome.exe (PID: 2964)
- Setup.exe (PID: 3416)
Dropped object may contain Bitcoin addresses
- Setup.exe (PID: 3416)
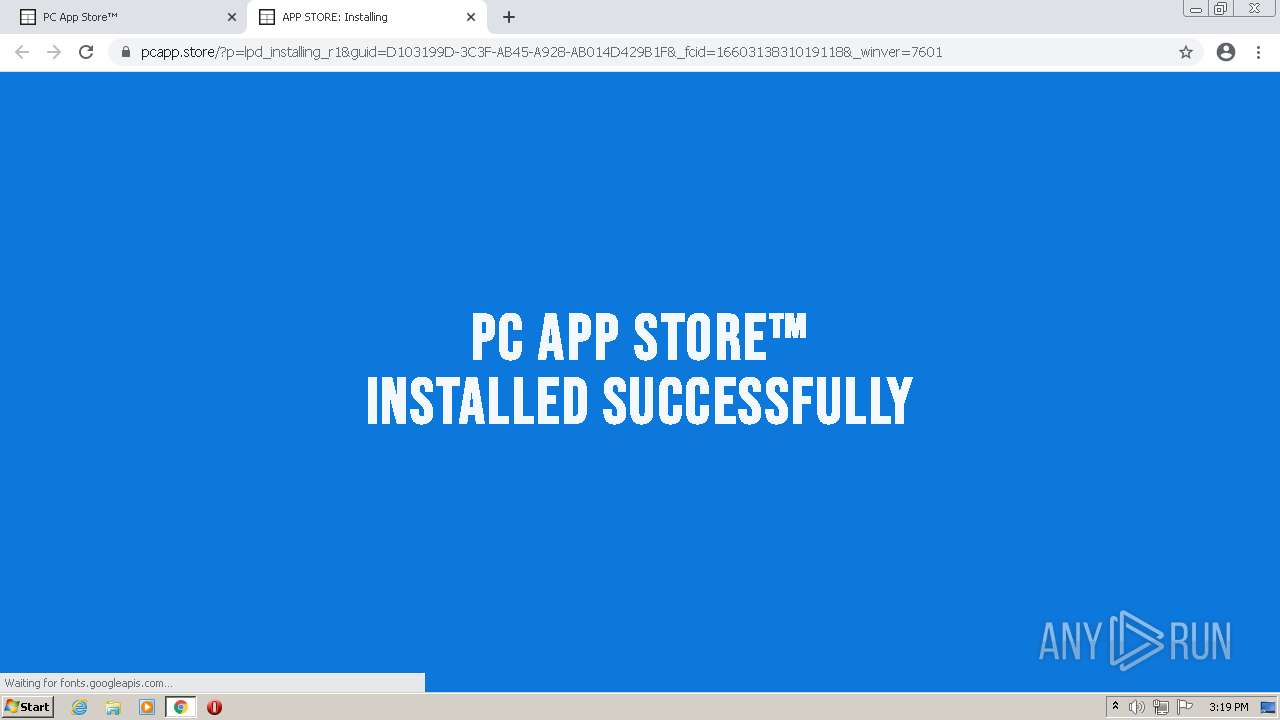
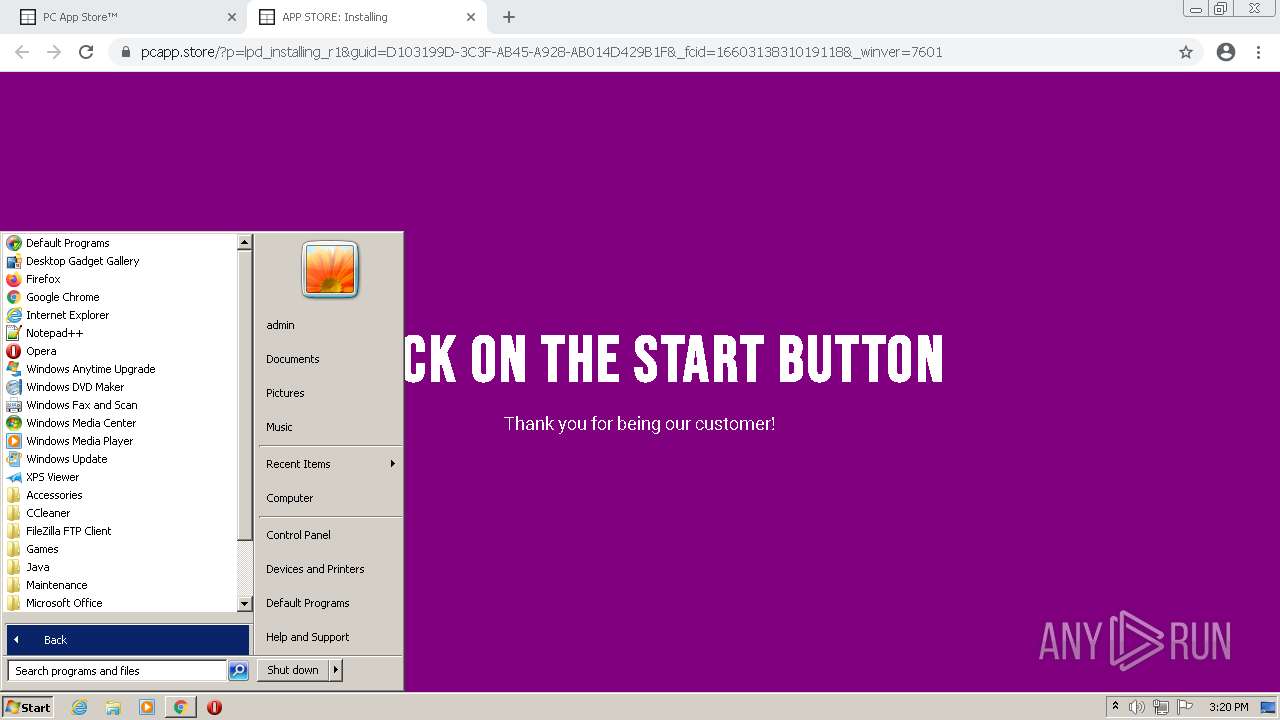
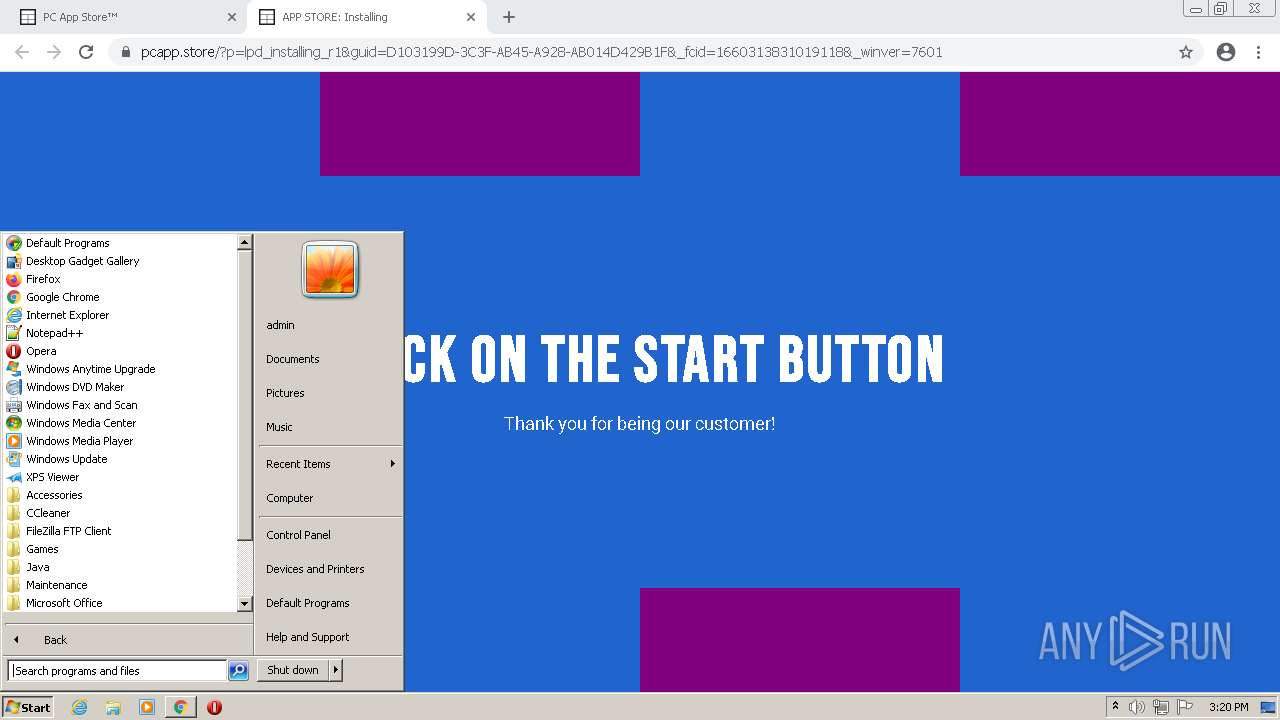
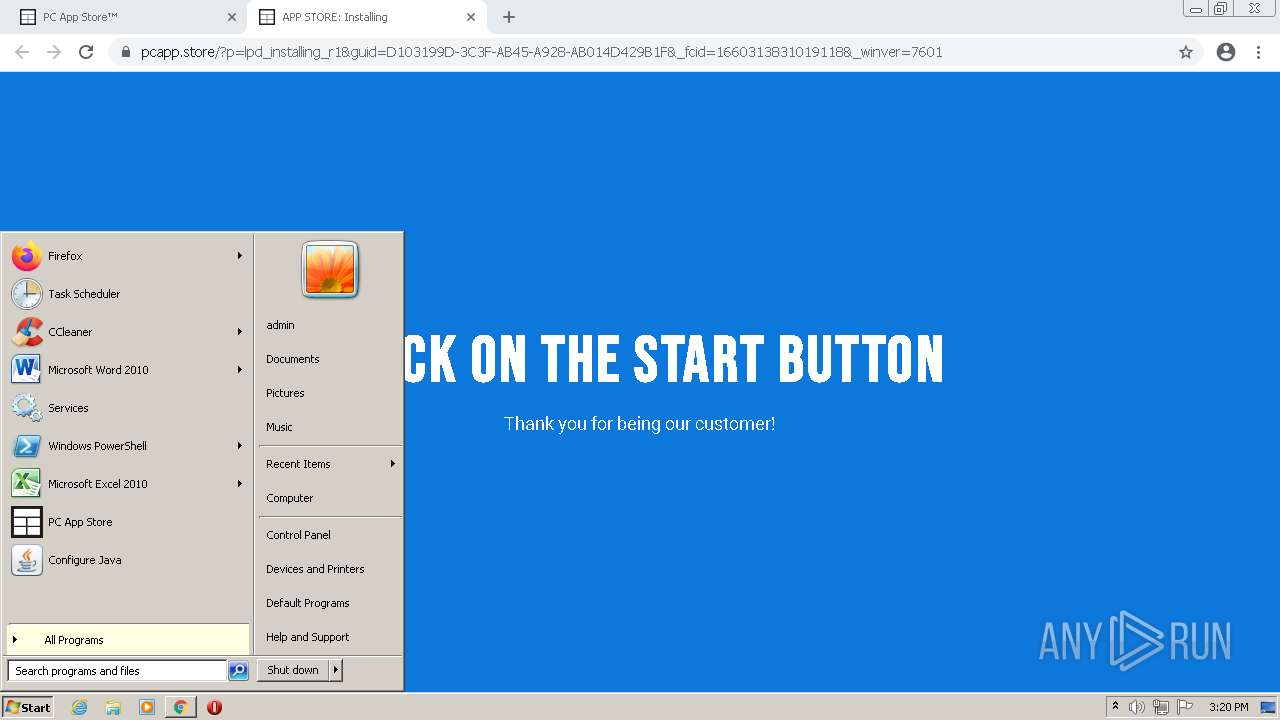
Manual execution by user
- PcAppStore.exe (PID: 2984)
- PcAppStore.exe (PID: 2332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
86
Monitored processes
43
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://storage.snappages.site" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 86.0.4240.198 | ||||
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6f70d988,0x6f70d998,0x6f70d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 86.0.4240.198 | ||||
| 3624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,15373860407787347838,4535734421263363493,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1060 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1036,15373860407787347838,4535734421263363493,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1240 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 86.0.4240.198 | ||||
| 420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,15373860407787347838,4535734421263363493,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1876 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 3464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,15373860407787347838,4535734421263363493,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1816 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,15373860407787347838,4535734421263363493,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2200 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 3804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,15373860407787347838,4535734421263363493,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1024 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 86.0.4240.198 | ||||
| 2164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,15373860407787347838,4535734421263363493,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2708 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 2736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1036,15373860407787347838,4535734421263363493,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3632 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
Total events
23 443
Read events
23 203
Write events
0
Delete events
0
Modification events
Executable files
22
Suspicious files
61
Text files
238
Unknown types
68
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62F660DD-B94.pma | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fd1cccca-6960-4a5f-b25b-8086b4a23f99.tmp | text | |
MD5:7A200B0EB26FB64C0E3AFA677BCDFA1C | SHA256:04DC61FF658E77BBEE6B1707480A654E8A3FCBC53E1112441CD539076F171F84 | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:7A200B0EB26FB64C0E3AFA677BCDFA1C | SHA256:04DC61FF658E77BBEE6B1707480A654E8A3FCBC53E1112441CD539076F171F84 | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RFda652.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFda48d.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old~RFda99e.TMP | text | |
MD5:D0BA19096D6C8F8DE58312E8D938E893 | SHA256:AADE90A7B0984F3C719D528E4E6FAE3854E28B30363BDD4DF65037E69784A078 | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old | text | |
MD5:5202CA4D6AF0C37DAEC0D528CC7F2986 | SHA256:8F5B8FF94B14C36EA0CBE8FA0A4D165A632B45F834BBB7239E1A6CF6685F256C | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RFda71e.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
64
DNS requests
31
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acym664js5xux6kw2viy4atw4uda_2022.8.8.1144/ggkkehgbnfjpeggfpleeakpidbkibbmn_2022.8.8.1144_all_olesxce7qq7cy7sctjkoeb4tce.crx3 | US | — | — | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acym664js5xux6kw2viy4atw4uda_2022.8.8.1144/ggkkehgbnfjpeggfpleeakpidbkibbmn_2022.8.8.1144_all_olesxce7qq7cy7sctjkoeb4tce.crx3 | US | binary | 3.01 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 90.0 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 358 Kb | whitelisted |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODJiQUFYYVJaZ0k5di1hUFlXS1prX2xDZw/1.0.0.13_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | binary | 8.94 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ctobqmjkcx6vb5b5bkfjsvzaf4_7515/hfnkpimlhhgieaddgfemjhofmfblmnib_7515_all_ad4zhmk67skhjeisdlirizreje5a.crx3 | US | binary | 8.94 Kb | whitelisted |
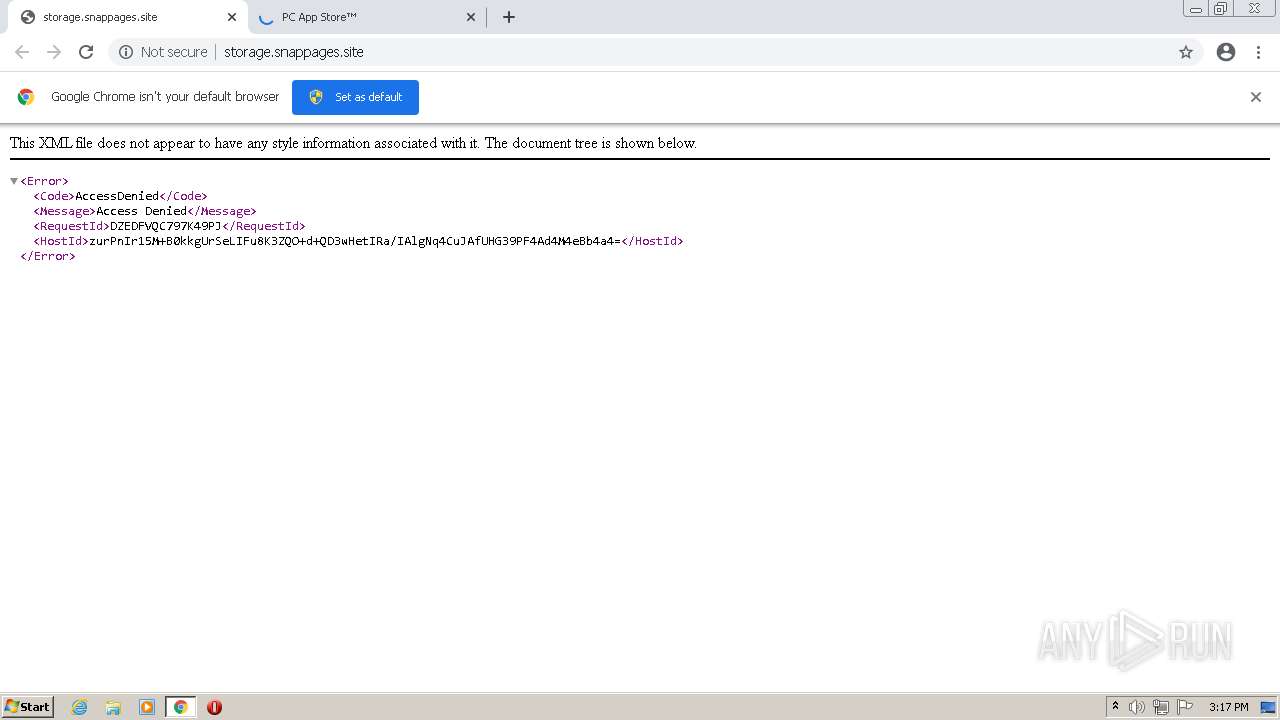
1192 | chrome.exe | GET | 403 | 13.224.189.76:80 | http://storage.snappages.site/ | US | xml | 243 b | malicious |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 718 Kb | whitelisted |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ctobqmjkcx6vb5b5bkfjsvzaf4_7515/hfnkpimlhhgieaddgfemjhofmfblmnib_7515_all_ad4zhmk67skhjeisdlirizreje5a.crx3 | US | binary | 3.01 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 1.41 Mb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1192 | chrome.exe | 142.250.186.110:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
— | — | 142.250.185.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
1192 | chrome.exe | 142.250.186.36:443 | www.google.com | Google Inc. | US | whitelisted |
1192 | chrome.exe | 142.250.74.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
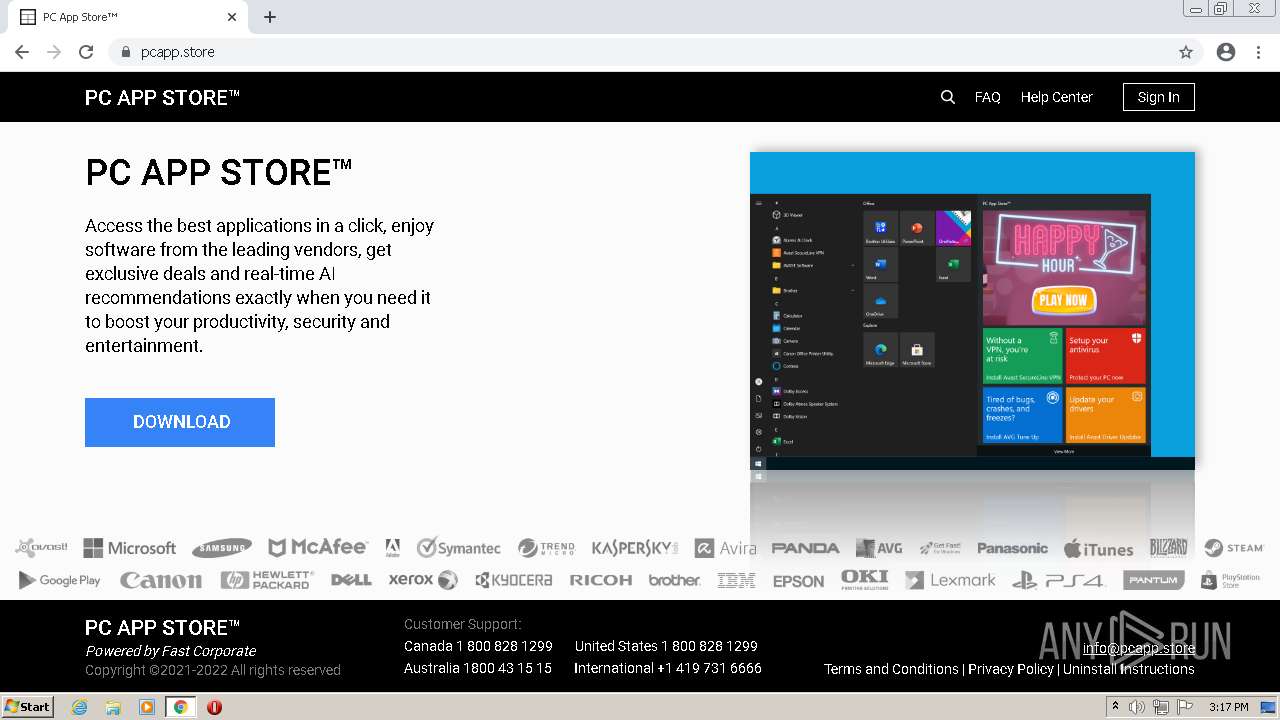
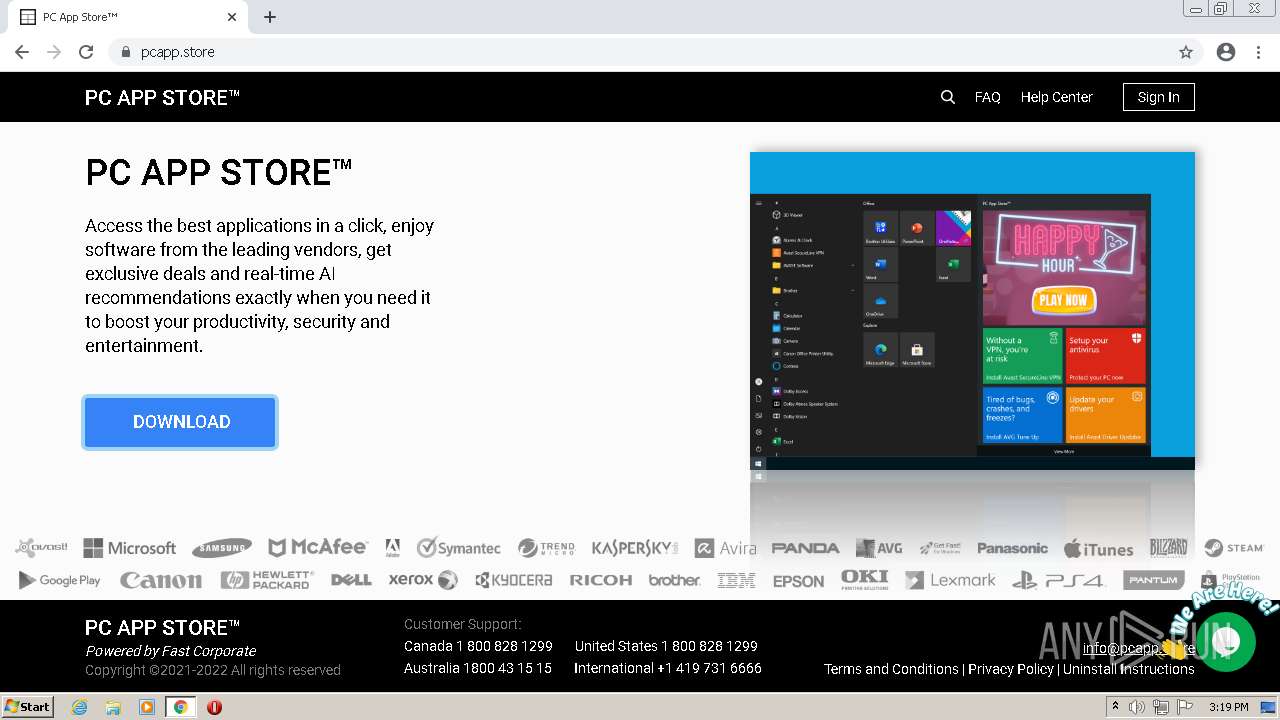
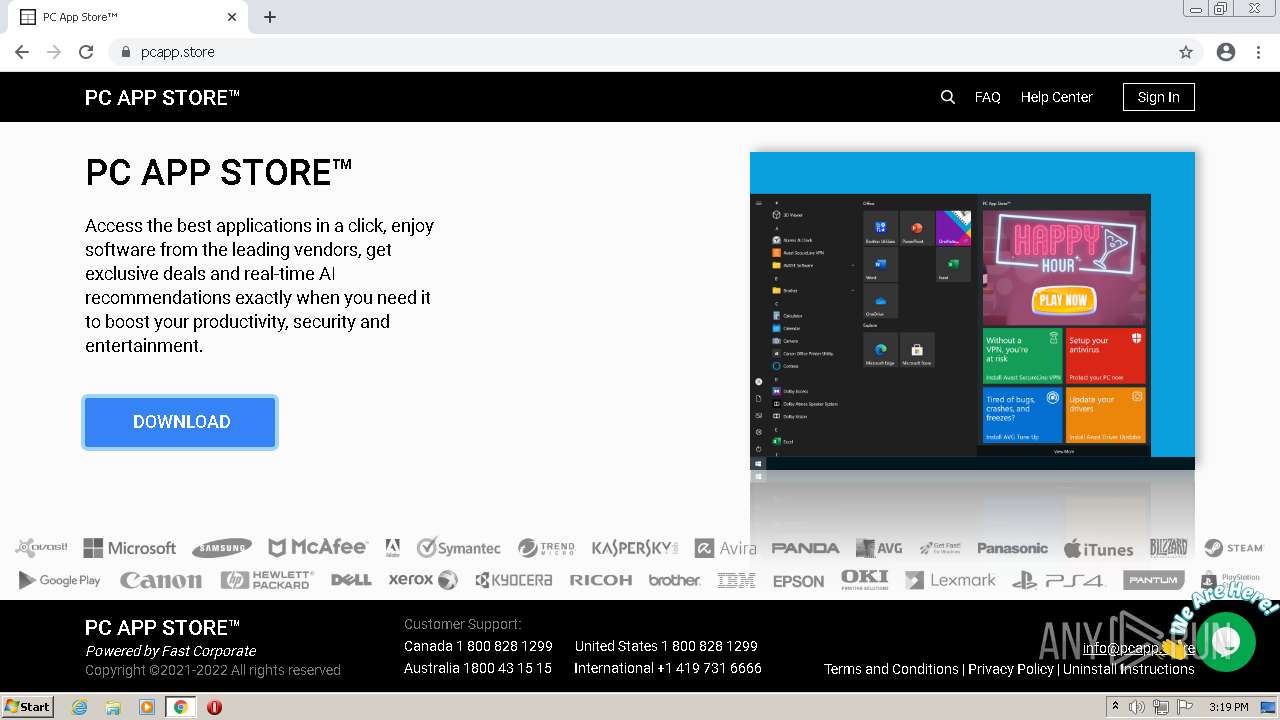
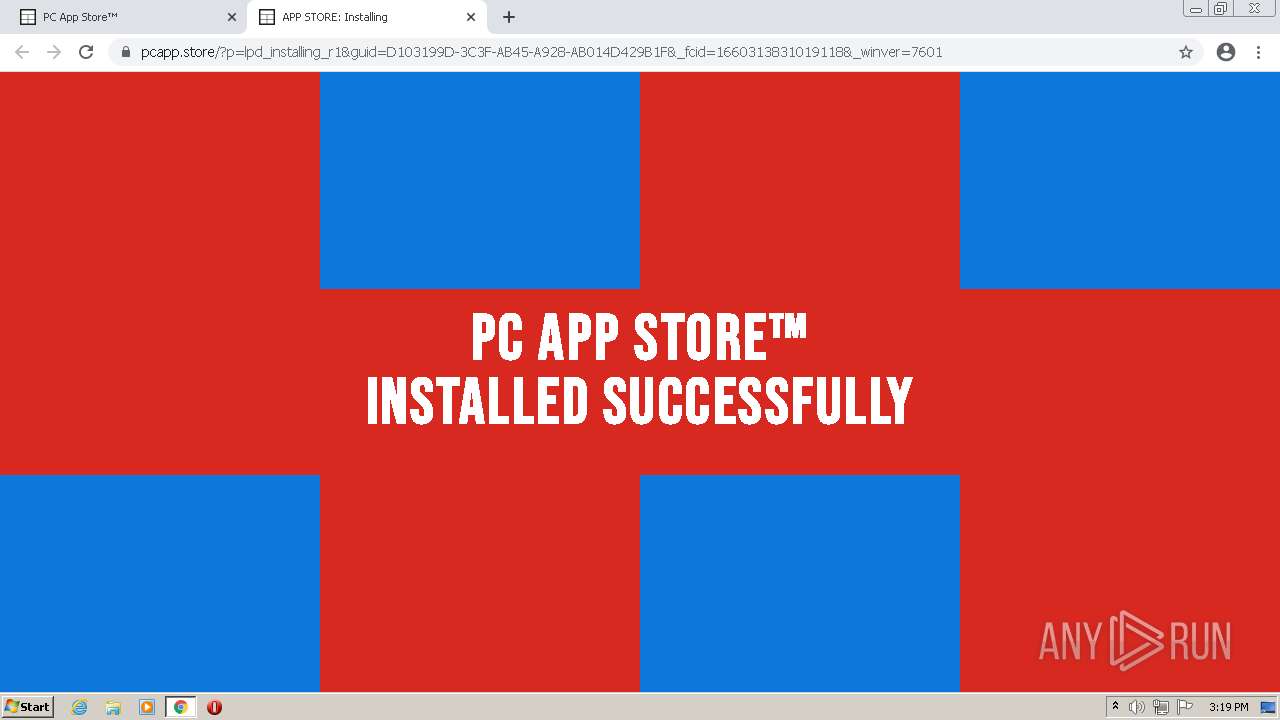
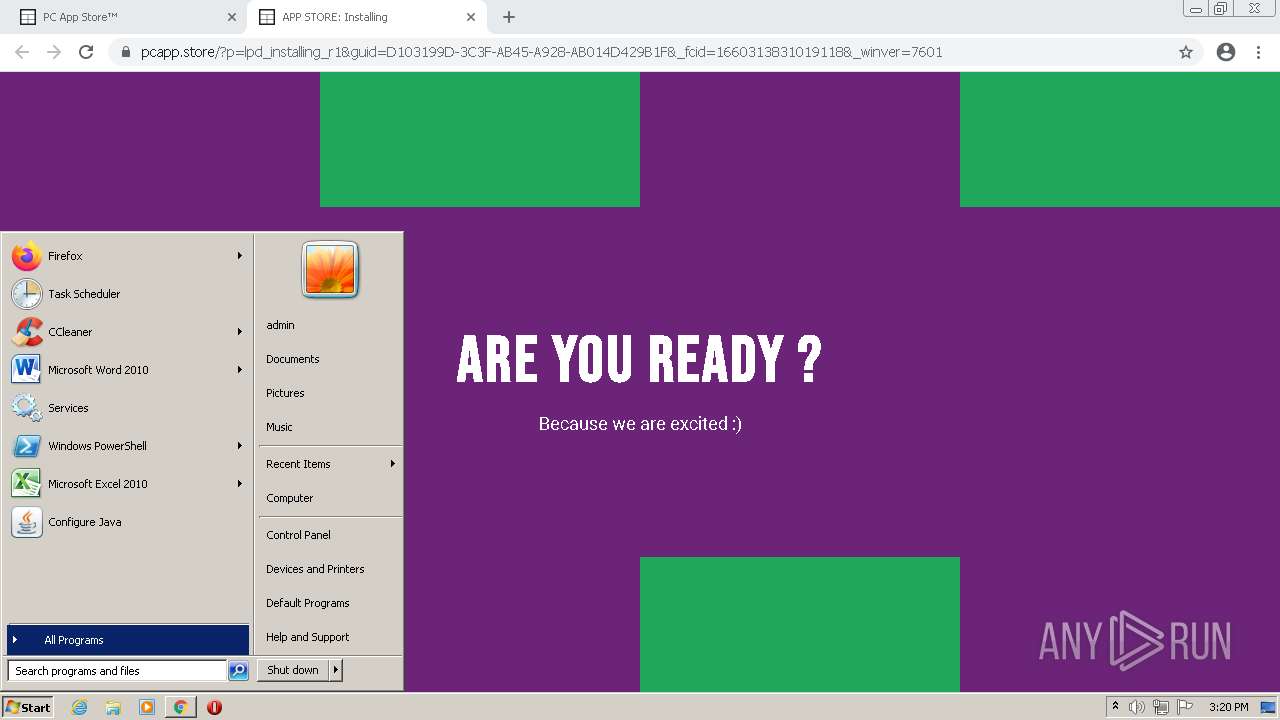
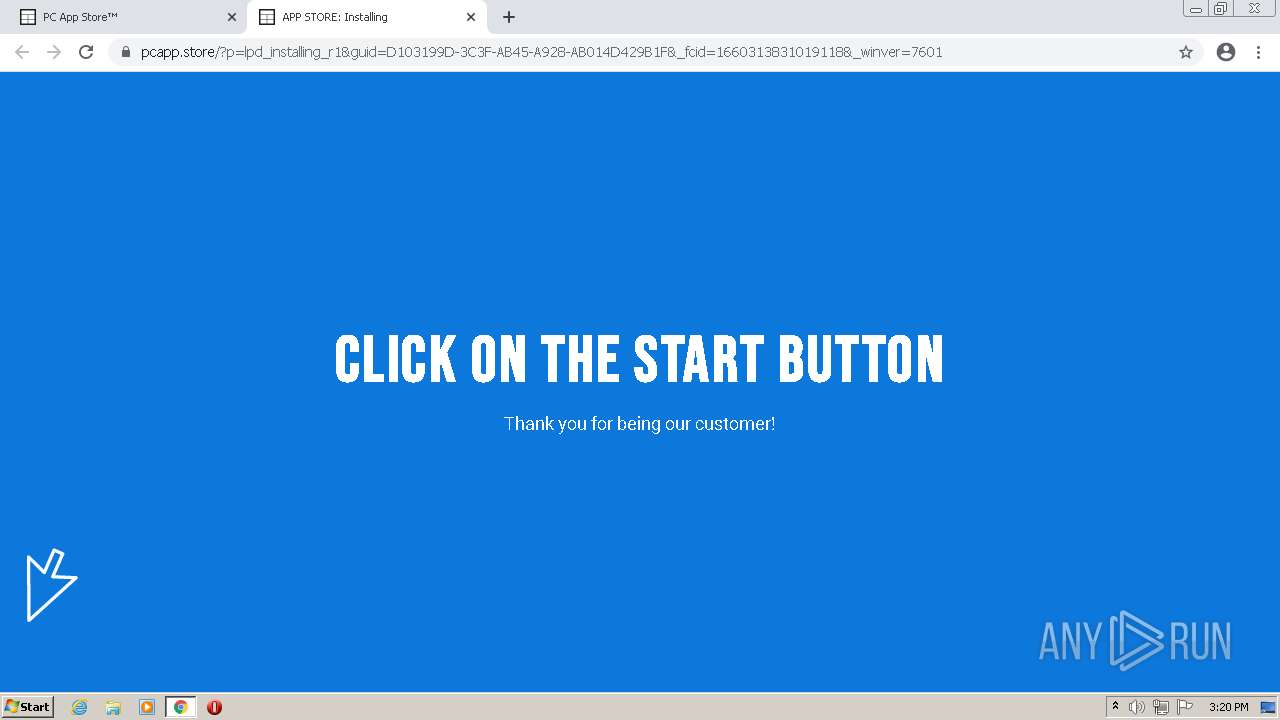
1192 | chrome.exe | 3.215.103.17:80 | pcapp.store | — | US | unknown |
1192 | chrome.exe | 13.224.189.76:80 | storage.snappages.site | — | US | unknown |
1192 | chrome.exe | 3.215.103.17:443 | pcapp.store | — | US | unknown |
1192 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
1192 | chrome.exe | 108.177.15.157:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
1192 | chrome.exe | 142.250.186.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
storage.snappages.site |
| malicious |
www.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
pcapp.store |
| suspicious |
fonts.gstatic.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
embed.tawk.to |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |