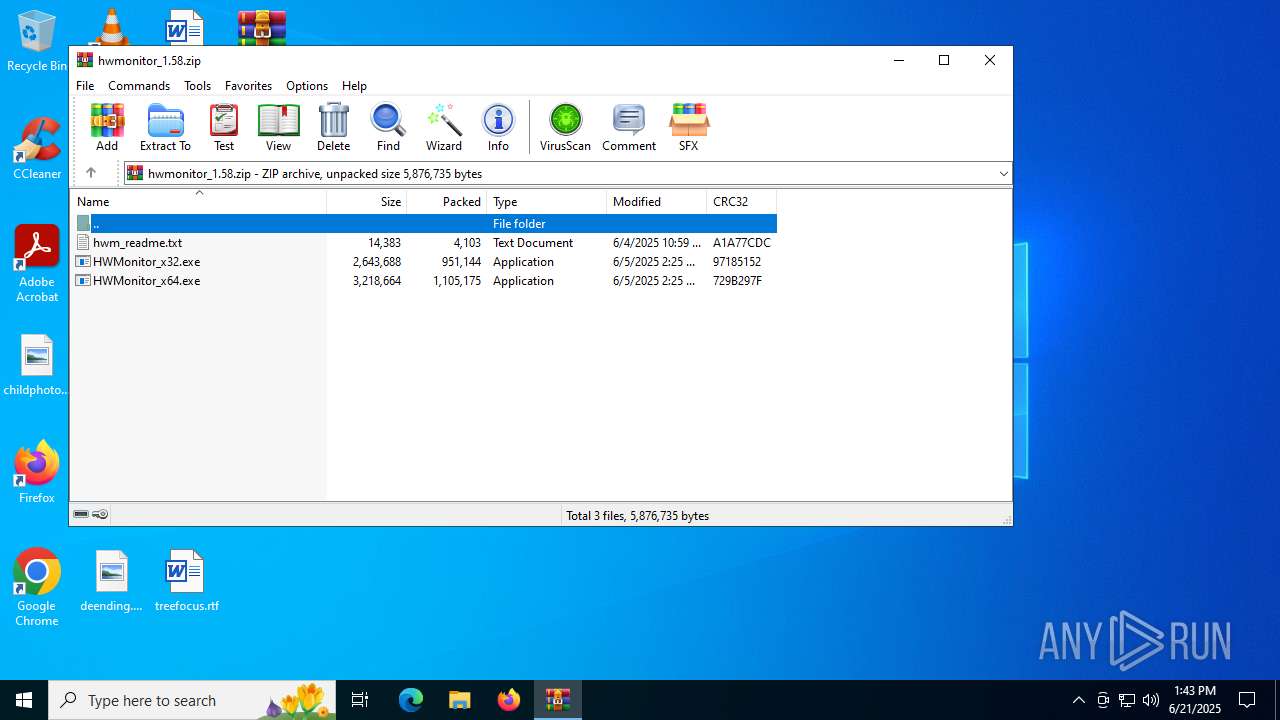
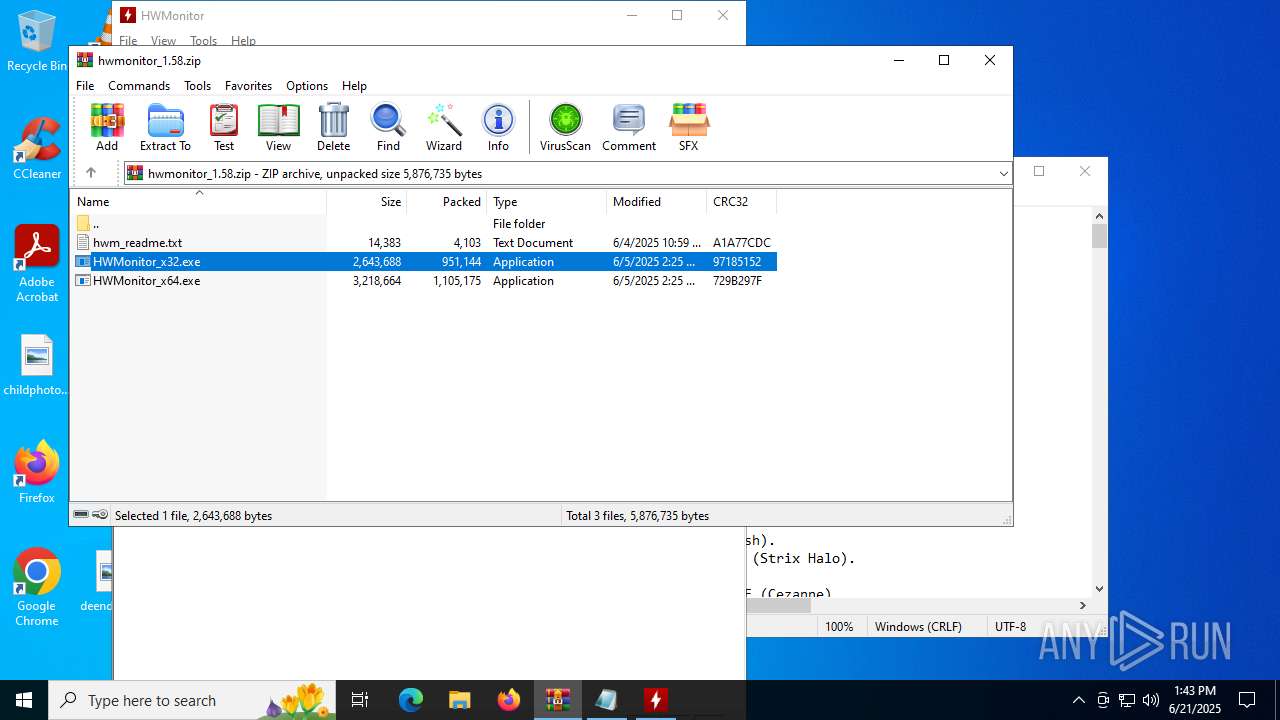
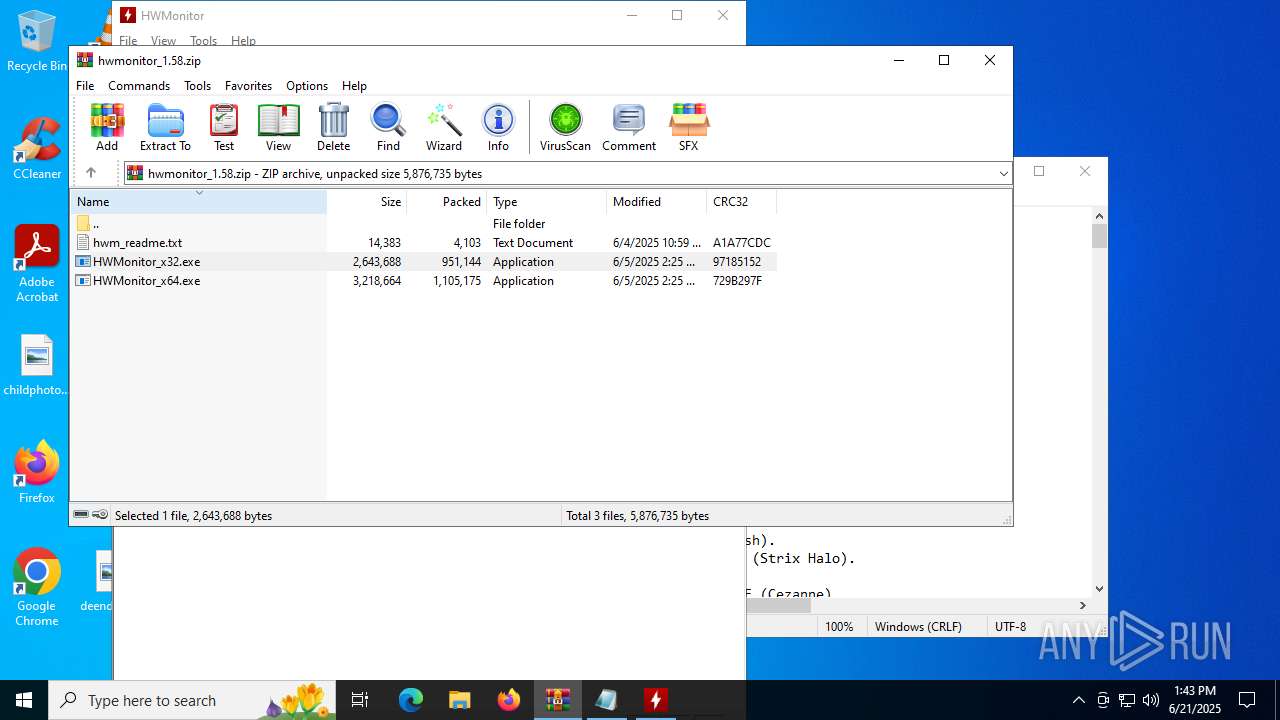
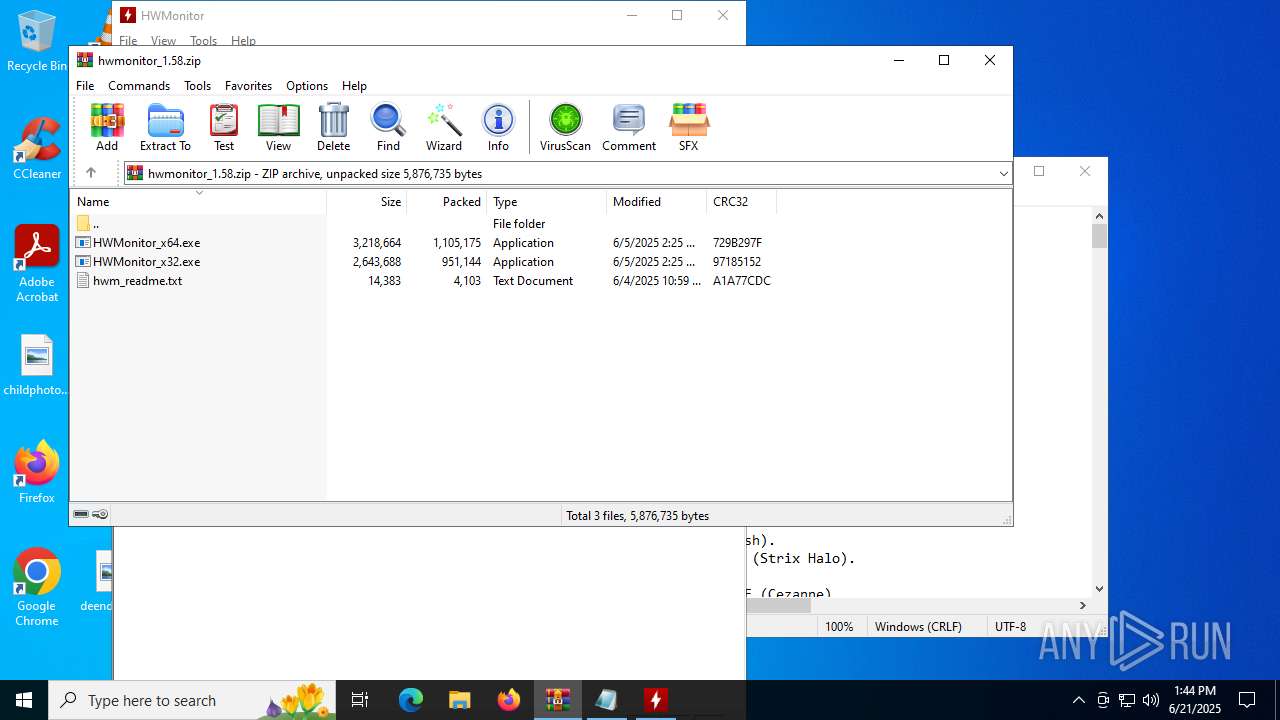
| File name: | hwmonitor_1.58.zip |
| Full analysis: | https://app.any.run/tasks/fe27ddaf-29da-4607-88c7-f406043431dd |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 13:43:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | E6062DCD70068B624BF3D00DB984CDAB |
| SHA1: | C3D1C01D68B1AE396493F49699BE8C90AB9281C1 |
| SHA256: | FDA3B6D7F906709E4ACE010E260EB83471673664FDED96EB3C60DEFAE0FEC620 |
| SSDEEP: | 98304:zZ4hE0lCZS+uZiNMnSo9GkkVy3LNDrquUPlo1V1T+J52/90OLN8IRWpf3qlDMA5y:YE3P |
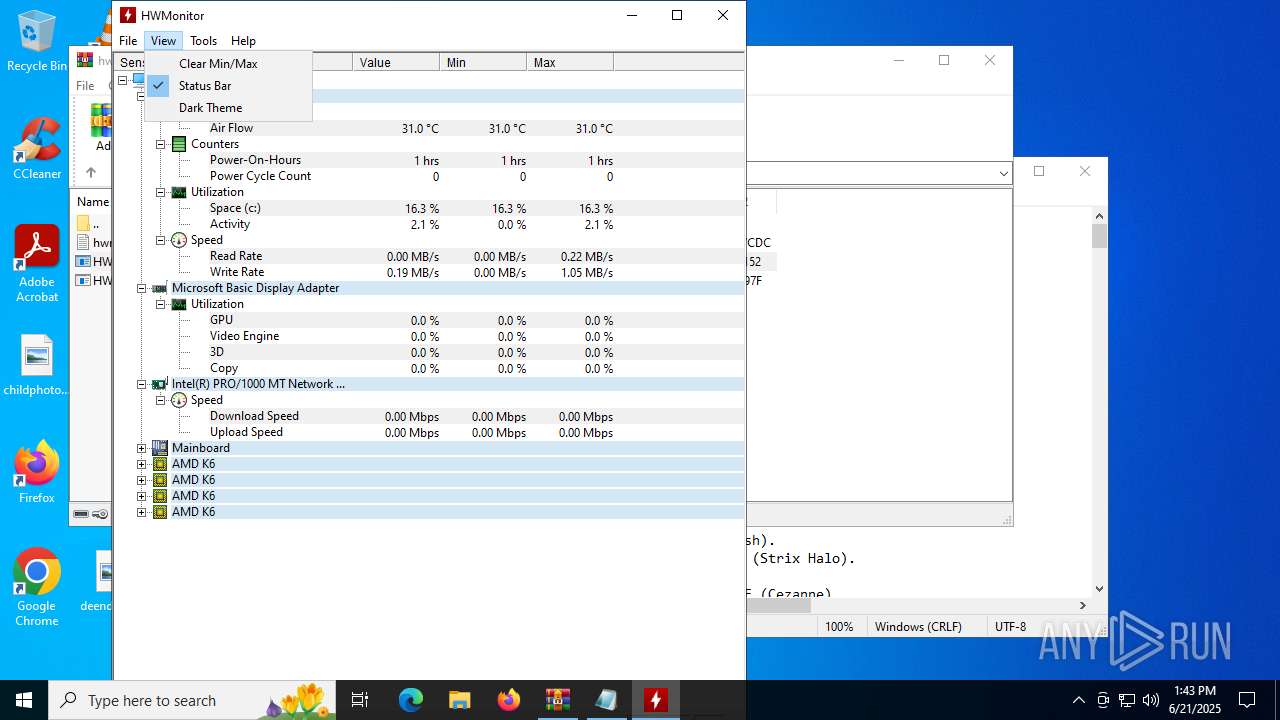
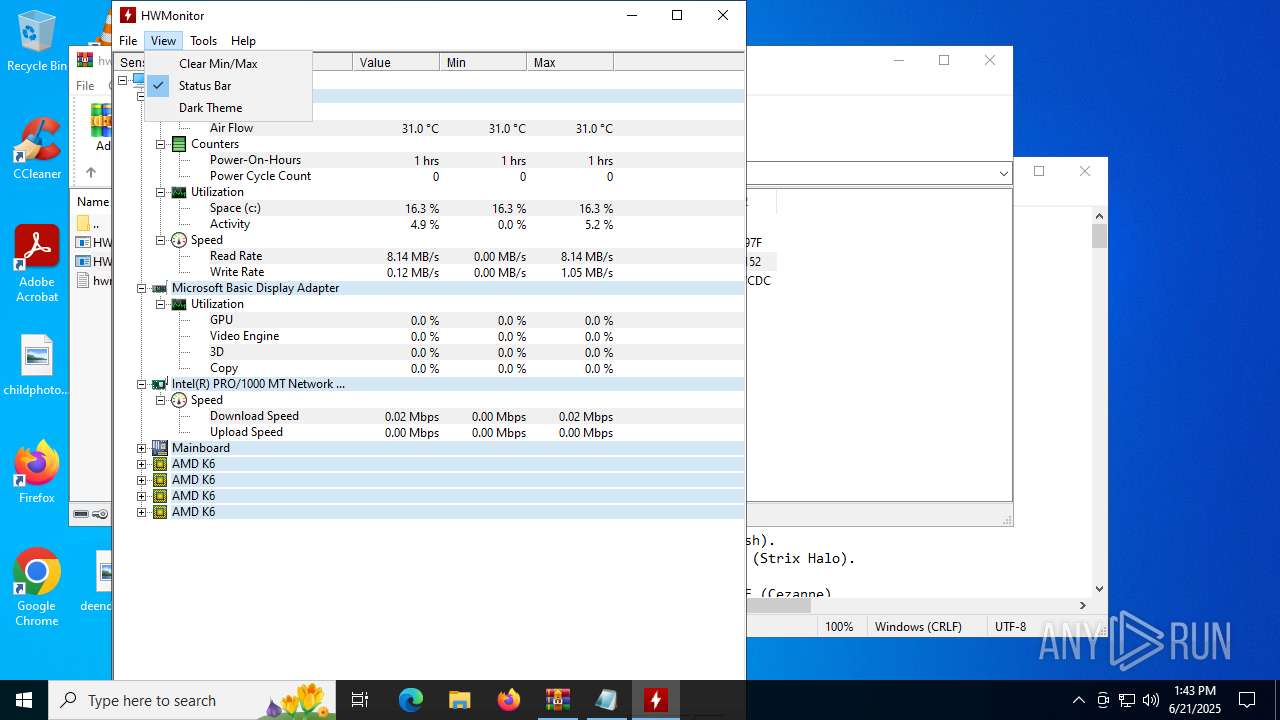
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 188)
SUSPICIOUS
Executable content was dropped or overwritten
- HWMonitor_x64.exe (PID: 7124)
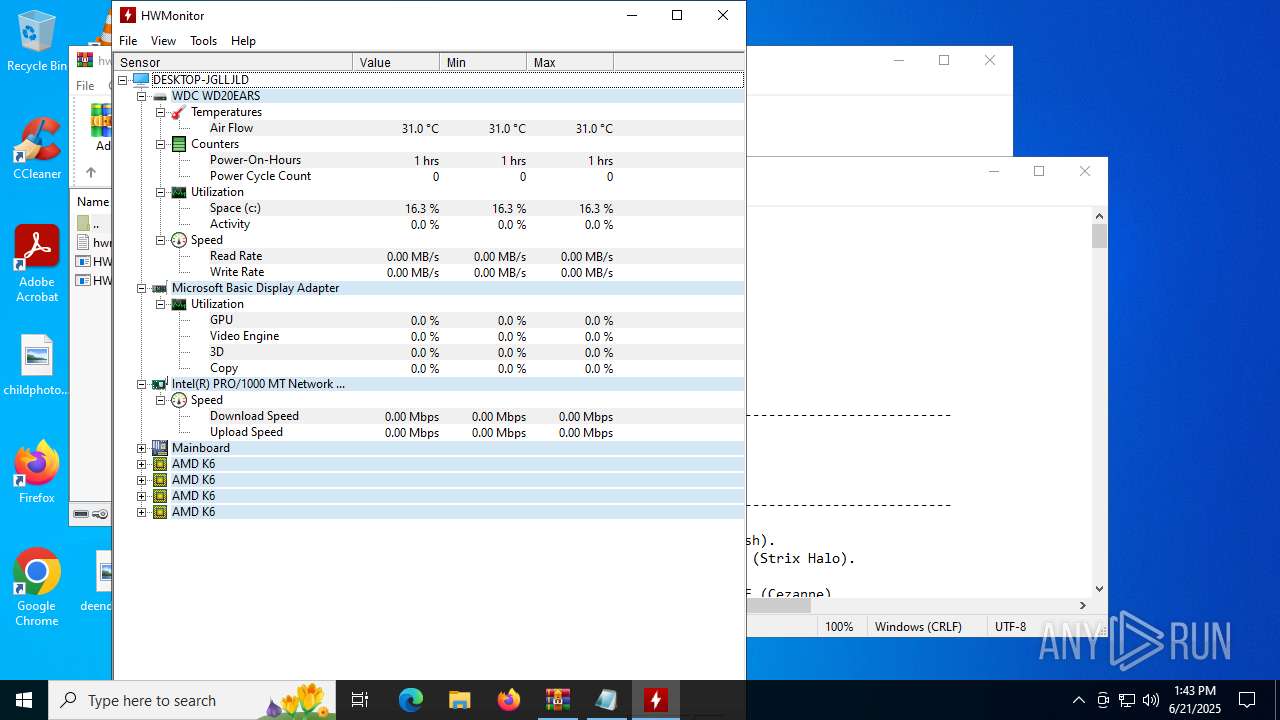
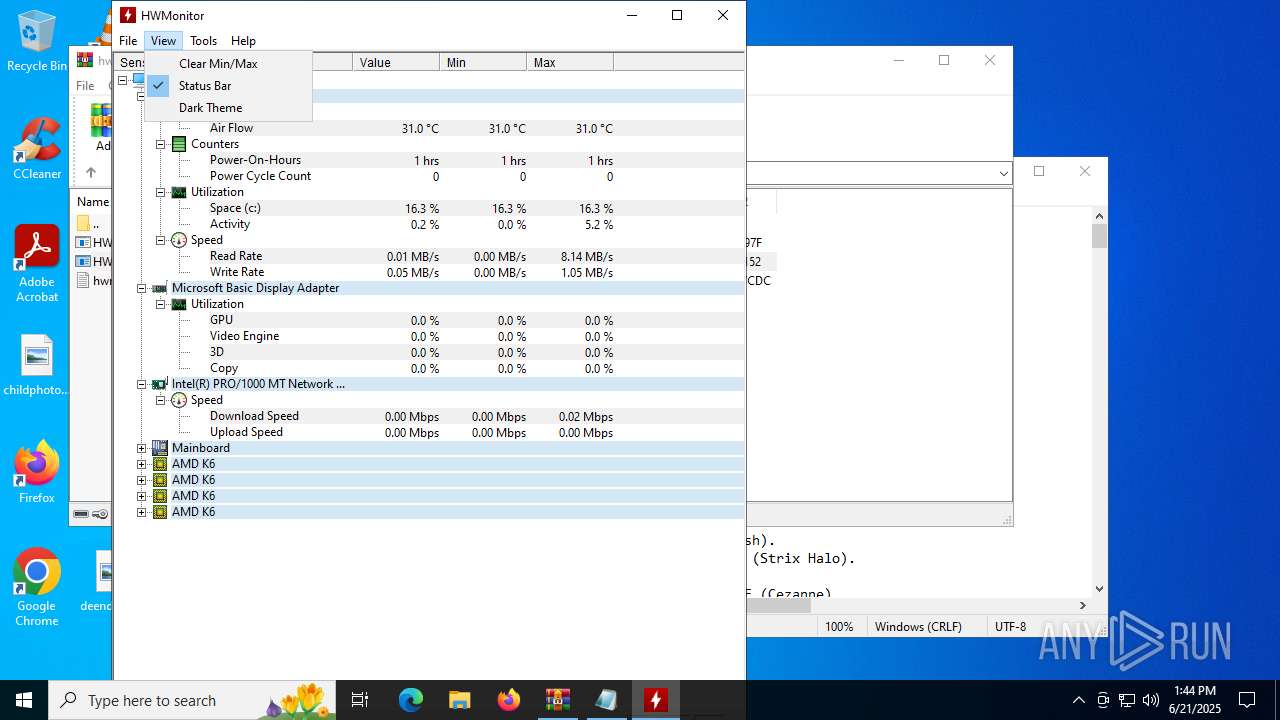
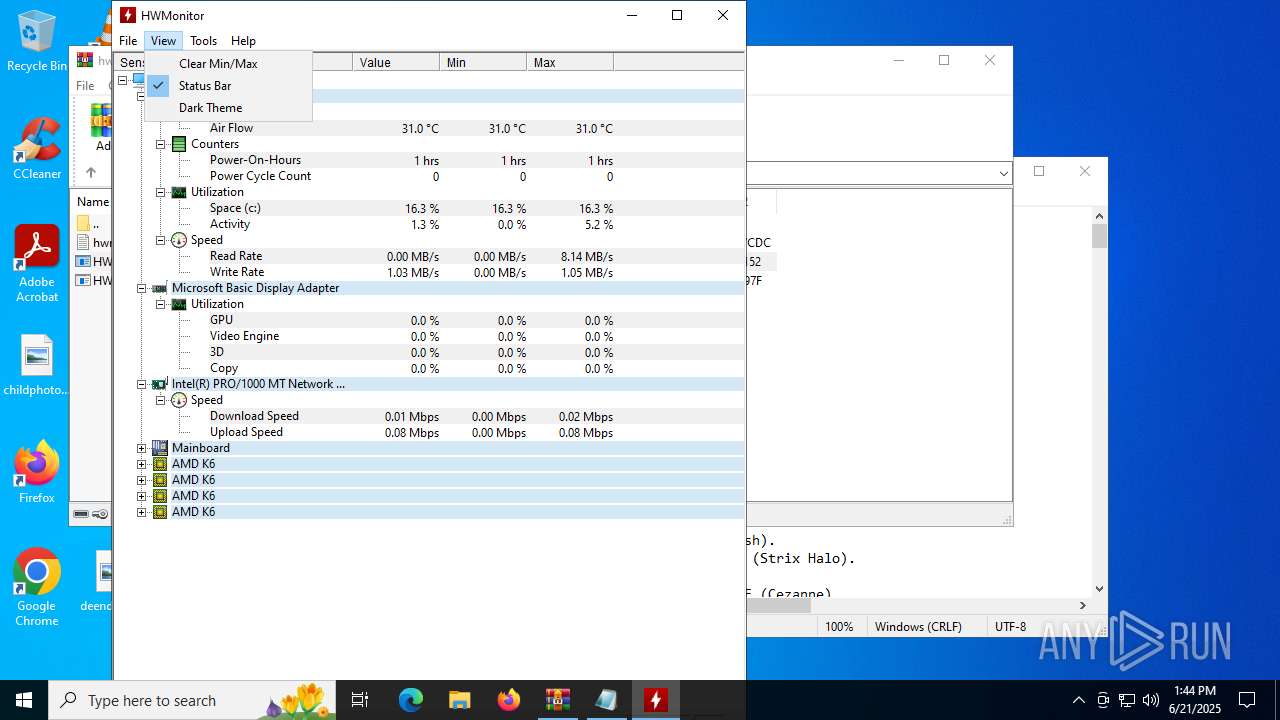
The process checks if it is being run in the virtual environment
- HWMonitor_x64.exe (PID: 7124)
Executes as Windows Service
- WmiApSrv.exe (PID: 3652)
Reads security settings of Internet Explorer
- HWMonitor_x64.exe (PID: 7124)
Drops a system driver (possible attempt to evade defenses)
- HWMonitor_x64.exe (PID: 7124)
INFO
Reads security settings of Internet Explorer
- notepad.exe (PID: 3888)
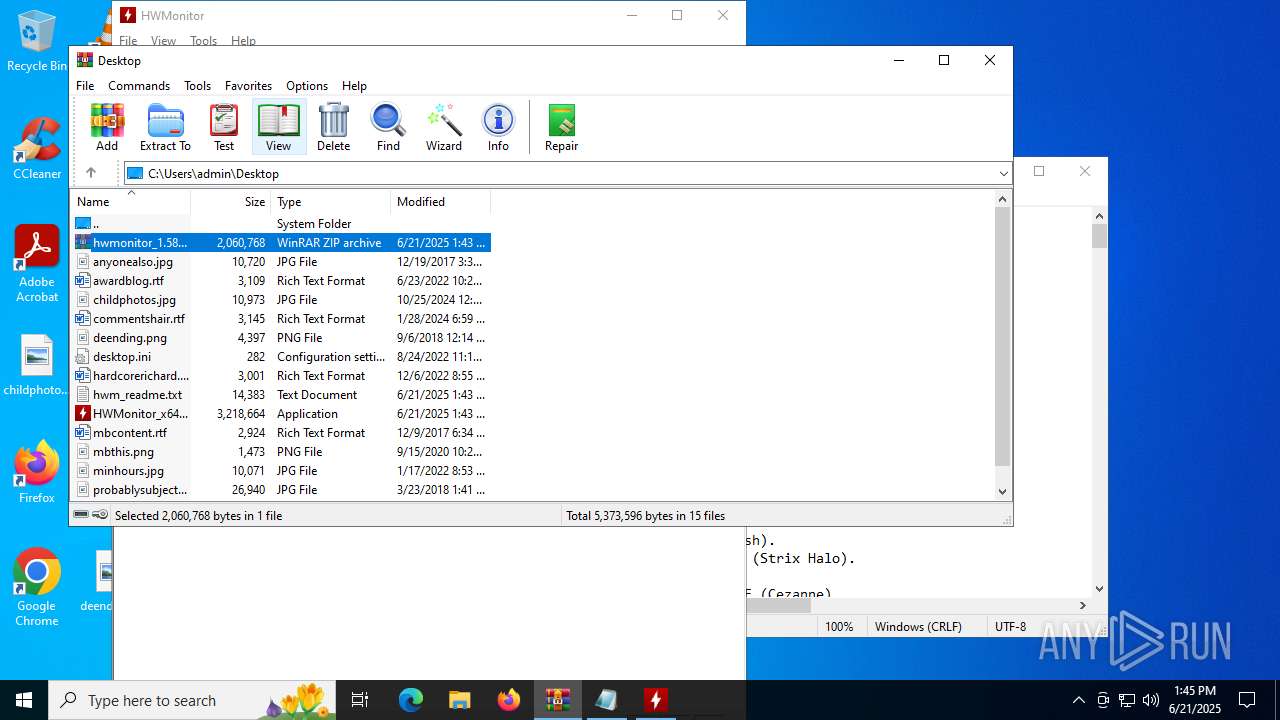
Manual execution by a user
- HWMonitor_x64.exe (PID: 7100)
- notepad.exe (PID: 3888)
- HWMonitor_x64.exe (PID: 7124)
CPUZ mutex has been found
- HWMonitor_x64.exe (PID: 7124)
Reads the machine GUID from the registry
- HWMonitor_x64.exe (PID: 7124)
Reads the software policy settings
- HWMonitor_x64.exe (PID: 7124)
- slui.exe (PID: 4312)
The sample compiled with english language support
- HWMonitor_x64.exe (PID: 7124)
Creates files or folders in the user directory
- HWMonitor_x64.exe (PID: 7124)
Checks proxy server information
- slui.exe (PID: 4312)
- HWMonitor_x64.exe (PID: 7124)
Reads the time zone
- HWMonitor_x64.exe (PID: 7124)
Reads CPU info
- HWMonitor_x64.exe (PID: 7124)
Checks supported languages
- HWMonitor_x64.exe (PID: 7124)
Reads the computer name
- HWMonitor_x64.exe (PID: 7124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:06:04 10:59:58 |
| ZipCRC: | 0xa1a77cdc |
| ZipCompressedSize: | 4103 |
| ZipUncompressedSize: | 14383 |
| ZipFileName: | hwm_readme.txt |
Total processes
141
Monitored processes
6
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\hwmonitor_1.58.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 3652 | C:\WINDOWS\system32\wbem\WmiApSrv.exe | C:\Windows\System32\wbem\WmiApSrv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Performance Reverse Adapter Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3888 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\hwm_readme.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4312 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7100 | "C:\Users\admin\Desktop\HWMonitor_x64.exe" | C:\Users\admin\Desktop\HWMonitor_x64.exe | — | explorer.exe | |||||||||||
User: admin Company: CPUID Integrity Level: MEDIUM Description: HWMonitor Exit code: 3221226540 Version: 1, 5, 8, 0 Modules
| |||||||||||||||
| 7124 | "C:\Users\admin\Desktop\HWMonitor_x64.exe" | C:\Users\admin\Desktop\HWMonitor_x64.exe | explorer.exe | ||||||||||||
User: admin Company: CPUID Integrity Level: HIGH Description: HWMonitor Version: 1, 5, 8, 0 Modules
| |||||||||||||||
Total events
13 806
Read events
13 763
Write events
43
Delete events
0
Modification events
| (PID) Process: | (188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\hwmonitor_1.58.zip | |||
| (PID) Process: | (188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
Executable files
1
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7124 | HWMonitor_x64.exe | C:\Windows\INF\basicrender.PNF | binary | |
MD5:F633F91CD25918725CC1193934BDB4D1 | SHA256:1BDF5C7710D4CB3CB5A00859779E5AC9F81702E927E5159D8707F2D6FE77E472 | |||
| 7124 | HWMonitor_x64.exe | C:\Windows\INF\display.PNF | binary | |
MD5:8C9889C33A26A1CD2A23341C16A8BAB1 | SHA256:8CCD07B8ADCDB4D72E84F082D685E80C64D4B68A709191169CB91B32A5DF8AC7 | |||
| 7124 | HWMonitor_x64.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\cpuid[1].ver | text | |
MD5:B022CDD4E457059A41F2858F37331EDA | SHA256:8D51554BF51E2F42B6AA8A139FA364A3BAC2434938CD06DBA11C91AF0CF97E59 | |||
| 7124 | HWMonitor_x64.exe | C:\Windows\Temp\cpuz160\cpuz160_x64.sys | executable | |
MD5:4C24FA0C01F6753C8F181D1D0E248244 | SHA256:BF467221B0A9A5FE75B61C61FF679247DE093EB9846B5B143D396484AD8C6FCD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
22
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4172 | RUXIMICS.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 195.154.81.43:443 | https://download.cpuid.com/cpuid.ver | unknown | text | 142 b | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4172 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
2940 | svchost.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4172 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
1268 | svchost.exe | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
4172 | RUXIMICS.exe | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
download.cpuid.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |