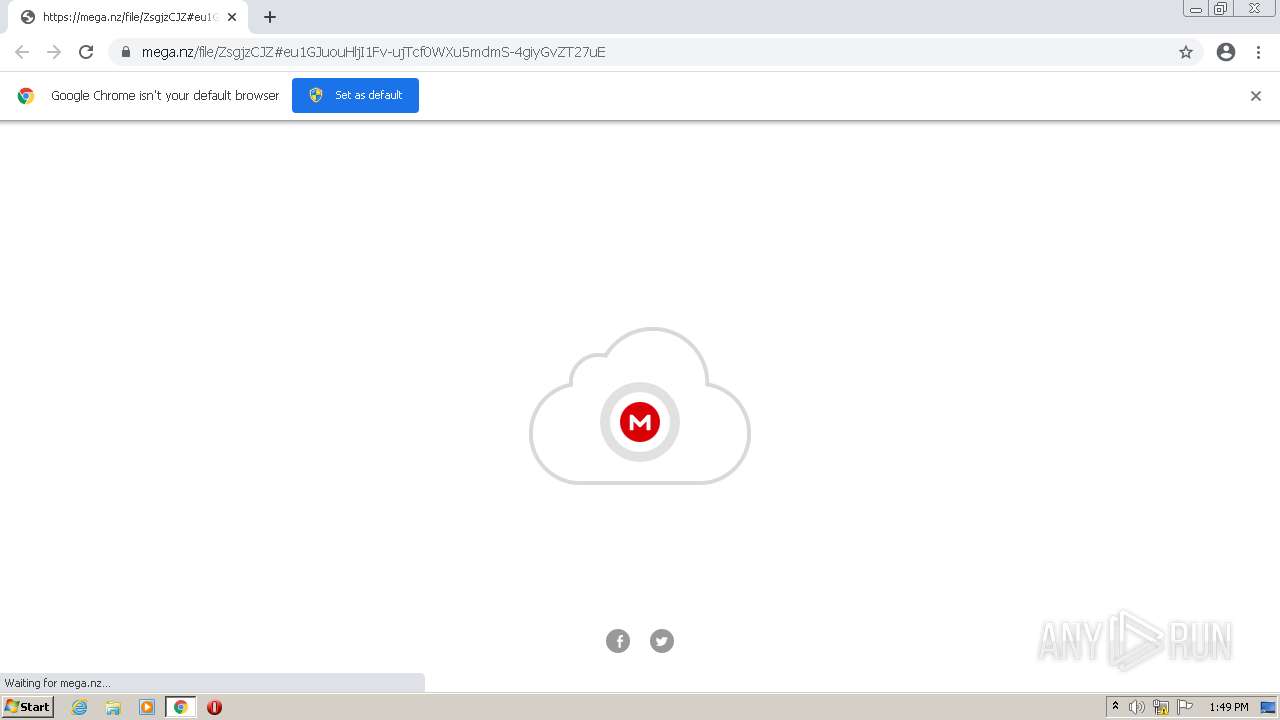
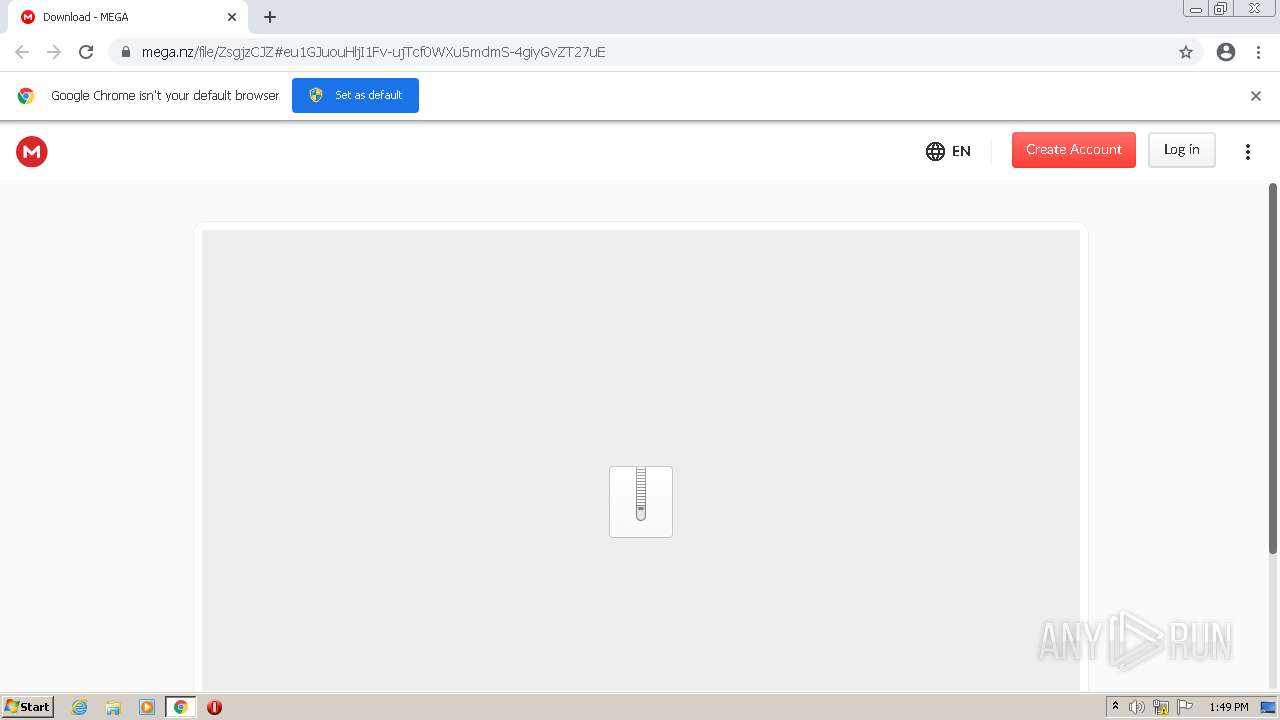
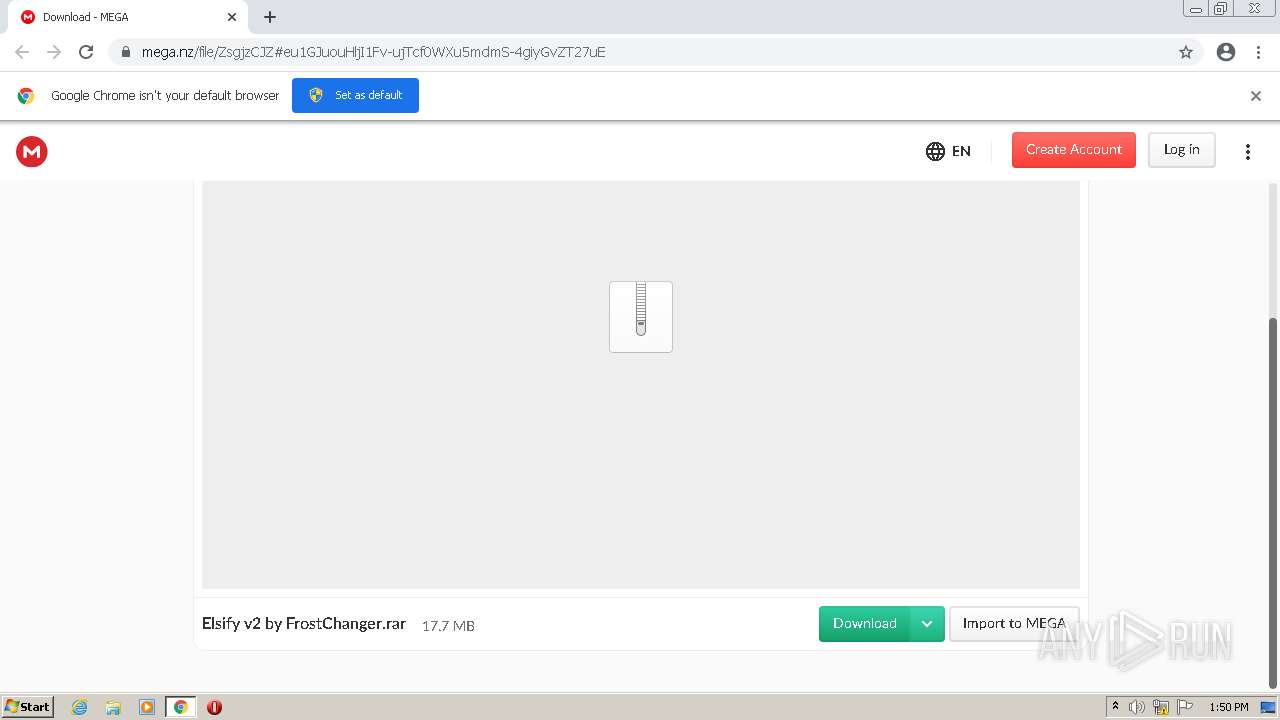
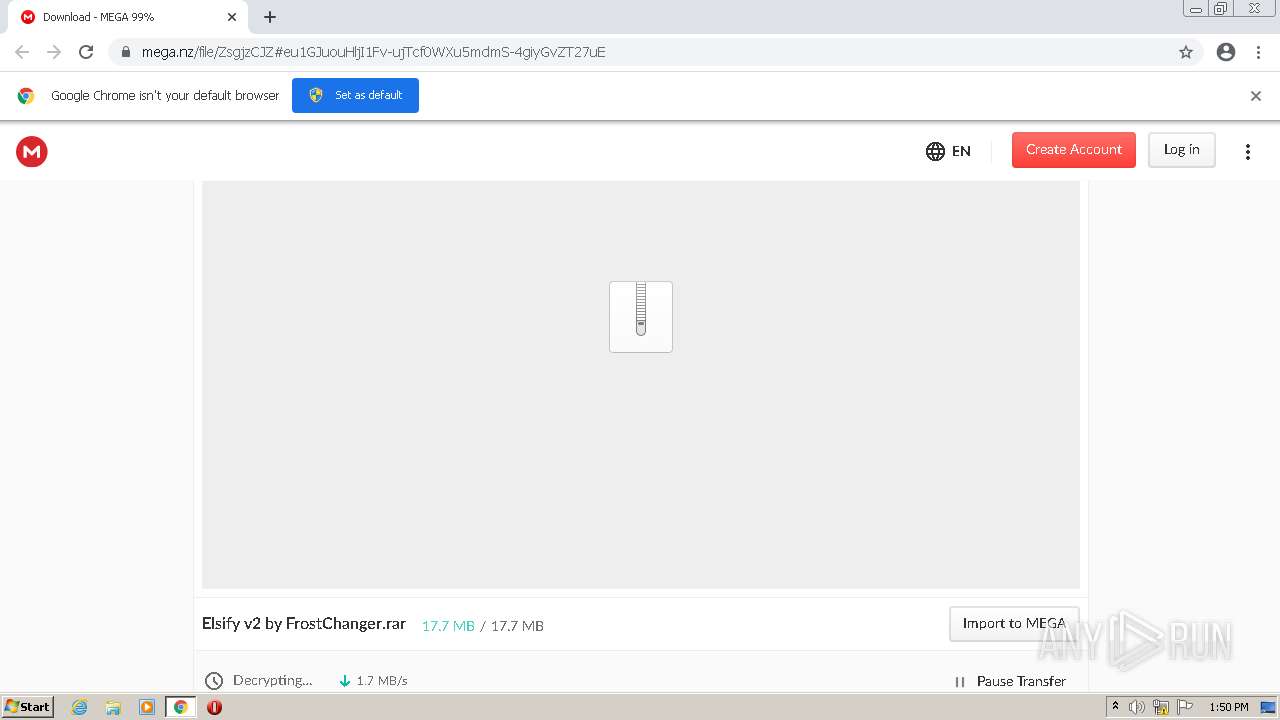
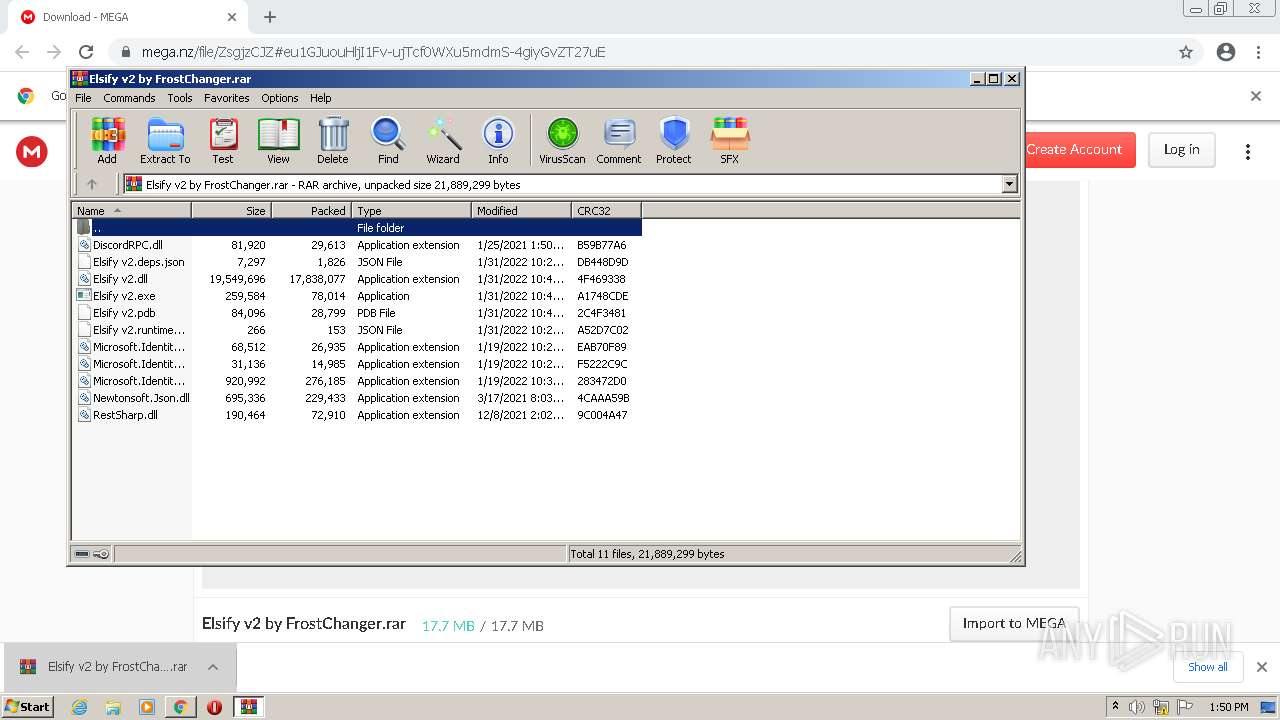
| URL: | https://mega.nz/file/ZsgjzCJZ#eu1GJuouHljI1Fv-ujTcf0WXu5mdmS-4giyGvZT27uE |
| Full analysis: | https://app.any.run/tasks/e1eacd6d-814b-47da-bb3d-0990f2fe05b3 |
| Verdict: | Malicious activity |
| Analysis date: | February 12, 2022, 13:49:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B8AF21C7BCC4065DF78AB4F1B54B78D7 |
| SHA1: | E094C2991BB5A89EF7B45CD85D01639B67CDA61E |
| SHA256: | FDA1FA6E909E83606AA4DC1DCE17F47662816DD9B4C70C2B72681E2F6D351893 |
| SSDEEP: | 3:N8X/iuOG9IL5j5PAJyyd+Oidg:25IL5j5qZx |
MALICIOUS
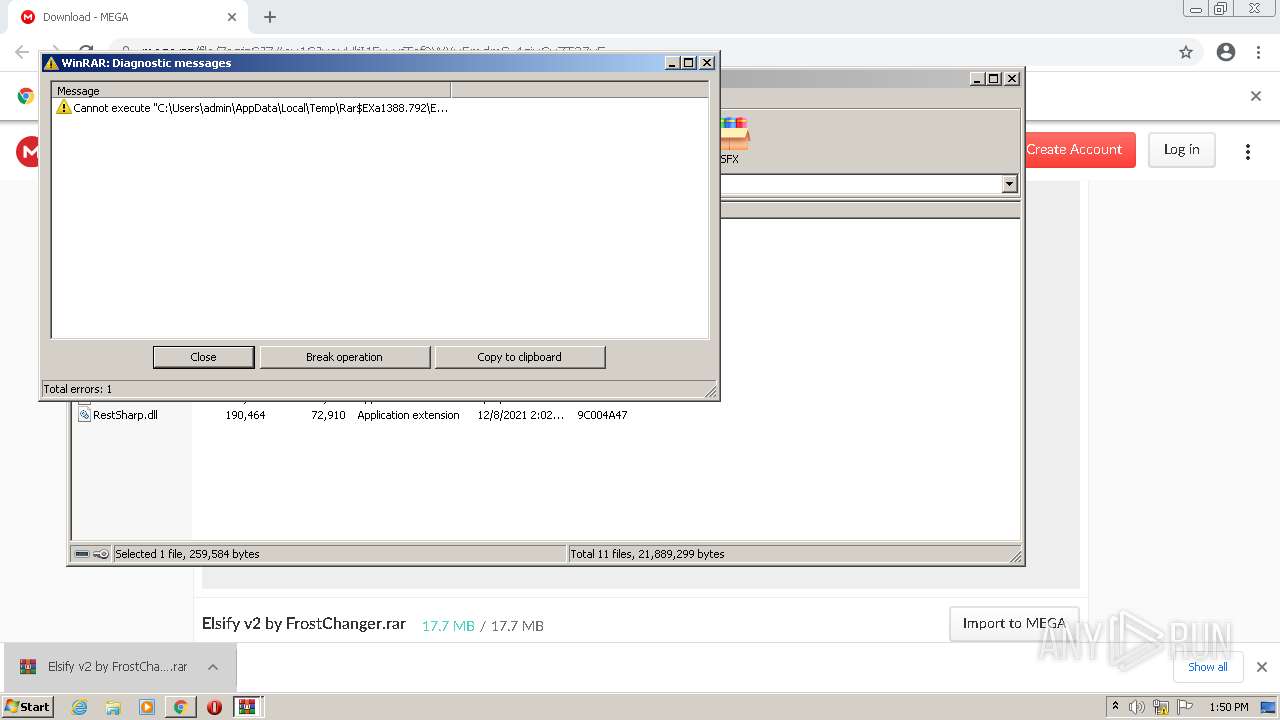
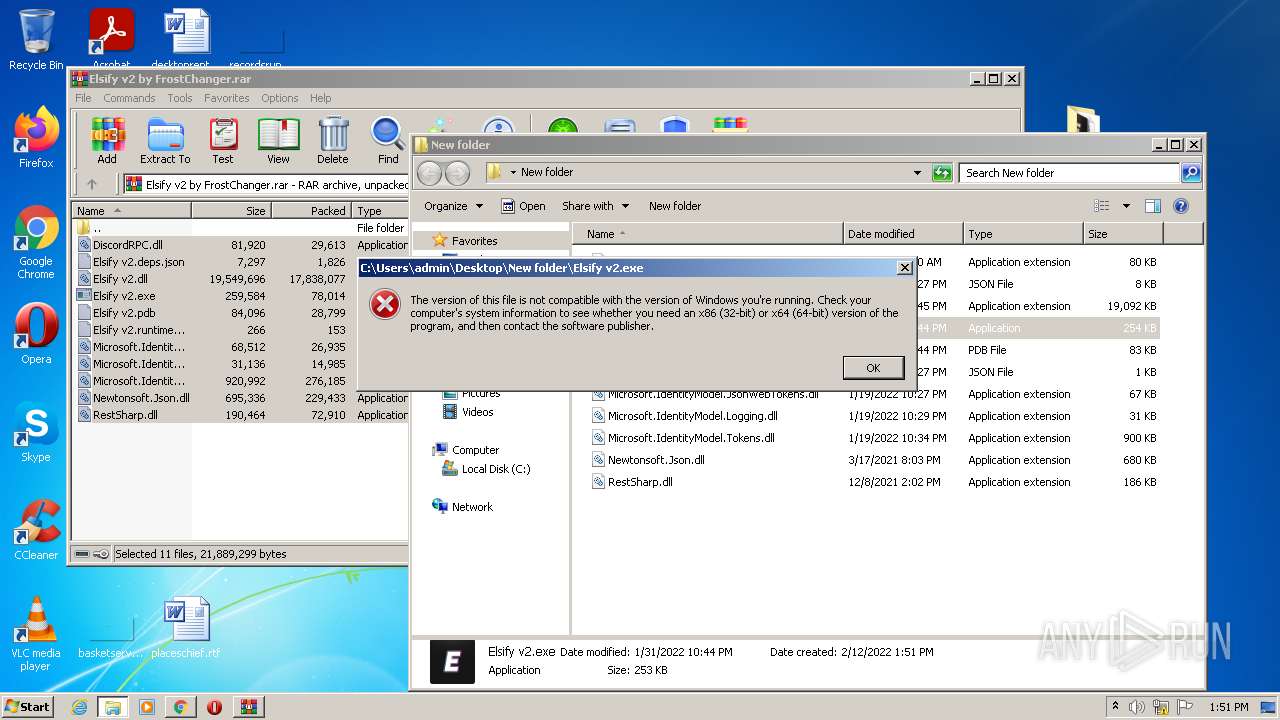
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3704)
SUSPICIOUS
Reads Microsoft Outlook installation path
- chrome.exe (PID: 2056)
Checks supported languages
- WinRAR.exe (PID: 1388)
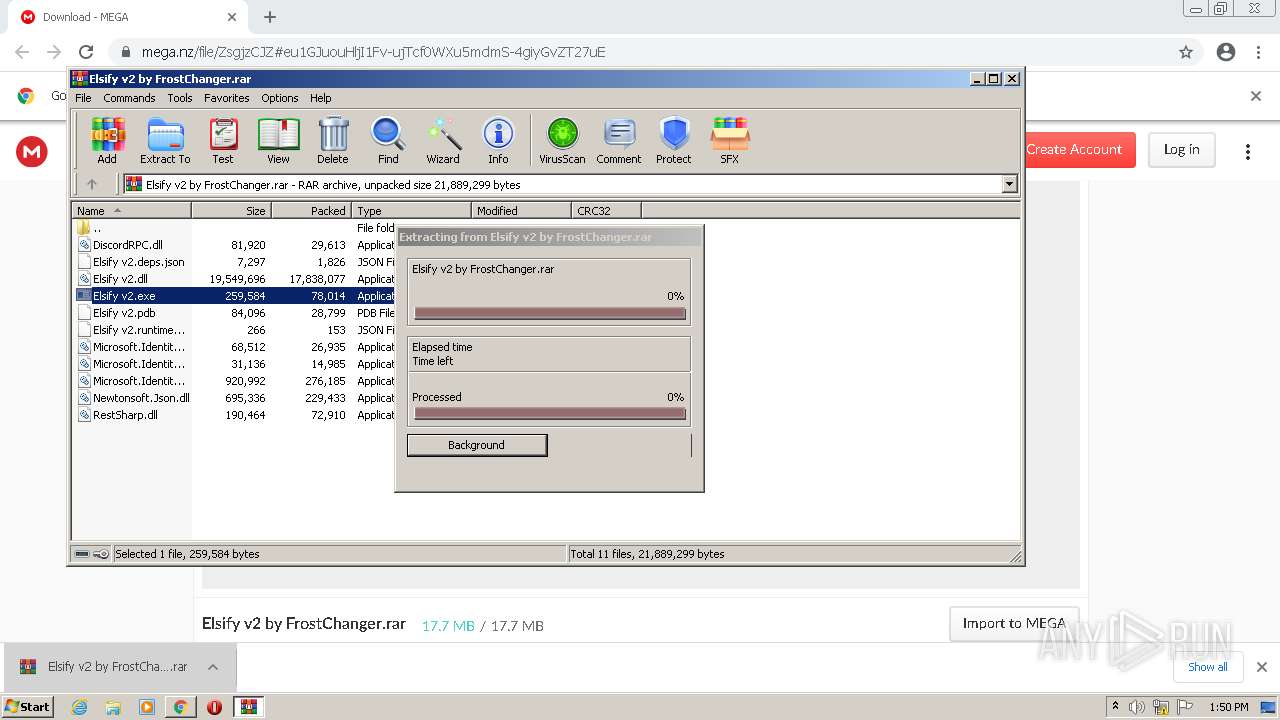
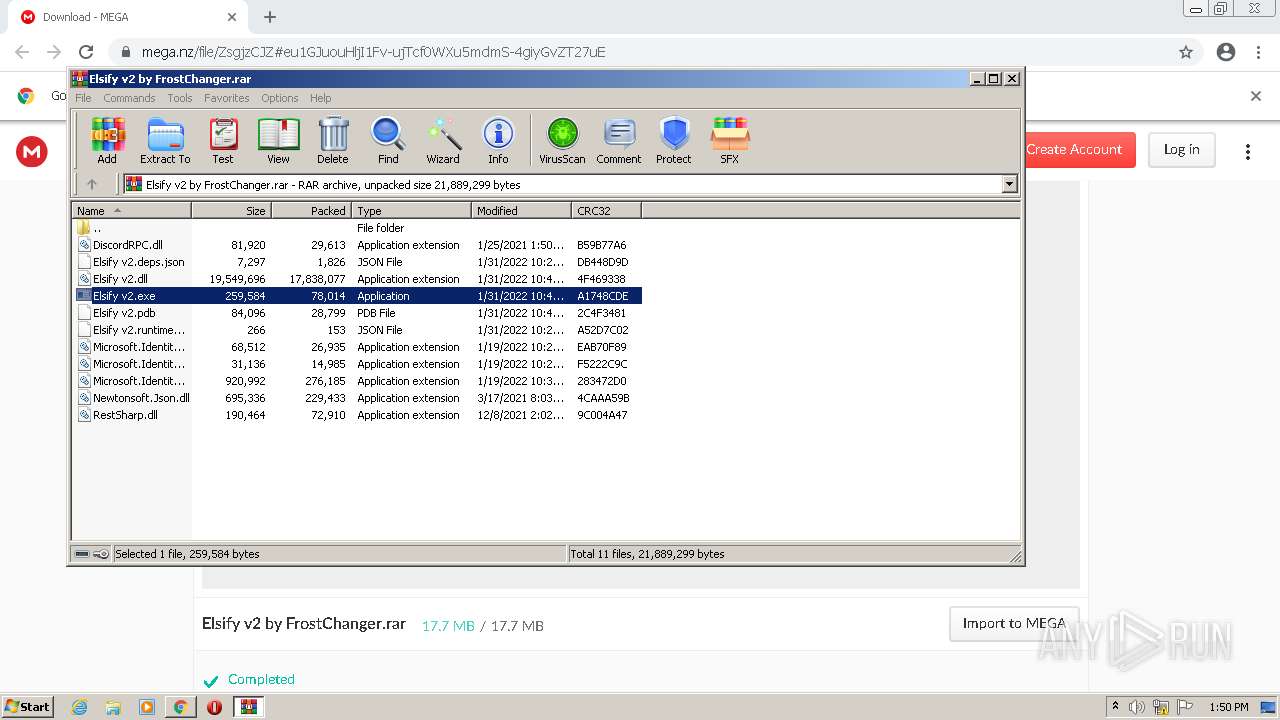
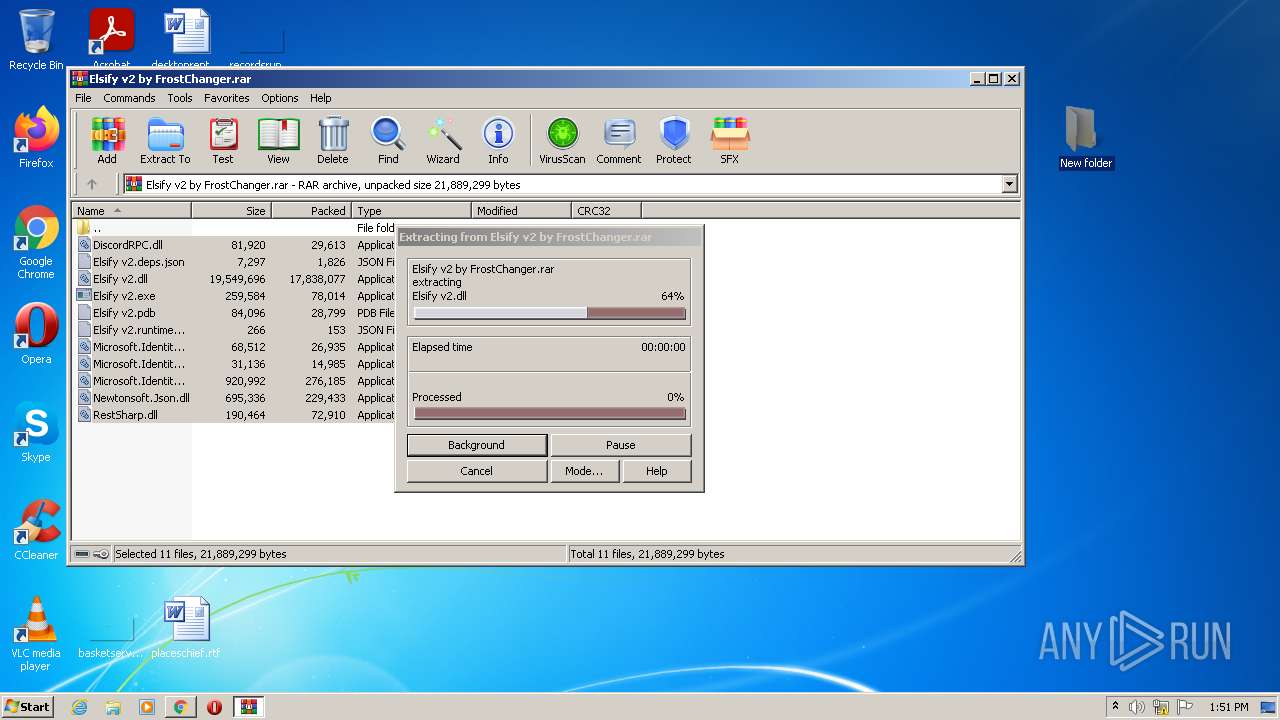
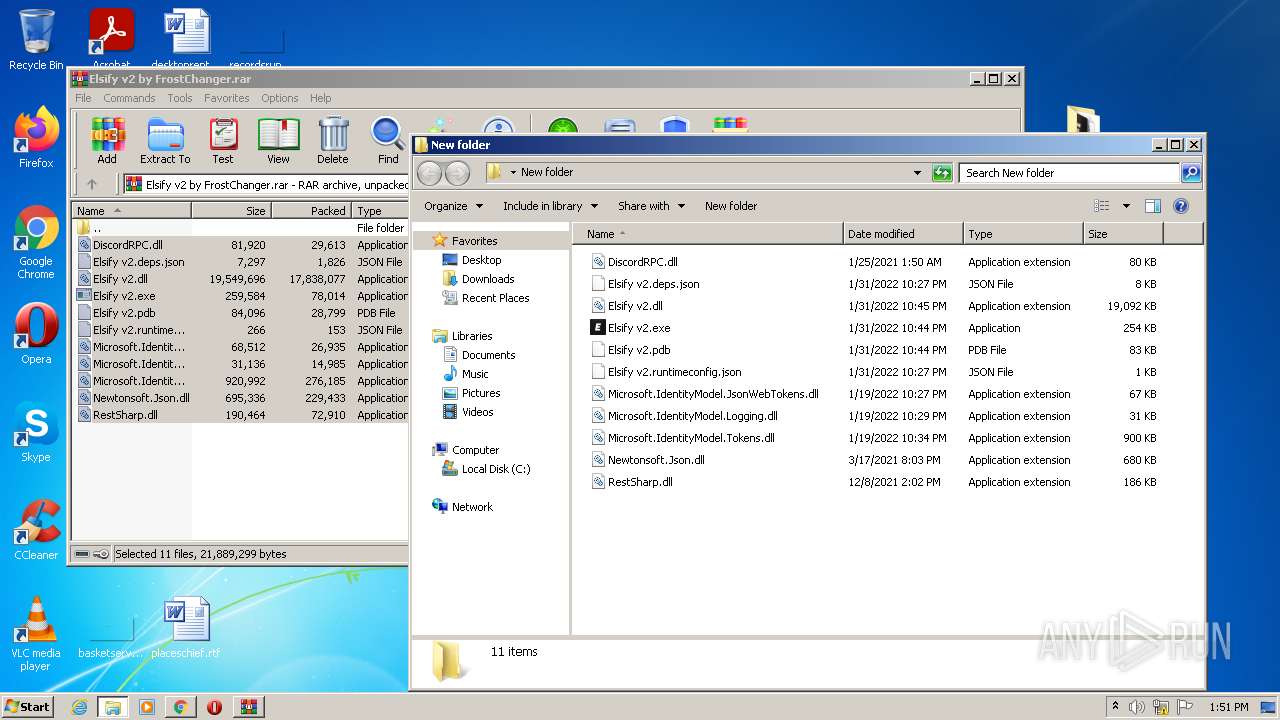
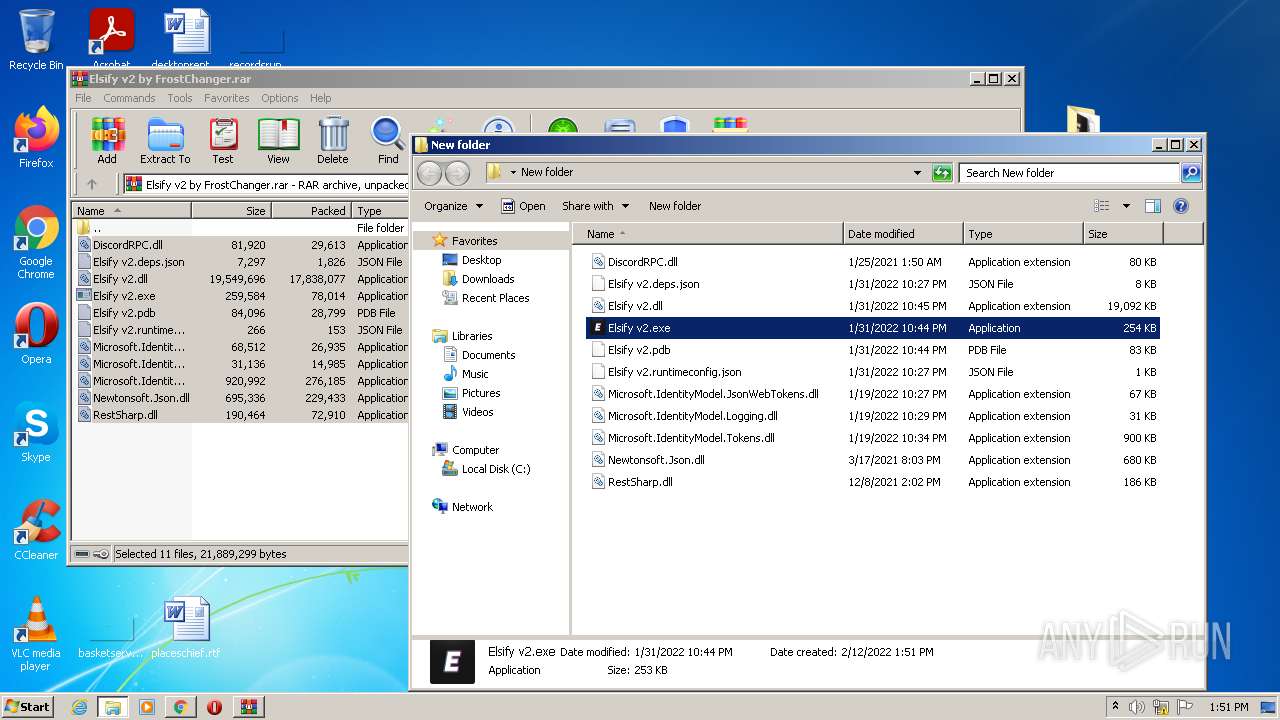
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1388)
Reads the computer name
- WinRAR.exe (PID: 1388)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 1388)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 1388)
INFO
Checks supported languages
- chrome.exe (PID: 3368)
- chrome.exe (PID: 3572)
- chrome.exe (PID: 1596)
- chrome.exe (PID: 4056)
- chrome.exe (PID: 2768)
- chrome.exe (PID: 960)
- chrome.exe (PID: 1996)
- chrome.exe (PID: 3428)
- chrome.exe (PID: 3480)
- chrome.exe (PID: 2840)
- chrome.exe (PID: 2052)
- chrome.exe (PID: 2056)
- chrome.exe (PID: 1784)
- chrome.exe (PID: 2380)
- chrome.exe (PID: 960)
- chrome.exe (PID: 3732)
- chrome.exe (PID: 3172)
- chrome.exe (PID: 1004)
- chrome.exe (PID: 2848)
- chrome.exe (PID: 3576)
- chrome.exe (PID: 2576)
- chrome.exe (PID: 572)
- chrome.exe (PID: 2816)
- chrome.exe (PID: 3380)
- chrome.exe (PID: 2272)
- chrome.exe (PID: 3676)
Reads the computer name
- chrome.exe (PID: 3368)
- chrome.exe (PID: 1596)
- chrome.exe (PID: 4056)
- chrome.exe (PID: 3428)
- chrome.exe (PID: 3480)
- chrome.exe (PID: 2840)
- chrome.exe (PID: 2052)
- chrome.exe (PID: 1784)
- chrome.exe (PID: 2380)
- chrome.exe (PID: 2056)
- chrome.exe (PID: 3732)
Reads the hosts file
- chrome.exe (PID: 3368)
- chrome.exe (PID: 4056)
Application launched itself
- chrome.exe (PID: 3368)
Reads settings of System Certificates
- chrome.exe (PID: 4056)
Reads the date of Windows installation
- chrome.exe (PID: 2380)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
63
Monitored processes
28
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1012,2493759154618157988,9177342896924768705,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1784 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,2493759154618157988,9177342896924768705,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2168 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --field-trial-handle=1012,2493759154618157988,9177342896924768705,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=980 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1012,2493759154618157988,9177342896924768705,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3108 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
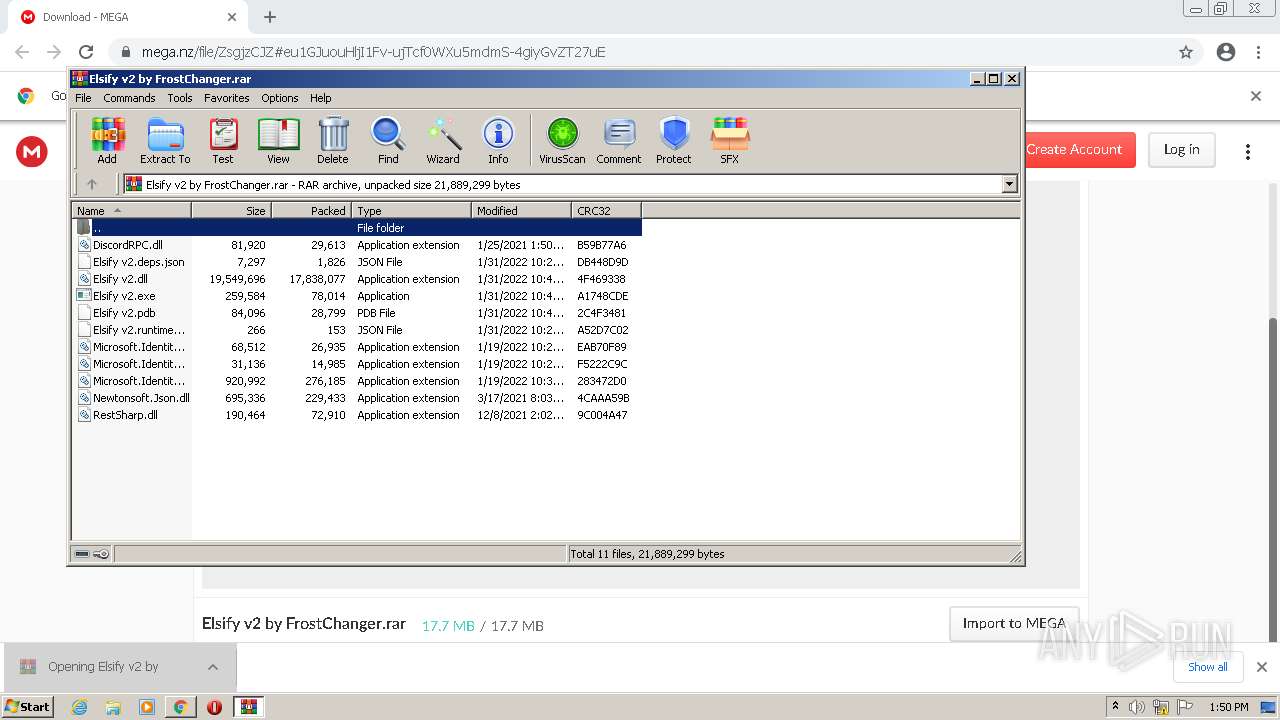
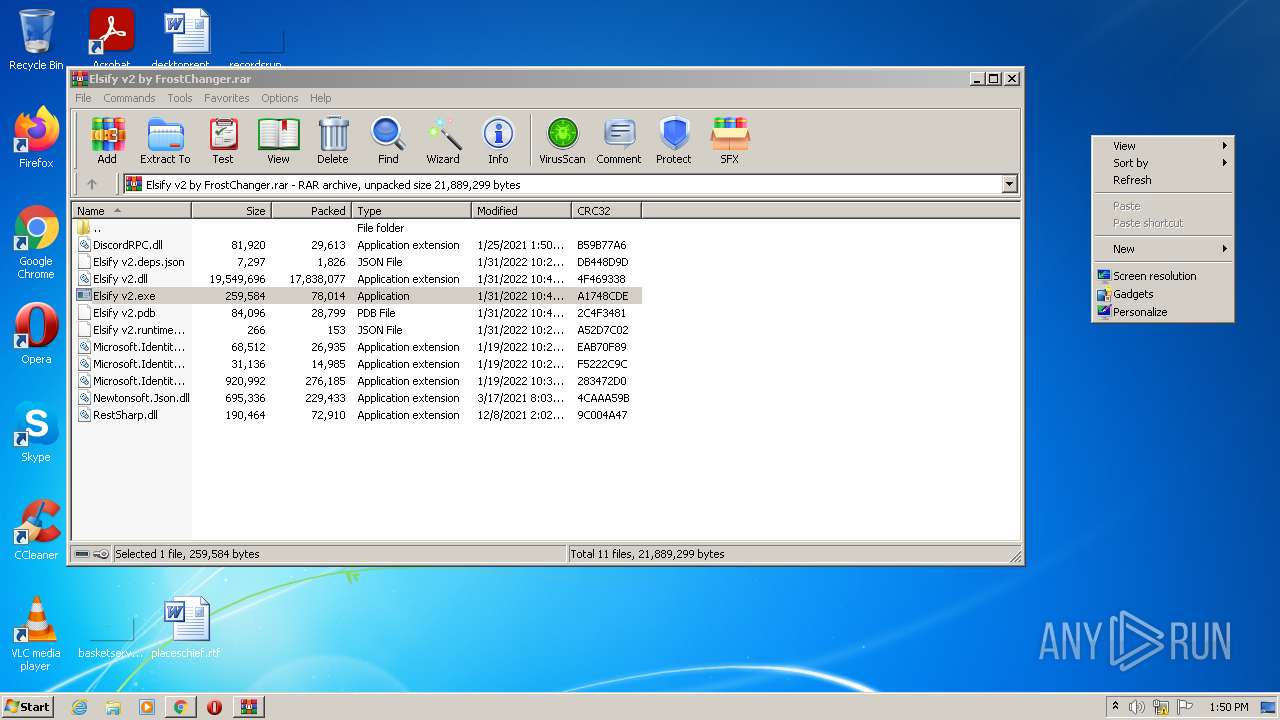
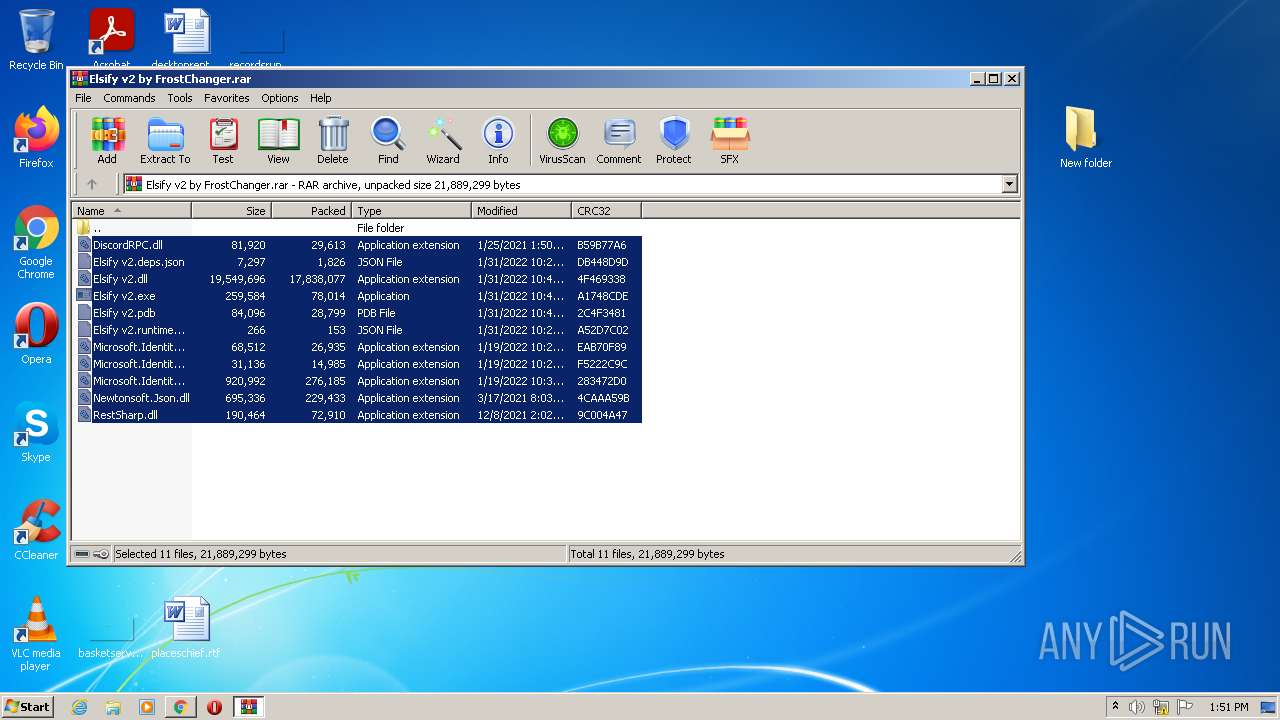
| 1388 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Elsify v2 by FrostChanger.rar" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | |
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 | ||||
| 1596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,2493759154618157988,9177342896924768705,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1048 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1012,2493759154618157988,9177342896924768705,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1660 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,2493759154618157988,9177342896924768705,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1856 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 2052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1012,2493759154618157988,9177342896924768705,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2348 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1012,2493759154618157988,9177342896924768705,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3168 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
16
Suspicious files
52
Text files
125
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6207BAFD-D28.pma | — | |
MD5:— | SHA256:— | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d9d7603d-81ee-4817-9d2a-86408e933677.tmp | text | |
MD5:31CAE9271B02BDA030637FAABB671D24 | SHA256:DB29F9B6DB3484C10EDD7BC730114CFC845BDDA4BC0974FCF55206680DEE9B47 | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:31CAE9271B02BDA030637FAABB671D24 | SHA256:DB29F9B6DB3484C10EDD7BC730114CFC845BDDA4BC0974FCF55206680DEE9B47 | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF114f46.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF114f65.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ddc10d4b-e8ec-4b6b-b4ea-963124676ee7.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:CDB4EE2AEA69CC6A83331BBE96DC2CAA9A299D21329EFB0336FC02A82E1839A8 | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF114f36.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 3572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
31
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
876 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acgds5evoc6kswf25gqqstds37sq_2022.2.6.1202/ggkkehgbnfjpeggfpleeakpidbkibbmn_2022.2.6.1202_all_mjvc6ylu63z5m7tztmh5pkul3q.crx3 | US | crx | 36.7 Kb | whitelisted |
876 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acgds5evoc6kswf25gqqstds37sq_2022.2.6.1202/ggkkehgbnfjpeggfpleeakpidbkibbmn_2022.2.6.1202_all_mjvc6ylu63z5m7tztmh5pkul3q.crx3 | US | crx | 9.51 Kb | whitelisted |
876 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx | US | crx | 9.51 Kb | whitelisted |
876 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | — | — | whitelisted |
876 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 5.64 Kb | whitelisted |
876 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 9.70 Kb | whitelisted |
876 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 9.70 Kb | whitelisted |
876 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 20.9 Kb | whitelisted |
876 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | vc | 9.70 Kb | whitelisted |
876 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 88.5 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4056 | chrome.exe | 216.58.212.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
4056 | chrome.exe | 142.250.185.173:443 | accounts.google.com | Google Inc. | US | suspicious |
4056 | chrome.exe | 142.250.185.138:443 | content-autofill.googleapis.com | Google Inc. | US | whitelisted |
4056 | chrome.exe | 31.216.145.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | malicious |
4056 | chrome.exe | 66.203.124.37:443 | eu.static.mega.co.nz | RealNetworks, Inc. | US | suspicious |
4056 | chrome.exe | 66.203.125.14:443 | g.api.mega.co.nz | RealNetworks, Inc. | US | unknown |
4056 | chrome.exe | 142.250.186.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
4056 | chrome.exe | 142.250.186.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
4056 | chrome.exe | 162.208.16.30:443 | gfs302n120.userstorage.mega.co.nz | Tellarc LLC | US | unknown |
4056 | chrome.exe | 31.216.144.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
mega.nz |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
eu.static.mega.co.nz |
| shared |
g.api.mega.co.nz |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
gfs302n120.userstorage.mega.co.nz |
| unknown |
sb-ssl.google.com |
| whitelisted |