| download: | upd365_58v01.exe |
| Full analysis: | https://app.any.run/tasks/17703a67-bff1-4768-ace6-cfe3e0dde829 |
| Verdict: | Malicious activity |
| Analysis date: | July 16, 2019, 22:50:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 779E3C94AF16C4FBAB6C0BD41849FC35 |
| SHA1: | D9911773A13093AFFEEA77914C0404B759BCDC31 |
| SHA256: | FD97342E1968AED9D8F50468D3B7B7868981D9D360B2F049B6706E72D8184E3F |
| SSDEEP: | 6144:fdTMq0StmGrejiOCs+XH/cxpO4/tJyTqZmAXS+hn145AGp+SiRvWDlu2:hMdSQWsAUxXYqZmD+hn1UAtSRDc |
MALICIOUS
Disables Windows Defender
- HSYАТЧЧЫЭУ.exe (PID: 3252)
- HUYАТЧЧЫЭУ.exe (PID: 3524)
Executes PowerShell scripts
- cmd.exe (PID: 3512)
- cmd.exe (PID: 2192)
- cmd.exe (PID: 1960)
- cmd.exe (PID: 3044)
- cmd.exe (PID: 3776)
- cmd.exe (PID: 1360)
- cmd.exe (PID: 3532)
- cmd.exe (PID: 1876)
- cmd.exe (PID: 3168)
- cmd.exe (PID: 640)
- cmd.exe (PID: 1728)
- cmd.exe (PID: 2724)
- cmd.exe (PID: 3792)
- cmd.exe (PID: 2820)
- cmd.exe (PID: 2976)
- cmd.exe (PID: 700)
- cmd.exe (PID: 4092)
- cmd.exe (PID: 3440)
- cmd.exe (PID: 3324)
- cmd.exe (PID: 940)
Known privilege escalation attack
- DllHost.exe (PID: 1496)
Stops/Deletes Windows Defender service via SC.exe
- cmd.exe (PID: 2220)
- cmd.exe (PID: 3884)
- cmd.exe (PID: 2944)
- cmd.exe (PID: 4056)
Loads the Task Scheduler COM API
- HSYАТЧЧЫЭУ.exe (PID: 3252)
- HUYАТЧЧЫЭУ.exe (PID: 3524)
SUSPICIOUS
Executable content was dropped or overwritten
- upd365_58v01.exe (PID: 3788)
- HSYАТЧЧЫЭУ.exe (PID: 3252)
Creates files in the program directory
- upd365_58v01.exe (PID: 3788)
- HUYАТЧЧЫЭУ.exe (PID: 3524)
Executed via COM
- DllHost.exe (PID: 1496)
Starts CMD.EXE for commands execution
- HSYАТЧЧЫЭУ.exe (PID: 3252)
- HUYАТЧЧЫЭУ.exe (PID: 3524)
Creates files in the user directory
- powershell.exe (PID: 3332)
- powershell.exe (PID: 2652)
- powershell.exe (PID: 1188)
- powershell.exe (PID: 3176)
- powershell.exe (PID: 1744)
- powershell.exe (PID: 3728)
- powershell.exe (PID: 2504)
- powershell.exe (PID: 3256)
- powershell.exe (PID: 1708)
- HSYАТЧЧЫЭУ.exe (PID: 3252)
- powershell.exe (PID: 3508)
- HUYАТЧЧЫЭУ.exe (PID: 3524)
Executed via Task Scheduler
- HUYАТЧЧЫЭУ.exe (PID: 3524)
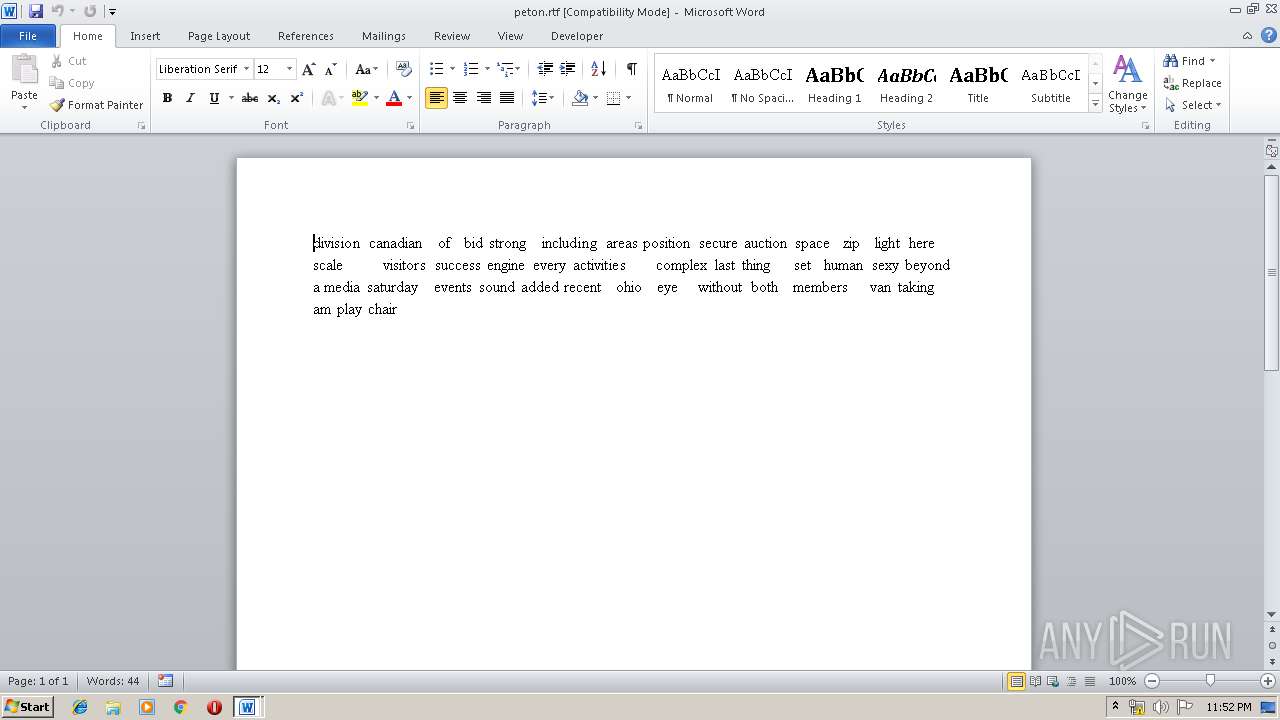
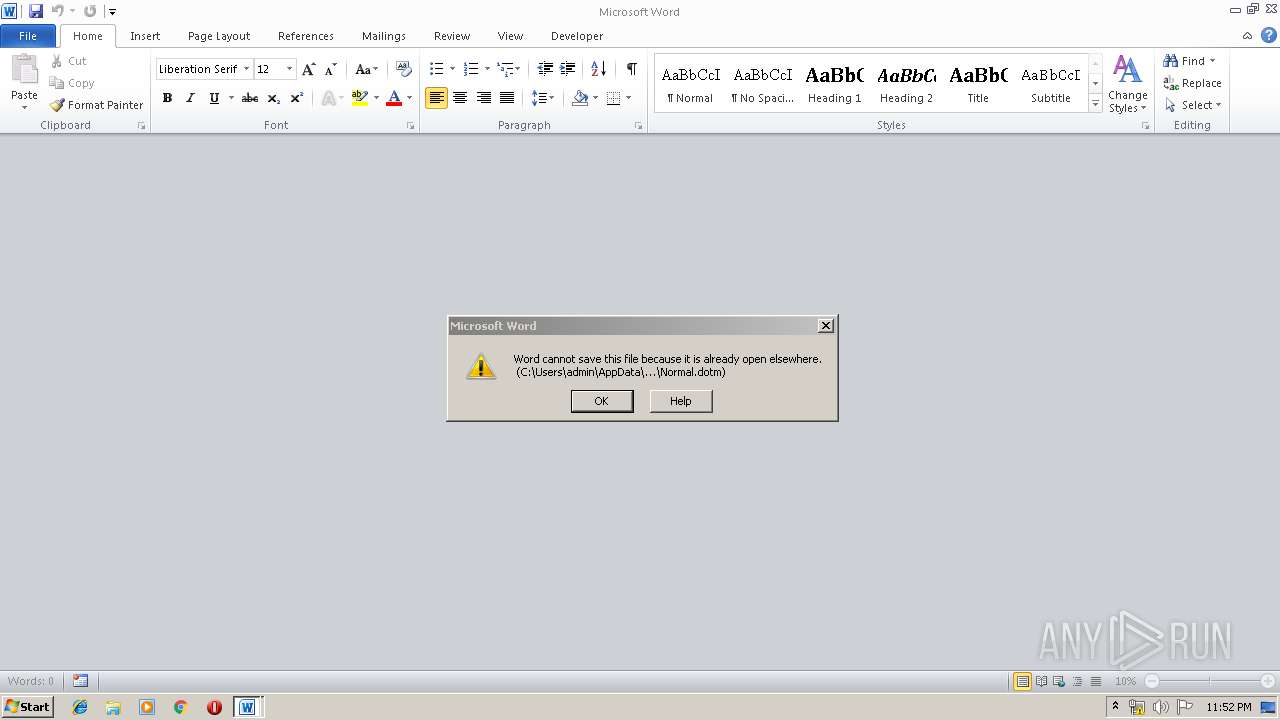
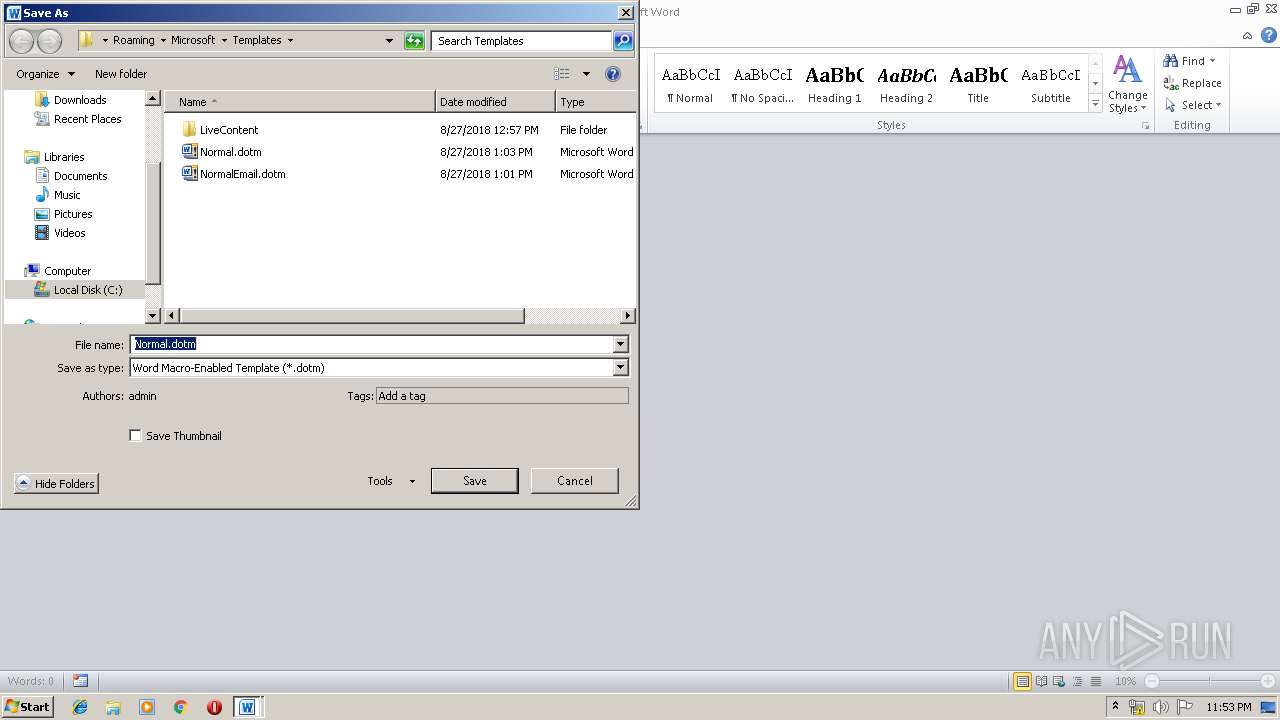
INFO
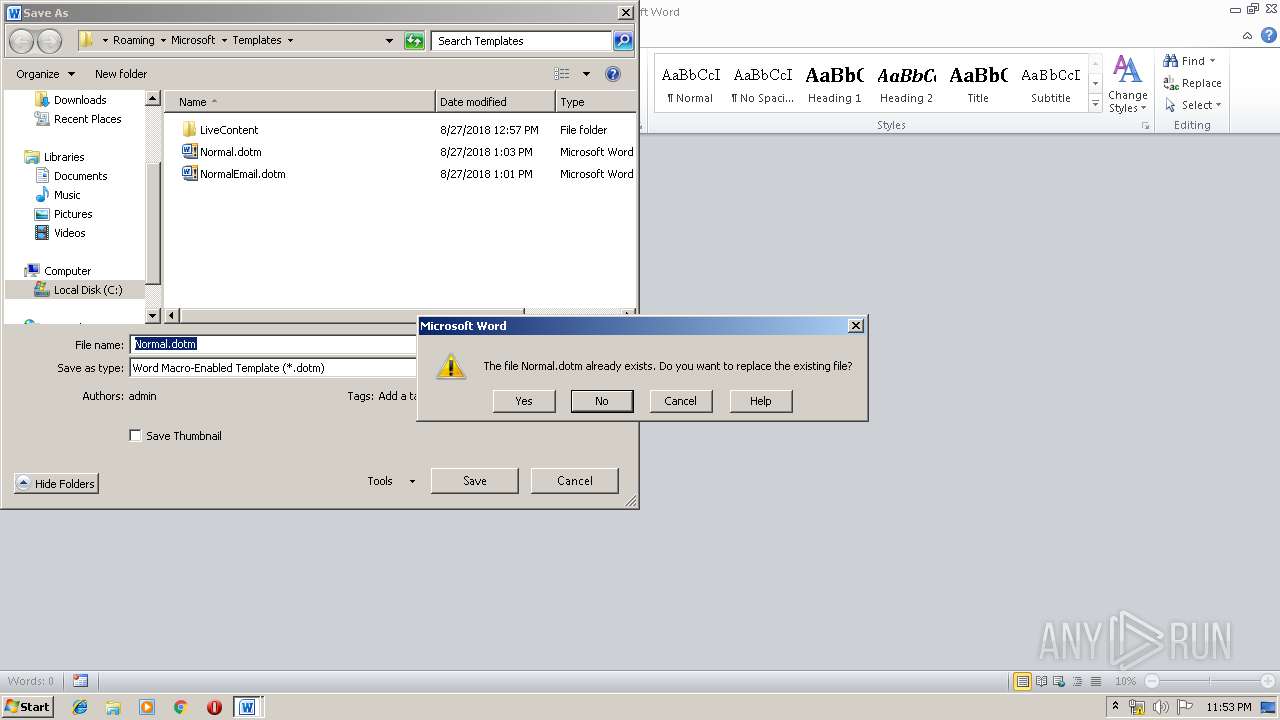
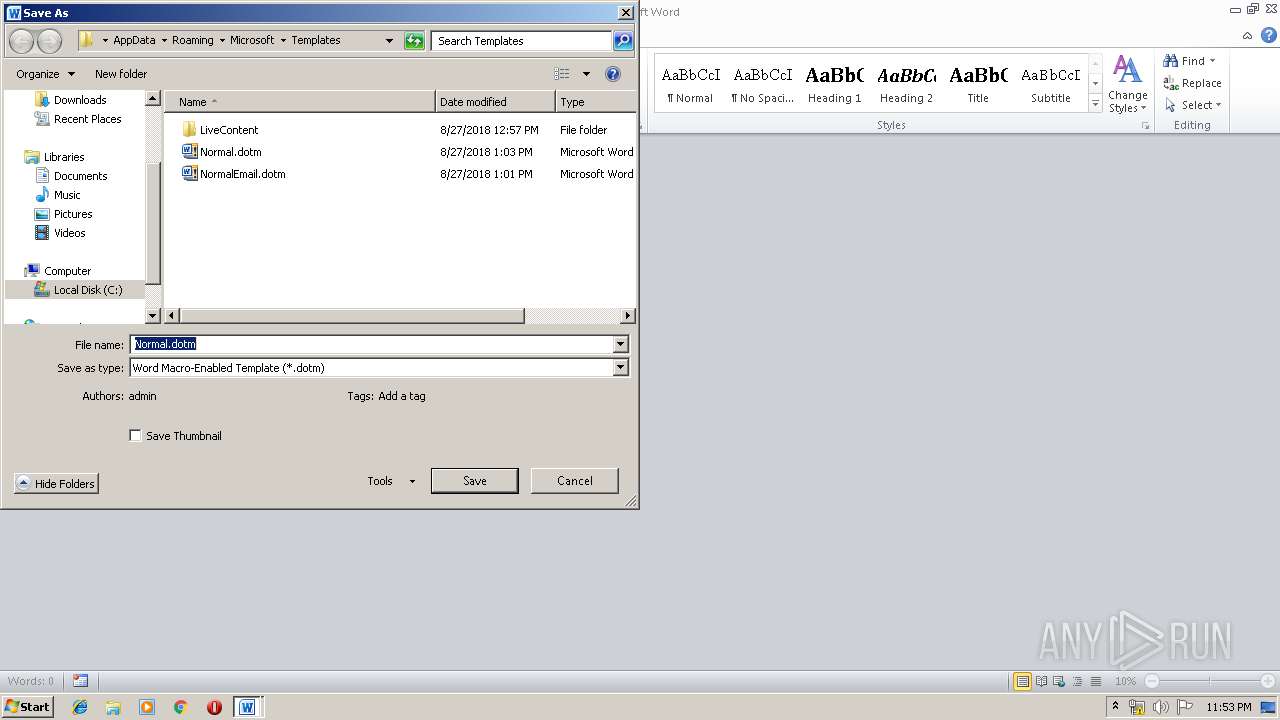
Creates files in the user directory
- WINWORD.EXE (PID: 1756)
- WINWORD.EXE (PID: 2260)
- WINWORD.EXE (PID: 3120)
Manual execution by user
- WINWORD.EXE (PID: 1756)
- WINWORD.EXE (PID: 2260)
- WINWORD.EXE (PID: 3120)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3120)
- WINWORD.EXE (PID: 2260)
- WINWORD.EXE (PID: 1756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (35.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (27) |
| .exe | | | Win64 Executable (generic) (23.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:16 14:08:14+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 89088 |
| InitializedDataSize: | 256512 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc7f5 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Jul-2019 12:08:14 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 16-Jul-2019 12:08:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00015A3E | 0x00015C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.5257 |
.rdata | 0x00017000 | 0x00004DB8 | 0x00004E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.77458 |
.data | 0x0001C000 | 0x00001E18 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.62202 |
.rsrc | 0x0001E000 | 0x000388FC | 0x00038A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.08268 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.79597 | 346 | Latin 1 / Western European | English - United States | RT_MANIFEST |
7 | 2.47148 | 96 | Latin 1 / Western European | English - United States | RT_STRING |
101 | 3.05449 | 794 | Latin 1 / Western European | English - United States | RT_DIALOG |
103 | 3.47351 | 686 | Latin 1 / Western European | English - United States | RT_DIALOG |
109 | 1.79879 | 16 | Latin 1 / Western European | English - United States | RT_ACCELERATOR |
111 | 5.99991 | 226648 | Latin 1 / Western European | English - United States | GOOLES |
132 | 1.81924 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
2049 | 1.91282 | 68 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
Total processes
121
Monitored processes
56
Malicious processes
23
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | powershell Set-MpPreference -DisableIntrusionPreventionSystem $true | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 308 | powershell Set-MpPreference -DisableBlockAtFirstSeen $true | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 580 | powershell Set-MpPreference -DisableScriptScanning $true | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 640 | "C:\Windows\System32\cmd.exe" /c powershell Set-MpPreference -DisableScriptScanning $true | C:\Windows\System32\cmd.exe | — | HSYАТЧЧЫЭУ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 700 | "C:\Windows\System32\cmd.exe" /c powershell Set-MpPreference -SevereThreatDefaultAction 6 | C:\Windows\System32\cmd.exe | — | HUYАТЧЧЫЭУ.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 940 | "C:\Windows\System32\cmd.exe" /c powershell Set-MpPreference -ModerateThreatDefaultAction 6 | C:\Windows\System32\cmd.exe | — | HUYАТЧЧЫЭУ.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1188 | powershell Set-MpPreference -DisableIOAVProtection $true | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1360 | "C:\Windows\System32\cmd.exe" /c powershell Set-MpPreference -DisableIntrusionPreventionSystem $true | C:\Windows\System32\cmd.exe | — | HSYАТЧЧЫЭУ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1496 | C:\Windows\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1504 | sc delete WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 137
Read events
4 447
Write events
1 660
Delete events
30
Modification events
| (PID) Process: | (3788) upd365_58v01.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3788) upd365_58v01.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3252) HSYАТЧЧЫЭУ.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (3252) HSYАТЧЧЫЭУ.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-time Protection |
| Operation: | write | Name: | DisableBehaviorMonitoring |
Value: 1 | |||
| (PID) Process: | (3252) HSYАТЧЧЫЭУ.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-time Protection |
| Operation: | write | Name: | DisableOnAccessProtection |
Value: 1 | |||
| (PID) Process: | (3252) HSYАТЧЧЫЭУ.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-time Protection |
| Operation: | write | Name: | DisableScanOnRealtimeEnable |
Value: 1 | |||
| (PID) Process: | (3252) HSYАТЧЧЫЭУ.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-time Protection |
| Operation: | write | Name: | DisableIOAVProtection |
Value: 1 | |||
| (PID) Process: | (3252) HSYАТЧЧЫЭУ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3252) HSYАТЧЧЫЭУ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1496) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
19
Text files
9
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3332 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4FNFWXLBZATDGORI9G14.temp | — | |
MD5:— | SHA256:— | |||
| 2652 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\H0K0VPRRD05QWG2K9JH9.temp | — | |
MD5:— | SHA256:— | |||
| 3508 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\NMZHZGYWODJT1LQ07WUE.temp | — | |
MD5:— | SHA256:— | |||
| 1188 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\KBA2UAAQGGO4N04H8UMH.temp | — | |
MD5:— | SHA256:— | |||
| 3728 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\IOZL6M3O3NK3EGD8F8BB.temp | — | |
MD5:— | SHA256:— | |||
| 2504 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\O0QRMS6WHOOGOZWFYDZT.temp | — | |
MD5:— | SHA256:— | |||
| 3256 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\5QJ2R3K7430W6XG2KO7C.temp | — | |
MD5:— | SHA256:— | |||
| 1744 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2H12OKC1AFAC3RIRC2MU.temp | — | |
MD5:— | SHA256:— | |||
| 3176 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\Q786IEBKSZBOG3YNK07A.temp | — | |
MD5:— | SHA256:— | |||
| 1708 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\MW1A8I5HMWGDAQ0S8BHZ.temp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3524 | HUYАТЧЧЫЭУ.exe | 92.38.171.12:443 | — | JSC Digital Network | RU | suspicious |