| download: | ogx7vtz2tr4j_8g5j473-096029329350379 |
| Full analysis: | https://app.any.run/tasks/618daae0-3673-4956-9ad5-76f395ae7652 |
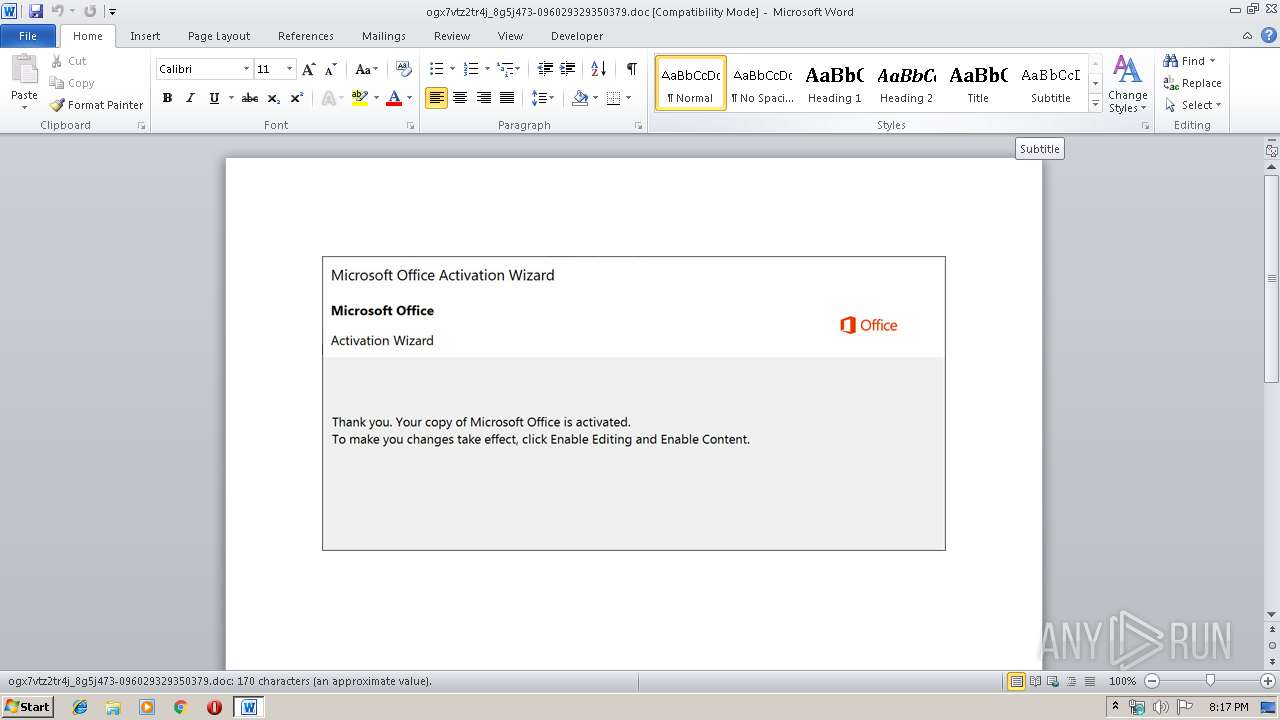
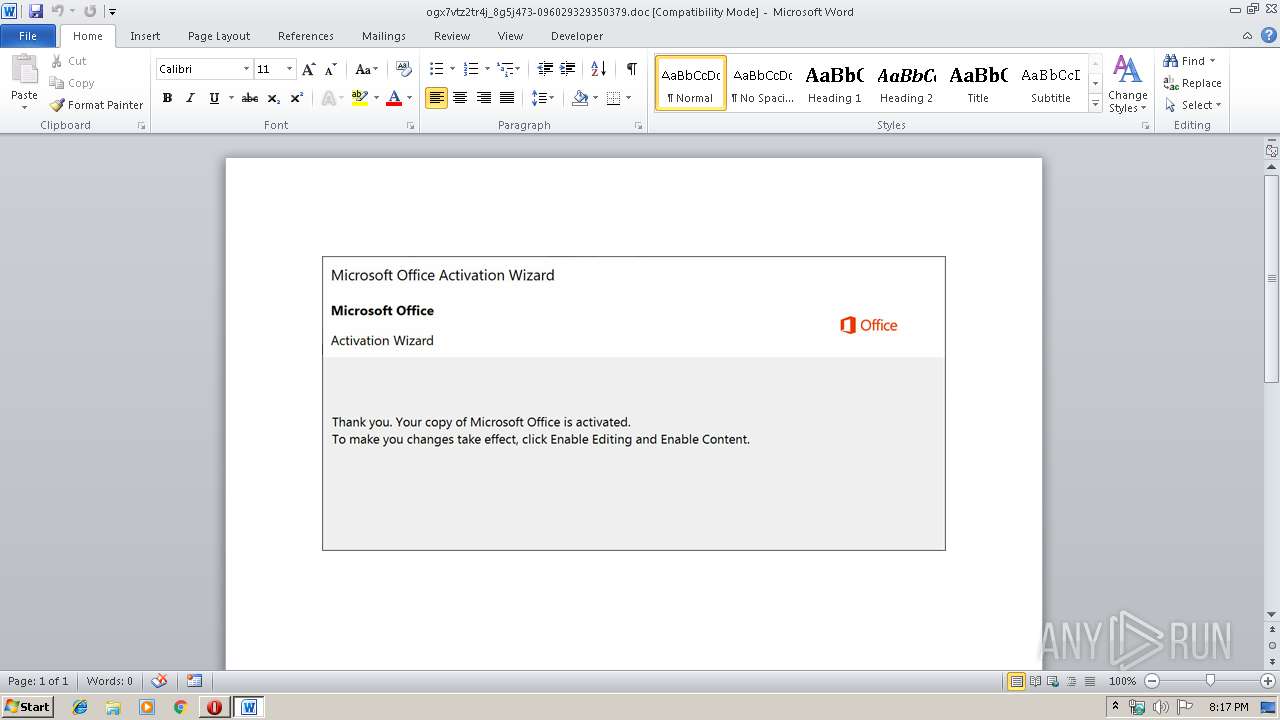
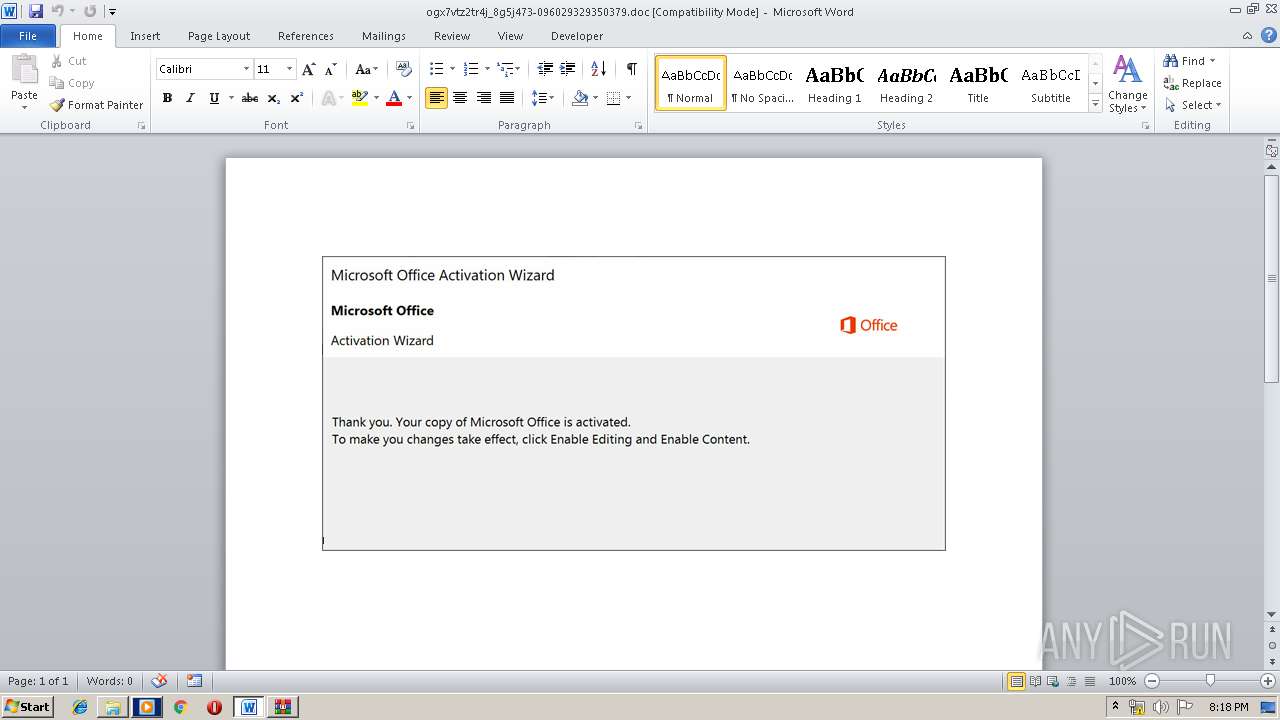
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 09, 2019, 19:16:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Australian Dollar, Subject: Rubber, Author: Thalia Romaguera, Keywords: Bedfordshire, Comments: visionary, Template: Normal.dotm, Last Saved By: Nona Tremblay, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Oct 9 17:49:00 2019, Last Saved Time/Date: Wed Oct 9 17:49:00 2019, Number of Pages: 1, Number of Words: 30, Number of Characters: 176, Security: 0 |
| MD5: | 9513B1D4CC78349DAD3C20151118EAFF |
| SHA1: | 7B63D465E84D2A4961E69C69464B807500C9AEEB |
| SHA256: | FD8C3FCF8CA04DDD17F6FB7F7A6463912E6F33BFAF27E765188887FDE52686F0 |
| SSDEEP: | 6144:mRIR/1OyR5Iocj3x/iEm/6/iIJ8MiRdZZb3tpTkPSP/bd8bijiH8pk4FiLW46di1:mRIR/1OyR5Iocj3x/iEm/6/iIJ8MiRdg |
MALICIOUS
Application was dropped or rewritten from another process
- 249.exe (PID: 3664)
- 249.exe (PID: 2472)
- msptermsizes.exe (PID: 2380)
- msptermsizes.exe (PID: 920)
Emotet process was detected
- 249.exe (PID: 2472)
EMOTET was detected
- msptermsizes.exe (PID: 920)
Connects to CnC server
- msptermsizes.exe (PID: 920)
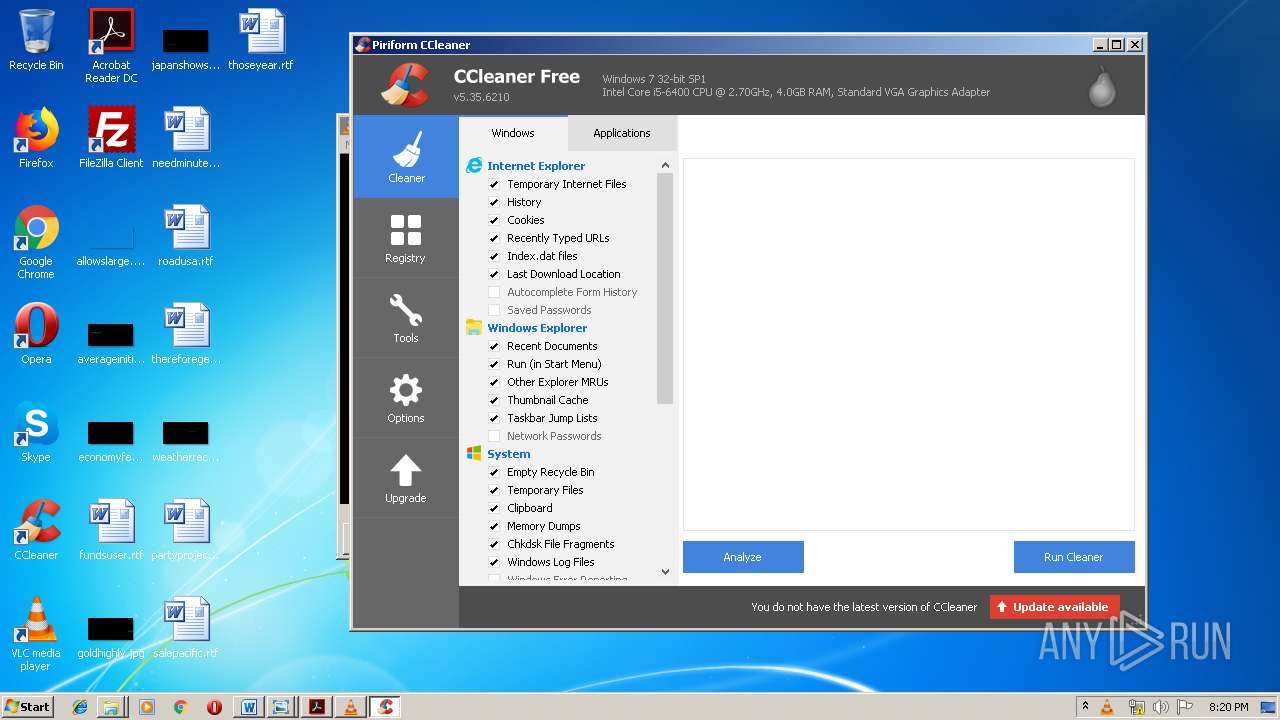
Changes the autorun value in the registry
- msptermsizes.exe (PID: 920)
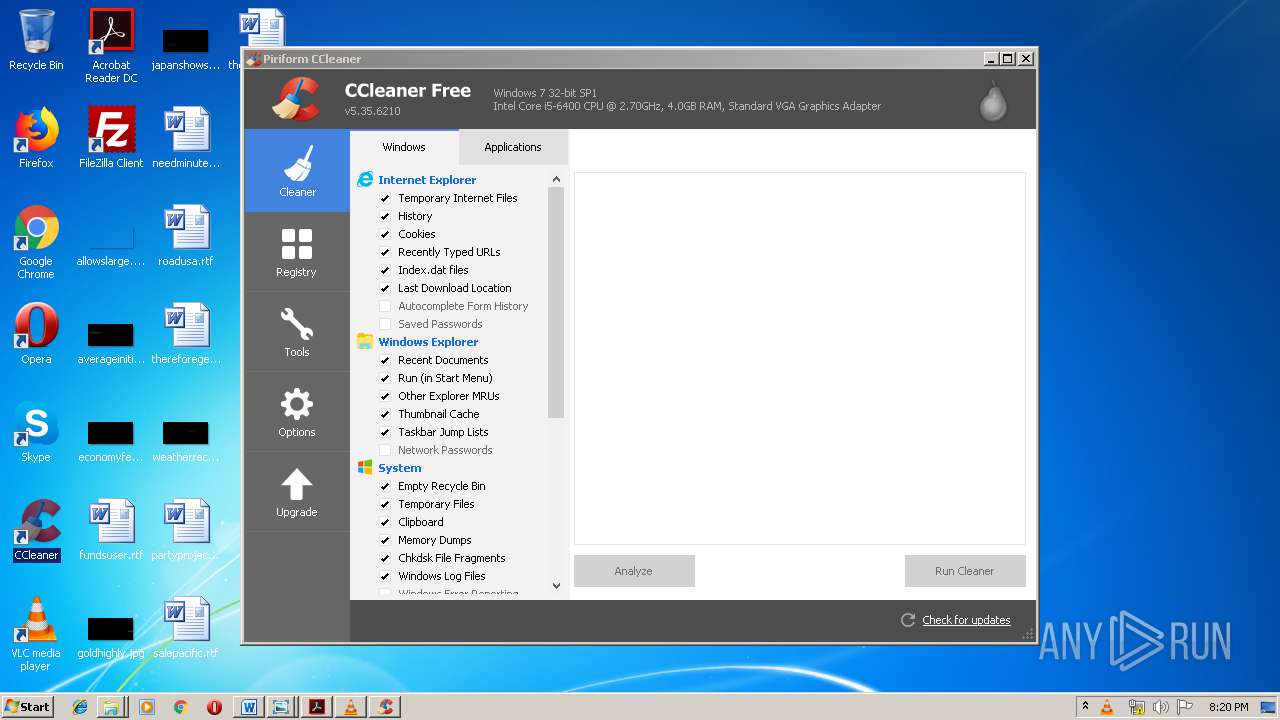
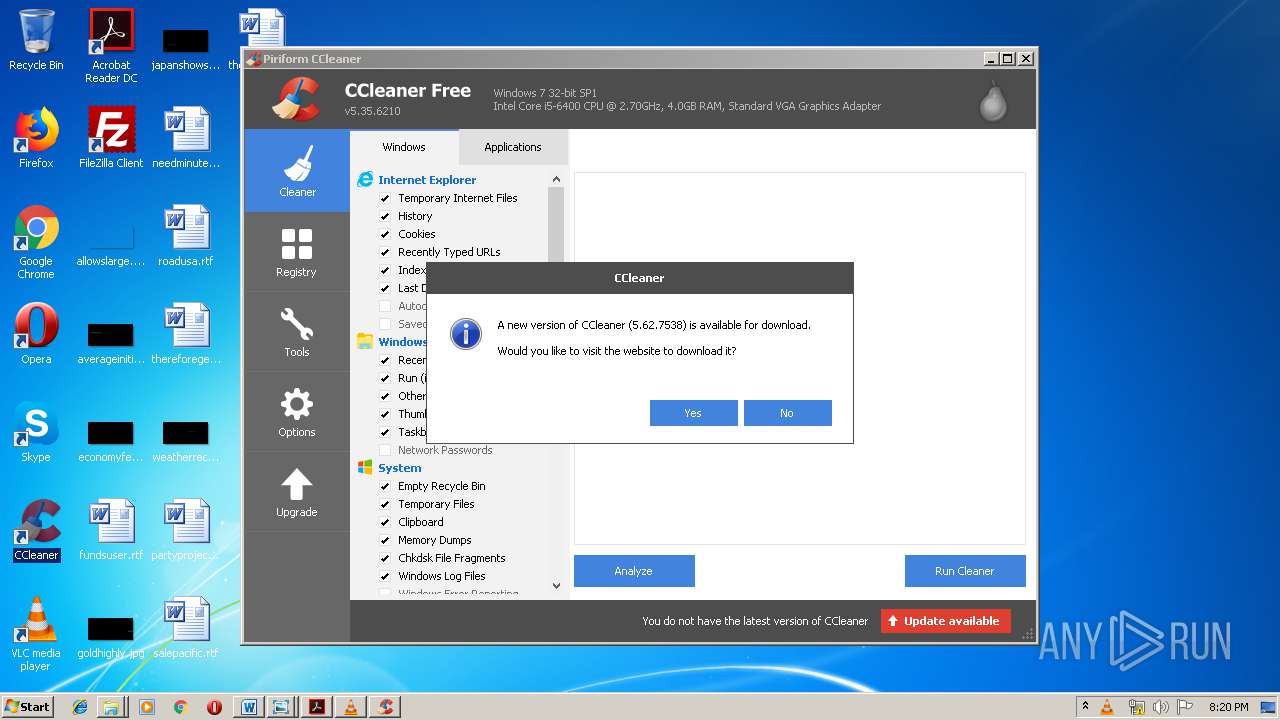
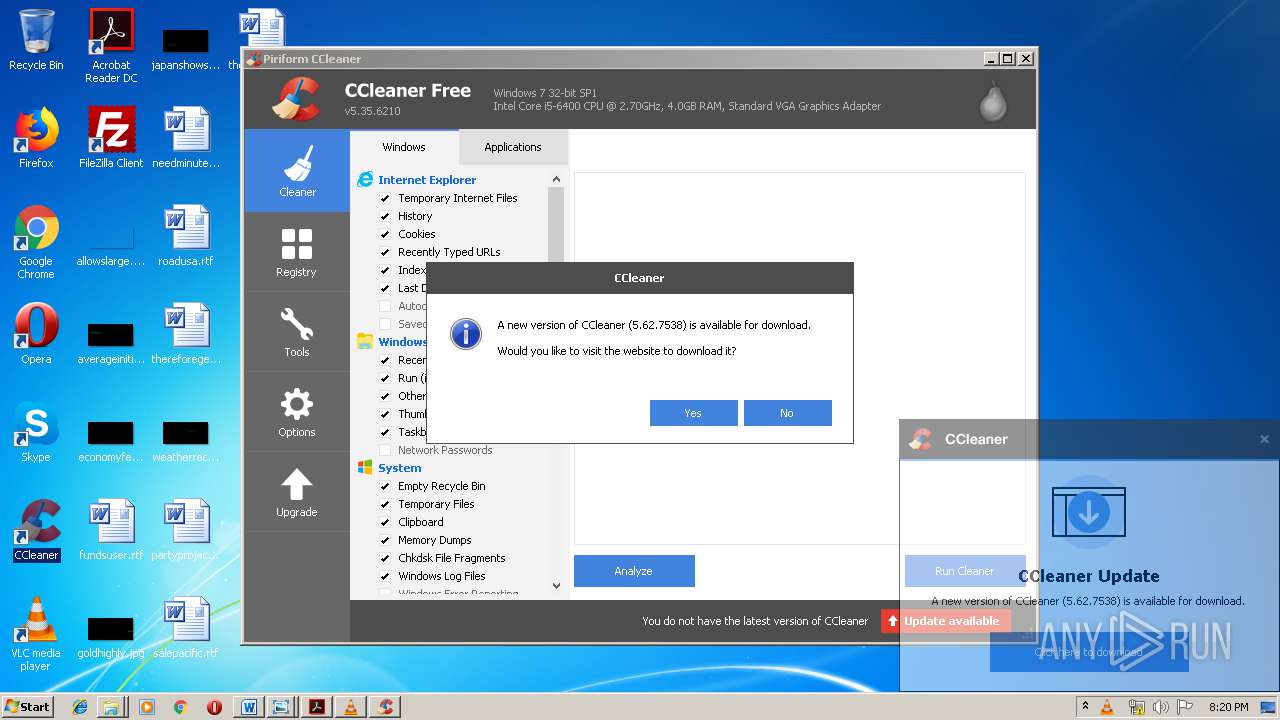
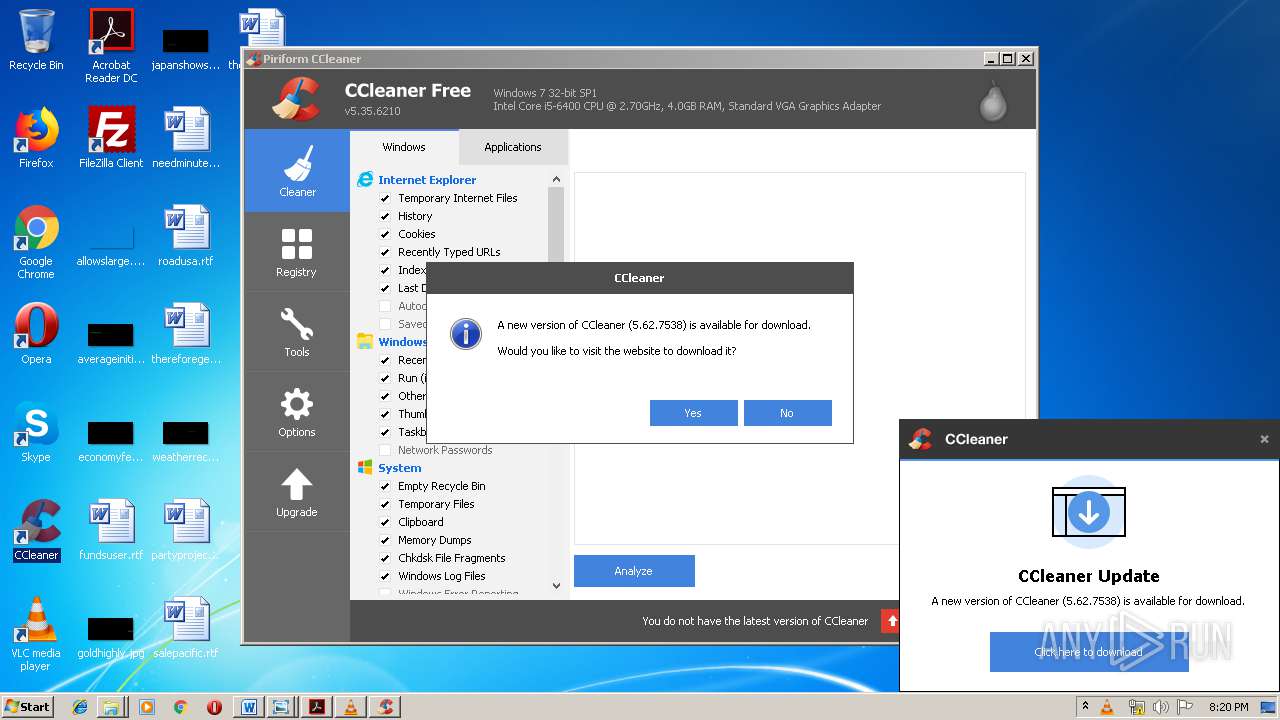
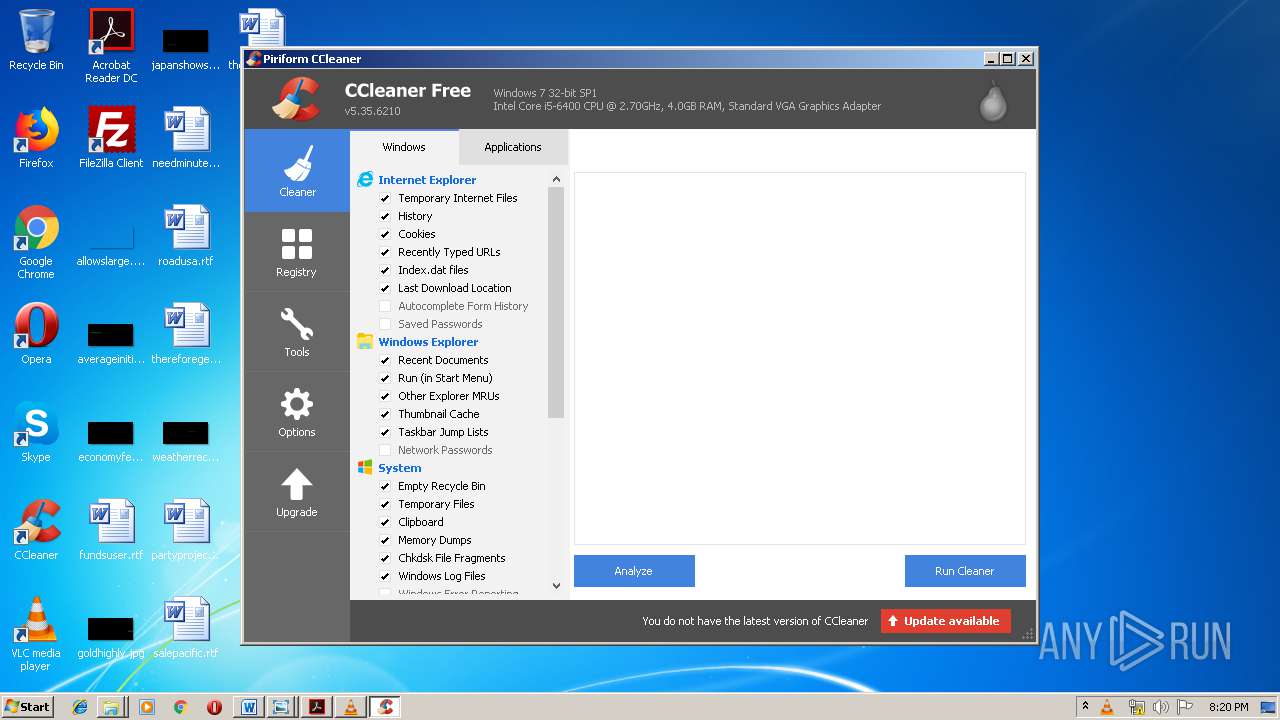
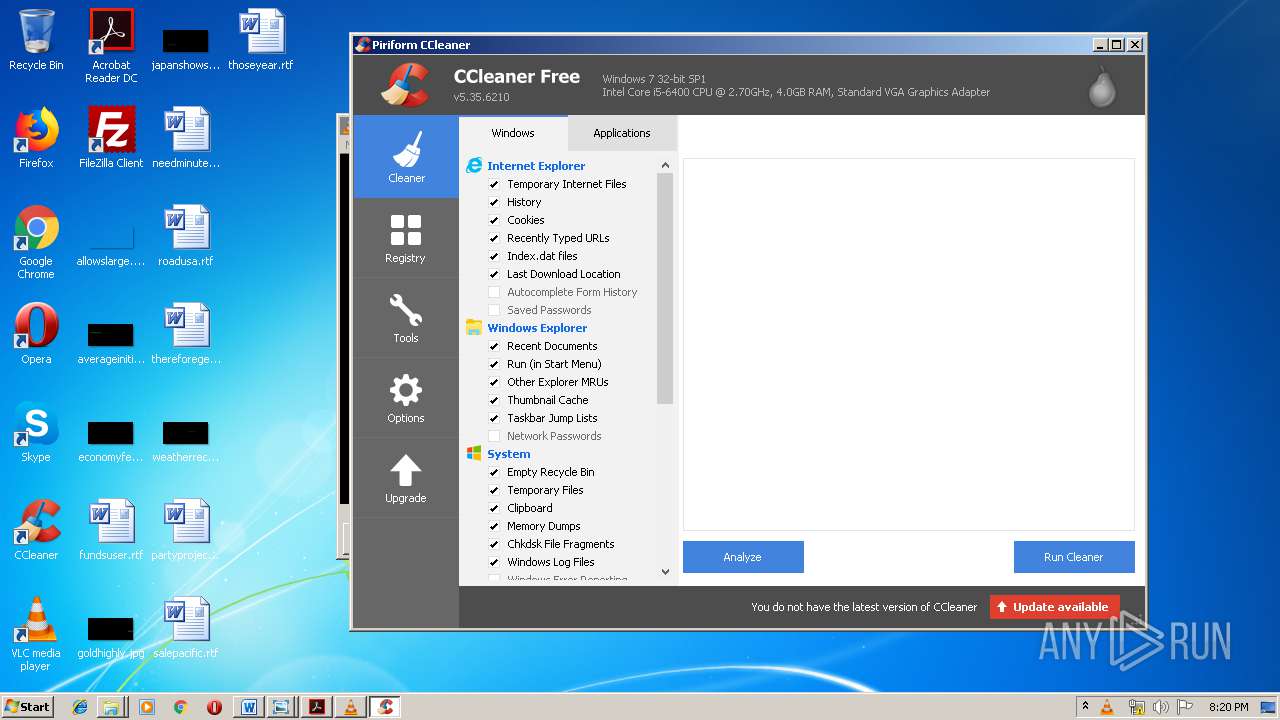
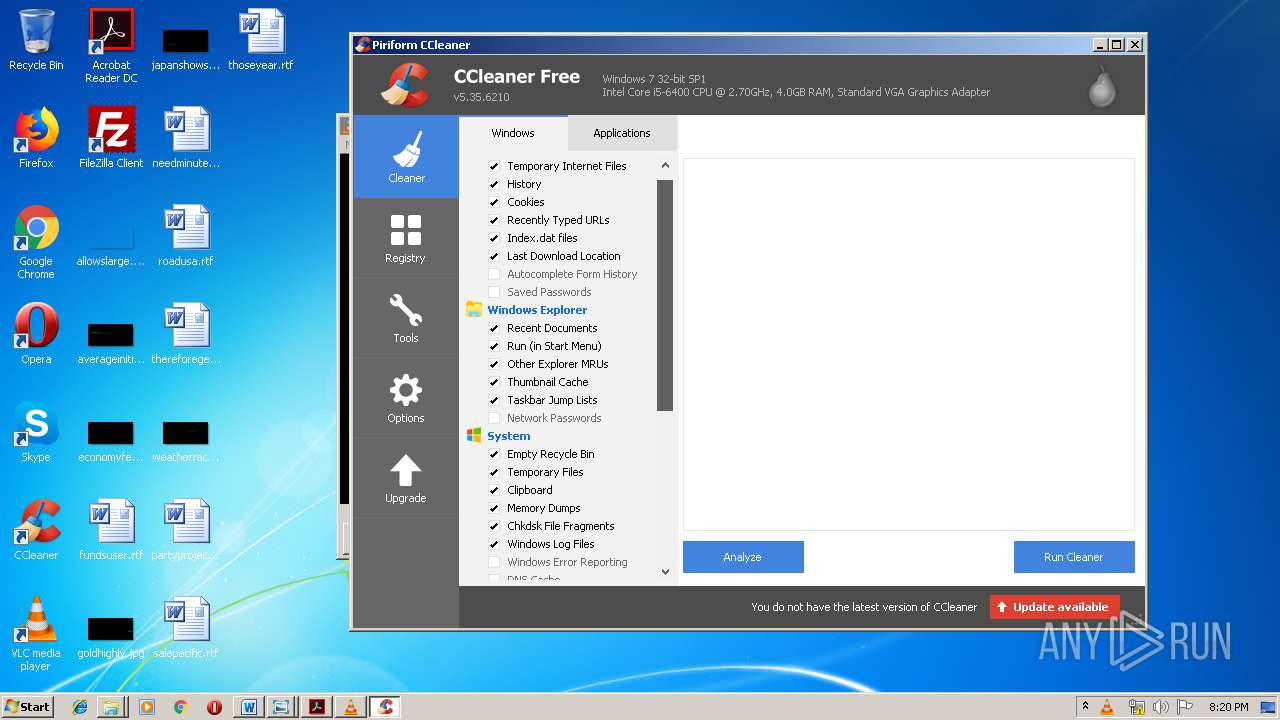
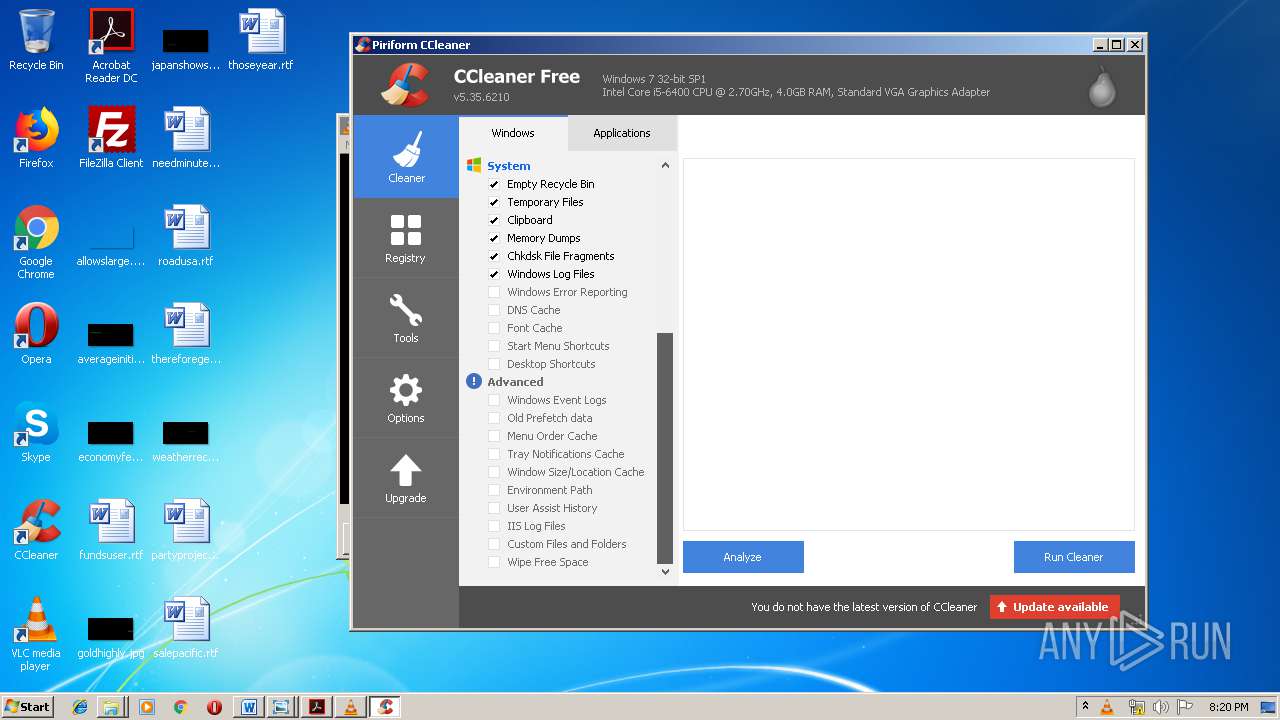
- CCleaner.exe (PID: 3596)
Loads the Task Scheduler COM API
- CCleaner.exe (PID: 2648)
- CCleaner.exe (PID: 3596)
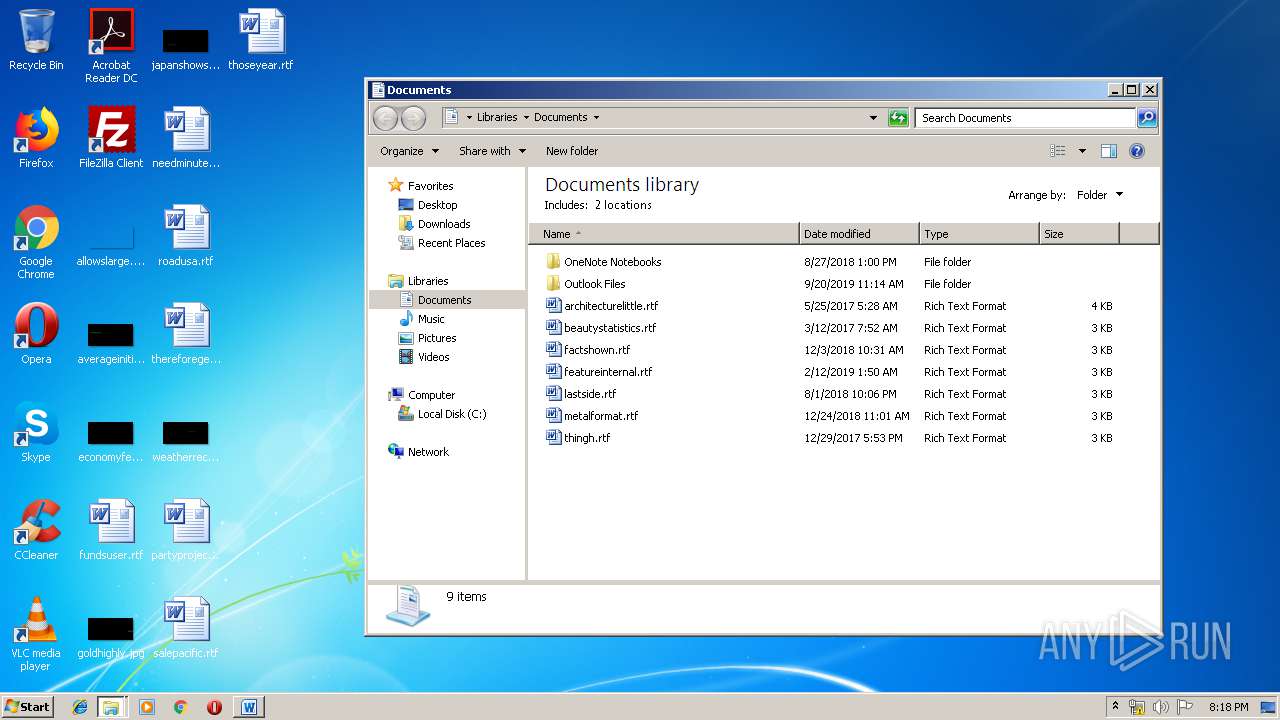
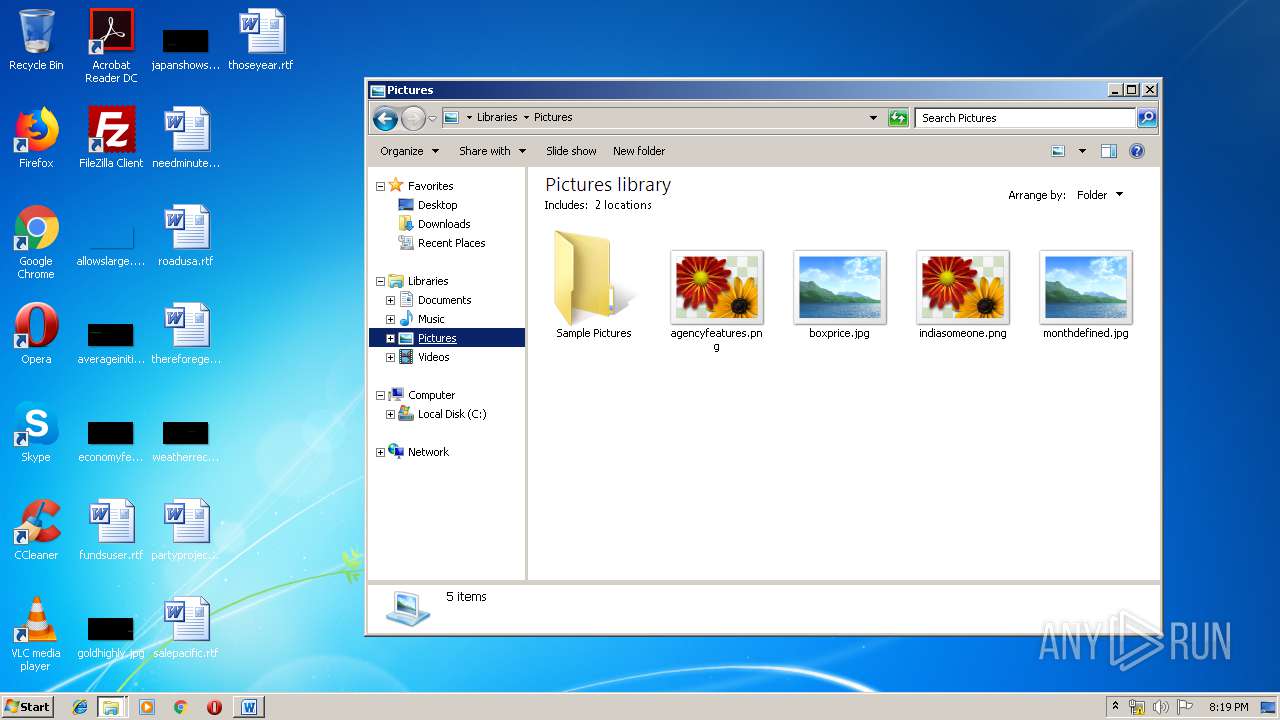
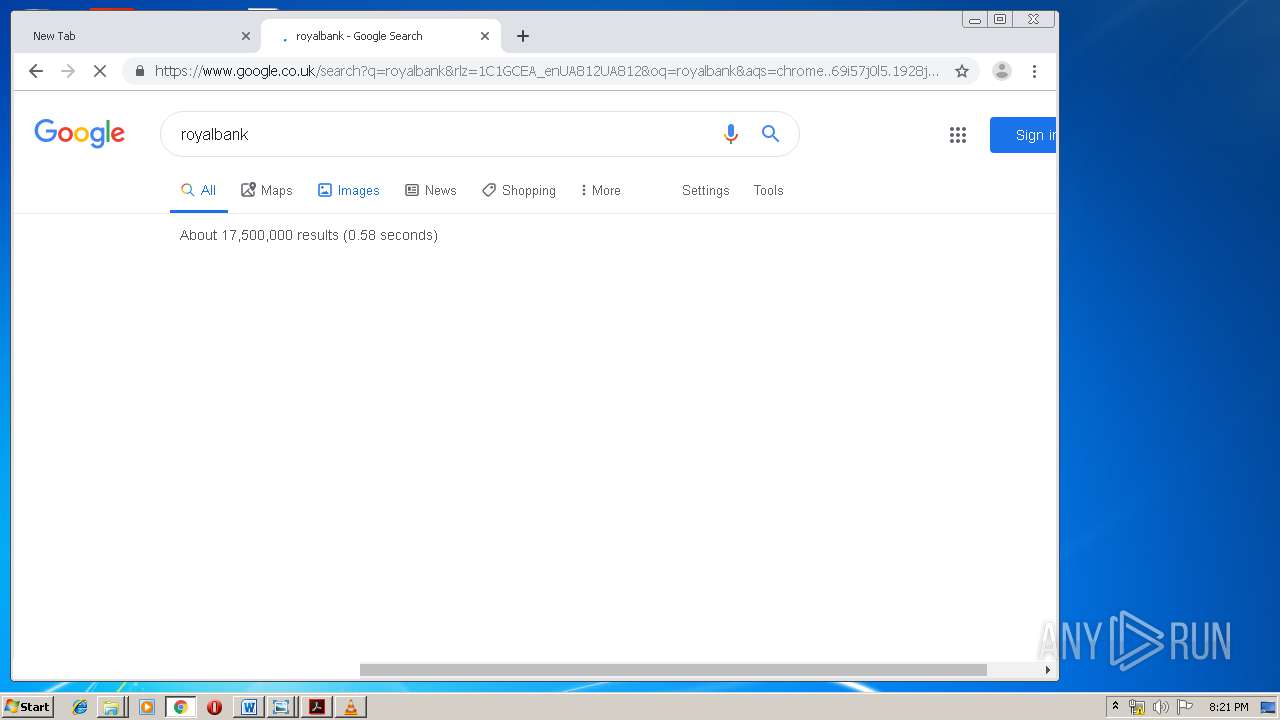
Actions looks like stealing of personal data
- CCleaner.exe (PID: 3380)
- CCleaner.exe (PID: 3596)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 3112)
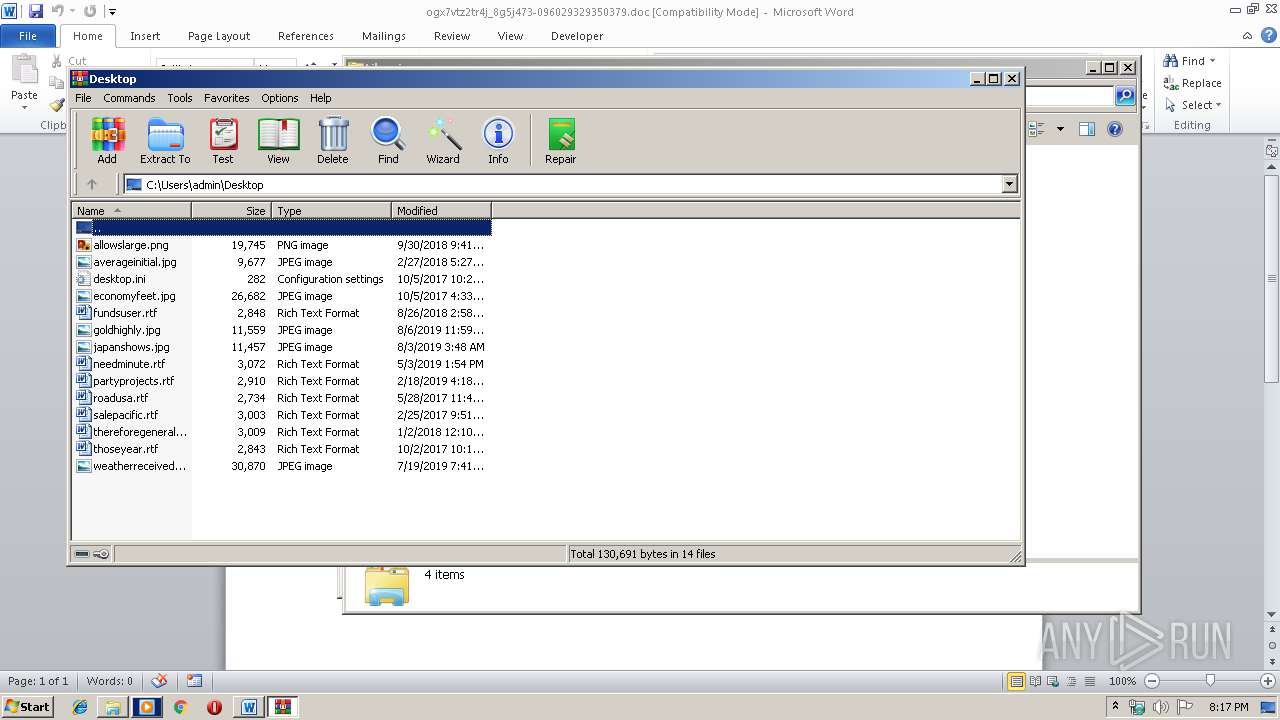
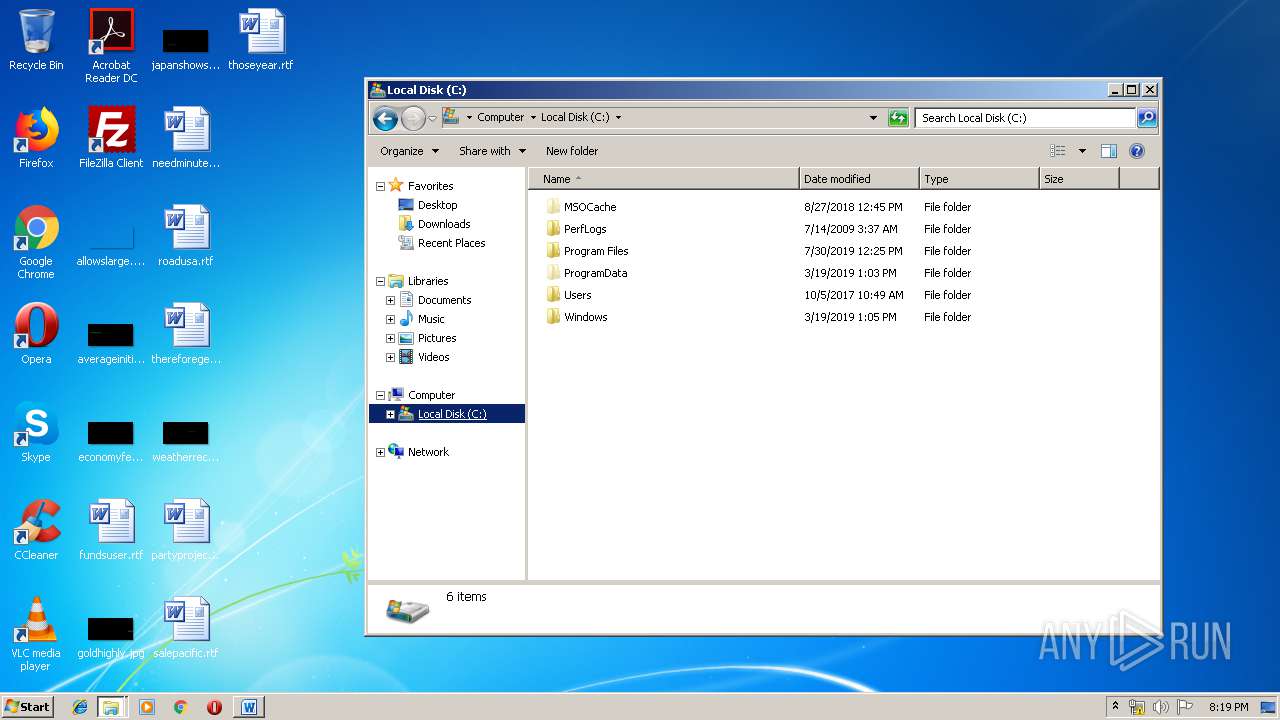
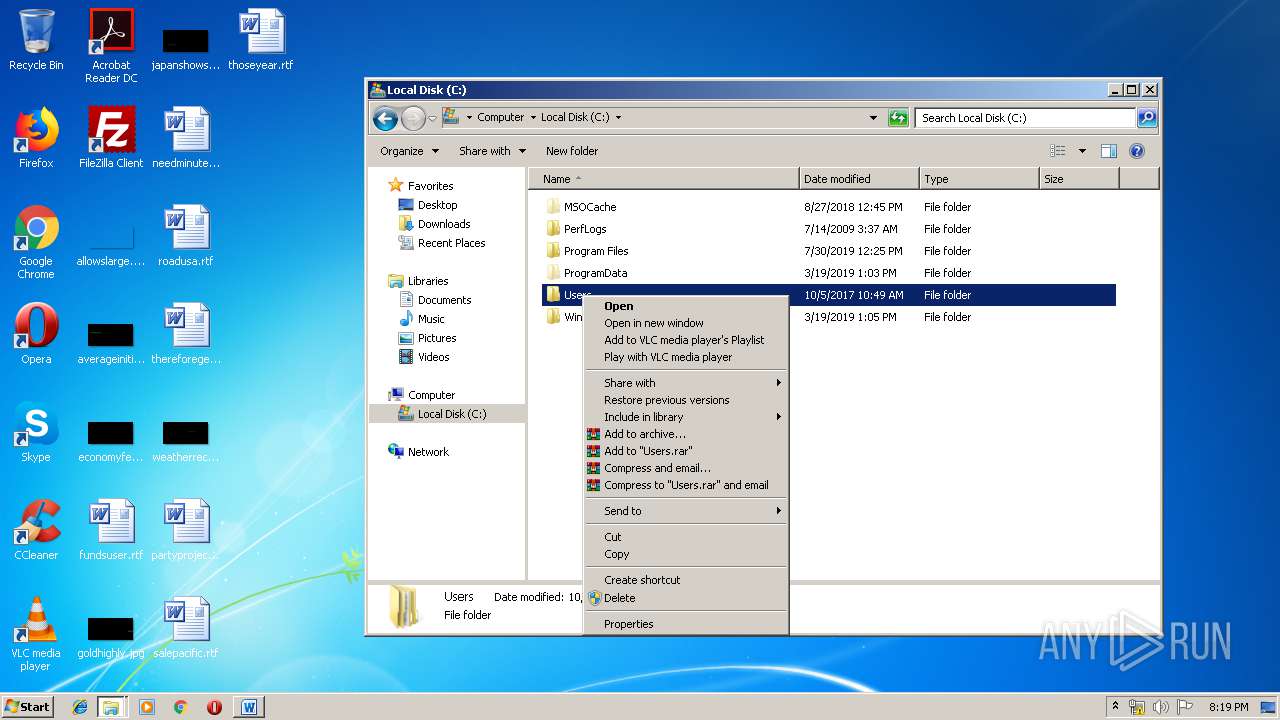
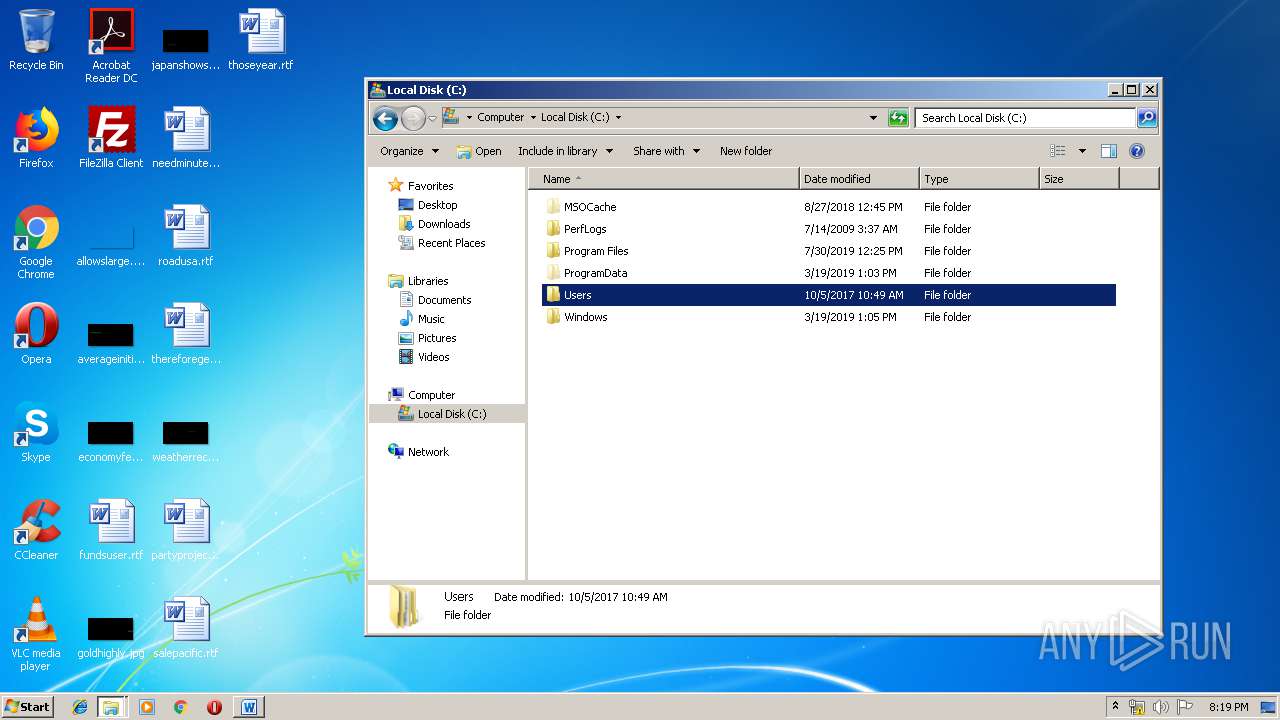
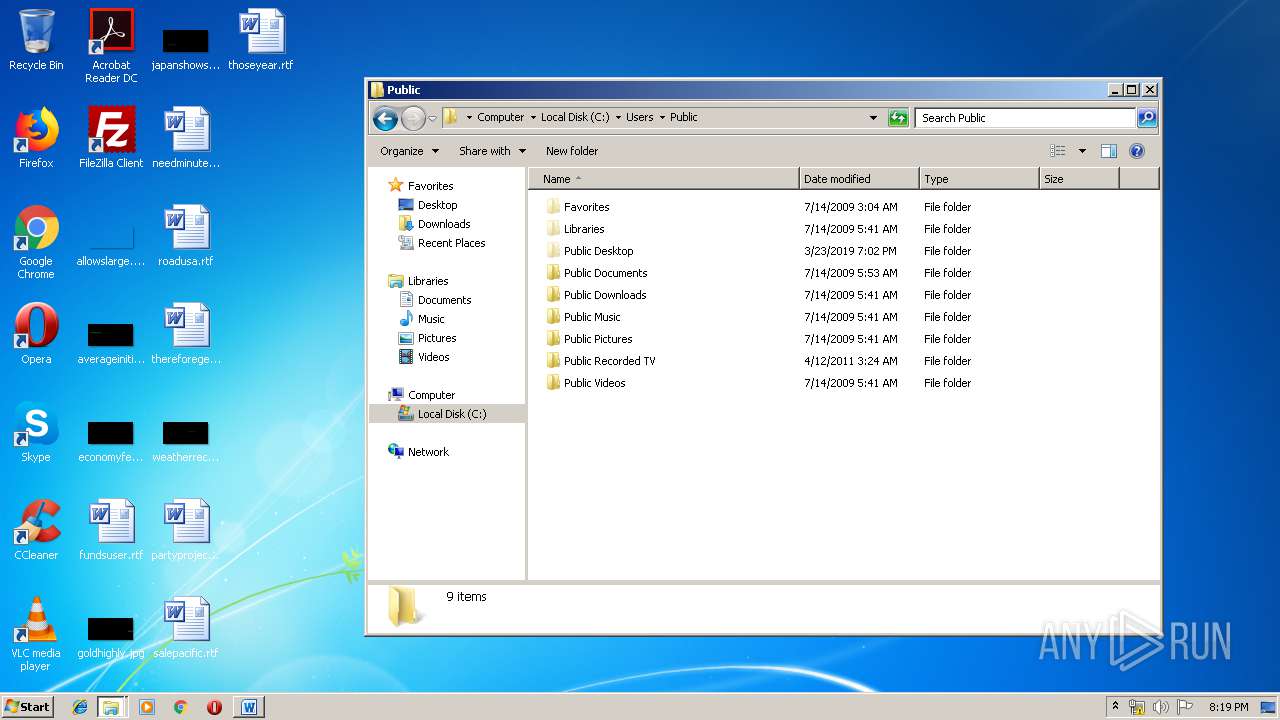
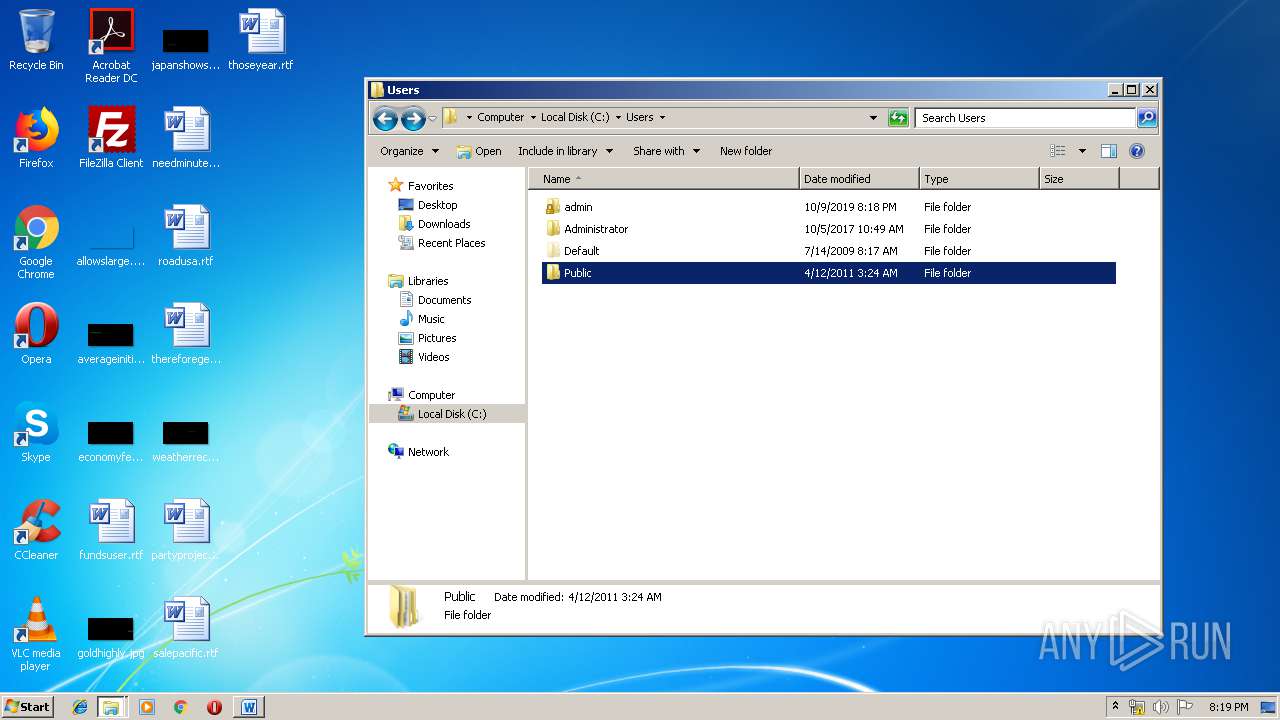
Creates files in the user directory
- powershell.exe (PID: 3112)
- vlc.exe (PID: 3884)
- CCleaner.exe (PID: 3380)
PowerShell script executed
- powershell.exe (PID: 3112)
Starts itself from another location
- 249.exe (PID: 2472)
Executable content was dropped or overwritten
- powershell.exe (PID: 3112)
- 249.exe (PID: 2472)
Application launched itself
- 249.exe (PID: 3664)
- msptermsizes.exe (PID: 2380)
- CCleaner.exe (PID: 3380)
Executed via COM
- DllHost.exe (PID: 3920)
Executed via Task Scheduler
- CCleaner.exe (PID: 3380)
Reads the cookies of Google Chrome
- CCleaner.exe (PID: 3380)
Reads internet explorer settings
- CCleaner.exe (PID: 3380)
- CCleaner.exe (PID: 3596)
Reads the cookies of Mozilla Firefox
- CCleaner.exe (PID: 3380)
Low-level read access rights to disk partition
- CCleaner.exe (PID: 3380)
Creates files in the program directory
- AdobeARM.exe (PID: 3000)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2800)
Creates files in the user directory
- WINWORD.EXE (PID: 2800)
Reads settings of System Certificates
- powershell.exe (PID: 3112)
- CCleaner.exe (PID: 3380)
- chrome.exe (PID: 936)
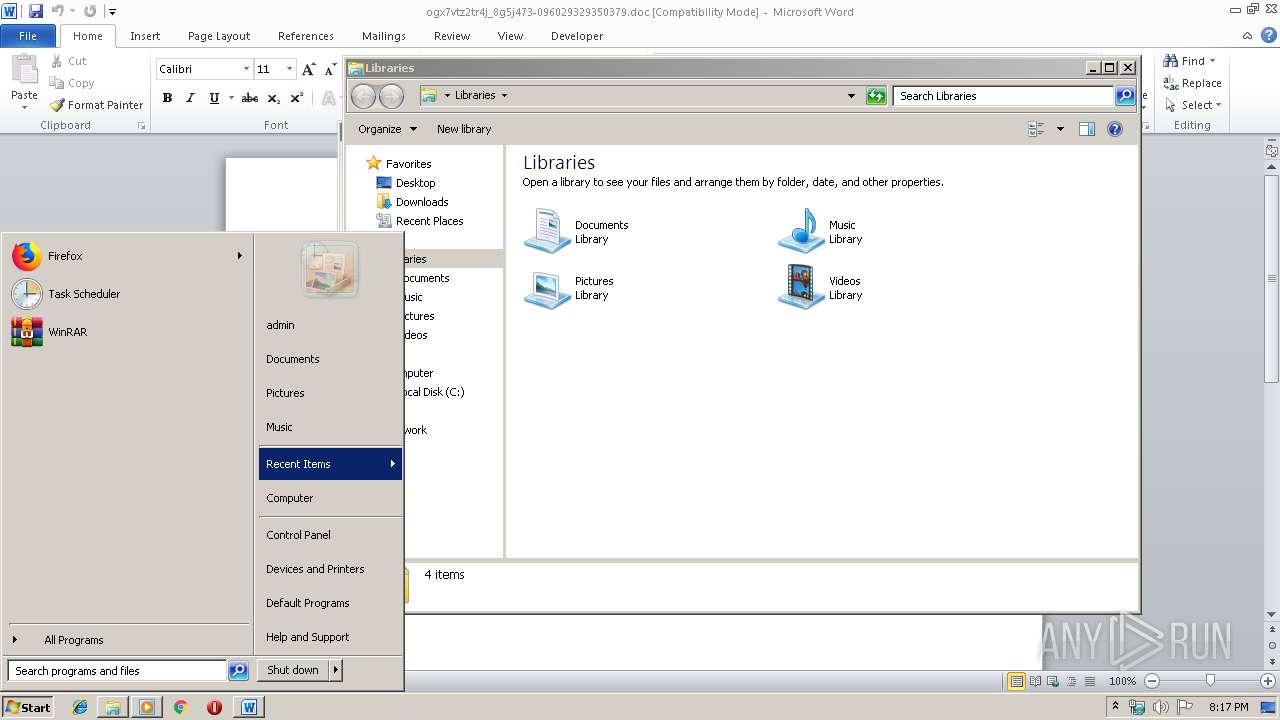
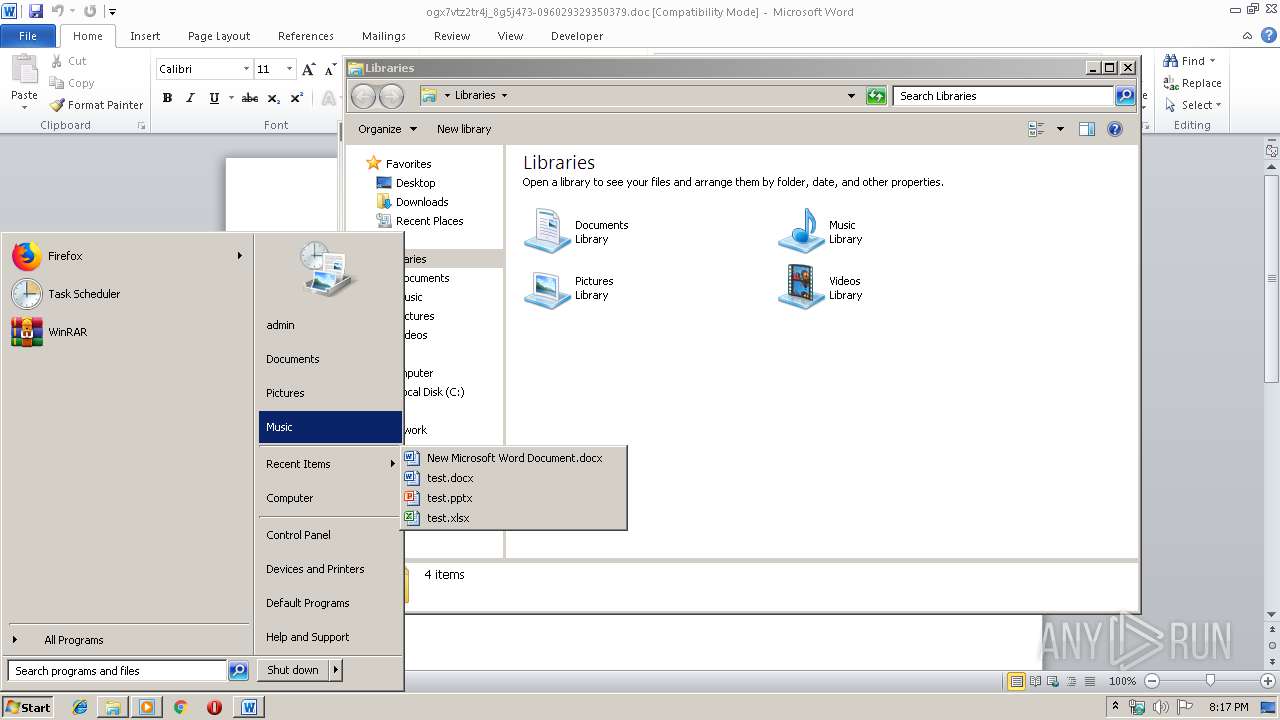
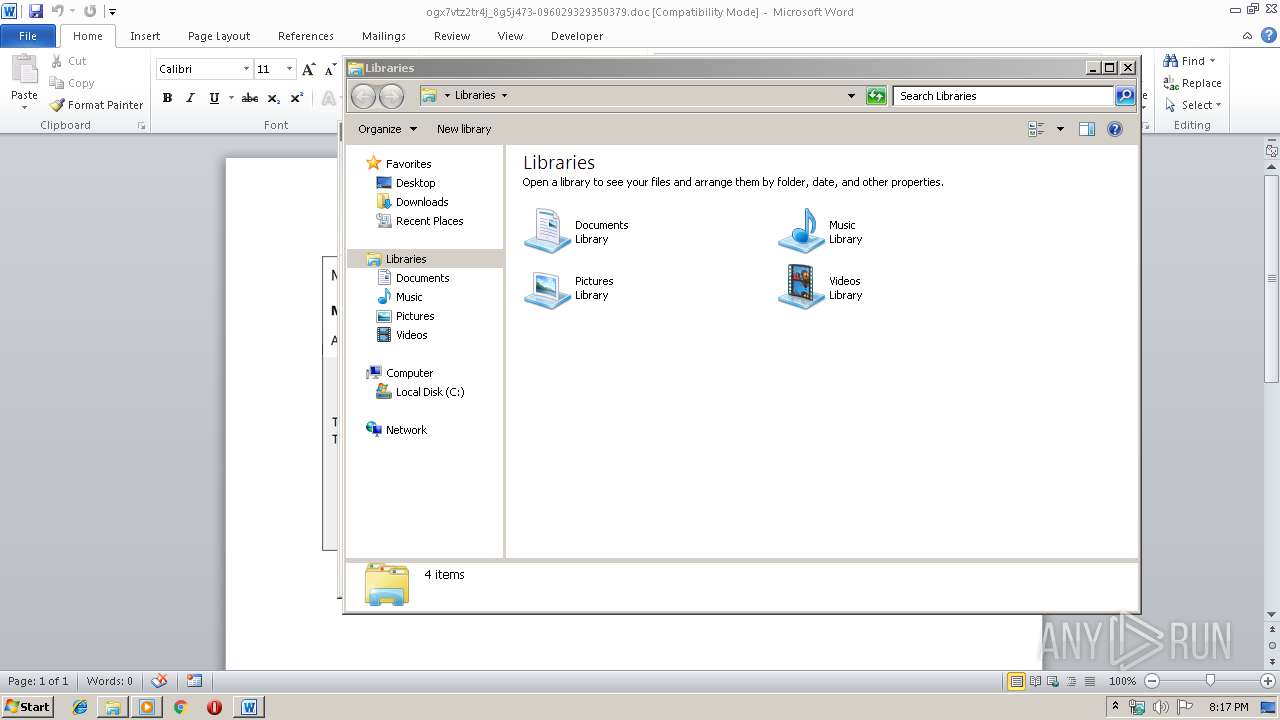
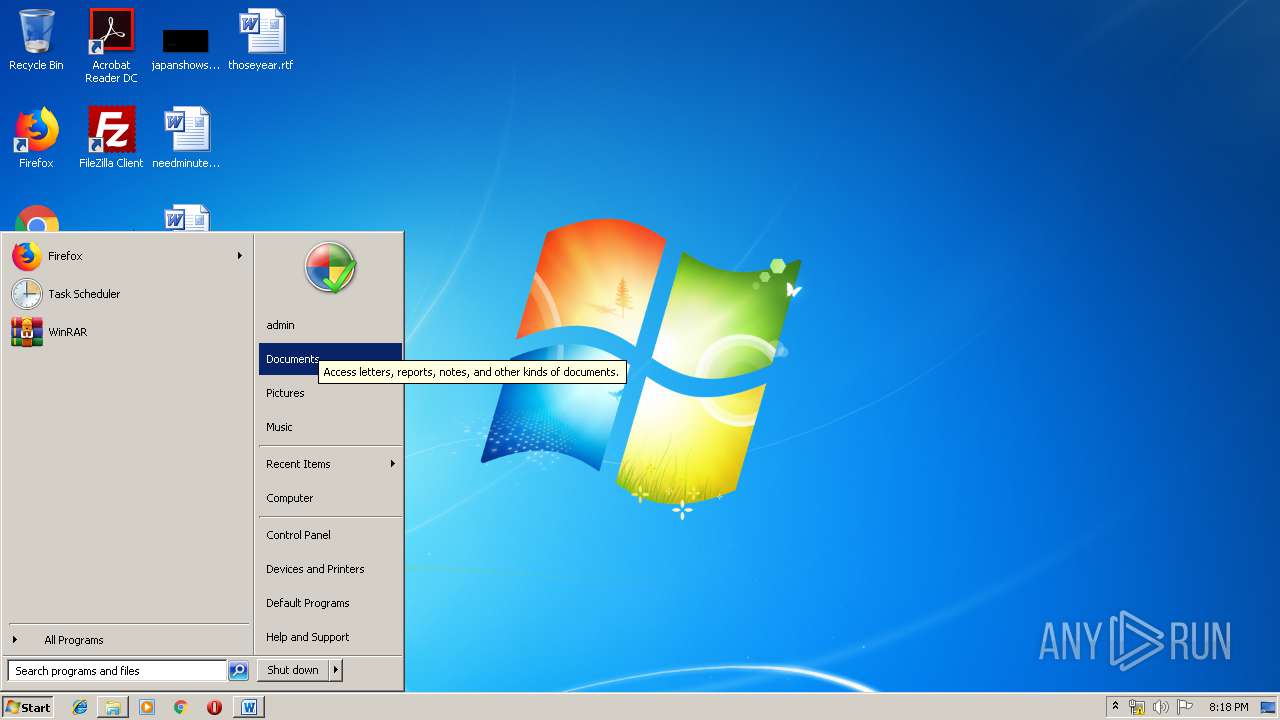
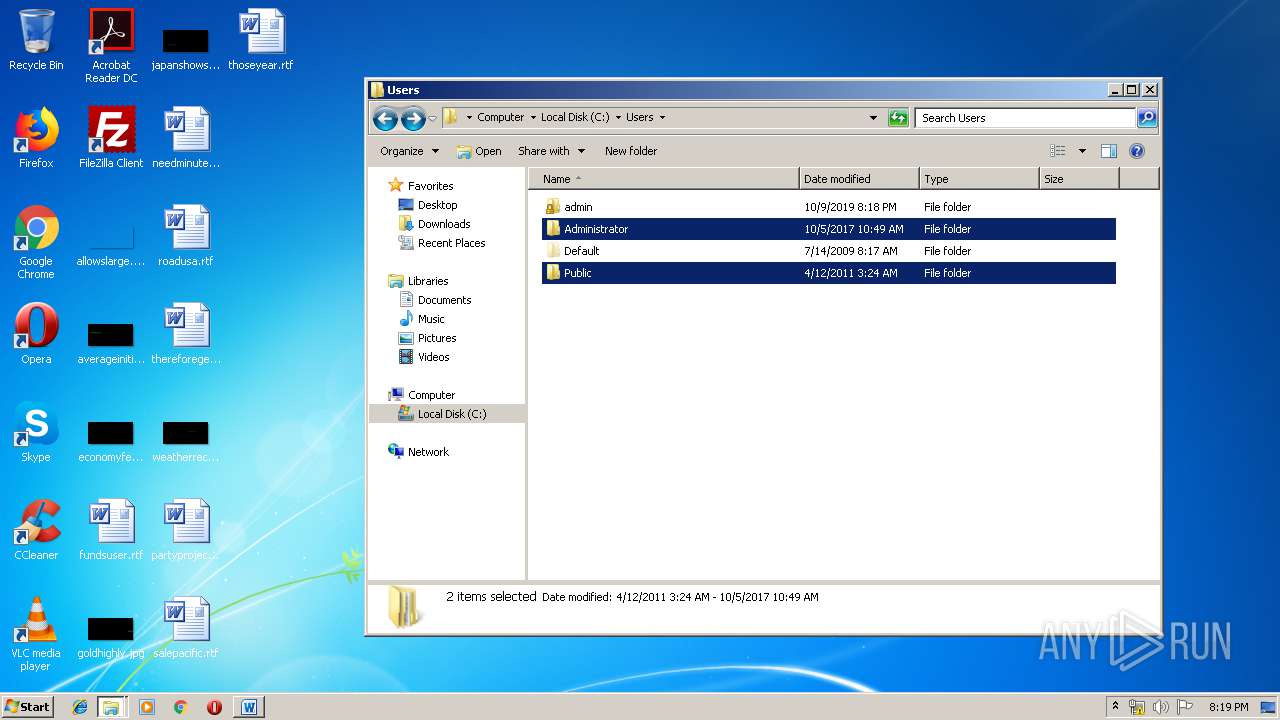
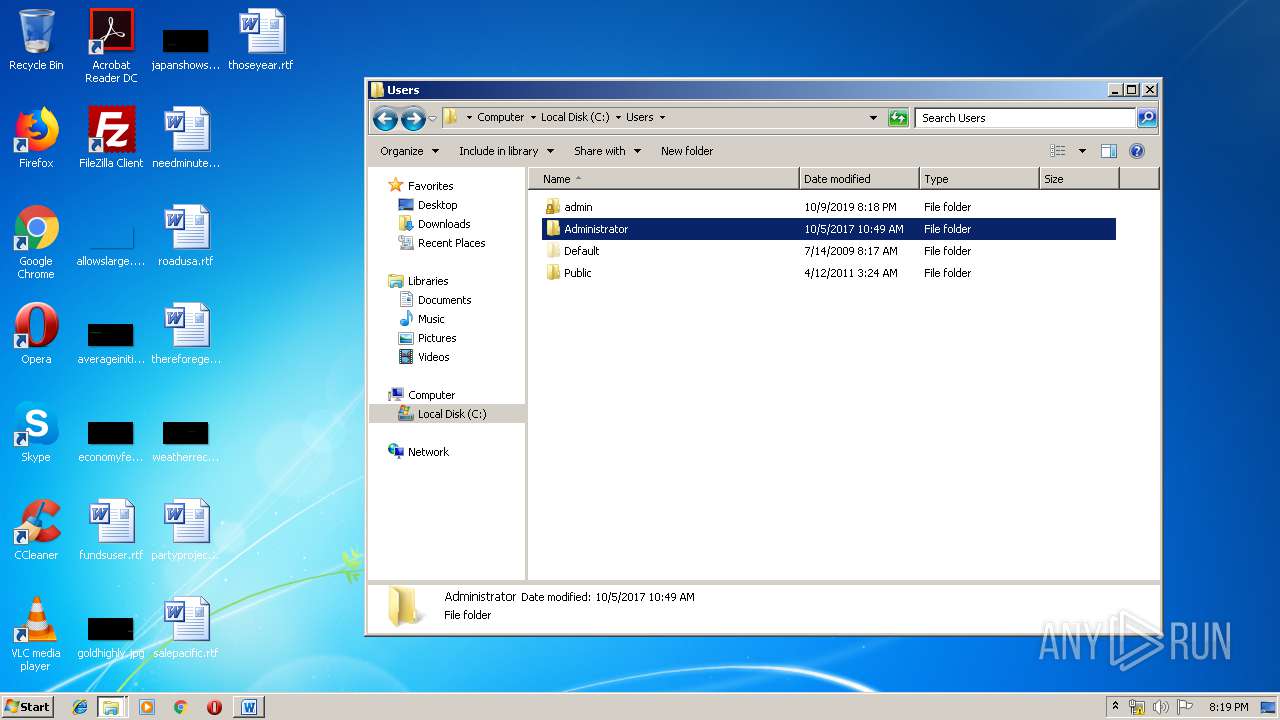
Manual execution by user
- wmplayer.exe (PID: 2488)
- explorer.exe (PID: 3388)
- WinRAR.exe (PID: 3796)
- CCleaner.exe (PID: 2648)
- AcroRd32.exe (PID: 1868)
- vlc.exe (PID: 3884)
- chrome.exe (PID: 2880)
Reads the hosts file
- RdrCEF.exe (PID: 3532)
- chrome.exe (PID: 2880)
- chrome.exe (PID: 936)
Application launched itself
- RdrCEF.exe (PID: 3532)
- chrome.exe (PID: 2880)
Changes settings of System certificates
- chrome.exe (PID: 936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Australian Dollar |
|---|---|
| Subject: | Rubber |
| Author: | Thalia Romaguera |
| Keywords: | Bedfordshire |
| Comments: | visionary |
| Template: | Normal.dotm |
| LastModifiedBy: | Nona Tremblay |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:10:09 16:49:00 |
| ModifyDate: | 2019:10:09 16:49:00 |
| Pages: | 1 |
| Words: | 30 |
| Characters: | 176 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Marks - Kassulke |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 205 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Schroeder |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
101
Monitored processes
56
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,14247296806055864136,3457735065831419913,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18339726825247763648 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3592 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 920 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | msptermsizes.exe | ||||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,14247296806055864136,3457735065831419913,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=204992764454420826 --mojo-platform-channel-handle=1584 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 1436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,14247296806055864136,3457735065831419913,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9695048911810569156 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,14247296806055864136,3457735065831419913,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3432304325392870559 --mojo-platform-channel-handle=4476 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2452 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,14247296806055864136,3457735065831419913,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9184006044356691662 --mojo-platform-channel-handle=3796 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,14247296806055864136,3457735065831419913,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9252071378283535060 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4732 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | |||||||||||||||
| 1868 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | explorer.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
Total events
3 632
Read events
2 791
Write events
817
Delete events
24
Modification events
| (PID) Process: | (2800) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | *b< |
Value: 2A623C00F00A0000010000000000000000000000 | |||
| (PID) Process: | (2800) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2800) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2800) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330184241 | |||
| (PID) Process: | (2800) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1330184355 | |||
| (PID) Process: | (2800) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1330184356 | |||
| (PID) Process: | (2800) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: F00A000050ECD11FD67ED50100000000 | |||
| (PID) Process: | (2800) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 3c< |
Value: 33633C00F00A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2800) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 3c< |
Value: 33633C00F00A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2800) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
68
Text files
238
Unknown types
33
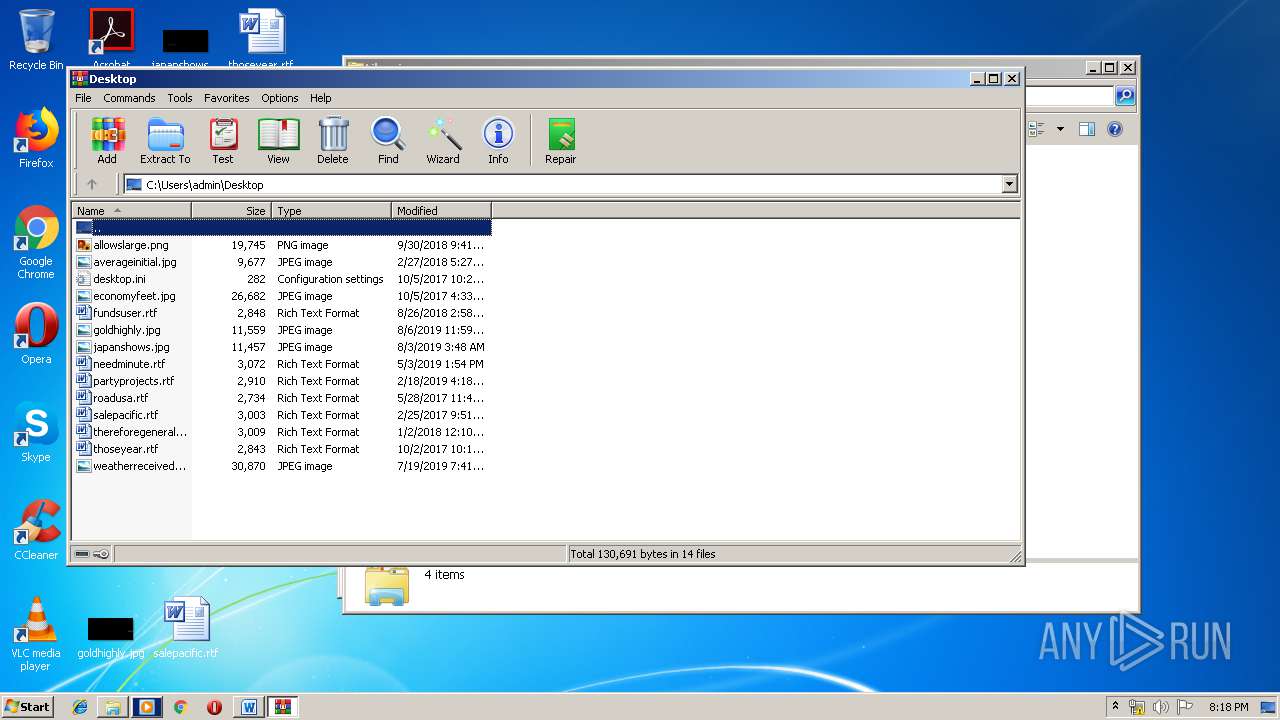
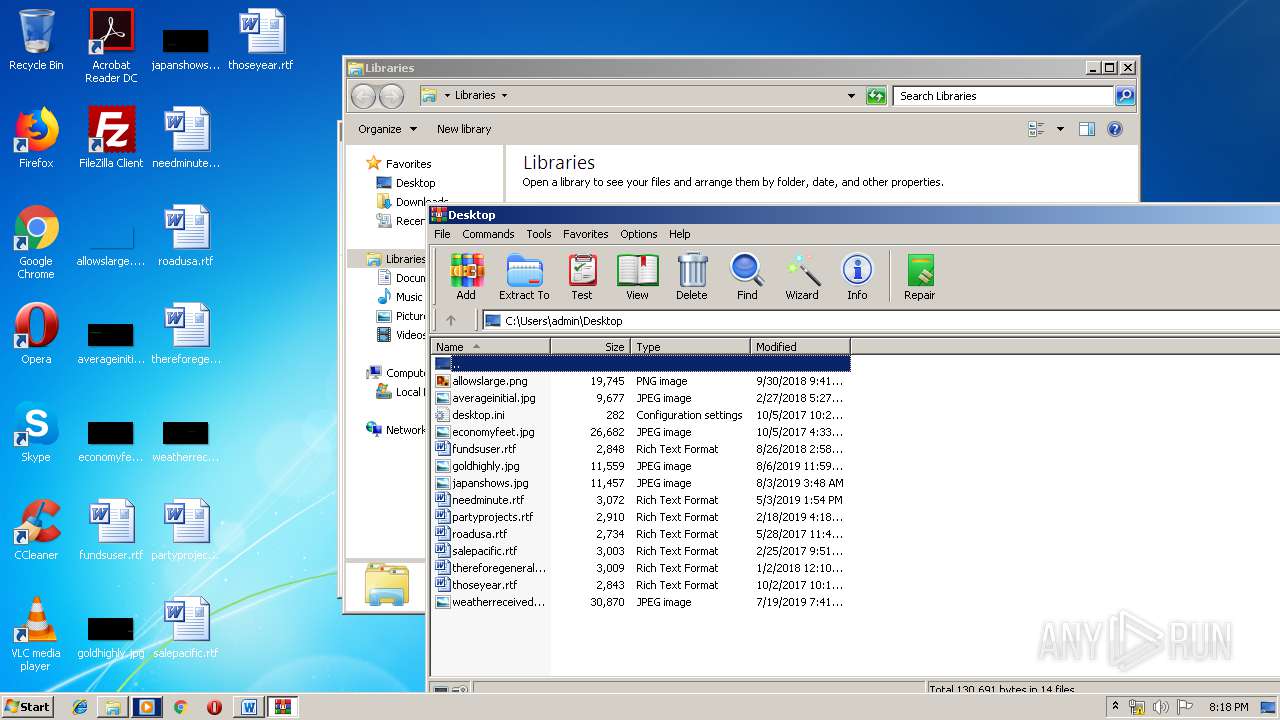
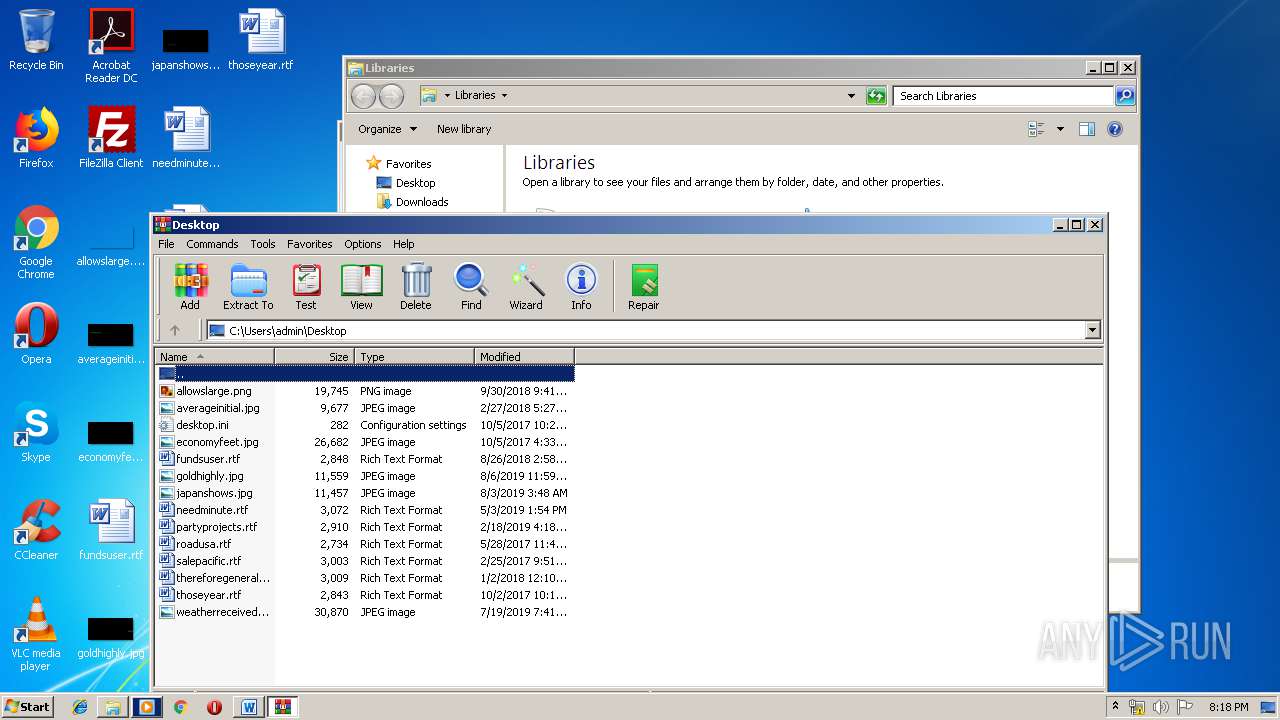
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2800 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4E8A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3112 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ZGF4BADJWZ403UU38XTF.temp | — | |
MD5:— | SHA256:— | |||
| 2800 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1360 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 2800 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\72766F55.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1360 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\Cache\AdobeFnt16.lst.1360 | — | |
MD5:— | SHA256:— | |||
| 2800 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$x7vtz2tr4j_8g5j473-096029329350379.doc | pgc | |
MD5:— | SHA256:— | |||
| 1360 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\AdobeFnt16.lst.1360 | — | |
MD5:— | SHA256:— | |||
| 2800 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\9614EBE.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2800 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1DE3712B.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
90
DNS requests
61
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3380 | CCleaner.exe | GET | 301 | 151.101.0.64:80 | http://www.piriform.com/auto?a=0&p=cc&v=5.35.6210&l=1033&lk=&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-VJCA&o=6.1W3&au=1&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gu=00000000-0000-4000-8000-d6f7f2be5127 | US | — | — | whitelisted |
936 | chrome.exe | GET | 204 | 172.217.26.35:80 | http://csi.gstatic.com/csi?v=3&s=gapi_module&action=gapi_iframes__googleapis_cli12&it=mli.27,mei.5&tbsrt=725&tran=15&e=abc_l0,abc_m0,abc_pgapi_iframes__googleapis_cli12,abc_u0&rt= | US | — | — | whitelisted |
1868 | AcroRd32.exe | GET | 304 | 2.16.186.97:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/279_15_23_20070.zip | unknown | — | — | whitelisted |
1868 | AcroRd32.exe | GET | 304 | 2.16.186.97:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | unknown | — | — | whitelisted |
1868 | AcroRd32.exe | GET | 304 | 2.16.186.97:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | unknown | — | — | whitelisted |
1868 | AcroRd32.exe | GET | 304 | 2.16.186.97:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/message.zip | unknown | — | — | whitelisted |
920 | msptermsizes.exe | POST | 200 | 198.199.114.69:8080 | http://198.199.114.69:8080/taskbar/vermont/ringin/merge/ | US | binary | 132 b | malicious |
920 | msptermsizes.exe | POST | — | 23.239.29.211:443 | http://23.239.29.211:443/health/free/ | US | — | — | malicious |
936 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
1868 | AcroRd32.exe | GET | 304 | 2.16.186.97:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 151.101.0.64:443 | www.piriform.com | Fastly | US | whitelisted |
3380 | CCleaner.exe | 151.101.2.202:443 | www.ccleaner.com | Fastly | US | suspicious |
— | — | 2.21.36.203:443 | armmf.adobe.com | GTT Communications Inc. | FR | suspicious |
— | — | 2.18.233.74:443 | ardownload2.adobe.com | Akamai International B.V. | — | whitelisted |
936 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
936 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
936 | chrome.exe | 172.217.16.131:443 | www.google.com.ua | Google Inc. | US | whitelisted |
936 | chrome.exe | 172.217.21.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
936 | chrome.exe | 172.217.23.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3112 | powershell.exe | 45.56.100.50:80 | www.soprettyhairllc.com | Linode, LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.soprettyhairllc.com |
| unknown |
www.zhizaisifang.com |
| unknown |
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
www.piriform.com |
| whitelisted |
www.ccleaner.com |
| whitelisted |
ardownload2.adobe.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
920 | msptermsizes.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
920 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
920 | msptermsizes.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
920 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
7 ETPRO signatures available at the full report
Process | Message |
|---|---|
vlc.exe | core libvlc: Running vlc with the default interface. Use 'cvlc' to use vlc without interface.
|