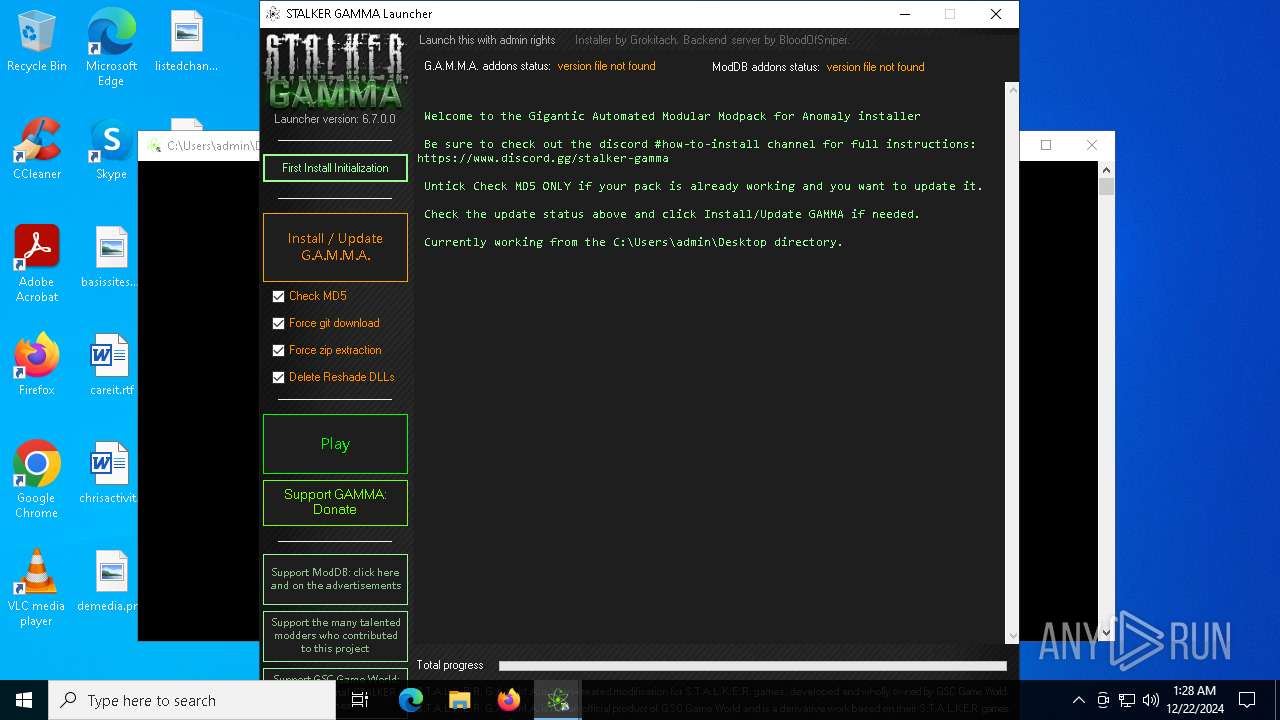
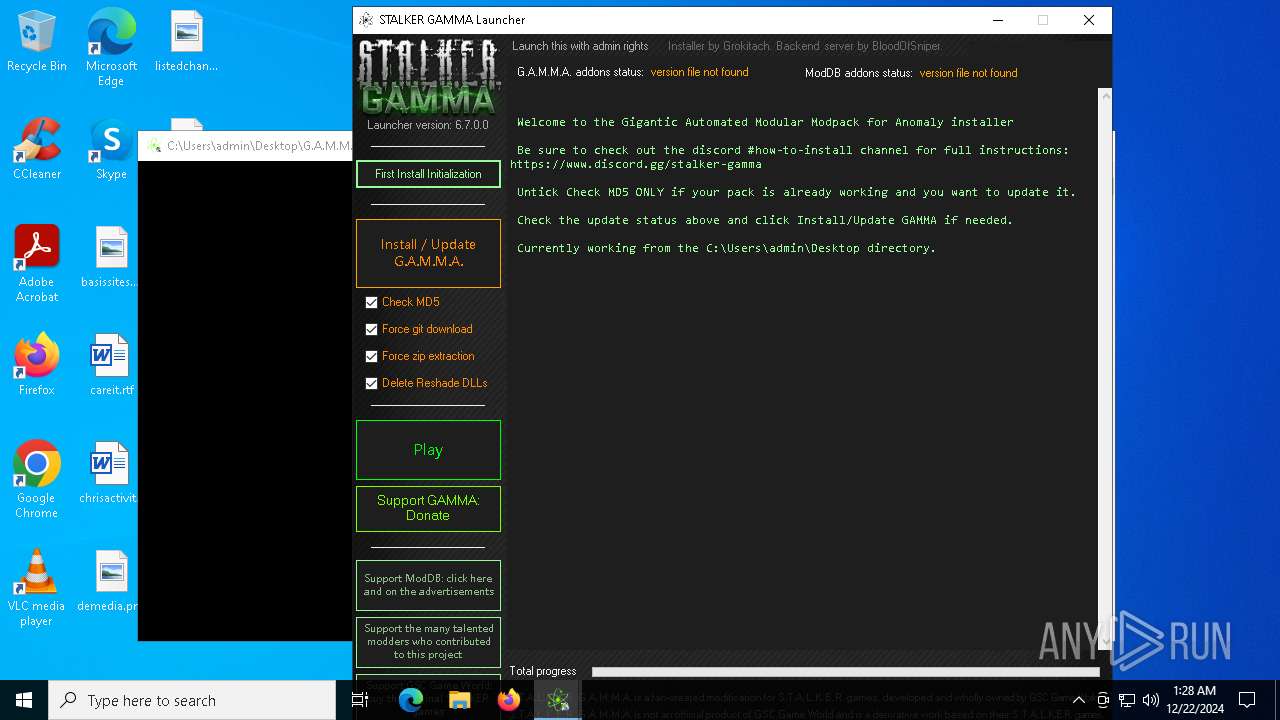
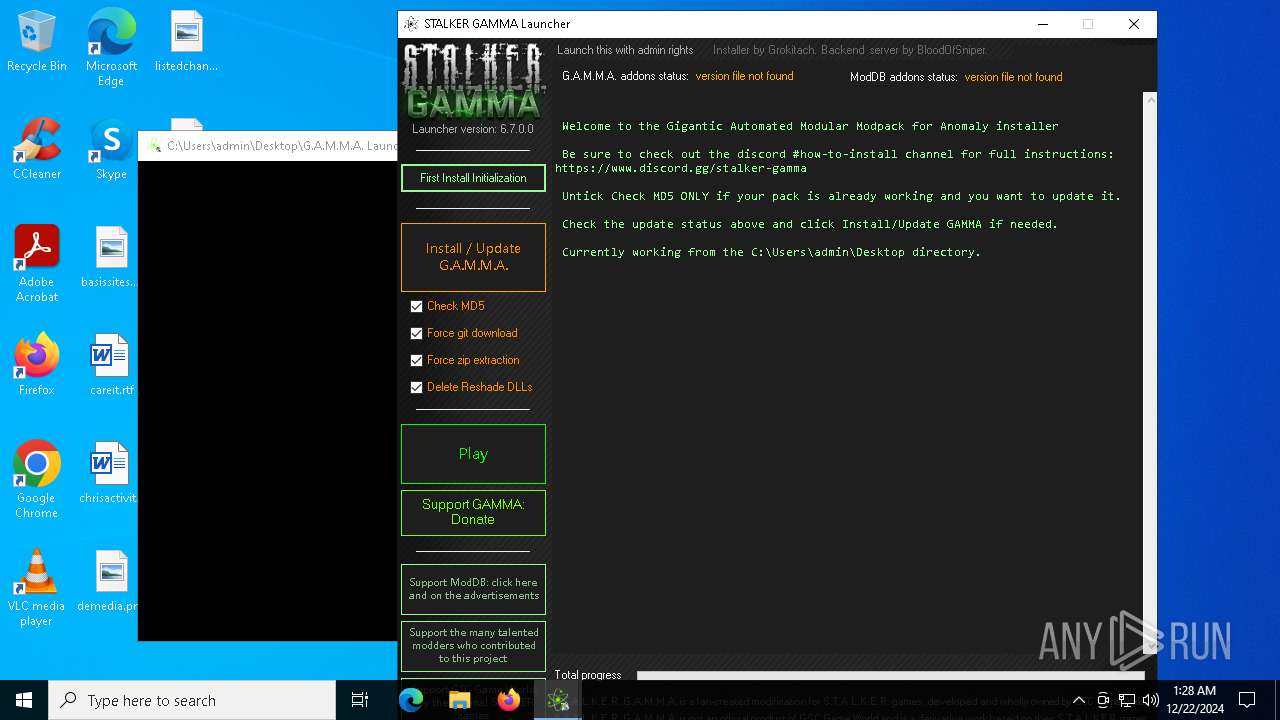
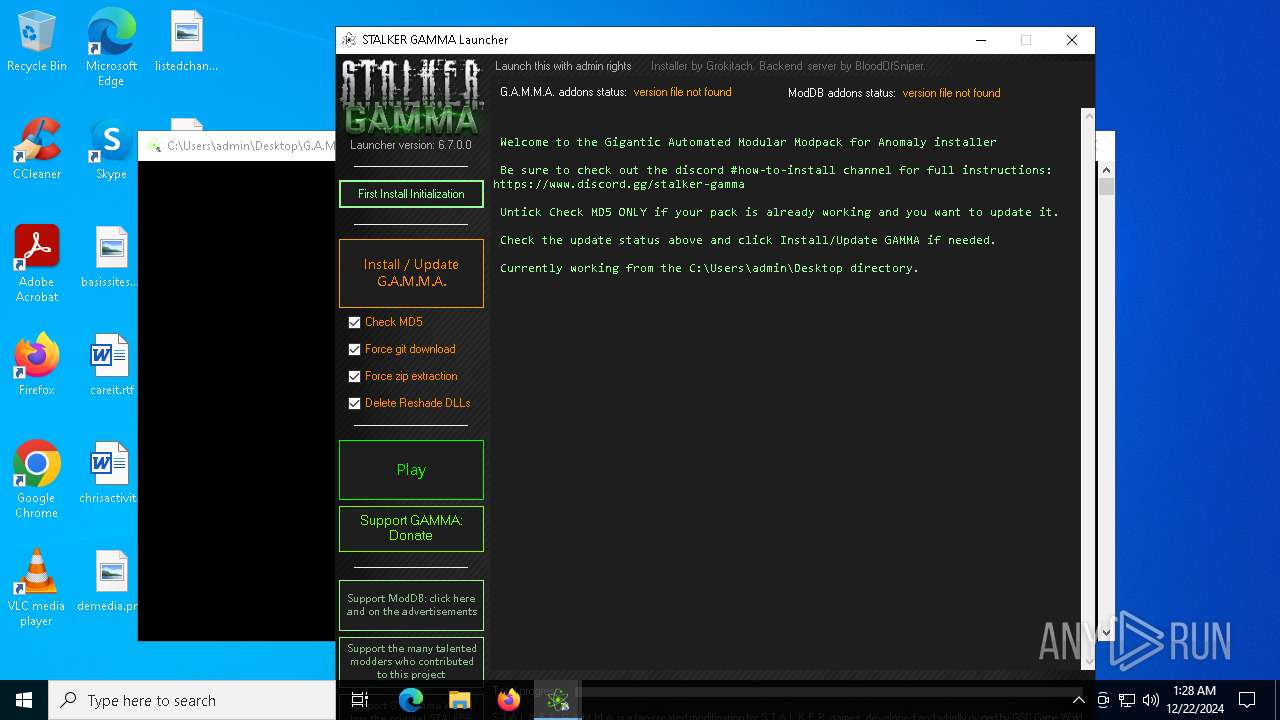
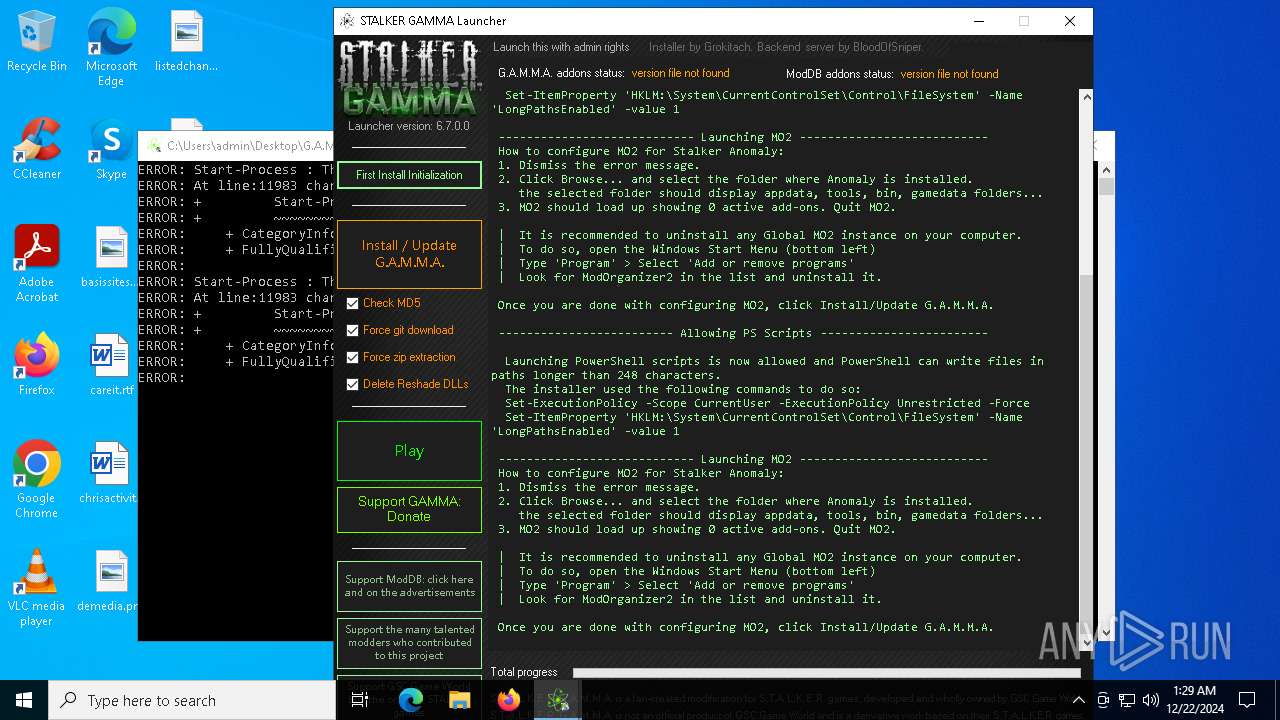
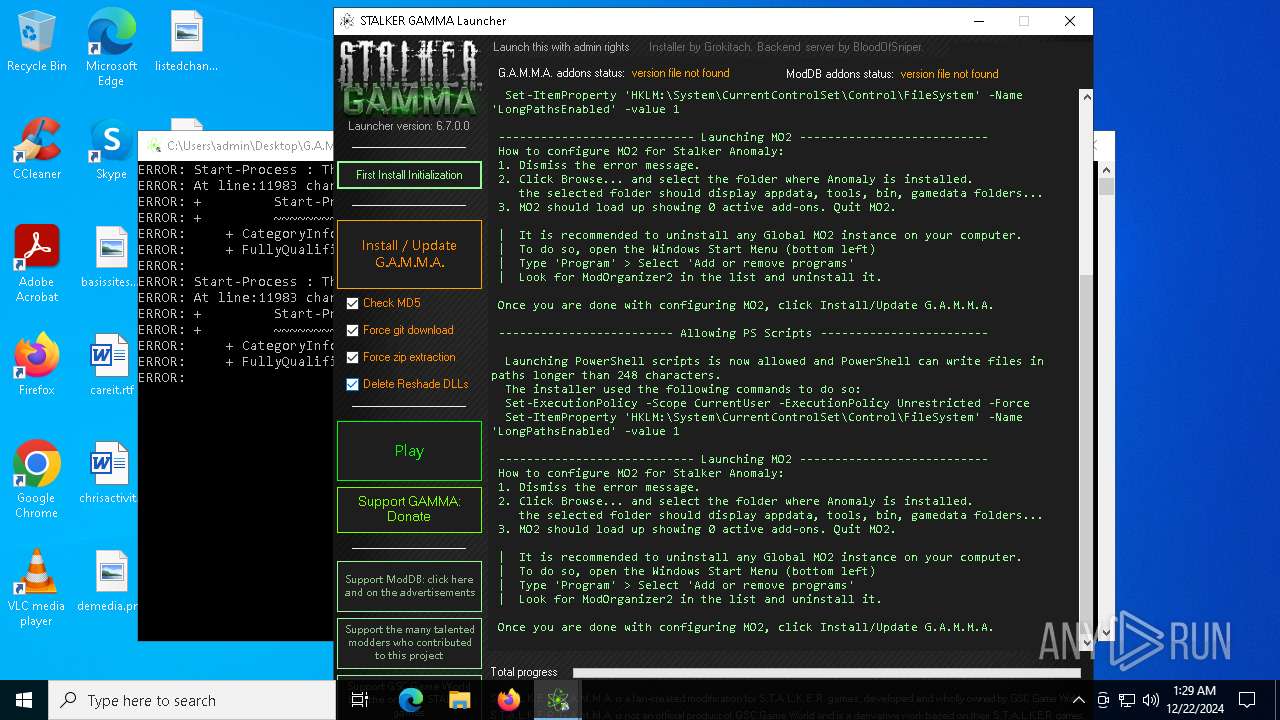
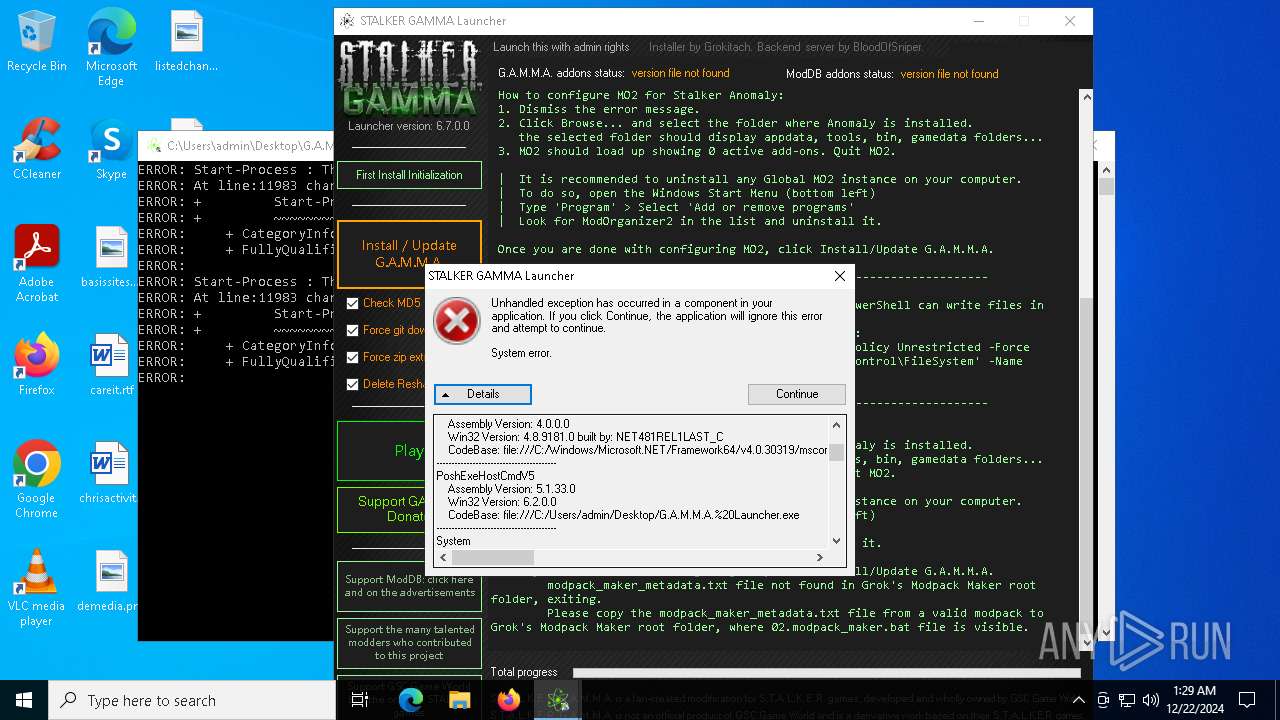
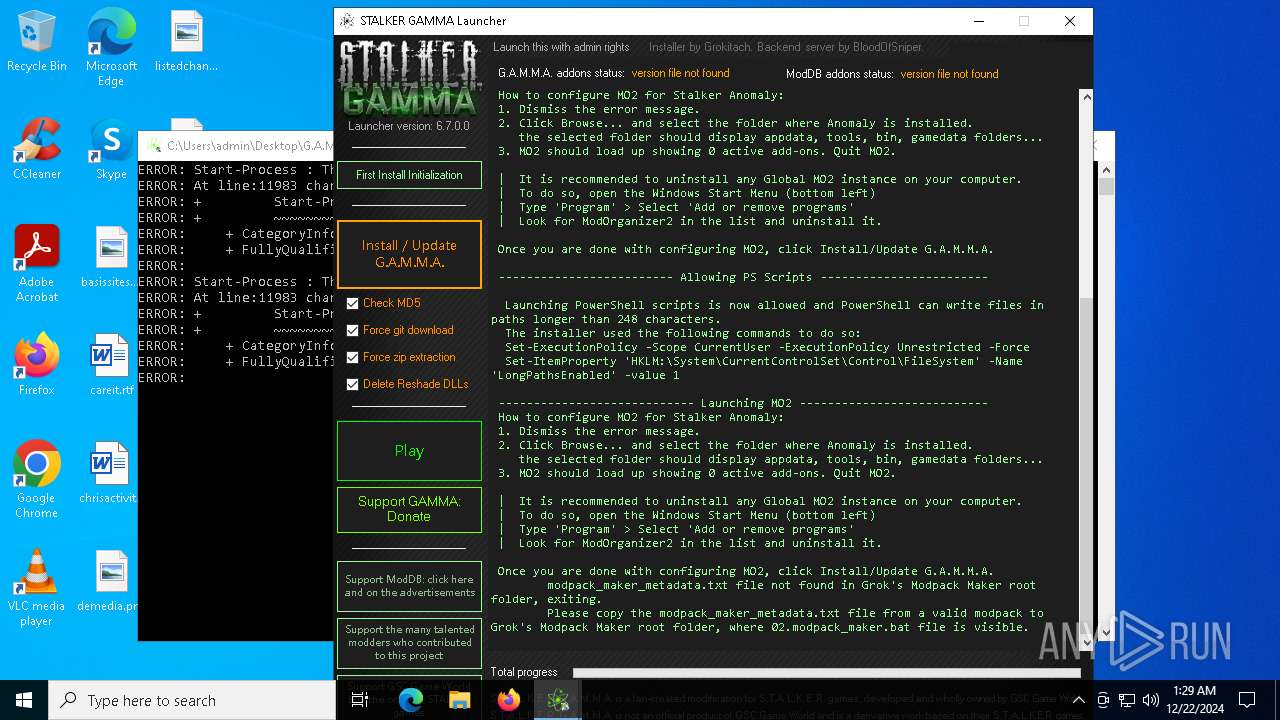
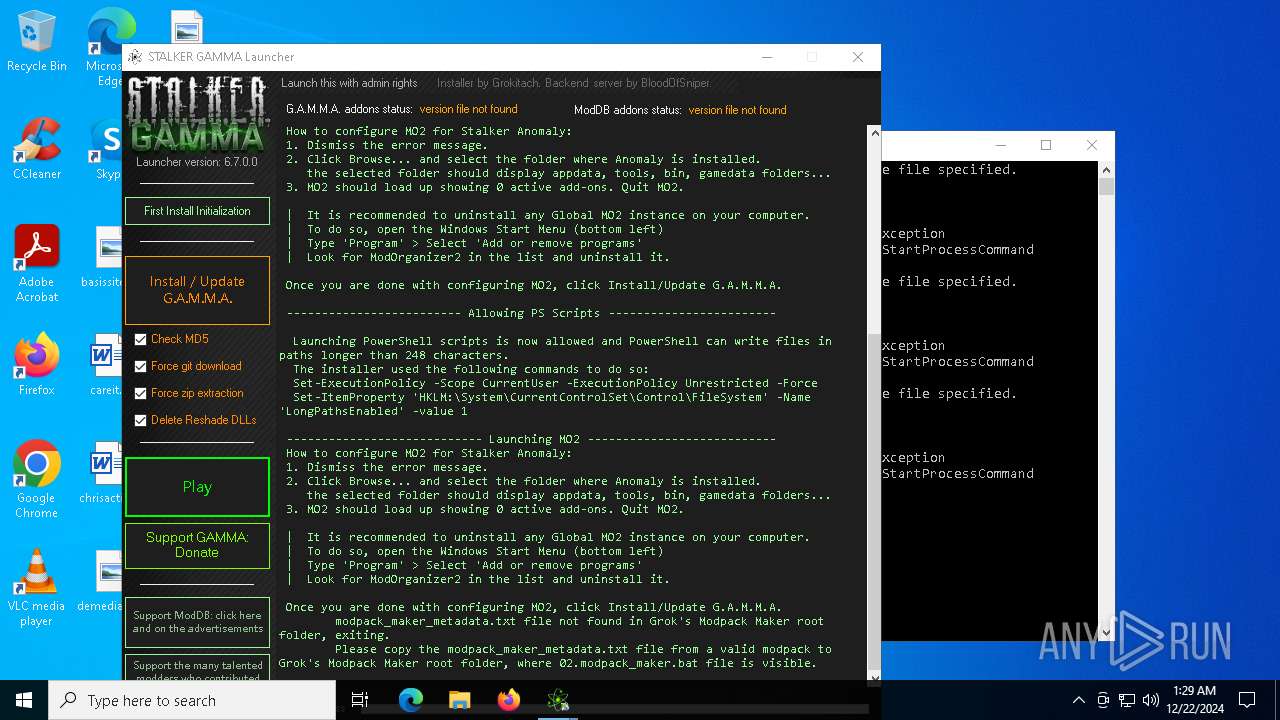
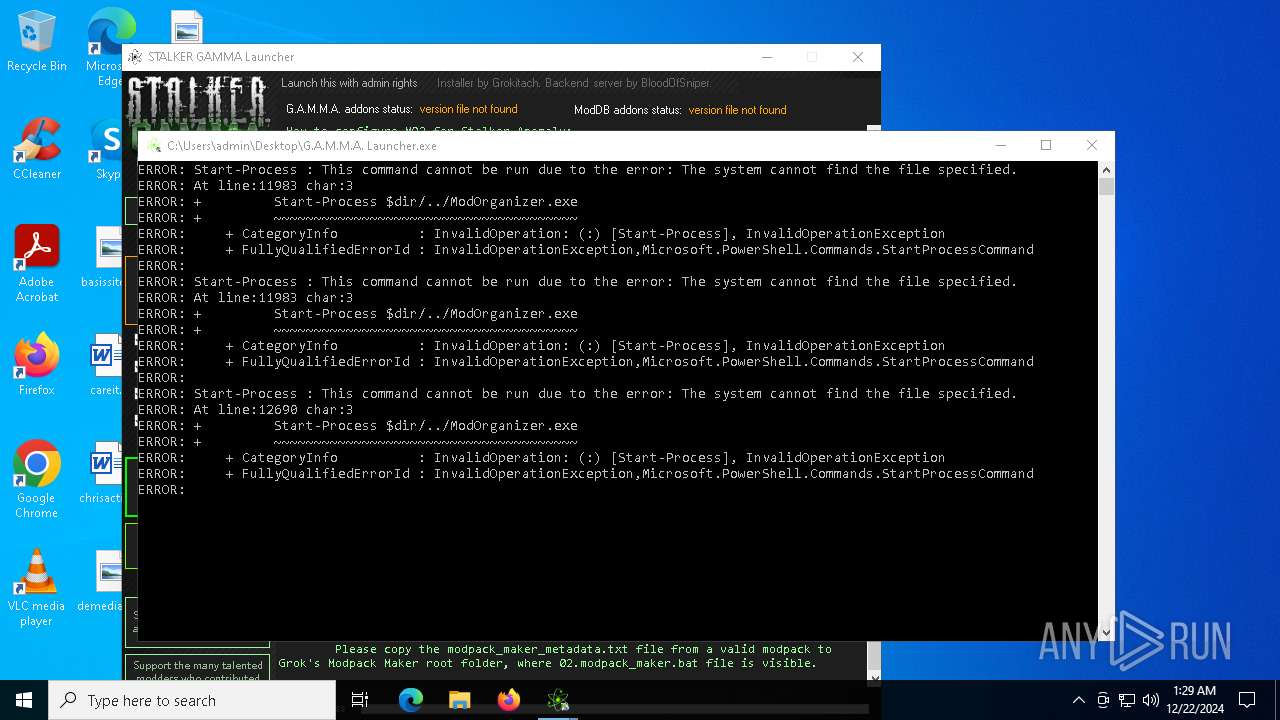
| File name: | G.A.M.M.A. Launcher.exe |
| Full analysis: | https://app.any.run/tasks/cc037a09-019d-4674-8b9a-ad8228271f5c |
| Verdict: | Malicious activity |
| Analysis date: | December 22, 2024, 01:28:09 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64 Mono/.Net assembly, for MS Windows, 2 sections |
| MD5: | FBFF014CC642DB966F0A834D3CD8D6F2 |
| SHA1: | CE1CB7296DCFCCE2DCFBE26D53541F6C7F03B177 |
| SHA256: | FD88DF850A57800B11438AB10EEC8B695EF8979817342EBA55A0D3E422D5677C |
| SSDEEP: | 98304:9PTs316Rk3VaIYQv46Be9k7Jy9HVFdCUkS25Fi33LVIdXYJD5MtnObgolKPT3W0s:Hwkl7k3gwyL9X |
MALICIOUS
Dynamically loads an assembly (POWERSHELL)
- G.A.M.M.A. Launcher.exe (PID: 6272)
Script downloads file (POWERSHELL)
- G.A.M.M.A. Launcher.exe (PID: 6272)
SUSPICIOUS
Reads security settings of Internet Explorer
- G.A.M.M.A. Launcher.exe (PID: 6272)
Checks Windows Trust Settings
- G.A.M.M.A. Launcher.exe (PID: 6272)
Uses base64 encoding (POWERSHELL)
- G.A.M.M.A. Launcher.exe (PID: 6272)
Gets content of a file (POWERSHELL)
- G.A.M.M.A. Launcher.exe (PID: 6272)
Gets or sets the security protocol (POWERSHELL)
- G.A.M.M.A. Launcher.exe (PID: 6272)
INFO
Reads the computer name
- G.A.M.M.A. Launcher.exe (PID: 6272)
Checks supported languages
- G.A.M.M.A. Launcher.exe (PID: 6272)
Reads Environment values
- G.A.M.M.A. Launcher.exe (PID: 6272)
Reads the machine GUID from the registry
- G.A.M.M.A. Launcher.exe (PID: 6272)
Create files in a temporary directory
- G.A.M.M.A. Launcher.exe (PID: 6272)
Checks whether the specified file exists (POWERSHELL)
- G.A.M.M.A. Launcher.exe (PID: 6272)
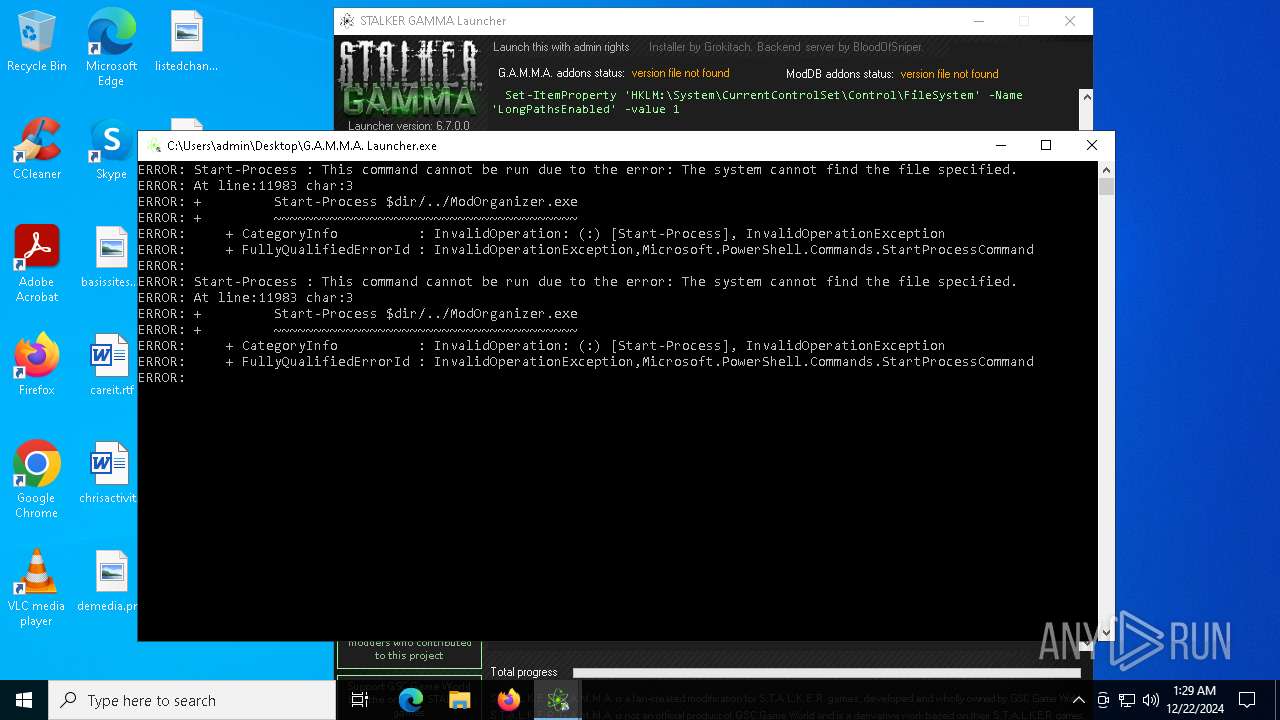
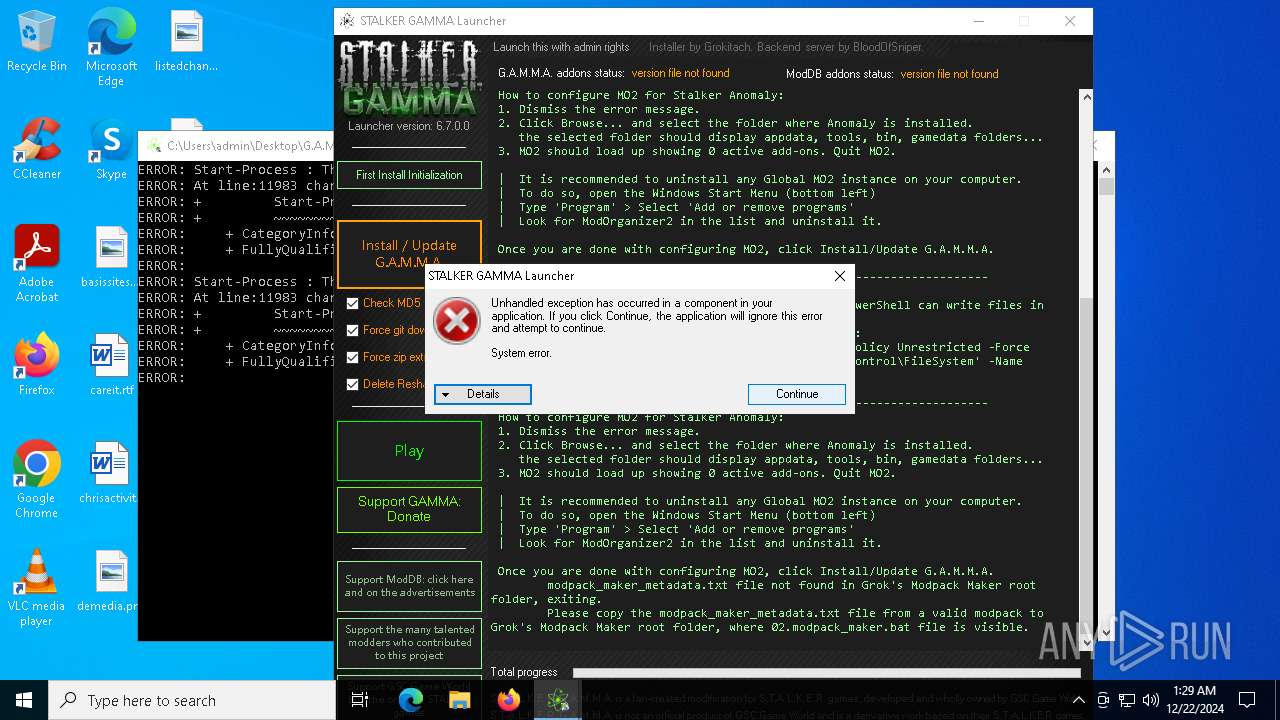
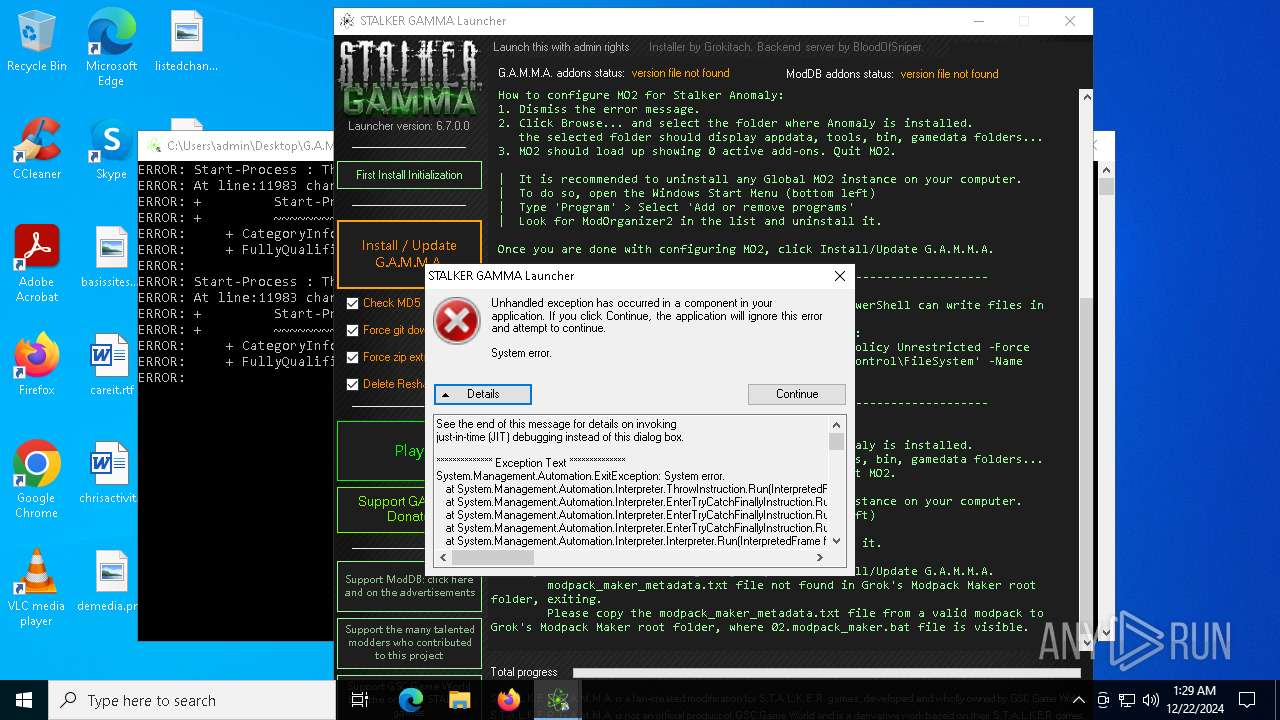
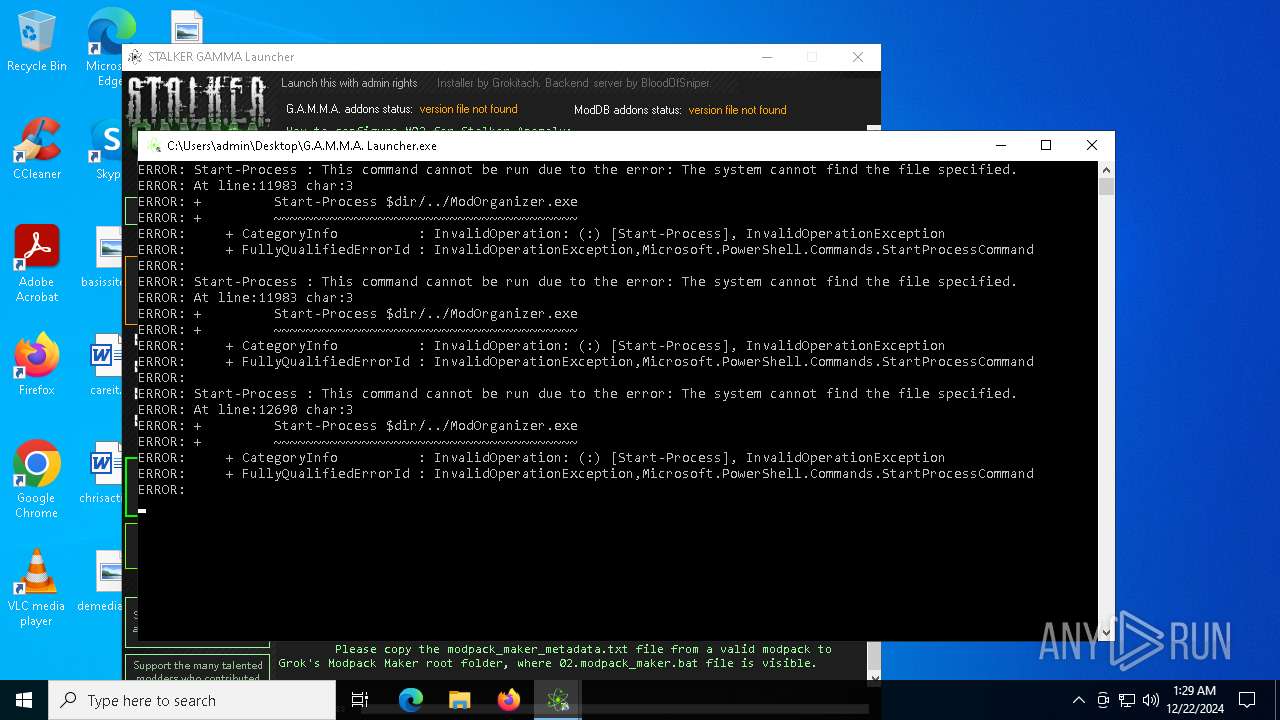
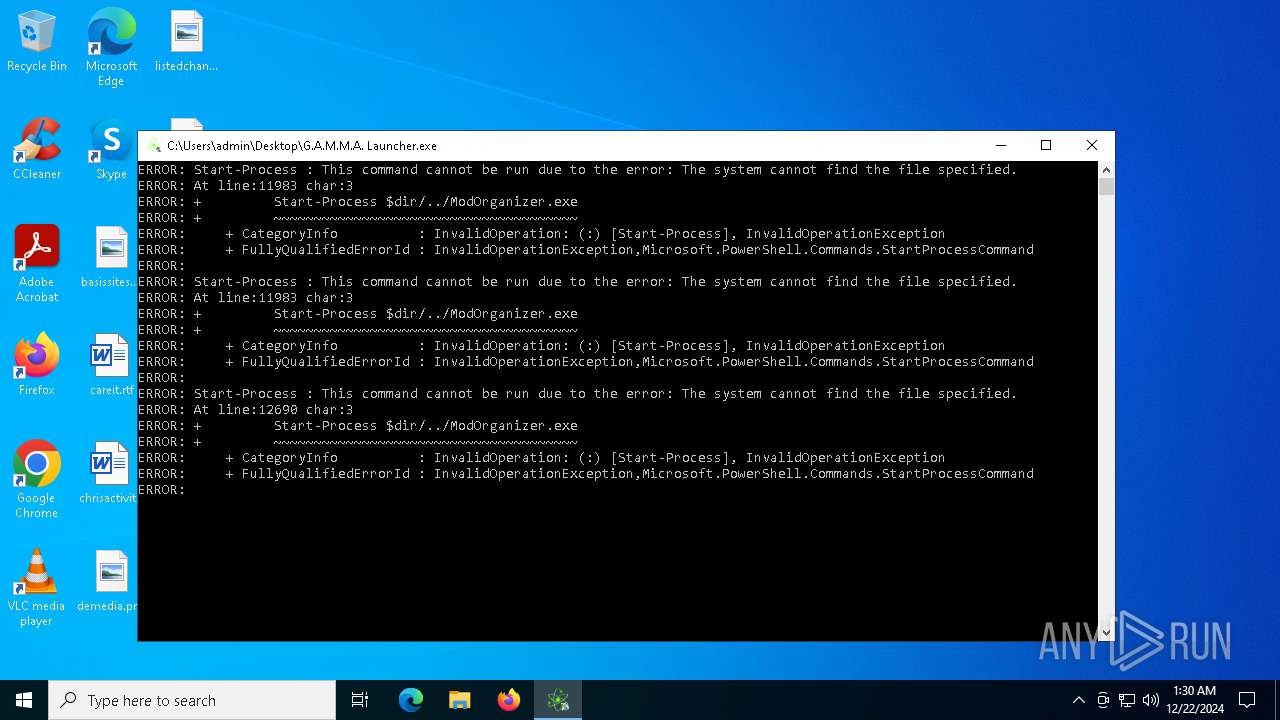
Script raised an exception (POWERSHELL)
- G.A.M.M.A. Launcher.exe (PID: 6272)
Found Base64 encoded reference to WMI classes (YARA)
- G.A.M.M.A. Launcher.exe (PID: 6272)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2018:01:02 05:53:16+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 8 |
| CodeSize: | 90112 |
| InitializedDataSize: | 3794944 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 6.2.0.0 |
| ProductVersionNumber: | 6.2.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
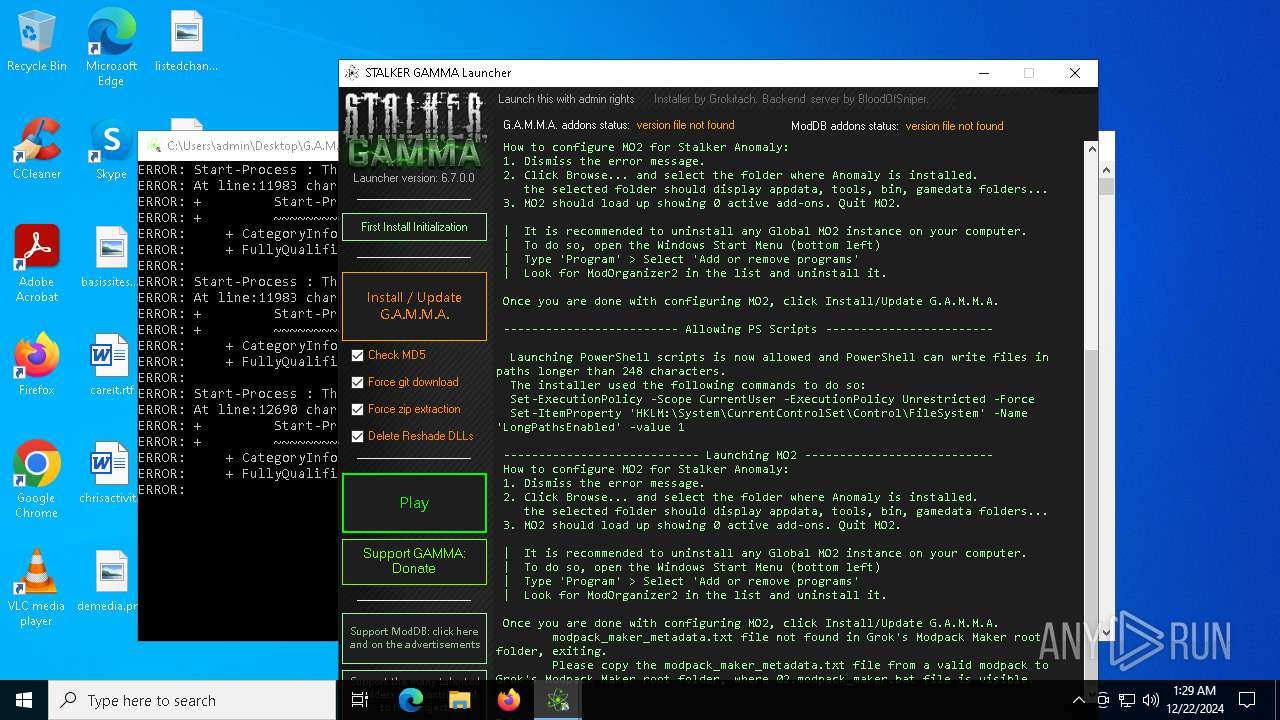
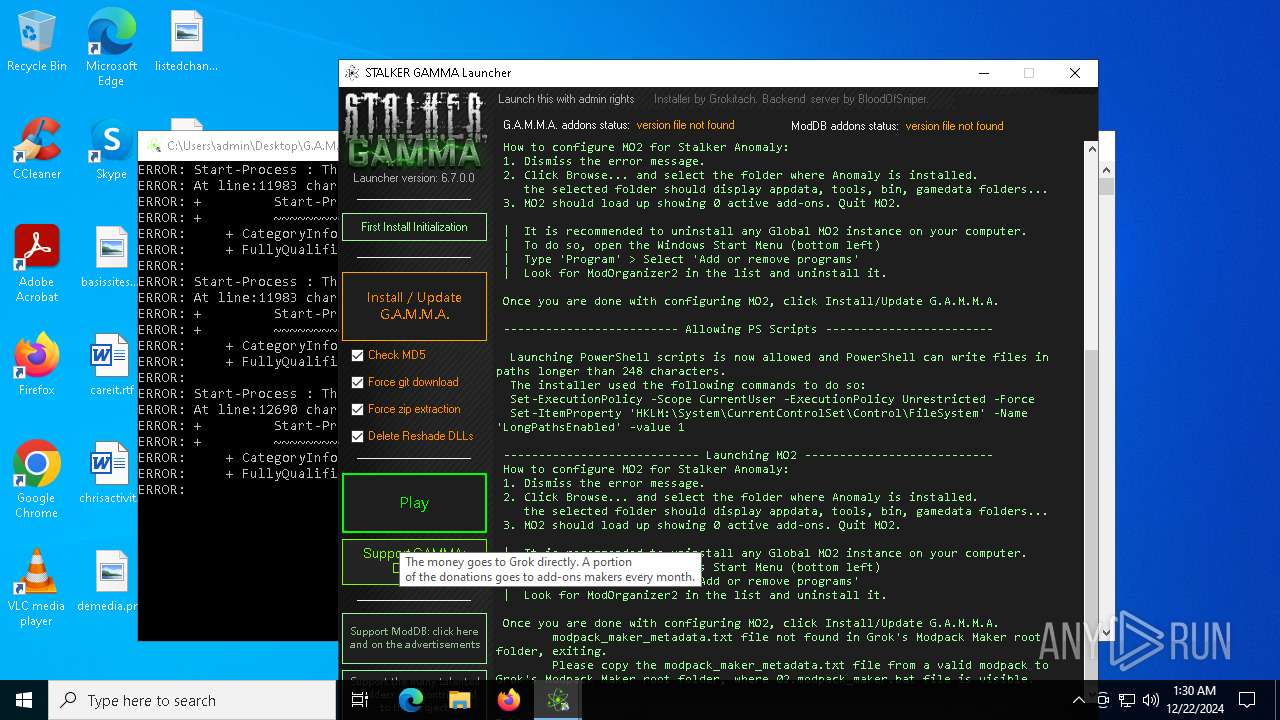
| FileDescription: | Downloads and installs a list of addons from moddb, to MO2 for STALKER Anomaly |
| FileVersion: | 6.2.0.0 |
| InternalName: | G.A.M.M.A. Launcher |
| LegalCopyright: | Copyright (c) 2022 All rights reserved |
| OriginalFileName: | G.A.M.M.A. Launcher |
| ProductVersion: | 6,2,0,0 |
| AssemblyVersion: | 5.1.33.0 |
| CompanyName: | STALKER GAMMA Team |
| ProductName: | G.A.M.M.A. Launcher |
| Comments: | - |
Total processes
131
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5576 | "C:\Users\admin\Desktop\G.A.M.M.A. Launcher.exe" | C:\Users\admin\Desktop\G.A.M.M.A. Launcher.exe | — | explorer.exe | |||||||||||
User: admin Company: STALKER GAMMA Team Integrity Level: MEDIUM Description: Downloads and installs a list of addons from moddb, to MO2 for STALKER Anomaly Exit code: 3221226540 Version: 6.2.0.0 Modules
| |||||||||||||||
| 6272 | "C:\Users\admin\Desktop\G.A.M.M.A. Launcher.exe" | C:\Users\admin\Desktop\G.A.M.M.A. Launcher.exe | explorer.exe | ||||||||||||
User: admin Company: STALKER GAMMA Team Integrity Level: HIGH Description: Downloads and installs a list of addons from moddb, to MO2 for STALKER Anomaly Exit code: 0 Version: 6.2.0.0 Modules
| |||||||||||||||
| 6304 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | G.A.M.M.A. Launcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 483
Read events
1 479
Write events
4
Delete events
0
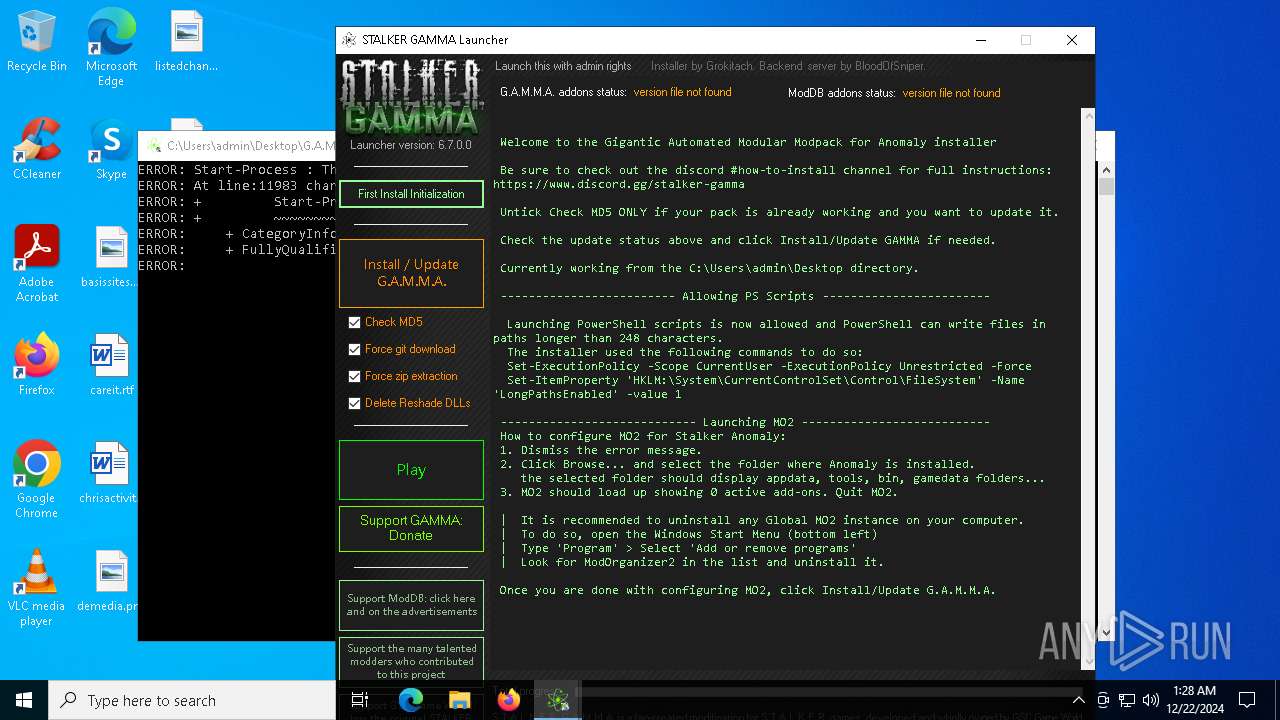
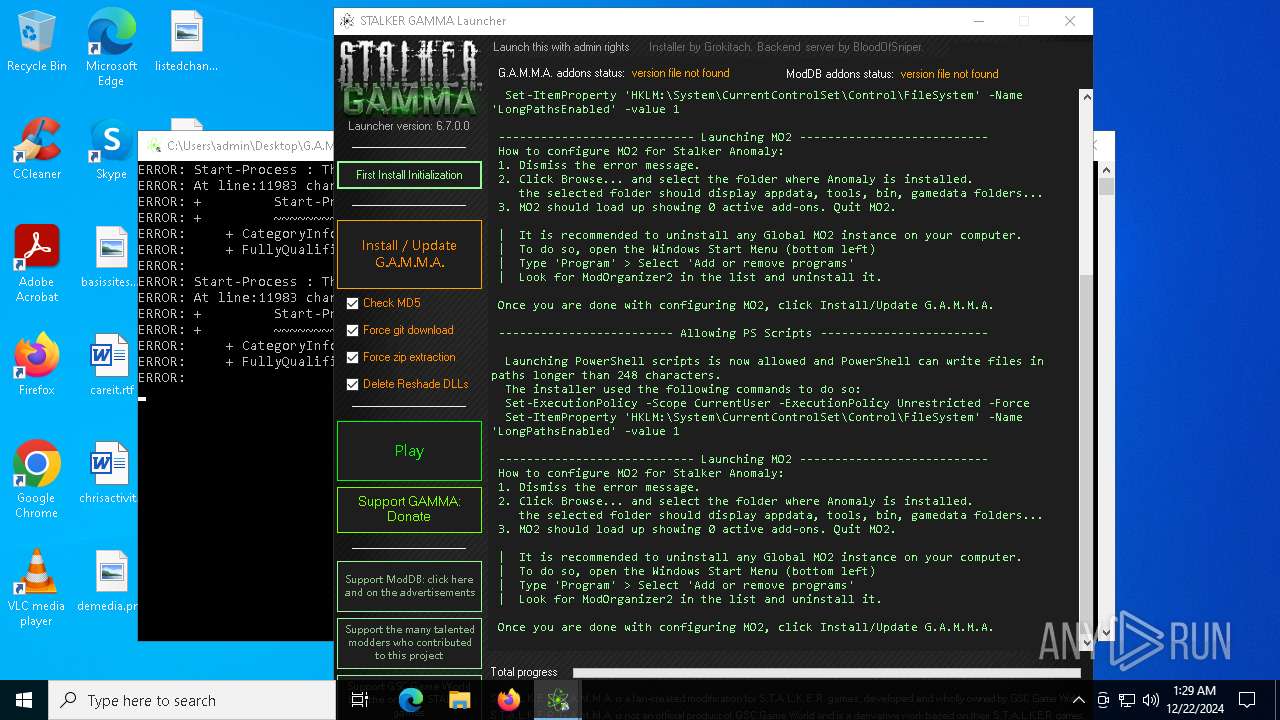
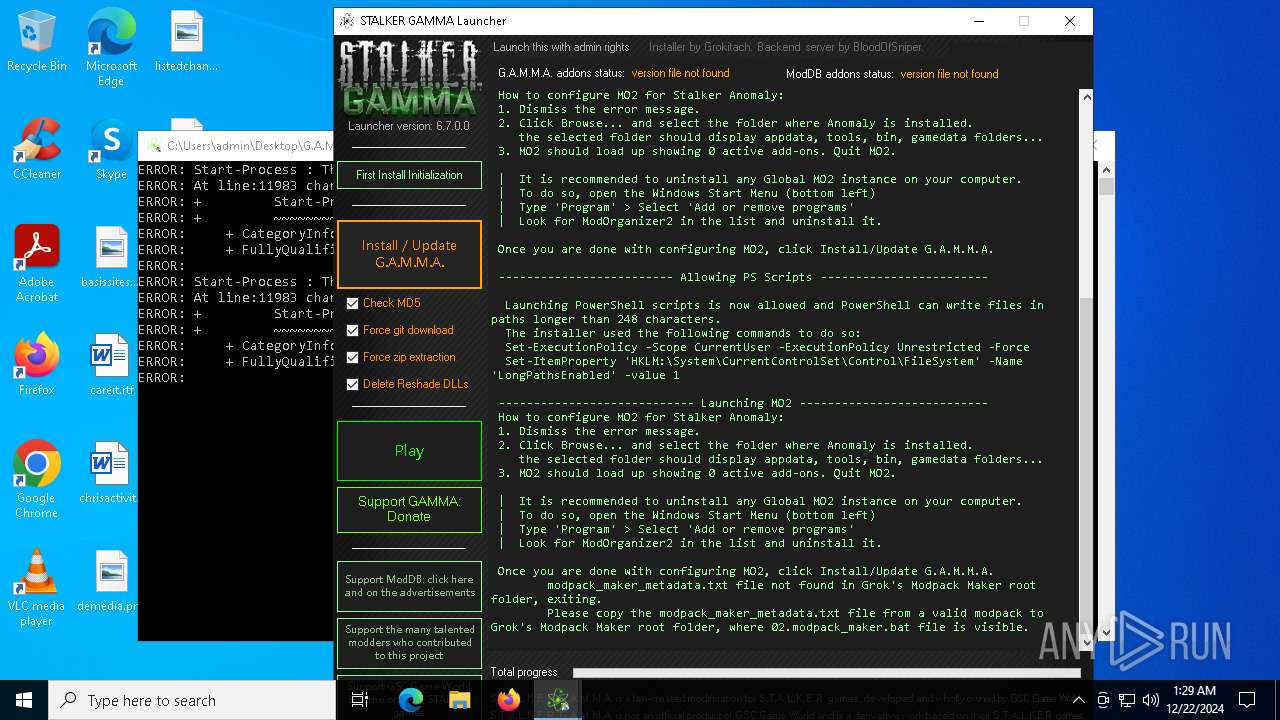
Modification events
| (PID) Process: | (6272) G.A.M.M.A. Launcher.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\PowerShell\1\ShellIds\Microsoft.PowerShell |
| Operation: | write | Name: | ExecutionPolicy |
Value: Unrestricted | |||
| (PID) Process: | (6272) G.A.M.M.A. Launcher.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\FileSystem |
| Operation: | write | Name: | LongPathsEnabled |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
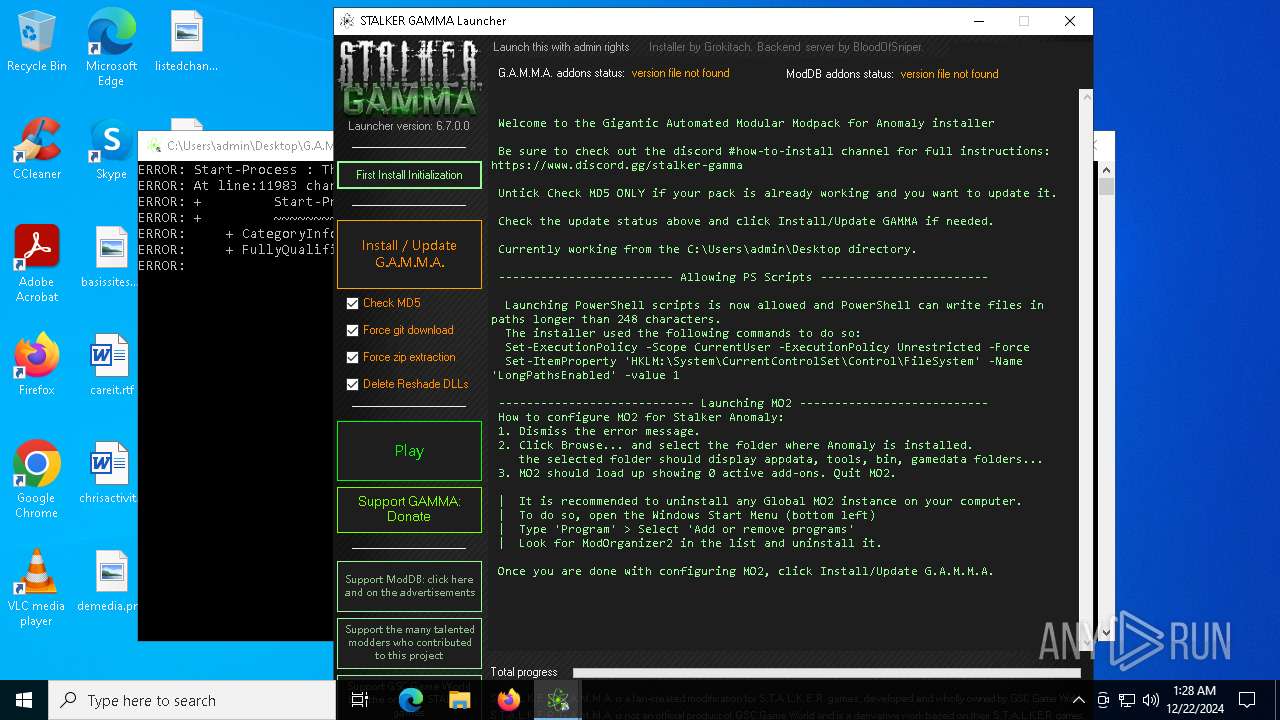
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6272 | G.A.M.M.A. Launcher.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ku4raxuf.eu0.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6272 | G.A.M.M.A. Launcher.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4aotv3uz.2cn.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
31
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
732 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
732 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7096 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7096 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6204 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
732 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
732 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.209.187:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |