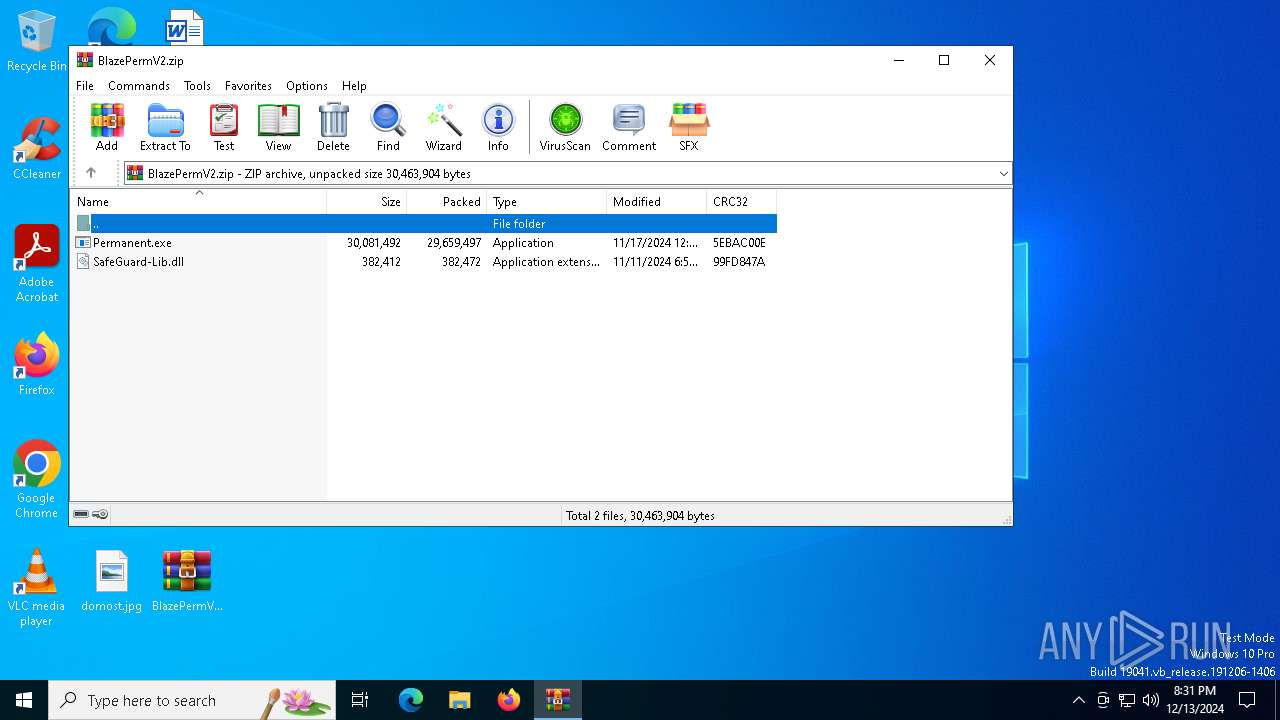
| File name: | BlazePermV2.zip |
| Full analysis: | https://app.any.run/tasks/a145fa41-900d-48d7-8d0e-a43ac829d0b7 |
| Verdict: | Malicious activity |
| Analysis date: | December 13, 2024, 20:30:34 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | EFDAAC12A5CAAB60E991B46FC1E33EFD |
| SHA1: | 4DFB2BCC91AF977A2AB4162E495186384C35E98D |
| SHA256: | FD881ED5183A73BBA8B2251EC0A621105D96B01E1534203C4B66675C3775C63B |
| SSDEEP: | 196608:Pj/ajTxMI3Dwnj42IMqk2PKdbU35zyIzwvMT0JfX+DyMLpXiBO6gw1FlUZ9NCY2+:Pcd1ij42Is5435zfkWwfXGLpXeT1I8G |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 3508)
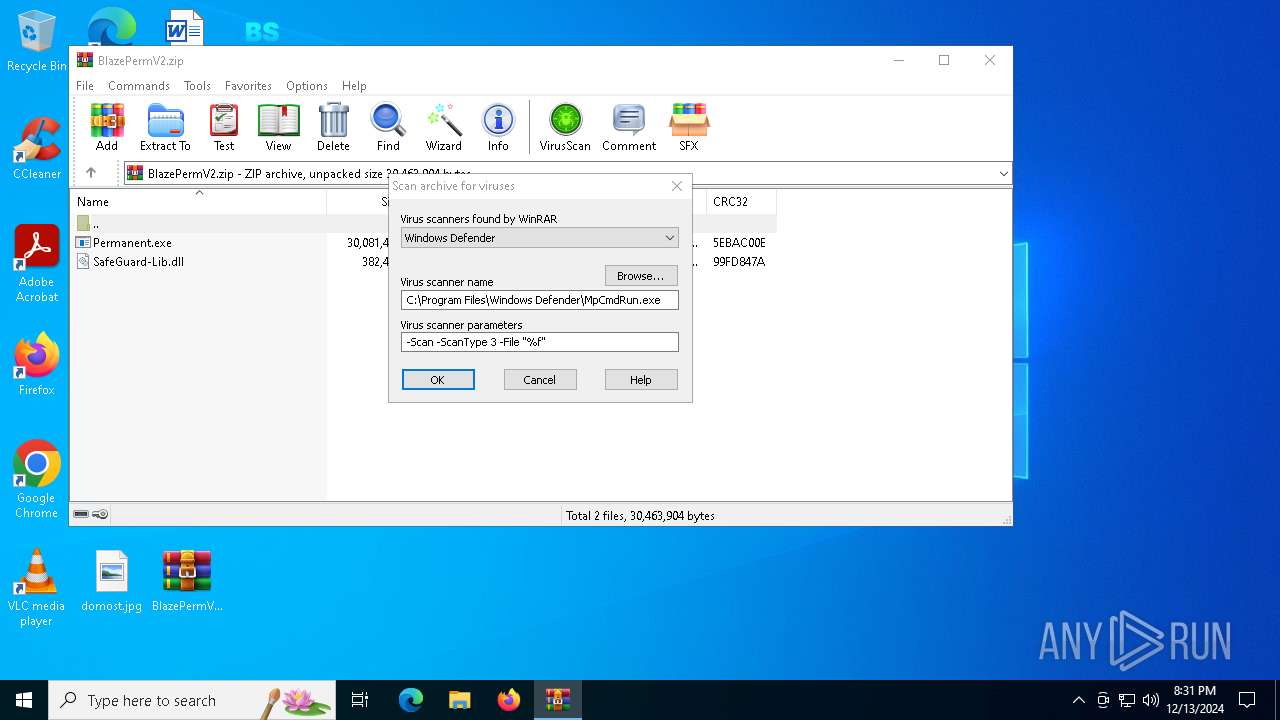
Antivirus name has been found in the command line (generic signature)
- MpCmdRun.exe (PID: 5556)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3508)
Executing commands from a ".bat" file
- WinRAR.exe (PID: 3508)
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 3508)
INFO
Manual execution by a user
- Permanent.exe (PID: 3680)
Reads the computer name
- Permanent.exe (PID: 3680)
- MpCmdRun.exe (PID: 5556)
Checks supported languages
- Permanent.exe (PID: 3680)
- MpCmdRun.exe (PID: 5556)
Create files in a temporary directory
- Permanent.exe (PID: 3680)
- MpCmdRun.exe (PID: 5556)
The process uses the downloaded file
- WinRAR.exe (PID: 3508)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:11:17 13:00:06 |
| ZipCRC: | 0x5ebac00e |
| ZipCompressedSize: | 29659497 |
| ZipUncompressedSize: | 30081492 |
| ZipFileName: | Permanent.exe |
Total processes
121
Monitored processes
6
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 716 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$VR3508.18621\Rar$Scan14957.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Permanent.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2796 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3508 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\BlazePermV2.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 3680 | "C:\Users\admin\Desktop\Permanent.exe" | C:\Users\admin\Desktop\Permanent.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
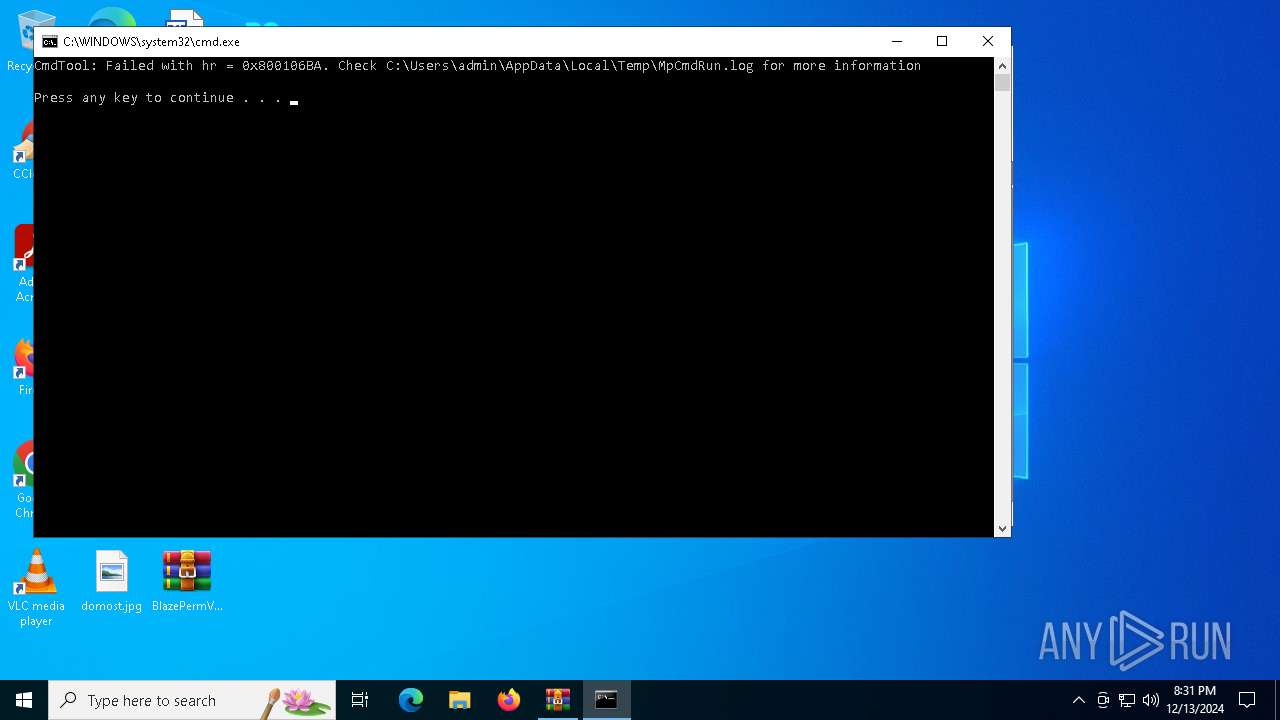
| 5556 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -ScanType 3 -File "C:\Users\admin\AppData\Local\Temp\Rar$VR3508.18621" | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 629
Read events
1 620
Write events
9
Delete events
0
Modification events
| (PID) Process: | (3508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\BlazePermV2.zip | |||
| (PID) Process: | (3508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\VirusScan |
| Operation: | write | Name: | DefScanner |
Value: Windows Defender | |||
Executable files
1
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3508 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR3508.18621\BlazePermV2.zip\SafeGuard-Lib.dll | binary | |
MD5:C8488DFFF4AB22247D99D30BD788F14B | SHA256:4CA168D4B2678F4C83D7A8467AFE91A78D24F63CA90AE3C9C44BB647032E135D | |||
| 3508 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR3508.18621\Rar$Scan14957.bat | text | |
MD5:D8BB1FF842AD43BCD80C08A690D63AE5 | SHA256:CC1F23DD213C63D11C75E4A3140359B4B437722F27640A9C051292160FED76D7 | |||
| 3508 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR3508.18621\BlazePermV2.zip\Permanent.exe | executable | |
MD5:A8EA20E52B270A5BBBBD147D11E76F57 | SHA256:6B62E76DAC003555C1D9F4852CDEC2E1680939262DCF492C95E78FD7CAD39F54 | |||
| 5556 | MpCmdRun.exe | C:\Users\admin\AppData\Local\Temp\MpCmdRun.log | text | |
MD5:24AAD5BF8209C0EA5FDF46DE8F40F653 | SHA256:BE78E7FE25FCA74CBD5122892A3FB262436578783B46071F87A86532AC6BDA6D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
19
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.24.77.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6060 | svchost.exe | GET | 200 | 184.24.77.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6060 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6060 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6060 | svchost.exe | 184.24.77.35:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.24.77.35:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6060 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3976 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |