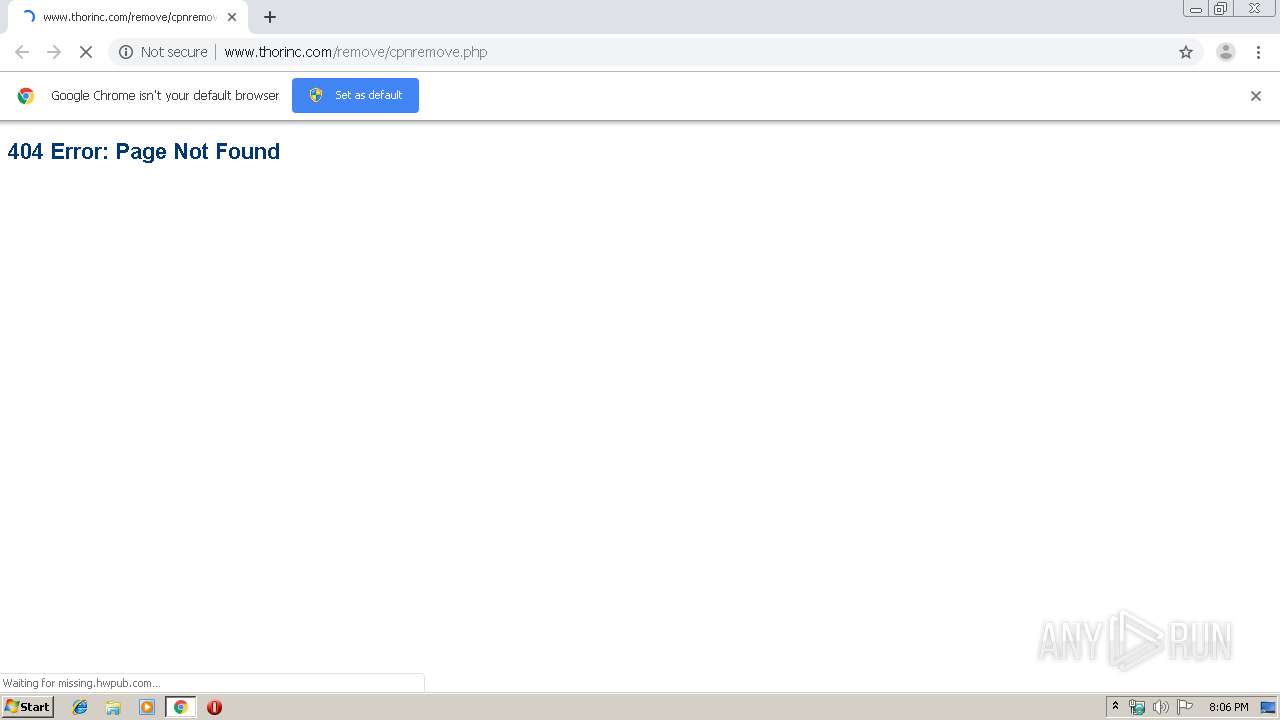
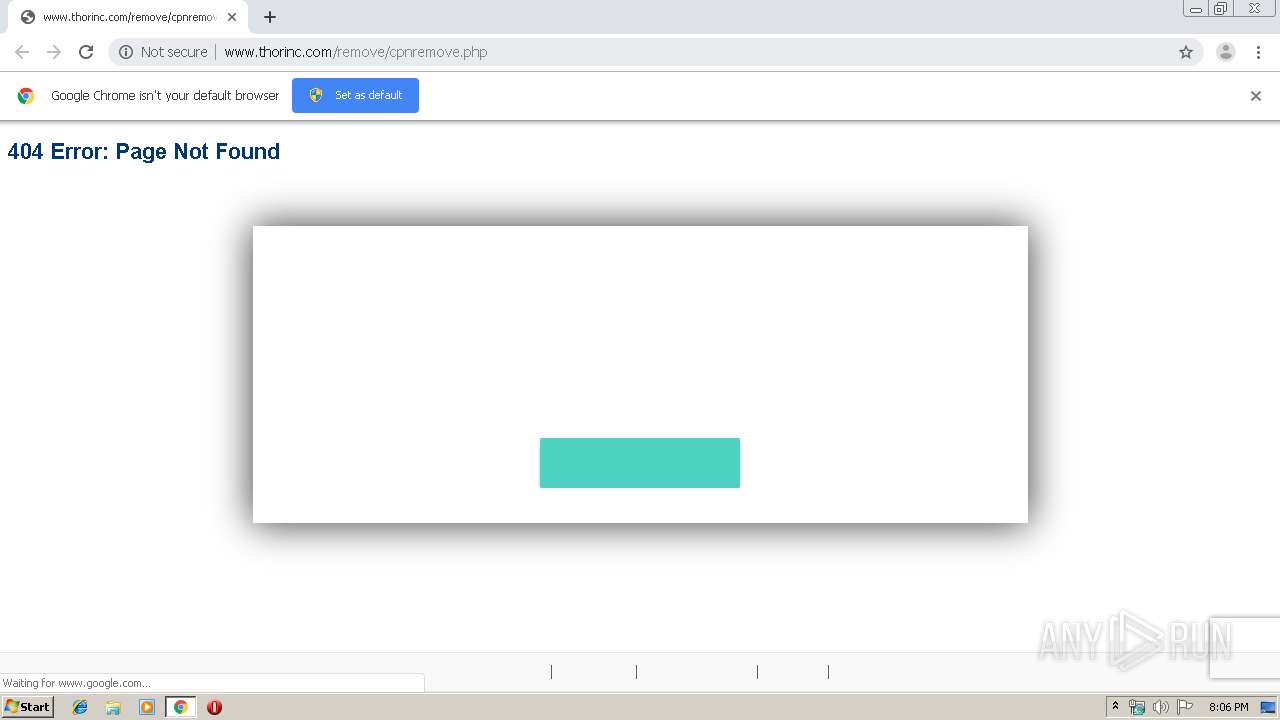
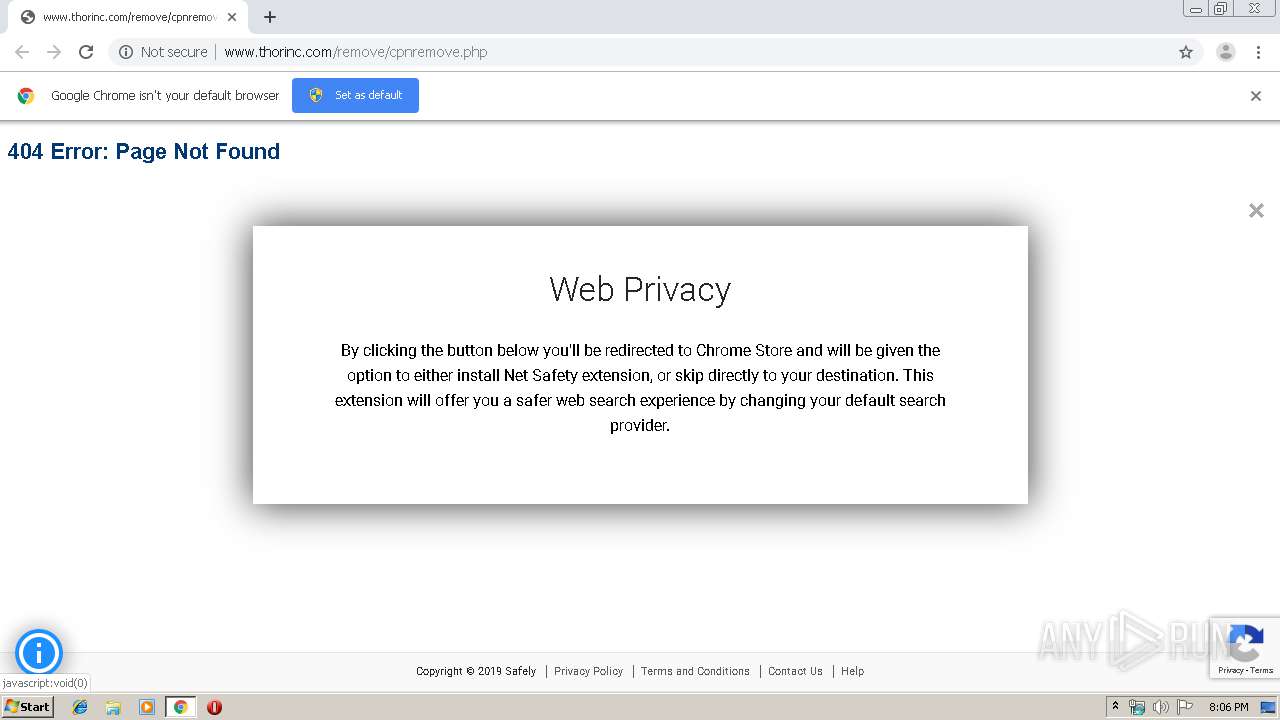
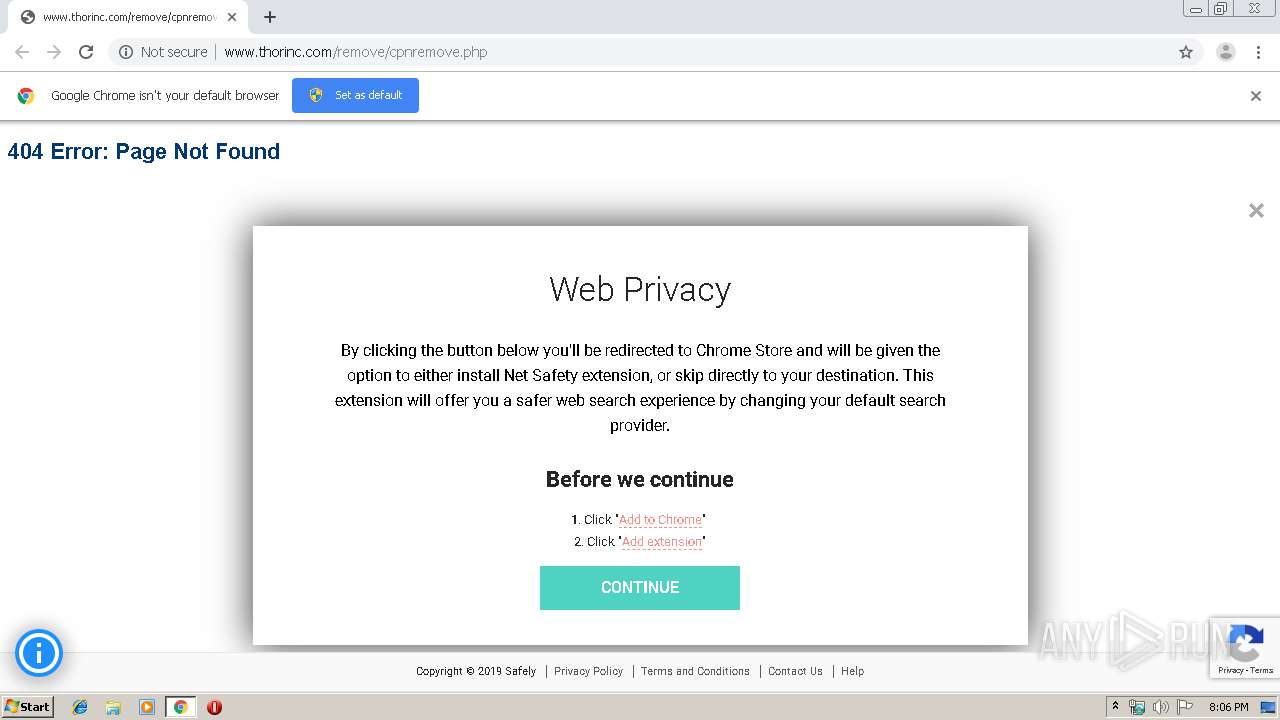
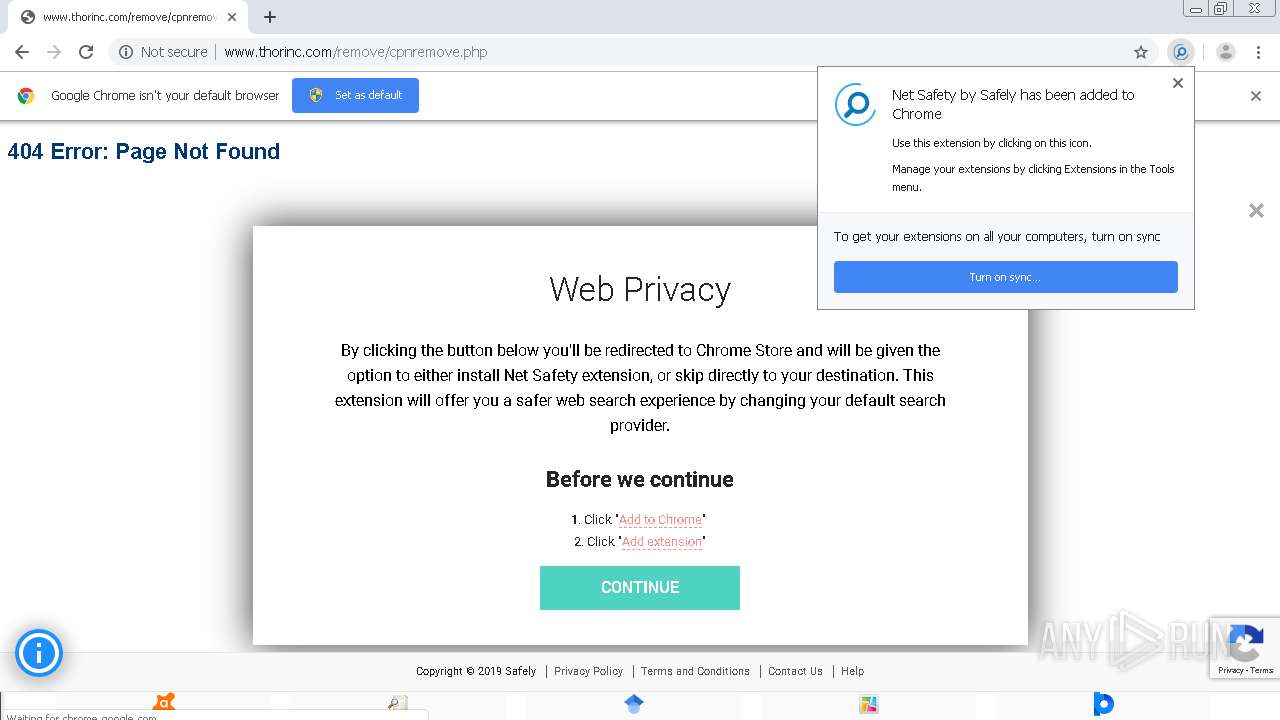
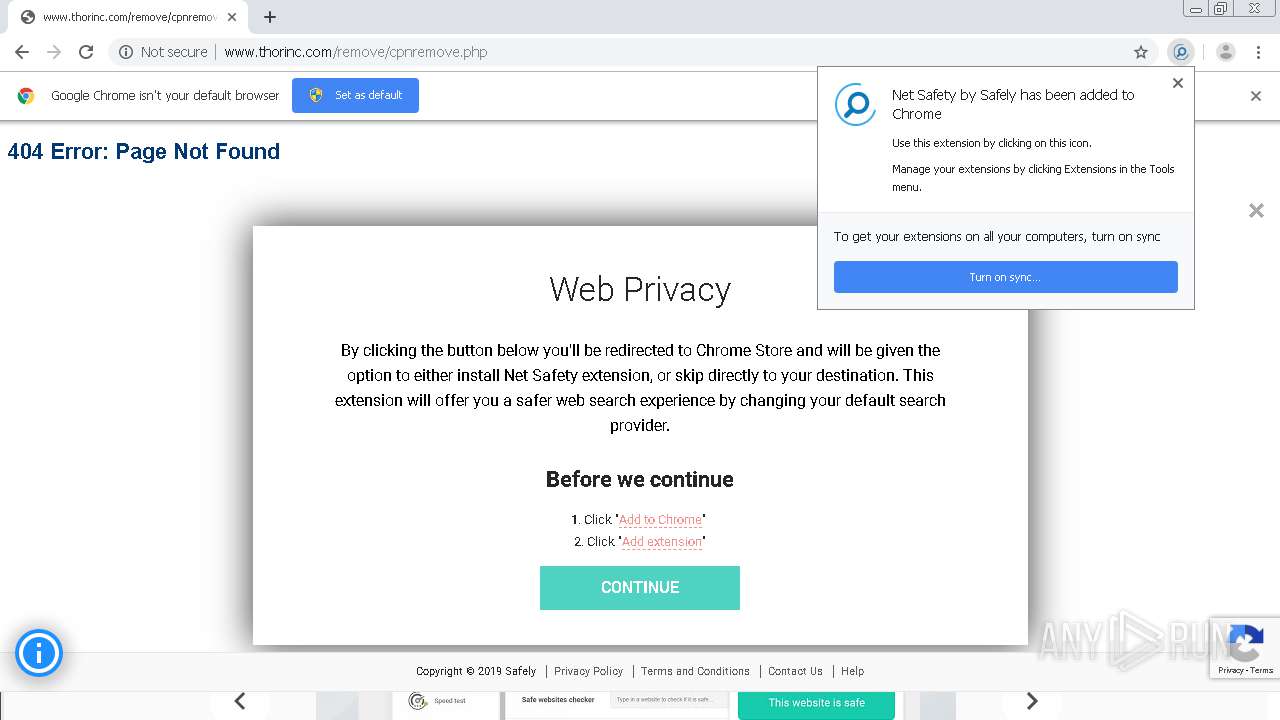
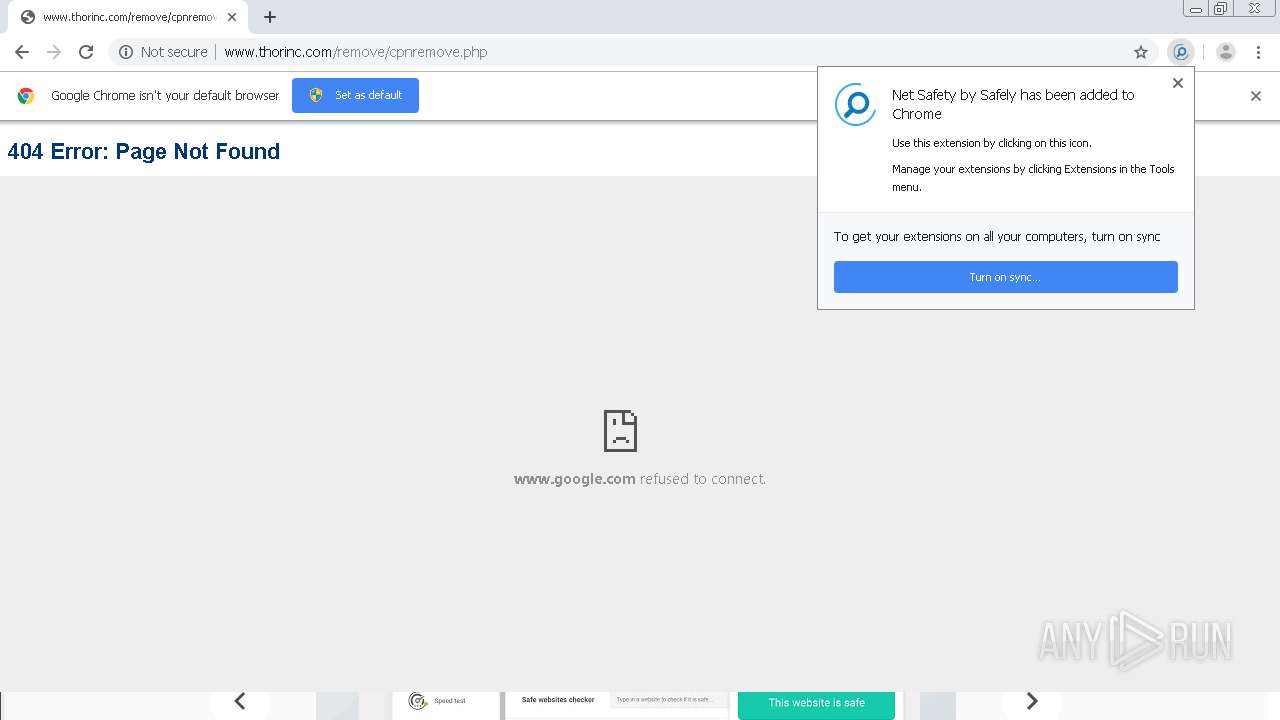
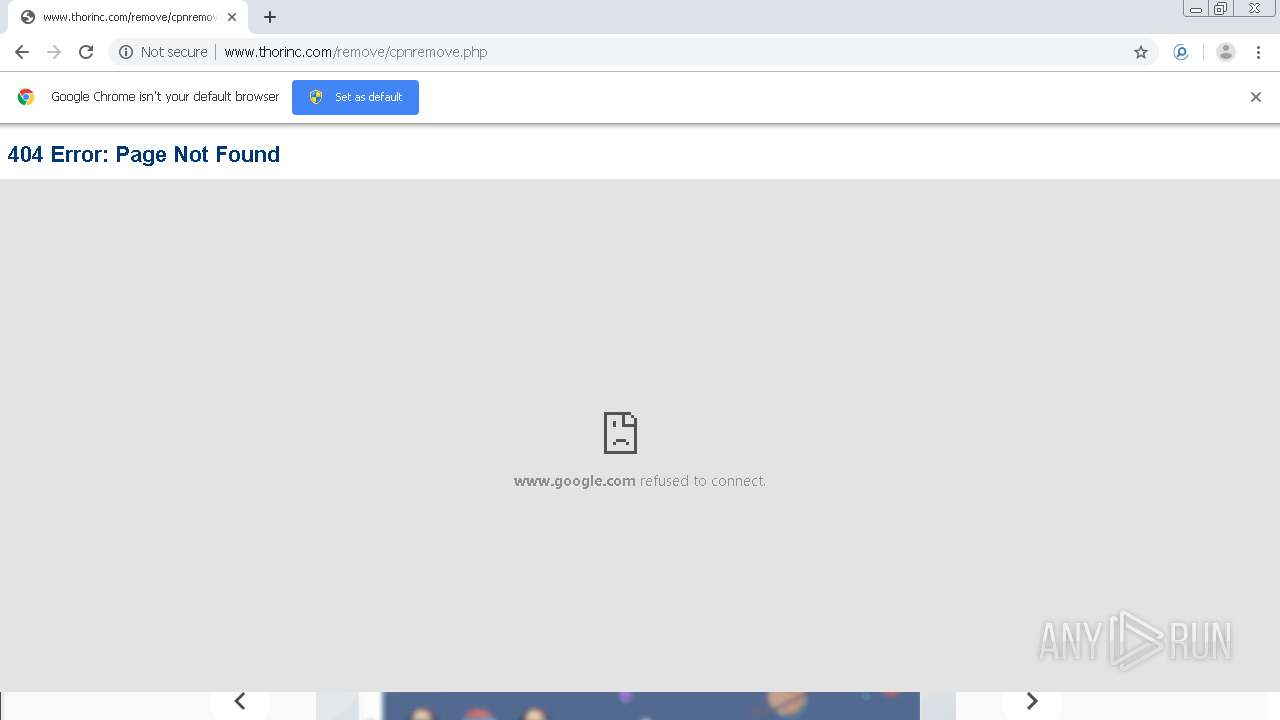
| URL: | http://www.thorinc.com/remove/cpnremove.php |
| Full analysis: | https://app.any.run/tasks/fb7c2a38-a78a-4a3d-8a43-4d2db98c2ac5 |
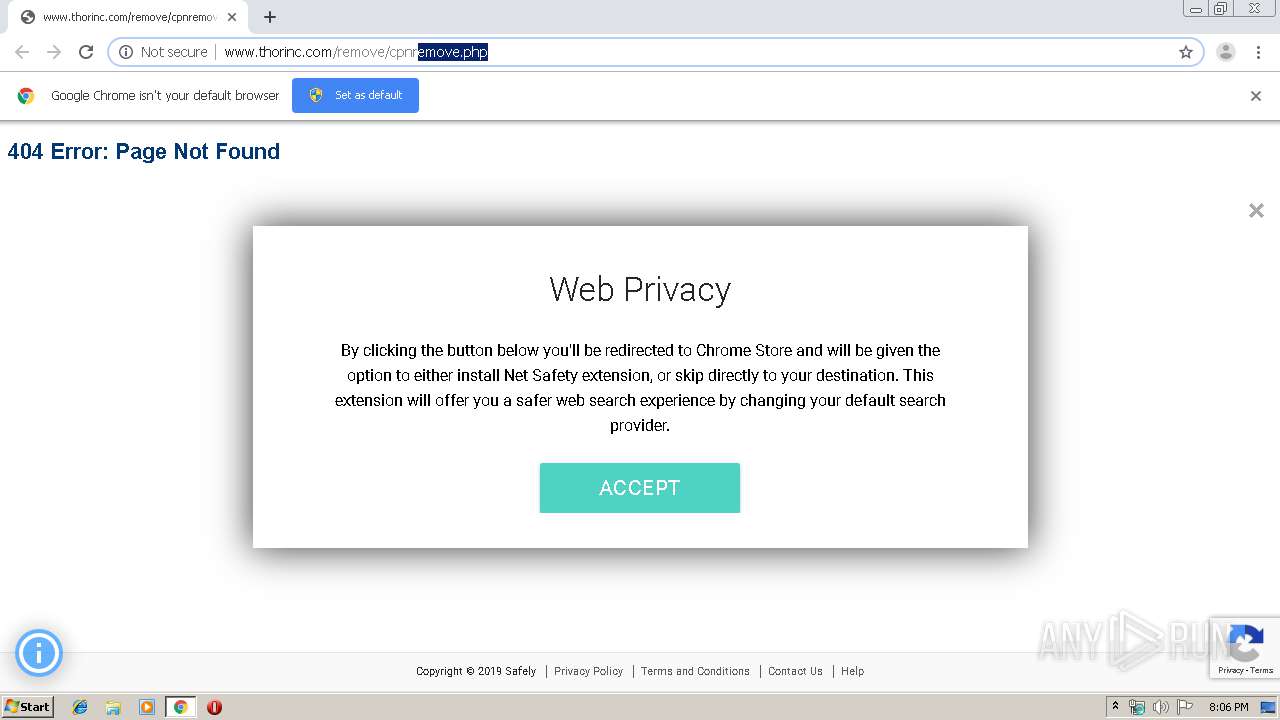
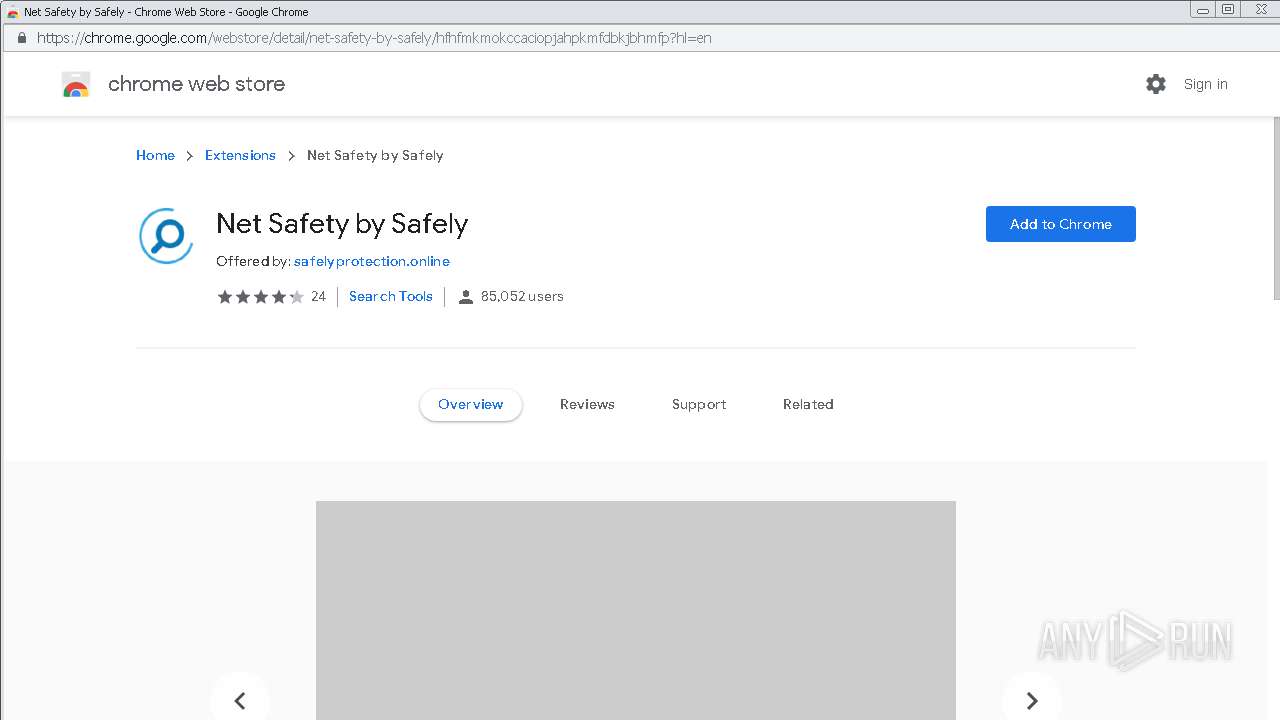
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 19:06:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F2F05E7FB3492CB3971DF815509F7C9E |
| SHA1: | 9D48C6867723DF5FBFF17B2F5DC31FDED01026B6 |
| SHA256: | FD86EDF6531531DC2ECC3E03B2E586E8346E45A86020D85929984C828201084C |
| SSDEEP: | 3:N1KJS4etLd4MX02n:Cc4ULiGd |
MALICIOUS
No malicious indicators.SUSPICIOUS
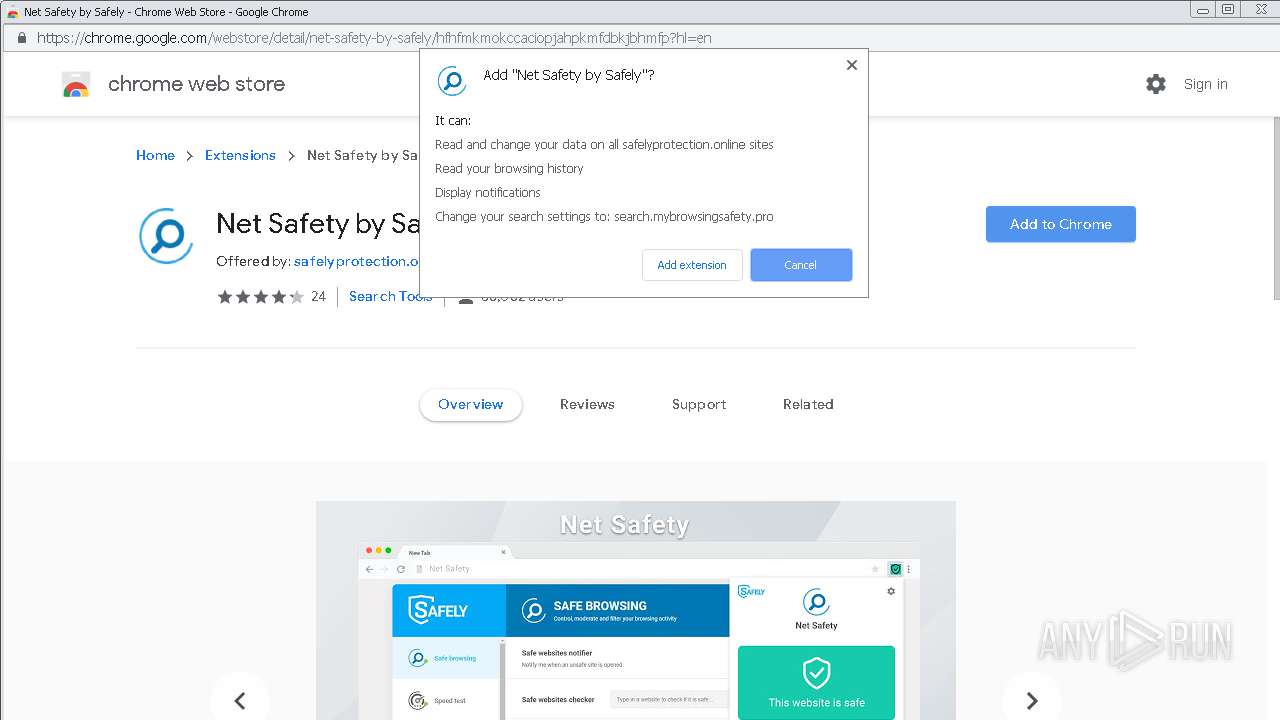
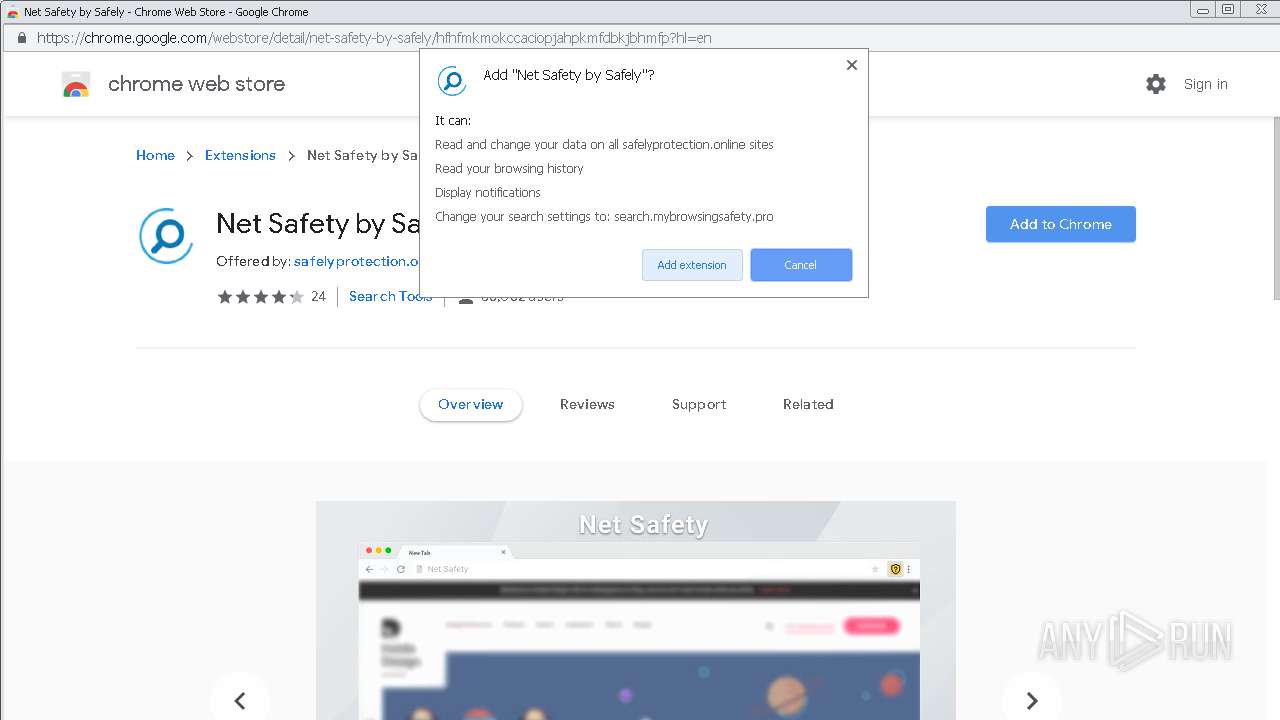
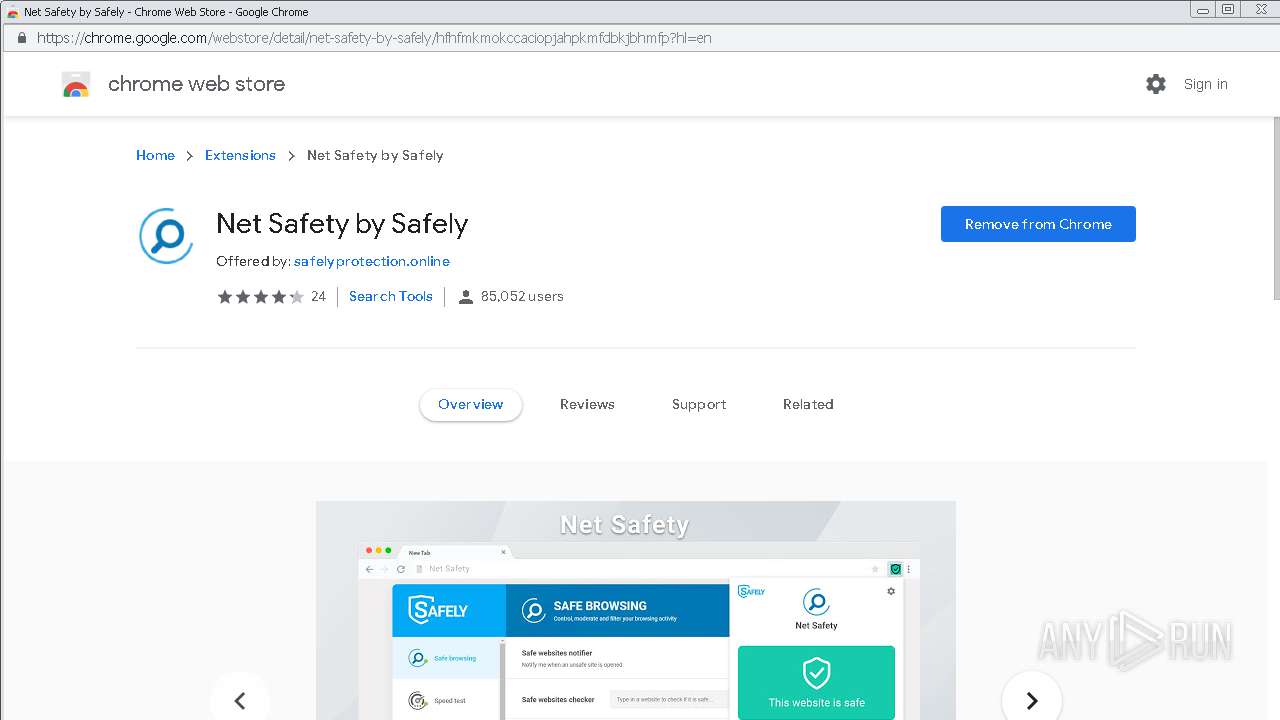
Modifies files in Chrome extension folder
- chrome.exe (PID: 2580)
INFO
Reads the hosts file
- chrome.exe (PID: 2580)
- chrome.exe (PID: 1796)
Application launched itself
- chrome.exe (PID: 2580)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2580)
Reads Internet Cache Settings
- chrome.exe (PID: 2580)
Reads settings of System Certificates
- chrome.exe (PID: 1796)
Creates files in the user directory
- chrome.exe (PID: 2580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
78
Monitored processes
43
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,8884800729120744698,16136946106396241878,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16020182886016189942 --mojo-platform-channel-handle=4492 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,8884800729120744698,16136946106396241878,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13959149827733281951 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3404 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,8884800729120744698,16136946106396241878,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7021252453963882850 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2468 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,8884800729120744698,16136946106396241878,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9694659871785003565 --mojo-platform-channel-handle=4288 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,8884800729120744698,16136946106396241878,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2435971699898480877 --mojo-platform-channel-handle=2836 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,8884800729120744698,16136946106396241878,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12741565741013536632 --mojo-platform-channel-handle=4888 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,8884800729120744698,16136946106396241878,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18342308145586136931 --mojo-platform-channel-handle=2916 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,8884800729120744698,16136946106396241878,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10940696764284637028 --mojo-platform-channel-handle=2068 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,8884800729120744698,16136946106396241878,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12865636025891865947 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,8884800729120744698,16136946106396241878,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18255672304818191855 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3200 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
755
Read events
623
Write events
126
Delete events
6
Modification events
| (PID) Process: | (2064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2580-13215553599699500 |
Value: 259 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
45
Text files
206
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1430fed1-8950-4869-8fcf-86e78616a847.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a5c0.TMP | text | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39a5fe.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
82
DNS requests
44
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
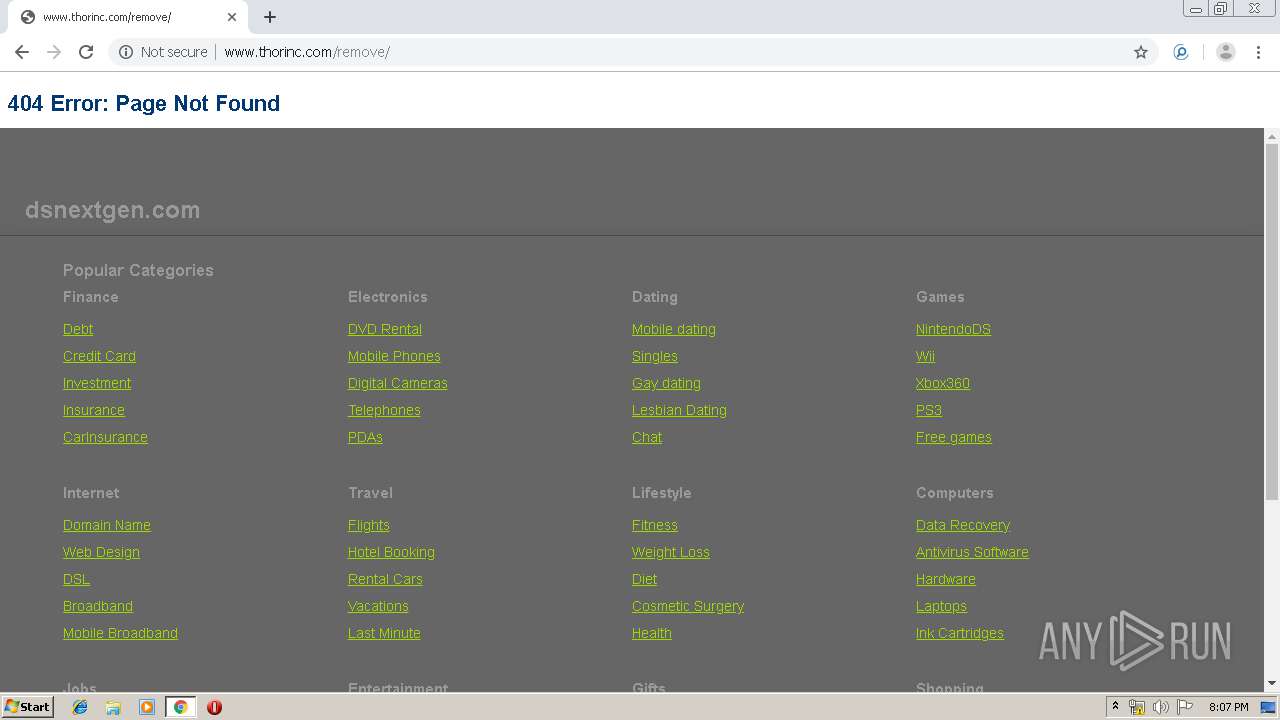
1796 | chrome.exe | GET | 302 | 91.195.240.136:80 | http://ww1.dsnextgen.com/search/tcerider.php?f=http%3A%2F%2Fforwrdnow.com%2FaS%2Ffeedclick%3Fs%3DN96qfziHQqR1ciMM9brhsSdsBF_uyqHoXdKpm_iE5krdhoJao1-3Qp1B-kb1vwChg2RvEwrk2epbC7U30TJp2WvoICO3pAFB-9ayILa_jmcWRUYpqyAbUfbBAycg447jGj5CCziVxGvhd-BnC8BekWeukOm6WVEECf2oHXffqu71a0YWJmhCJv9Za4ILVqu53eldyEAwy2Rnr1HRloN17azqNkSZ4MP9vulPRUFeAVwG2Du9JEbwYUDM2w0Cs7SSUy9cmJ4sC0SD43xSpehqYhTLJukT4HX33_sEEIcFZ2Wrtl55W9s6IXMC36MOV9Q69Ozk3Rv2P2Z9WHTN2jN6lvuQt-XSQxhwu-Vn6P0Pc8CD5cigUmAzks1URkm10xRKUJYhDADFGSiqNZHnb0rUW1Xp4dJh_CuyqooSm0JQumhiqnPRglMnxOF7FOlSMsjaHosHnVPI9MmTONUgmEsT9BI6tuMRurl75e6A6czmb7wXusqaFnoxlbxiZoo5y7X8IerNKT4pGDupvY895NyWiNeY_JnsouBr9mn05_3sEJ-M43HctUWGfKT6Ifj6CGUXDd6khgw1xizex3btw87HaAp4fFE_zlx7_Kbc8xtuWKx-wwWZE6djSweIx6tRiLMQVrpRduPoD8AQvEzNJDopS07PspS4ce5ISOXwdJJoXhB-Pc0hDBUuM2GKtkyD3Tx4udjCRaoEDDMRWioH9gEvvWS7NIXugPuUVuX8DBYjjollq5JkCl20SXmUCkx-zzZDLlehVd0497npJxJVhoqb5XKtzZZF_NnTF_8zc5Ey_xAVNSbP4L6VxJxgJknSkiei-Enx24tEQ5CLEdKV0ZSi2nUAqCEfRpfP6ScSVYaKm-UBLMcmL5Iv0FRdfOSQMJ-KyQmel9ltqNomDW_olsHQNA&v=YmY3MGM3MTQxY2UzNjc2MzljZjYxNGUxMjY3Yjg1ZmQJMQl3dzEuZHNuZXh0Z2VuLmNvbTVkYTRjNzQyZWQ0ZTAzLjUxNTE4NzM0CXd3MS5kc25leHRnZW4uY29tNWRhNGM3NDJlZDUzYTYuMDQxNjYwNTUJMTU3MTA4MDAwMwlhZF81Ml8w&l=NglBRFMJNTA0Y2Y5MTM1NGRkNDFhODdjYzgwNzY5MjQ2ODBhOTYJMAkxMwkJMzEJMQkxCTAJYWZhYjVjYjg0MzFmOWFiN2Y1ZGVhNzRhMzNjMjk0NDQJCTMzNTgyNTA4NgljCTAJCWRzbmV4dGdlbgkxMTAxCTUyCTQJMwkxNTcxMDgwMDAzCTAuMDM3NQlOCTAJMAkwCQkJCQkJd3cxLmRzbmV4dGdlbi5jb201ZGE0Yzc0MmVkNGUwMy41MTUxODczNAkwCQkwCTAJMTIwNQk5ODIwMDg2OQkJMTg1LjkyLjI1LjIw | DE | — | 2.08 Kb | malicious |
1796 | chrome.exe | GET | 302 | 72.52.179.175:80 | http://dsnextgen.com/?o_id=130920&domainname=www.thorinc.com%2Fremove%2Fcpnremove.php | US | — | — | malicious |
1796 | chrome.exe | GET | 302 | 108.168.193.184:80 | http://forwrdnow.com/aS/feedclick?s=N96qfziHQqR1ciMM9brhsSdsBF_uyqHoXdKpm_iE5krdhoJao1-3Qp1B-kb1vwChg2RvEwrk2epbC7U30TJp2WvoICO3pAFB-9ayILa_jmcWRUYpqyAbUfbBAycg447jGj5CCziVxGvhd-BnC8BekWeukOm6WVEECf2oHXffqu71a0YWJmhCJv9Za4ILVqu53eldyEAwy2Rnr1HRloN17azqNkSZ4MP9vulPRUFeAVwG2Du9JEbwYUDM2w0Cs7SSUy9cmJ4sC0SD43xSpehqYhTLJukT4HX33_sEEIcFZ2Wrtl55W9s6IXMC36MOV9Q69Ozk3Rv2P2Z9WHTN2jN6lvuQt-XSQxhwu-Vn6P0Pc8CD5cigUmAzks1URkm10xRKUJYhDADFGSiqNZHnb0rUW1Xp4dJh_CuyqooSm0JQumhiqnPRglMnxOF7FOlSMsjaHosHnVPI9MmTONUgmEsT9BI6tuMRurl75e6A6czmb7wXusqaFnoxlbxiZoo5y7X8IerNKT4pGDupvY895NyWiNeY_JnsouBr9mn05_3sEJ-M43HctUWGfKT6Ifj6CGUXDd6khgw1xizex3btw87HaAp4fFE_zlx7_Kbc8xtuWKx-wwWZE6djSweIx6tRiLMQVrpRduPoD8AQvEzNJDopS07PspS4ce5ISOXwdJJoXhB-Pc0hDBUuM2GKtkyD3Tx4udjCRaoEDDMRWioH9gEvvWS7NIXugPuUVuX8DBYjjollq5JkCl20SXmUCkx-zzZDLlehVd0497npJxJVhoqb5XKtzZZF_NnTF_8zc5Ey_xAVNSbP4L6VxJxgJknSkiei-Enx24tEQ5CLEdKV0ZSi2nUAqCEfRpfP6ScSVYaKm-UBLMcmL5Iv0FRdfOSQMJ-KyQmel9ltqNomDW_olsHQNA | US | — | — | whitelisted |
1796 | chrome.exe | GET | 302 | 91.195.240.136:80 | http://ww1.dsnextgen.com/search/redirect.php?f=http%3A%2F%2Fforwrdnow.com%2FaS%2Ffeedclick%3Fs%3DN96qfziHQqR1ciMM9brhsSdsBF_uyqHoXdKpm_iE5krdhoJao1-3Qp1B-kb1vwChg2RvEwrk2epbC7U30TJp2WvoICO3pAFB-9ayILa_jmcWRUYpqyAbUfbBAycg447jGj5CCziVxGvhd-BnC8BekWeukOm6WVEECf2oHXffqu71a0YWJmhCJv9Za4ILVqu53eldyEAwy2Rnr1HRloN17azqNkSZ4MP9vulPRUFeAVwG2Du9JEbwYUDM2w0Cs7SSUy9cmJ4sC0SD43xSpehqYhTLJukT4HX33_sEEIcFZ2Wrtl55W9s6IXMC36MOV9Q69Ozk3Rv2P2Z9WHTN2jN6lvuQt-XSQxhwu-Vn6P0Pc8CD5cigUmAzks1URkm10xRKUJYhDADFGSiqNZHnb0rUW1Xp4dJh_CuyqooSm0JQumhiqnPRglMnxOF7FOlSMsjaHosHnVPI9MmTONUgmEsT9BI6tuMRurl75e6A6czmb7wXusqaFnoxlbxiZoo5y7X8IerNKT4pGDupvY895NyWiNeY_JnsouBr9mn05_3sEJ-M43HctUWGfKT6Ifj6CGUXDd6khgw1xizex3btw87HaAp4fFE_zlx7_Kbc8xtuWKx-wwWZE6djSweIx6tRiLMQVrpRduPoD8AQvEzNJDopS07PspS4ce5ISOXwdJJoXhB-Pc0hDBUuM2GKtkyD3Tx4udjCRaoEDDMRWioH9gEvvWS7NIXugPuUVuX8DBYjjollq5JkCl20SXmUCkx-zzZDLlehVd0497npJxJVhoqb5XKtzZZF_NnTF_8zc5Ey_xAVNSbP4L6VxJxgJknSkiei-Enx24tEQ5CLEdKV0ZSi2nUAqCEfRpfP6ScSVYaKm-UBLMcmL5Iv0FRdfOSQMJ-KyQmel9ltqNomDW_olsHQNA&v=YmY3MGM3MTQxY2UzNjc2MzljZjYxNGUxMjY3Yjg1ZmQJMQl3dzEuZHNuZXh0Z2VuLmNvbTVkYTRjNzQyZWQ0ZTAzLjUxNTE4NzM0CXd3MS5kc25leHRnZW4uY29tNWRhNGM3NDJlZDUzYTYuMDQxNjYwNTUJMTU3MTA4MDAwMwlhZF81Ml8w&l=NglBRFMJNTA0Y2Y5MTM1NGRkNDFhODdjYzgwNzY5MjQ2ODBhOTYJMAkxMwkJMzEJMQkxCTAJYWZhYjVjYjg0MzFmOWFiN2Y1ZGVhNzRhMzNjMjk0NDQJCTMzNTgyNTA4NgljCTAJCWRzbmV4dGdlbgkxMTAxCTUyCTQJMwkxNTcxMDgwMDAzCTAuMDM3NQlOCTAJMAkwCQkJCQkJd3cxLmRzbmV4dGdlbi5jb201ZGE0Yzc0MmVkNGUwMy41MTUxODczNAkwCQkwCTAJMTIwNQk5ODIwMDg2OQkJMTg1LjkyLjI1LjIw | DE | — | 3.48 Kb | malicious |
1796 | chrome.exe | GET | 302 | 23.82.9.96:80 | http://7lyonline.com/app/feedclick?p=rJN8Jng_F5yxndamoMMBM_aRhs-CREPEIWARlL2iuDsOE1-_2QnHIcNnA02fFaz8AJK7QCMm8YpoxwBQdUZd4Q3jO6VAG9VkBDEK4mzoj_t-qcu8A8nJ8Y215MfW-IjvIoi8cntXzXh-Pc0hDBUuM7kNGEndgfntM6XsBtxvuDneA1bPkeVeUskaH6AvEtnJ1hfYJhlu9LI | US | — | — | whitelisted |
1796 | chrome.exe | GET | 200 | 91.195.240.136:80 | http://ww1.dsnextgen.com/ | DE | html | 3.48 Kb | malicious |
1796 | chrome.exe | GET | 200 | 204.174.223.48:80 | http://missing.hwpub.com/404-header.htm | CA | html | 445 b | unknown |
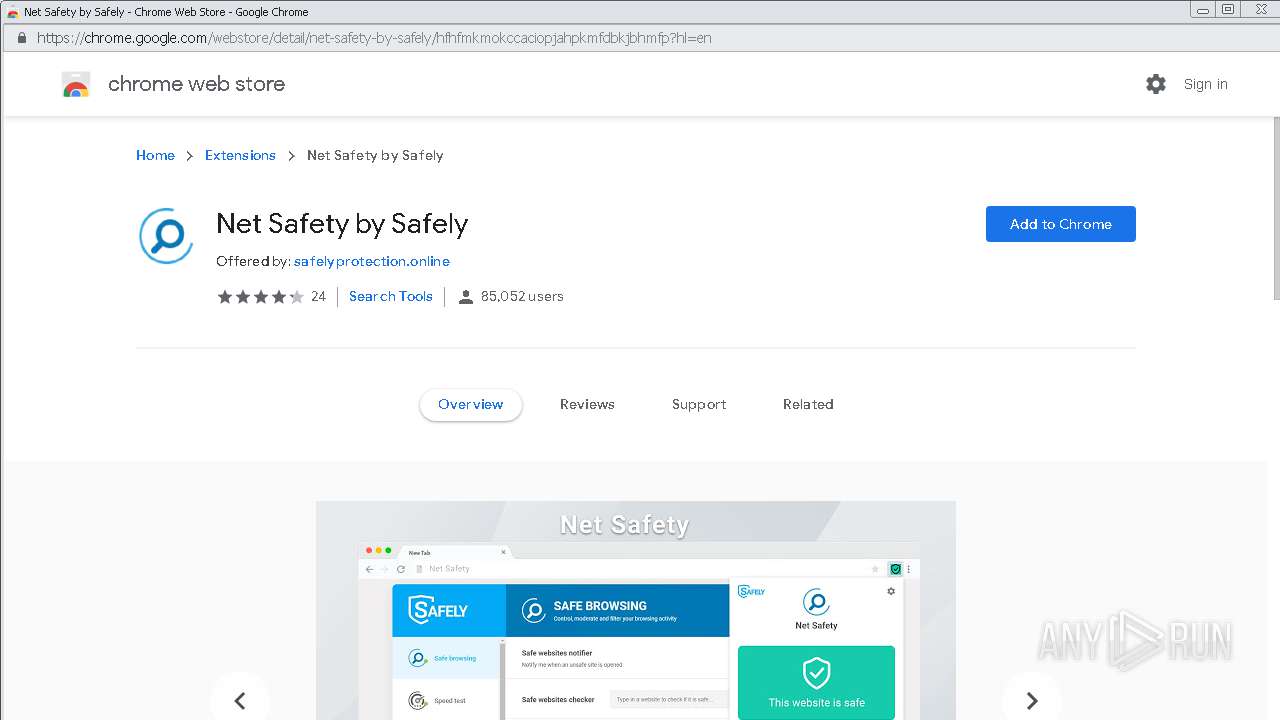
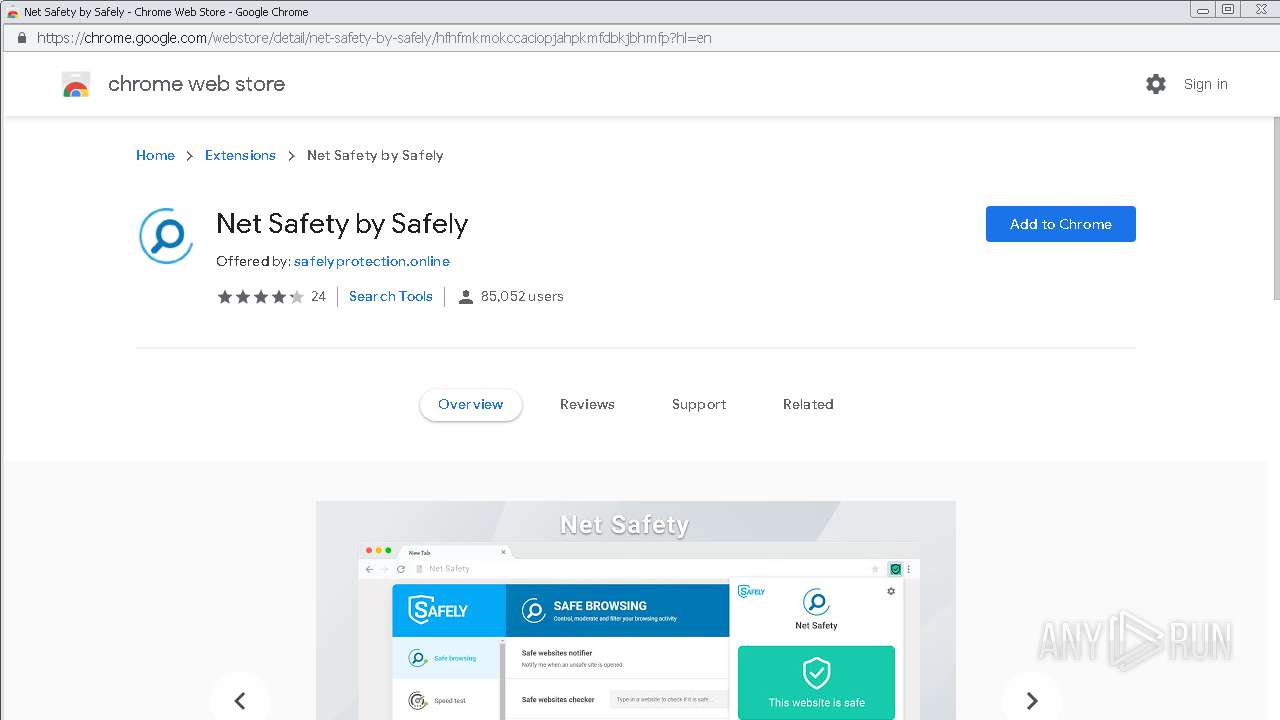
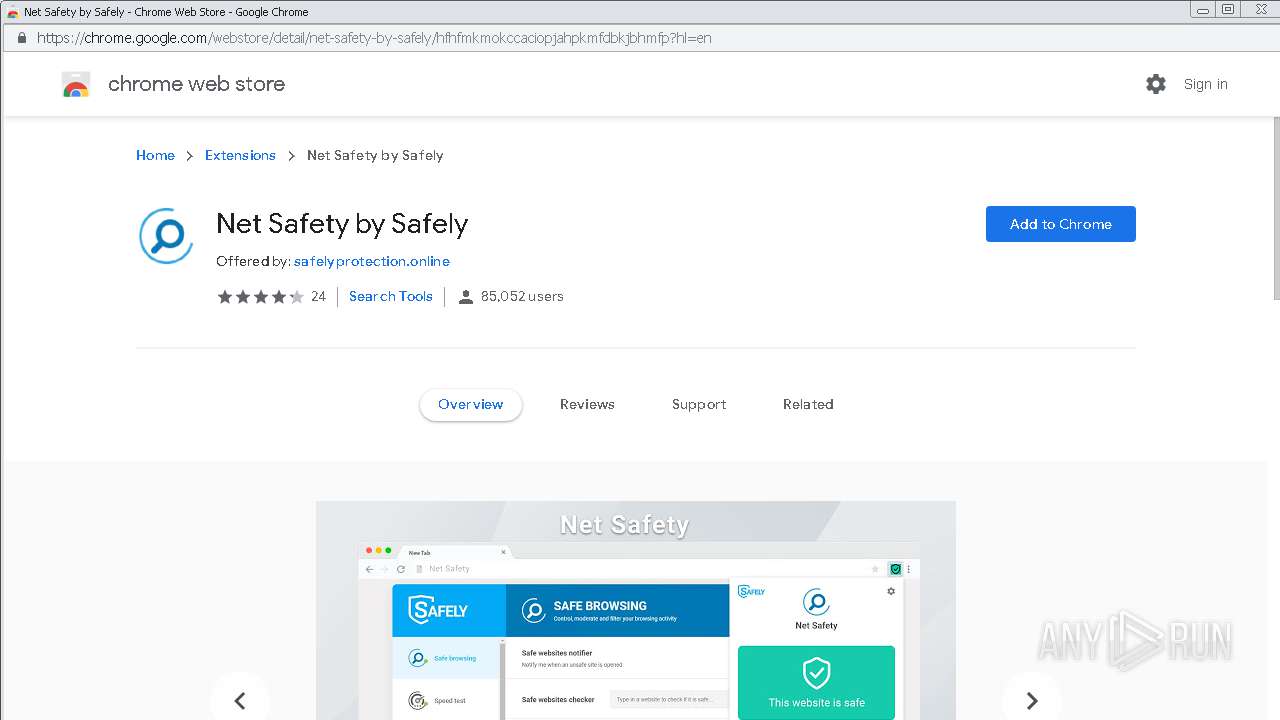
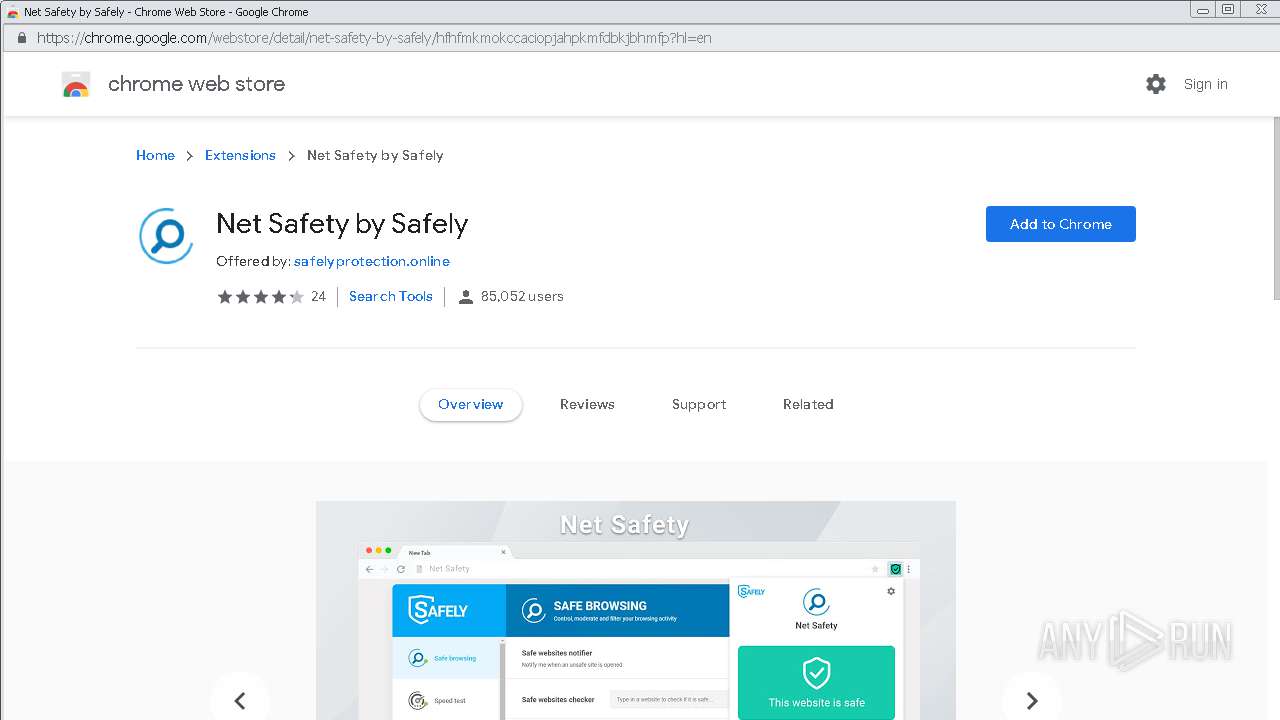
1796 | chrome.exe | GET | 200 | 151.139.237.32:80 | http://check.safelyprotection.online/check.php?domain=chrome.google.com | US | text | 24 b | malicious |
1796 | chrome.exe | GET | 302 | 204.174.223.48:80 | http://missing.hwpub.com/?ck=ndc96uyh76&et=1 | CA | text | 2 b | unknown |
1796 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 513 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1796 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1796 | chrome.exe | 64.71.33.30:80 | www.thorinc.com | Hostway Corporation | US | unknown |
1796 | chrome.exe | 204.174.223.48:80 | missing.hwpub.com | NetNation Commmunications, Inc. | CA | unknown |
1796 | chrome.exe | 205.234.175.175:80 | img.sedoparking.com | CacheNetworks, Inc. | US | suspicious |
1796 | chrome.exe | 108.168.193.184:80 | forwrdnow.com | SoftLayer Technologies Inc. | US | unknown |
1796 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
1796 | chrome.exe | 23.82.9.96:80 | 7lyonline.com | Nobis Technology Group, LLC | US | suspicious |
1796 | chrome.exe | 91.195.240.136:80 | ww1.dsnextgen.com | SEDO GmbH | DE | malicious |
1796 | chrome.exe | 104.31.85.132:80 | www.givemeapplink.com | Cloudflare Inc | US | shared |
1796 | chrome.exe | 172.217.18.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.thorinc.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
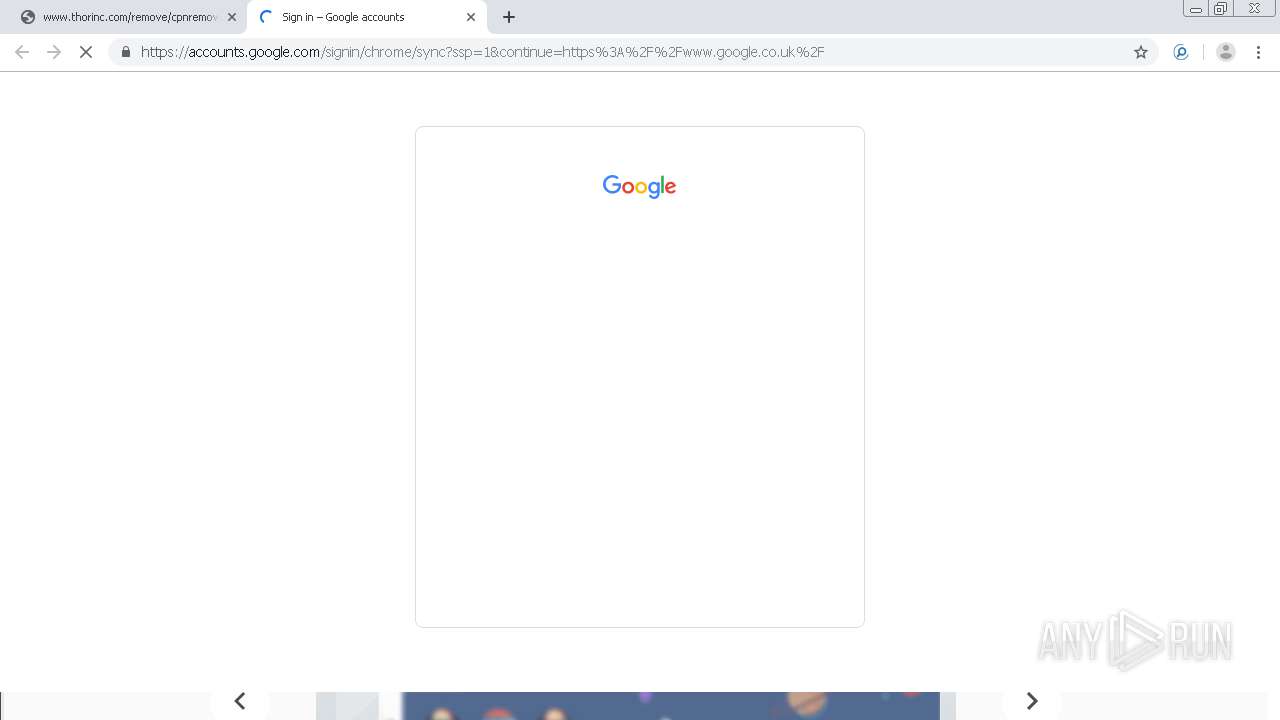
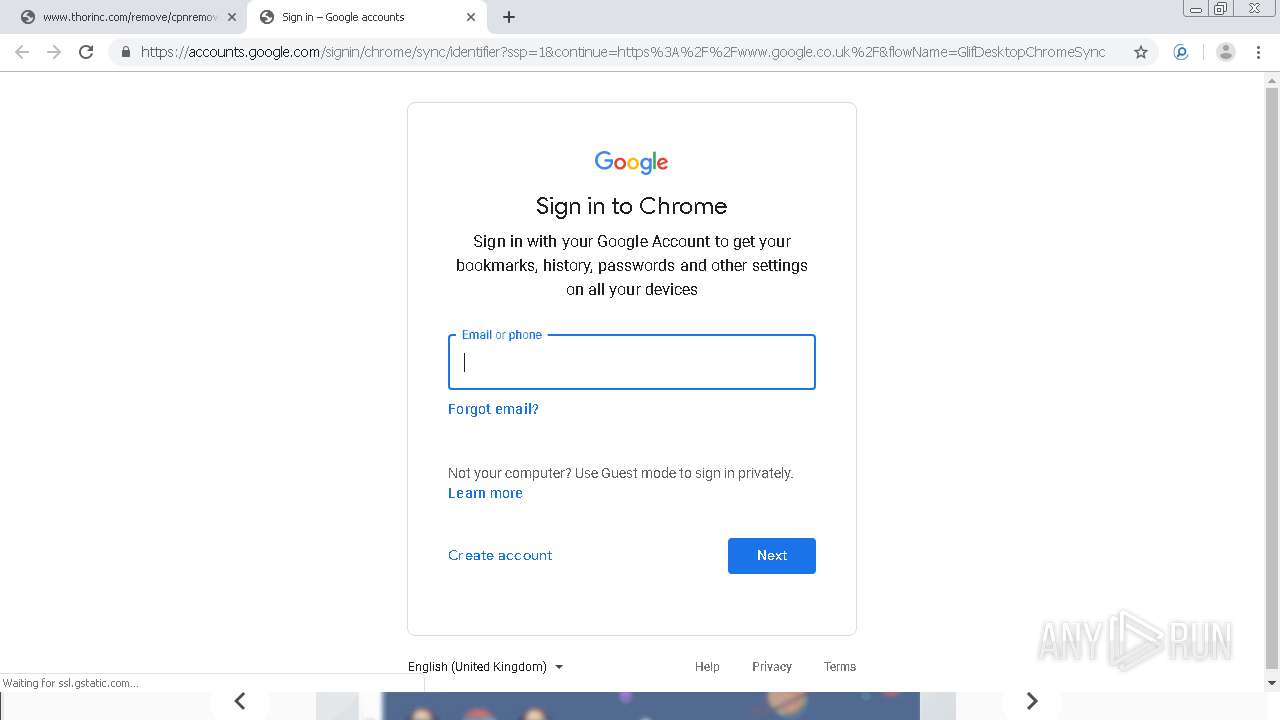
accounts.google.com |
| shared |
missing.hwpub.com |
| unknown |
dsnextgen.com |
| malicious |
ww1.dsnextgen.com |
| malicious |
img.sedoparking.com |
| whitelisted |
www.google.com |
| malicious |
forwrdnow.com |
| whitelisted |
7lyonline.com |
| whitelisted |