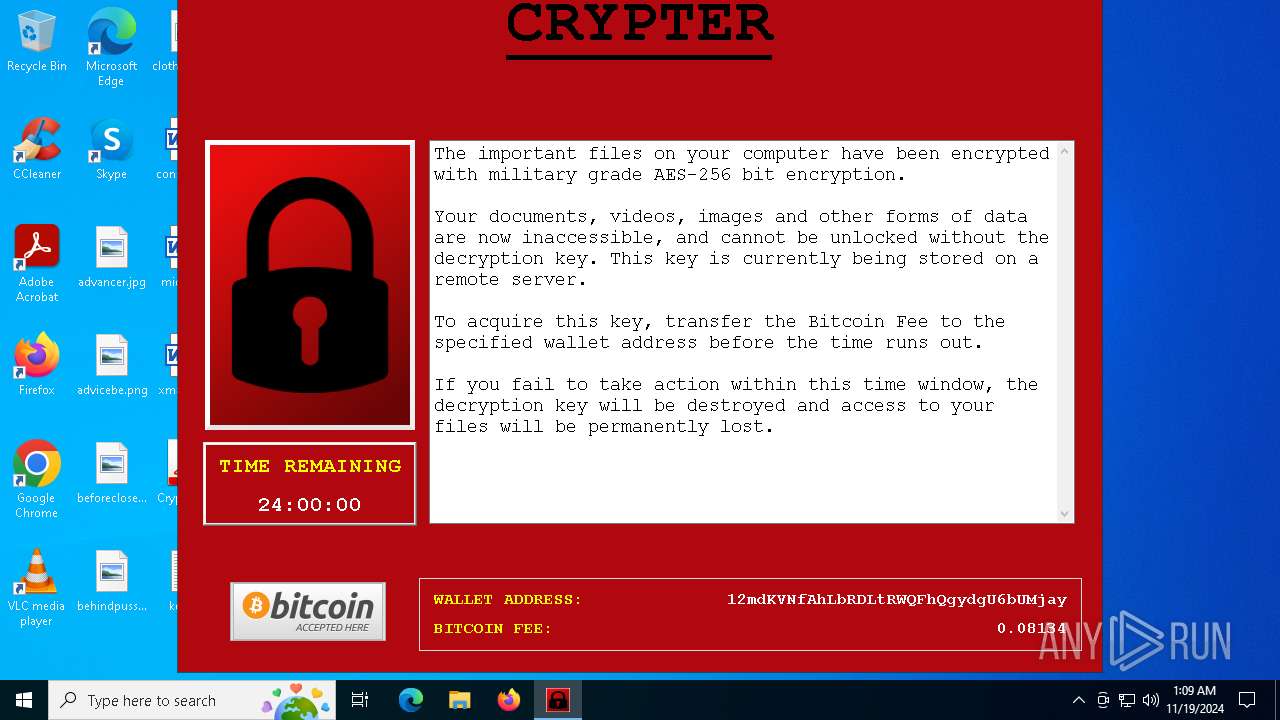
| File name: | Crypter.exe |
| Full analysis: | https://app.any.run/tasks/dfeba668-2a80-4c8c-8393-fd9dd283022a |
| Verdict: | Malicious activity |
| Analysis date: | November 19, 2024, 01:09:09 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | 24FB23E6DBC99CE49F37F8AB69F5BB5E |
| SHA1: | 478725F77A78CCD321020C55897BFA87FD7DE07D |
| SHA256: | FD838C2329A42EF298976E529398F74641E4D9BC90D30AC6A891D04CDA52E8F7 |
| SSDEEP: | 98304:gJNyFDD4Jw/axJhVS6ilkNsojZqMm9YT15/uWkuwfrQSLCjFy6EgrZcLujtJF80h:Z1CrTLKZUbmIaFFZvcgEDEIKOmKQW1 |
MALICIOUS
Uses Task Scheduler to run other applications
- cmd.exe (PID: 6716)
Changes the autorun value in the registry
- Crypter.exe (PID: 5240)
SUSPICIOUS
Executable content was dropped or overwritten
- Crypter.exe (PID: 6464)
Process drops python dynamic module
- Crypter.exe (PID: 6464)
The process drops C-runtime libraries
- Crypter.exe (PID: 6464)
Application launched itself
- Crypter.exe (PID: 6464)
Process drops legitimate windows executable
- Crypter.exe (PID: 6464)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 5788)
Loads Python modules
- Crypter.exe (PID: 5240)
Starts CMD.EXE for commands execution
- Crypter.exe (PID: 5240)
INFO
Checks supported languages
- Crypter.exe (PID: 6464)
- Crypter.exe (PID: 5240)
Reads the computer name
- Crypter.exe (PID: 6464)
- Crypter.exe (PID: 5240)
Creates files or folders in the user directory
- Crypter.exe (PID: 5240)
Reads the machine GUID from the registry
- Crypter.exe (PID: 5240)
PyInstaller has been detected (YARA)
- Crypter.exe (PID: 6464)
- Crypter.exe (PID: 5240)
Create files in a temporary directory
- Crypter.exe (PID: 6464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (57.6) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.9) |
| .exe | | | Generic Win/DOS Executable (2.6) |
| .exe | | | DOS Executable Generic (2.6) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2020:01:05 12:15:46+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14 |
| CodeSize: | 134656 |
| InitializedDataSize: | 183296 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8ef8 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
Total processes
132
Monitored processes
11
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1084 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4316 | C:\WINDOWS\system32\cmd.exe /c "schtasks /delete /tn updater47 /f" | C:\Windows\System32\cmd.exe | — | Crypter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5036 | schtasks /create /tn updater47 /sc once /sd 01/01/1901 /tr "vssadmin Delete Shadows /All /Quiet" /st 00:00 /rl highest /ru SYSTEM /f | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5240 | "C:\Users\admin\Desktop\Crypter.exe" | C:\Users\admin\Desktop\Crypter.exe | Crypter.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 5788 | schtasks /delete /tn updater47 /f | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6208 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6336 | C:\WINDOWS\system32\cmd.exe /c "schtasks /run /i /tn updater47" | C:\Windows\System32\cmd.exe | — | Crypter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6464 | "C:\Users\admin\Desktop\Crypter.exe" | C:\Users\admin\Desktop\Crypter.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6716 | C:\WINDOWS\system32\cmd.exe /c "schtasks /create /tn updater47 /sc once /sd 01/01/1901 /tr "vssadmin Delete Shadows /All /Quiet" /st 00:00 /rl highest /ru SYSTEM /f" | C:\Windows\System32\cmd.exe | — | Crypter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6824 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
204
Read events
203
Write events
1
Delete events
0
Modification events
| (PID) Process: | (5240) Crypter.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Crypter |
Value: C:\Users\admin\Desktop\Crypter.exe | |||
Executable files
107
Suspicious files
3
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6464 | Crypter.exe | C:\Users\admin\AppData\Local\Temp\_MEI64642\Crypto\Cipher\_raw_arc2.cp37-win_amd64.pyd | executable | |
MD5:F33D0CD6A54FFCB17C604808A7E09CD7 | SHA256:A744F78086E189FB63547A49F7195C8315FE8CFEC61E7875E4F09F6026E02034 | |||
| 6464 | Crypter.exe | C:\Users\admin\AppData\Local\Temp\_MEI64642\Crypto\Cipher\_raw_aesni.cp37-win_amd64.pyd | executable | |
MD5:94DAF3DA5654A5B4E98B45CF58D1AE17 | SHA256:2331F45B306D6392F7F89A963A817D10621D5B1BB0BC3D6617E73AA7E9F595BD | |||
| 6464 | Crypter.exe | C:\Users\admin\AppData\Local\Temp\_MEI64642\Crypto\Cipher\_raw_aes.cp37-win_amd64.pyd | executable | |
MD5:29DC40CA28734062927E35F159045D00 | SHA256:62A8DFD622505D3961B53EC718D4B1FA7932996921A70E5043D28C82014C958F | |||
| 6464 | Crypter.exe | C:\Users\admin\AppData\Local\Temp\_MEI64642\Crypto\Cipher\_raw_cfb.cp37-win_amd64.pyd | executable | |
MD5:EAEB30F73165BEF13C17703E524BA4E7 | SHA256:37DCEB92E4712F70725B79309E1B3313C9A6FE4F0129EB873EC283F8A4FC966A | |||
| 6464 | Crypter.exe | C:\Users\admin\AppData\Local\Temp\_MEI64642\Crypto\Cipher\_ARC4.cp37-win_amd64.pyd | executable | |
MD5:2E1E4C3719872D61F14AA5C0AFD120F0 | SHA256:6C6E6243FD51DF85E06D24BE2BF5D01F3B7201624D878AE2C85BC273F77E1CC6 | |||
| 6464 | Crypter.exe | C:\Users\admin\AppData\Local\Temp\_MEI64642\Crypto\Cipher\_chacha20.cp37-win_amd64.pyd | executable | |
MD5:46097C3B9B3E3678661630156D03F278 | SHA256:80EF6198A889F6AF006A7E6583EF25ECBEB8B23BC04F40735DF69878E28D3EFE | |||
| 6464 | Crypter.exe | C:\Users\admin\AppData\Local\Temp\_MEI64642\Crypto\Cipher\_raw_cast.cp37-win_amd64.pyd | executable | |
MD5:CBDF30B89917BB36DE4240CFC3309AEE | SHA256:F9806E20740F10CCD1A149A235B4F74213339CEC44834CFC11578C47CF72657D | |||
| 6464 | Crypter.exe | C:\Users\admin\AppData\Local\Temp\_MEI64642\Crypto\Cipher\_Salsa20.cp37-win_amd64.pyd | executable | |
MD5:346613B7B5476BC5E0F2052337096745 | SHA256:8E321257DF73855DD2C676211BC701417615036486D86C26A2D534EB3D012CC2 | |||
| 6464 | Crypter.exe | C:\Users\admin\AppData\Local\Temp\_MEI64642\Crypto\Cipher\_raw_blowfish.cp37-win_amd64.pyd | executable | |
MD5:E88EACC5B68A0528FF437FB0015429A3 | SHA256:548AF33A9E3234F0E4D1735E6493007468F7DEE6CF047034BAB0962743A5461A | |||
| 6464 | Crypter.exe | C:\Users\admin\AppData\Local\Temp\_MEI64642\Crypto\Cipher\_raw_ctr.cp37-win_amd64.pyd | executable | |
MD5:9C4F7079923415405BDC57170343D276 | SHA256:0A3D953BBECD62553EC35CCD2B5E97E54849171AE3BEC86361F18E5641F51CB4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
21
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 2.19.126.133:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3952 | RUXIMICS.exe | GET | 200 | 2.19.126.133:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.19.126.133:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3952 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3952 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 2.19.126.133:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3952 | RUXIMICS.exe | 2.19.126.133:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.19.126.133:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3952 | RUXIMICS.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |