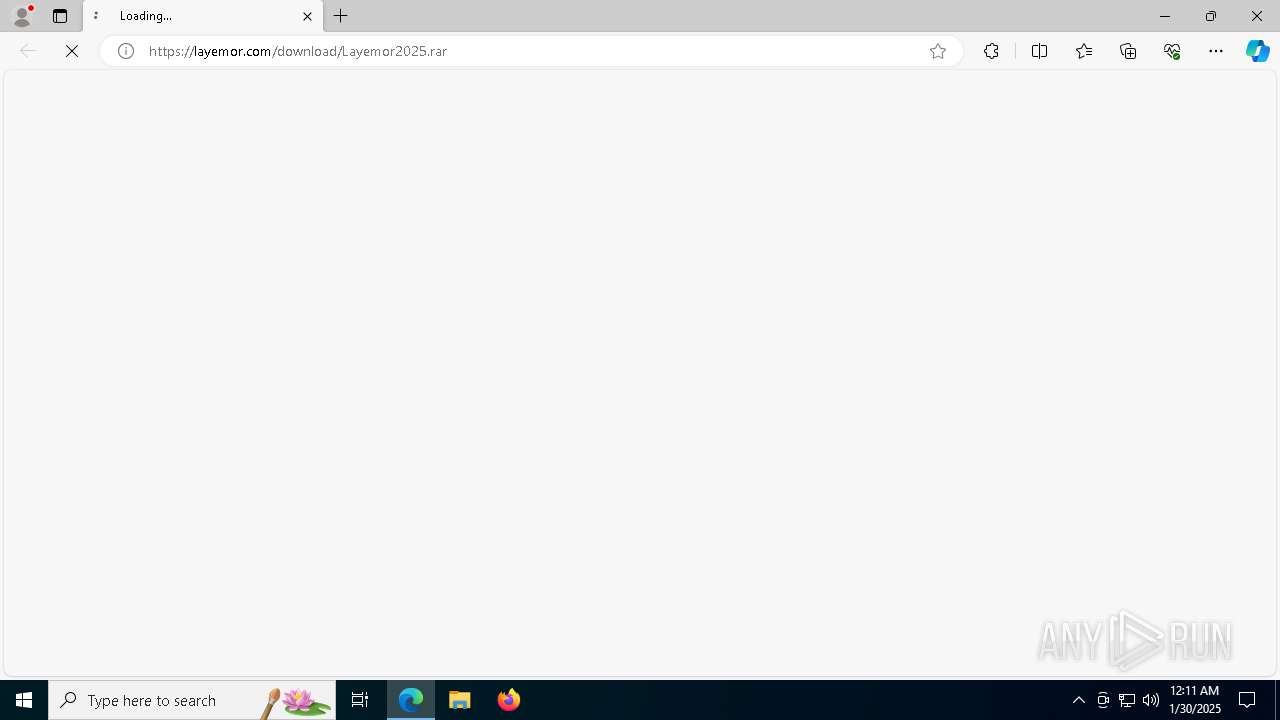
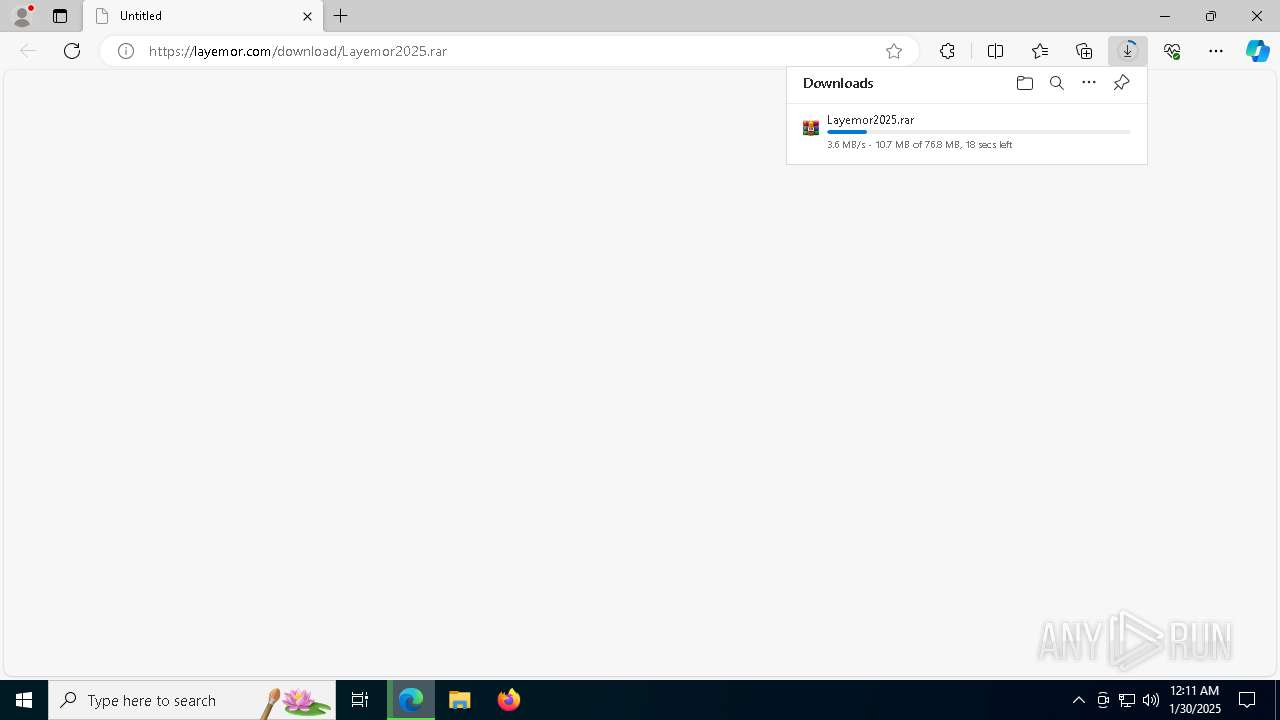
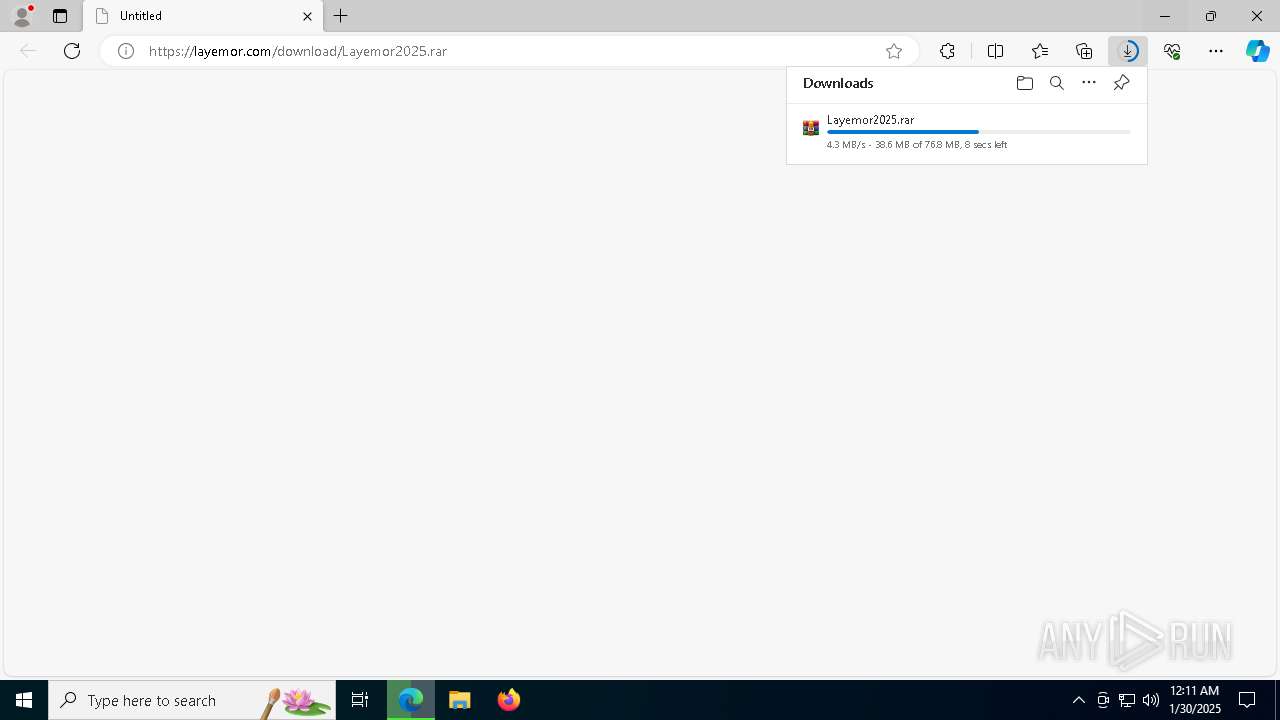
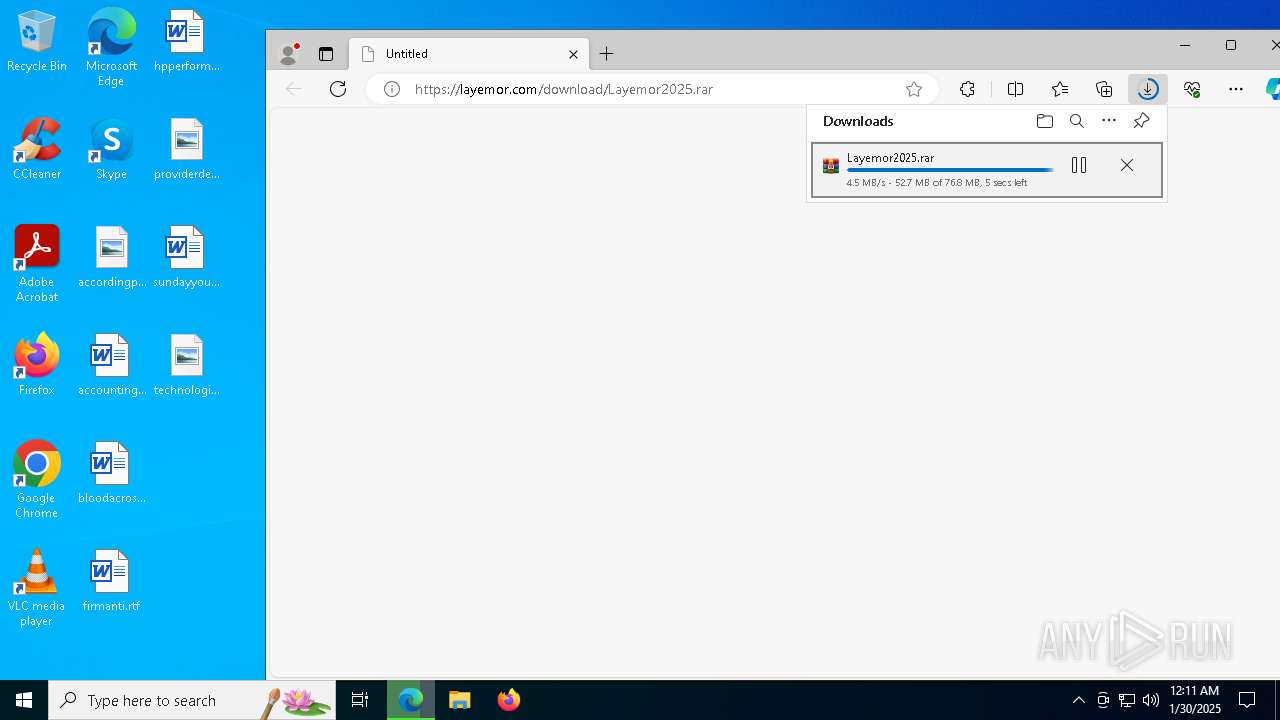
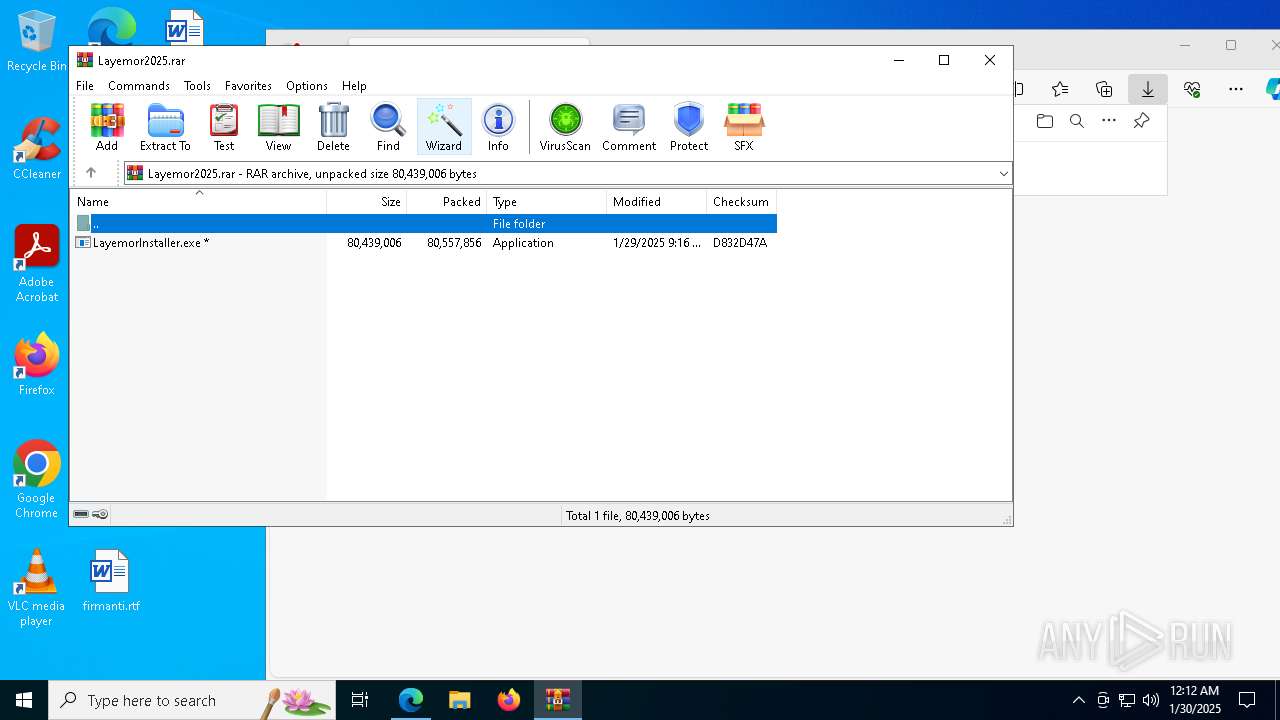
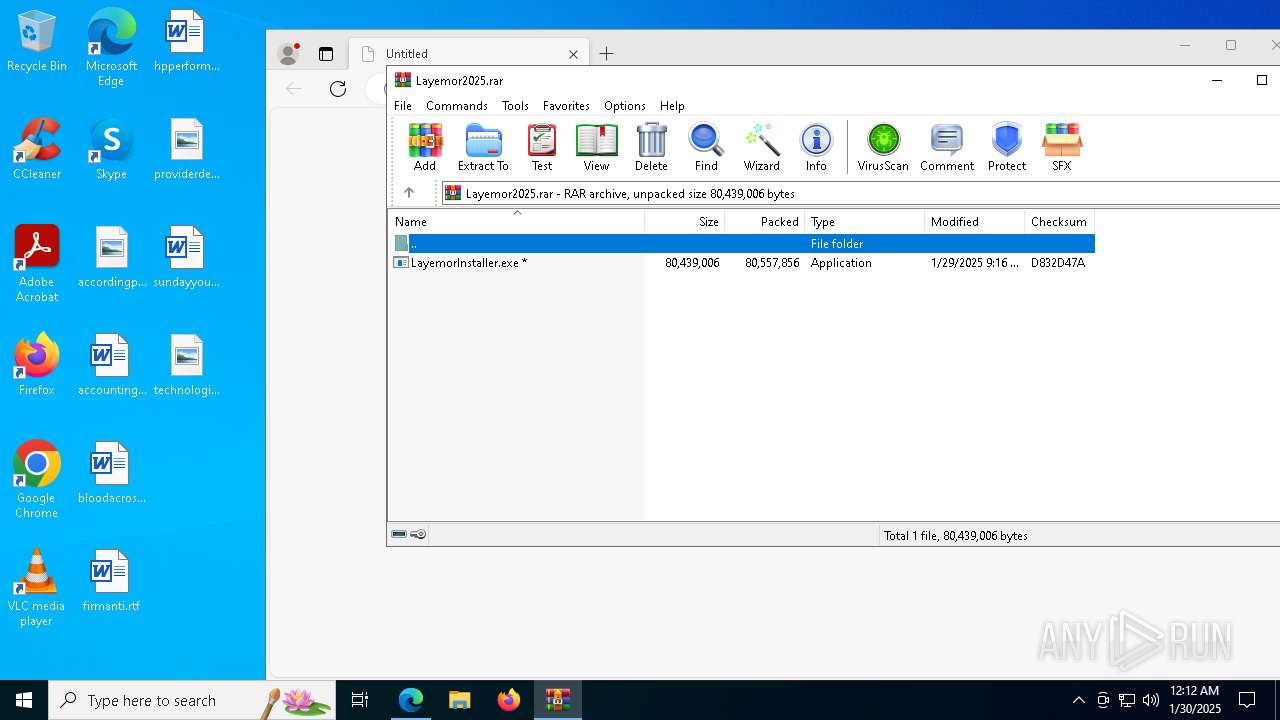
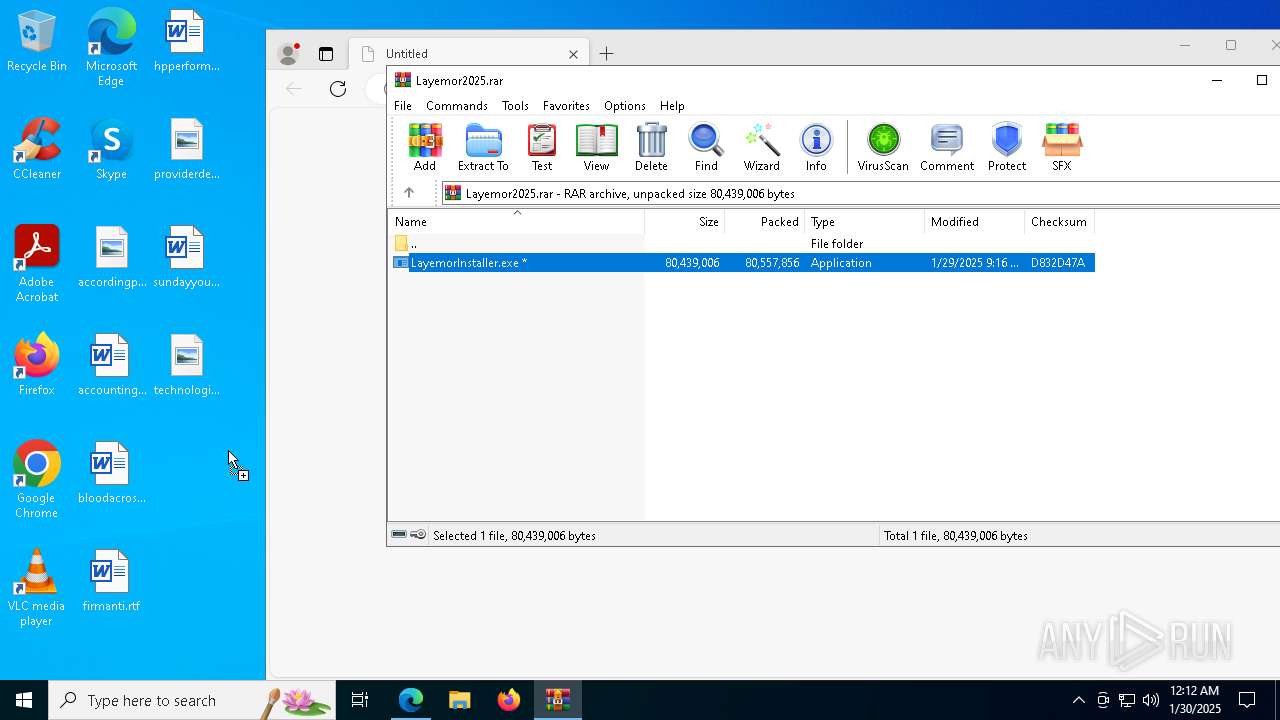
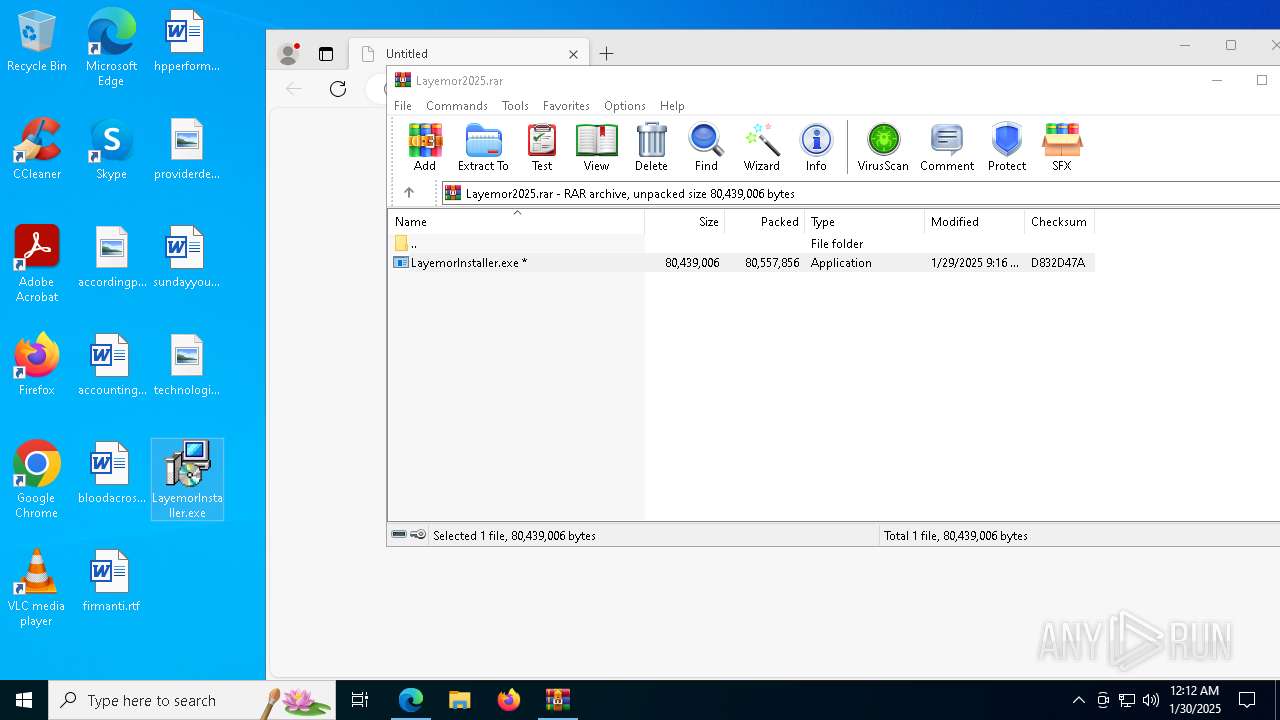
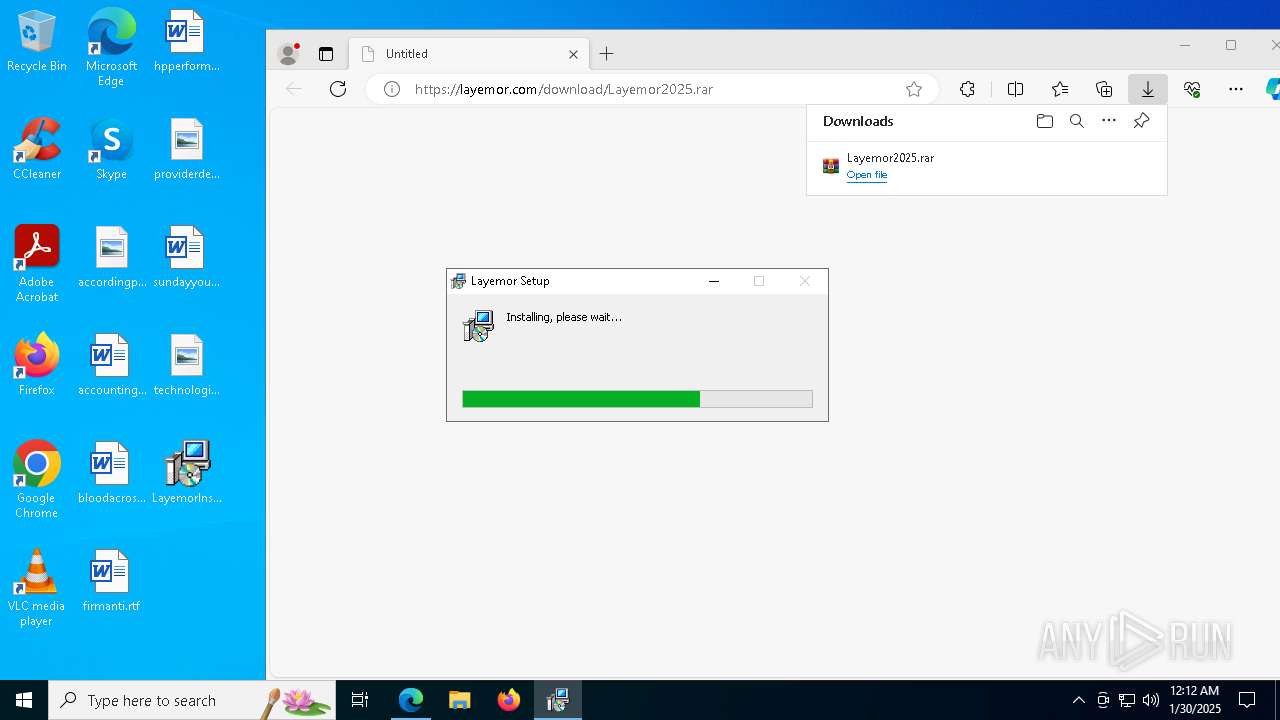
| URL: | https://layemor.com/download/Layemor2025.rar |
| Full analysis: | https://app.any.run/tasks/68bfcc0a-28ef-4fa1-8a0b-e7c03b8df20d |
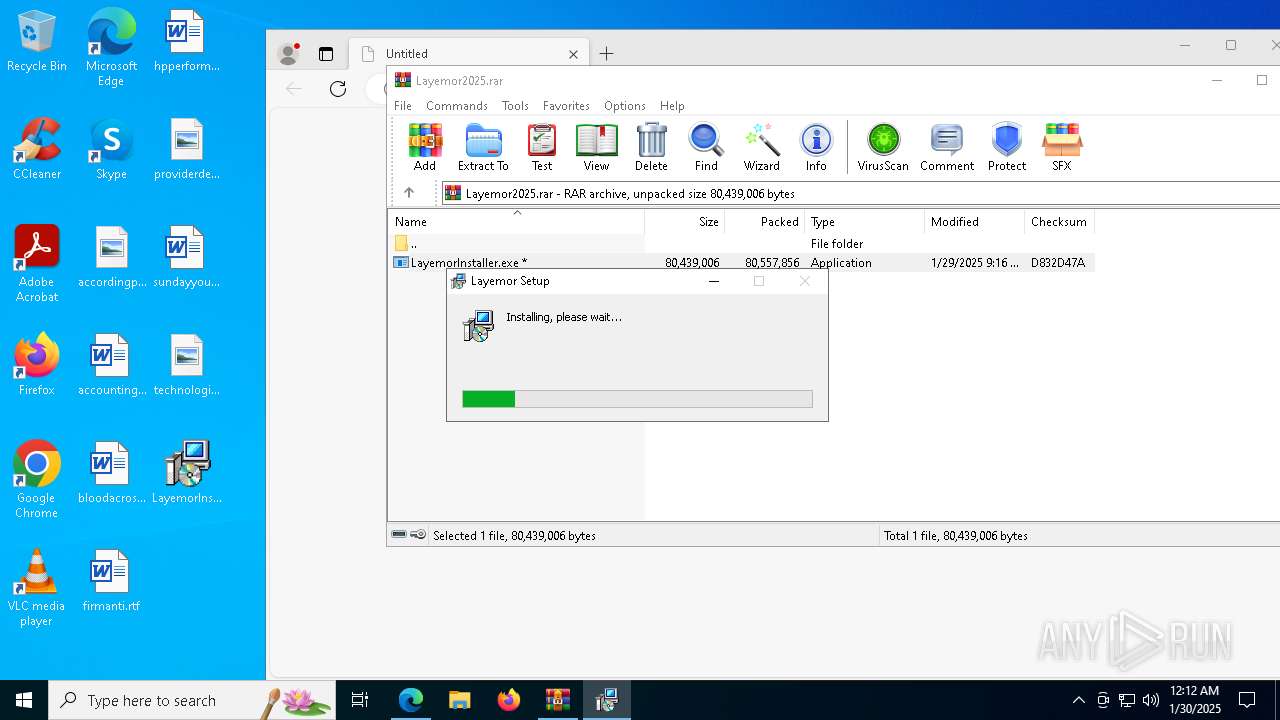
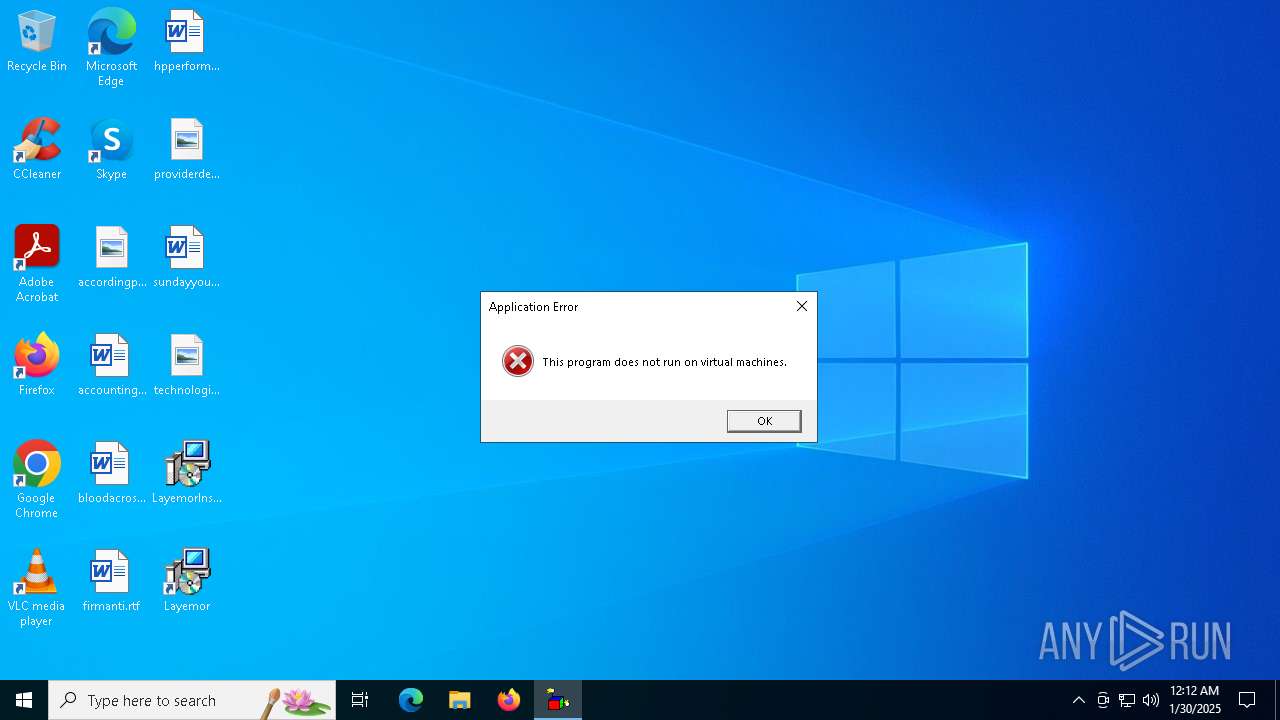
| Verdict: | Malicious activity |
| Analysis date: | January 30, 2025, 00:11:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7B674AF16B3517923039CD96CC37AFAA |
| SHA1: | 4D2D3EBBFBC0E57E22678F16C566967C607E931C |
| SHA256: | FD82827C8C644718DE7A881E1BDFA7662DE7BF345226AF64F7D4A2E13EAE8EC6 |
| SSDEEP: | 3:N8EcjNLqxoO:2EcjNXO |
MALICIOUS
No malicious indicators.SUSPICIOUS
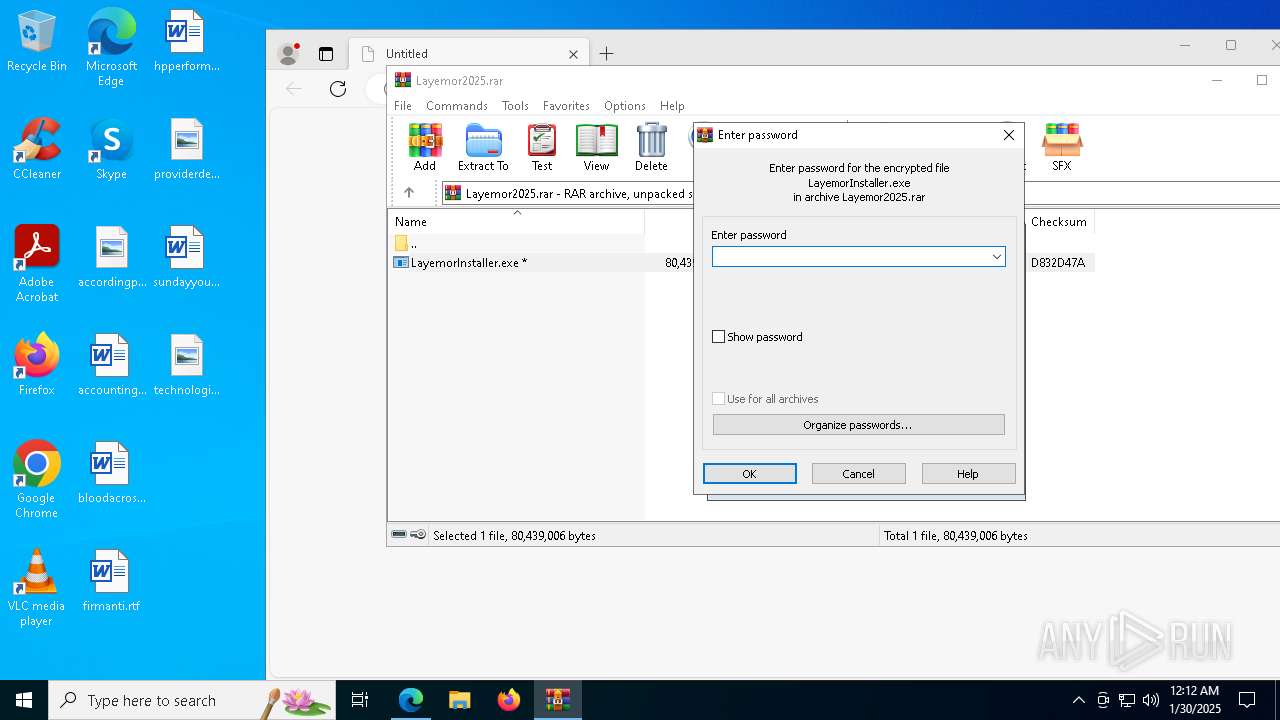
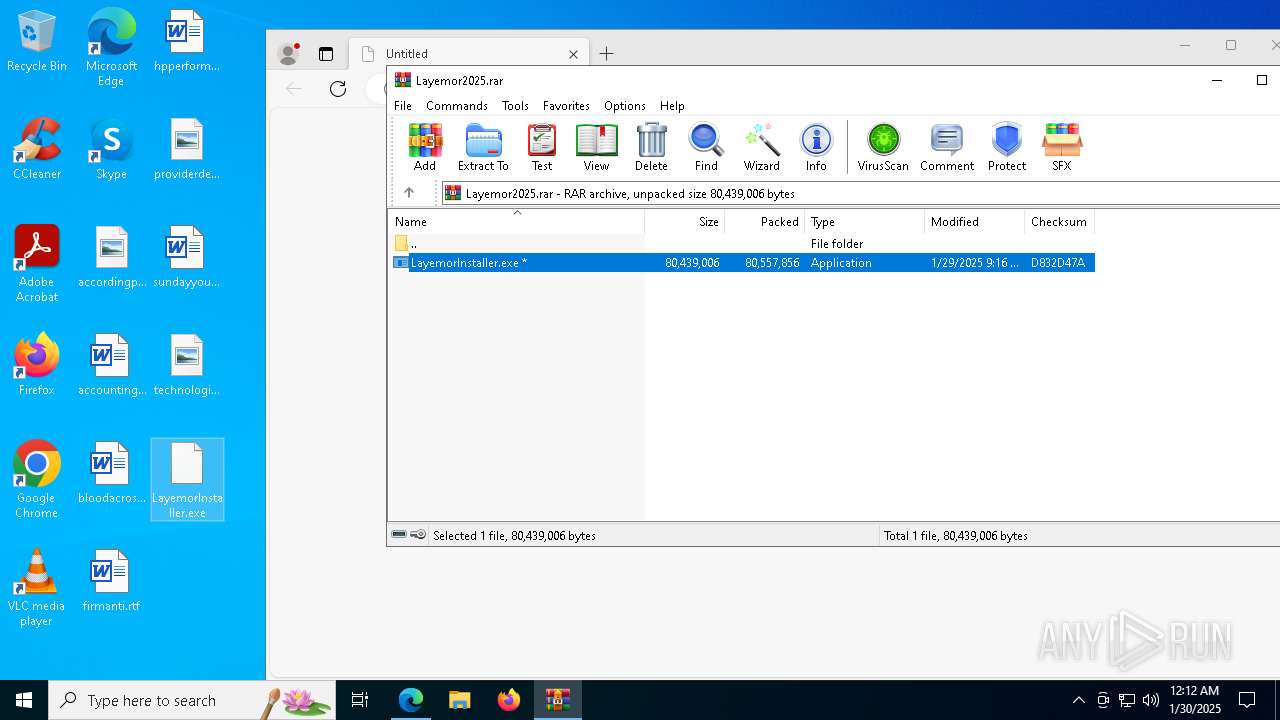
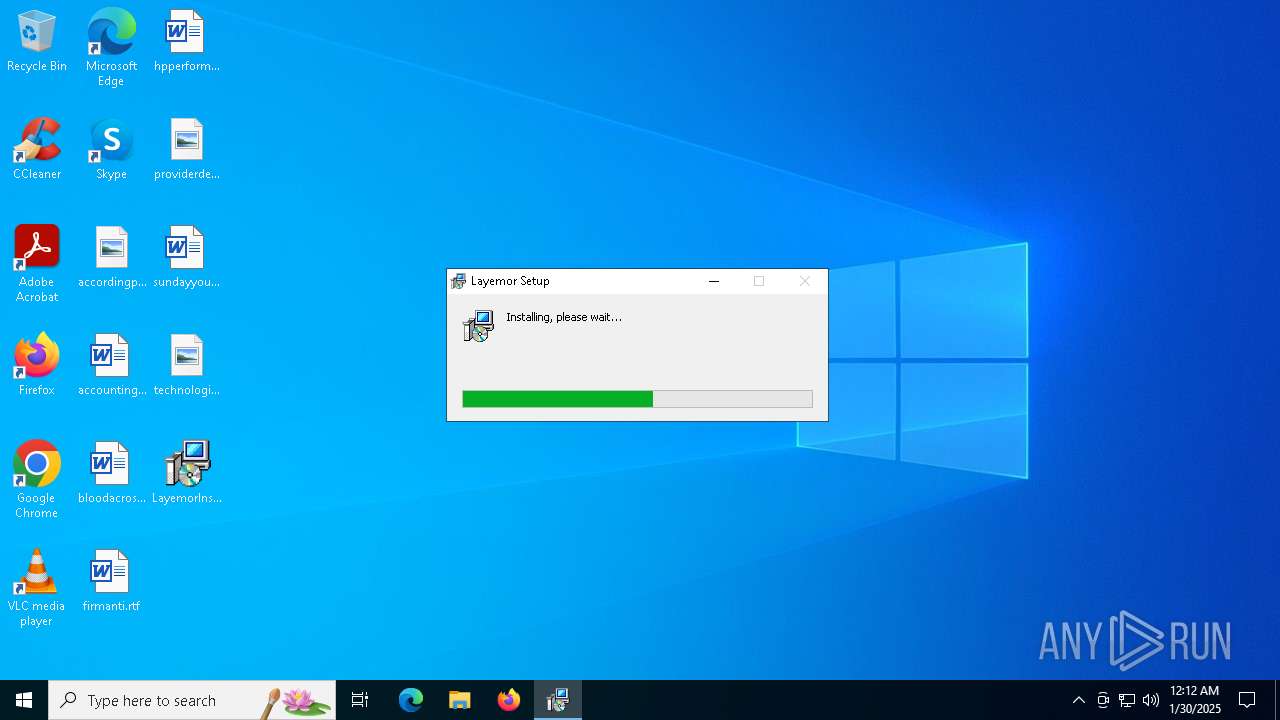
The process creates files with name similar to system file names
- LayemorInstaller.exe (PID: 5308)
Malware-specific behavior (creating "System.dll" in Temp)
- LayemorInstaller.exe (PID: 5308)
Starts CMD.EXE for commands execution
- LayemorInstaller.exe (PID: 5308)
- Layemor.exe (PID: 8000)
Executable content was dropped or overwritten
- LayemorInstaller.exe (PID: 5308)
Get information on the list of running processes
- LayemorInstaller.exe (PID: 5308)
- cmd.exe (PID: 5640)
- cmd.exe (PID: 3848)
- Layemor.exe (PID: 8000)
Creates a software uninstall entry
- LayemorInstaller.exe (PID: 5308)
There is functionality for taking screenshot (YARA)
- LayemorInstaller.exe (PID: 5308)
Application launched itself
- Layemor.exe (PID: 8000)
Uses WMIC.EXE to obtain BIOS management information
- cmd.exe (PID: 6976)
The process executes VB scripts
- cmd.exe (PID: 7412)
Uses WMIC.EXE to obtain memory chip information
- cmd.exe (PID: 2136)
Reads security settings of Internet Explorer
- LayemorInstaller.exe (PID: 5308)
Process drops legitimate windows executable
- LayemorInstaller.exe (PID: 5308)
Drops 7-zip archiver for unpacking
- LayemorInstaller.exe (PID: 5308)
Checks for external IP
- curl.exe (PID: 6944)
INFO
Application launched itself
- msedge.exe (PID: 3564)
- msedge.exe (PID: 7296)
Checks supported languages
- identity_helper.exe (PID: 7416)
- LayemorInstaller.exe (PID: 5308)
- identity_helper.exe (PID: 7788)
- Layemor.exe (PID: 8000)
- Layemor.exe (PID: 7252)
- Layemor.exe (PID: 1616)
- curl.exe (PID: 6944)
Reads Environment values
- identity_helper.exe (PID: 7416)
- Layemor.exe (PID: 8000)
- identity_helper.exe (PID: 7788)
Reads Microsoft Office registry keys
- msedge.exe (PID: 3564)
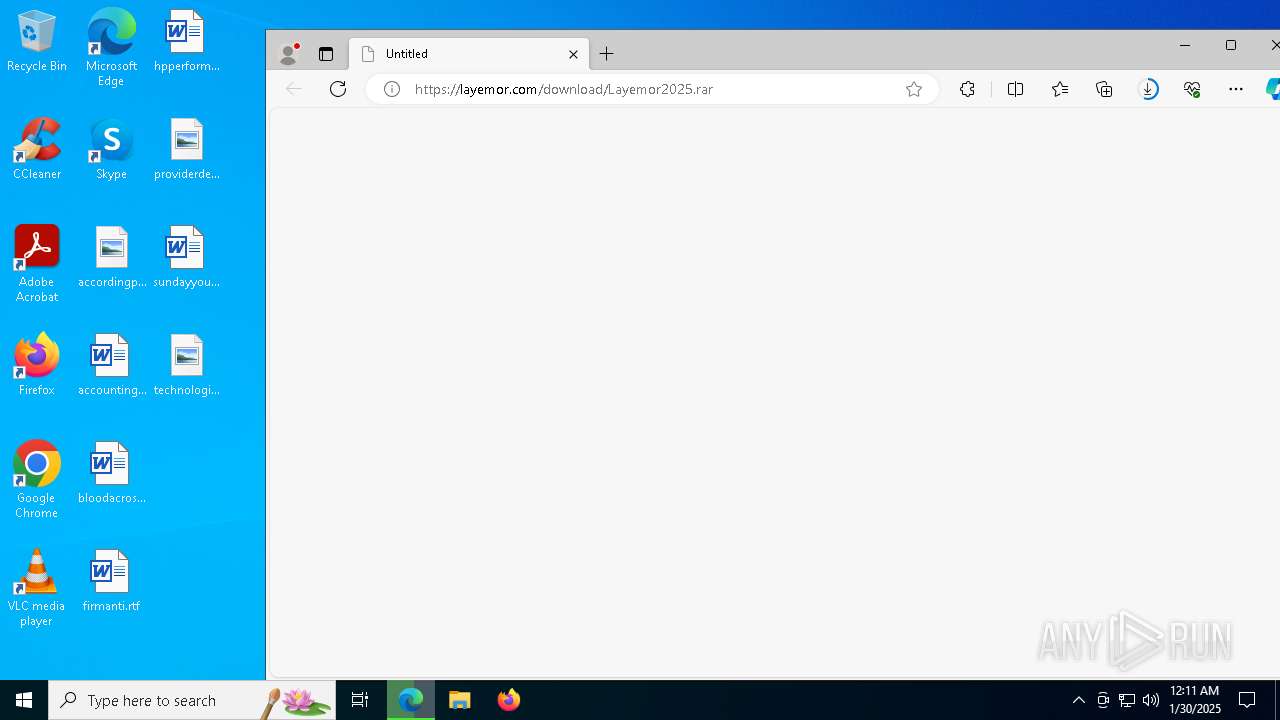
Manual execution by a user
- LayemorInstaller.exe (PID: 5308)
- Layemor.exe (PID: 8000)
The sample compiled with english language support
- LayemorInstaller.exe (PID: 5308)
Reads the computer name
- identity_helper.exe (PID: 7416)
- Layemor.exe (PID: 8000)
- Layemor.exe (PID: 1616)
- curl.exe (PID: 6944)
- Layemor.exe (PID: 7252)
- LayemorInstaller.exe (PID: 5308)
- identity_helper.exe (PID: 7788)
Create files in a temporary directory
- LayemorInstaller.exe (PID: 5308)
- Layemor.exe (PID: 8000)
Reads product name
- Layemor.exe (PID: 8000)
Creates files or folders in the user directory
- LayemorInstaller.exe (PID: 5308)
Reads the machine GUID from the registry
- Layemor.exe (PID: 8000)
Checks proxy server information
- Layemor.exe (PID: 8000)
Execution of CURL command
- cmd.exe (PID: 7072)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 3640)
- WMIC.exe (PID: 5572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
191
Monitored processes
66
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1296 | tasklist | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | "C:\Users\admin\AppData\Local\Programs\unrealgame\Layemor.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\unrealgame" --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1804 --field-trial-handle=1808,i,11489128730251583059,18214701578443299234,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Users\admin\AppData\Local\Programs\unrealgame\Layemor.exe | — | Layemor.exe | |||||||||||
User: admin Company: Unreal Game Inc. Integrity Level: LOW Description: Layemor Version: 1.0.0 Modules
| |||||||||||||||
| 1760 | "C:\WINDOWS\system32\find.exe" "Layemor.exe" | C:\Windows\SysWOW64\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1796 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | C:\WINDOWS\system32\cmd.exe /d /s /c "wmic MemoryChip get /format:list | find /i "Speed"" | C:\Windows\System32\cmd.exe | — | Layemor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2216 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3564 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://layemor.com/download/Layemor2025.rar" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3568 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5396 --field-trial-handle=2296,i,10923006336745091534,17230385625012951175,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3640 | wmic MemoryChip get /format:list | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3848 | C:\WINDOWS\system32\cmd.exe /d /s /c "tasklist" | C:\Windows\System32\cmd.exe | — | Layemor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 406
Read events
11 349
Write events
57
Delete events
0
Modification events
| (PID) Process: | (3564) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3564) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3564) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3564) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3564) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 05A1608D778B2F00 | |||
| (PID) Process: | (3564) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A5BE688D778B2F00 | |||
| (PID) Process: | (3564) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393764 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E2909C91-F157-4554-BDC8-D4D4834E5C54} | |||
| (PID) Process: | (3564) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393764 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CCCCEF27-CB16-48FD-B51A-F984AC90C114} | |||
| (PID) Process: | (3564) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7405C78D778B2F00 | |||
| (PID) Process: | (3564) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
36
Suspicious files
250
Text files
109
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135ecd.TMP | — | |
MD5:— | SHA256:— | |||
| 3564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135ecd.TMP | — | |
MD5:— | SHA256:— | |||
| 3564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135ecd.TMP | — | |
MD5:— | SHA256:— | |||
| 3564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135ecd.TMP | — | |
MD5:— | SHA256:— | |||
| 3564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135ecd.TMP | — | |
MD5:— | SHA256:— | |||
| 3564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
33
DNS requests
49
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.61.29.203:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.223.41.162:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.223.41.162:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.61.29.203:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6944 | curl.exe | GET | 200 | 104.26.13.205:80 | http://api.ipify.org/ | unknown | — | — | malicious |
5064 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.223.41.162:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
— | — | 23.223.41.162:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.61.29.203:80 | www.microsoft.com | NTT DOCOMO, INC. | JP | whitelisted |
— | — | 23.61.29.203:80 | www.microsoft.com | NTT DOCOMO, INC. | JP | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3564 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6416 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6416 | msedge.exe | 104.21.49.25:443 | layemor.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
layemor.com |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6944 | curl.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External IP Lookup by HTTP (api .ipify .org) |
6944 | curl.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
6944 | curl.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup api.ipify.org |
2192 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |