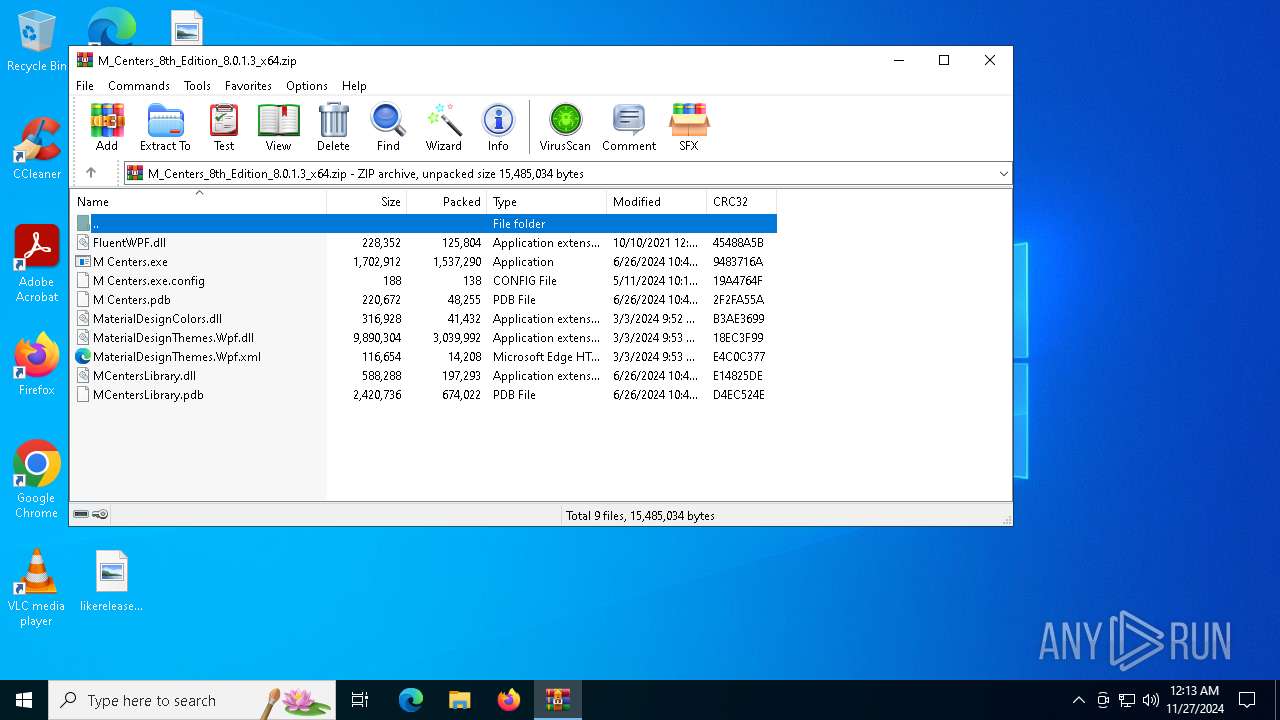
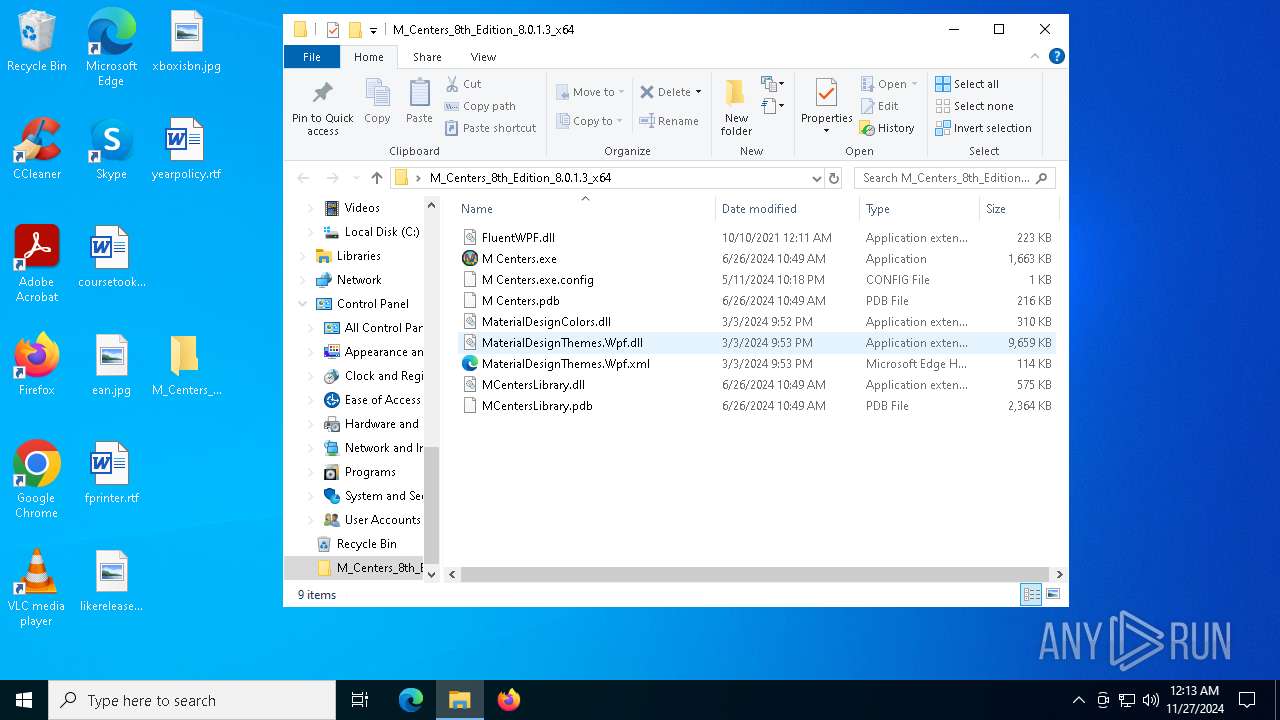
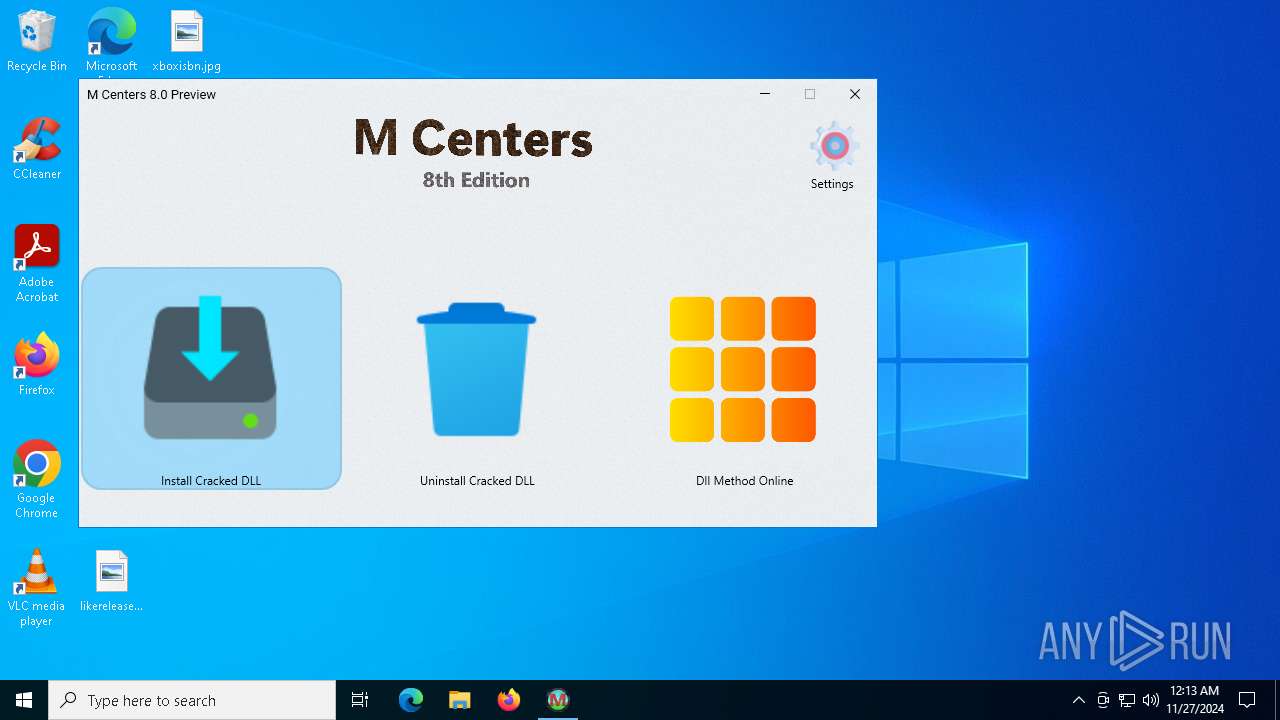
| File name: | M_Centers_8th_Edition_8.0.1.3_x64.zip |
| Full analysis: | https://app.any.run/tasks/c9a42d0e-e3ba-4571-875e-0fdbe95261db |
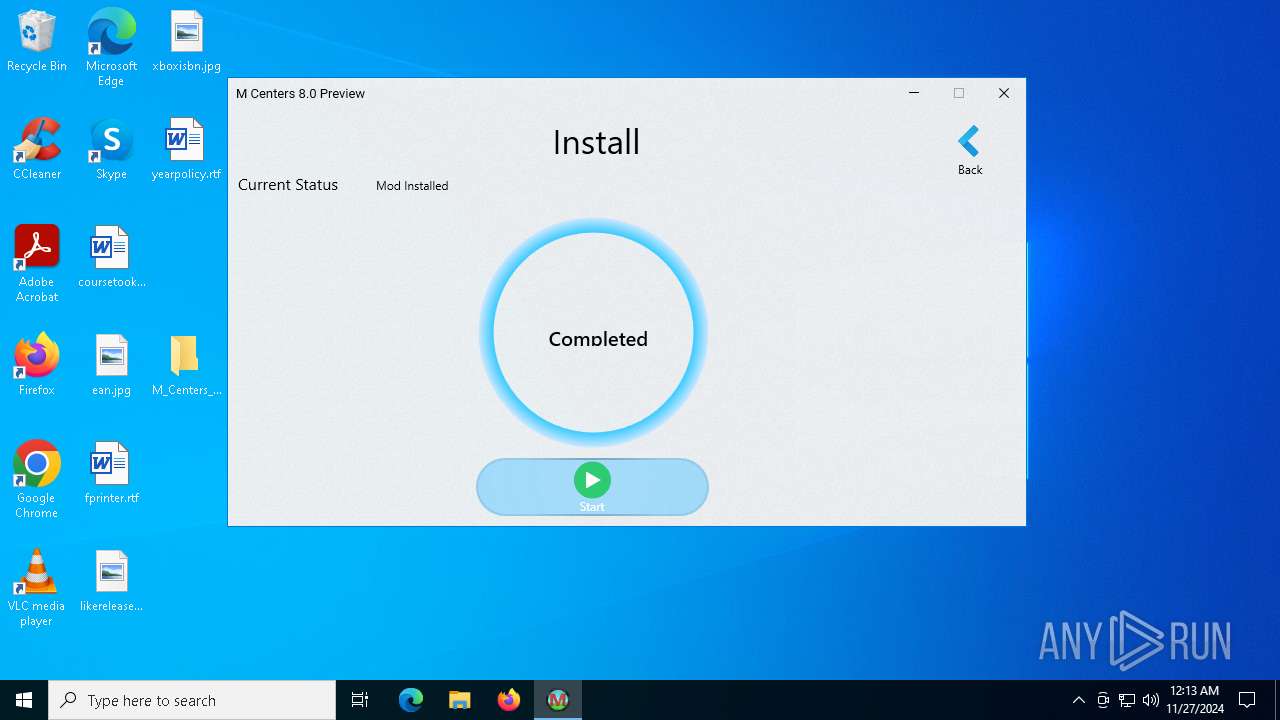
| Verdict: | Malicious activity |
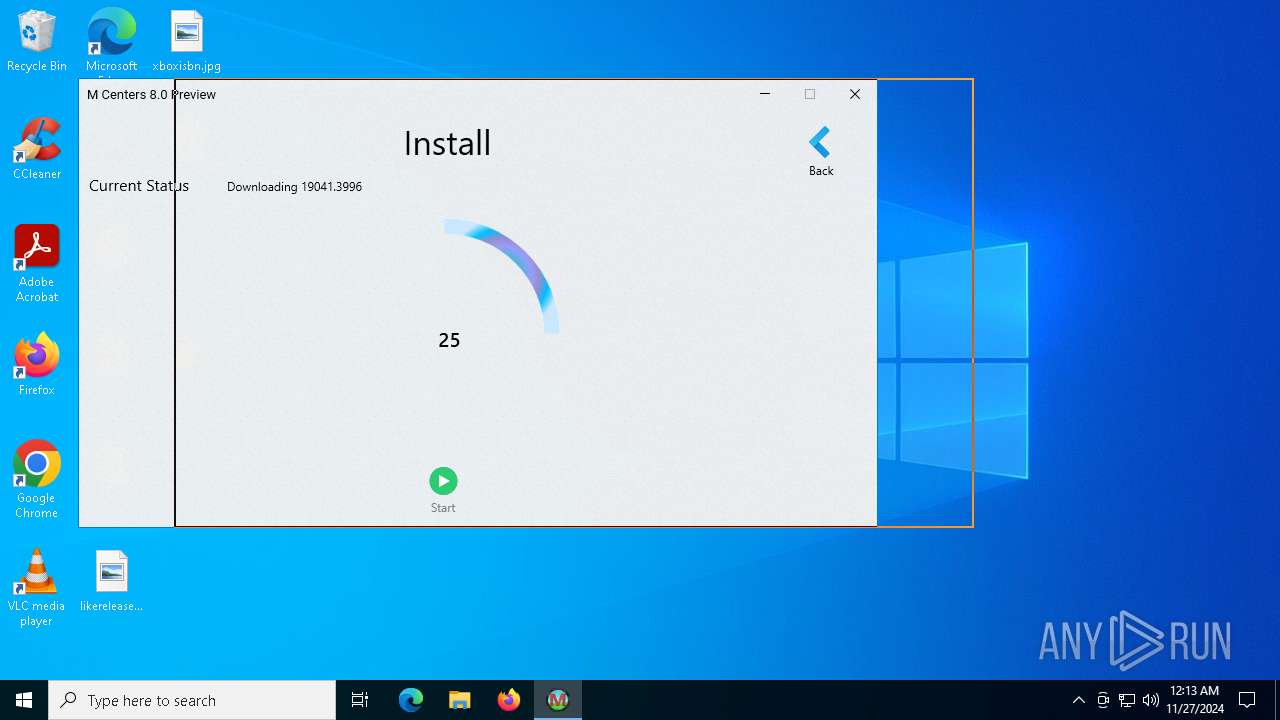
| Analysis date: | November 27, 2024, 00:13:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 45E79C6885617D804B3CD32374B73C35 |
| SHA1: | 4FDBFF28617C4A42DF7584767BB55970CC071411 |
| SHA256: | FD7AF6283FEED5A93D769D404BFC3A6F1F8361823CBB51D12A9EE9A5640AE654 |
| SSDEEP: | 98304:+rdi5SFDA2BoLpKuiZUwHKvCecouqe1QnG43FX1fezTCO8zP8beNokNabAbxAk6Y:UkBT5Ky0KD |
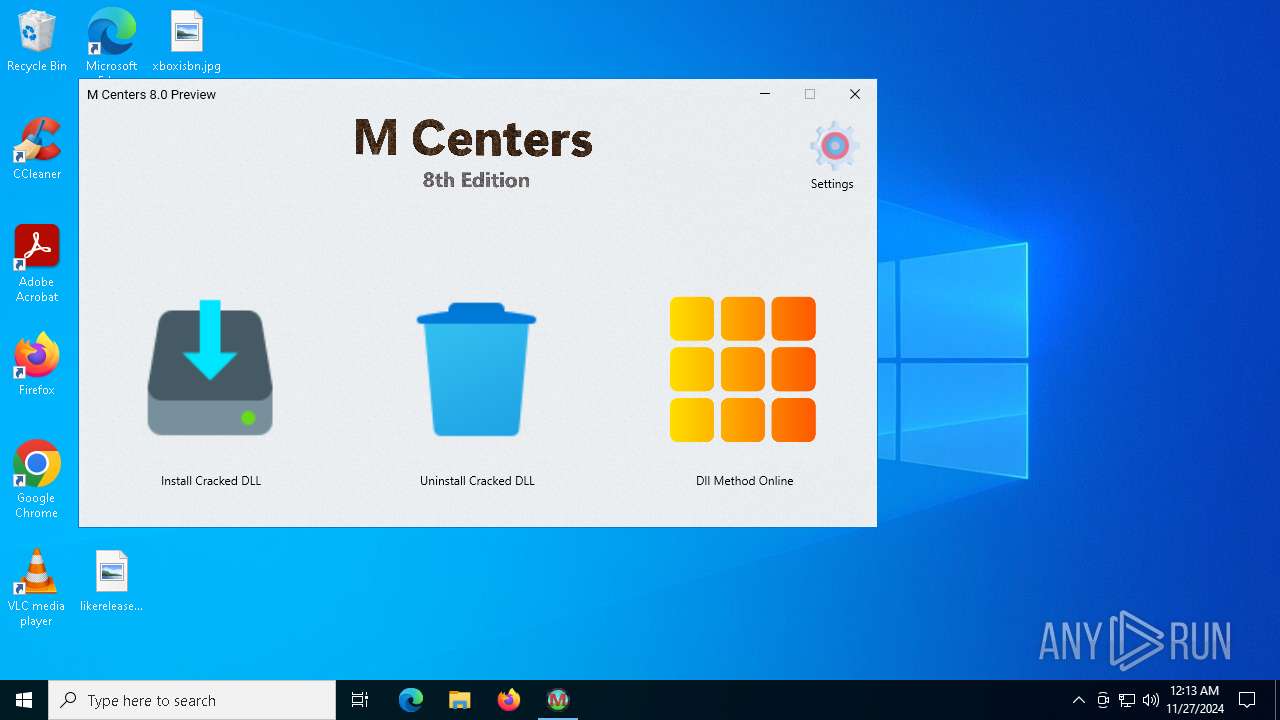
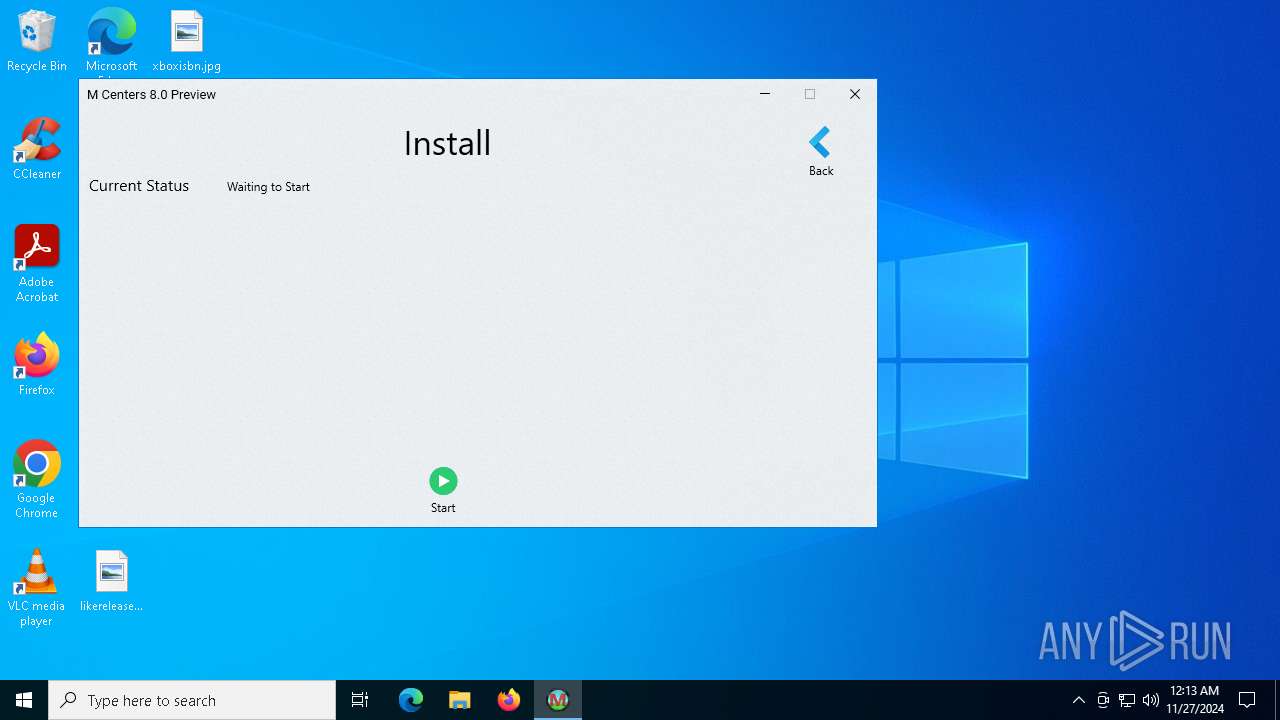
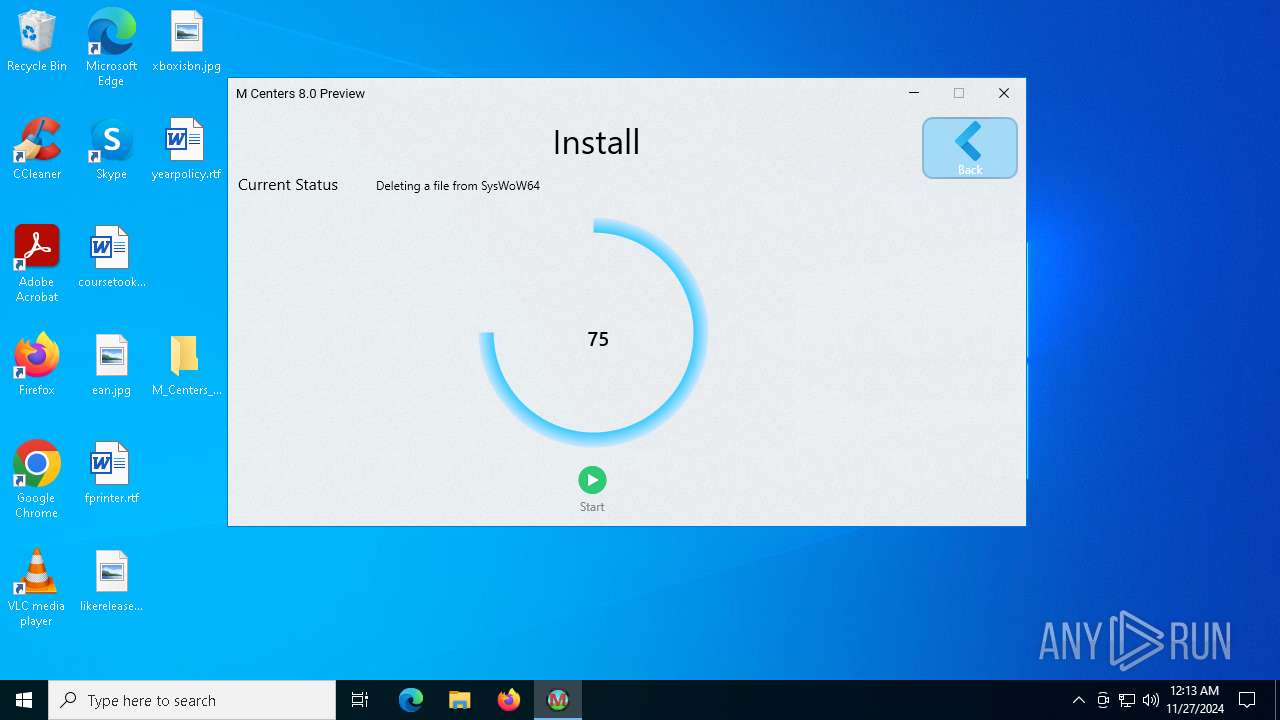
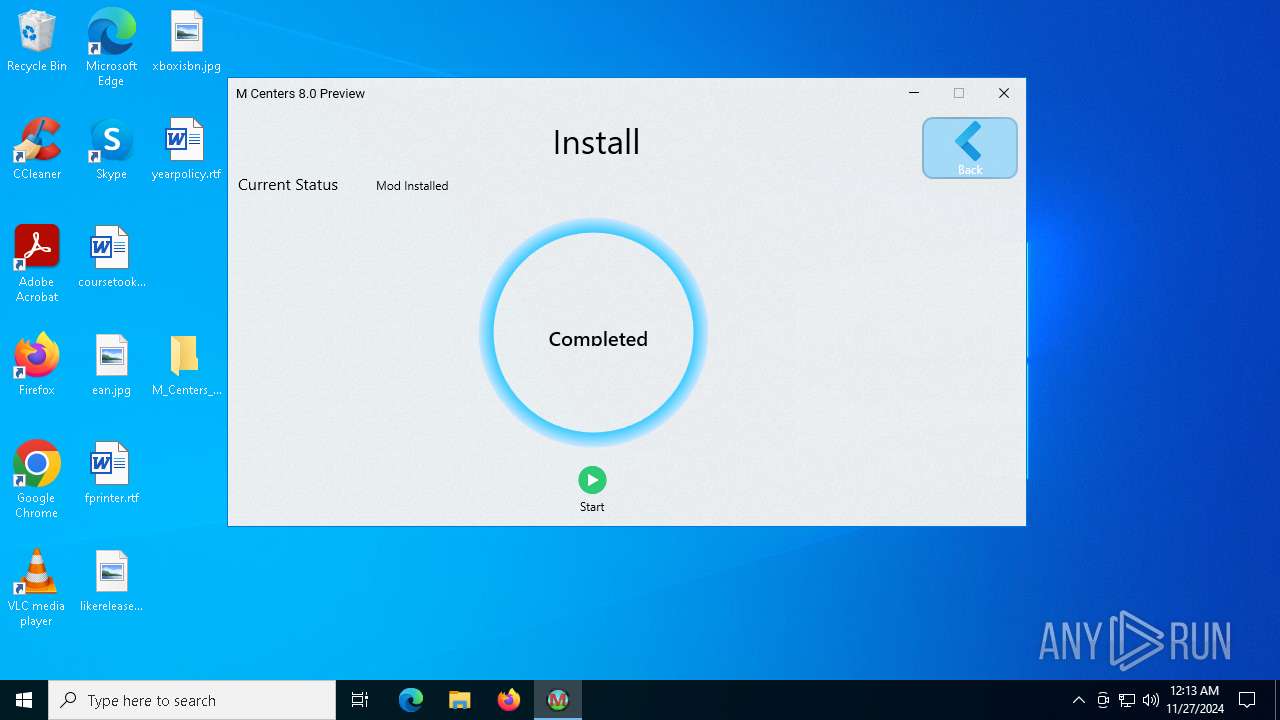
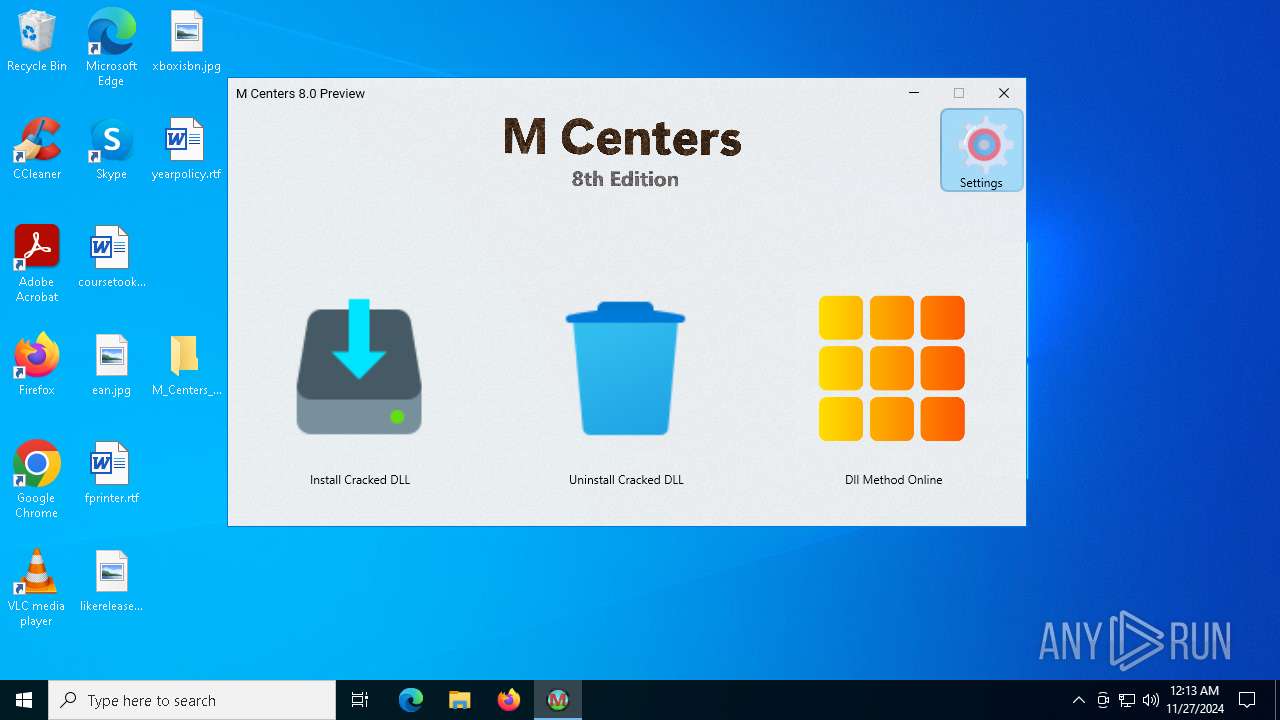
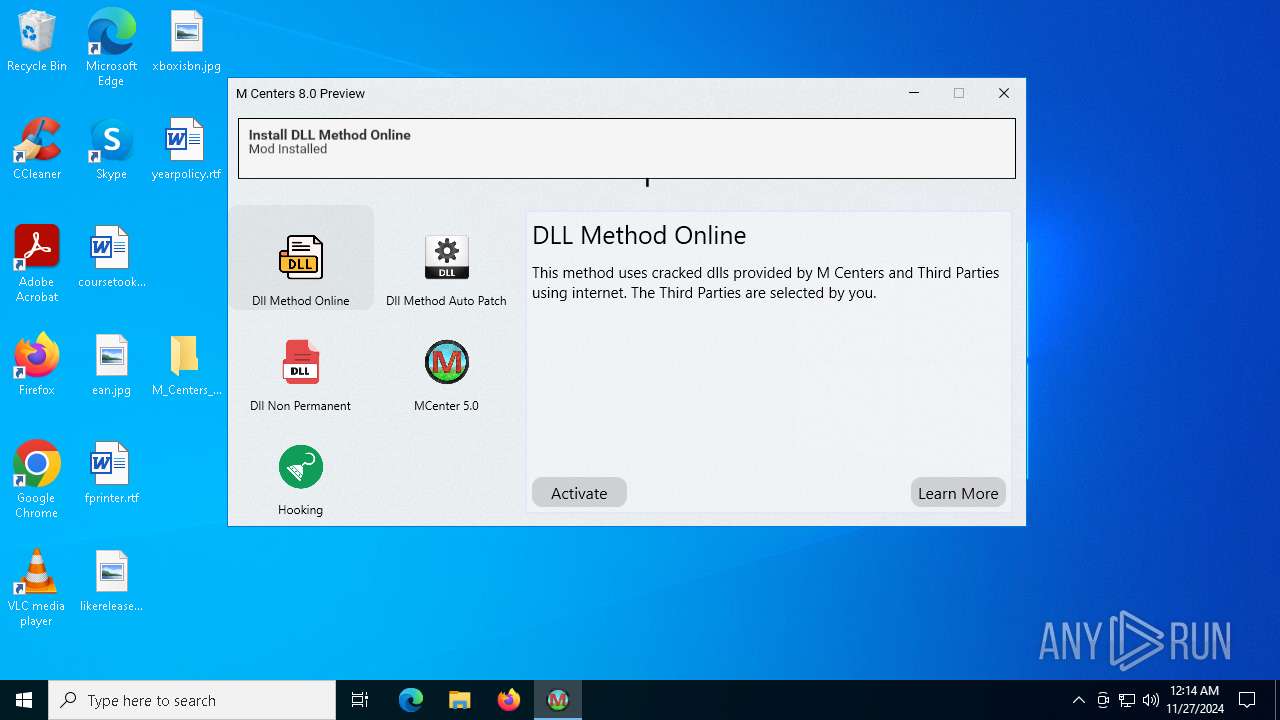
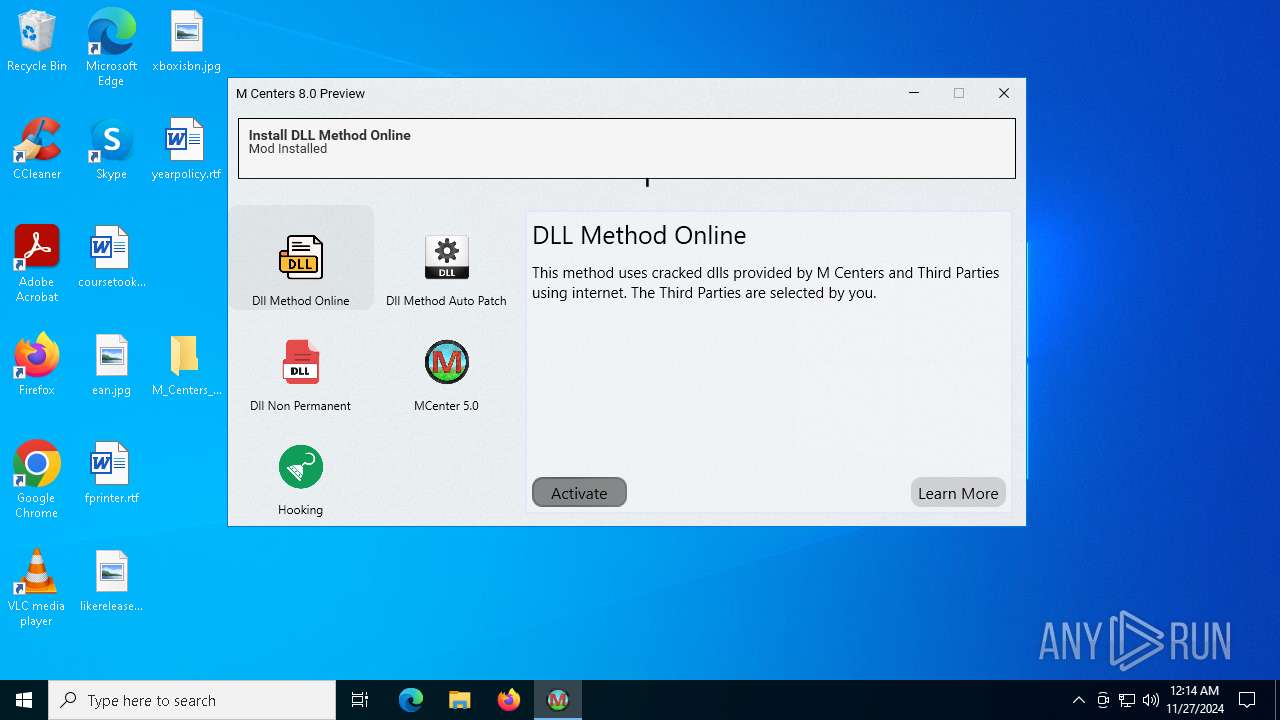
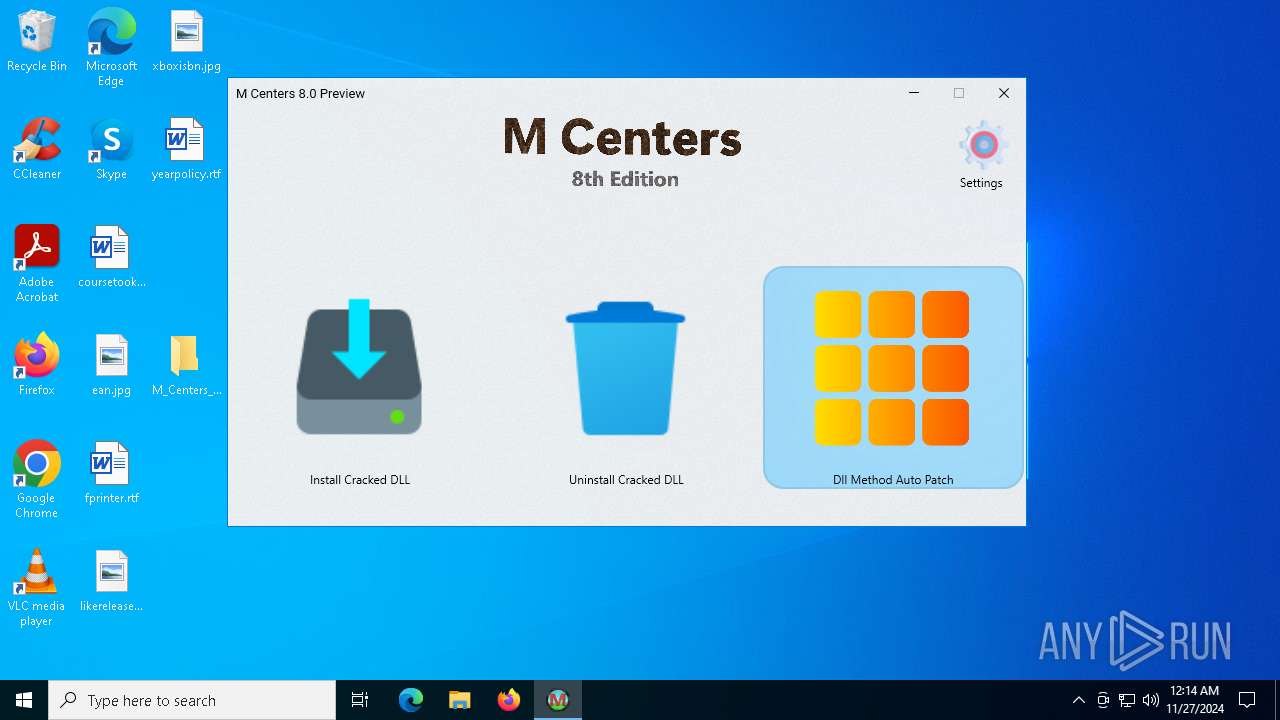
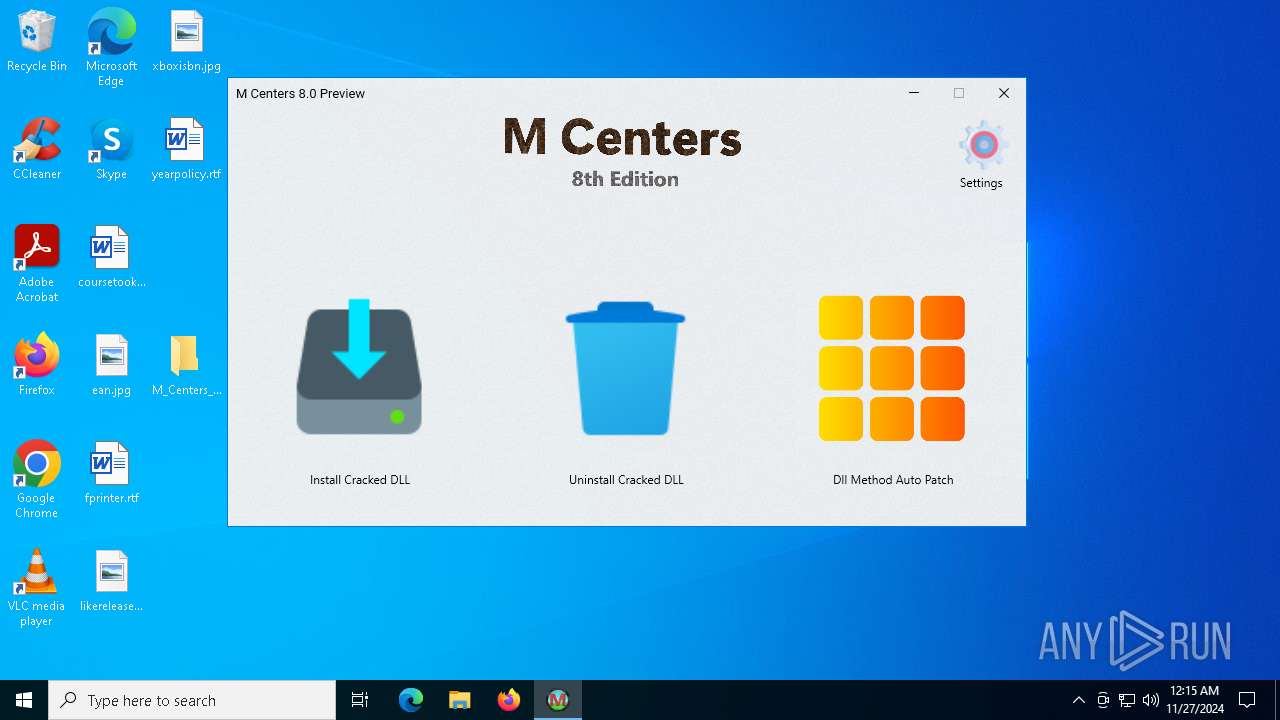
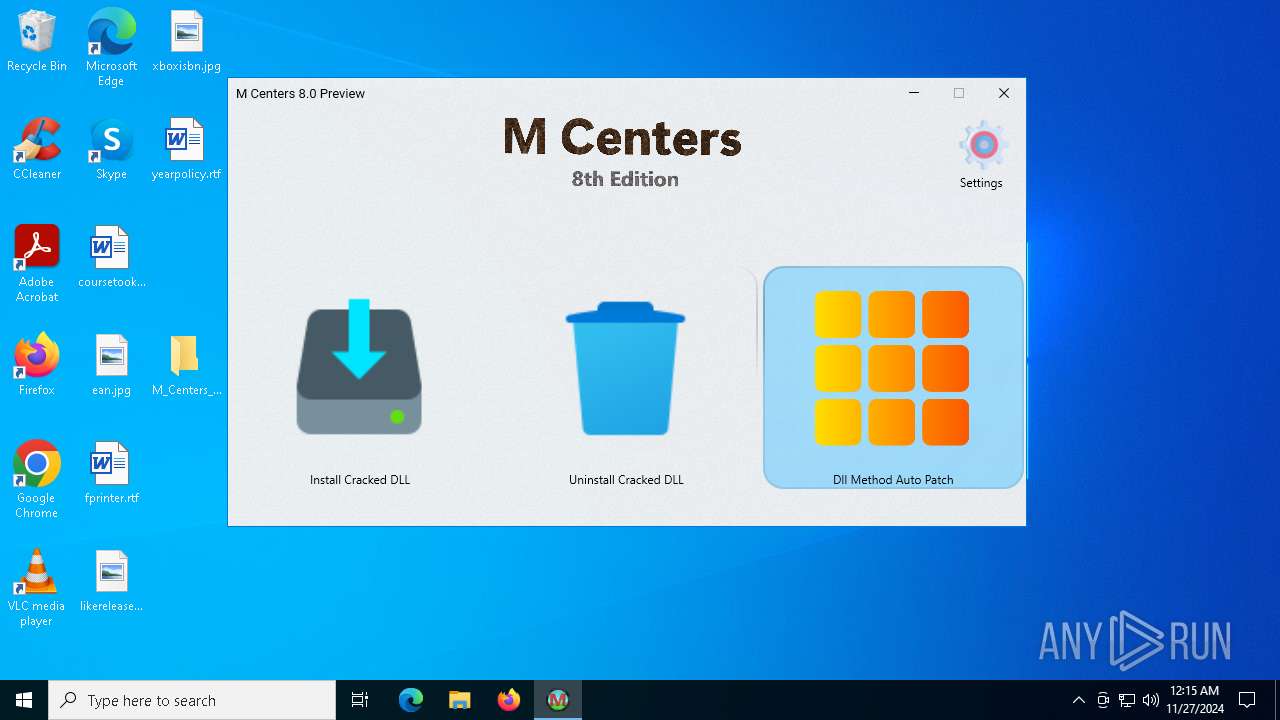
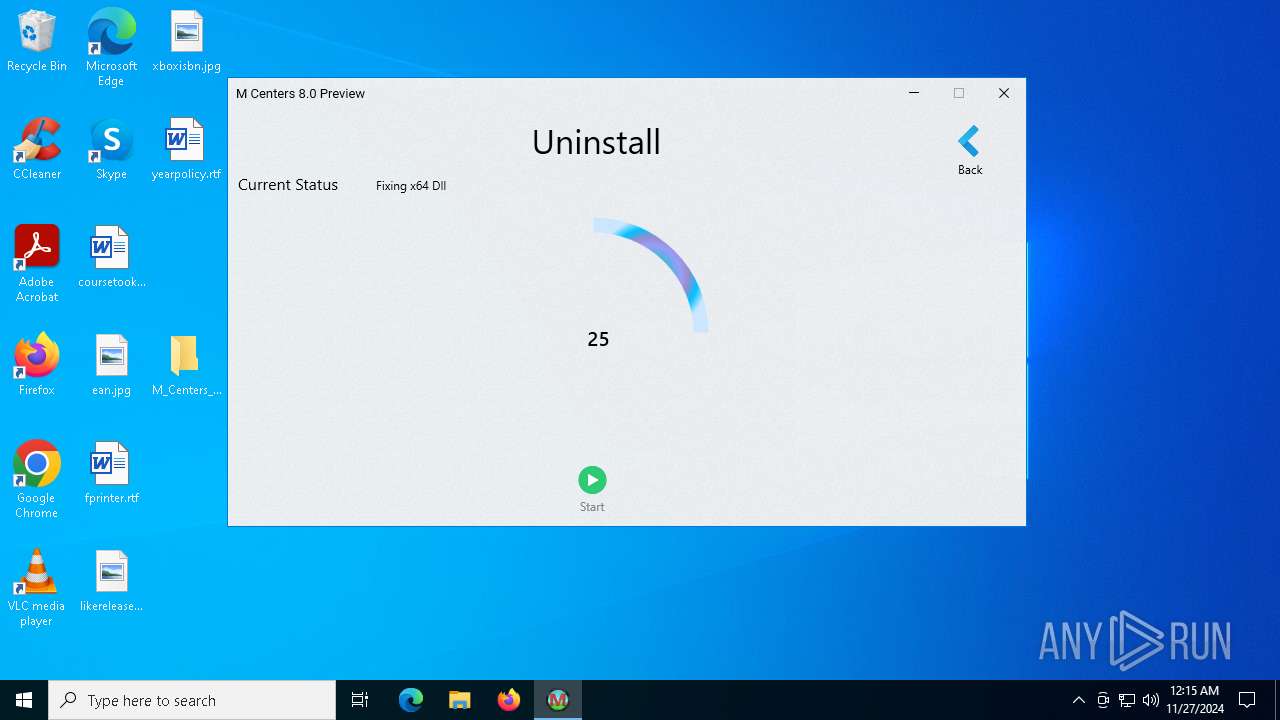
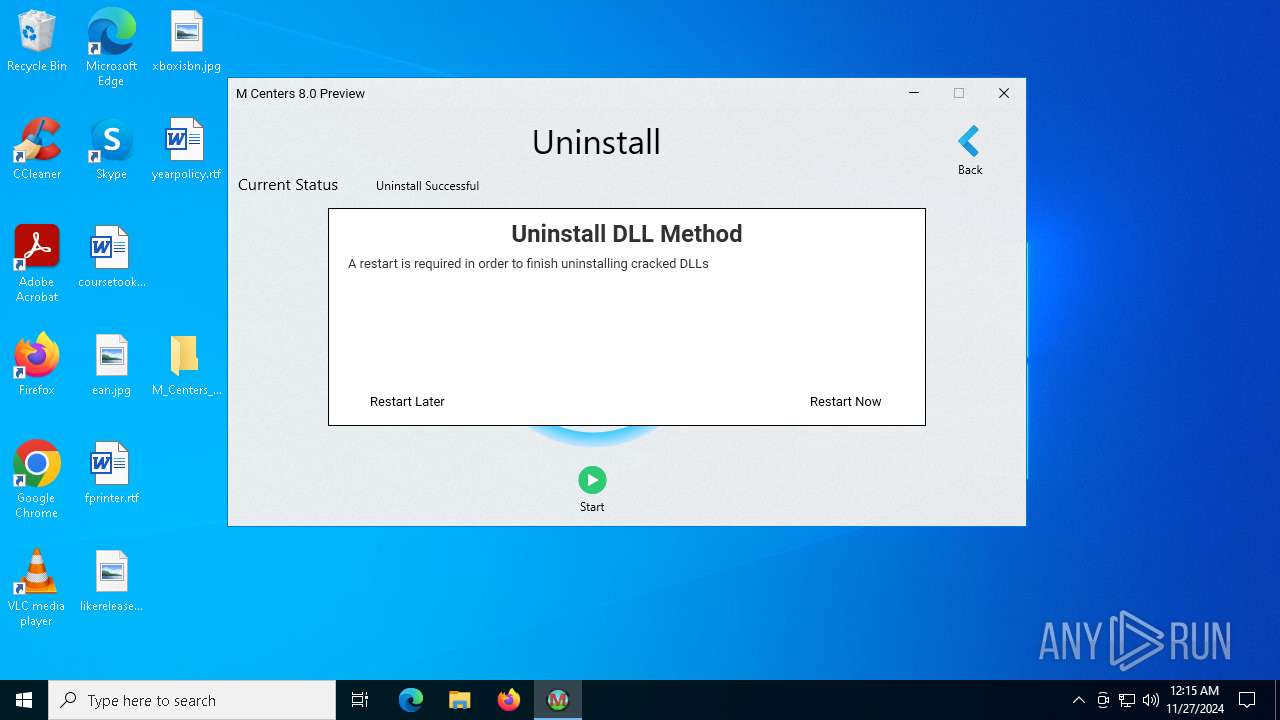
MALICIOUS
Antivirus name has been found in the command line (generic signature)
- sfc.exe (PID: 3884)
- sfc.exe (PID: 6944)
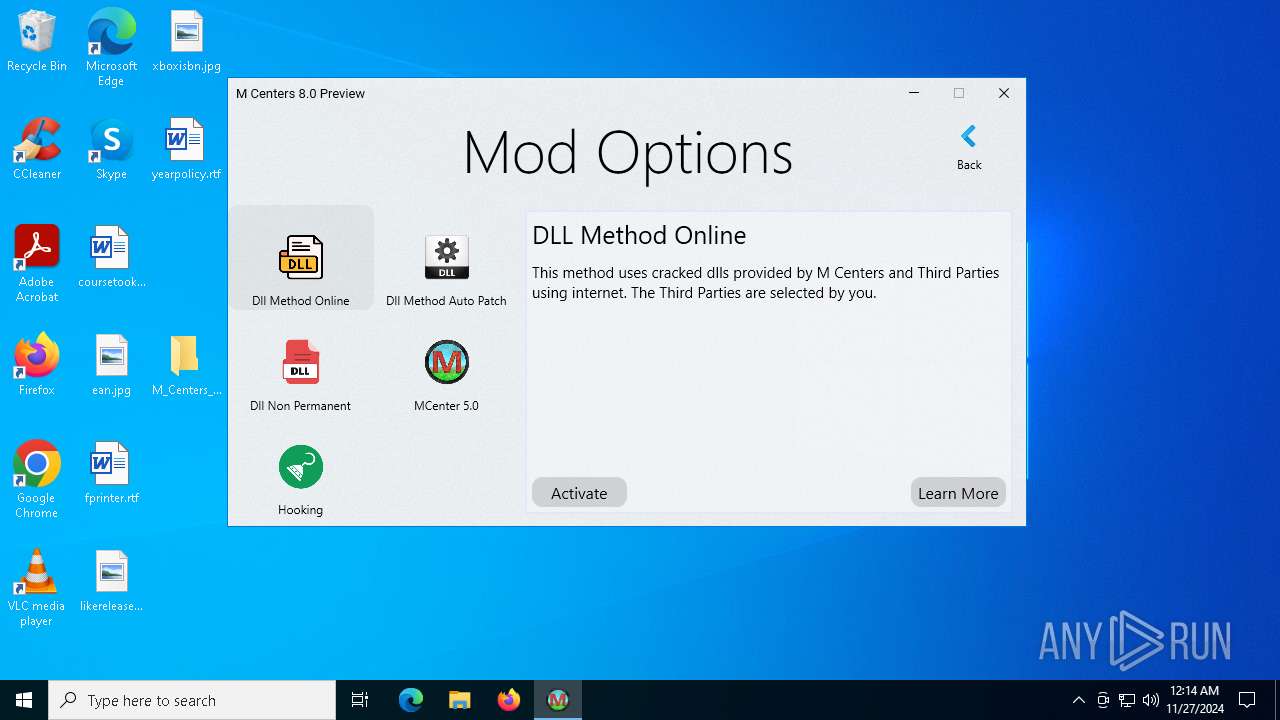
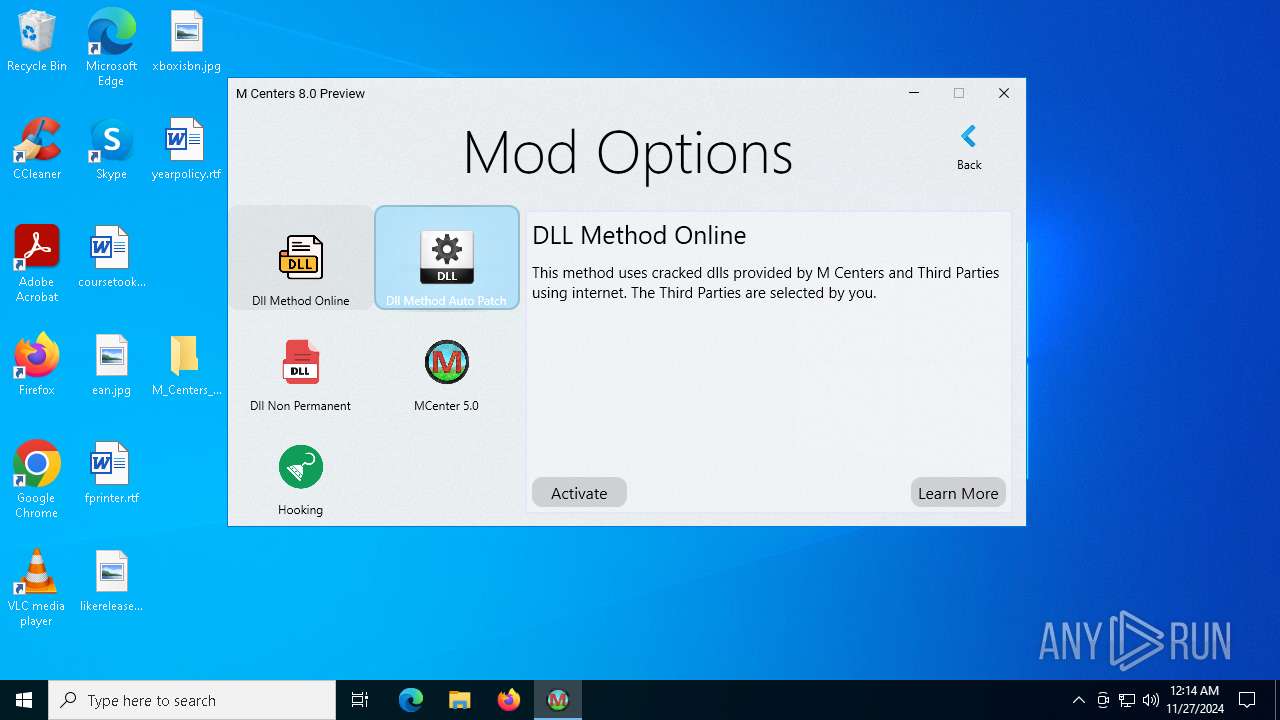
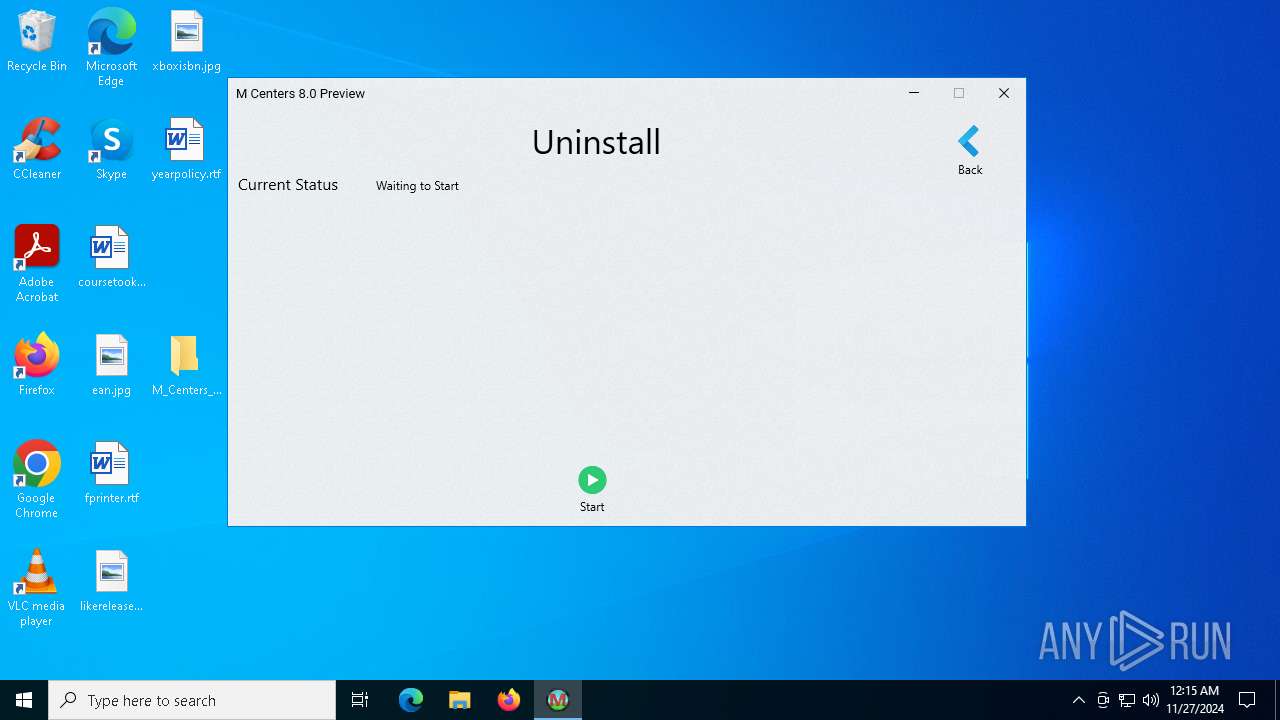
SUSPICIOUS
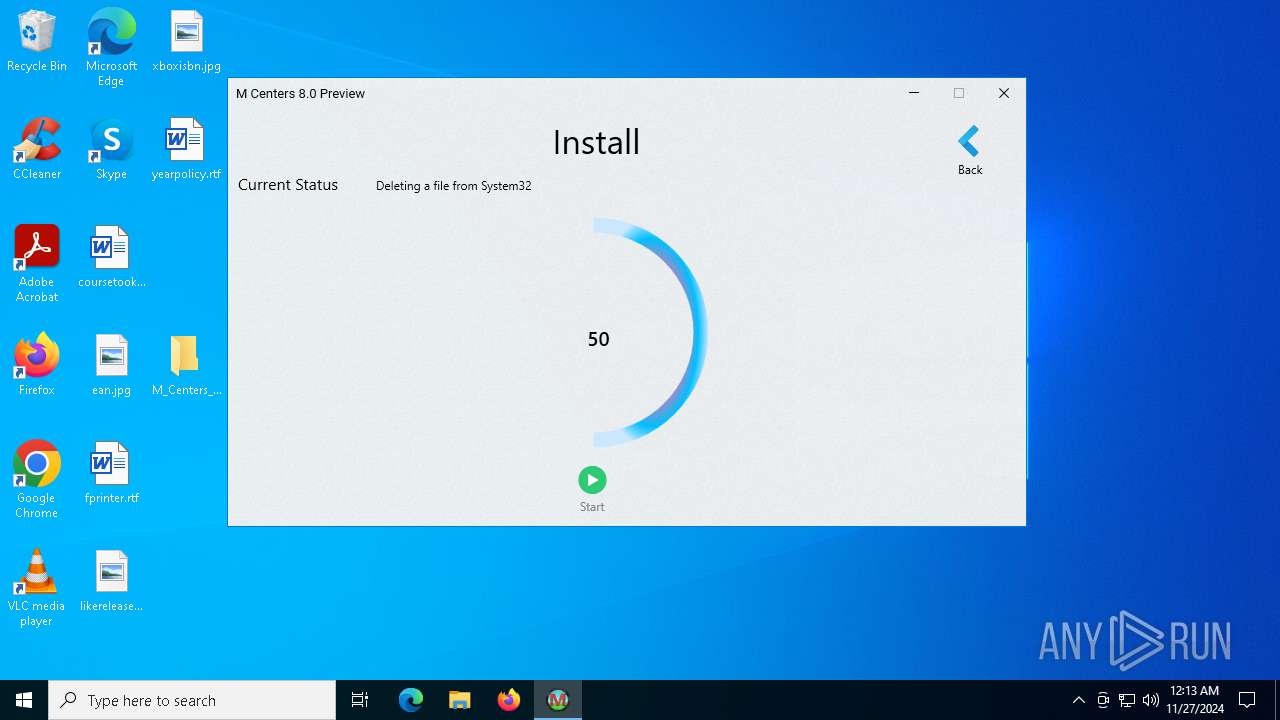
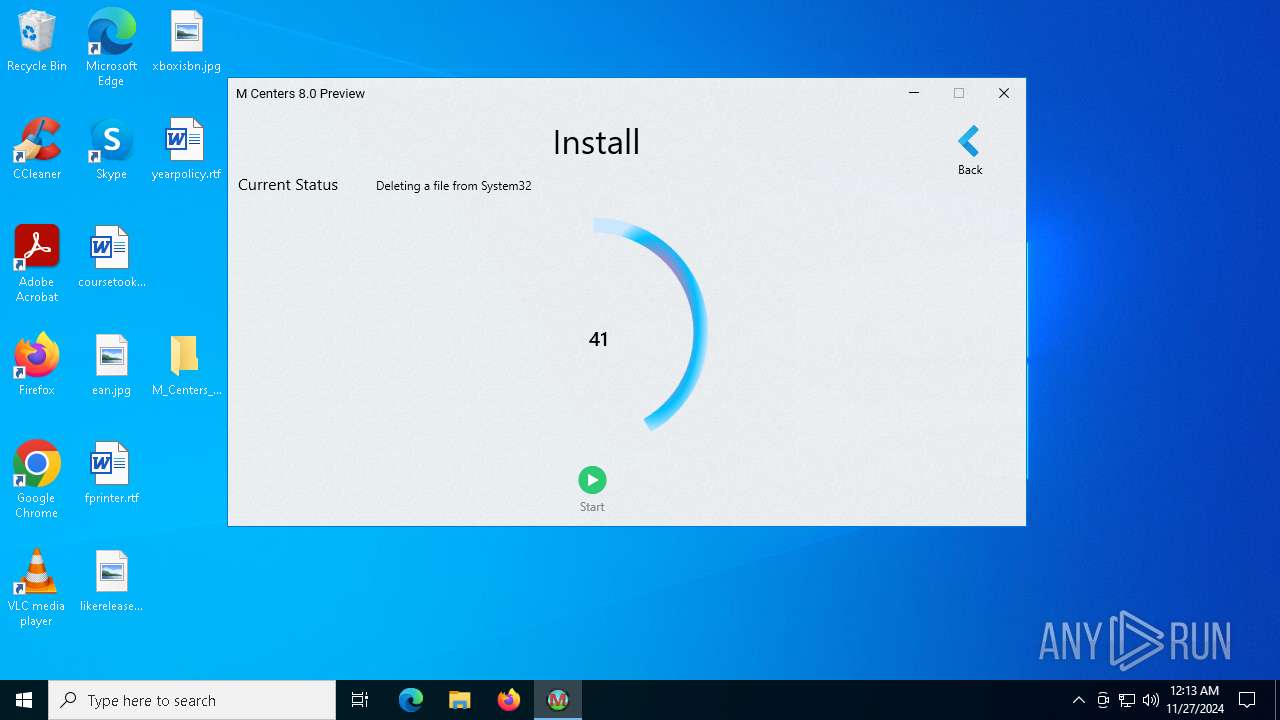
Process drops legitimate windows executable
- M Centers.exe (PID: 7000)
Executable content was dropped or overwritten
- M Centers.exe (PID: 7000)
Uses ICACLS.EXE to modify access control lists
- M Centers.exe (PID: 7000)
Takes ownership (TAKEOWN.EXE)
- M Centers.exe (PID: 7000)
INFO
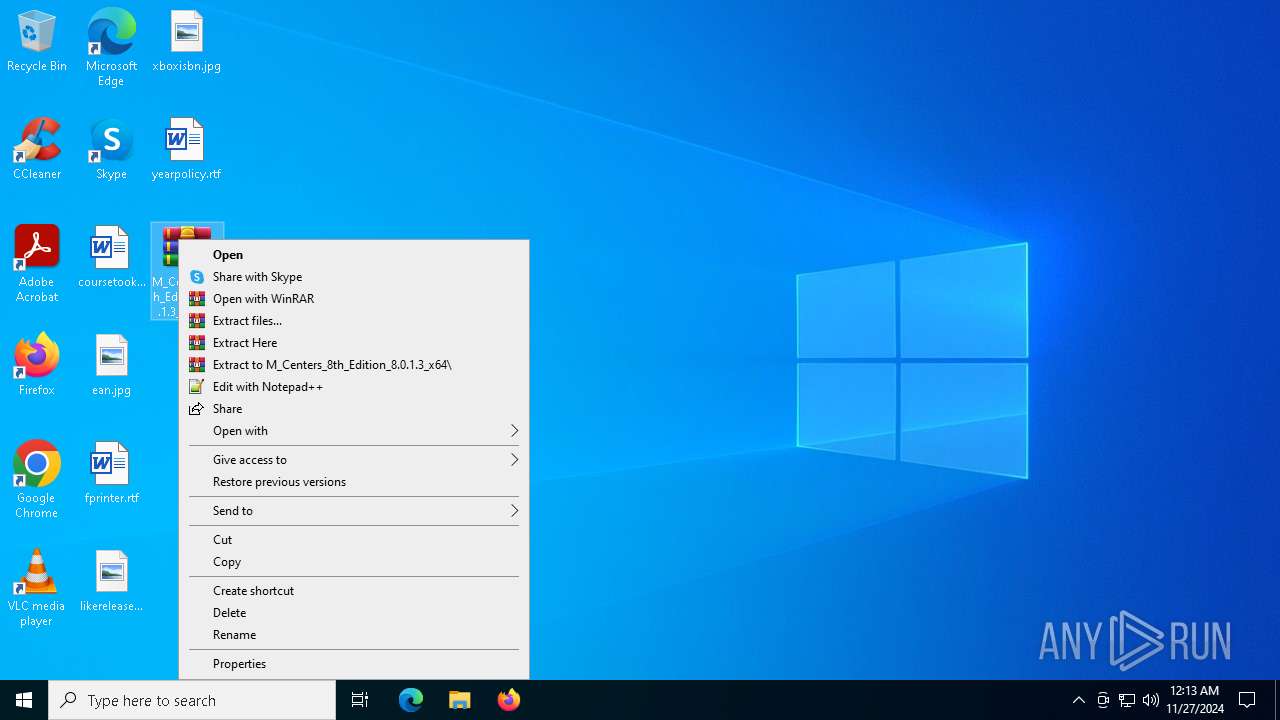
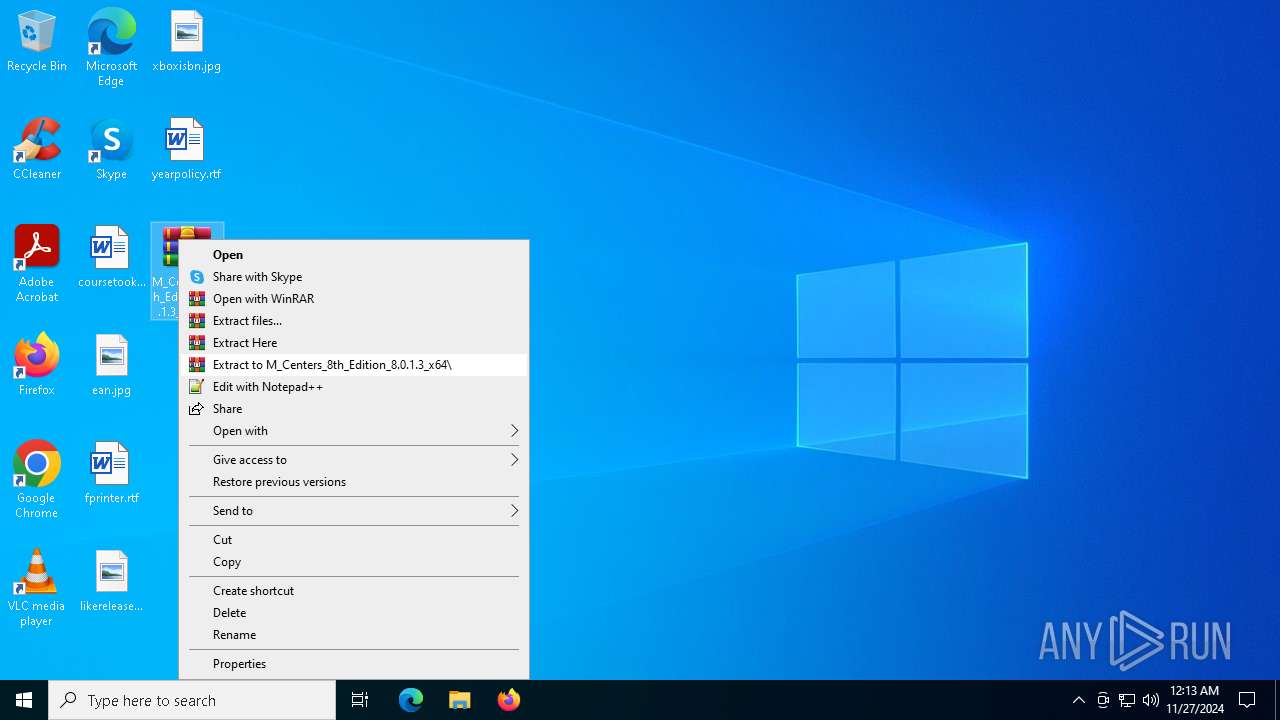
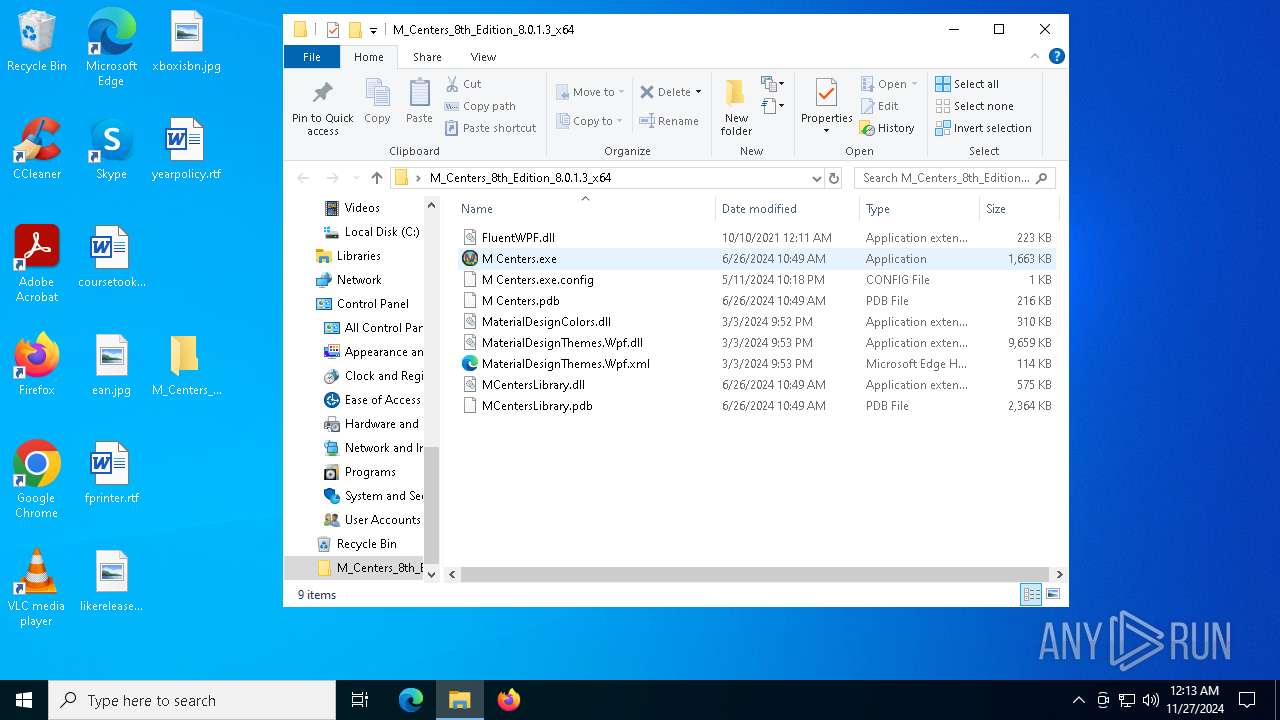
Manual execution by a user
- WinRAR.exe (PID: 6772)
- M Centers.exe (PID: 6948)
- M Centers.exe (PID: 7000)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .kmz | | | Google Earth saved working session (60) |
|---|---|---|
| .zip | | | ZIP compressed archive (40) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2021:10:10 00:11:58 |
| ZipCRC: | 0x45488a5b |
| ZipCompressedSize: | 125804 |
| ZipUncompressedSize: | 228352 |
| ZipFileName: | FluentWPF.dll |
Total processes
152
Monitored processes
26
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 880 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sfc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
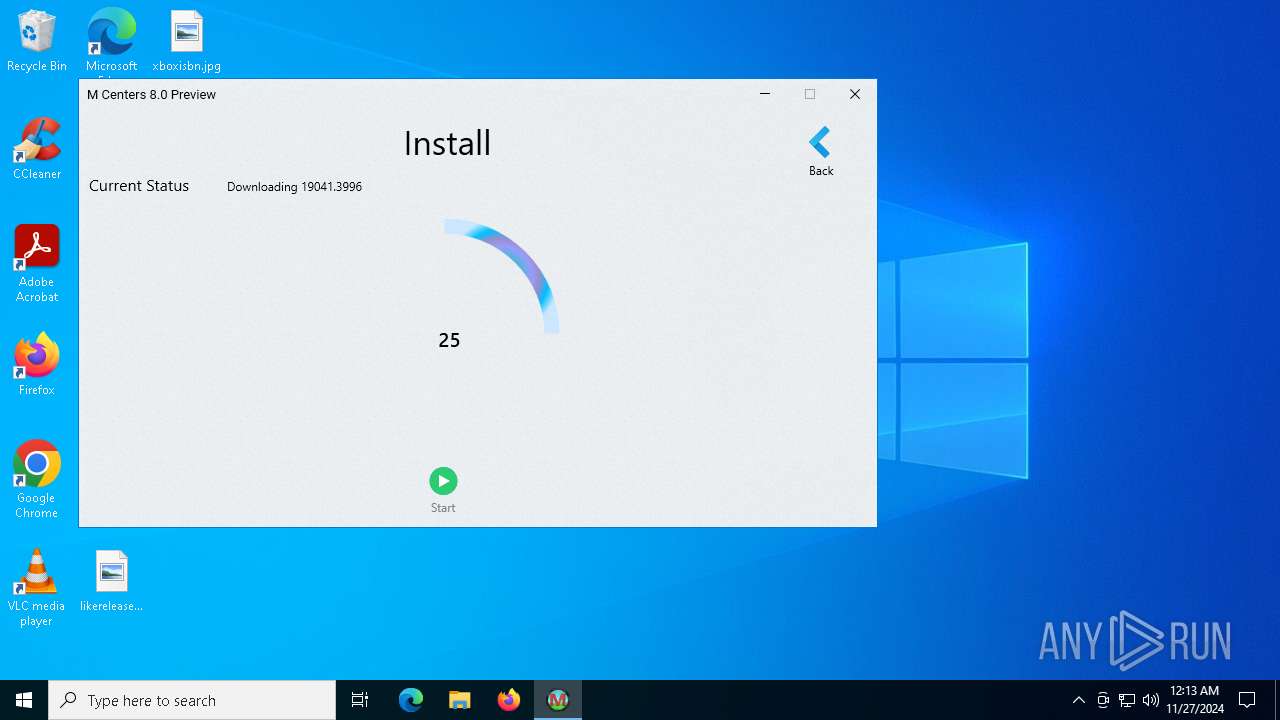
| 1328 | "takeown.exe" /f C:\Windows\SysWOW64\Windows.ApplicationModel.Store.dll /A | C:\Windows\System32\takeown.exe | — | M Centers.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3040 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3076 | "icacls.exe" C:\Windows\System32\Windows.ApplicationModel.Store.dll /grant *S-1-5-32-544:F | C:\Windows\System32\icacls.exe | — | M Centers.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3080 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\M_Centers_8th_Edition_8.0.1.3_x64.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3208 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3532 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3560 | "icacls.exe" C:\Windows\System32\Windows.ApplicationModel.Store.dll /grant *S-1-5-32-544:F | C:\Windows\System32\icacls.exe | — | M Centers.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3564 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | takeown.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3884 | "C:\Windows\System32\sfc.exe" /scanfile=C:\Windows\System32\Windows.ApplicationModel.Store.dll | C:\Windows\System32\sfc.exe | — | M Centers.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: System Integrity Check and Repair Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 676
Read events
3 633
Write events
38
Delete events
5
Modification events
| (PID) Process: | (3080) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3080) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3080) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3080) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\M_Centers_8th_Edition_8.0.1.3_x64.zip | |||
| (PID) Process: | (3080) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3080) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3080) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3080) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3080) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (3080) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
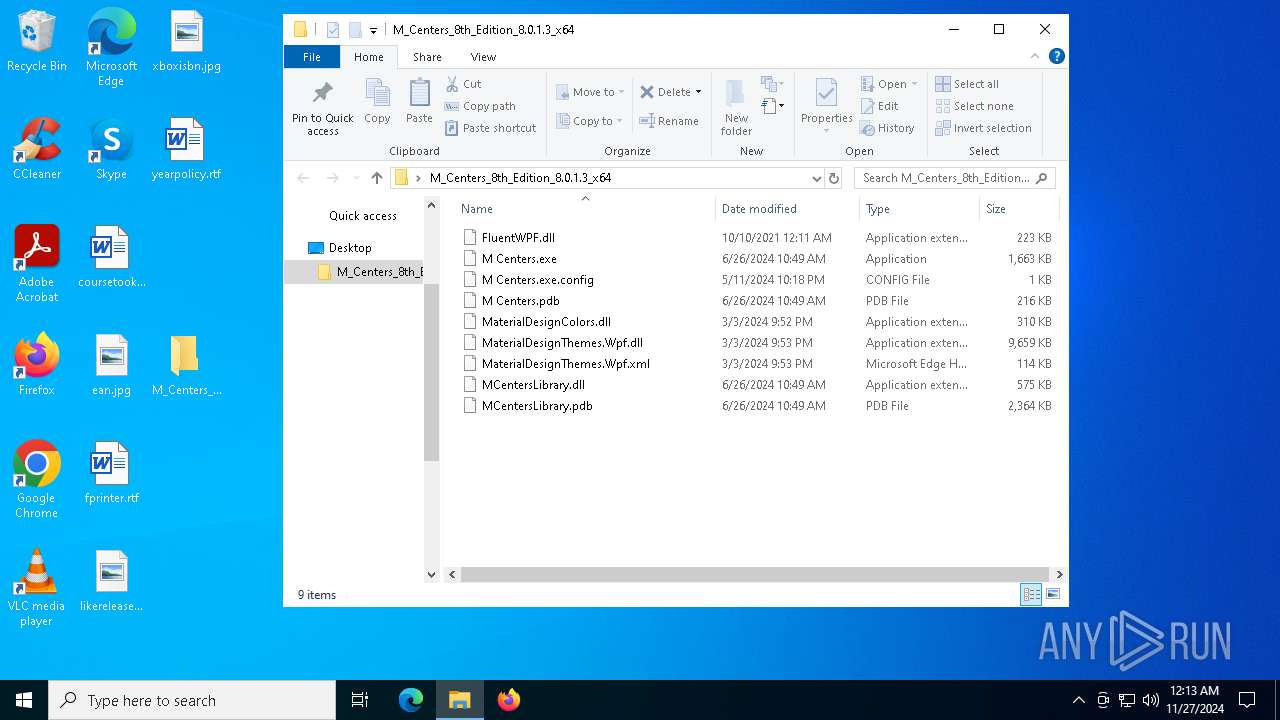
Executable files
9
Suspicious files
2
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6772 | WinRAR.exe | C:\Users\admin\Desktop\M_Centers_8th_Edition_8.0.1.3_x64\M Centers.exe.config | xml | |
MD5:FC89142FBA7697E848F0E0C5951D86F1 | SHA256:D9FF2B6C916E5B42BC486855EEBFBD9E5E409C01D49FC264850FDE2AC9268820 | |||
| 6772 | WinRAR.exe | C:\Users\admin\Desktop\M_Centers_8th_Edition_8.0.1.3_x64\M Centers.pdb | pdb | |
MD5:A0D02EB06DFE43AEF9CB905E2B86EBD9 | SHA256:CA4C956947FDFCAE838FD27CF9A719A97AB43F85AB994FCCB352662ED0AFED37 | |||
| 6772 | WinRAR.exe | C:\Users\admin\Desktop\M_Centers_8th_Edition_8.0.1.3_x64\MCentersLibrary.dll | executable | |
MD5:B7E0FAE475B740863FF755F83C797D81 | SHA256:A72909C32B024DD8304BD62472A18B778411456AF0FC1AC74DE762D1258917E3 | |||
| 6772 | WinRAR.exe | C:\Users\admin\Desktop\M_Centers_8th_Edition_8.0.1.3_x64\FluentWPF.dll | executable | |
MD5:908668FFDE26AB371A2EF711206AA05D | SHA256:8E136EC981ED7D7ABF0C8153DB901FCD9E7A311A61E209D88A9CA2B51FC17838 | |||
| 6772 | WinRAR.exe | C:\Users\admin\Desktop\M_Centers_8th_Edition_8.0.1.3_x64\MaterialDesignThemes.Wpf.dll | executable | |
MD5:05347205B59C343705C5B1DA21D8F9D3 | SHA256:F8144C2D063144A98E6FAA4E4D6F11CB3D08D20313E196CDD03ADDB8186CA6FD | |||
| 7000 | M Centers.exe | C:\ProgramData\MCenters\Methods\Dll\19041.3996\x86\Windows.ApplicationModel.Store.dll | executable | |
MD5:6D7B2C2DFE1403099E5235EAAA0C3920 | SHA256:FC8A582D9CC77AB06854750CCF6BEFA56B63BD1A9AF9E5D192C32BA76328FF57 | |||
| 7000 | M Centers.exe | C:\ProgramData\MCenters\Methods\Dll\19041.3996\x64\Windows.ApplicationModel.Store.dll | executable | |
MD5:6268293D82687B93D89D97FE02BBC41E | SHA256:1A6F46E70BB305B0A0DFDA9D76B38CB9137118DFB6EDF2BBC46F86E38F4B54EC | |||
| 7000 | M Centers.exe | C:\Windows\System32\Windows.ApplicationModel.Store.dll | executable | |
MD5:6268293D82687B93D89D97FE02BBC41E | SHA256:1A6F46E70BB305B0A0DFDA9D76B38CB9137118DFB6EDF2BBC46F86E38F4B54EC | |||
| 3532 | TiWorker.exe | C:\Windows\Logs\CBS\CBS.log | text | |
MD5:C7ACC6CE8D3A75C4266417C22F63CA64 | SHA256:E351A7D593886A2E8BF3BABE0C23FA4EC41E4943E1A0600F5E2D29723B27758E | |||
| 7000 | M Centers.exe | C:\ProgramData\MCenters\Methods\Dll\Records.txt | text | |
MD5:AC225ACB7BED3E9F8BE9DB4040DF455F | SHA256:893CCEC3166BB4D9BD36D9BA1BE7C4EFF4CD2422349FD5431CDD972136A9DA21 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
33
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2548 | svchost.exe | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 1.01 Kb | whitelisted |
2548 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
6236 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
236 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
236 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 418 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2548 | svchost.exe | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
2548 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 2.23.209.133:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
raw.githubusercontent.com |
| shared |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |