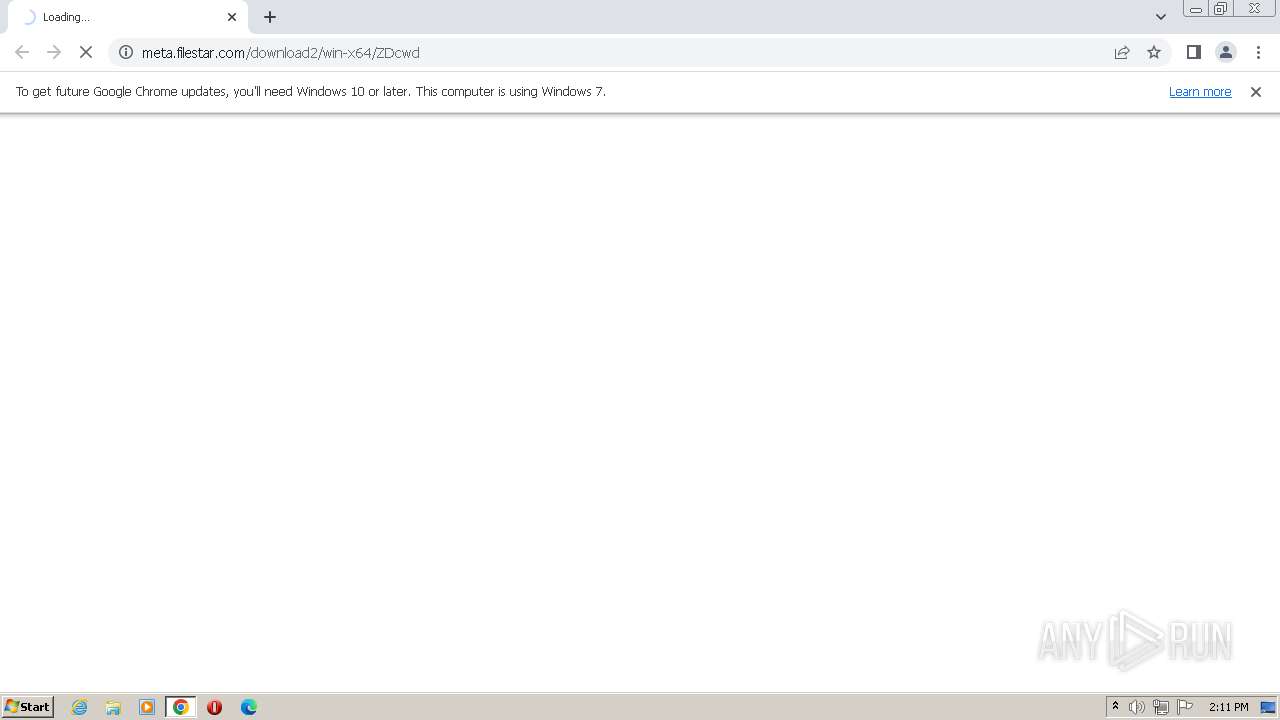
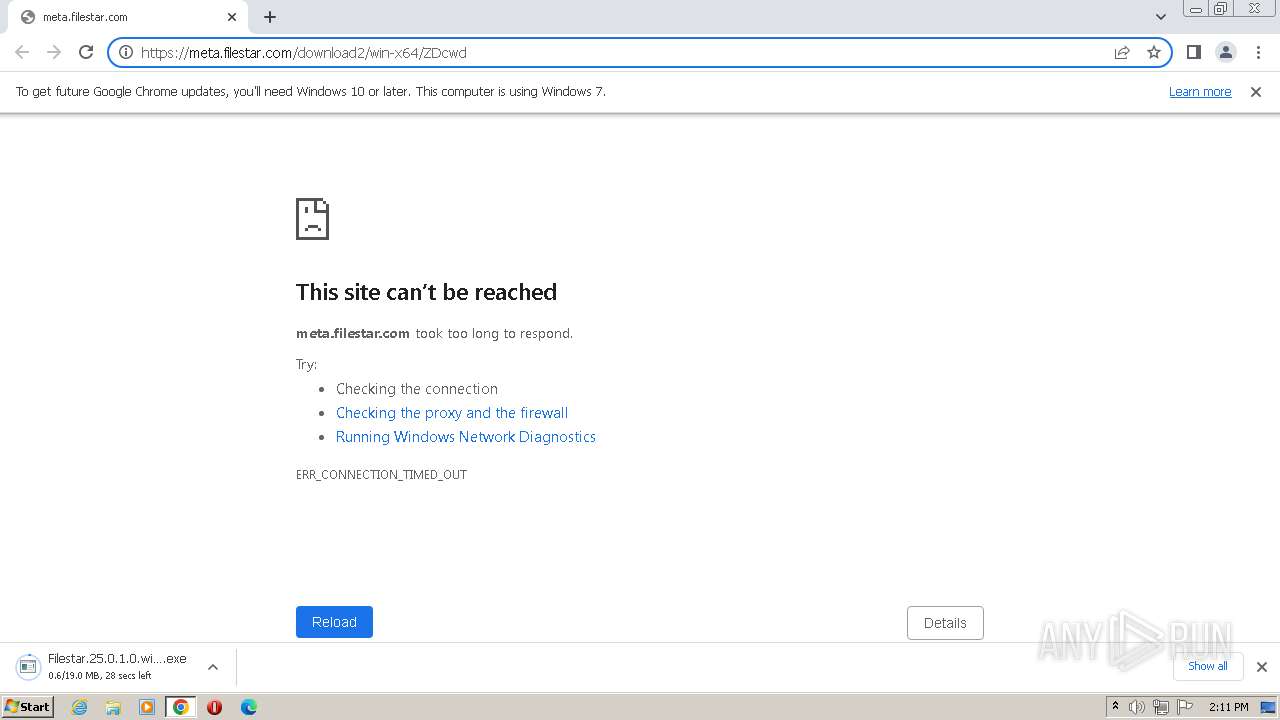
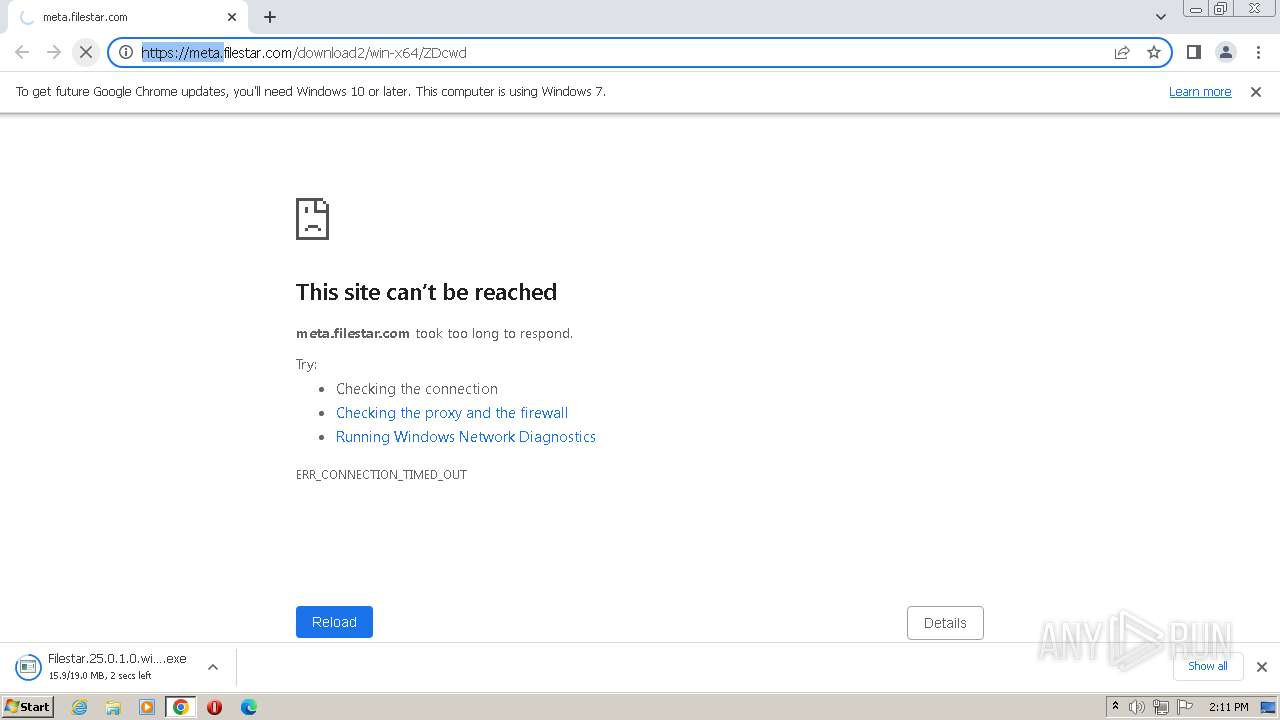
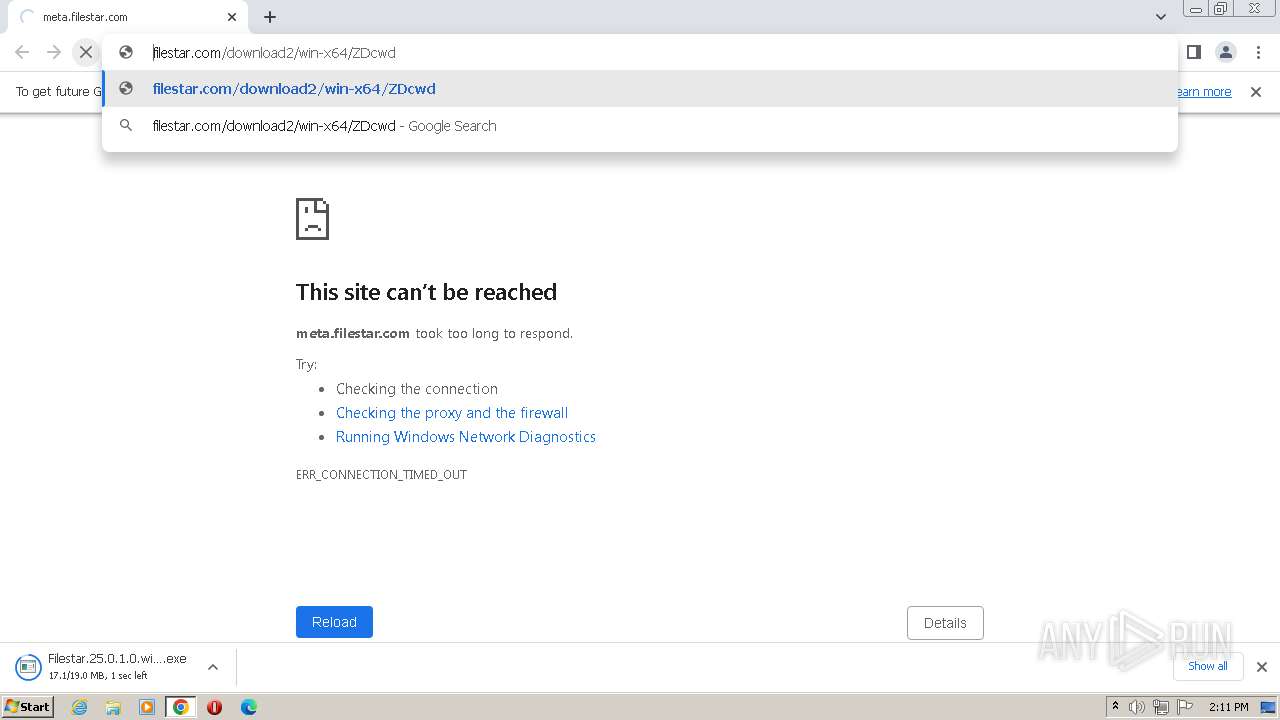
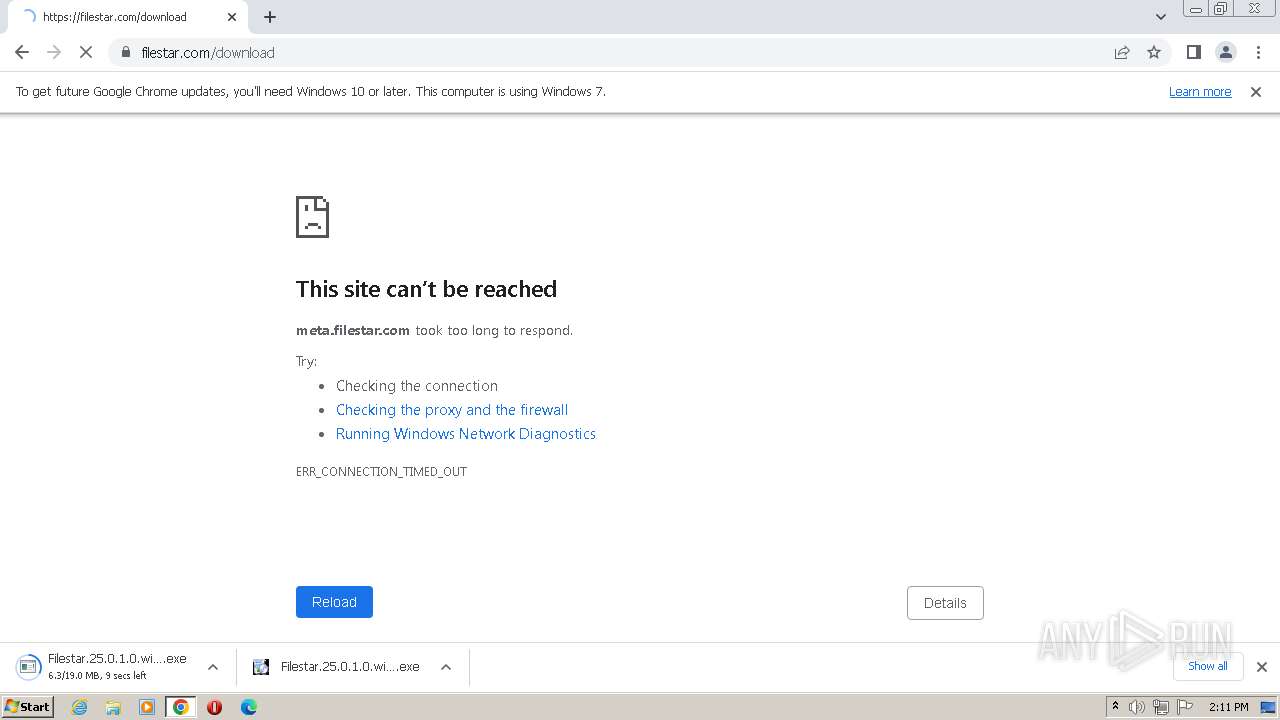
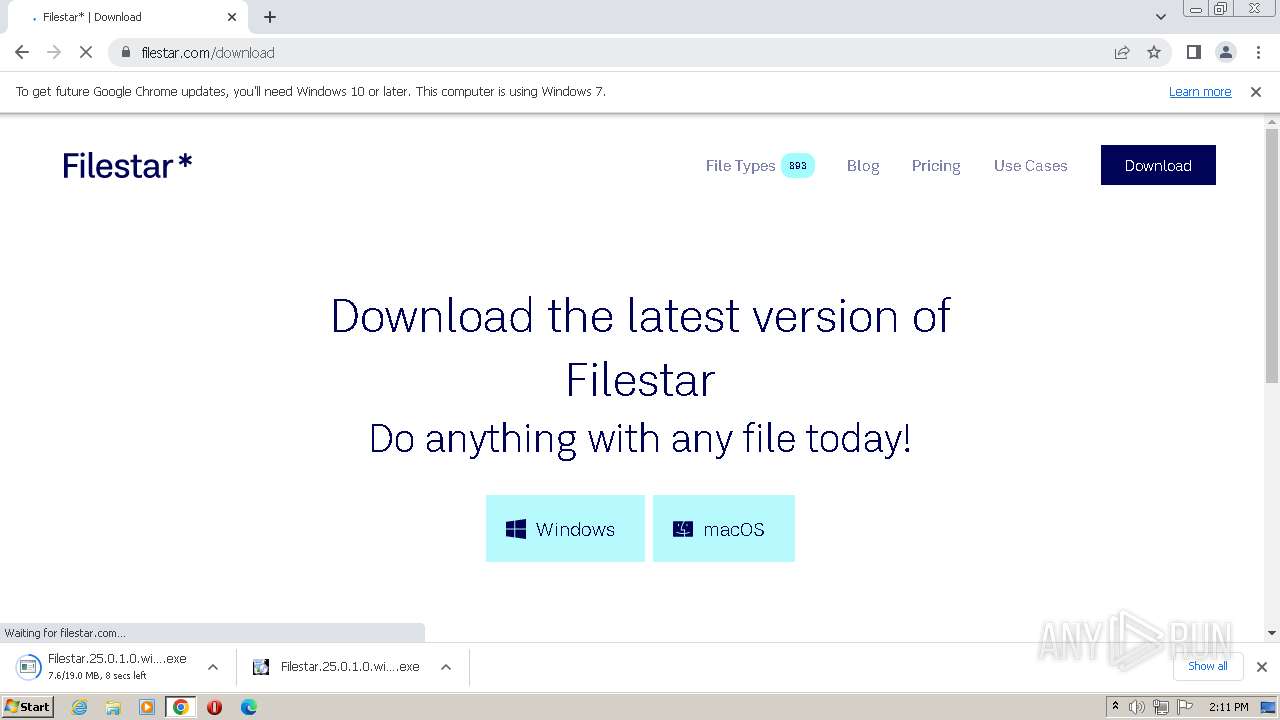
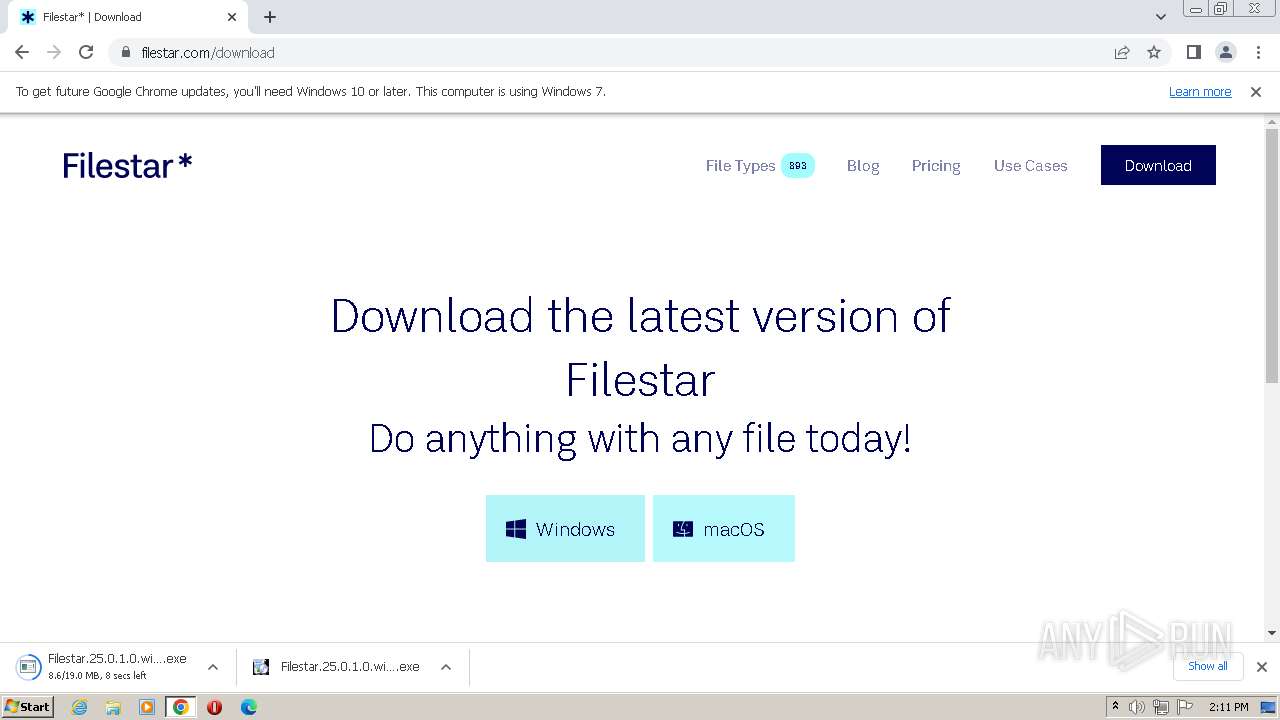
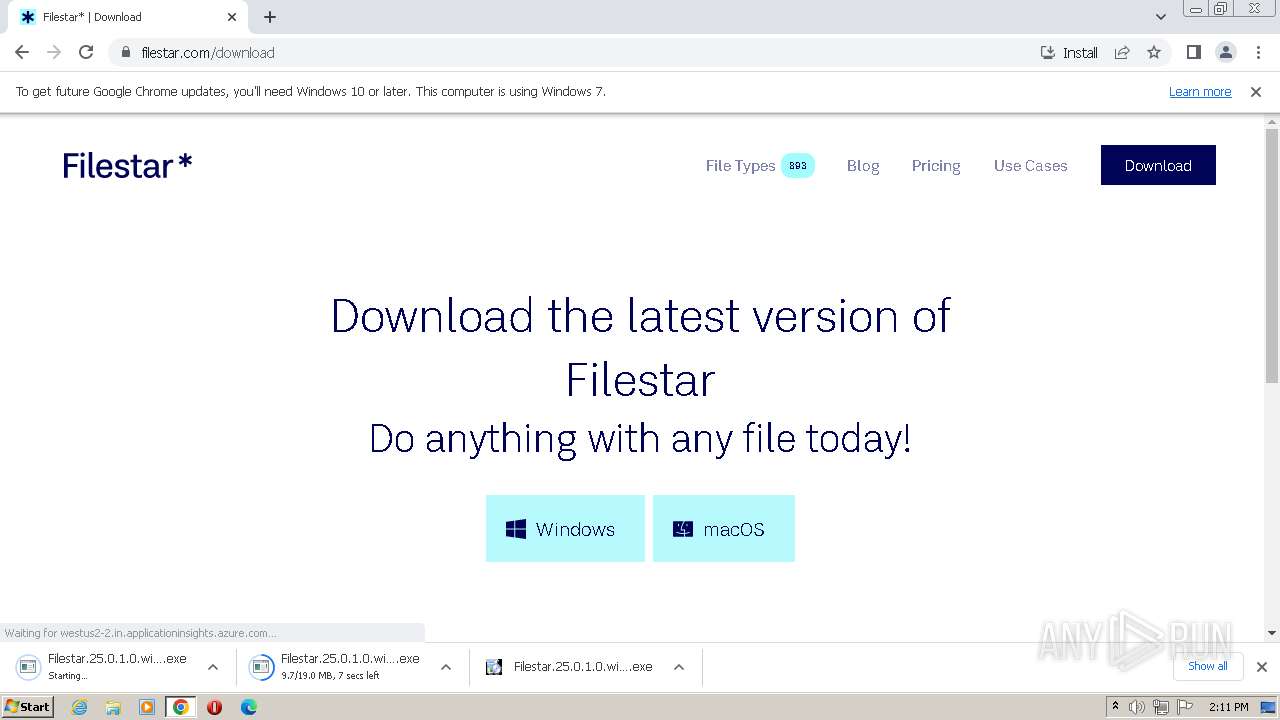
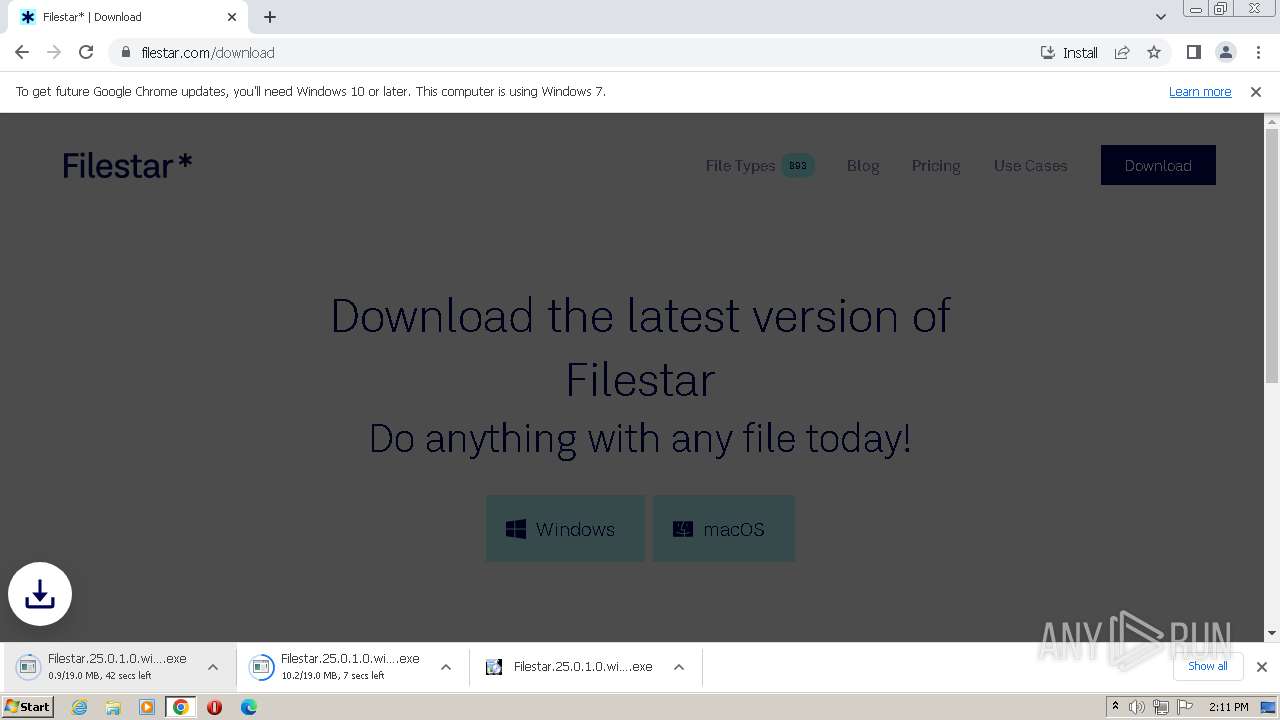
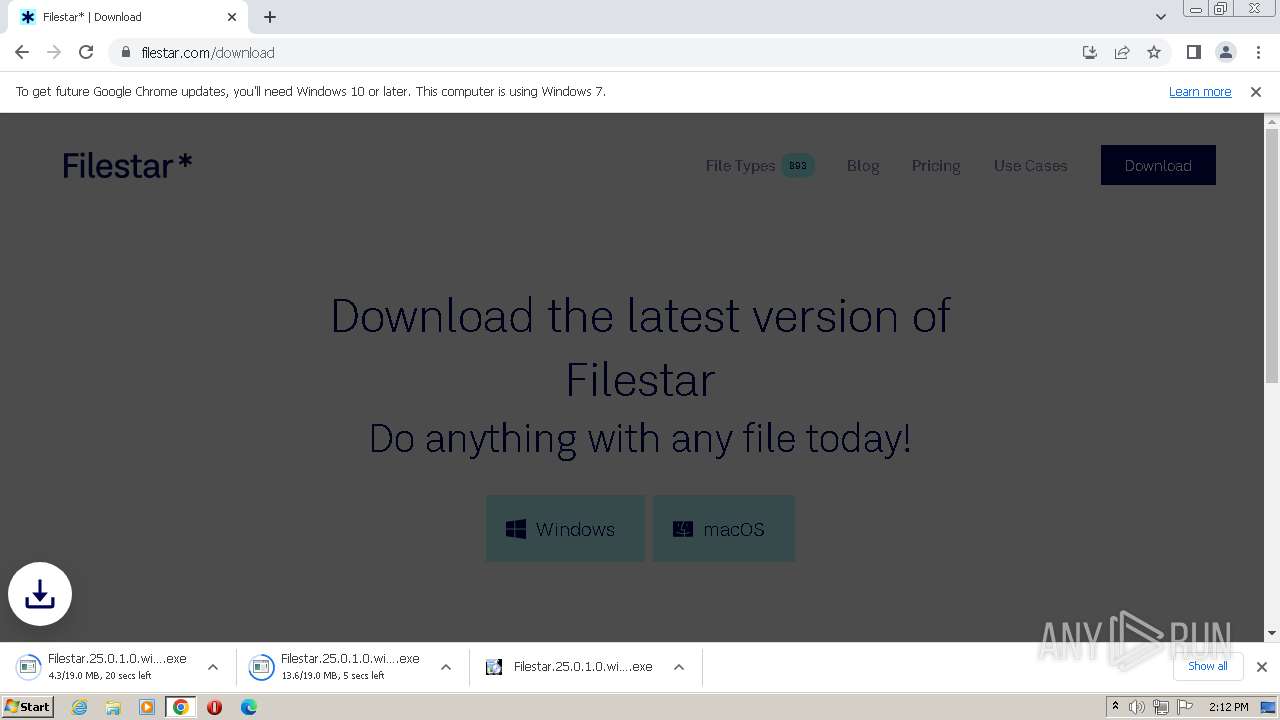
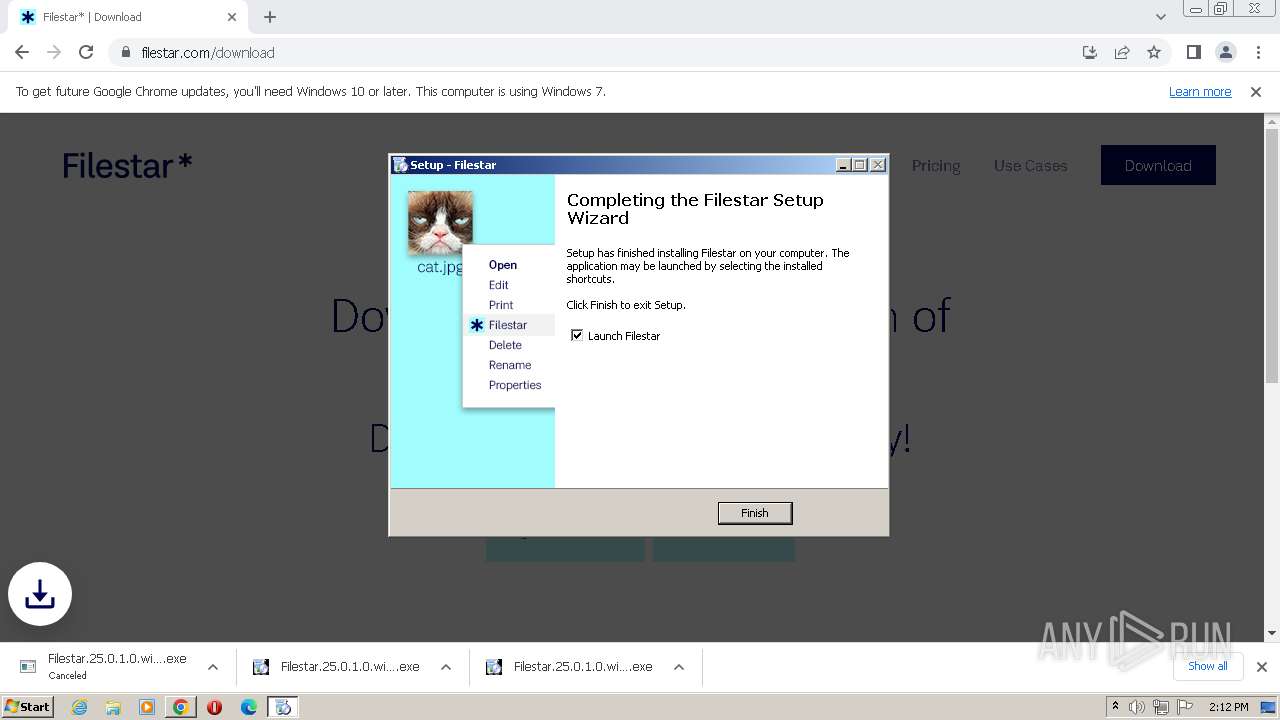
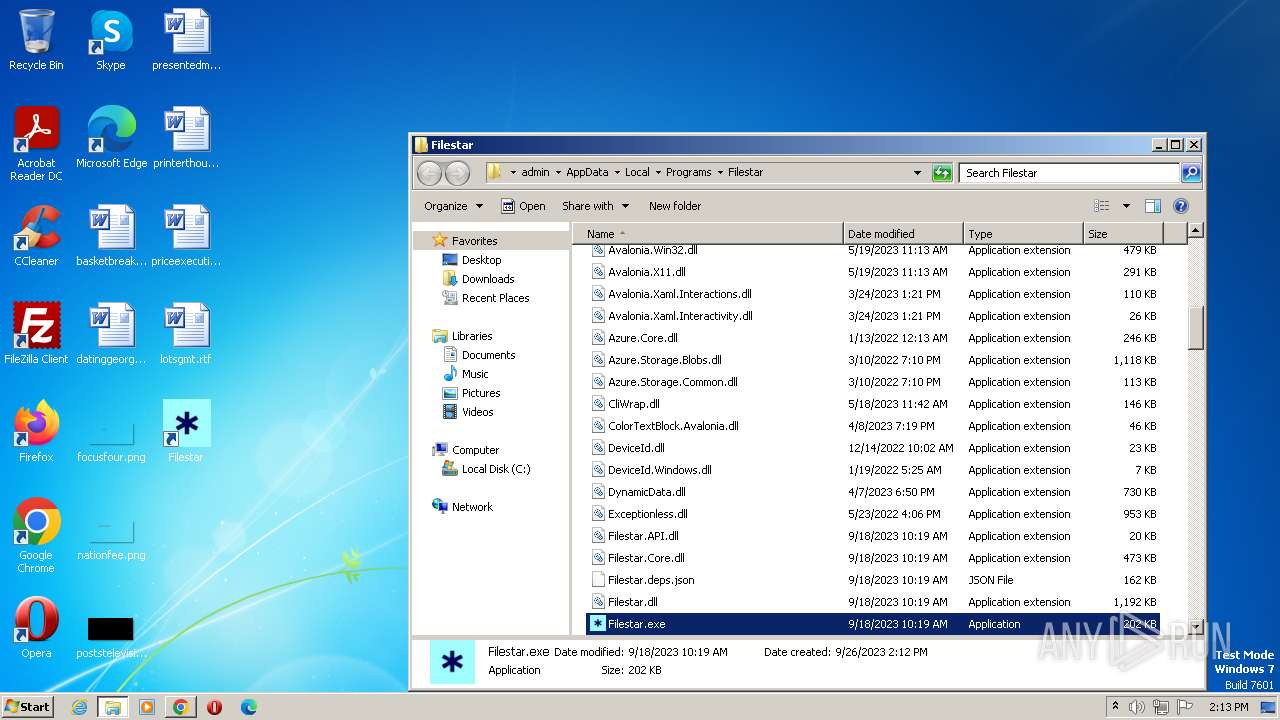
| URL: | https://meta.filestar.com/download2/win-x64/ZDcwd |
| Full analysis: | https://app.any.run/tasks/2825c461-a0e5-43e1-8386-0b7cd553d3c1 |
| Verdict: | Malicious activity |
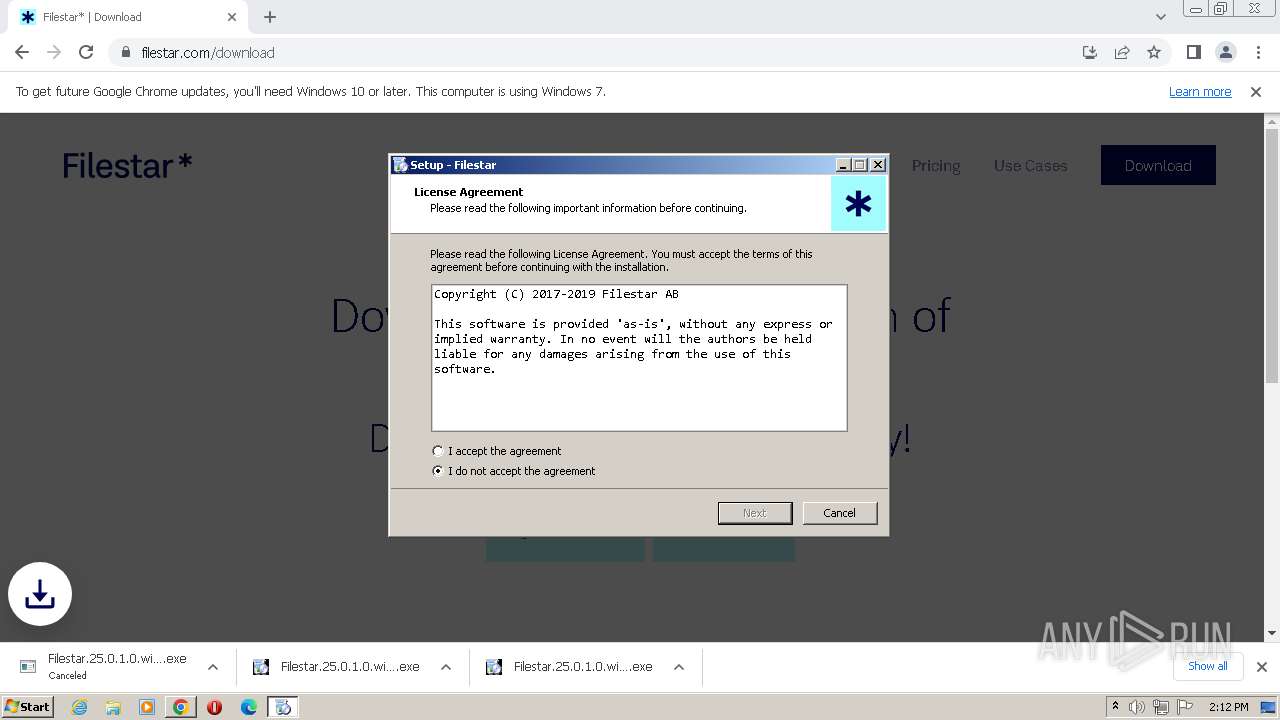
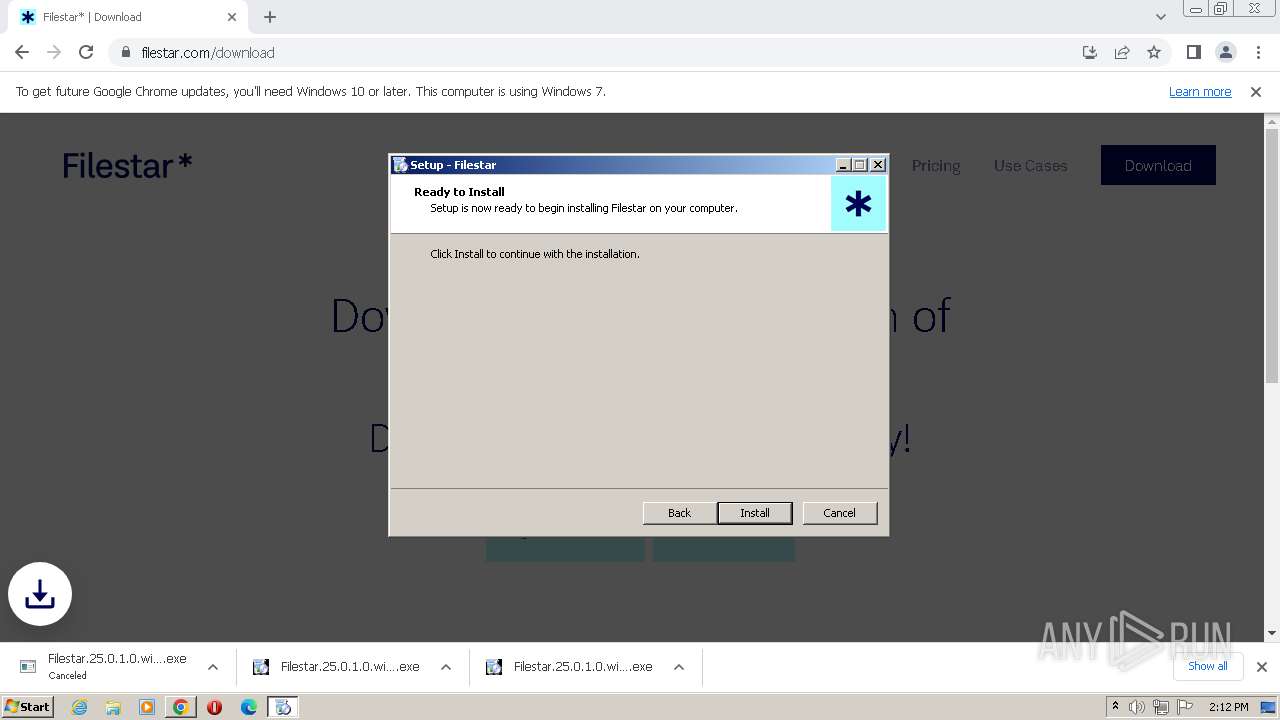
| Analysis date: | September 26, 2023, 13:11:02 |
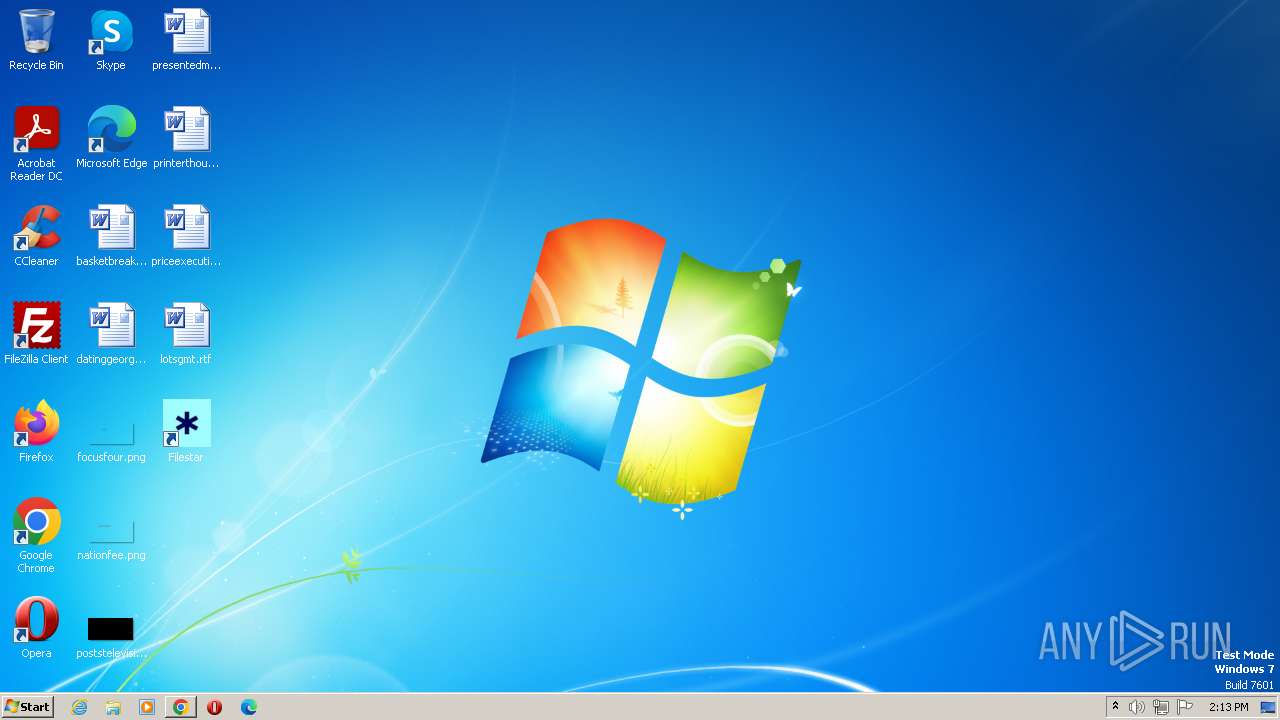
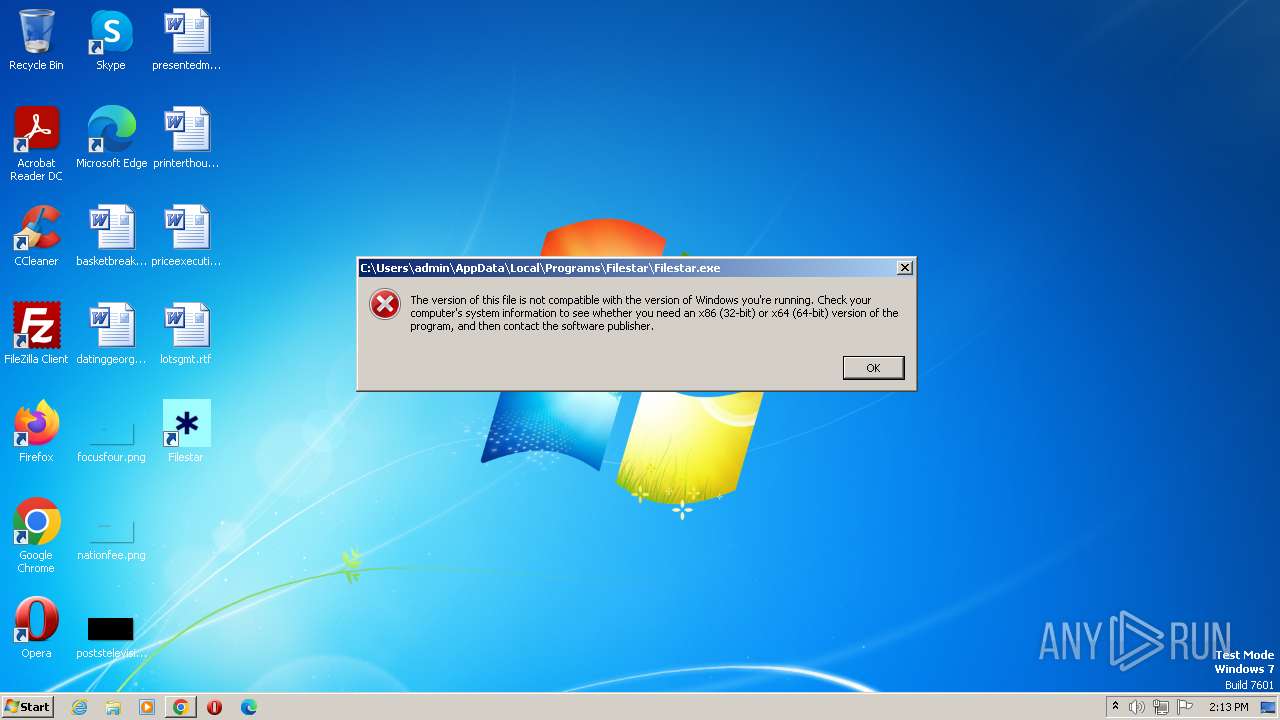
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3FE953C607413775D37A5C89FEF380A3 |
| SHA1: | 951D22DE497C3B8B19A6B19458DA3006B04EF5D8 |
| SHA256: | FD7999B38399CA20FE75C23AE2009CB7B6612F7F138DFCFF6EDE48A2ED2027F0 |
| SSDEEP: | 3:N8SLxWE2WXi7n:2SLEE2WX8 |
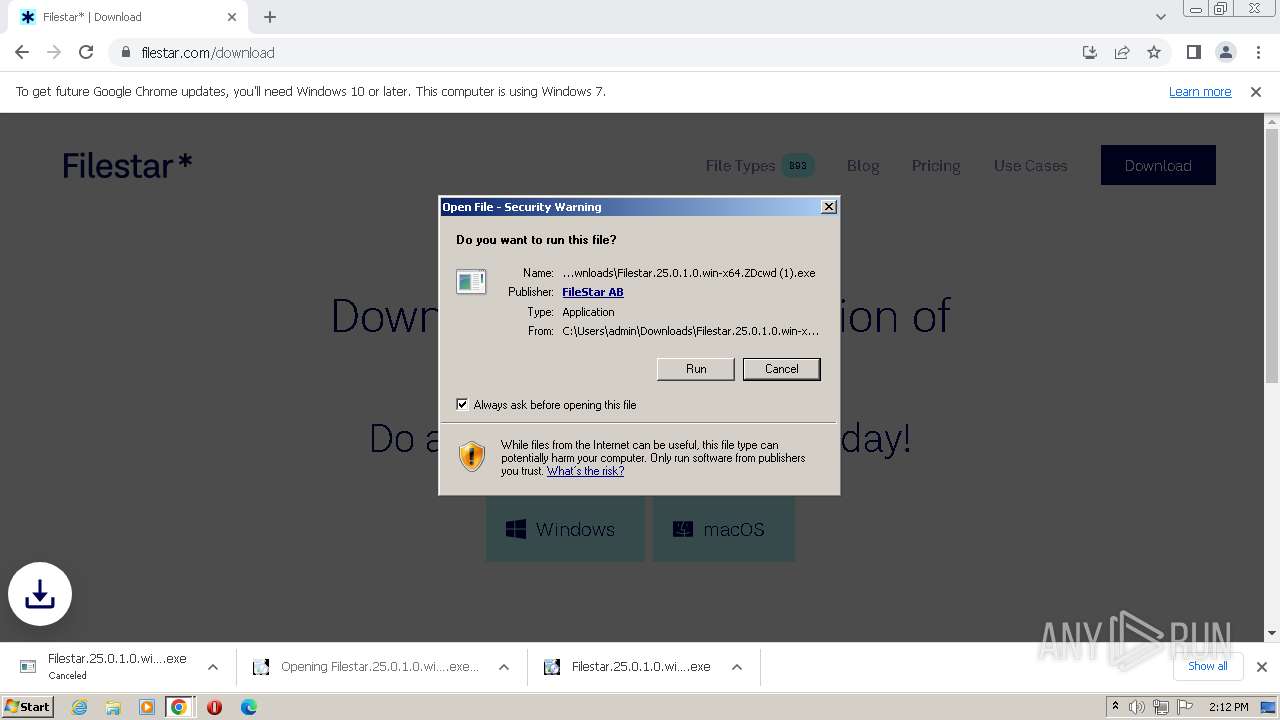
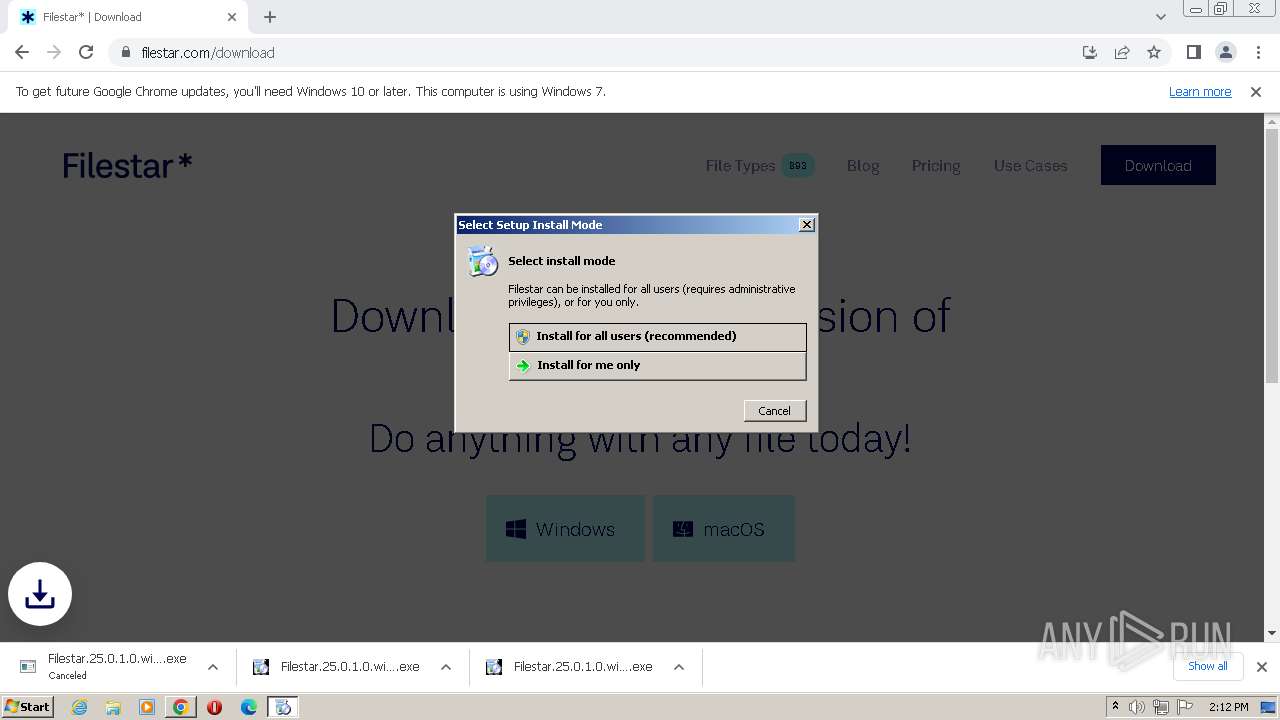
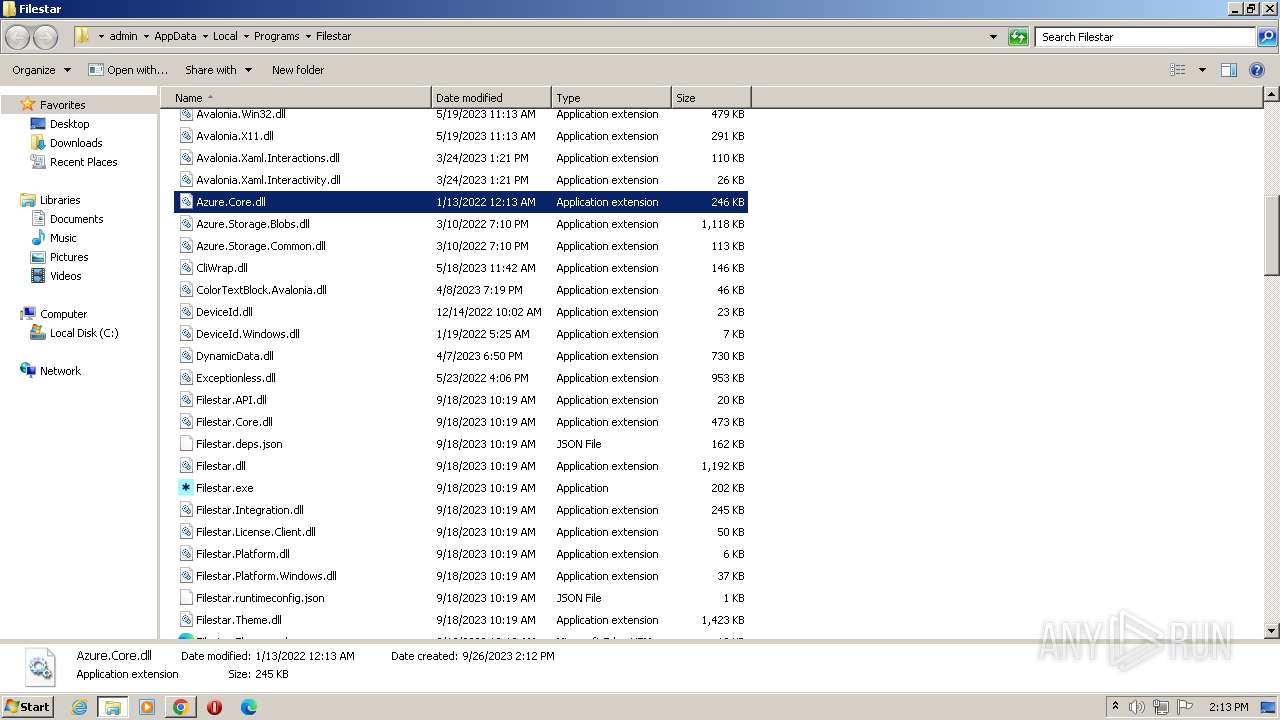
MALICIOUS
Application was dropped or rewritten from another process
- Filestar.25.0.1.0.win-x64.ZDcwd (1).exe (PID: 3232)
Loads dropped or rewritten executable
- Filestar.25.0.1.0.win-x64.ZDcwd (1).tmp (PID: 1764)
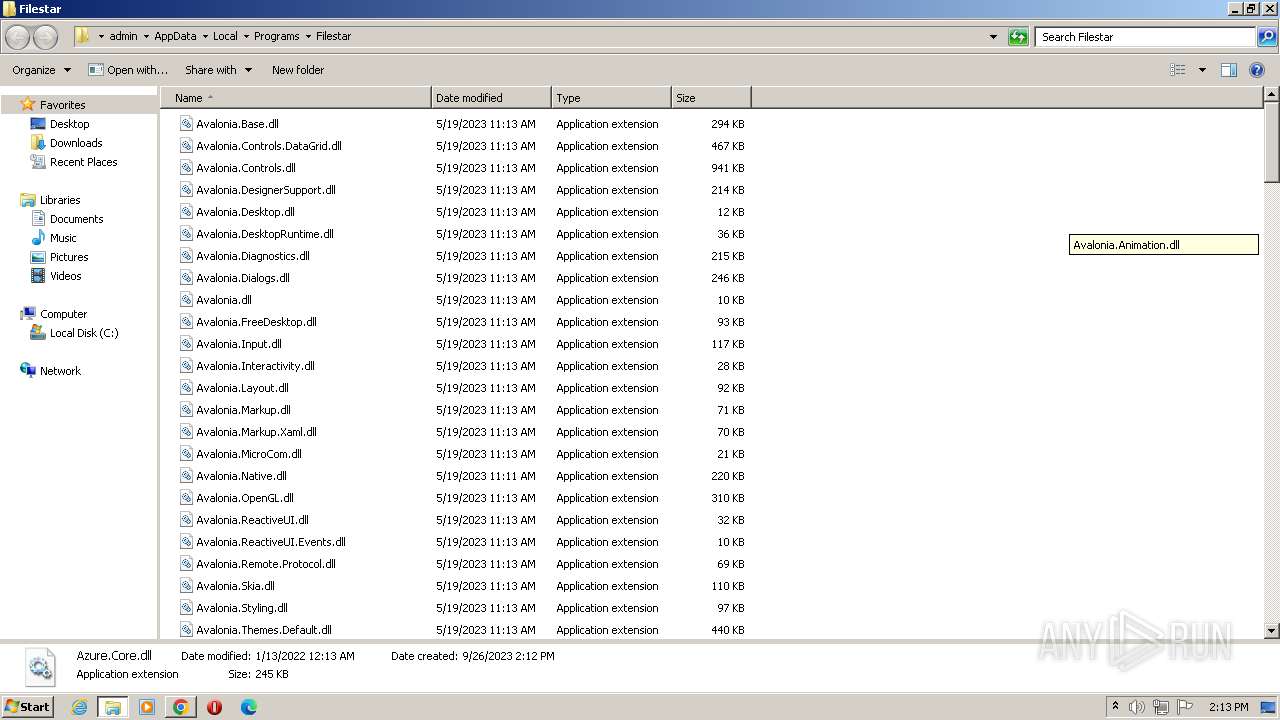
SUSPICIOUS
Reads the Windows owner or organization settings
- Filestar.25.0.1.0.win-x64.ZDcwd (1).tmp (PID: 1764)
Reads the Internet Settings
- Filestar.25.0.1.0.win-x64.ZDcwd (1).tmp (PID: 1764)
Uses TASKKILL.EXE to kill process
- Filestar.25.0.1.0.win-x64.ZDcwd (1).tmp (PID: 1764)
Starts CMD.EXE for commands execution
- Filestar.25.0.1.0.win-x64.ZDcwd (1).tmp (PID: 1764)
Checks Windows Trust Settings
- Filestar.25.0.1.0.win-x64.ZDcwd (1).tmp (PID: 1764)
Reads settings of System Certificates
- Filestar.25.0.1.0.win-x64.ZDcwd (1).tmp (PID: 1764)
Reads security settings of Internet Explorer
- Filestar.25.0.1.0.win-x64.ZDcwd (1).tmp (PID: 1764)
The process creates files with name similar to system file names
- unzip.exe (PID: 1000)
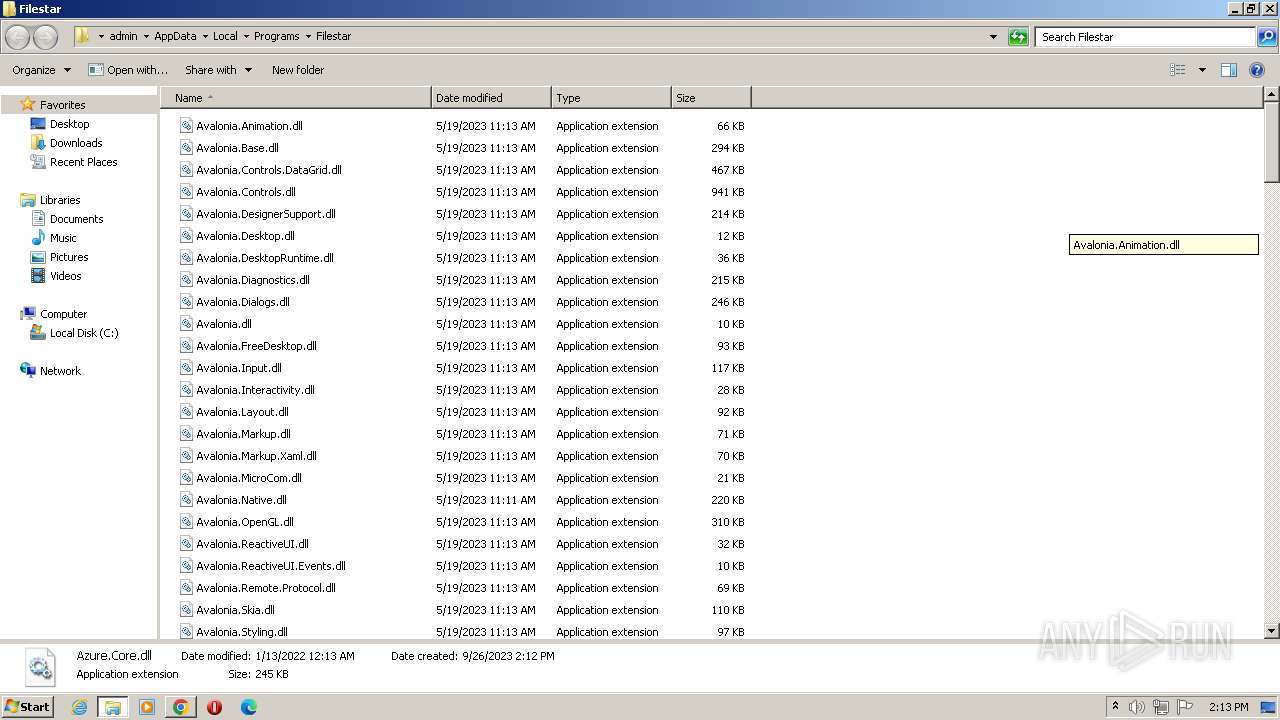
INFO
Checks supported languages
- Filestar.25.0.1.0.win-x64.ZDcwd (1).exe (PID: 3232)
- Filestar.25.0.1.0.win-x64.ZDcwd (1).tmp (PID: 1764)
- unzip.exe (PID: 1000)
- wmpnscfg.exe (PID: 2280)
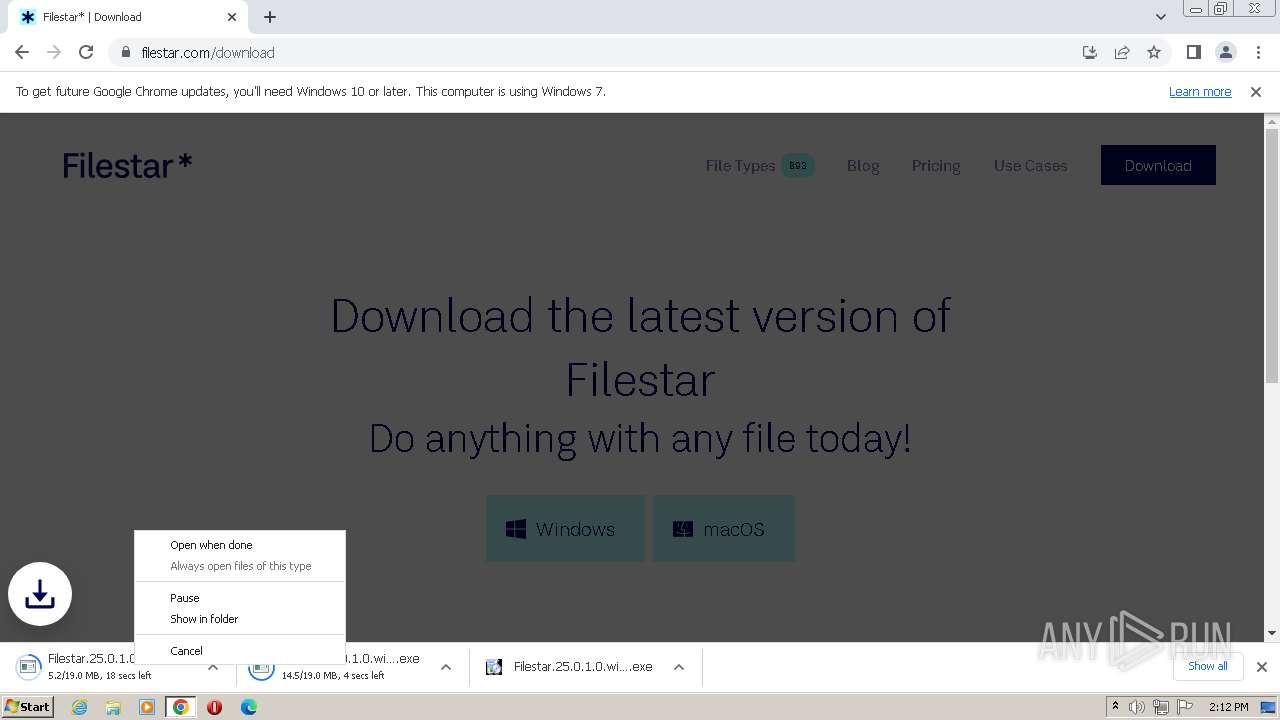
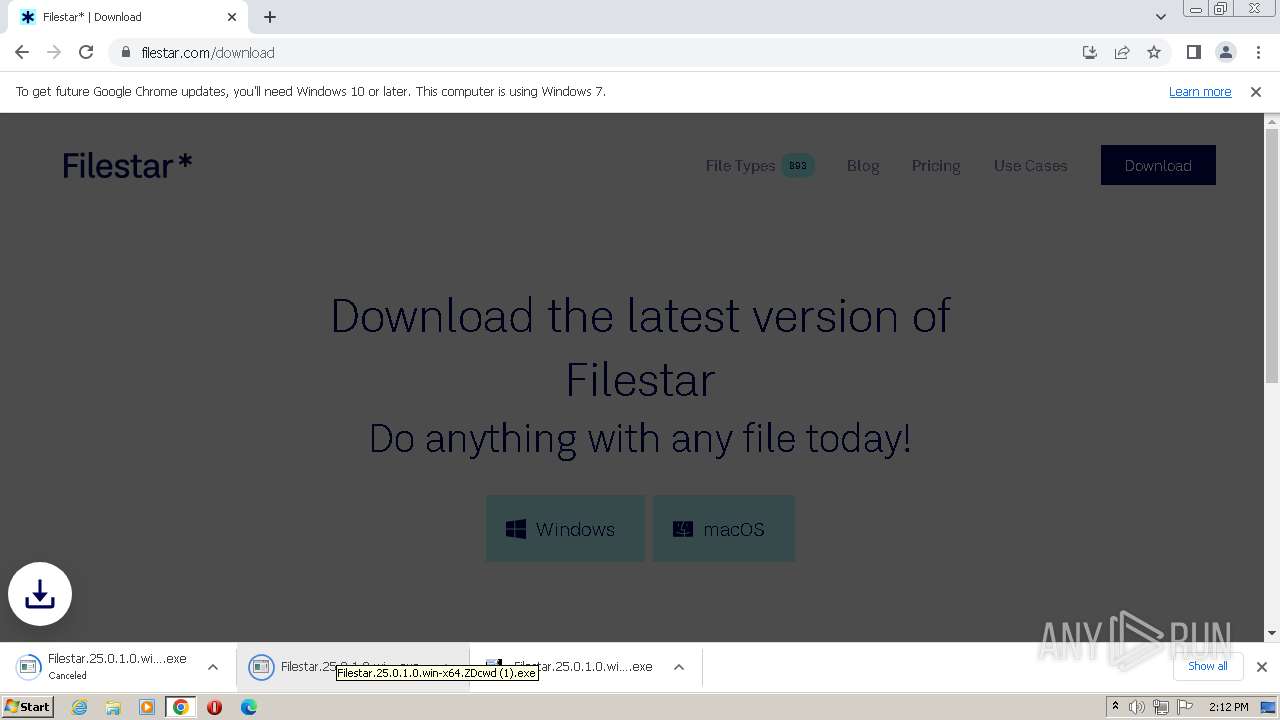
The process uses the downloaded file
- chrome.exe (PID: 1824)
- chrome.exe (PID: 1320)
- chrome.exe (PID: 1392)
- chrome.exe (PID: 1820)
- chrome.exe (PID: 2968)
- chrome.exe (PID: 2360)
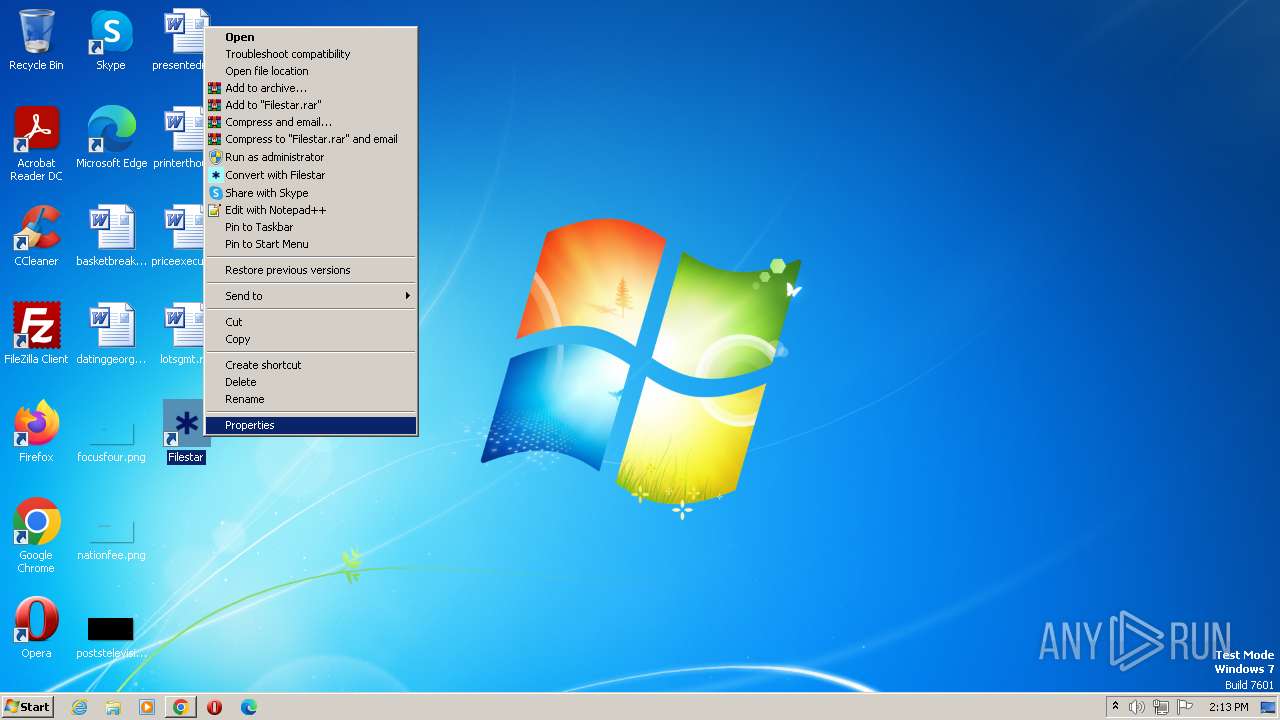
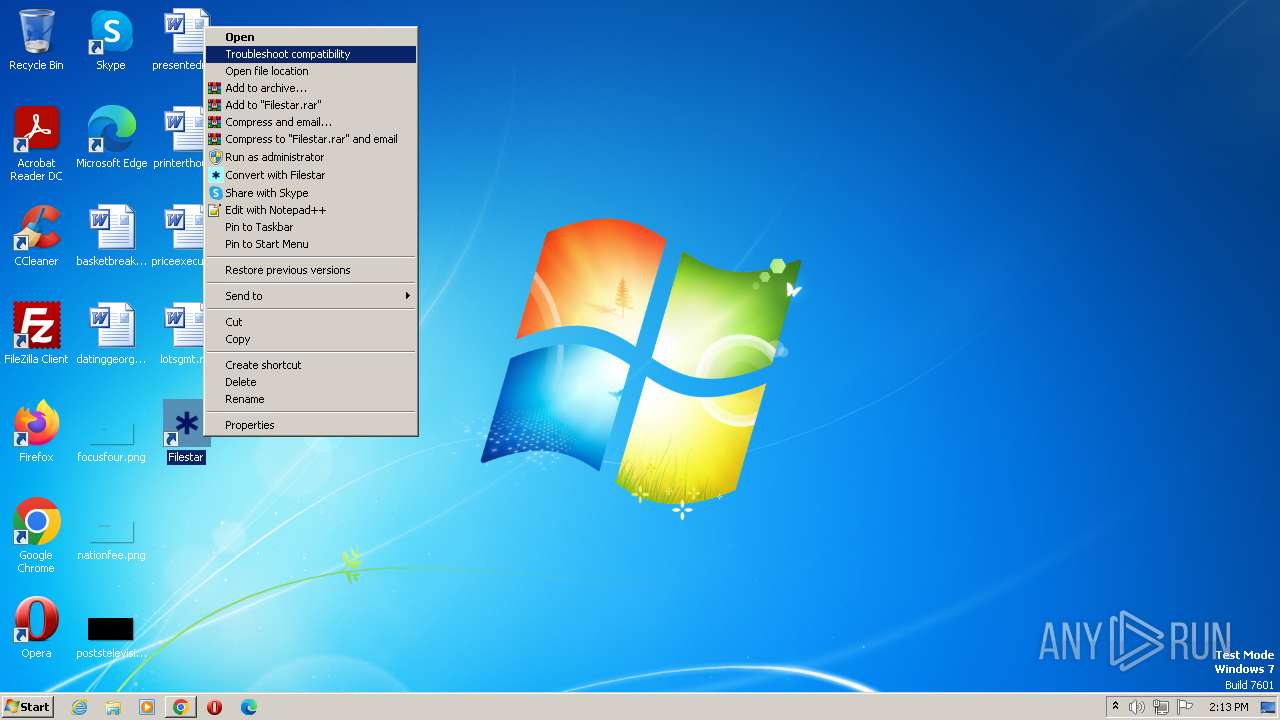
Manual execution by a user
- opera.exe (PID: 3528)
- wmpnscfg.exe (PID: 2280)
Reads the computer name
- Filestar.25.0.1.0.win-x64.ZDcwd (1).tmp (PID: 1764)
- wmpnscfg.exe (PID: 2280)
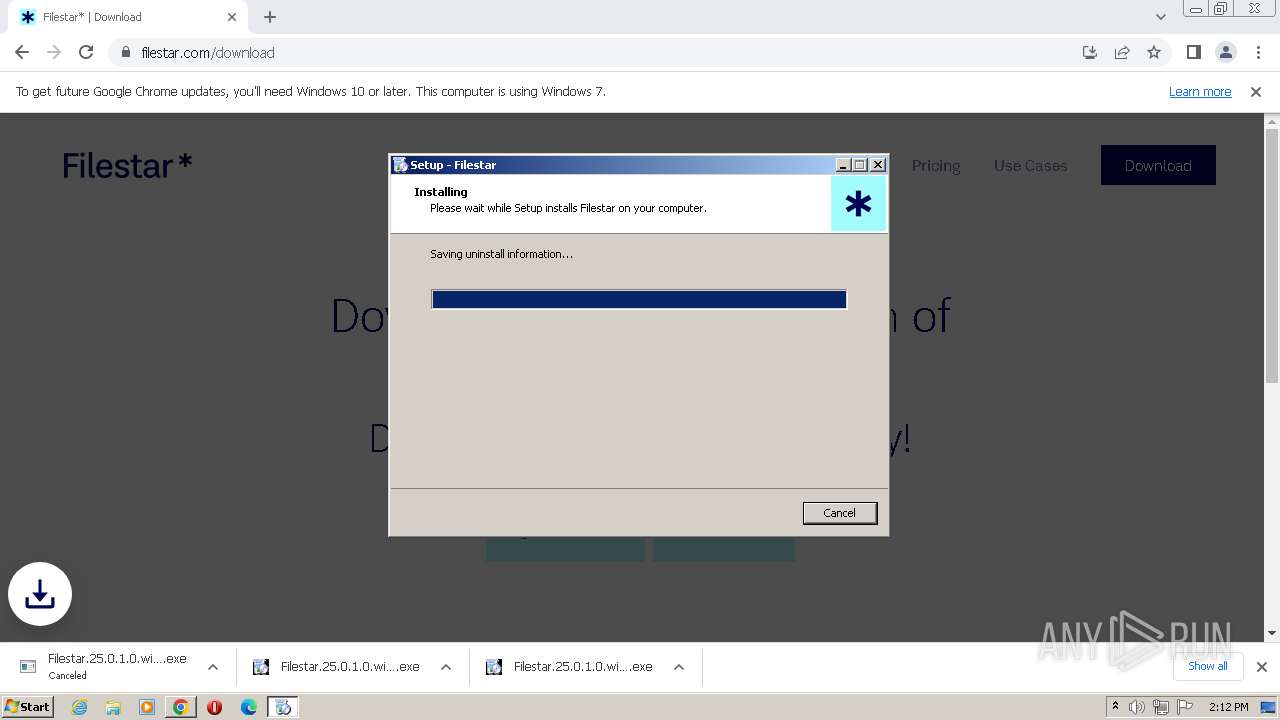
Create files in a temporary directory
- Filestar.25.0.1.0.win-x64.ZDcwd (1).exe (PID: 3232)
- Filestar.25.0.1.0.win-x64.ZDcwd (1).tmp (PID: 1764)
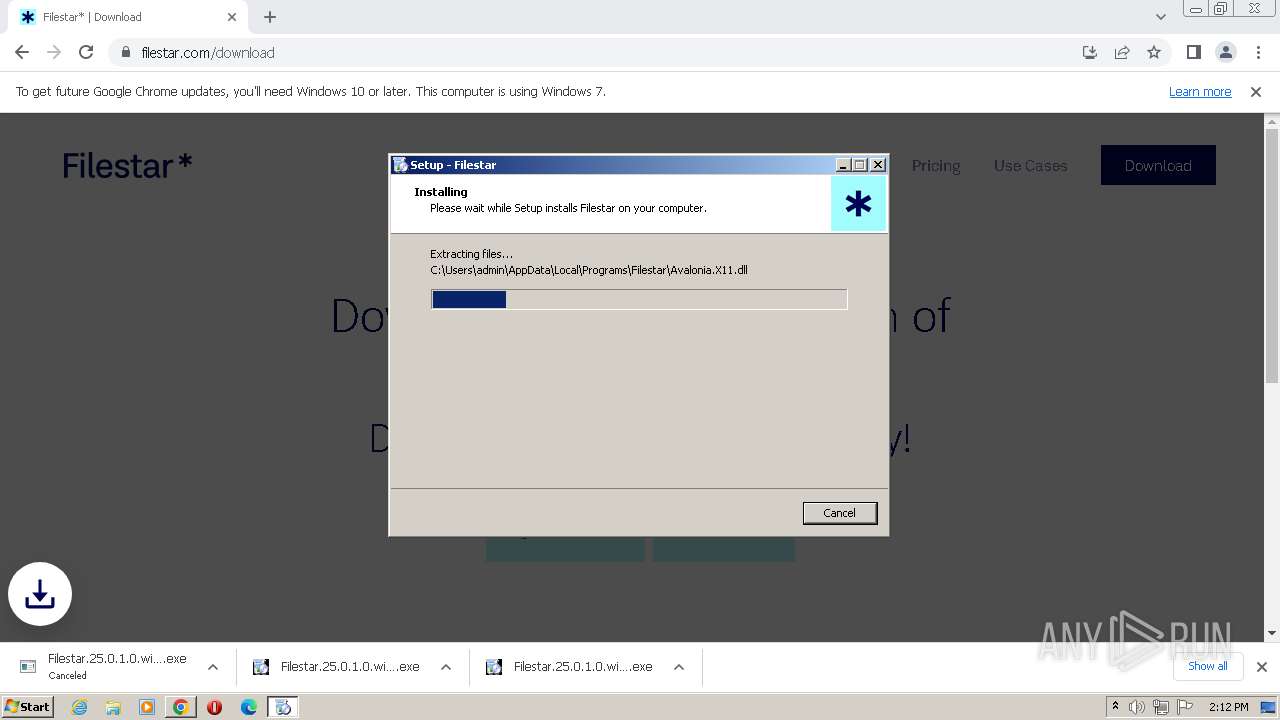
Application was dropped or rewritten from another process
- Filestar.25.0.1.0.win-x64.ZDcwd (1).tmp (PID: 1764)
- unzip.exe (PID: 1000)
Application launched itself
- chrome.exe (PID: 2968)
Checks proxy server information
- Filestar.25.0.1.0.win-x64.ZDcwd (1).tmp (PID: 1764)
Creates files or folders in the user directory
- unzip.exe (PID: 1000)
- Filestar.25.0.1.0.win-x64.ZDcwd (1).tmp (PID: 1764)
Reads the machine GUID from the registry
- Filestar.25.0.1.0.win-x64.ZDcwd (1).tmp (PID: 1764)
- wmpnscfg.exe (PID: 2280)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
88
Monitored processes
48
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1000 | "C:\Users\admin\AppData\Local\Temp\is-DT6U5.tmp\unzip.exe" C:\Users\admin\AppData\Local\Temp\is-DT6U5.tmp\dotnetruntime.zip -d C:\Users\admin\AppData\Roaming\Filestar\dotnetruntime | C:\Users\admin\AppData\Local\Temp\is-DT6U5.tmp\unzip.exe | — | Filestar.25.0.1.0.win-x64.ZDcwd (1).tmp | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1024 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=4032 --field-trial-handle=1164,i,10601288137965504502,18330067118195810232,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1480 --field-trial-handle=1164,i,10601288137965504502,18330067118195810232,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2188 --field-trial-handle=1164,i,10601288137965504502,18330067118195810232,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3212 --field-trial-handle=1164,i,10601288137965504502,18330067118195810232,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=4032 --field-trial-handle=1164,i,10601288137965504502,18330067118195810232,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1924 --field-trial-handle=1164,i,10601288137965504502,18330067118195810232,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3408 --field-trial-handle=1164,i,10601288137965504502,18330067118195810232,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1764 | "C:\Users\admin\AppData\Local\Temp\is-IHSAP.tmp\Filestar.25.0.1.0.win-x64.ZDcwd (1).tmp" /SL5="$E01CA,19070699,785920,C:\Users\admin\Downloads\Filestar.25.0.1.0.win-x64.ZDcwd (1).exe" | C:\Users\admin\AppData\Local\Temp\is-IHSAP.tmp\Filestar.25.0.1.0.win-x64.ZDcwd (1).tmp | Filestar.25.0.1.0.win-x64.ZDcwd (1).exe | ||||||||||||
User: admin Company: Filestar AB Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
17 890
Read events
17 497
Write events
380
Delete events
13
Modification events
| (PID) Process: | (1024) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000F6D6788197A75D498472ACE88906AC8D0000000002000000000010660000000100002000000075B0D7E28E2E17B576E141128F731FE5320CCA30C35292A435B65D5E91F3150B000000000E80000000020000200000000C791686155A322F498D360901A0BC88A787D4ADF186758AE2D9BB16BE317ECD30000000E07A76BA5A881A8B5FF9F7A7FE5833EB2B96D7A240E8CDC394ED7C494DEC5BF8E13DB07B279185F24F9C8B497FA4E70A400000008D71222A7DB9FE2EAB90303DA35140A5A9A6780343B0FFB0C4B233499C2F0735FA041306AFACB24F5B397960A2D4CBA893F7FF12508B7C84A5AE9013C2C0A092 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
519
Suspicious files
189
Text files
115
Unknown types
4
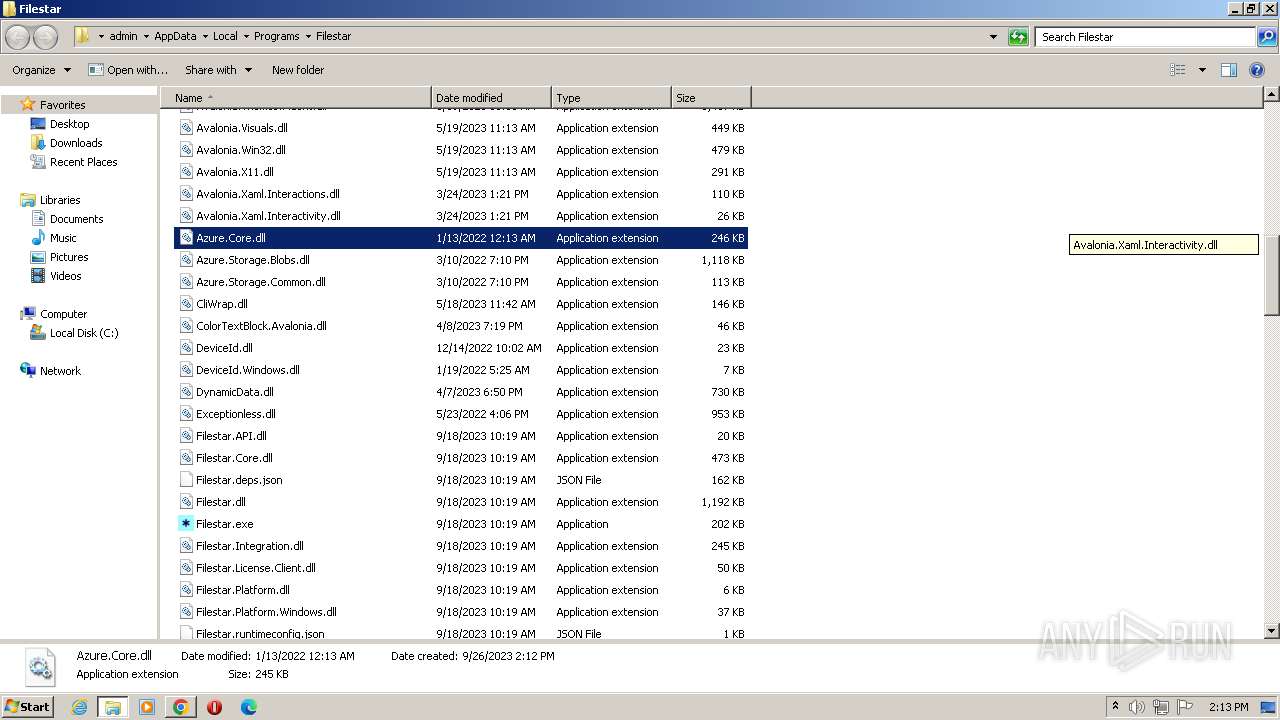
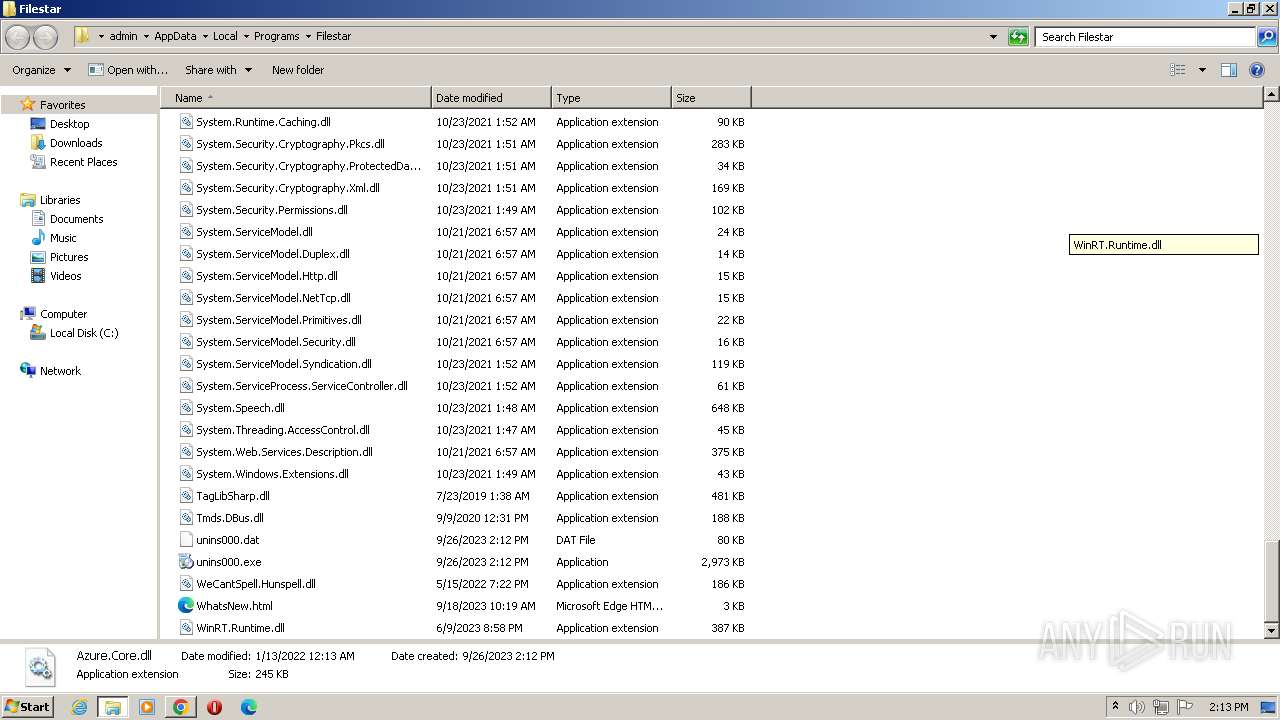
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFf83fc.TMP | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:513218482935B0D388C0A990D868387A | SHA256:8E39CBAAF4AACC3A01AFA74EA8C30FB24FE69A22B8B30728AFB1614FD68809D9 | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\793fb895-60b9-436e-834d-e2a564cf872d.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RFf865d.TMP | text | |
MD5:0917C6BFC618ACD47C1F53C7E7FFFF9C | SHA256:A5CAF56982DA7AE34B201E8609610786B4730371EF0812B7D418A2F9B73547BC | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:65635E713D5CFC914717D1CC4CAC6989 | SHA256:4CB3EEB0369758290ABD7868DFD85D663C4AEF6C727FFF43BE693FDDBD0A6C28 | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | text | |
MD5:A5EB529D94D3E97D0EE4A7E07700E0B2 | SHA256:08D211BFC570221AF7995C0625052FA7848F7E707D559C266656CDC3A9CC9F9C | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\optimization_guide_model_metadata_store\LOG.old~RFf9a52.TMP | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\optimization_guide_model_metadata_store\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\optimization_guide_hint_cache_store\LOG.old~RFf9a52.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
74
DNS requests
62
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2884 | chrome.exe | GET | 204 | 142.250.185.195:80 | http://www.gstatic.com/generate_204 | US | — | — | unknown |
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/fzrp6xpdtqq2vakspwulwu2yae_62/khaoiebndkojlmppeemjhbpbandiljpe_62_win_n2jkzx33j3rlsltywormztyyby.crx3 | US | — | — | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 224 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 85.4 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 443 Kb | unknown |
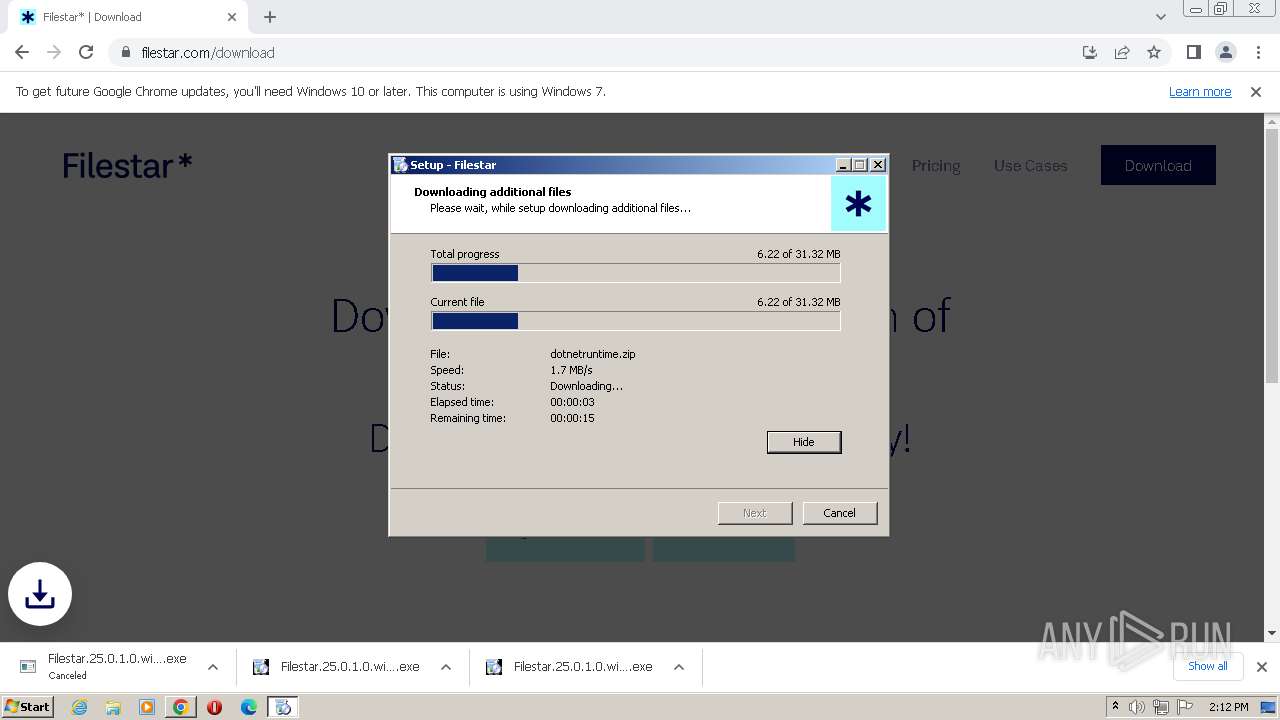
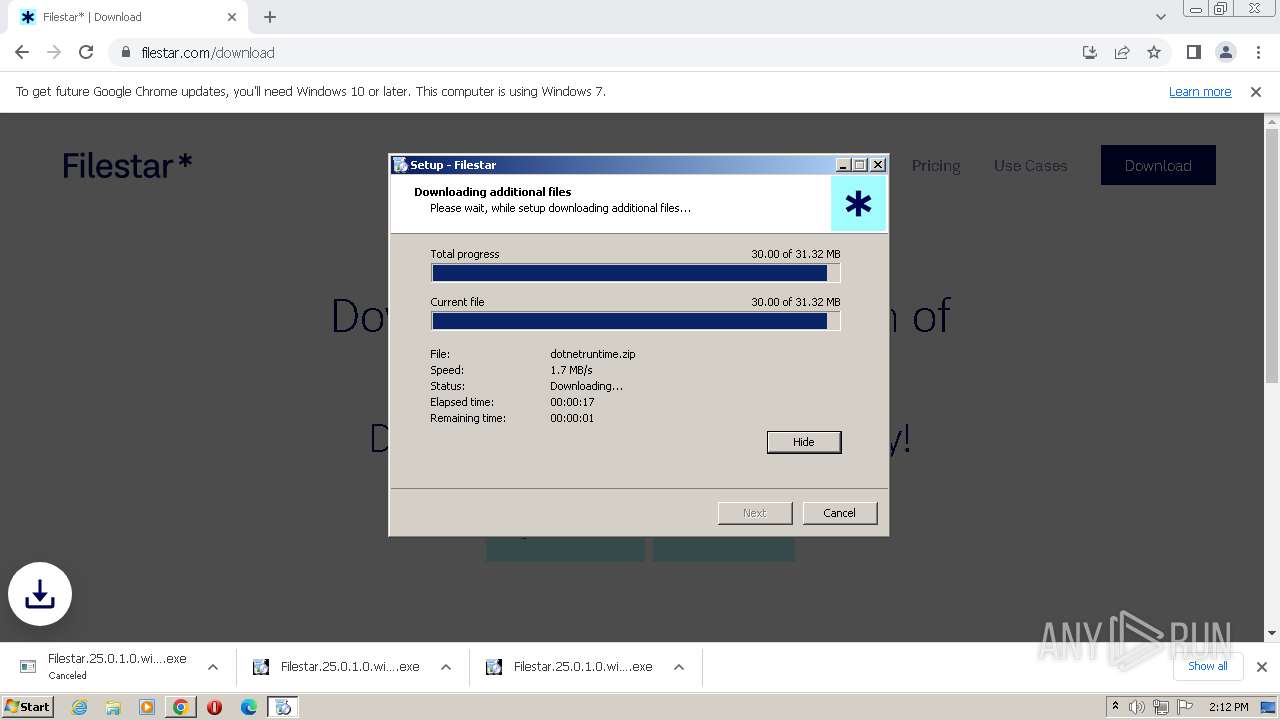
1764 | Filestar.25.0.1.0.win-x64.ZDcwd (1).tmp | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 584 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 1.02 Mb | unknown |
1764 | Filestar.25.0.1.0.win-x64.ZDcwd (1).tmp | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d110ee7d2fcf3918 | GB | compressed | 4.66 Kb | unknown |
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/epfl3euvq5fzms4lfyaaiom5_413/lmelglejhemejginpboagddgdfbepgmp_413_all_ZZ_idspawl3ljh6fivpg5wbgjqqhy.crx3 | US | crx | 5.51 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3284 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2968 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2884 | chrome.exe | 172.217.23.109:443 | accounts.google.com | GOOGLE | US | unknown |
2884 | chrome.exe | 40.68.214.185:443 | meta.filestar.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
2884 | chrome.exe | 142.250.186.68:443 | www.google.com | GOOGLE | US | whitelisted |
2968 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2884 | chrome.exe | 172.217.16.138:443 | optimizationguide-pa.googleapis.com | — | — | whitelisted |
3528 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
meta.filestar.com |
| unknown |
www.google.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |
certs.opera.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
filestar.com |
| unknown |
script.tapfiliate.com |
| whitelisted |