| download: | setup.exe |
| Full analysis: | https://app.any.run/tasks/b7f67be5-f43a-4998-bd59-92a2c9085758 |
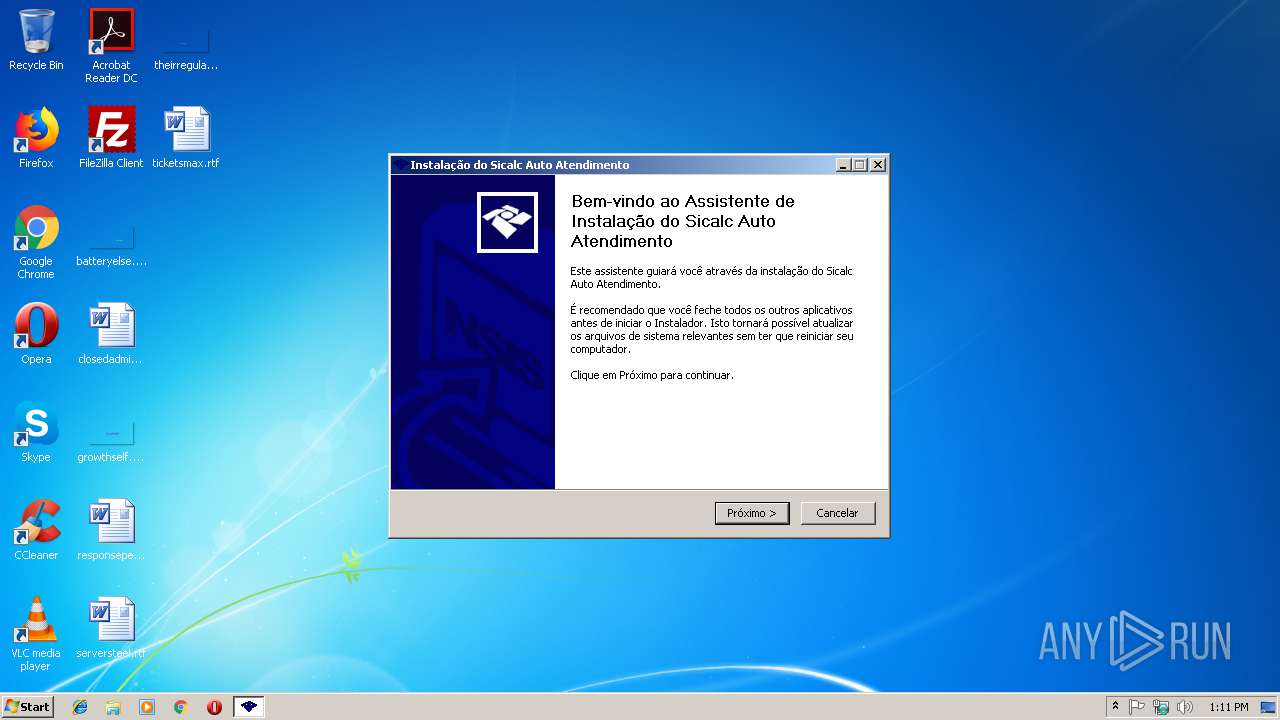
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2019, 13:11:19 |
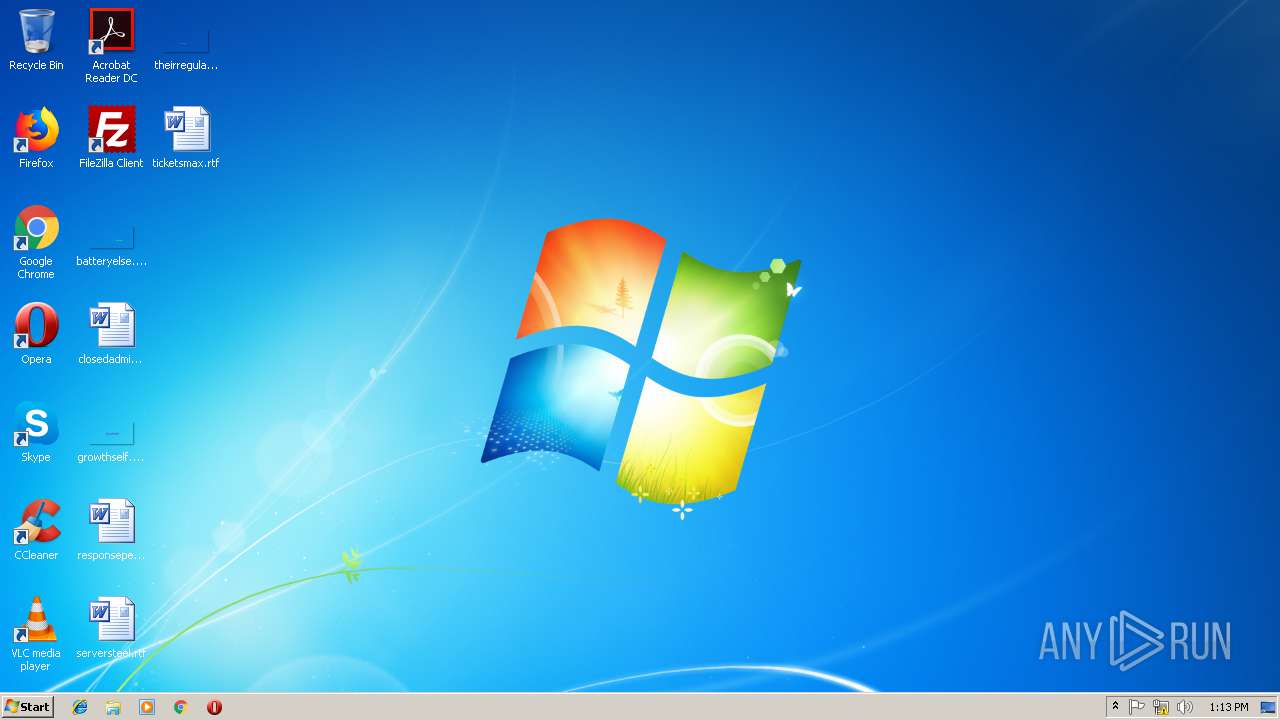
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 3BE20A25F7619D13A020B5E06413F003 |
| SHA1: | 962B855522A40CADDE0065D297338ED97BFE6150 |
| SHA256: | FD5F24429D25FD0EB730717EA0540C82FE9FBD7DFB3D345371FCBEB29E4DDDC0 |
| SSDEEP: | 49152:puLxxeY2j3l5KE/ITXLHstMrtrfUDwvFSnMxB:ULL2jVQfHstMhfU0vFZD |
MALICIOUS
Loads dropped or rewritten executable
- setup.exe (PID: 2164)
- SicalcAA.exe (PID: 2812)
- SicalcAA.exe (PID: 3800)
Application was dropped or rewritten from another process
- SicalcAA.exe (PID: 2812)
- SicalcAA.exe (PID: 3800)
SUSPICIOUS
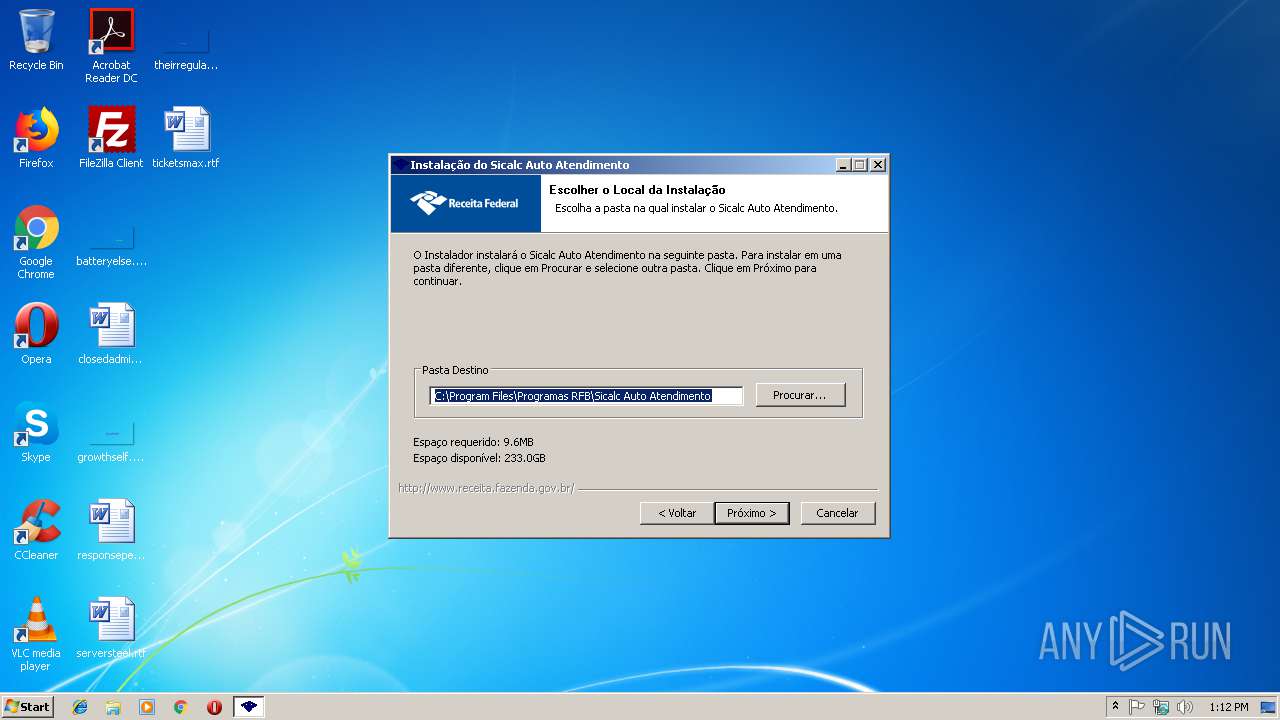
Creates files in the program directory
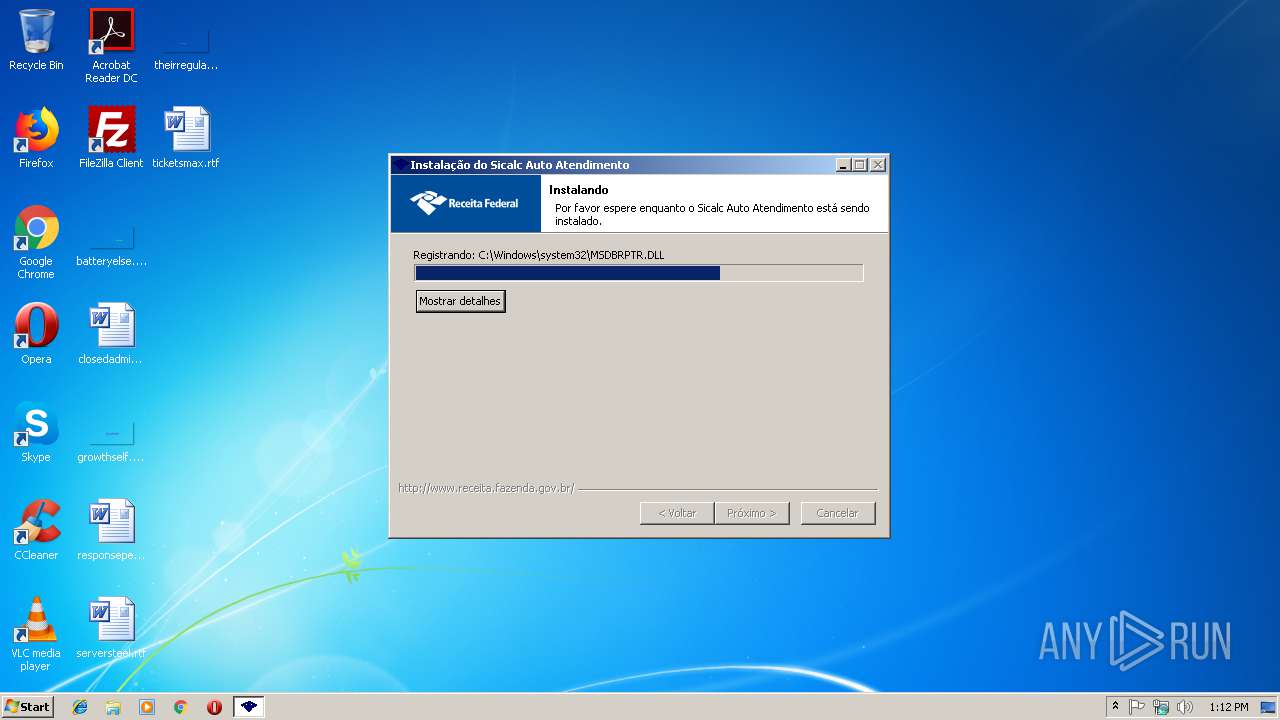
- setup.exe (PID: 2164)
Executable content was dropped or overwritten
- setup.exe (PID: 2164)
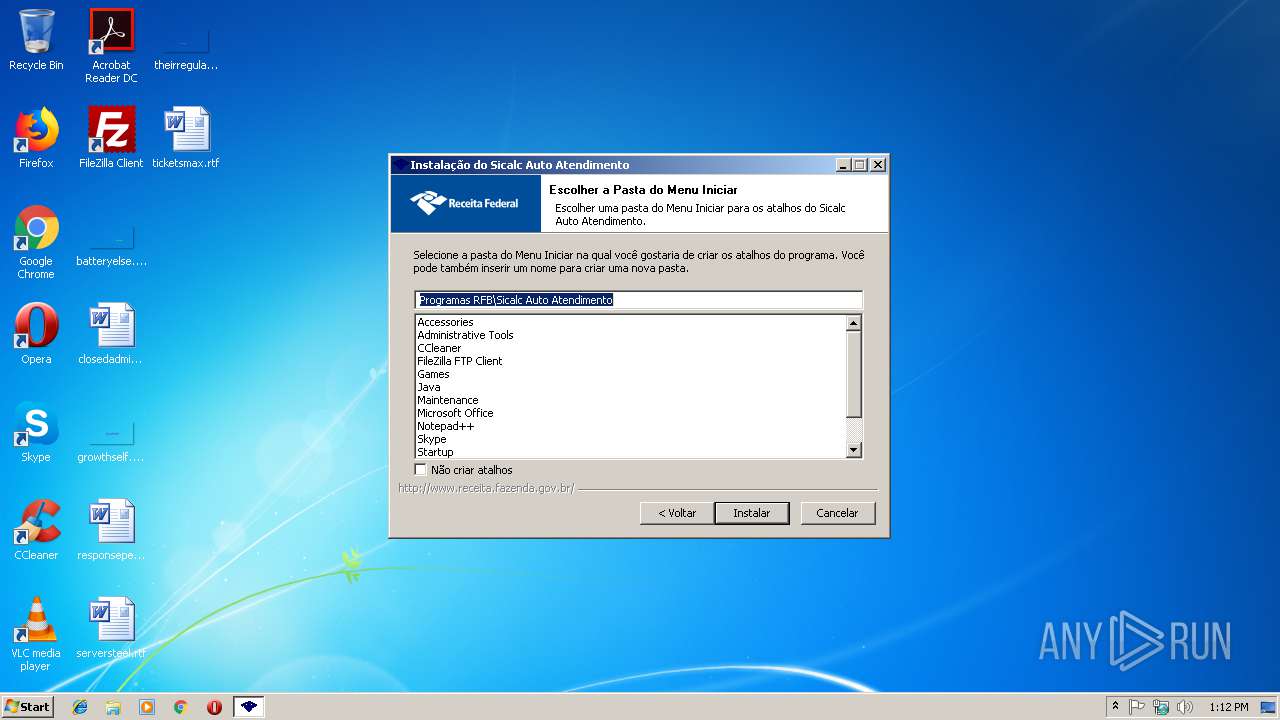
Creates a software uninstall entry
- setup.exe (PID: 2164)
Creates files in the Windows directory
- setup.exe (PID: 2164)
Creates COM task schedule object
- setup.exe (PID: 2164)
Creates files in the user directory
- SicalcAA.exe (PID: 2812)
- SicalcAA.exe (PID: 3800)
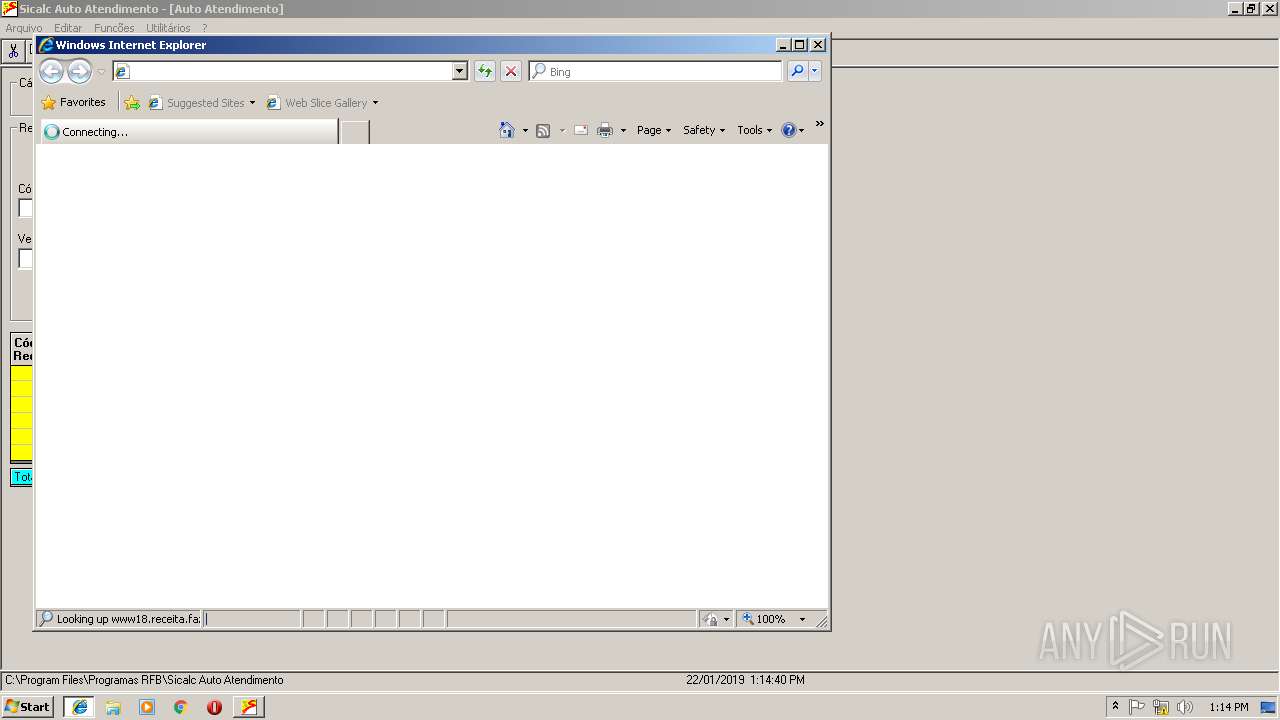
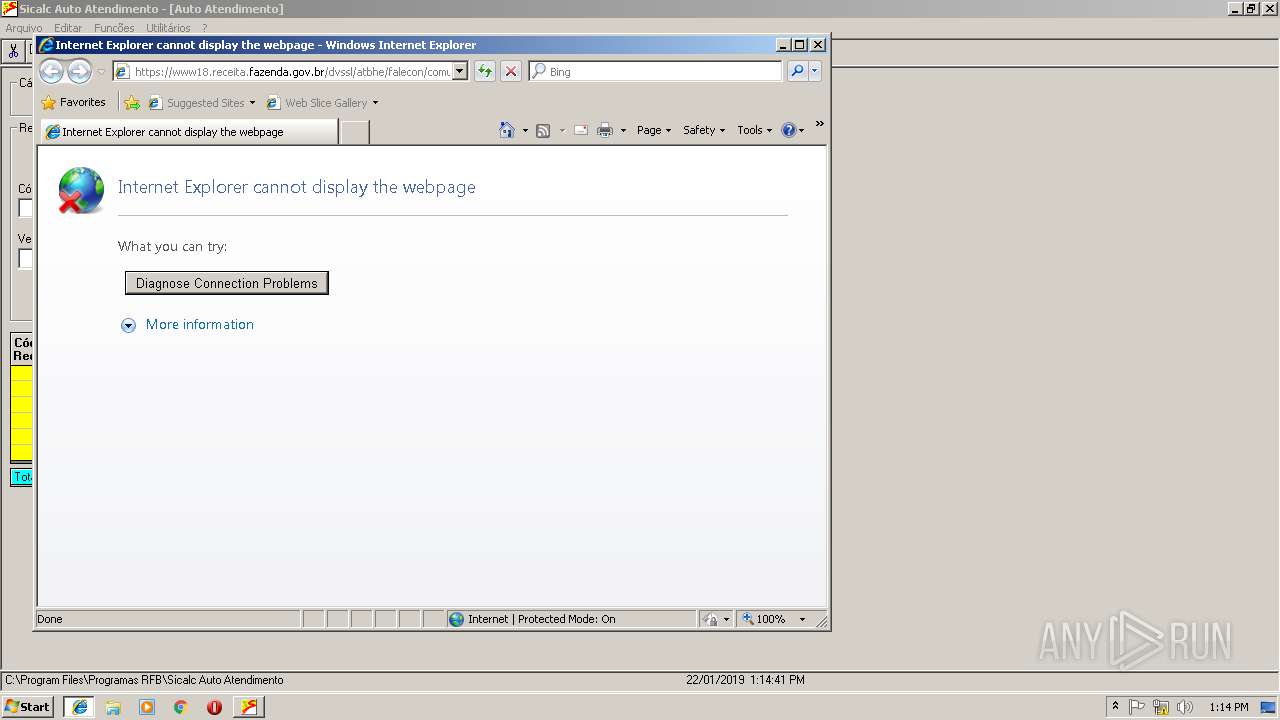
Starts Internet Explorer
- SicalcAA.exe (PID: 3800)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 568)
Changes internet zones settings
- iexplore.exe (PID: 2308)
Creates files in the user directory
- iexplore.exe (PID: 568)
- iexplore.exe (PID: 2308)
Reads internet explorer settings
- iexplore.exe (PID: 568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:02 05:20:13+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24576 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x312a |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Apr-2016 03:20:13 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 02-Apr-2016 03:20:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005E66 | 0x00006000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44066 |
.rdata | 0x00007000 | 0x000012A2 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.05833 |
.data | 0x00009000 | 0x00025D18 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.18773 |
.ndata | 0x0002F000 | 0x00017000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00046000 | 0x00001418 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.17906 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21417 | 958 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 1.81924 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.67385 | 512 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
107 | 2.52183 | 160 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.92787 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
39
Monitored processes
7
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 568 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2308 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 936 | calc.EXE | C:\Windows\system32\calc.EXE | — | SicalcAA.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Calculator Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2164 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2308 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | SicalcAA.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
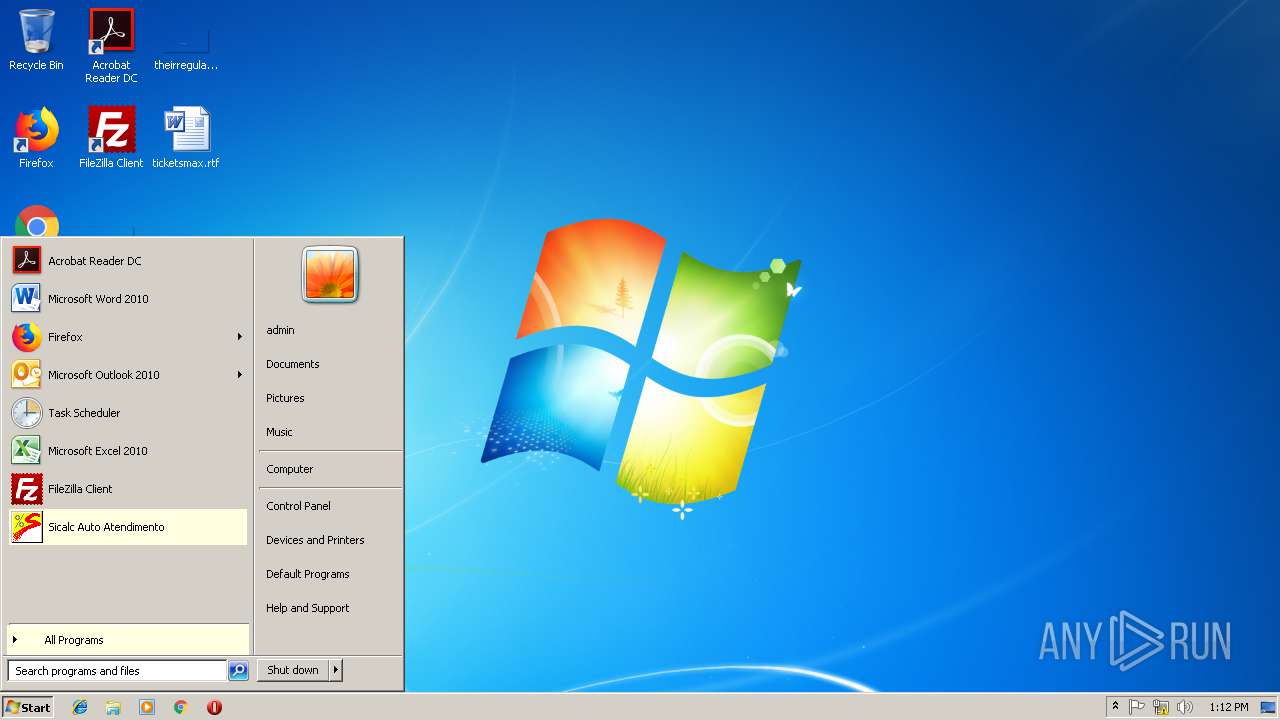
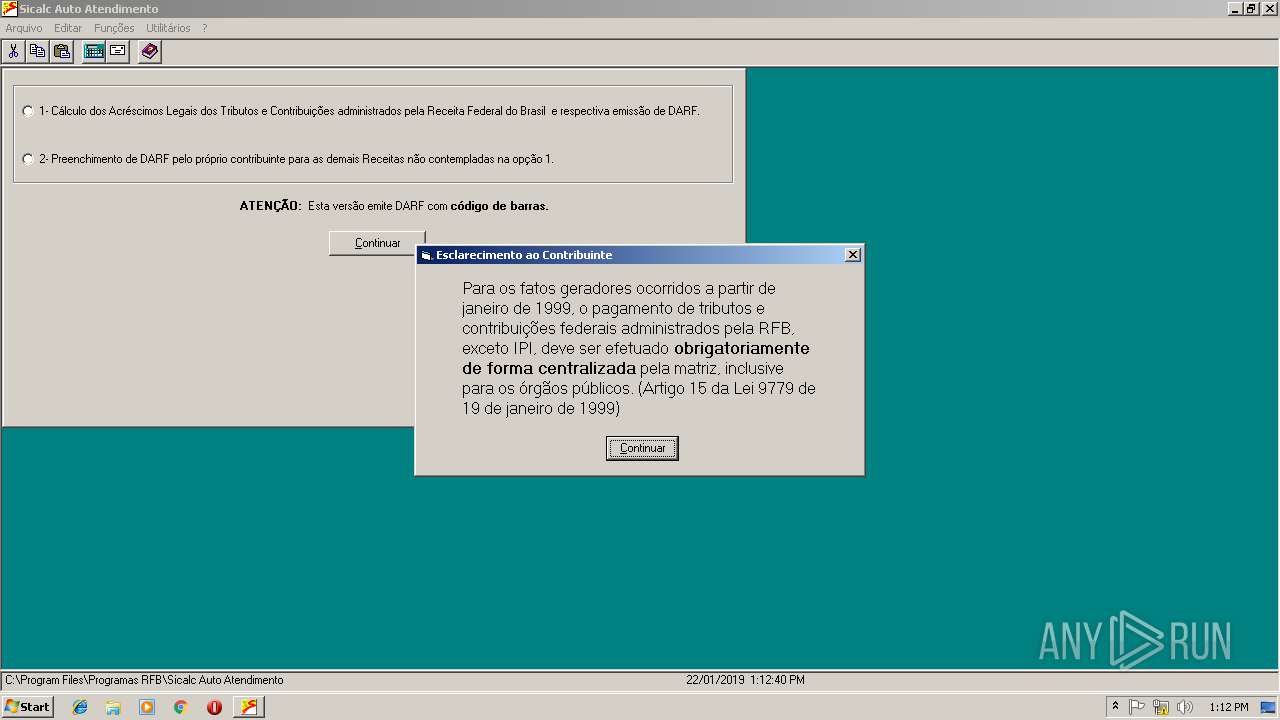
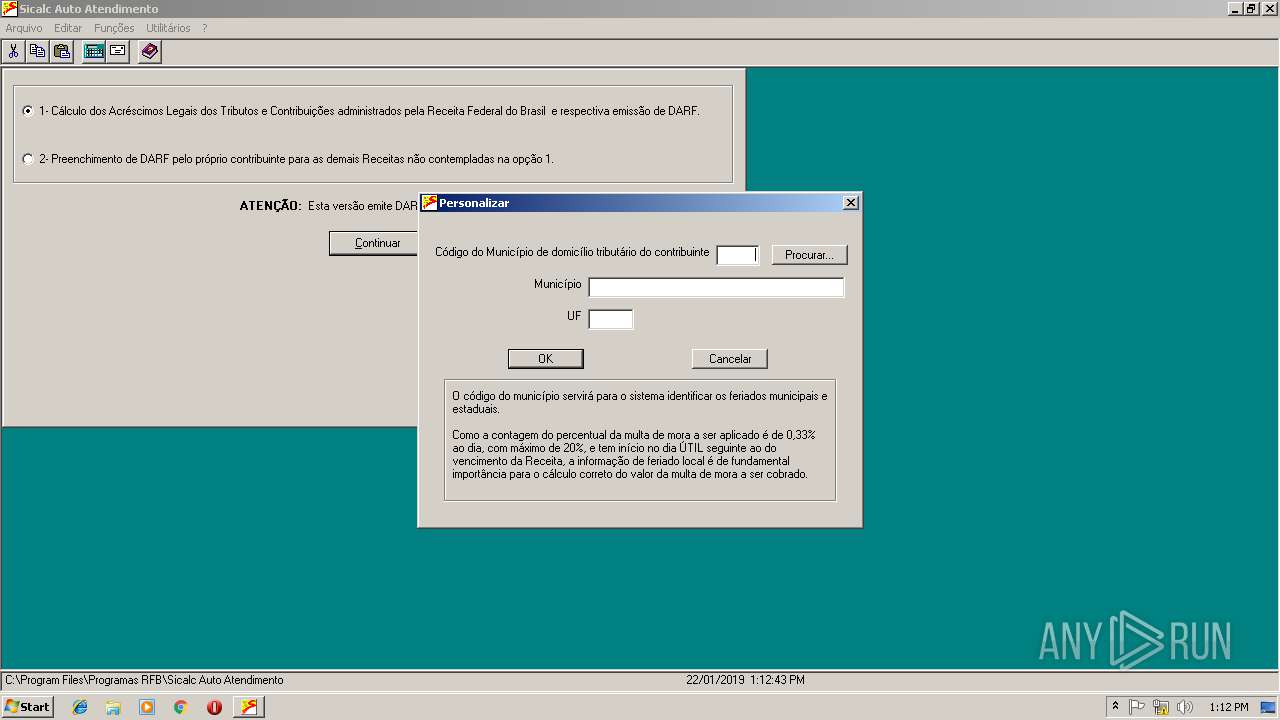
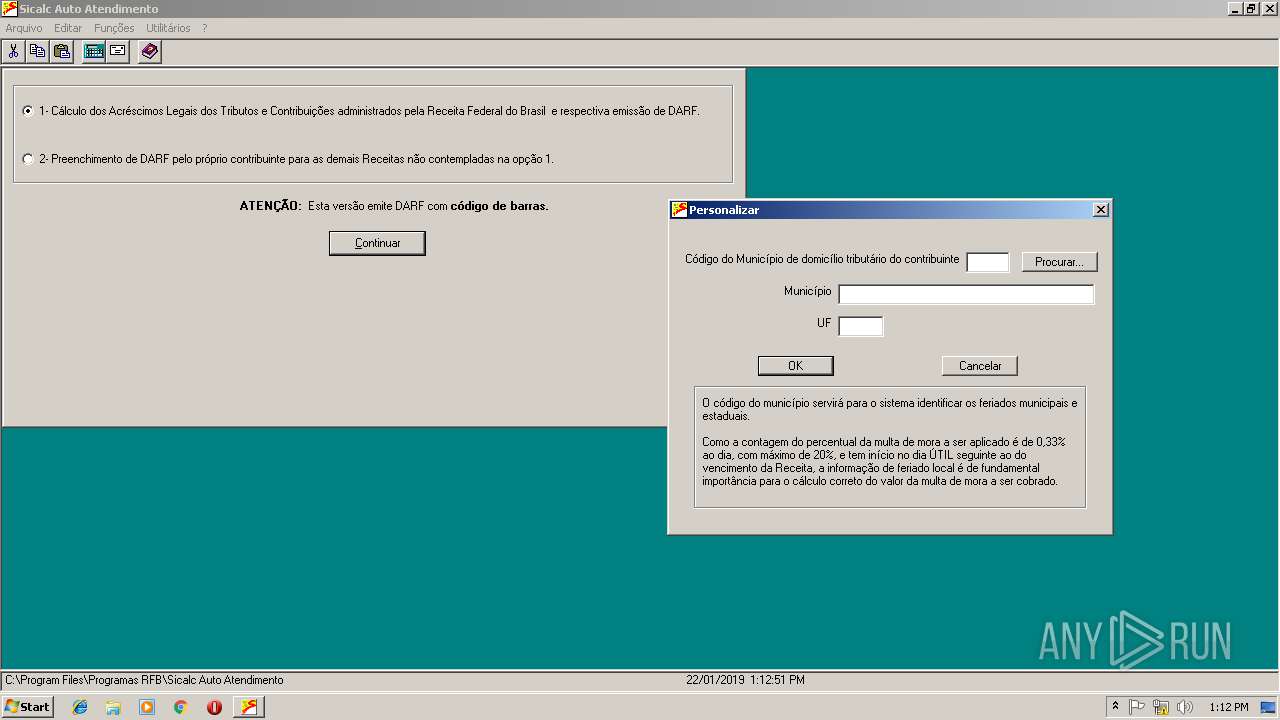
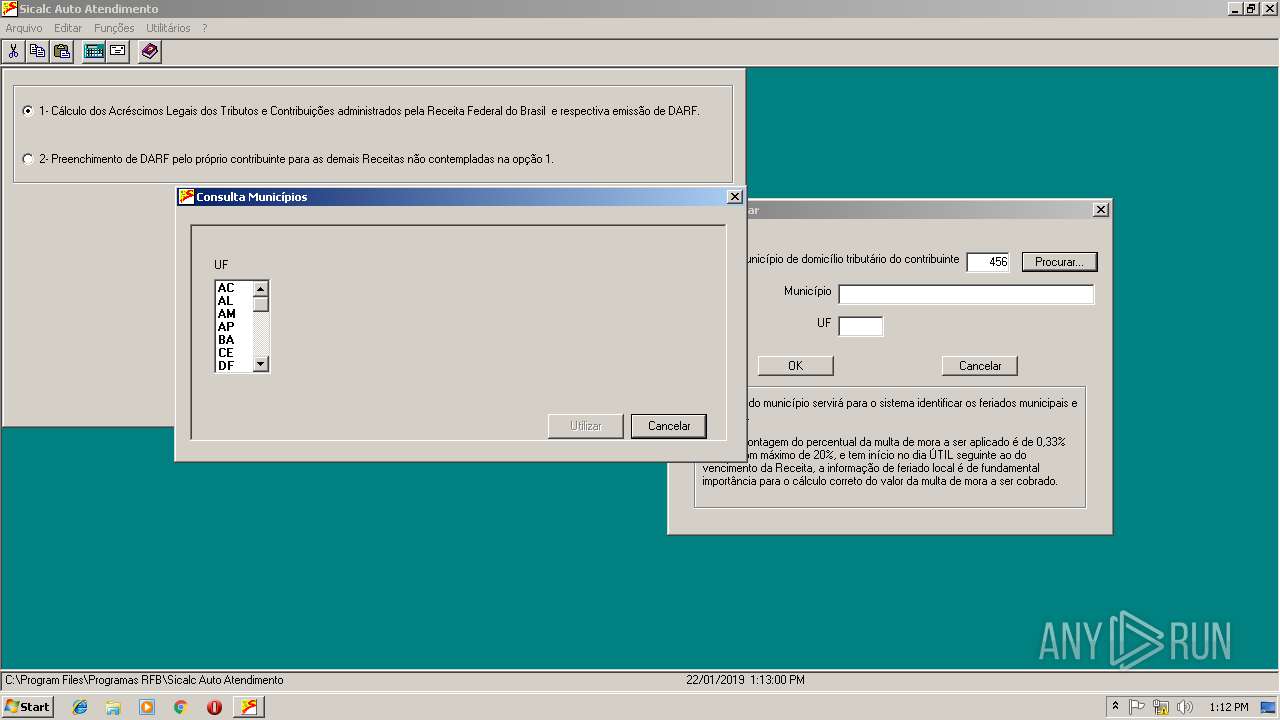
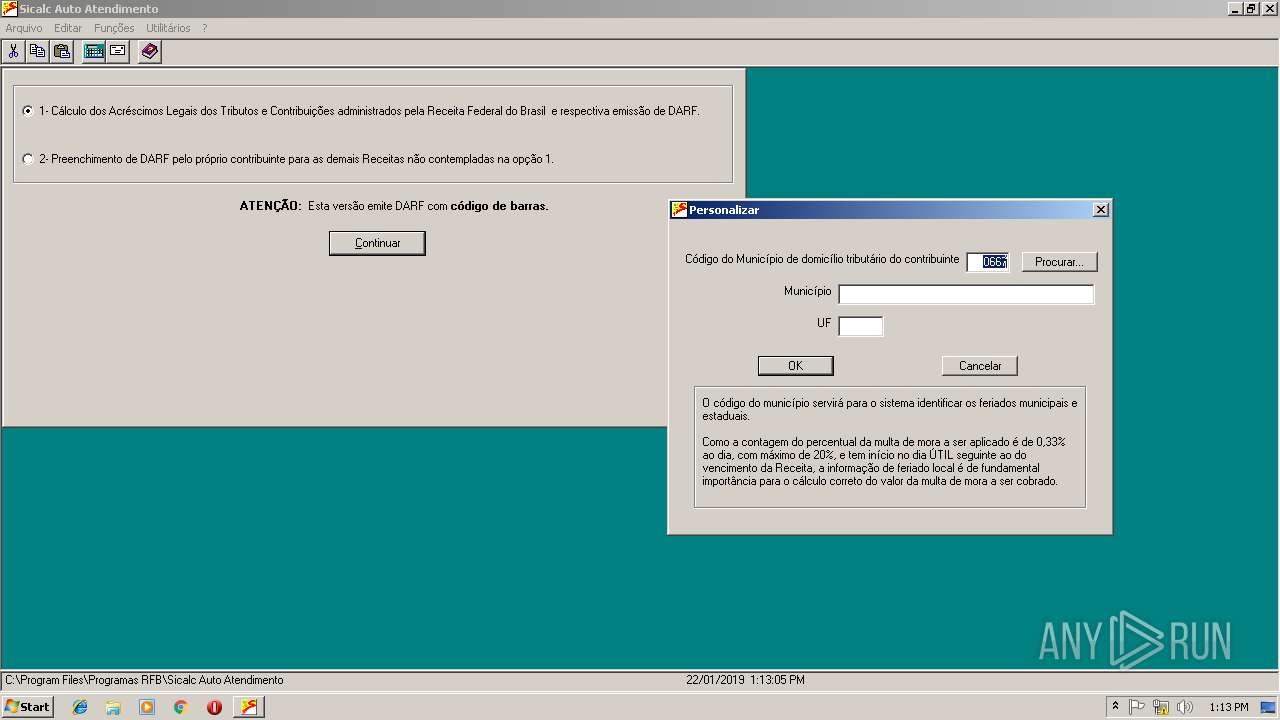
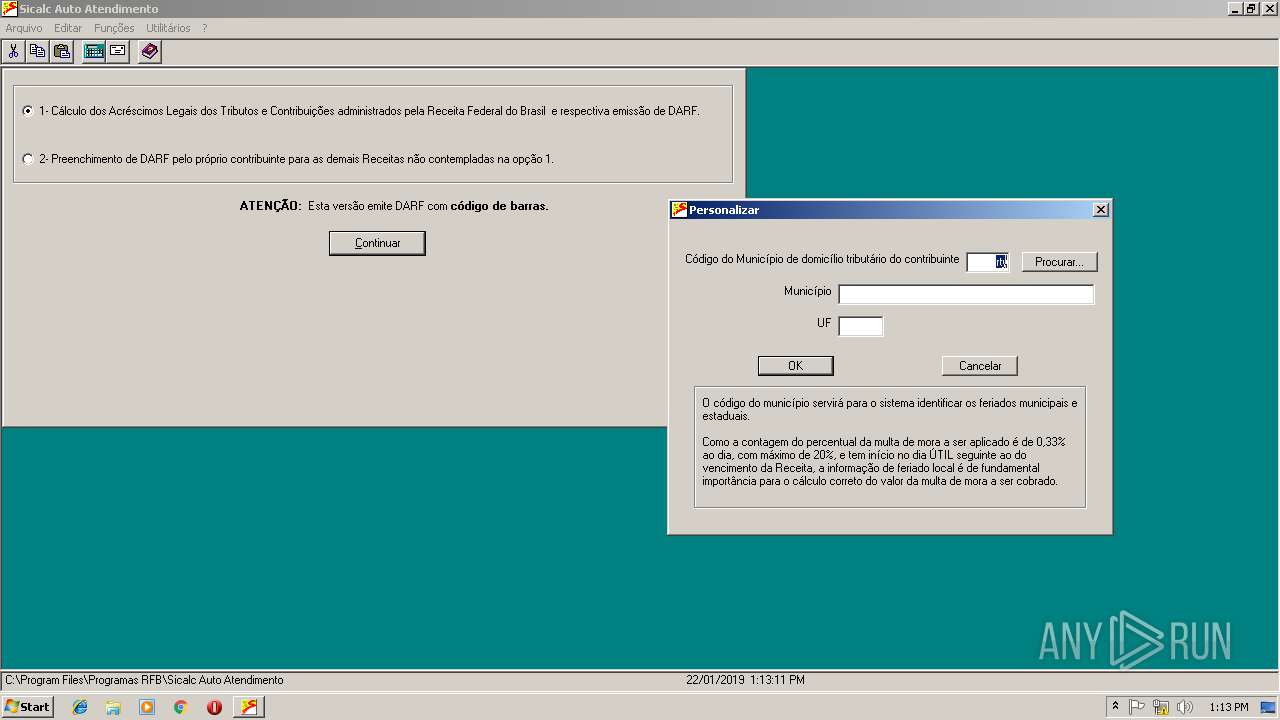
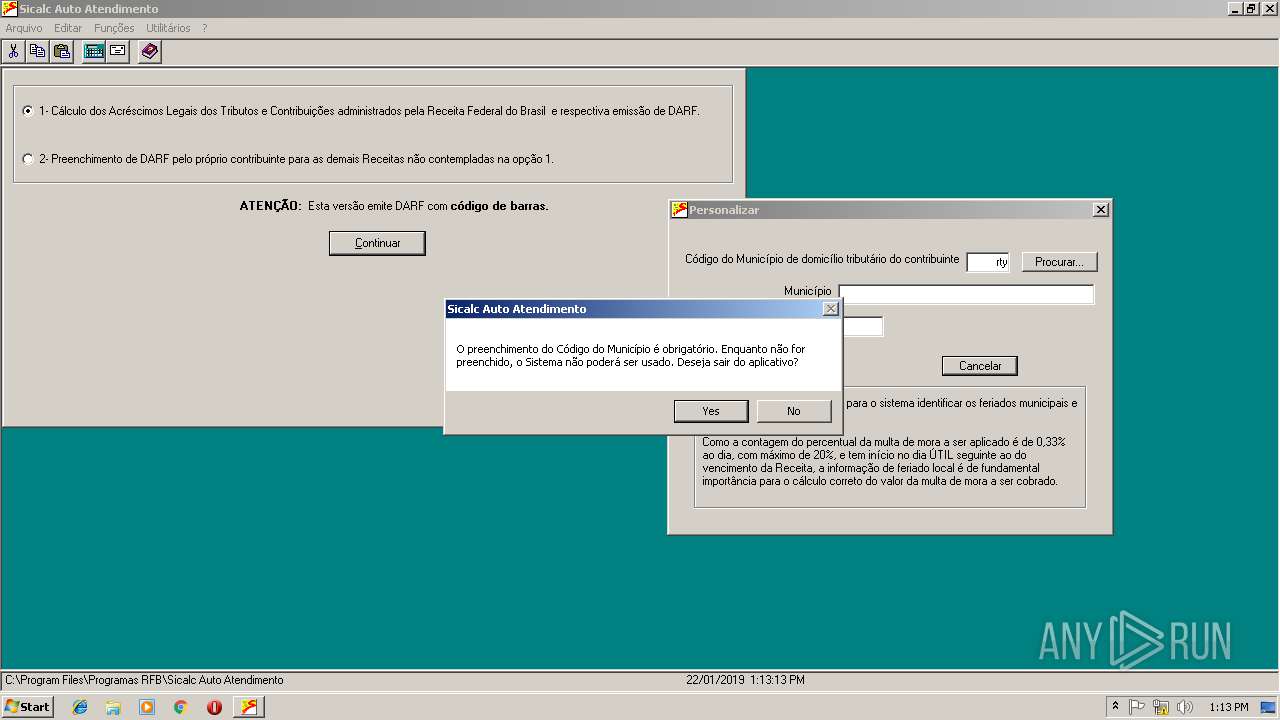
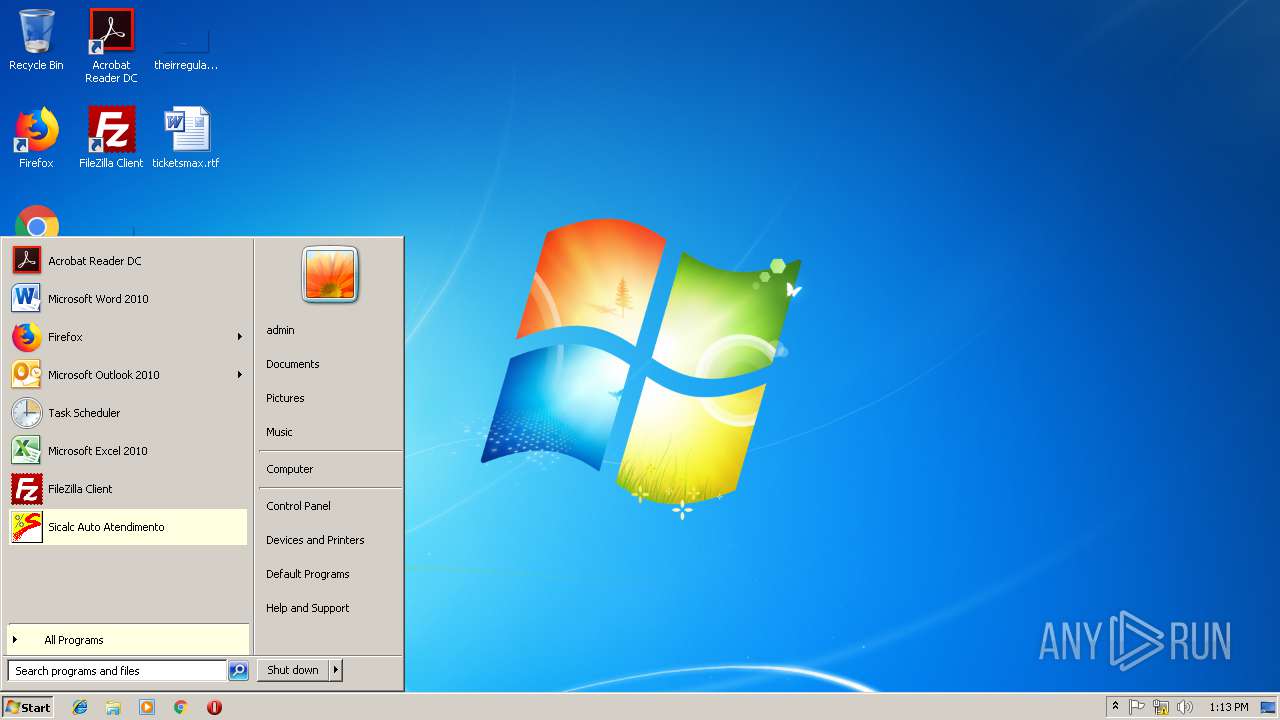
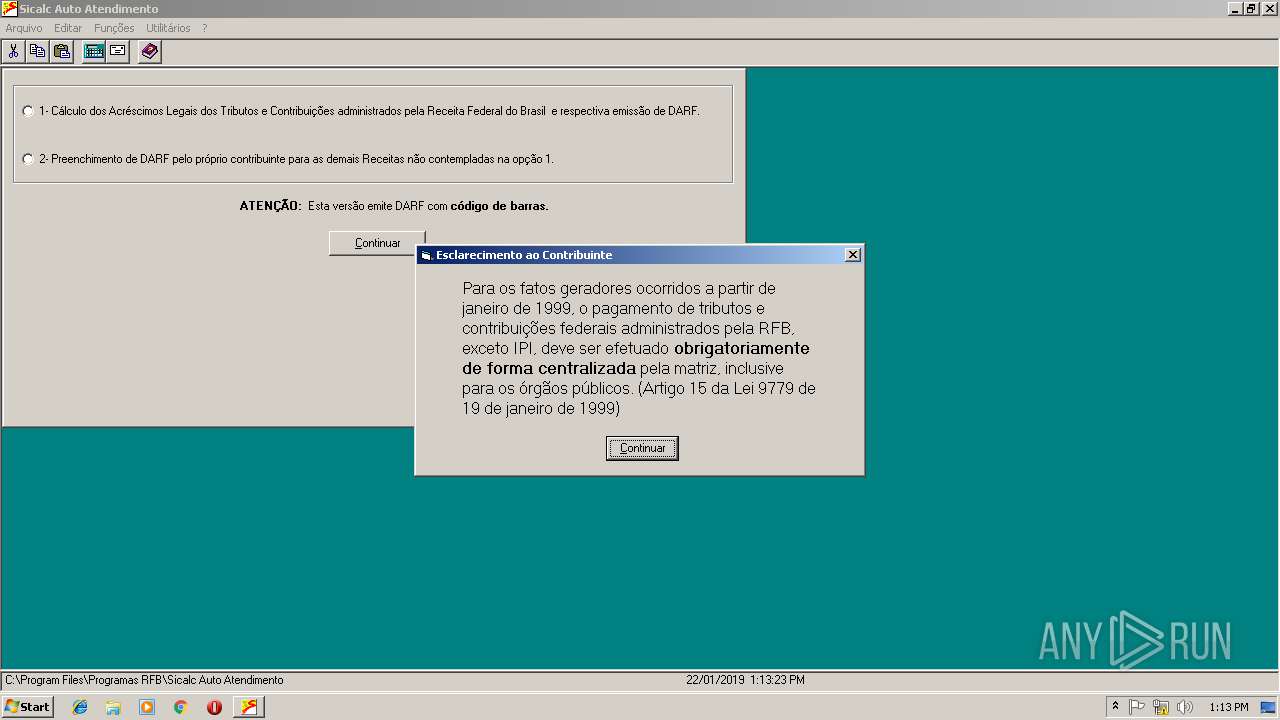
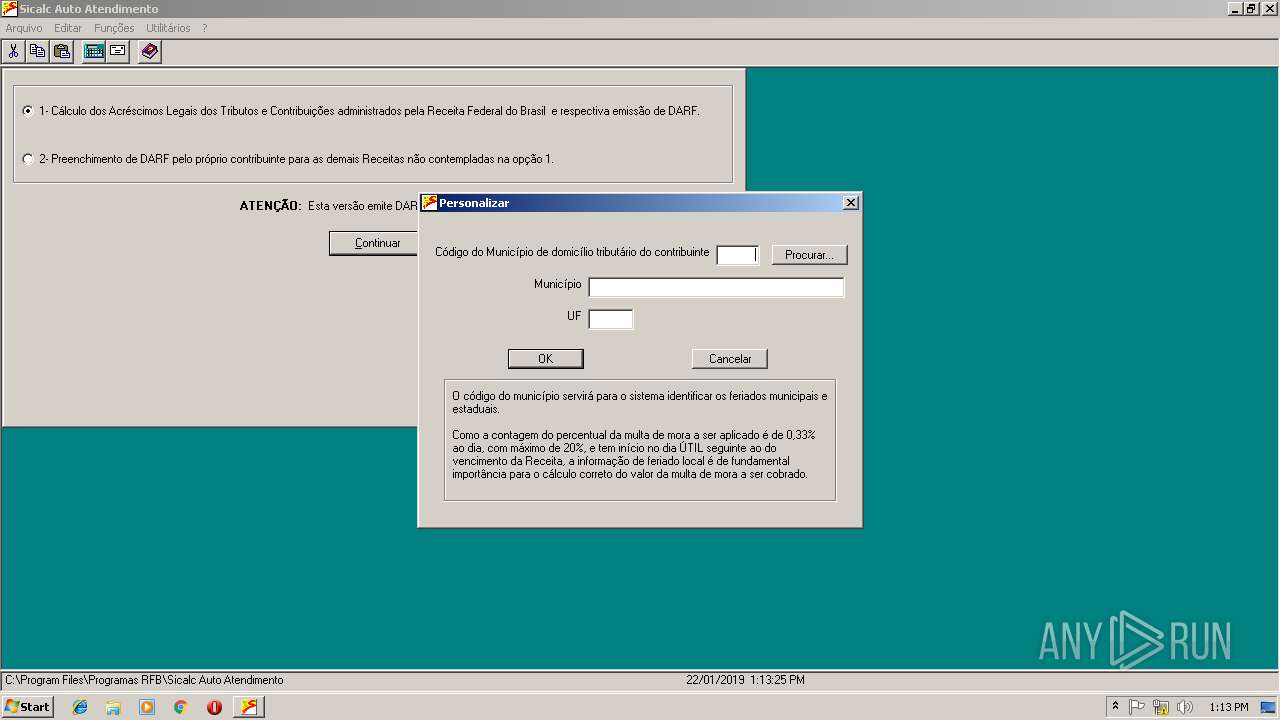
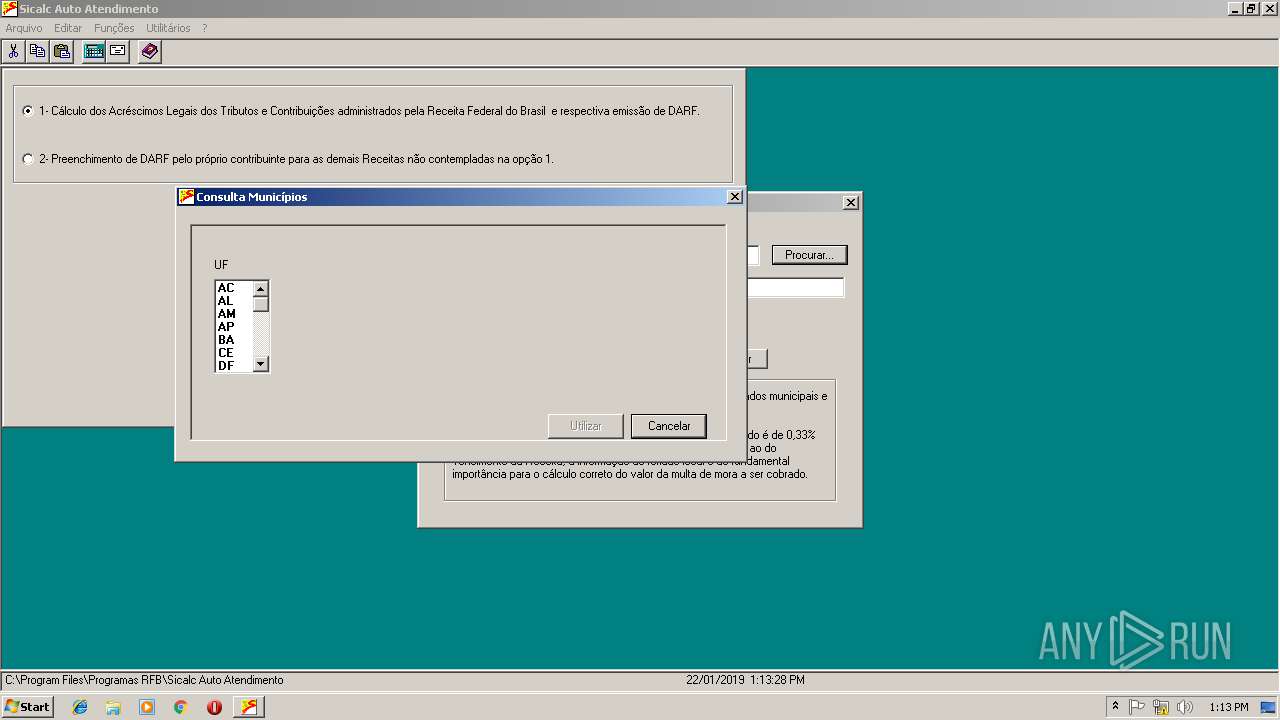
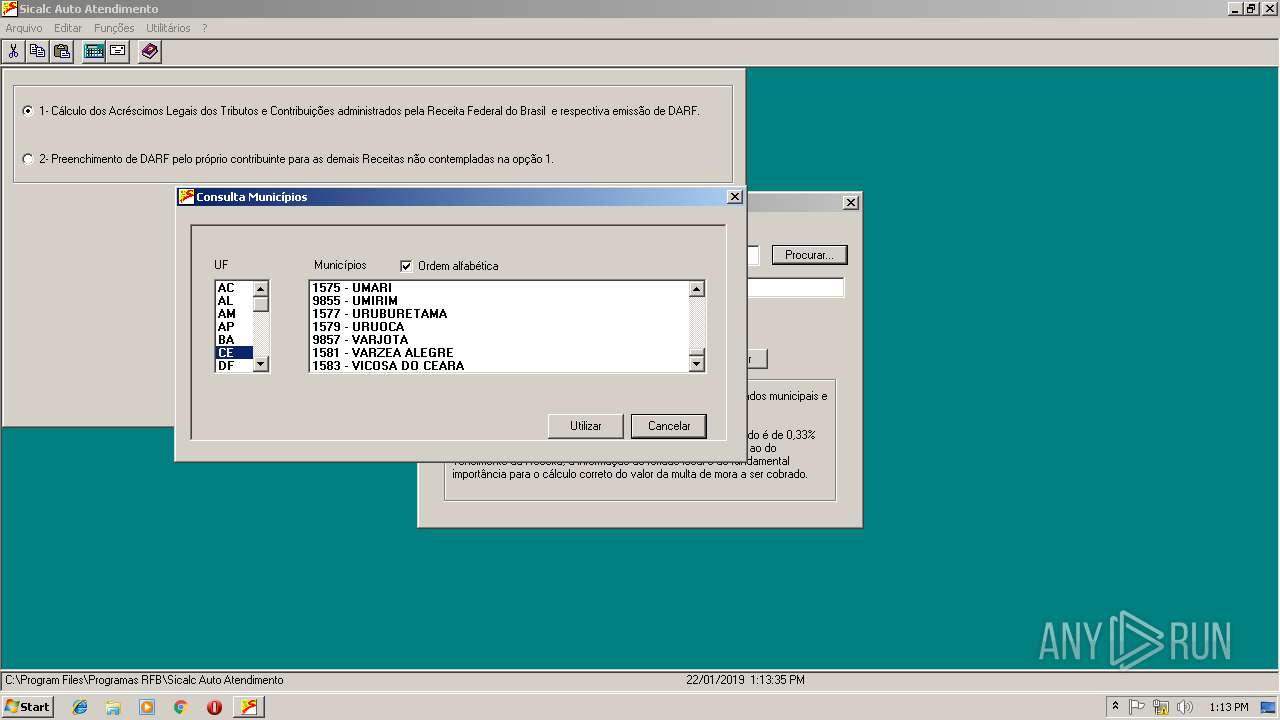
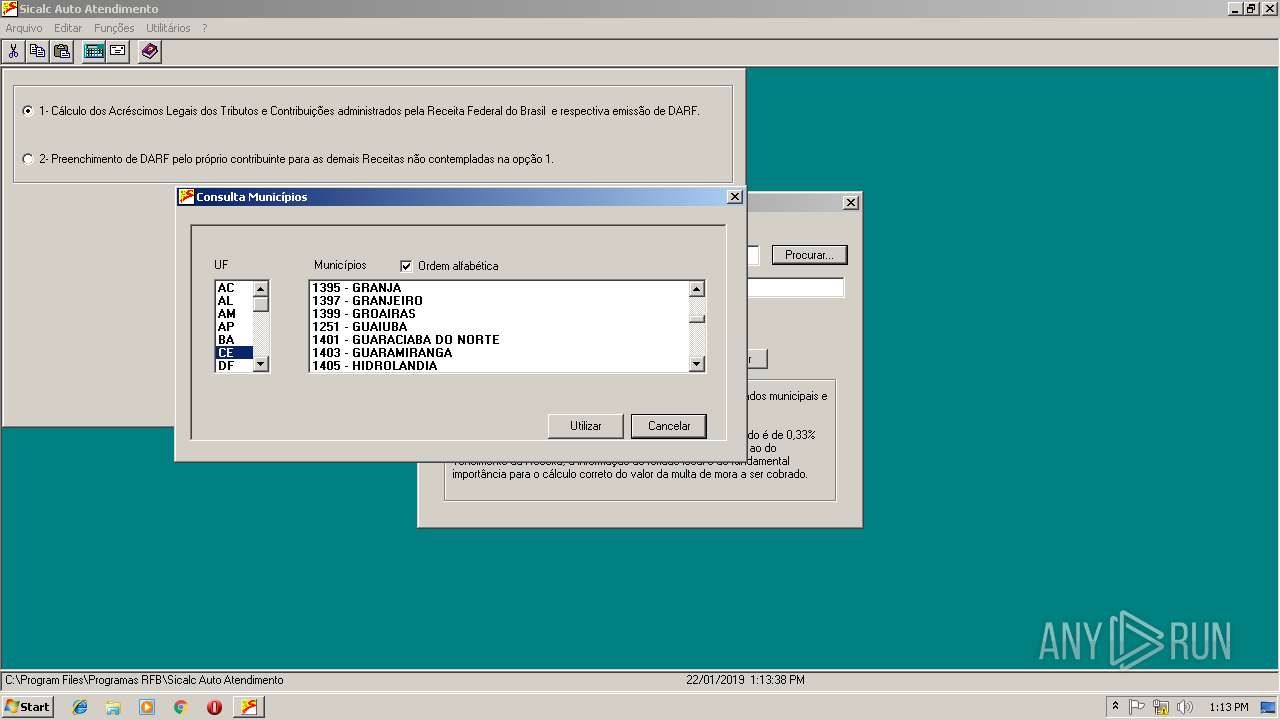
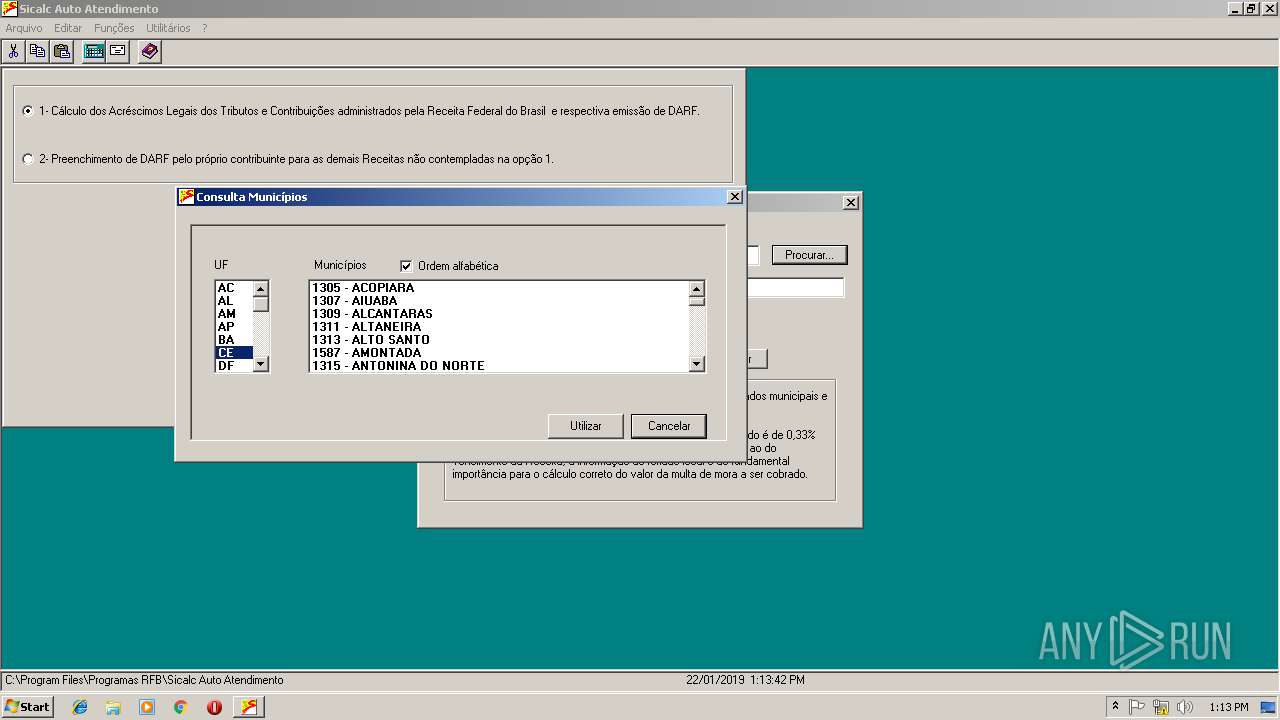
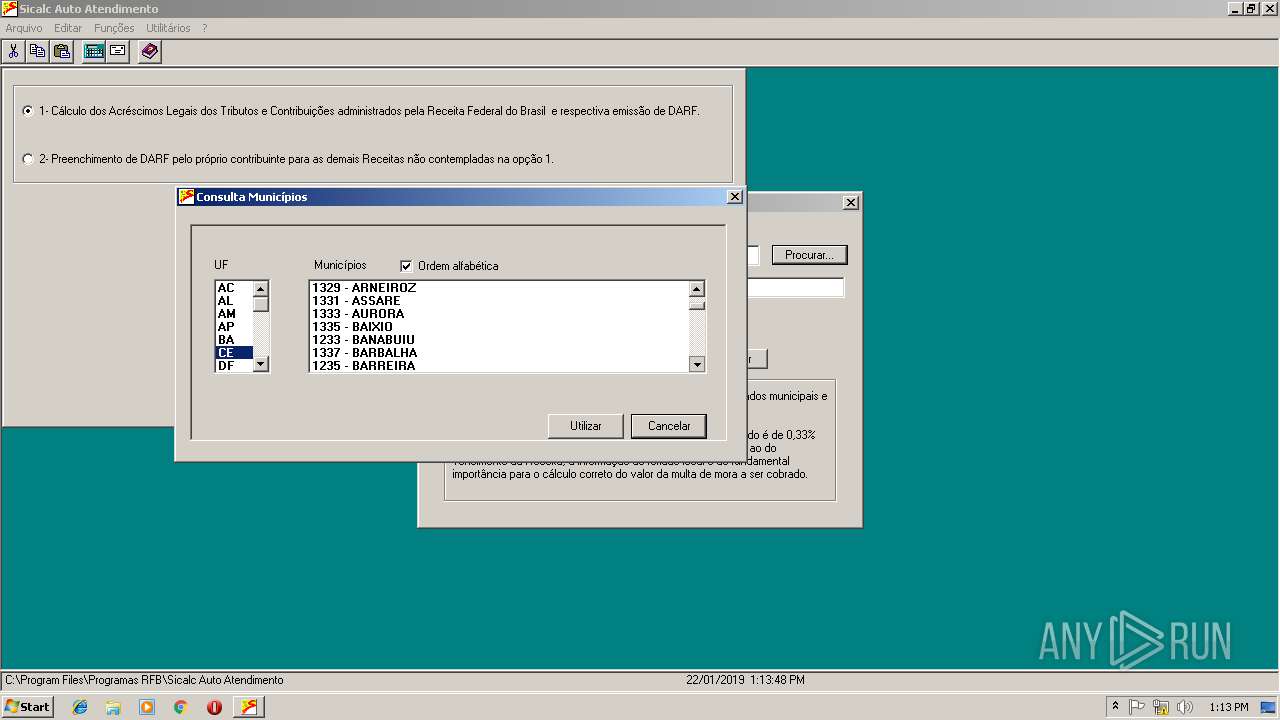
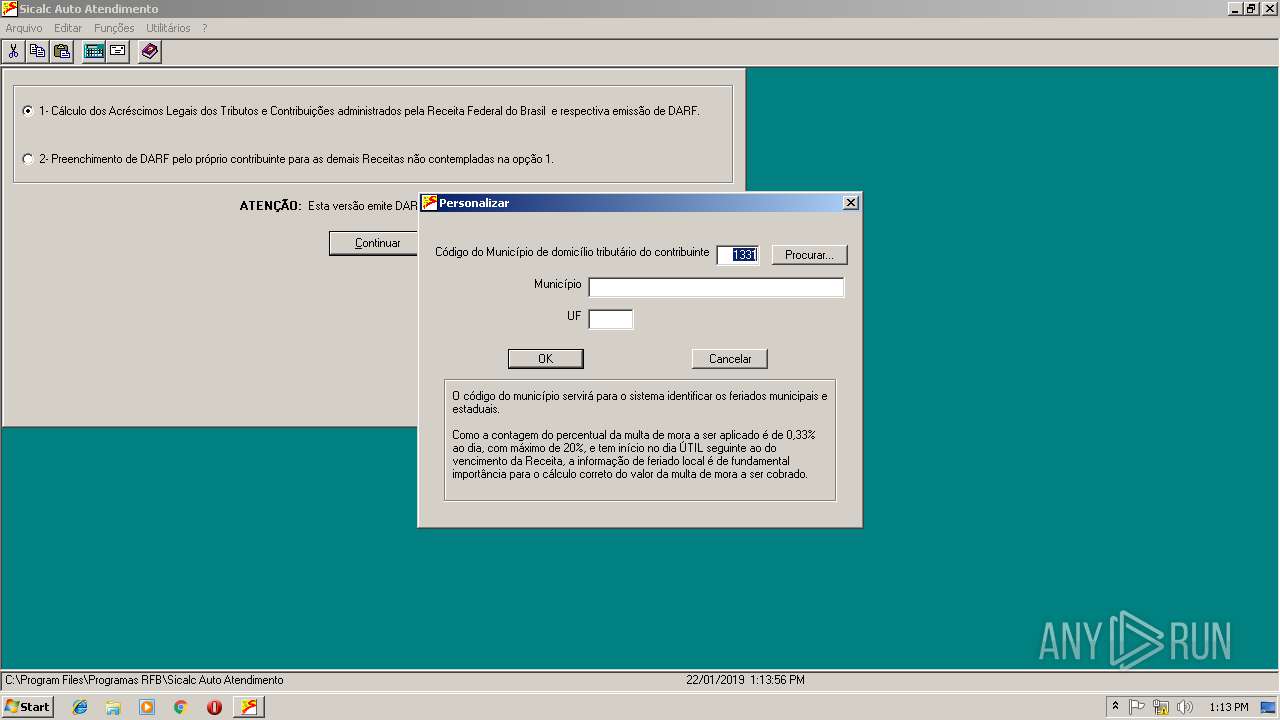
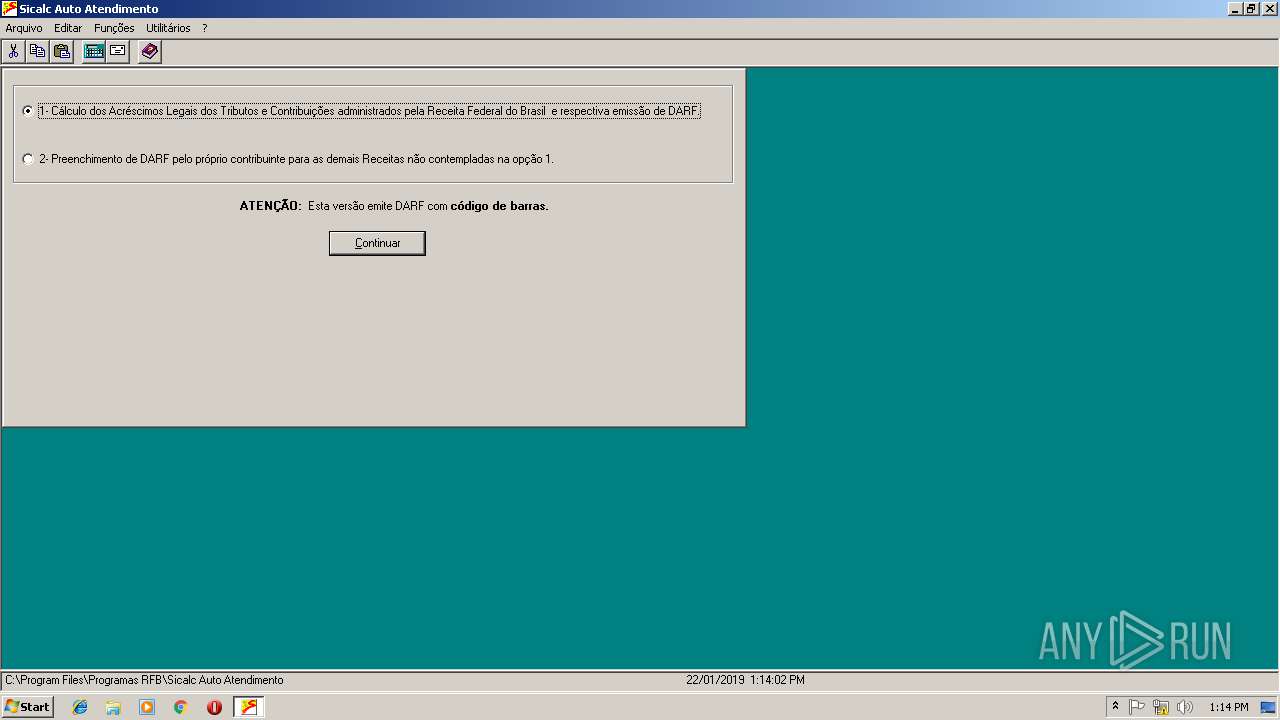
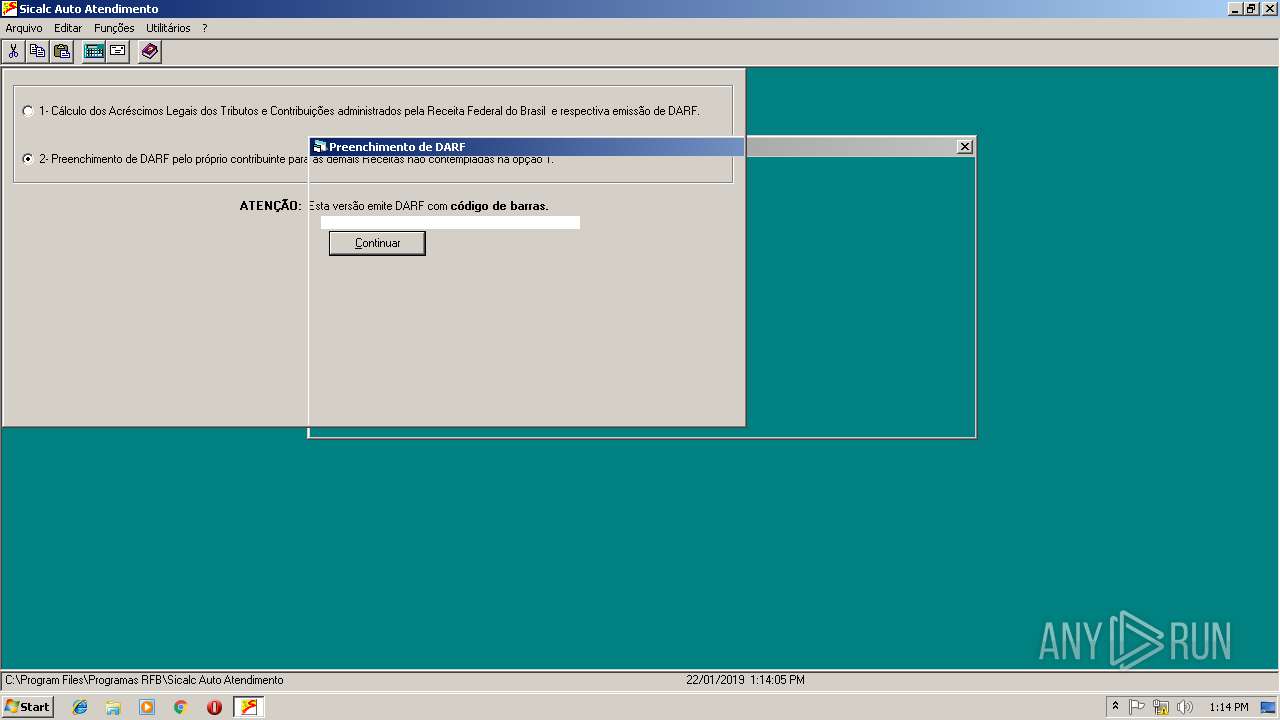
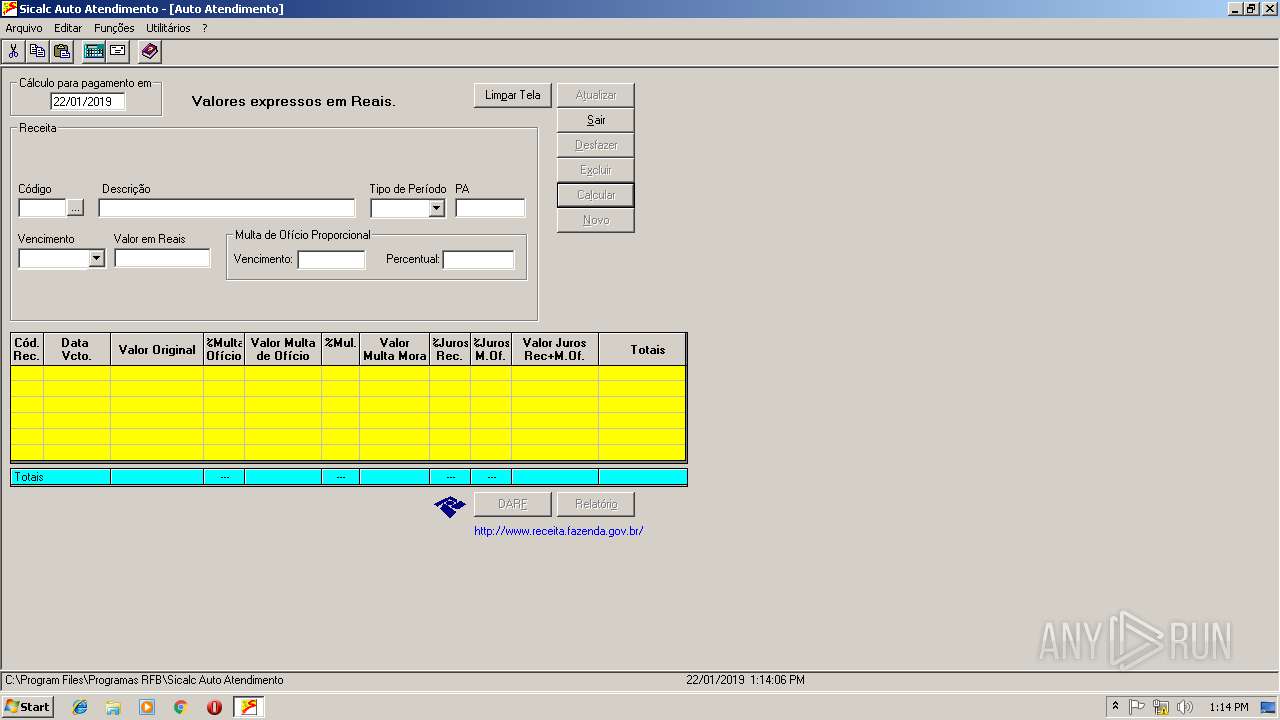
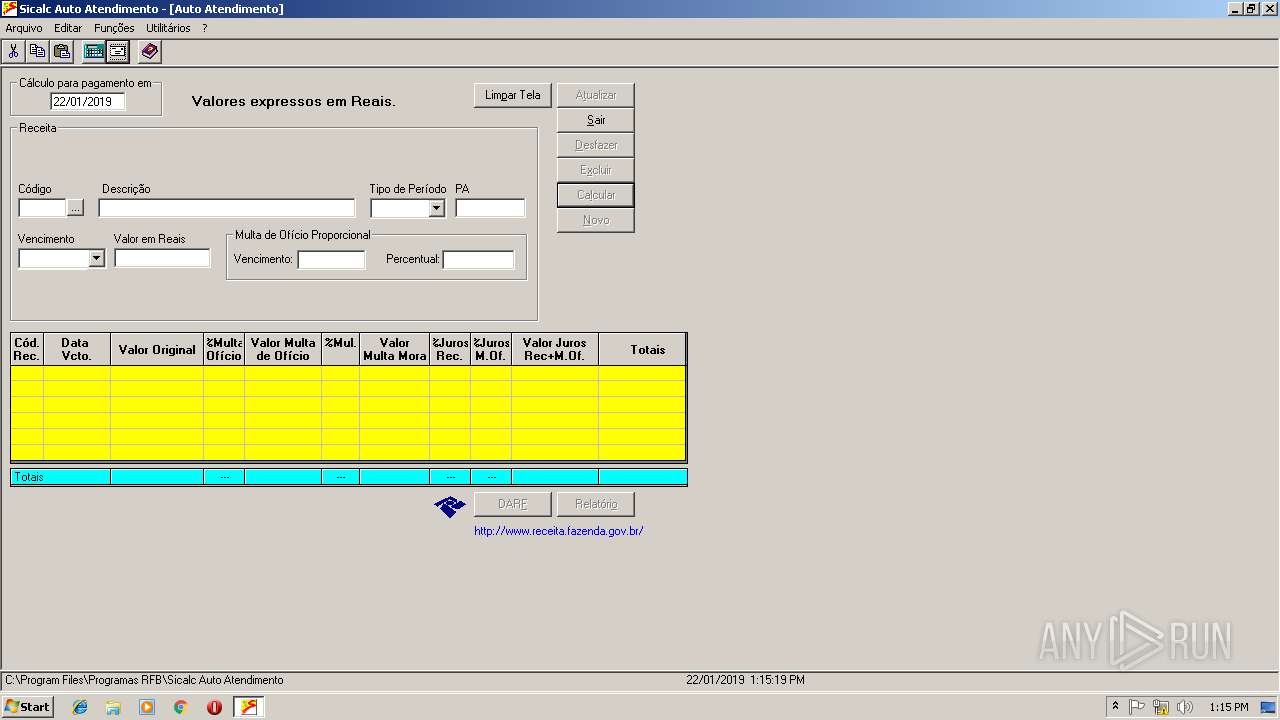
| 2812 | "C:\Program Files\Programas RFB\Sicalc Auto Atendimento\SicalcAA.exe" | C:\Program Files\Programas RFB\Sicalc Auto Atendimento\SicalcAA.exe | — | explorer.exe | |||||||||||
User: admin Company: SERPRO - Serviço Federal de Processamento de Dados Integrity Level: MEDIUM Exit code: 0 Version: 5.40.0066 Modules
| |||||||||||||||
| 3084 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 | |||||||||||||||
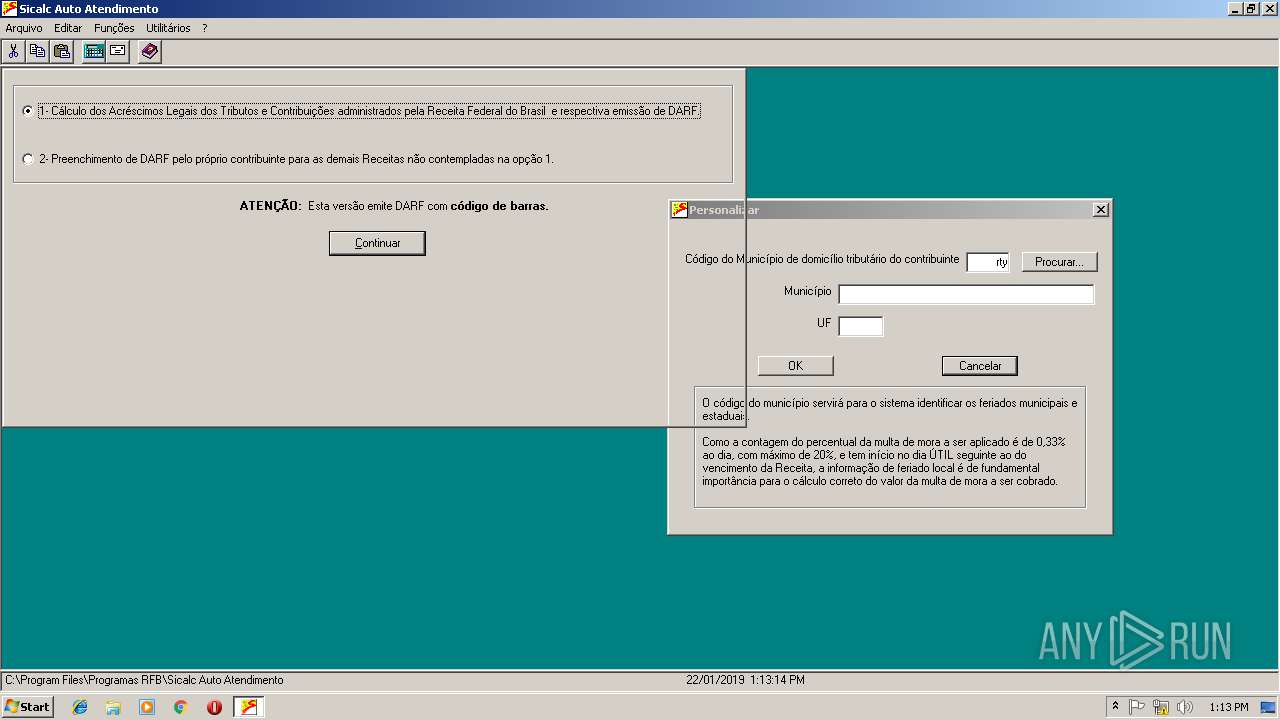
| 3800 | "C:\Program Files\Programas RFB\Sicalc Auto Atendimento\SicalcAA.exe" | C:\Program Files\Programas RFB\Sicalc Auto Atendimento\SicalcAA.exe | — | explorer.exe | |||||||||||
User: admin Company: SERPRO - Serviço Federal de Processamento de Dados Integrity Level: MEDIUM Exit code: 0 Version: 5.40.0066 Modules
| |||||||||||||||
Total events
1 338
Read events
817
Write events
489
Delete events
32
Modification events
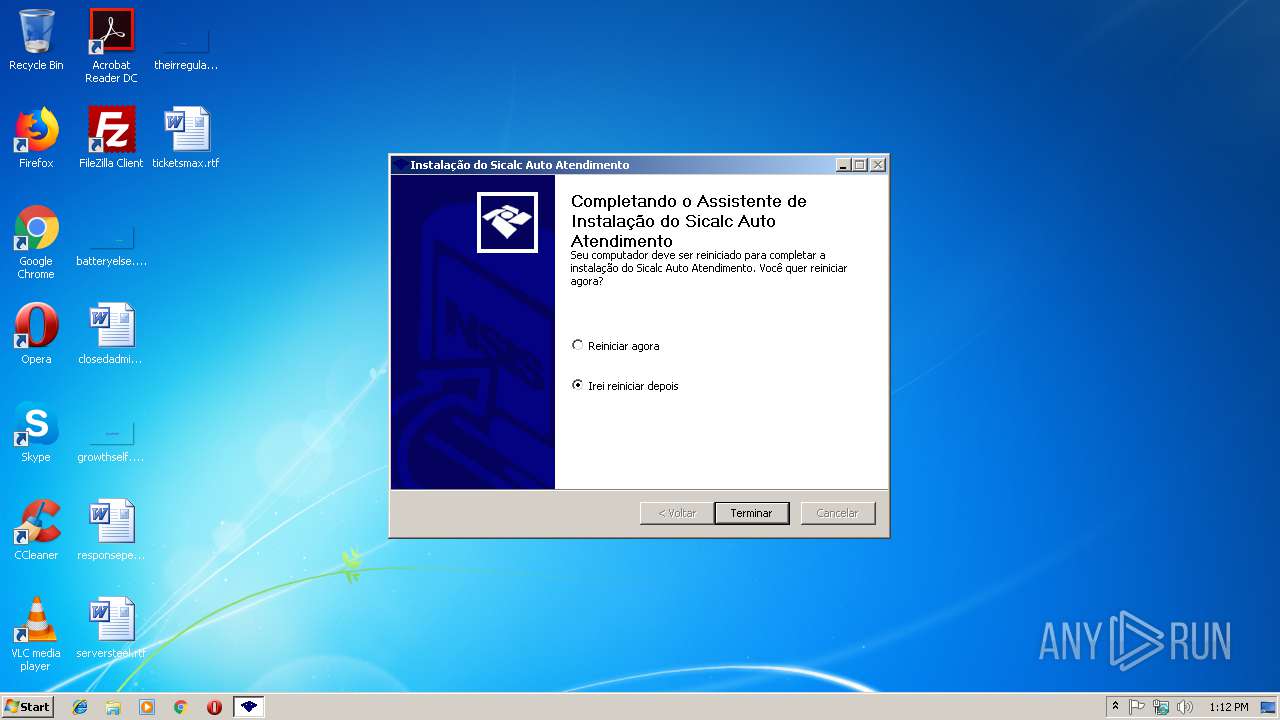
| (PID) Process: | (2164) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Programas RFB\Sicalc Auto Atendimento |
| Operation: | write | Name: | Install_Dir |
Value: C:\Program Files\Programas RFB\Sicalc Auto Atendimento | |||
| (PID) Process: | (2164) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Programas RFB\Sicalc Auto Atendimento |
| Operation: | write | Name: | InstallDate |
Value: 0 | |||
| (PID) Process: | (2164) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sicalc Auto Atendimento |
| Operation: | write | Name: | DisplayName |
Value: Sicalc Auto Atendimento | |||
| (PID) Process: | (2164) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sicalc Auto Atendimento |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\Programas RFB\Sicalc Auto Atendimento\uninstall.exe" | |||
| (PID) Process: | (2164) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sicalc Auto Atendimento |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Program Files\Programas RFB\Sicalc Auto Atendimento\uninstall.exe" /S | |||
| (PID) Process: | (2164) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sicalc Auto Atendimento |
| Operation: | write | Name: | DisplayIcon |
Value: "C:\Program Files\Programas RFB\Sicalc Auto Atendimento\SicalcAA.exe" | |||
| (PID) Process: | (2164) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sicalc Auto Atendimento |
| Operation: | write | Name: | DisplayVersion |
Value: 5.40 | |||
| (PID) Process: | (2164) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sicalc Auto Atendimento |
| Operation: | write | Name: | Publisher |
Value: Receita Federal do Brasil | |||
| (PID) Process: | (2164) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sicalc Auto Atendimento |
| Operation: | write | Name: | UrlInfoAbout |
Value: http://www.receita.fazenda.gov.br/ | |||
| (PID) Process: | (2164) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sicalc Auto Atendimento |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
Executable files
13
Suspicious files
6
Text files
16
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2164 | setup.exe | C:\ProgramData\Programas RFB\Sicalc Auto Atendimento\SicalcAA.mdb | — | |
MD5:— | SHA256:— | |||
| 2164 | setup.exe | C:\Program Files\Programas RFB\Sicalc Auto Atendimento\SicalcAA.exe | executable | |
MD5:— | SHA256:— | |||
| 2812 | SicalcAA.exe | C:\Users\admin\AppData\Roaming\Programas RFB\Sicalc Auto Atendimento\SicalcAA.mdb | — | |
MD5:— | SHA256:— | |||
| 2812 | SicalcAA.exe | C:\Users\admin\AppData\Roaming\Programas RFB\Sicalc Auto Atendimento\SicalcAA.ldb | — | |
MD5:— | SHA256:— | |||
| 2812 | SicalcAA.exe | C:\Users\admin\AppData\Local\Temp\~DFDCA894708FBCA309.TMP | — | |
MD5:— | SHA256:— | |||
| 3800 | SicalcAA.exe | C:\Users\admin\AppData\Roaming\Programas RFB\Sicalc Auto Atendimento\SicalcAA.ldb | — | |
MD5:— | SHA256:— | |||
| 3800 | SicalcAA.exe | C:\Users\admin\AppData\Roaming\Programas RFB\Sicalc Auto Atendimento\SicalcAA.mdb | — | |
MD5:— | SHA256:— | |||
| 2308 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2164 | setup.exe | C:\Program Files\Programas RFB\Sicalc Auto Atendimento\CriticasCalculo.dll.manifest | xml | |
MD5:— | SHA256:— | |||
| 2308 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2308 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2308 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
568 | iexplore.exe | 161.148.249.7:443 | www18.receita.fazenda.gov.br | SERVICO FEDERAL DE PROCESSAMENTO DE DADOS - SERPRO | BR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www18.receita.fazenda.gov.br |
| unknown |