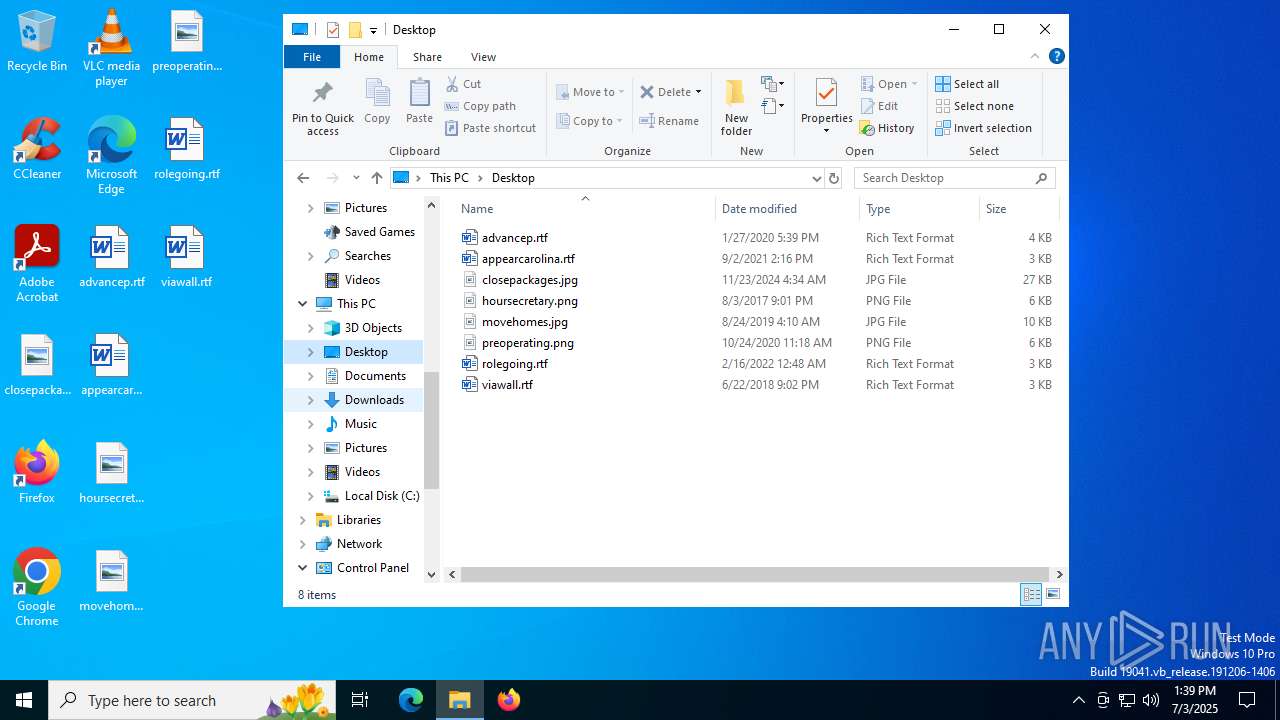
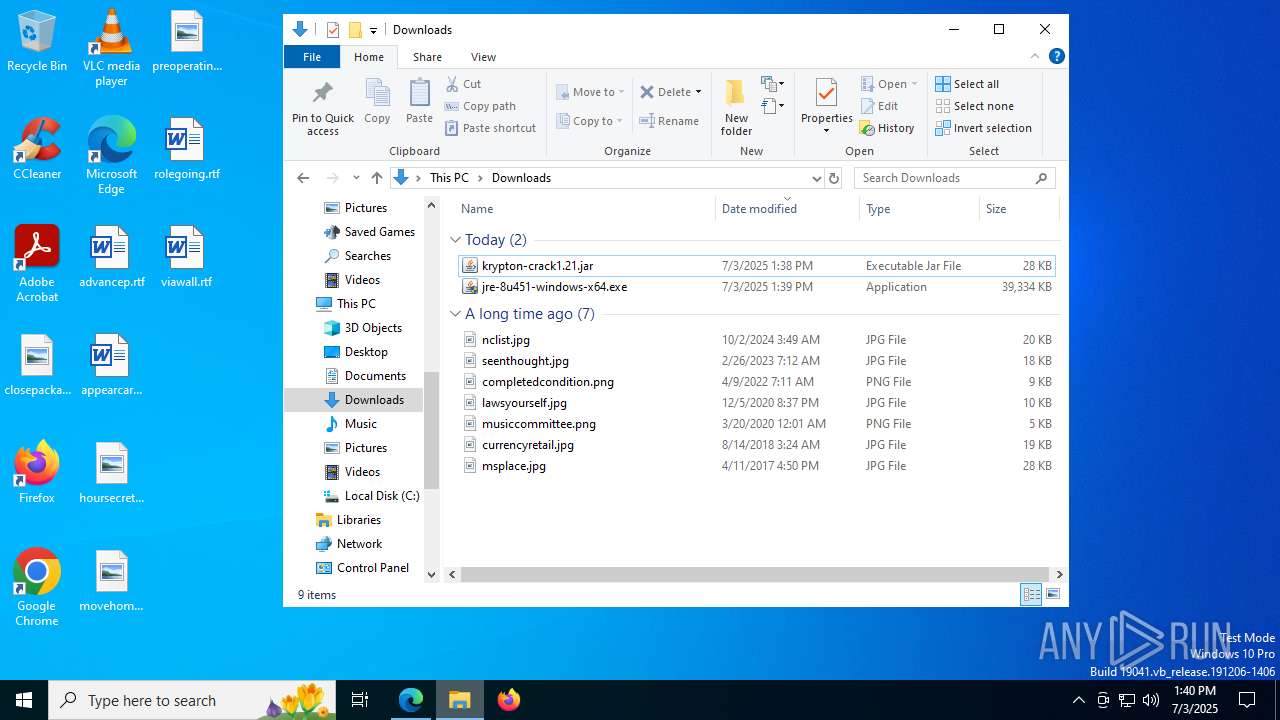
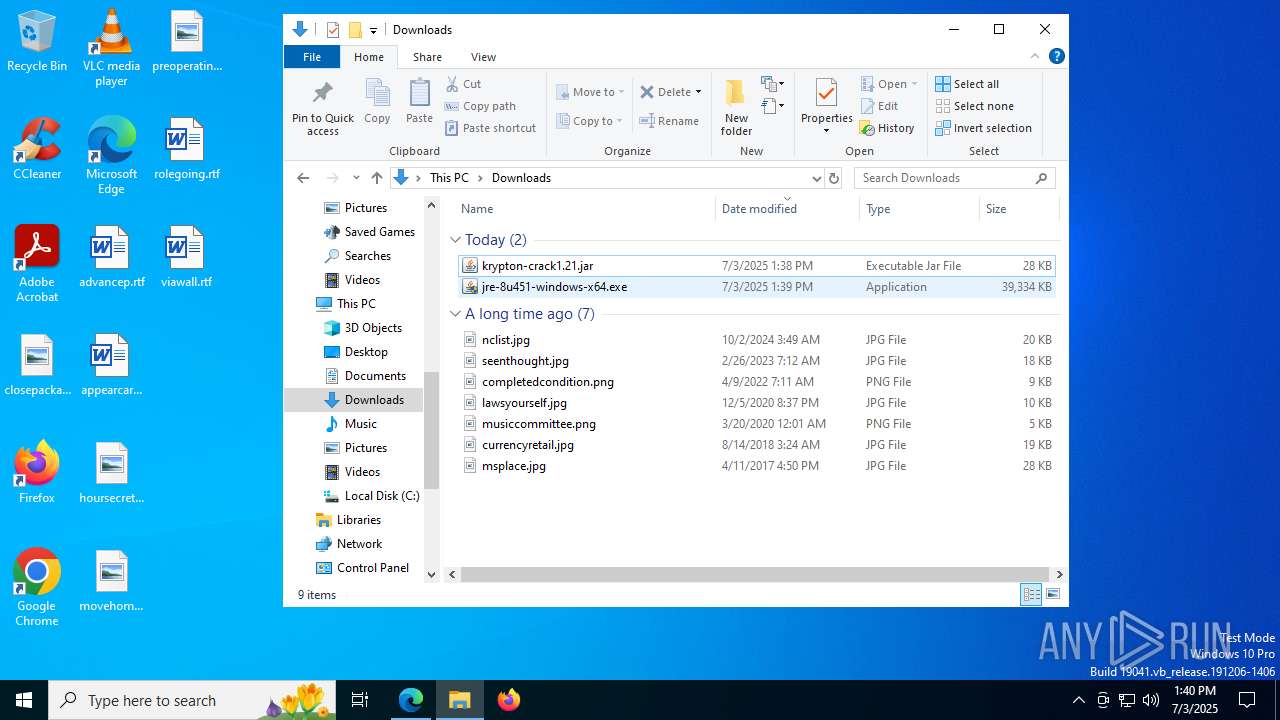
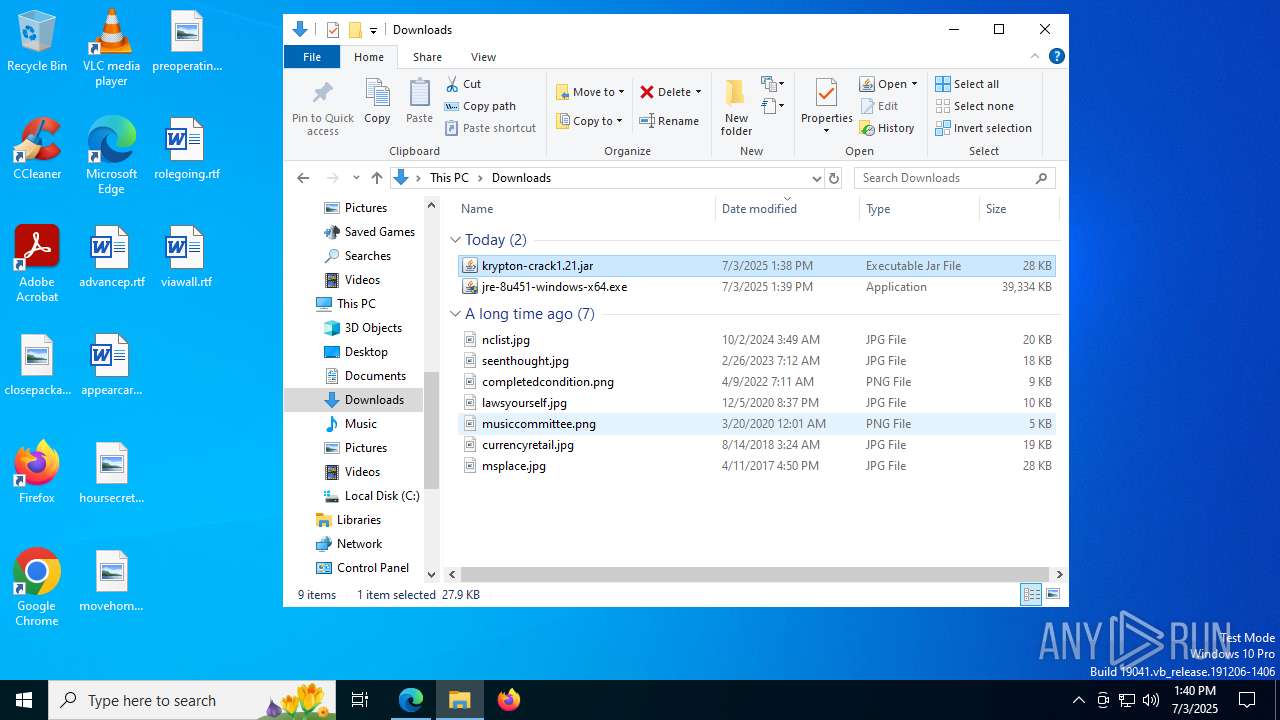
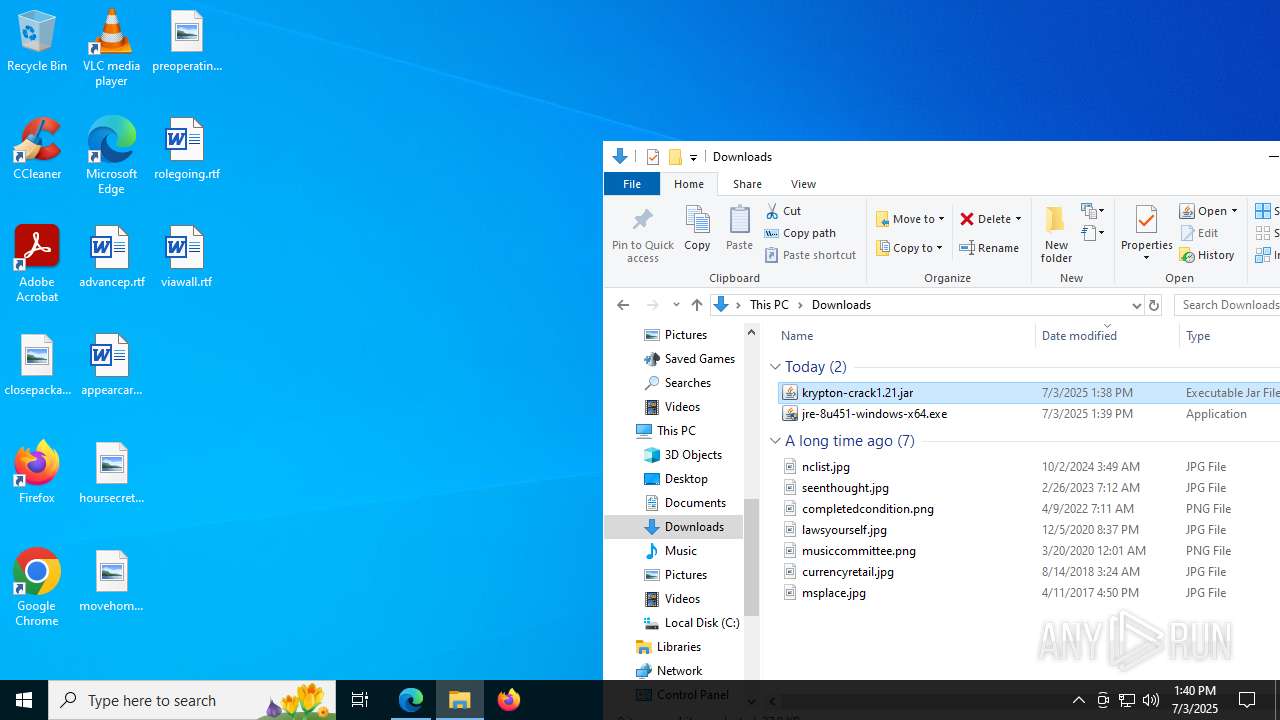
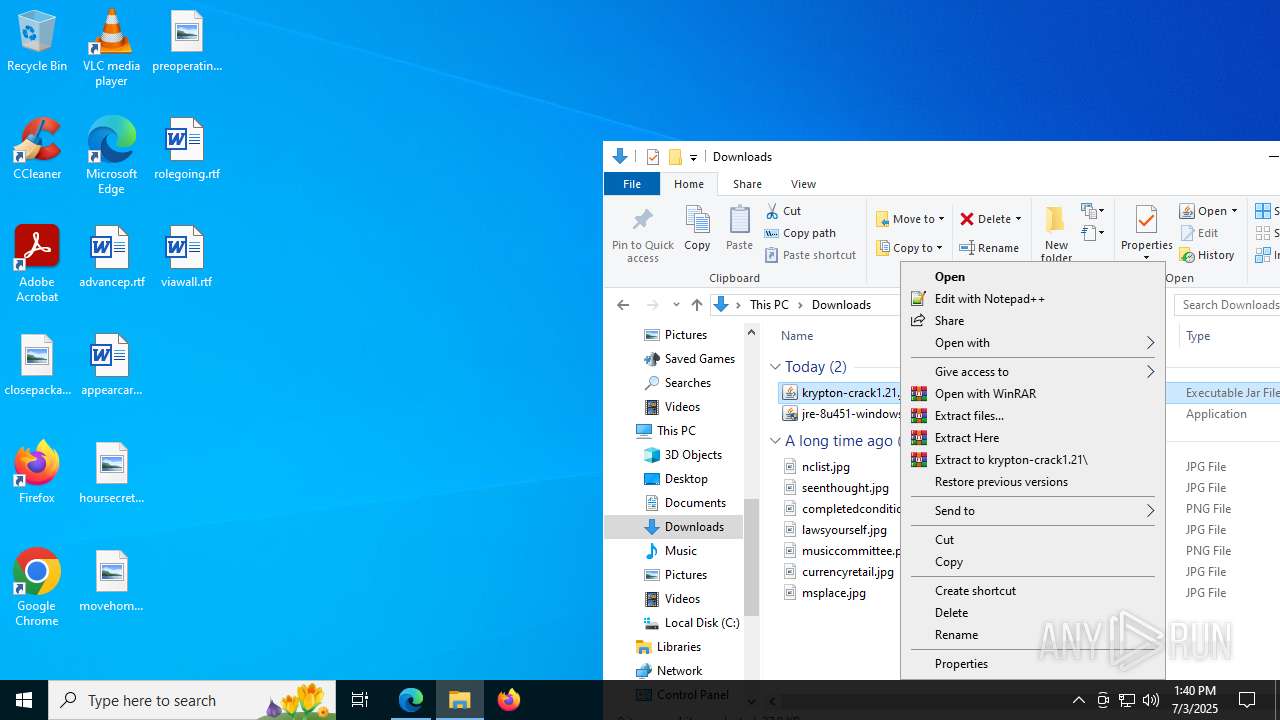
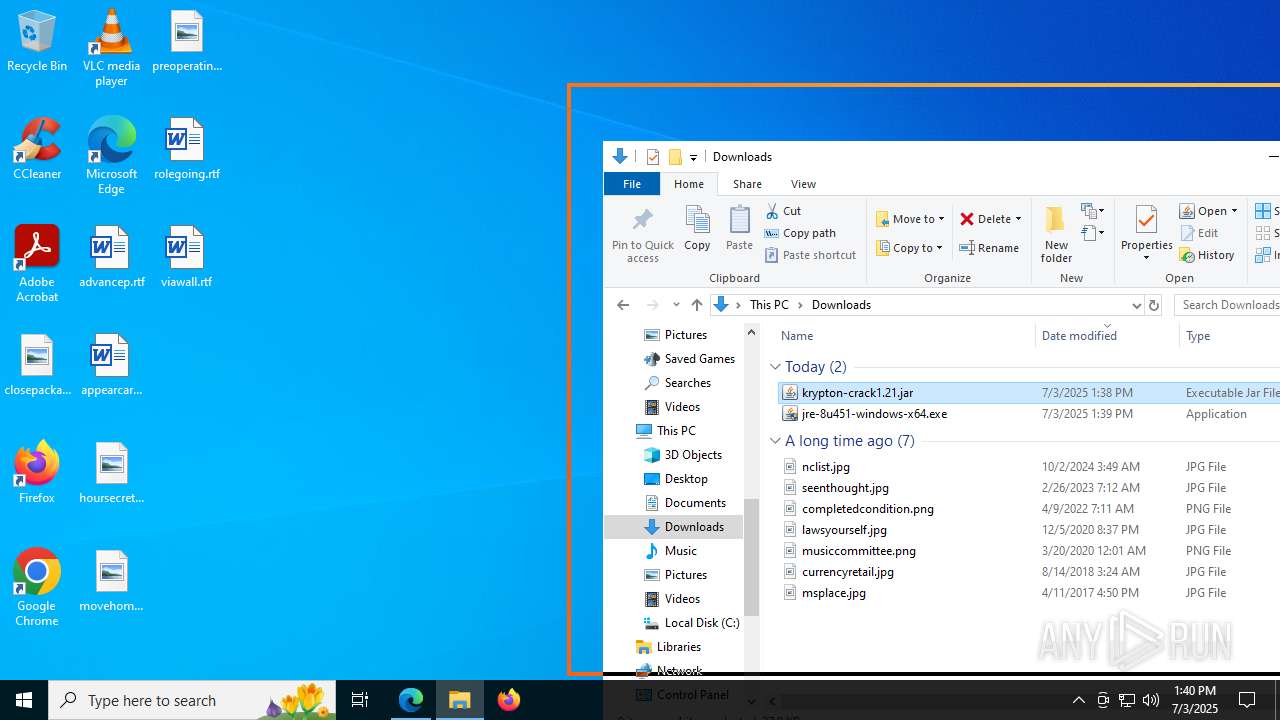
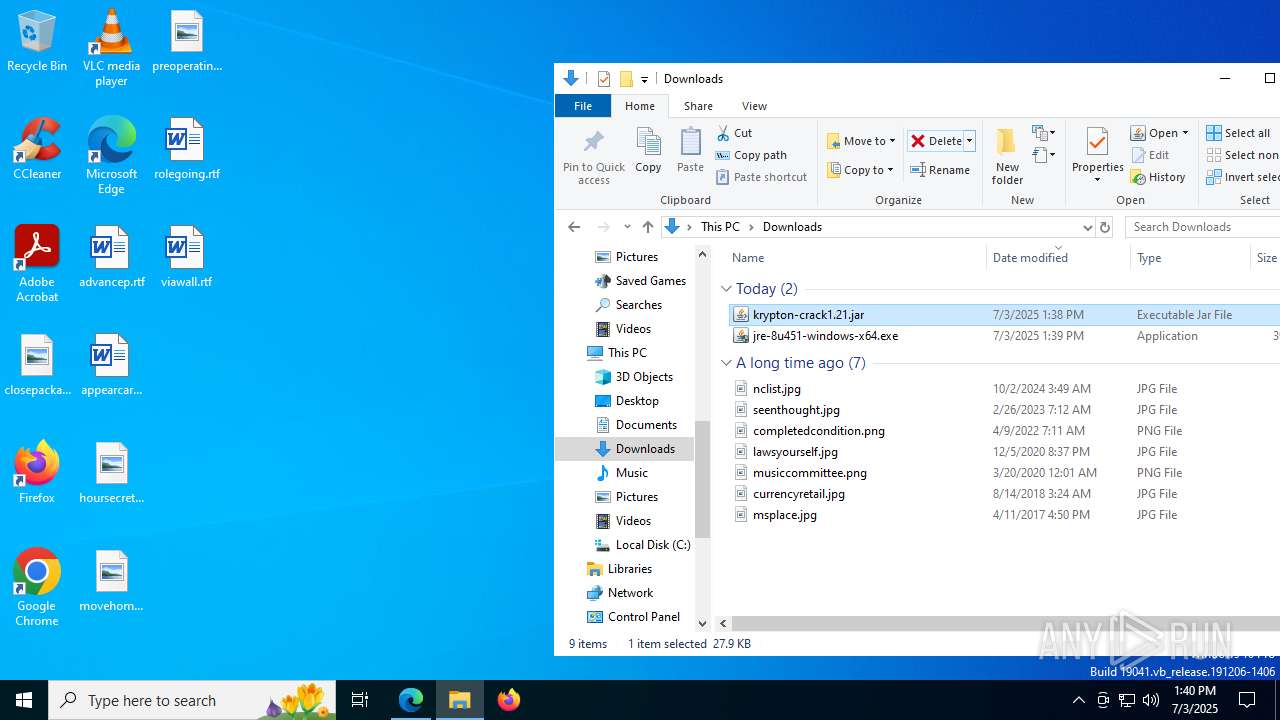
| File name: | krypton-crack1.21.jar |
| Full analysis: | https://app.any.run/tasks/95e16b38-cf51-4aab-90fd-2740f541ea91 |
| Verdict: | Malicious activity |
| Analysis date: | July 03, 2025, 13:38:50 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/java-archive |
| File info: | Java archive data (JAR) |
| MD5: | 5273BE1D7F2206CCCDC04325725C6C33 |
| SHA1: | 9769942C8E1C90EDEFB7BB9C53F3F9DF5070282E |
| SHA256: | FD4C7C423BA6D7332537D96B84F82FBAF905CA8B48ACDD2B184084A8062AE160 |
| SSDEEP: | 768:jI3X/ei2bqr8agSuJXQhqhN6IignIeicxcP:jI3X/ei2a8a+JXCqn68viIq |
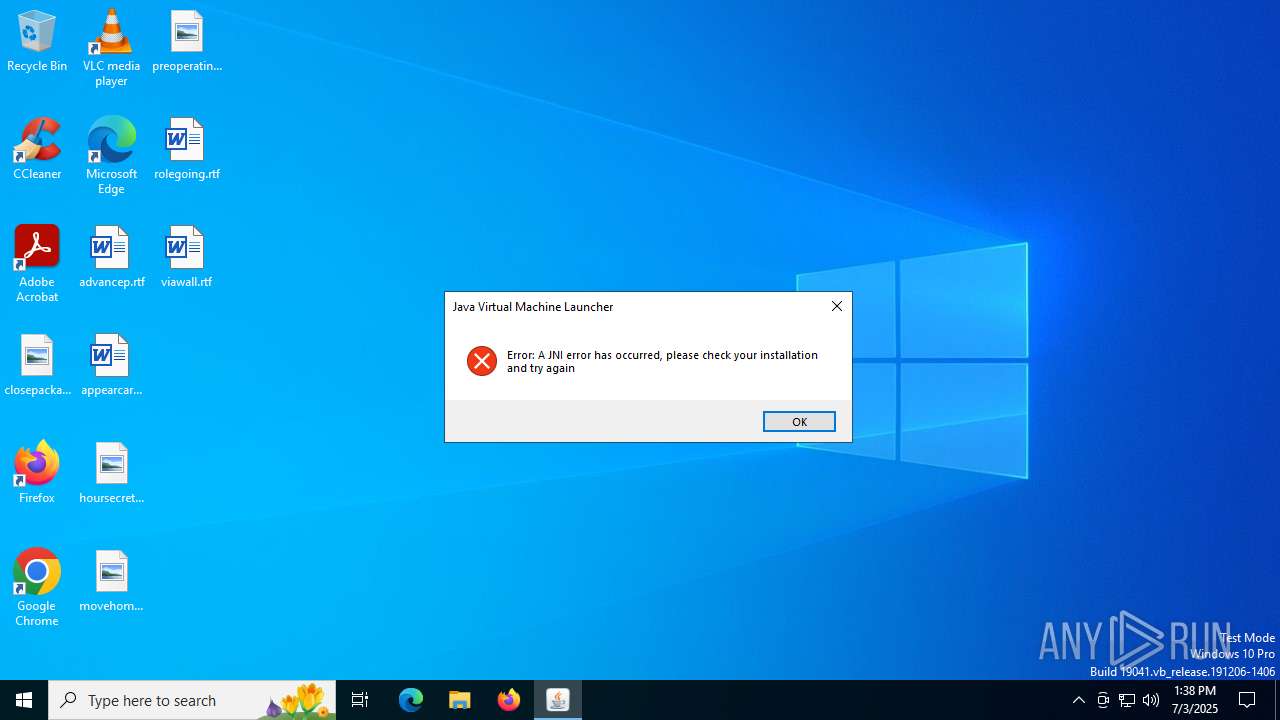
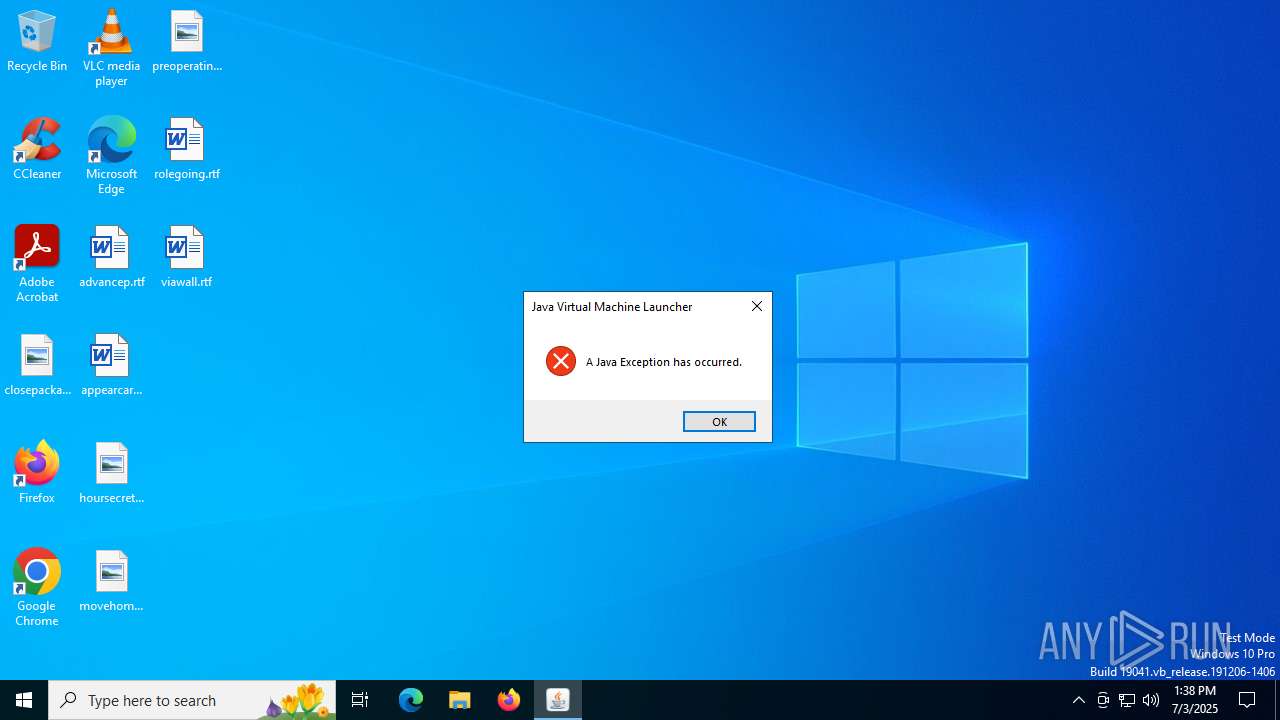
MALICIOUS
No malicious indicators.SUSPICIOUS
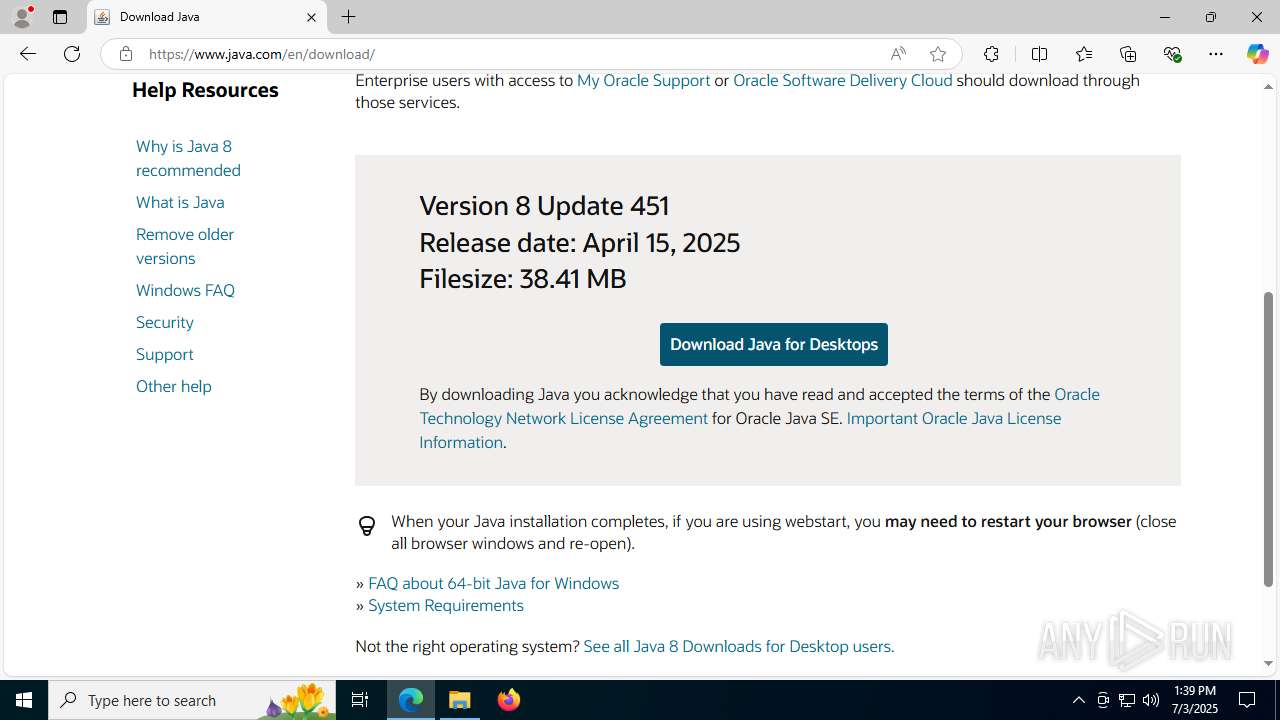
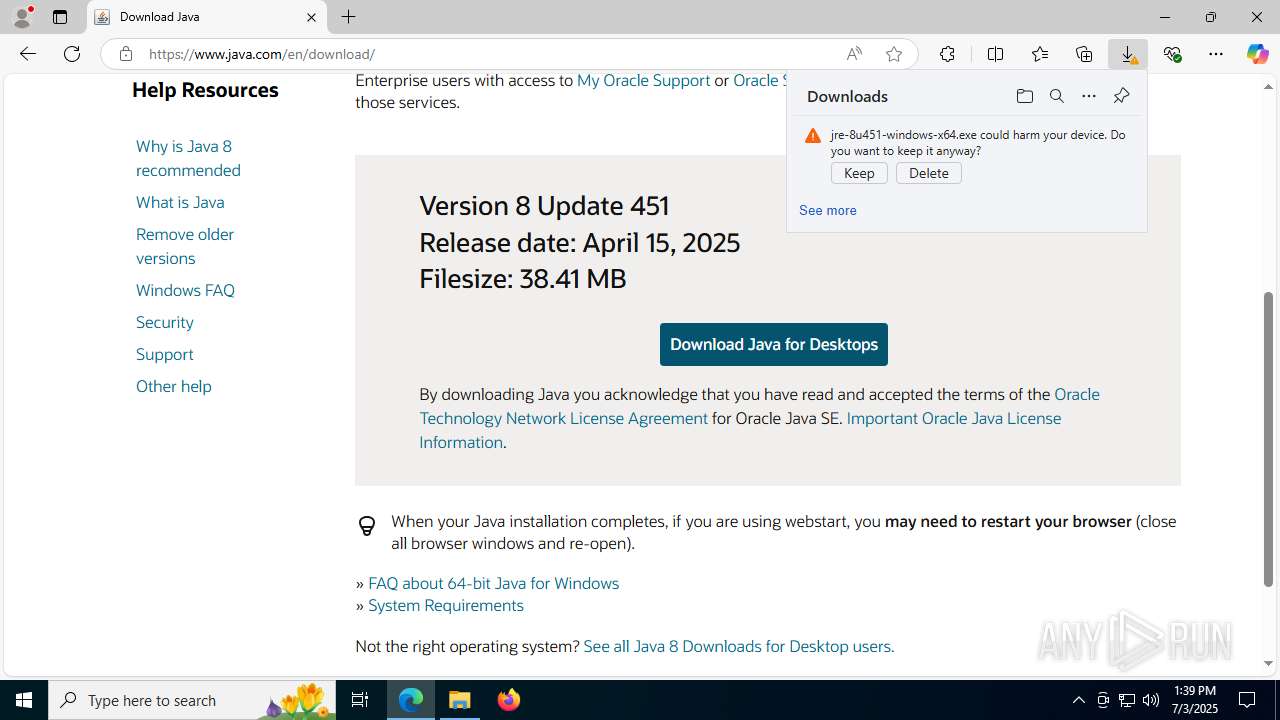
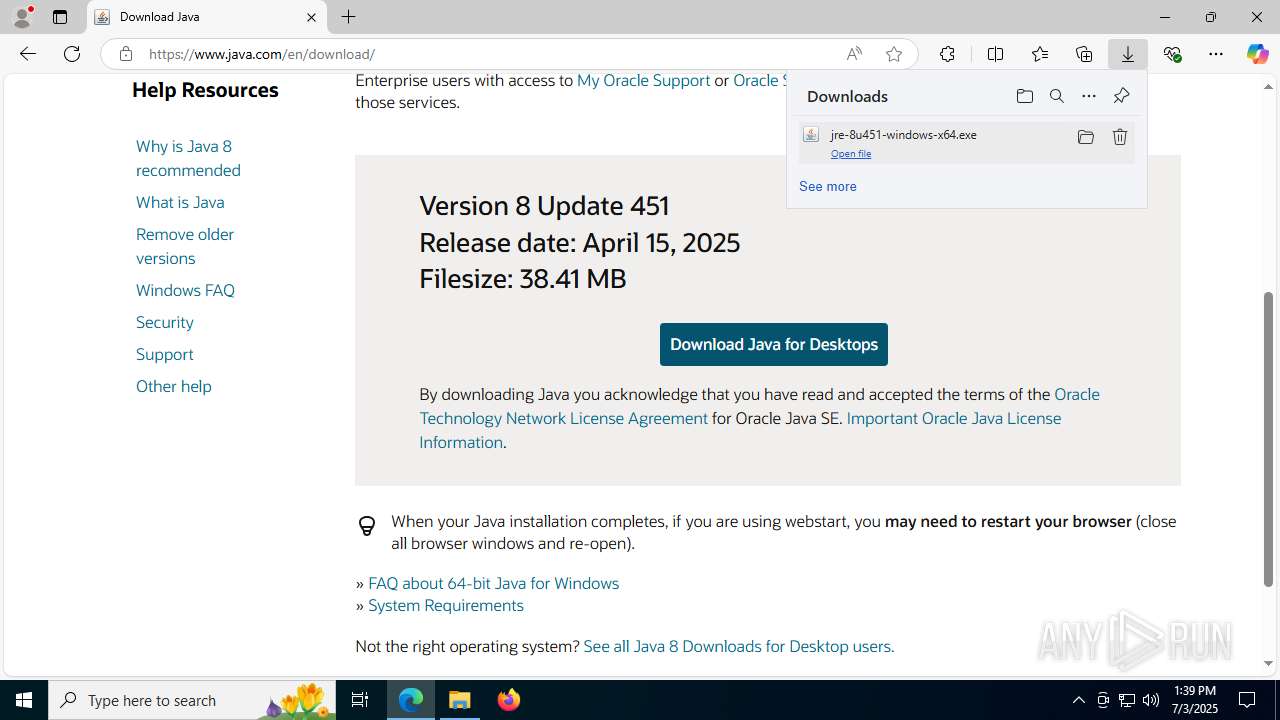
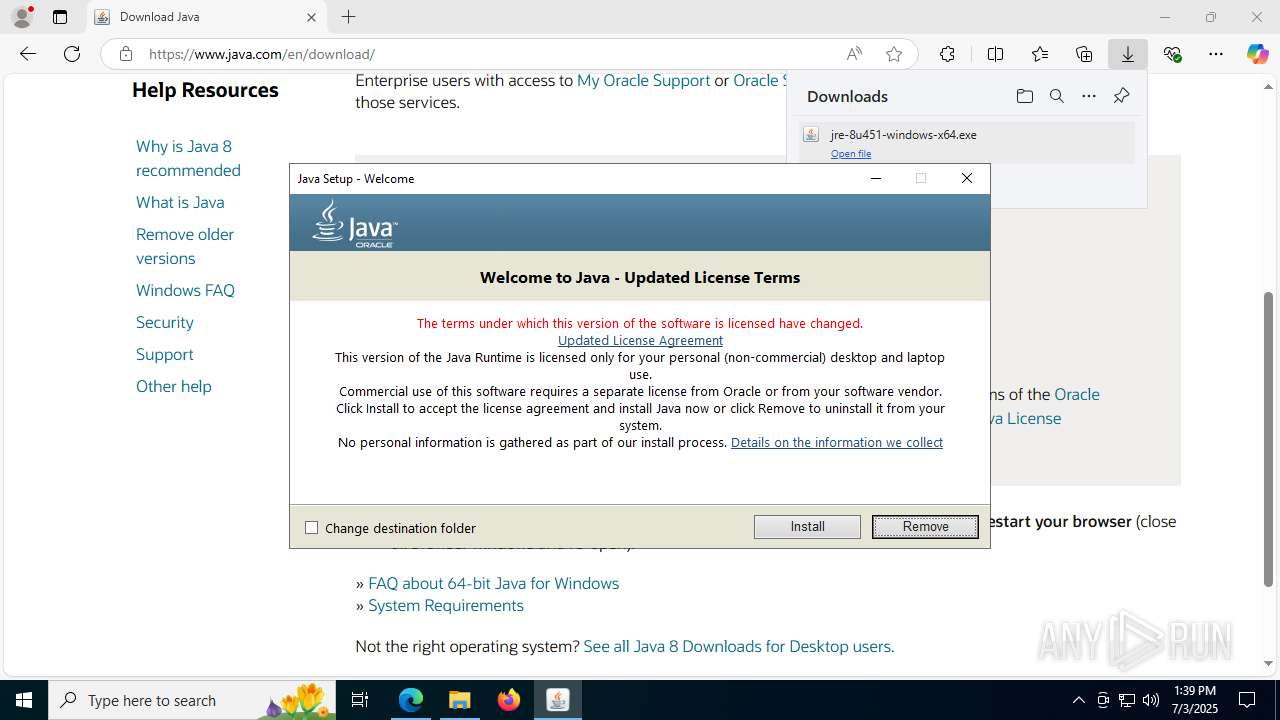
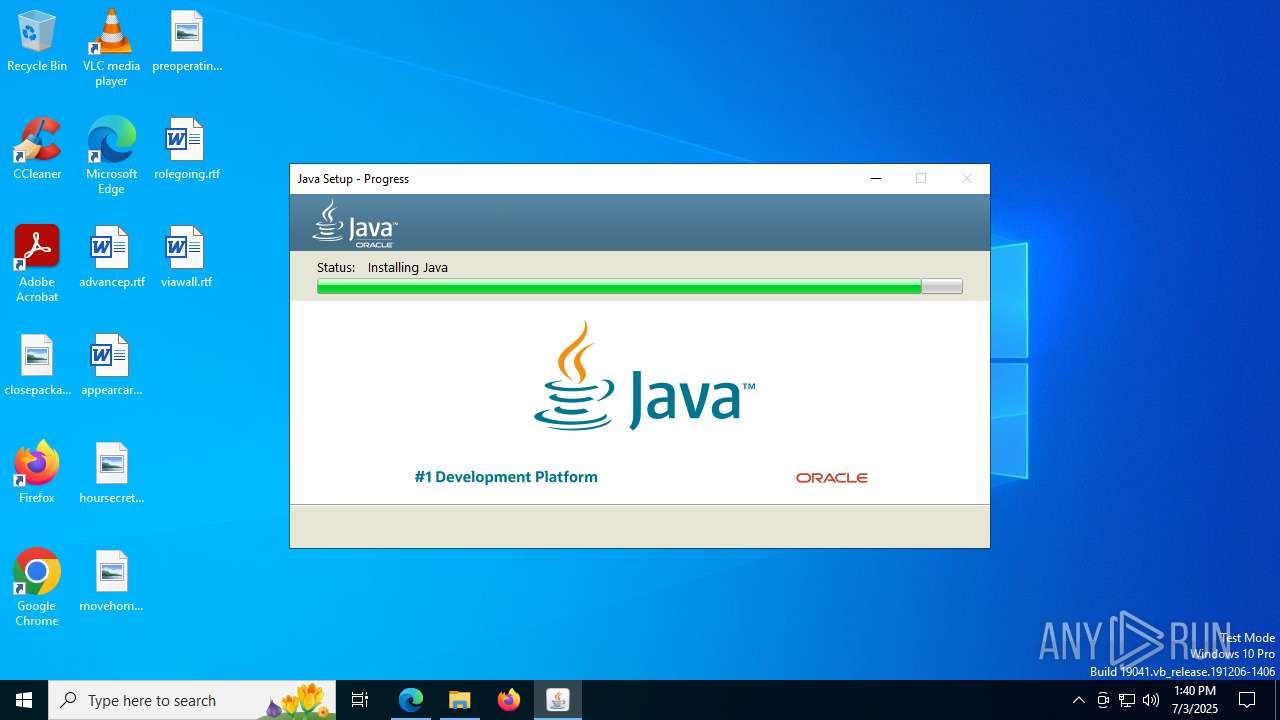
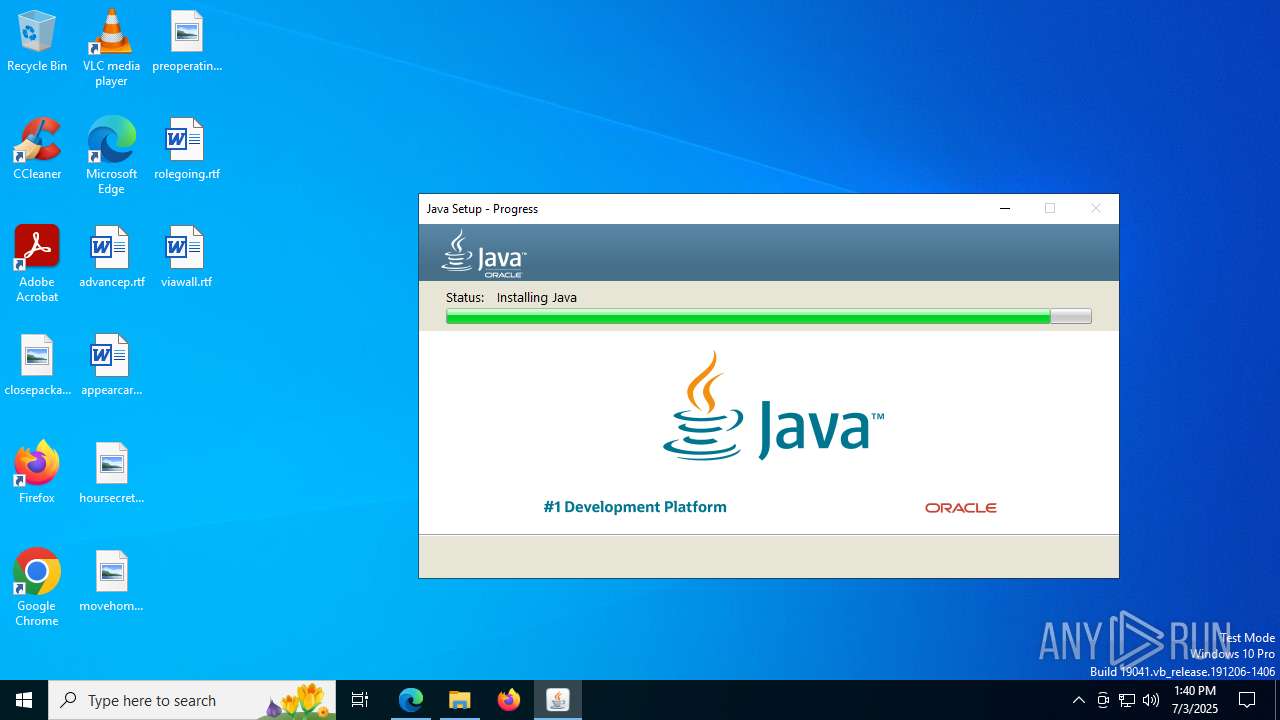
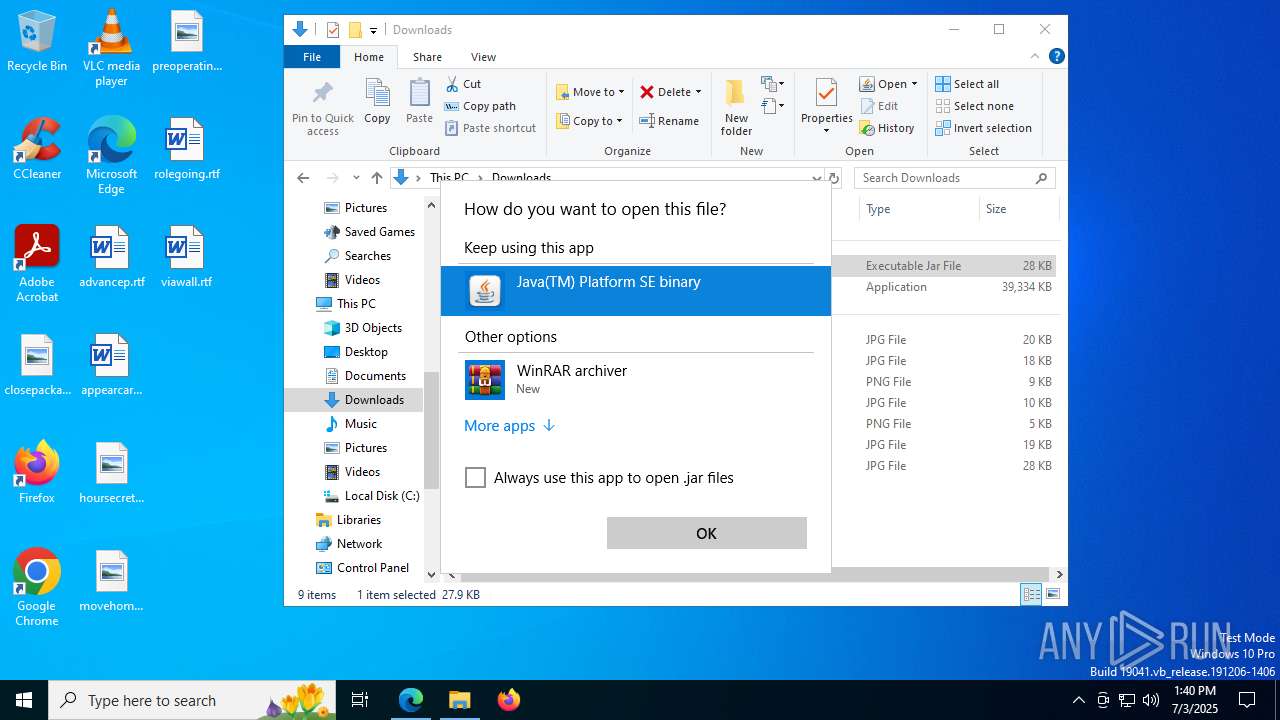
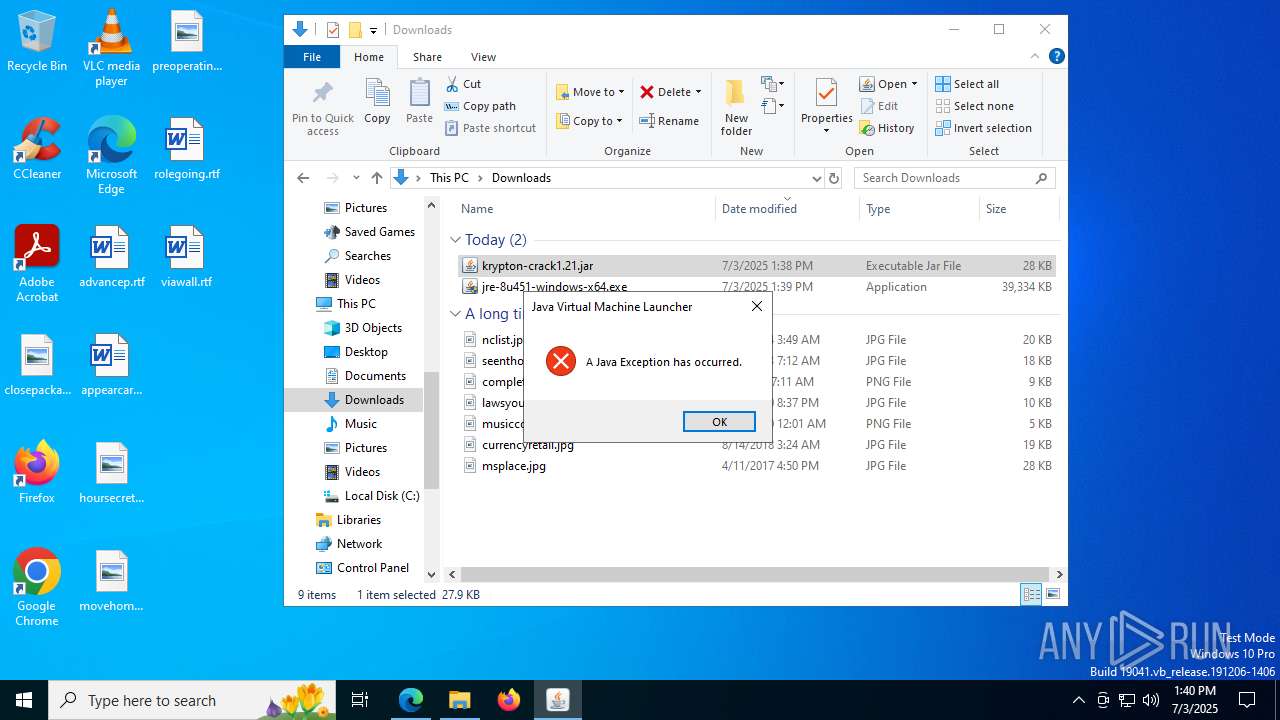
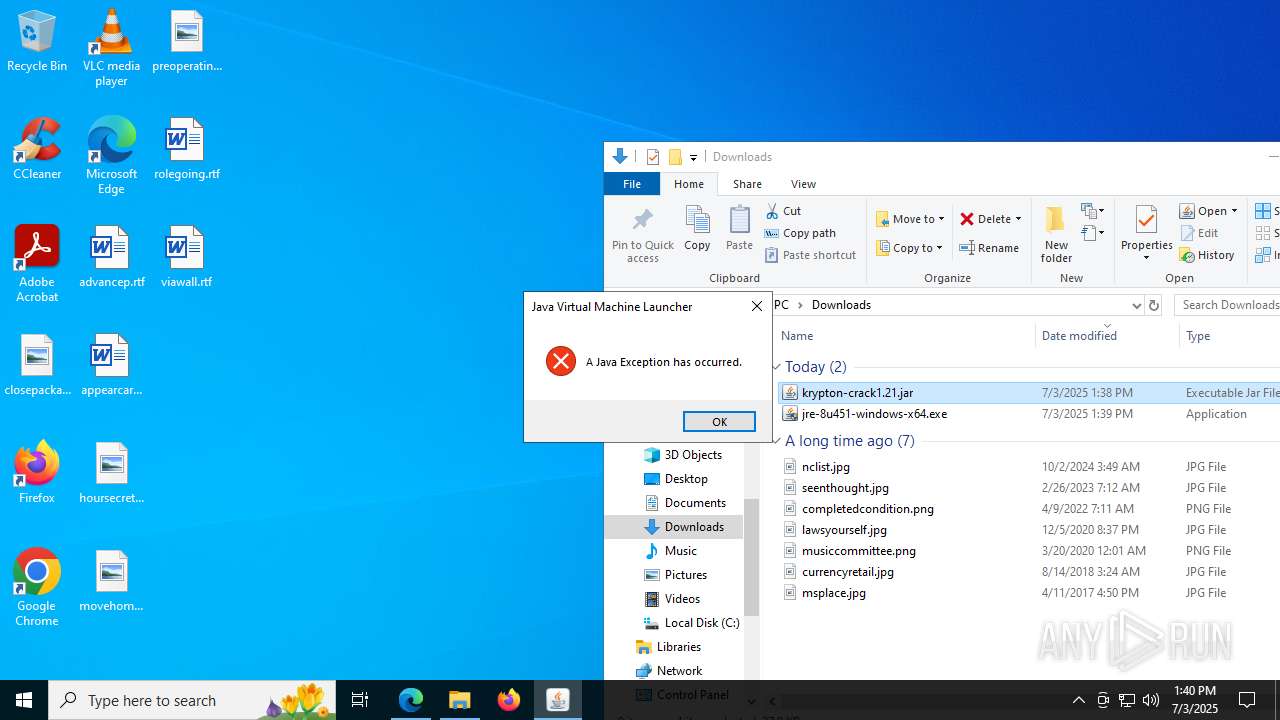
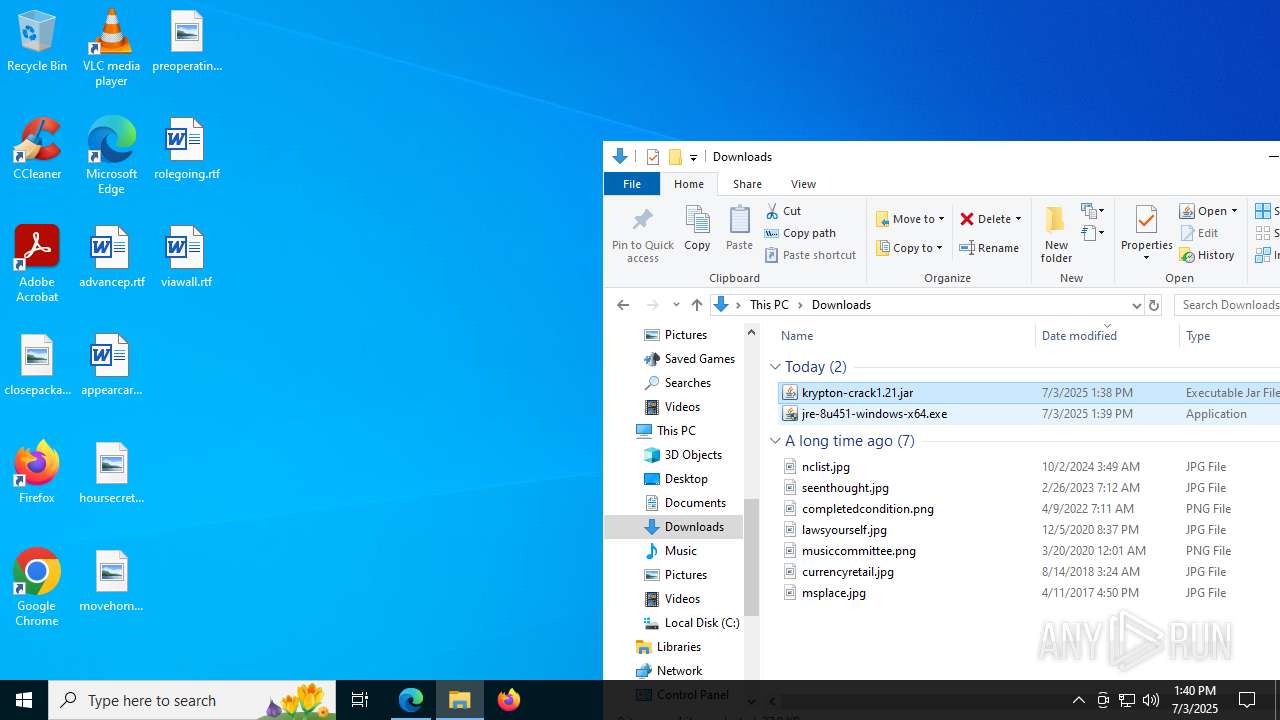
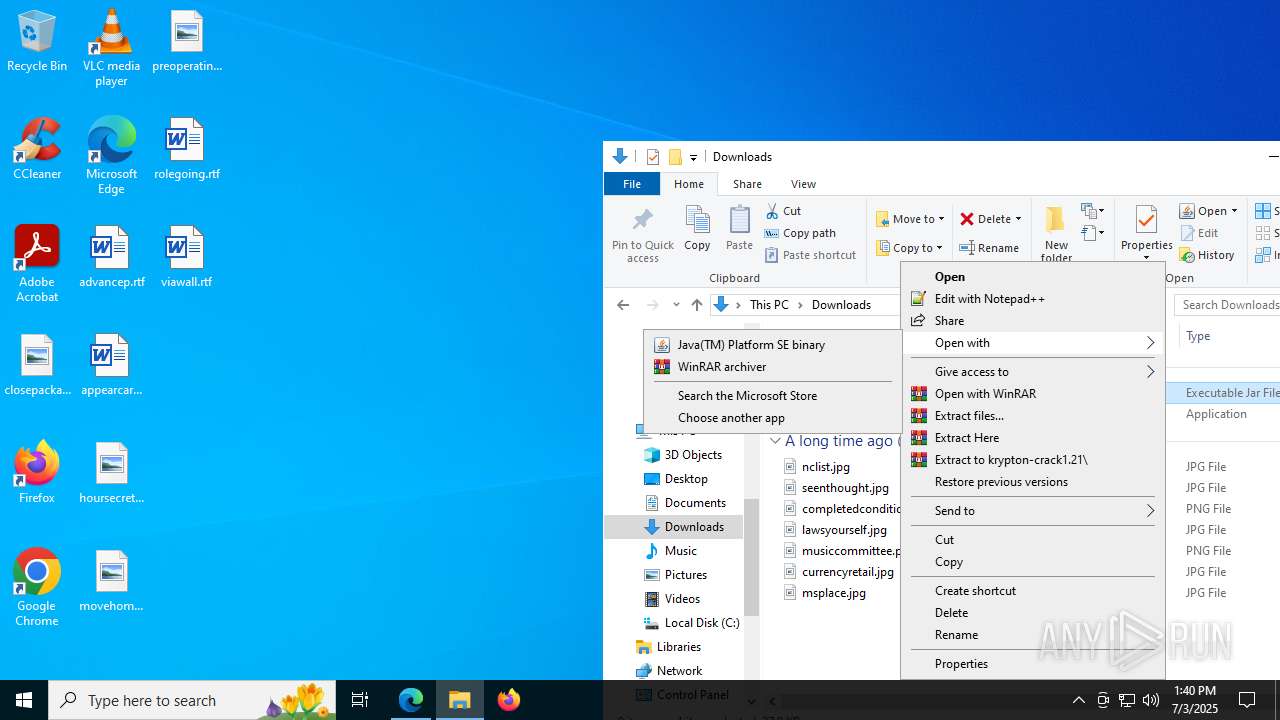
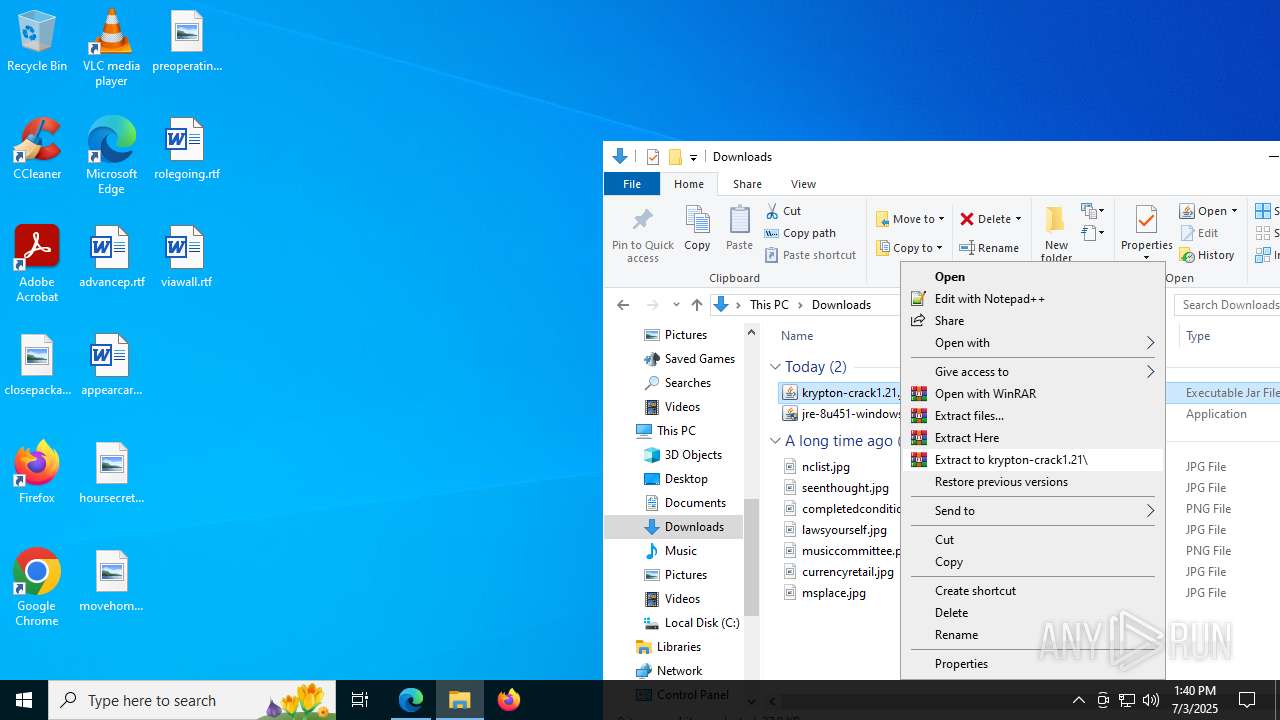
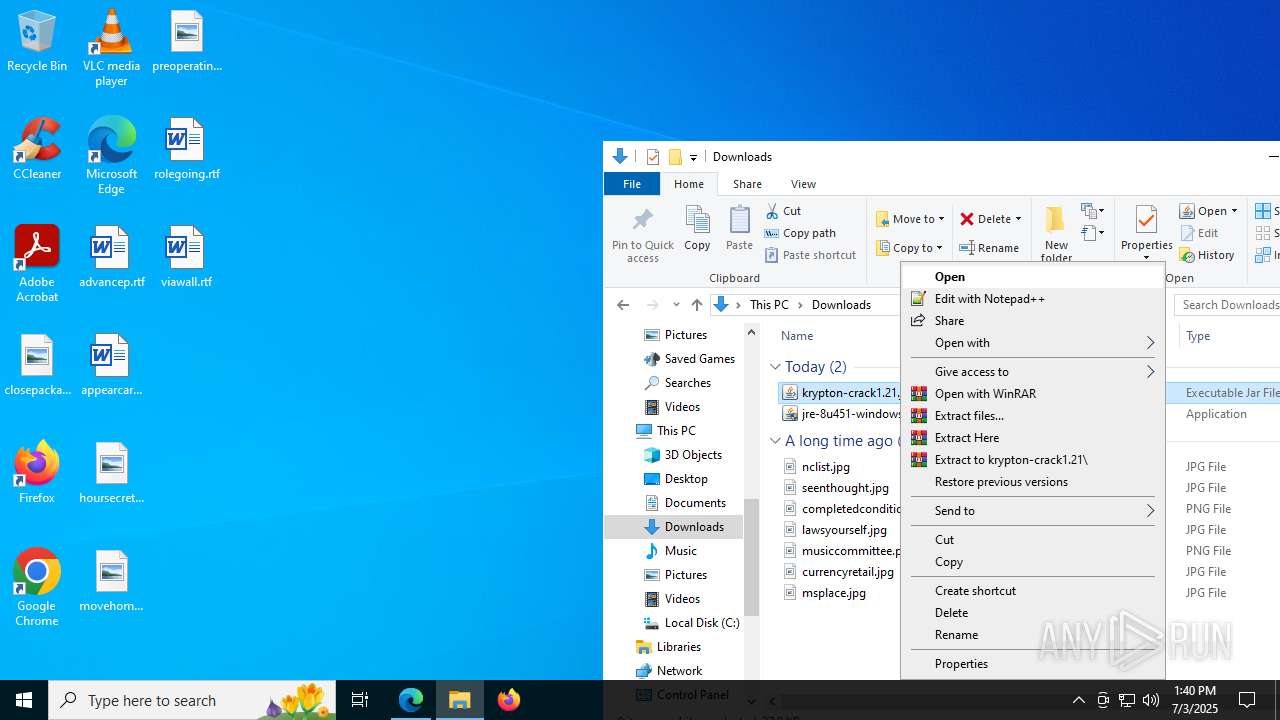
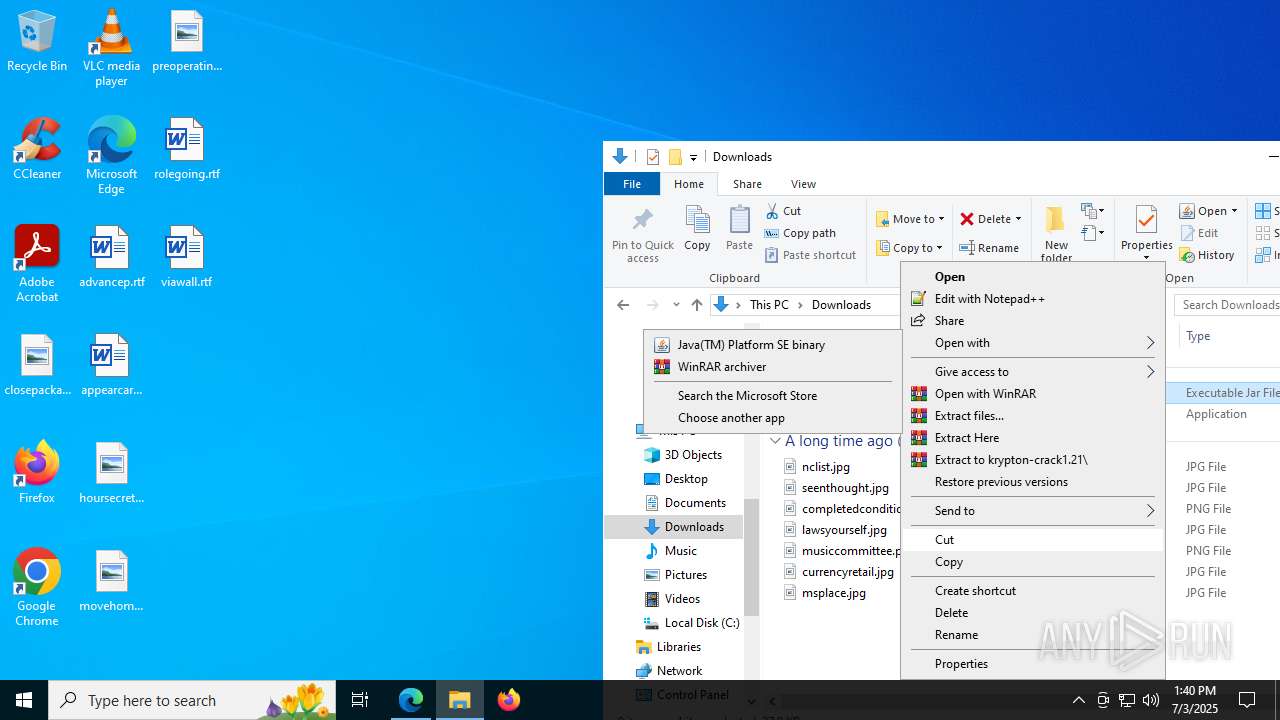
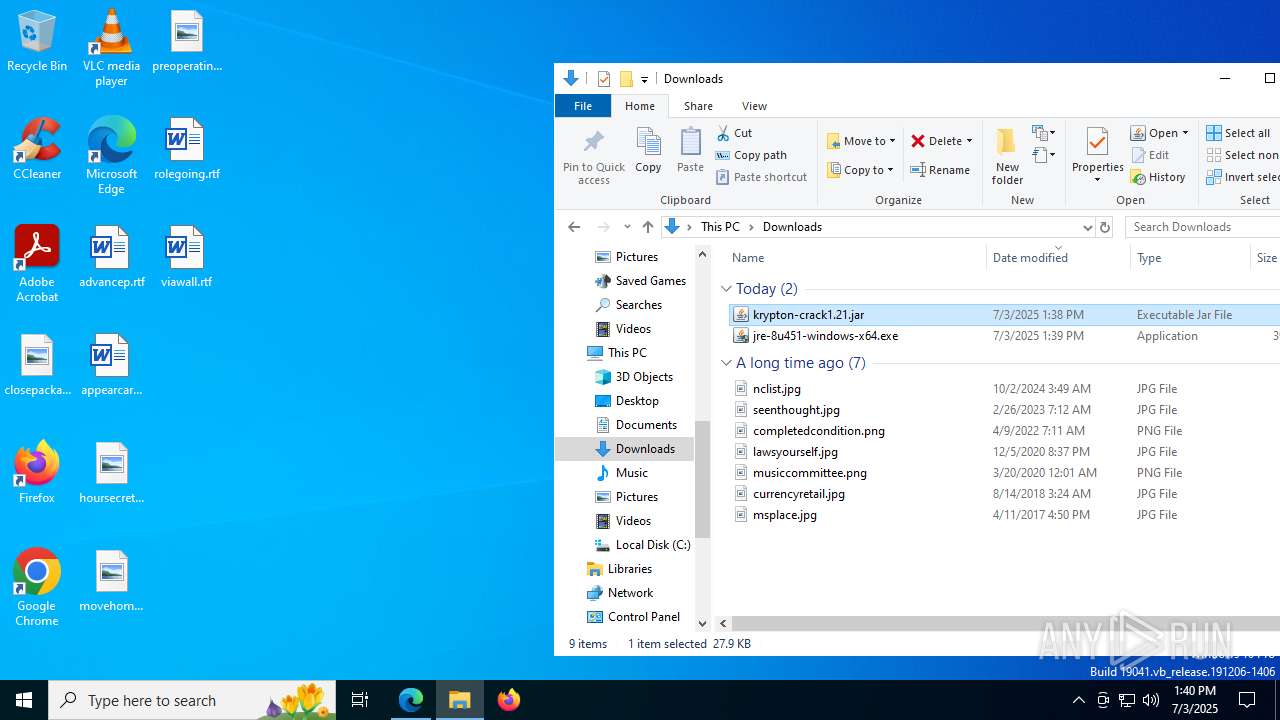
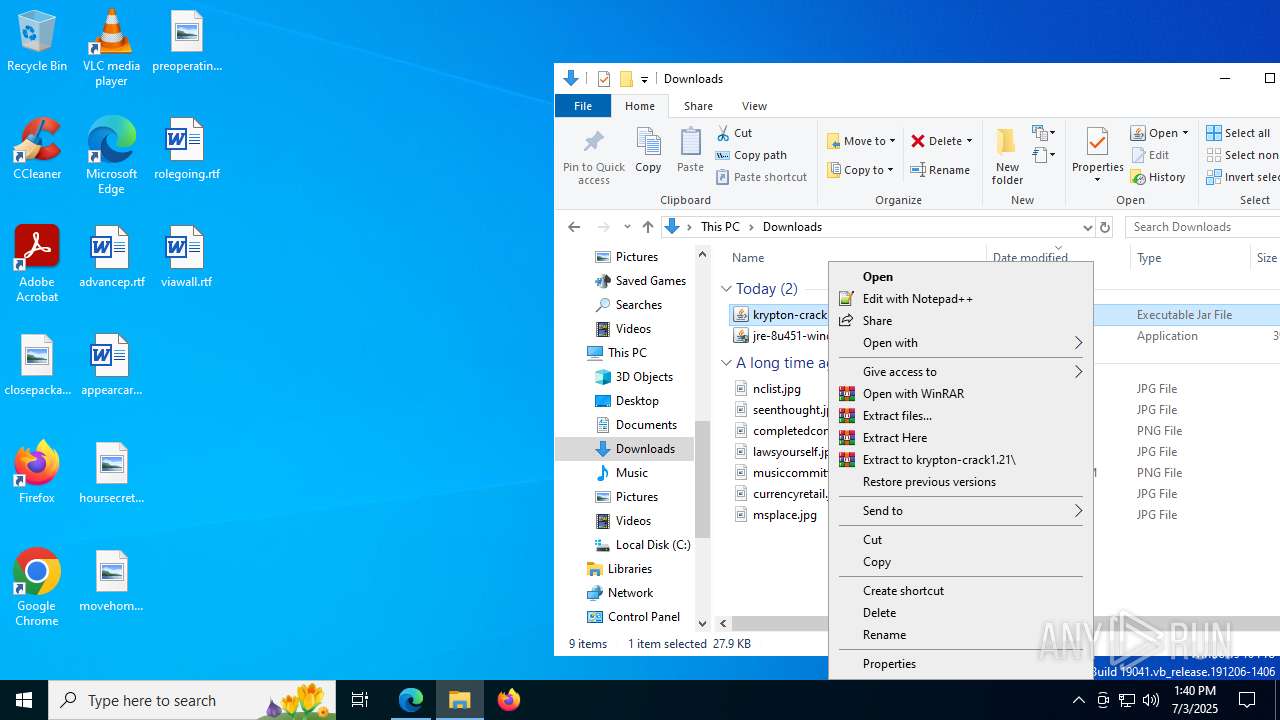
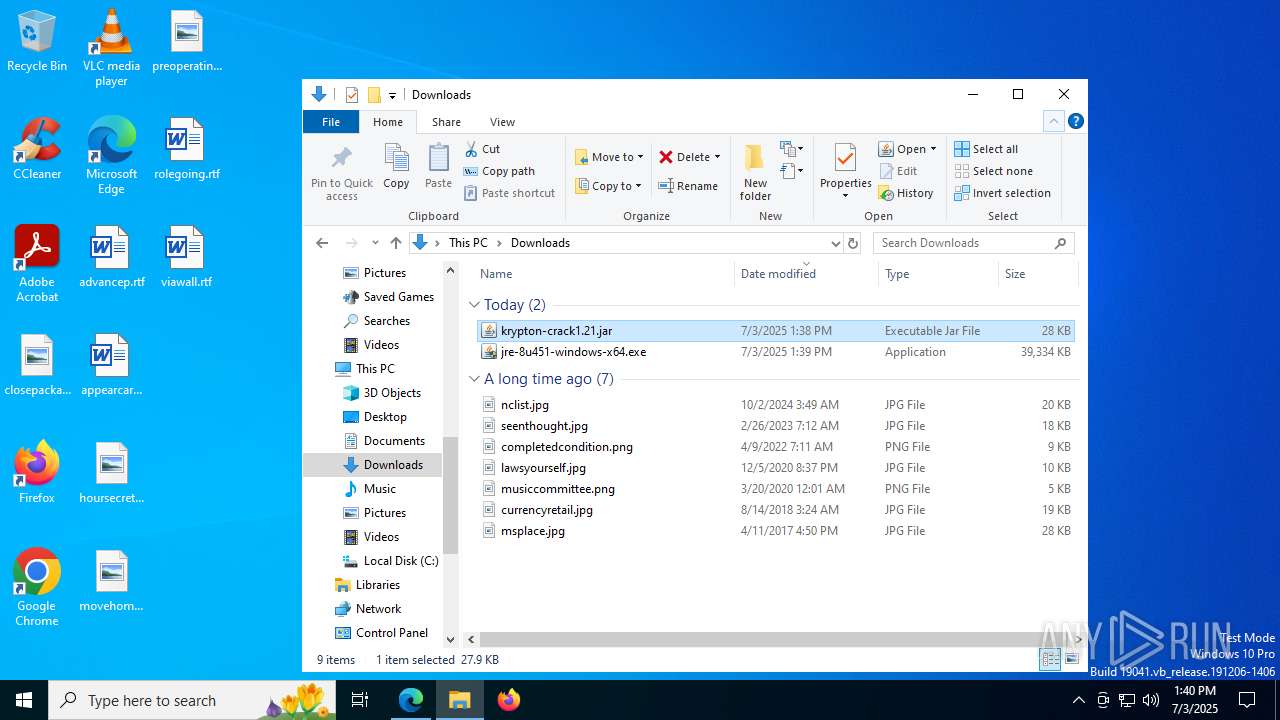
Checks for Java to be installed
- jre-8u451-windows-x64.exe (PID: 3108)
- msiexec.exe (PID: 4836)
- msiexec.exe (PID: 7840)
- installer.exe (PID: 7188)
- ssvagent.exe (PID: 8188)
- jp2launcher.exe (PID: 1948)
- jp2launcher.exe (PID: 1136)
- msiexec.exe (PID: 7828)
- javaw.exe (PID: 7724)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7840)
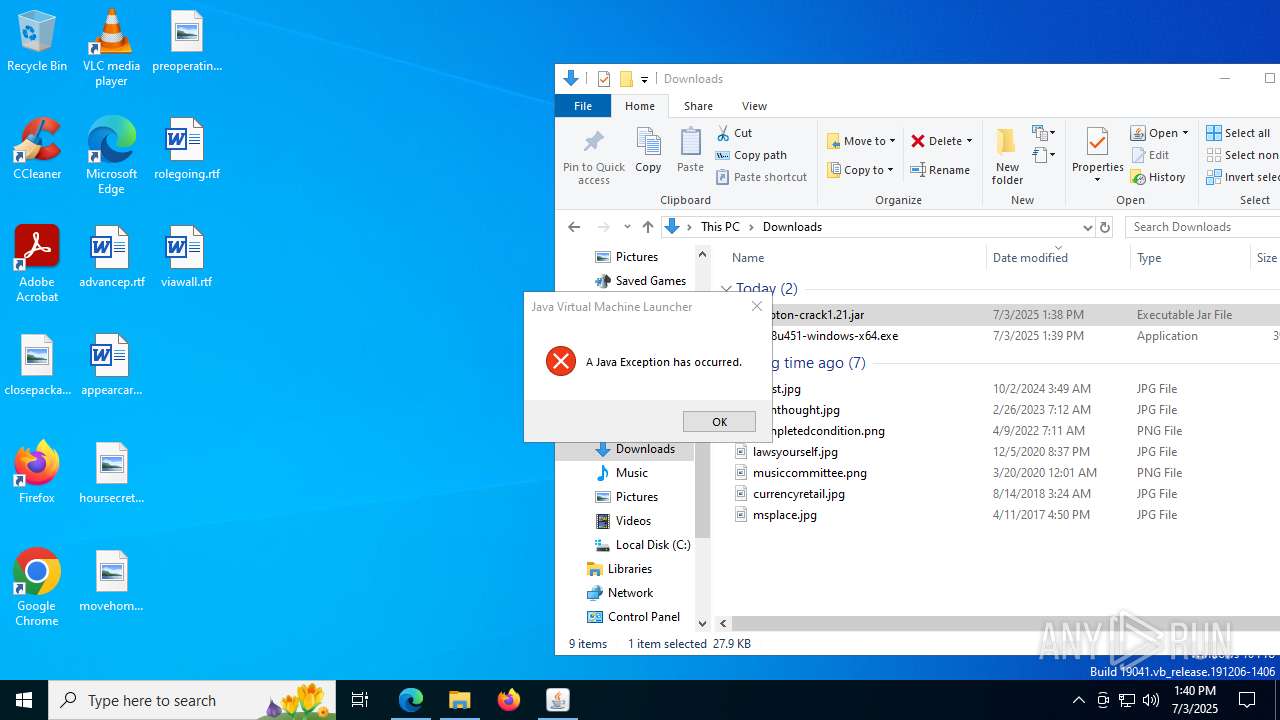
Application launched itself
- msiexec.exe (PID: 7840)
Reads Microsoft Outlook installation path
- jre-8u451-windows-x64.exe (PID: 3108)
Reads security settings of Internet Explorer
- jre-8u451-windows-x64.exe (PID: 3108)
- installer.exe (PID: 7188)
- jp2launcher.exe (PID: 1948)
- jp2launcher.exe (PID: 1136)
Reads Internet Explorer settings
- jre-8u451-windows-x64.exe (PID: 3108)
The process drops C-runtime libraries
- msiexec.exe (PID: 7840)
Process drops legitimate windows executable
- msiexec.exe (PID: 7840)
There is functionality for taking screenshot (YARA)
- jre-8u451-windows-x64.exe (PID: 3108)
Executable content was dropped or overwritten
- installer.exe (PID: 7188)
- jre-8u451-windows-x64.exe (PID: 3108)
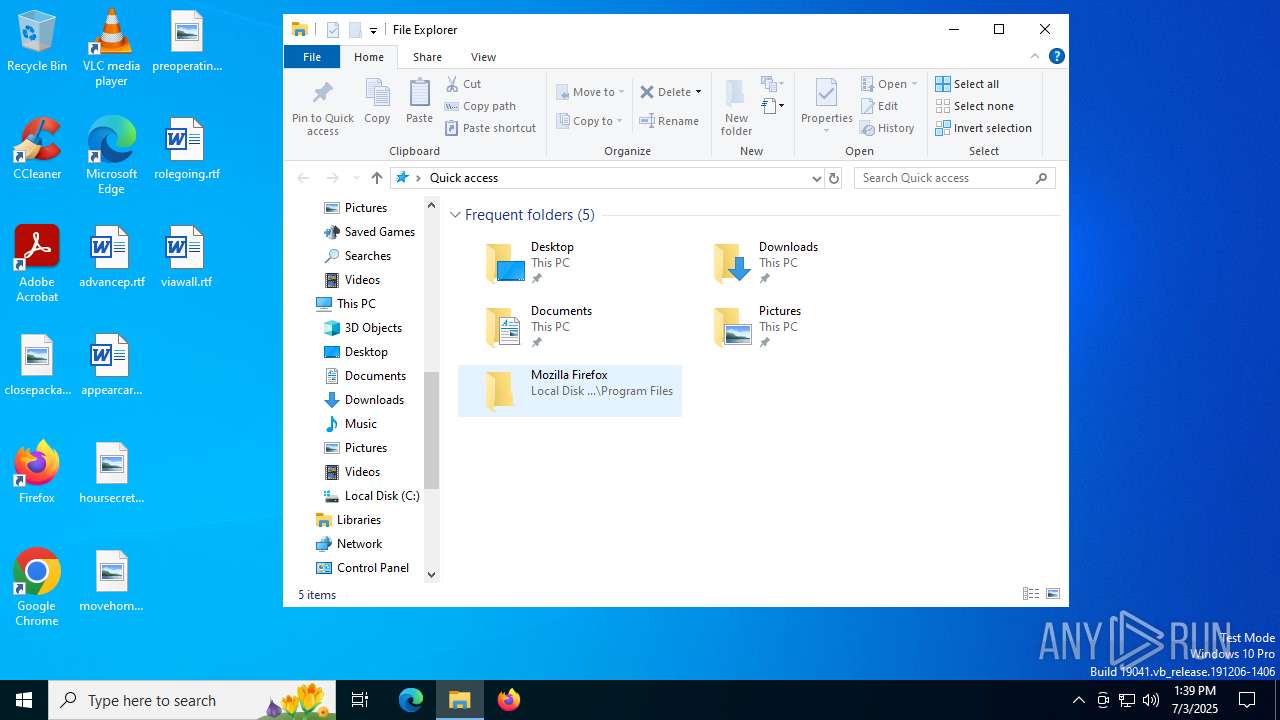
Reads Mozilla Firefox installation path
- MSI50B8.tmp (PID: 7724)
- installer.exe (PID: 7188)
Creates/Modifies COM task schedule object
- installer.exe (PID: 7188)
- ssvagent.exe (PID: 8188)
INFO
Checks supported languages
- javaw.exe (PID: 3540)
- identity_helper.exe (PID: 3476)
- jre-8u451-windows-x64.exe (PID: 3108)
- jre-8u451-windows-x64.exe (PID: 3780)
- jre-8u451-windows-x64.exe (PID: 6776)
- msiexec.exe (PID: 7840)
- msiexec.exe (PID: 4836)
- installer.exe (PID: 7188)
- javaw.exe (PID: 7456)
- MSI50B8.tmp (PID: 7724)
- jaureg.exe (PID: 7740)
- ssvagent.exe (PID: 8188)
- javaws.exe (PID: 6236)
- jp2launcher.exe (PID: 1948)
- jp2launcher.exe (PID: 1136)
- javaws.exe (PID: 6428)
- msiexec.exe (PID: 7828)
- msiexec.exe (PID: 8140)
- javaw.exe (PID: 7724)
- javaw.exe (PID: 2076)
- msiexec.exe (PID: 7852)
- msiexec.exe (PID: 6236)
- javaw.exe (PID: 3740)
- javaw.exe (PID: 4500)
- javaw.exe (PID: 7712)
- javaw.exe (PID: 3112)
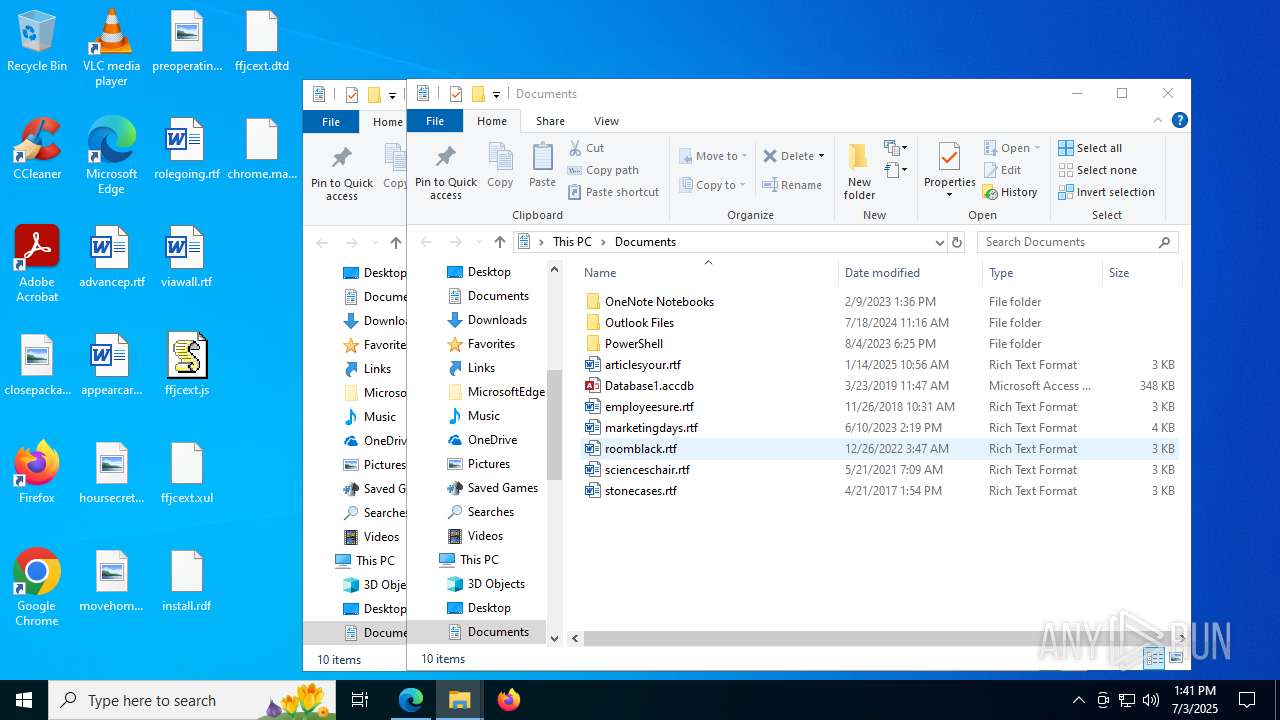
Creates files in the program directory
- javaw.exe (PID: 3540)
- installer.exe (PID: 7188)
- javaw.exe (PID: 7456)
- javaw.exe (PID: 4500)
Application based on Java
- javaw.exe (PID: 3540)
- javaw.exe (PID: 4500)
- javaw.exe (PID: 7712)
- javaw.exe (PID: 3112)
Create files in a temporary directory
- javaw.exe (PID: 3540)
- jre-8u451-windows-x64.exe (PID: 6776)
- jre-8u451-windows-x64.exe (PID: 3780)
- MSI50B8.tmp (PID: 7724)
- javaw.exe (PID: 7456)
- jp2launcher.exe (PID: 1948)
- jp2launcher.exe (PID: 1136)
- javaw.exe (PID: 7724)
- javaw.exe (PID: 3740)
- javaw.exe (PID: 2076)
- javaw.exe (PID: 4500)
- javaw.exe (PID: 7712)
- javaw.exe (PID: 3112)
Reads the computer name
- javaw.exe (PID: 3540)
- identity_helper.exe (PID: 3476)
- jre-8u451-windows-x64.exe (PID: 3108)
- jre-8u451-windows-x64.exe (PID: 6776)
- jre-8u451-windows-x64.exe (PID: 3780)
- msiexec.exe (PID: 4836)
- msiexec.exe (PID: 7840)
- MSI50B8.tmp (PID: 7724)
- installer.exe (PID: 7188)
- jp2launcher.exe (PID: 1948)
- javaws.exe (PID: 6428)
- jp2launcher.exe (PID: 1136)
- javaws.exe (PID: 6236)
- javaw.exe (PID: 7724)
- msiexec.exe (PID: 7828)
- msiexec.exe (PID: 8140)
- msiexec.exe (PID: 7852)
- msiexec.exe (PID: 6236)
- javaw.exe (PID: 3740)
- javaw.exe (PID: 2076)
- javaw.exe (PID: 4500)
- javaw.exe (PID: 7712)
- javaw.exe (PID: 3112)
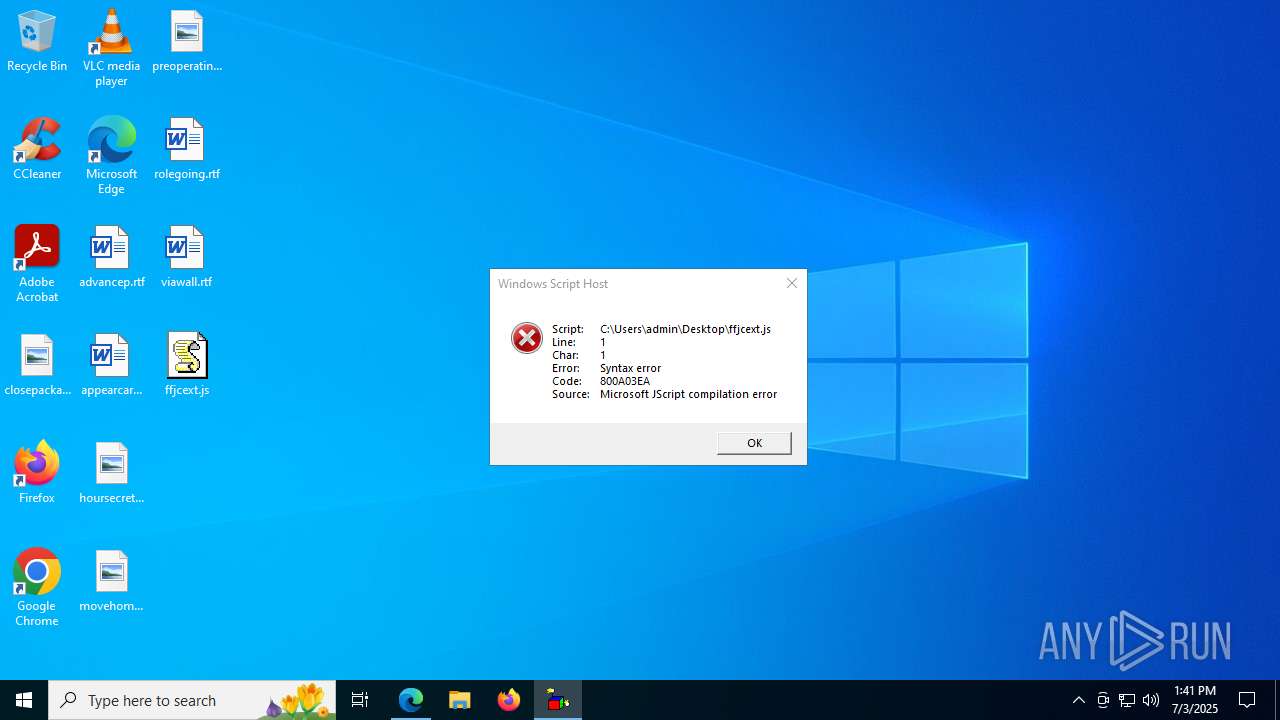
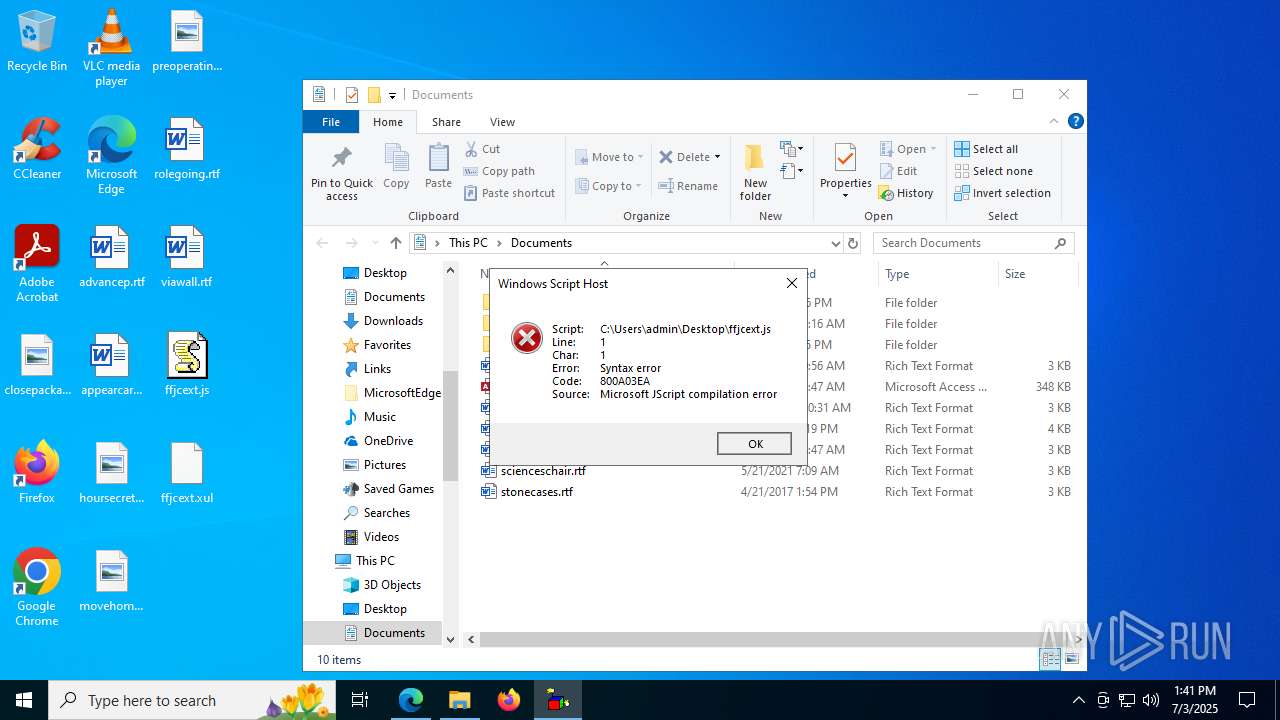
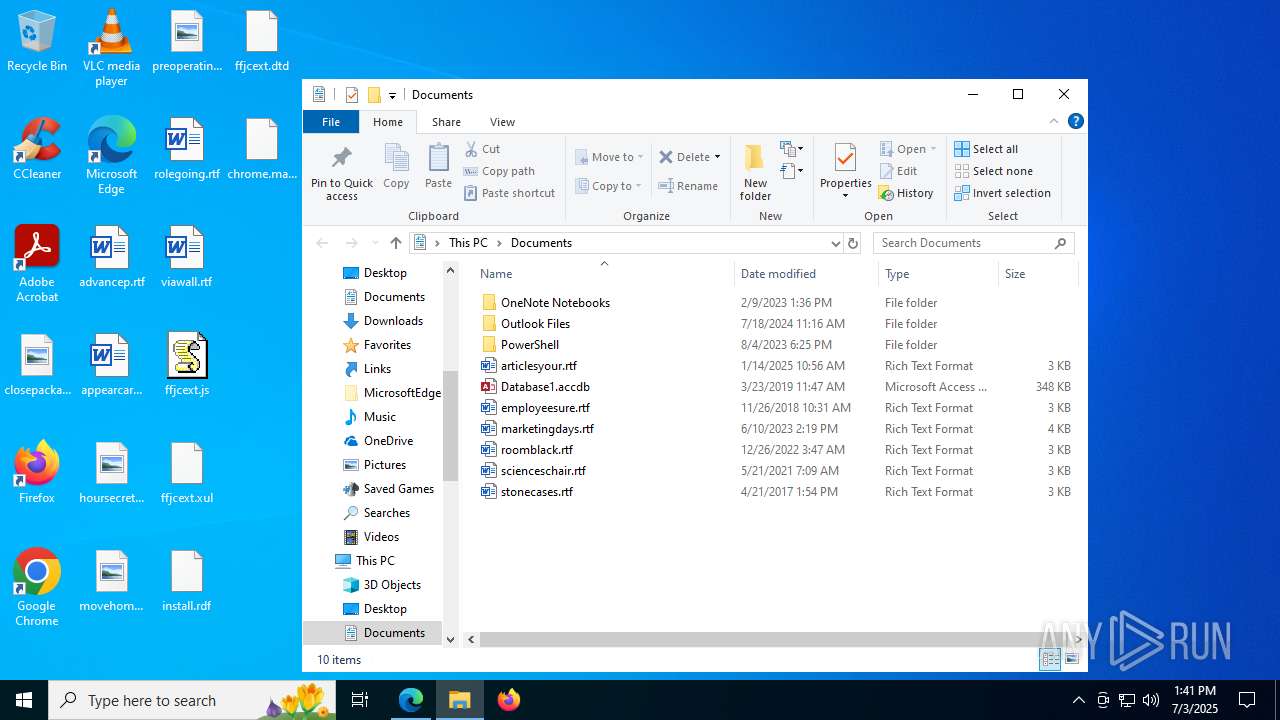
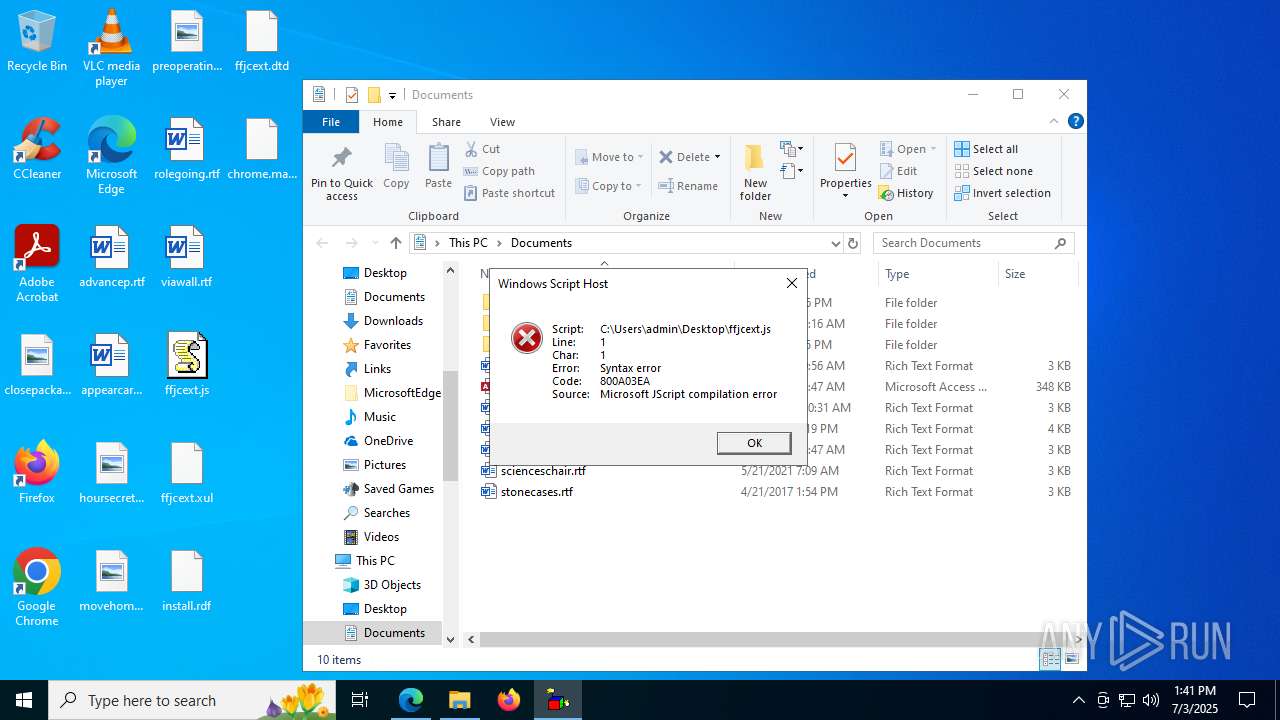
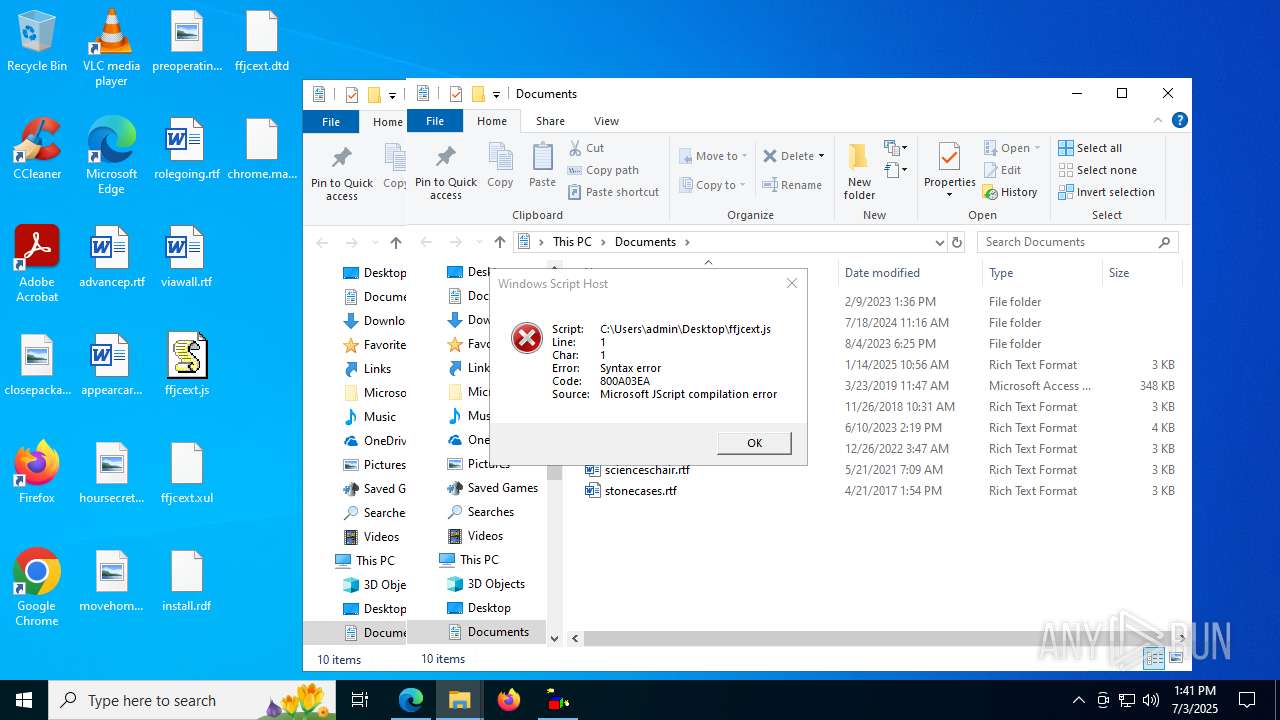
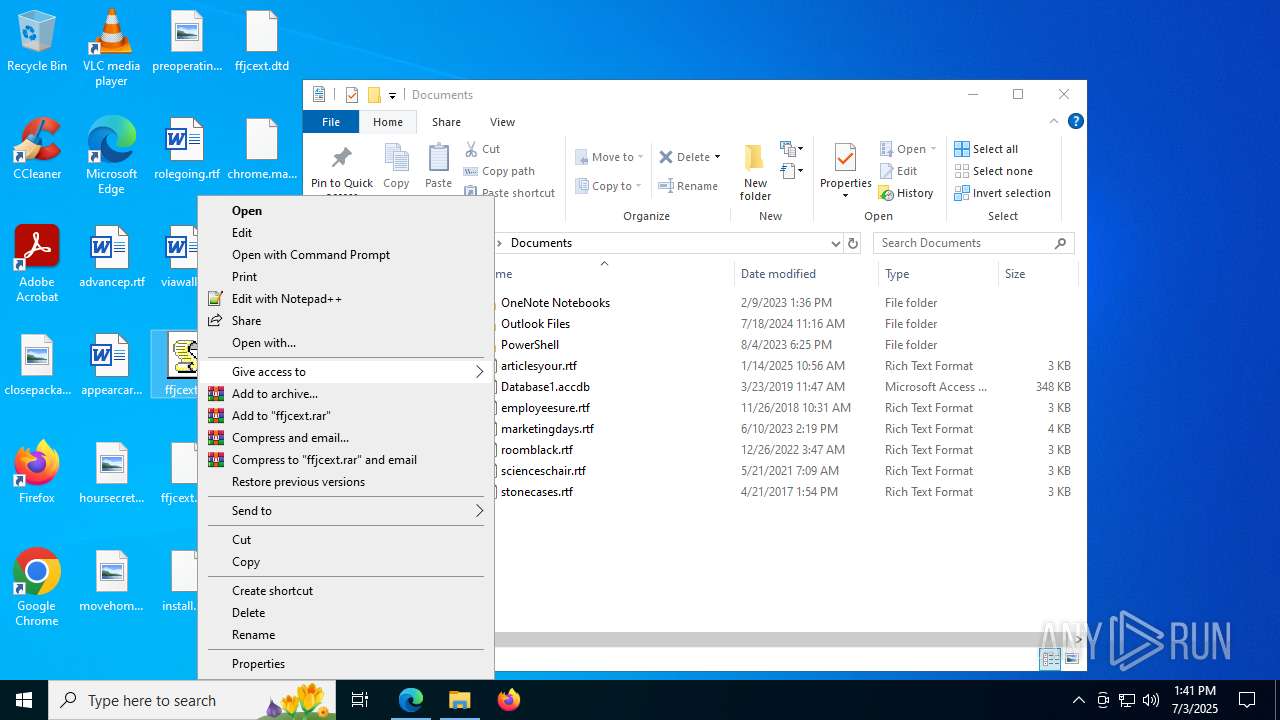
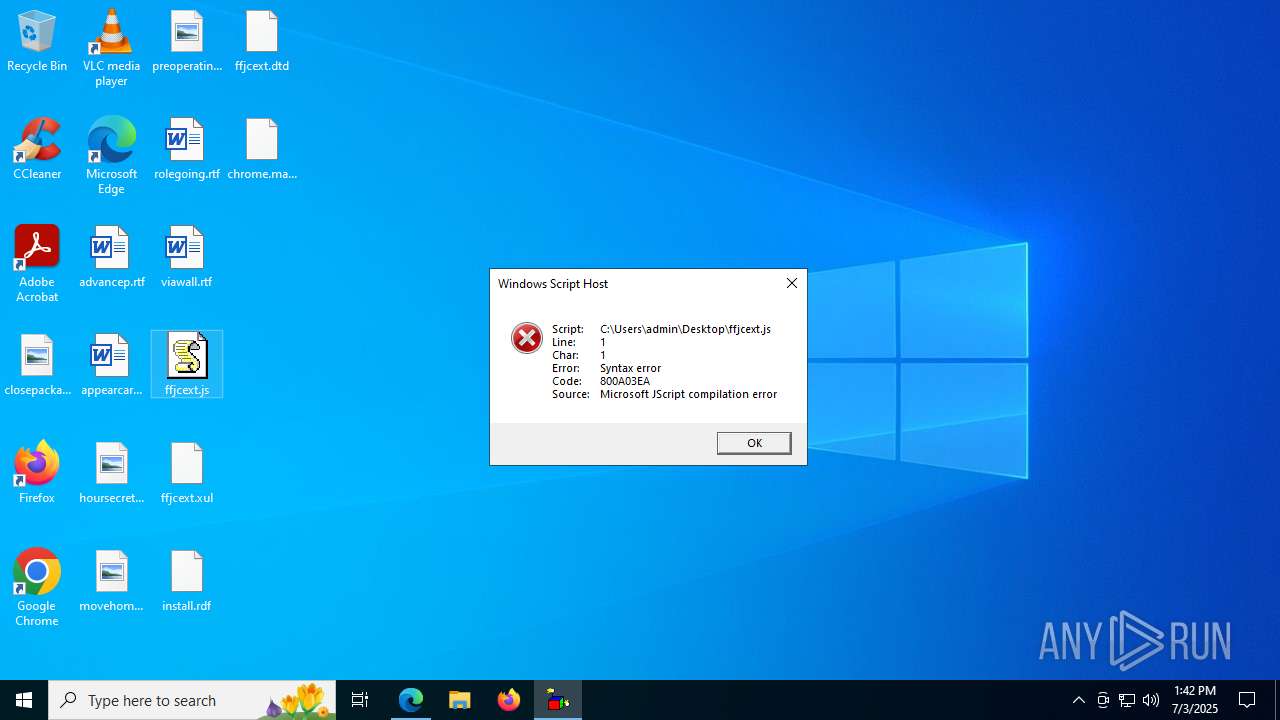
Manual execution by a user
- msedge.exe (PID: 6720)
- javaw.exe (PID: 7712)
- javaw.exe (PID: 3112)
- wscript.exe (PID: 3688)
- wscript.exe (PID: 3936)
- wscript.exe (PID: 4500)
Reads Environment values
- identity_helper.exe (PID: 3476)
- jre-8u451-windows-x64.exe (PID: 3108)
Application launched itself
- msedge.exe (PID: 6720)
Java executable
- jre-8u451-windows-x64.exe (PID: 4752)
- jre-8u451-windows-x64.exe (PID: 7188)
- jre-8u451-windows-x64.exe (PID: 3780)
- jre-8u451-windows-x64.exe (PID: 3108)
- jre-8u451-windows-x64.exe (PID: 6776)
- MSI50B8.tmp (PID: 7724)
- installer.exe (PID: 7188)
Executable content was dropped or overwritten
- msedge.exe (PID: 6720)
- msiexec.exe (PID: 7840)
Reads the software policy settings
- jre-8u451-windows-x64.exe (PID: 3108)
- msiexec.exe (PID: 7840)
- slui.exe (PID: 8032)
Reads the machine GUID from the registry
- jre-8u451-windows-x64.exe (PID: 3108)
- msiexec.exe (PID: 7840)
Creates files or folders in the user directory
- jre-8u451-windows-x64.exe (PID: 3108)
- msiexec.exe (PID: 7840)
Checks proxy server information
- jre-8u451-windows-x64.exe (PID: 3108)
- jp2launcher.exe (PID: 1948)
- jp2launcher.exe (PID: 1136)
- slui.exe (PID: 8032)
Starts application with an unusual extension
- msiexec.exe (PID: 7840)
The sample compiled with english language support
- msiexec.exe (PID: 7840)
- installer.exe (PID: 7188)
- jre-8u451-windows-x64.exe (PID: 3108)
Reads CPU info
- msiexec.exe (PID: 7840)
Creates a software uninstall entry
- msiexec.exe (PID: 7840)
JAVA mutex has been found
- jp2launcher.exe (PID: 1948)
- jp2launcher.exe (PID: 1136)
- msiexec.exe (PID: 8140)
- msiexec.exe (PID: 6236)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 7212)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 7212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jar | | | Java Archive (78.3) |
|---|---|---|
| .zip | | | ZIP compressed archive (21.6) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:07:01 21:25:06 |
| ZipCRC: | 0xed598c16 |
| ZipCompressedSize: | 6116 |
| ZipUncompressedSize: | 13115 |
| ZipFileName: | MaxCoffe/MaxCoffeClient.class |
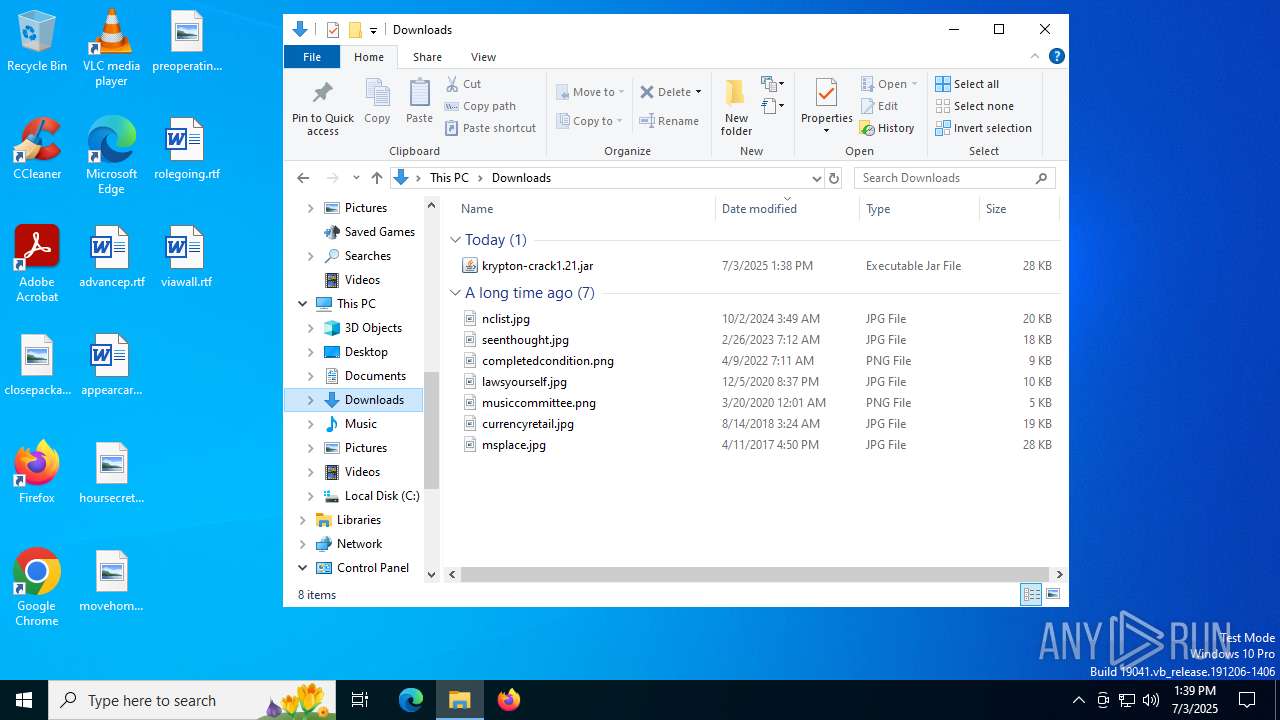
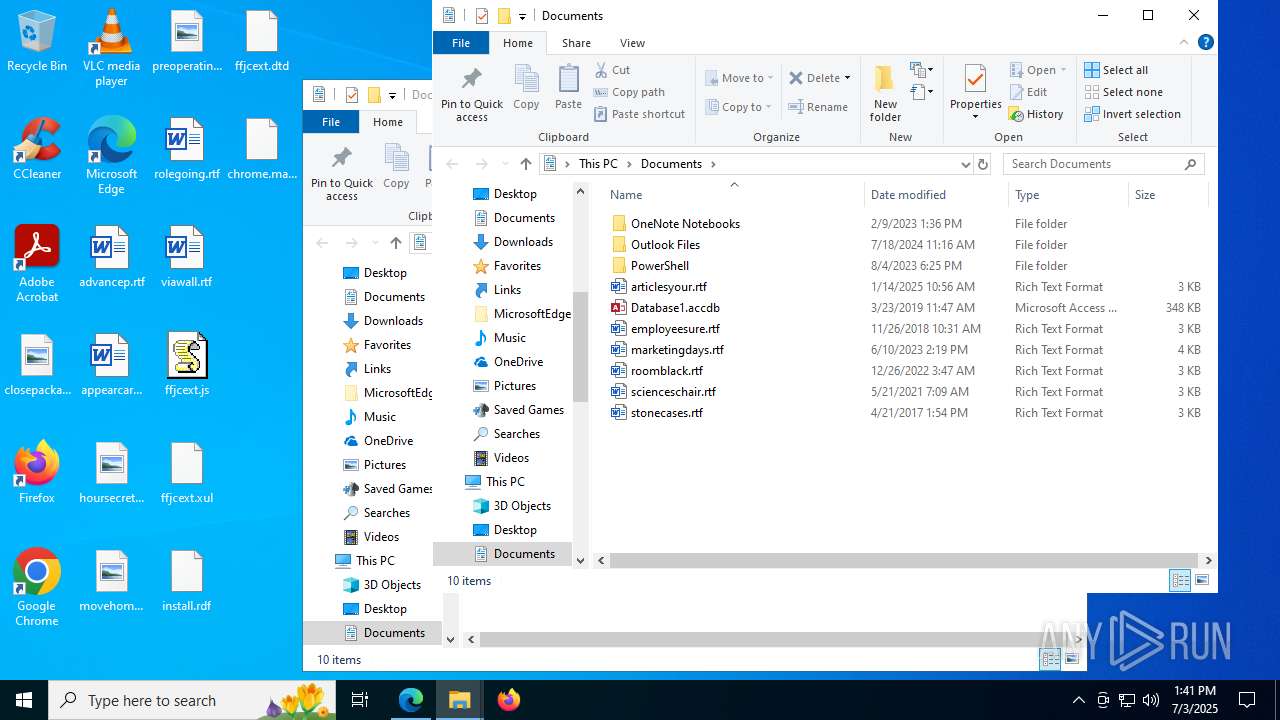
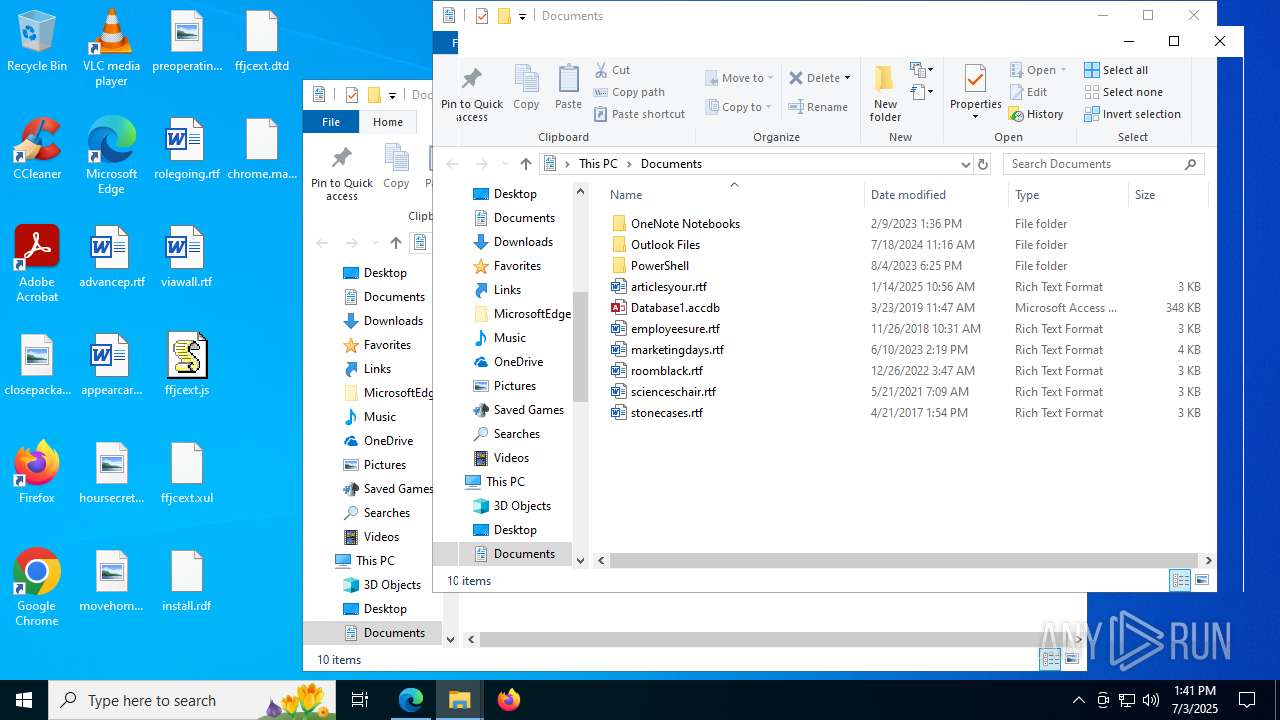
Total processes
218
Monitored processes
76
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5380,i,9470299062496478171,1620679322823639108,262144 --variations-seed-version --mojo-platform-channel-handle=7296 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7584,i,9470299062496478171,1620679322823639108,262144 --variations-seed-version --mojo-platform-channel-handle=5812 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2540,i,9470299062496478171,1620679322823639108,262144 --variations-seed-version --mojo-platform-channel-handle=2468 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1136 | "C:\Program Files\Java\jre1.8.0_451\bin\jp2launcher.exe" -secure -javaws -jre "C:\Program Files\Java\jre1.8.0_451" -vma LWNsYXNzcGF0aABDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDUxXGxpYlxkZXBsb3kuamFyAC1EamF2YS5zZWN1cml0eS5wb2xpY3k9ZmlsZTpDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDUxXGxpYlxzZWN1cml0eVxqYXZhd3MucG9saWN5AC1EdHJ1c3RQcm94eT10cnVlAC1YdmVyaWZ5OnJlbW90ZQAtRGpubHB4LmhvbWU9QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzQ1MVxiaW4ALURqYXZhLnNlY3VyaXR5Lm1hbmFnZXIALURzdW4uYXd0Lndhcm11cD10cnVlAC1YYm9vdGNsYXNzcGF0aC9hOkM6XFByb2dyYW0gRmlsZXNcSmF2YVxqcmUxLjguMF80NTFcbGliXGphdmF3cy5qYXI7QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzQ1MVxsaWJcZGVwbG95LmphcjtDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDUxXGxpYlxwbHVnaW4uamFyAC1EamF2YS5hd3QuaGVhZGxlc3M9dHJ1ZQAtRGpubHB4Lmp2bT1DOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDUxXGJpblxqYXZhdy5leGU= -ma LXdhaXQALWZpeAAtc2hvcnRjdXQALXNpbGVudAAtbm90V2ViSmF2YQ== | C:\Program Files\Java\jre1.8.0_451\bin\jp2launcher.exe | — | javaws.exe | |||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Web Launcher Exit code: 0 Version: 11.451.0.10 Modules
| |||||||||||||||
| 1740 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5716,i,9470299062496478171,1620679322823639108,262144 --variations-seed-version --mojo-platform-channel-handle=5500 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1828 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2244,i,9470299062496478171,1620679322823639108,262144 --variations-seed-version --mojo-platform-channel-handle=2596 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Java\jre1.8.0_451\bin\jp2launcher.exe" -secure -javaws -jre "C:\Program Files\Java\jre1.8.0_451" -vma LWNsYXNzcGF0aABDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDUxXGxpYlxkZXBsb3kuamFyAC1EamF2YS5zZWN1cml0eS5wb2xpY3k9ZmlsZTpDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDUxXGxpYlxzZWN1cml0eVxqYXZhd3MucG9saWN5AC1EdHJ1c3RQcm94eT10cnVlAC1YdmVyaWZ5OnJlbW90ZQAtRGpubHB4LmhvbWU9QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzQ1MVxiaW4ALURqYXZhLnNlY3VyaXR5Lm1hbmFnZXIALURzdW4uYXd0Lndhcm11cD10cnVlAC1YYm9vdGNsYXNzcGF0aC9hOkM6XFByb2dyYW0gRmlsZXNcSmF2YVxqcmUxLjguMF80NTFcbGliXGphdmF3cy5qYXI7QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzQ1MVxsaWJcZGVwbG95LmphcjtDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDUxXGxpYlxwbHVnaW4uamFyAC1EamF2YS5hd3QuaGVhZGxlc3M9dHJ1ZQAtRGpubHB4Lmp2bT1DOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDUxXGJpblxqYXZhdy5leGU= -ma LXdhaXQALWZpeAAtcGVybWlzc2lvbnMALXNpbGVudAAtbm90V2ViSmF2YQ== | C:\Program Files\Java\jre1.8.0_451\bin\jp2launcher.exe | — | javaws.exe | |||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Web Launcher Exit code: 0 Version: 11.451.0.10 Modules
| |||||||||||||||
| 2076 | -Djdk.disableLastUsageTracking -cp "C:\Program Files\Java\jre1.8.0_451\bin\..\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -systemConfig deployment.expiration.check.enabled false | C:\Program Files\Java\jre1.8.0_451\bin\javaw.exe | — | jre-8u451-windows-x64.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.4510.10 Modules
| |||||||||||||||
| 2124 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2260,i,9470299062496478171,1620679322823639108,262144 --variations-seed-version --mojo-platform-channel-handle=4952 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2160 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x30c,0x310,0x314,0x304,0x31c,0x7ffc4517f208,0x7ffc4517f214,0x7ffc4517f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
49 482
Read events
21 602
Write events
13 047
Delete events
14 833
Modification events
| (PID) Process: | (6720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6720) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 8E7741C99C972F00 | |||
| (PID) Process: | (6720) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A79847C99C972F00 | |||
| (PID) Process: | (6720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\131934 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {45E383A9-067B-444A-B9B0-D8DDA4BDB771} | |||
| (PID) Process: | (6720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\131934 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9603D6DE-C407-4FF2-9C24-1570A6AB0539} | |||
| (PID) Process: | (6720) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\131934 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E762503F-B75F-4017-8101-5F53CAE2B610} | |||
| (PID) Process: | (6720) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 573397C99C972F00 | |||
Executable files
346
Suspicious files
684
Text files
344
Unknown types
94
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF179068.TMP | — | |
MD5:— | SHA256:— | |||
| 6720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF179078.TMP | — | |
MD5:— | SHA256:— | |||
| 6720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF179078.TMP | — | |
MD5:— | SHA256:— | |||
| 6720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF179078.TMP | — | |
MD5:— | SHA256:— | |||
| 6720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF179078.TMP | — | |
MD5:— | SHA256:— | |||
| 6720 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
144
DNS requests
151
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.20.245.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1200 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1828 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:Kxix92Pyr9Kb8dbwutWPOPW18X9HtcMP8fpVJc1S1BA&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7324 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7324 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3108 | jre-8u451-windows-x64.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | — | — | whitelisted |
7840 | msiexec.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
7840 | msiexec.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
7840 | msiexec.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAqhj2P5bxF3HLsLQ%2BTWkLg%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
756 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 2.20.245.137:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1200 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1200 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
ntp.msn.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |