| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/6d0cc424-47a0-44f3-9d16-21335882ccb8 |
| Verdict: | Malicious activity |
| Analysis date: | April 28, 2024, 15:51:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AC6672E3DEF0922CDBCCA67F0CFB9B93 |
| SHA1: | 35BB1A3A39304F1982784B4DE6B1E2C00947237F |
| SHA256: | FD49A19D8D9895AACD3428F22452884E8B71B6A840710A9A195F2B31BE19918F |
| SSDEEP: | 98304:tYbEujRwrTo1kOfZXJnwC1GMy8zXncv/D0+JQlBEvEfXzsJneWXRhw/MR3+oBGbU:qwiq |
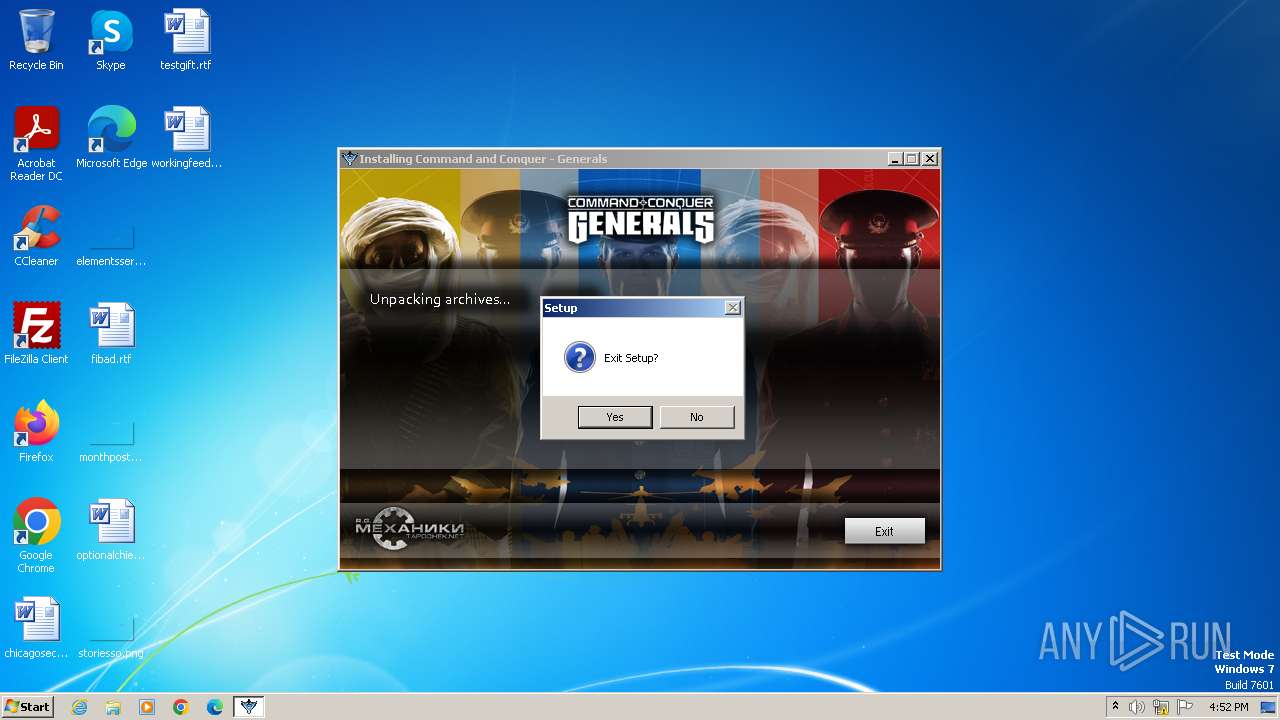
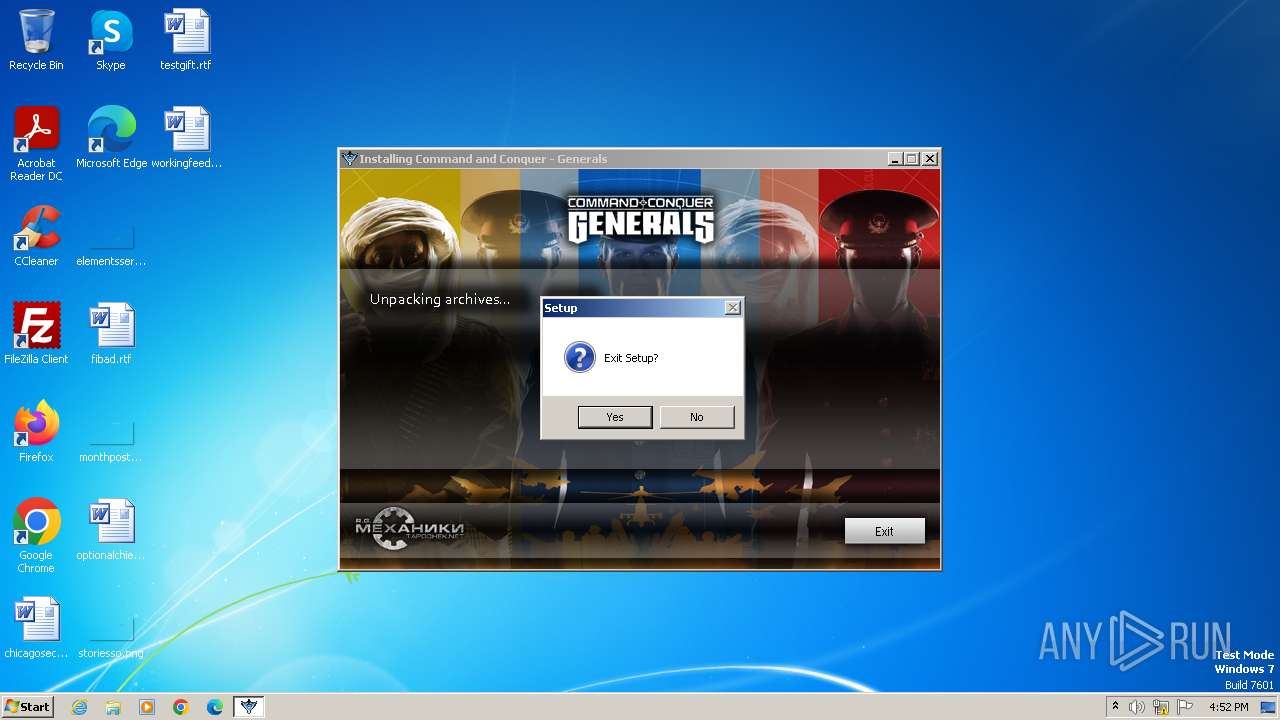
MALICIOUS
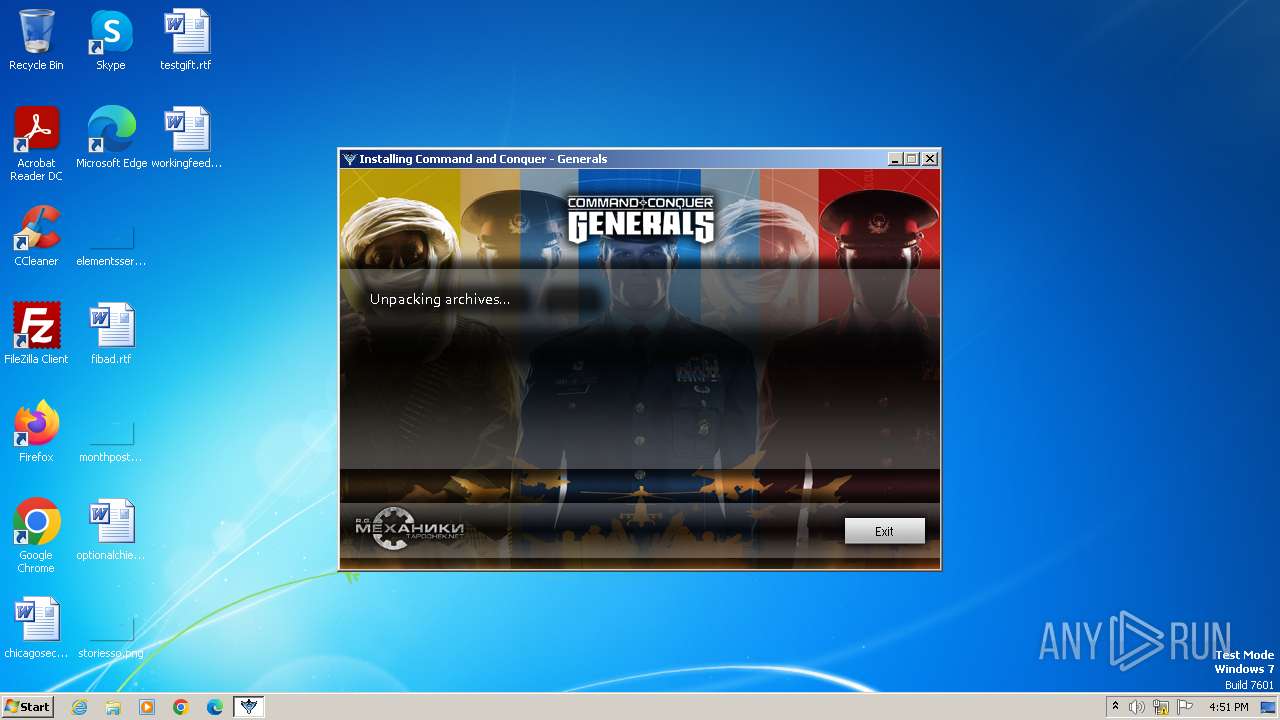
Drops the executable file immediately after the start
- setup.exe (PID: 4080)
- setup.tmp (PID: 2072)
- unins000.exe (PID: 1580)
- _iu14D2N.tmp (PID: 304)
SUSPICIOUS
Executable content was dropped or overwritten
- setup.exe (PID: 4080)
- setup.tmp (PID: 2072)
- unins000.exe (PID: 1580)
- _iu14D2N.tmp (PID: 304)
Process drops legitimate windows executable
- setup.tmp (PID: 2072)
- _iu14D2N.tmp (PID: 304)
Reads the Windows owner or organization settings
- setup.tmp (PID: 2072)
- _iu14D2N.tmp (PID: 304)
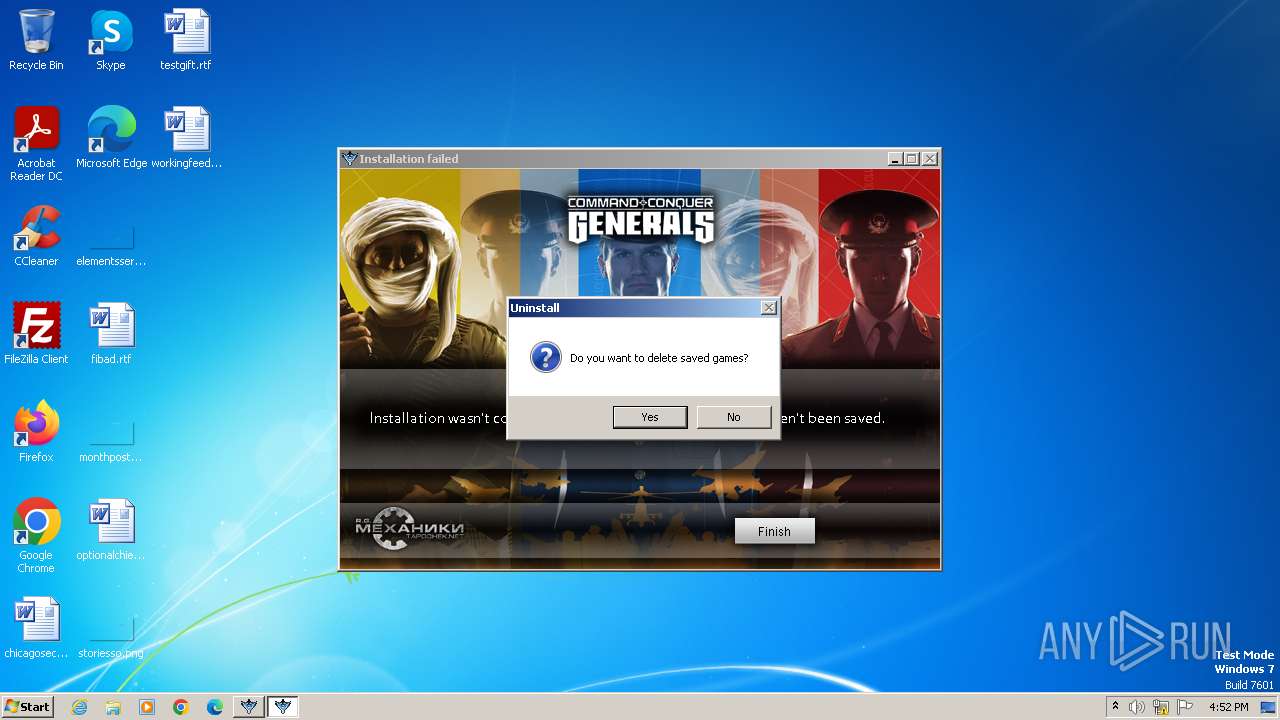
Starts itself from another location
- unins000.exe (PID: 1580)
Starts application with an unusual extension
- unins000.exe (PID: 1580)
INFO
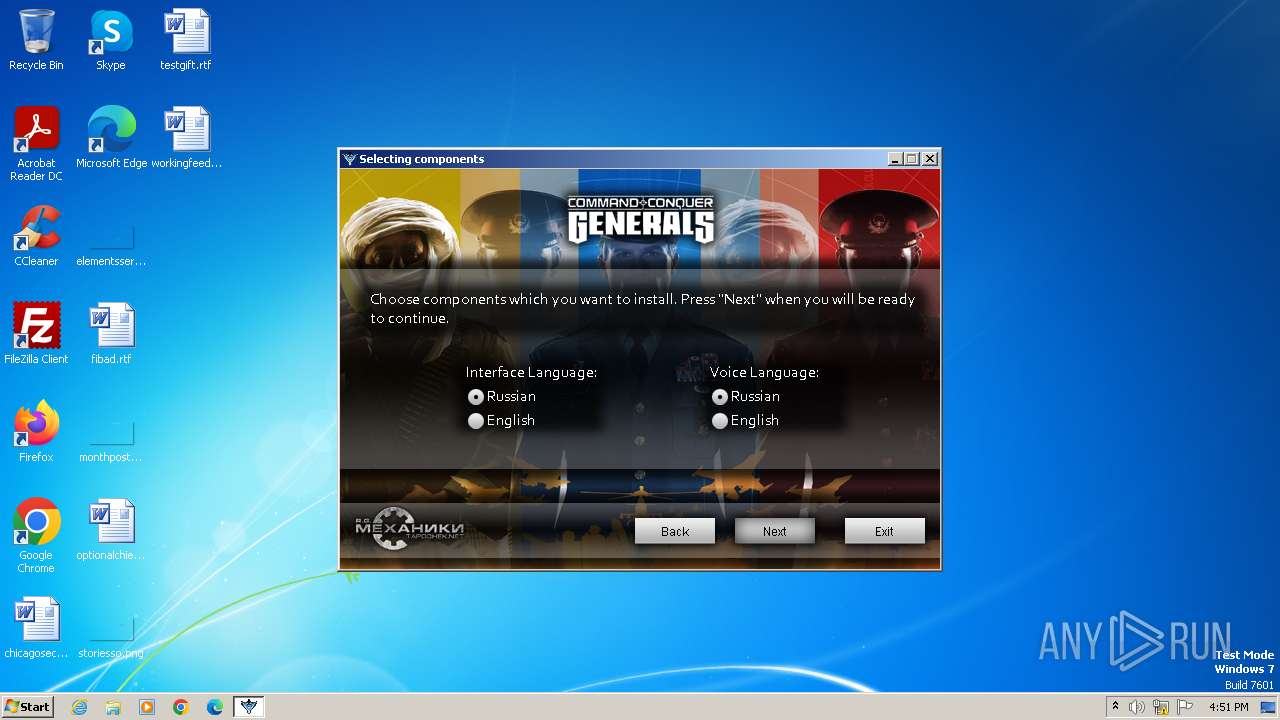
Checks supported languages
- setup.exe (PID: 4080)
- setup.tmp (PID: 2072)
- unins000.exe (PID: 1580)
- _iu14D2N.tmp (PID: 304)
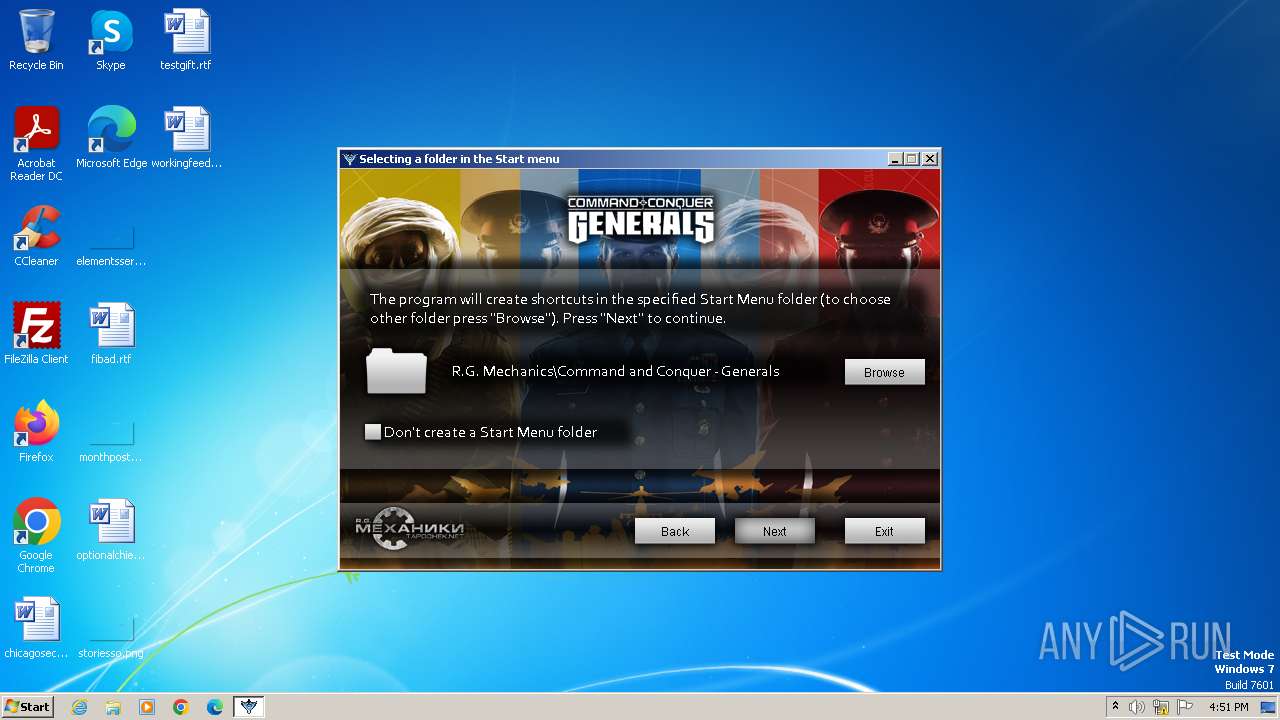
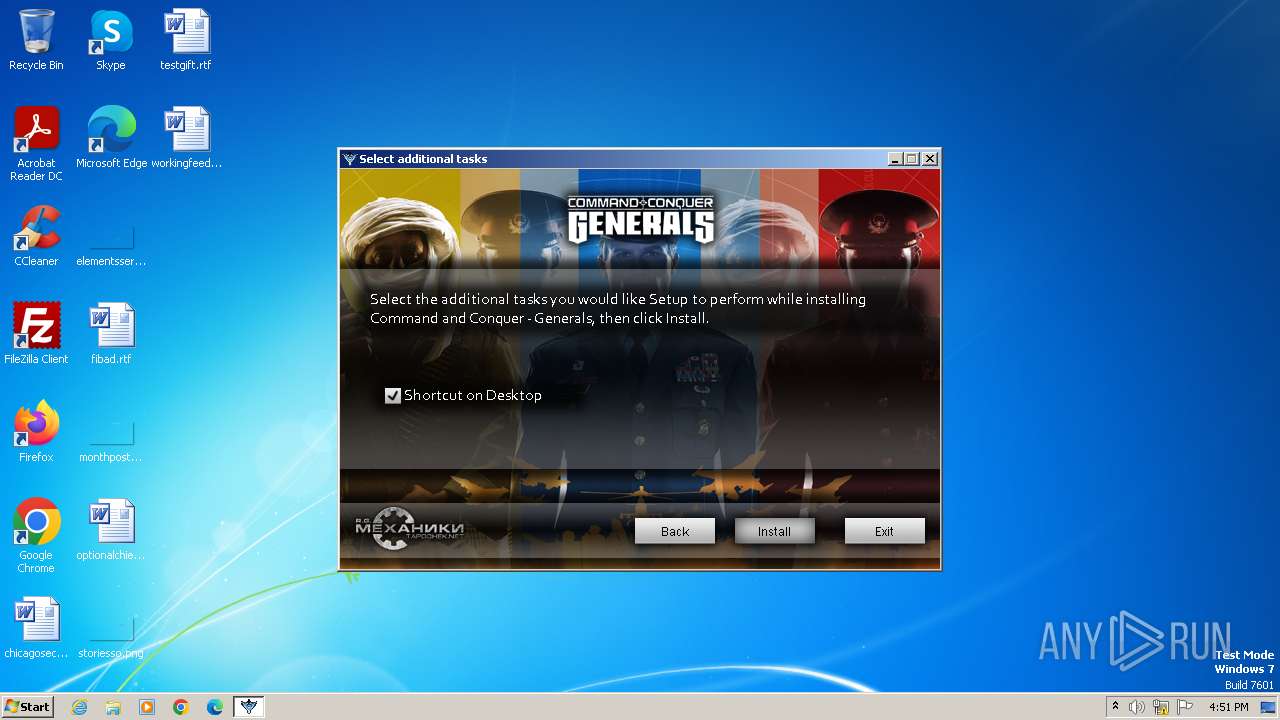
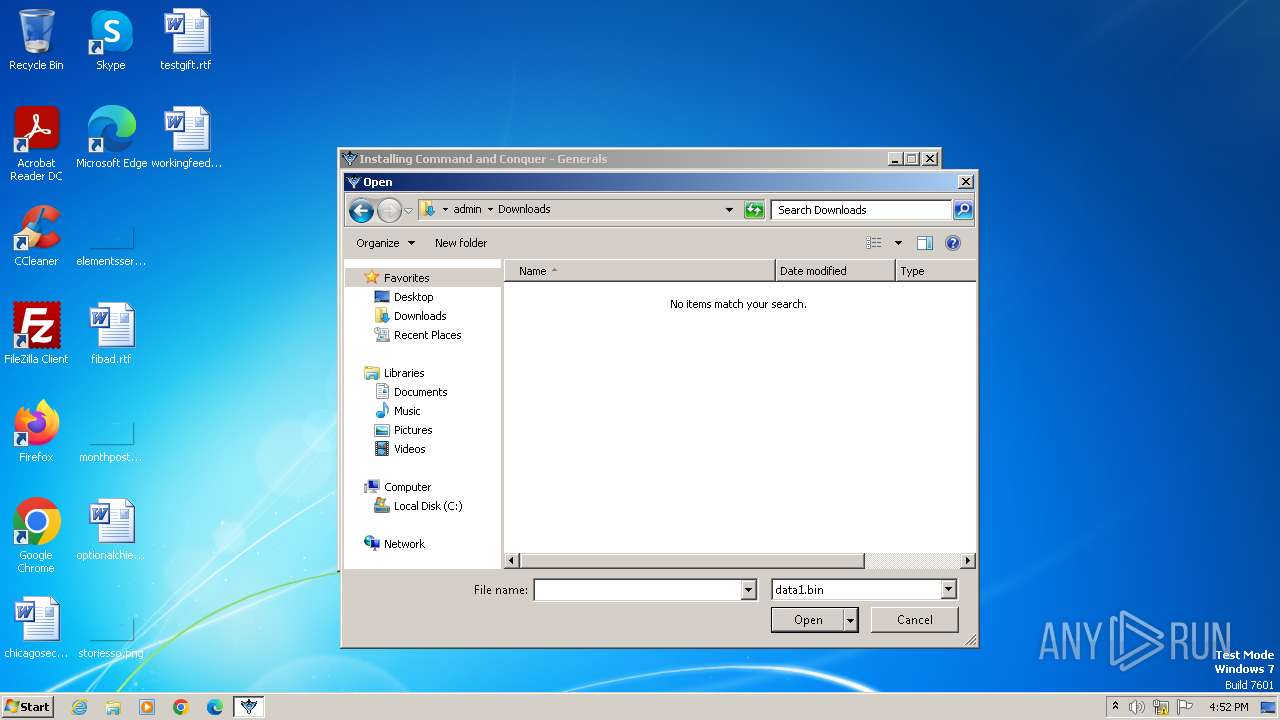
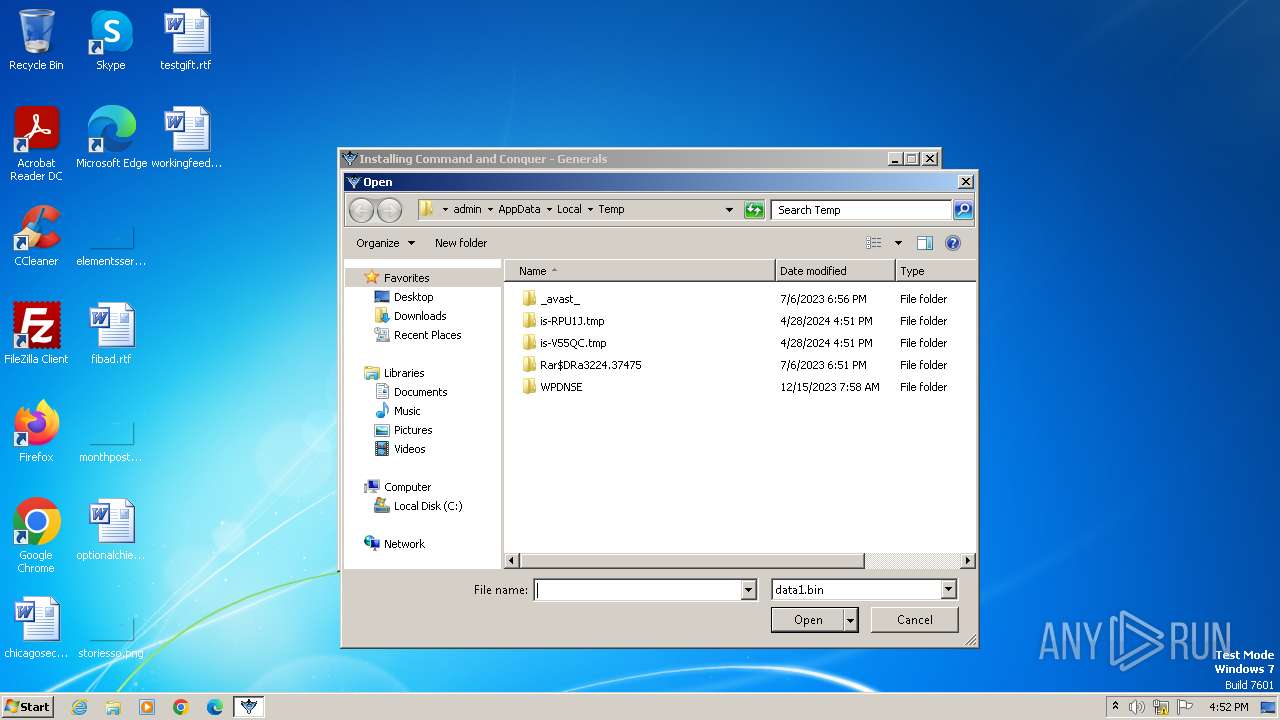
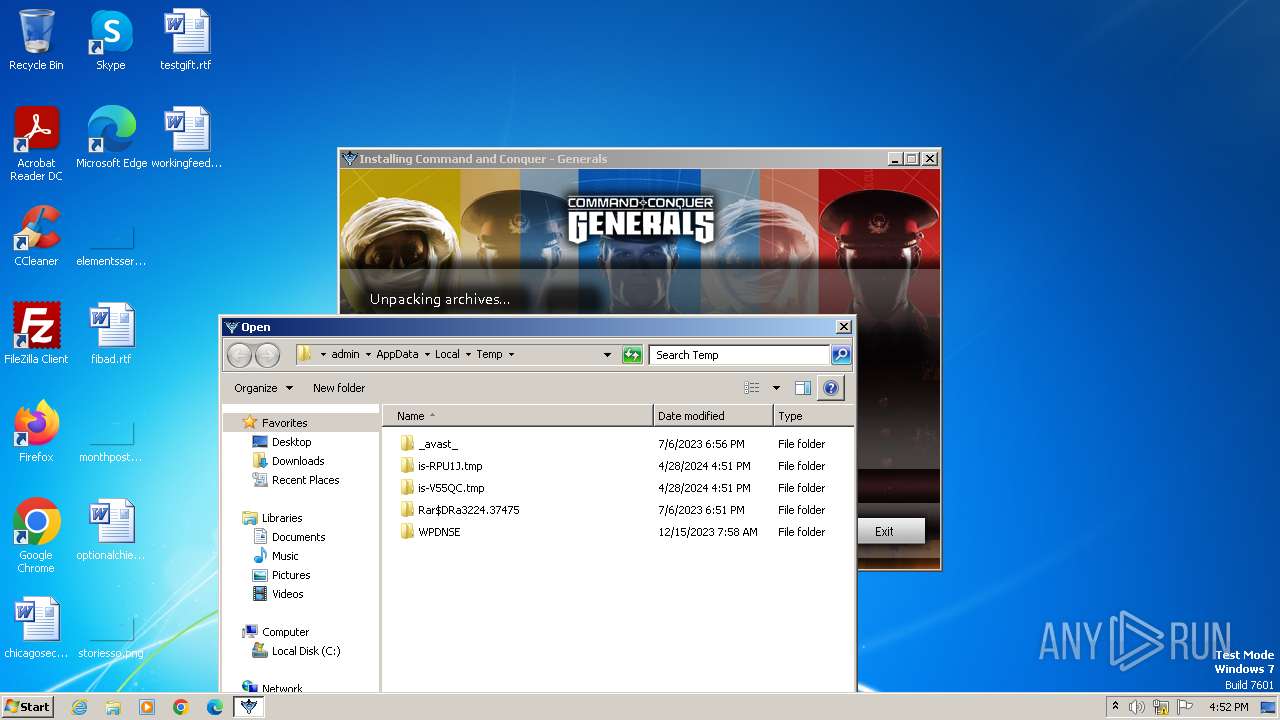
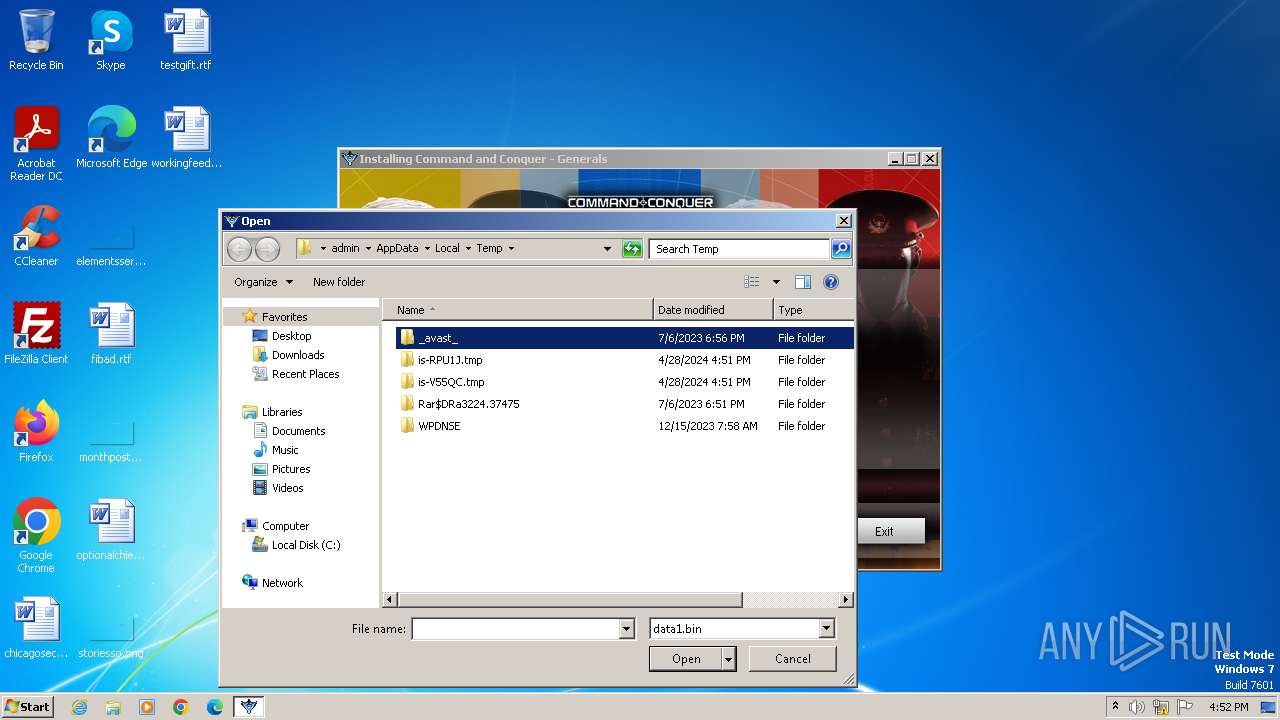
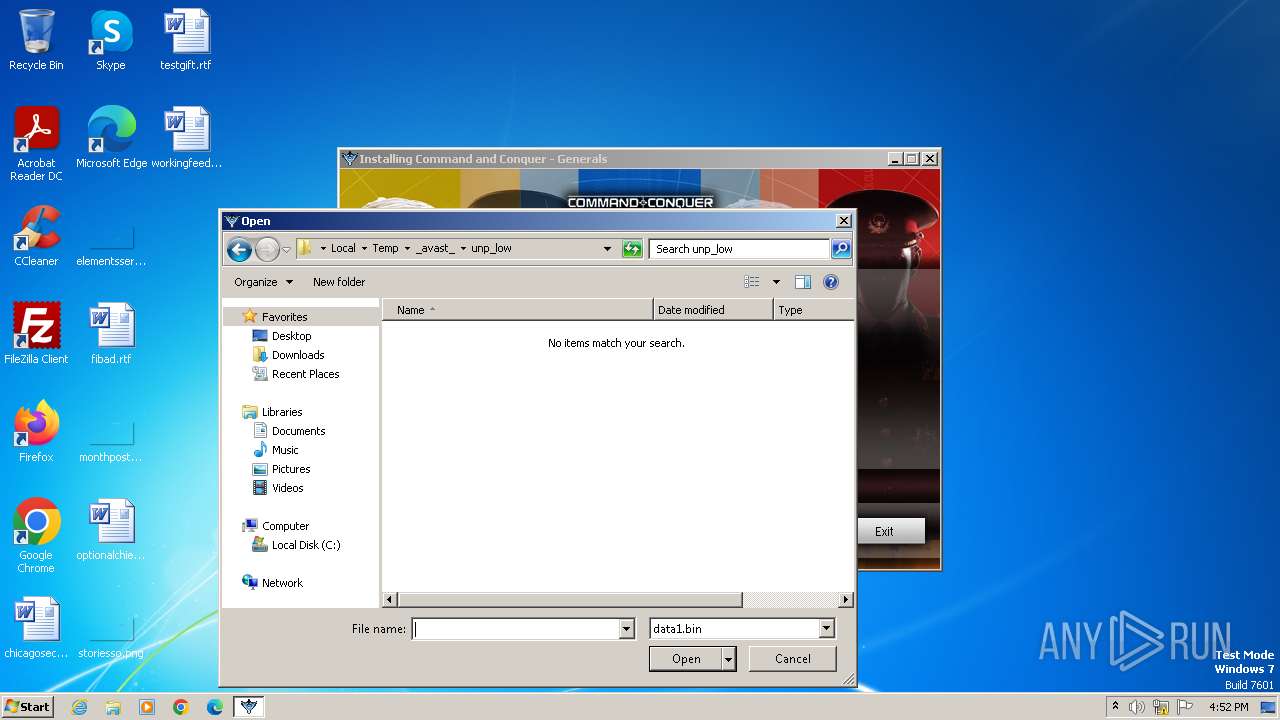
Create files in a temporary directory
- setup.exe (PID: 4080)
- setup.tmp (PID: 2072)
- unins000.exe (PID: 1580)
- _iu14D2N.tmp (PID: 304)
Reads the computer name
- setup.tmp (PID: 2072)
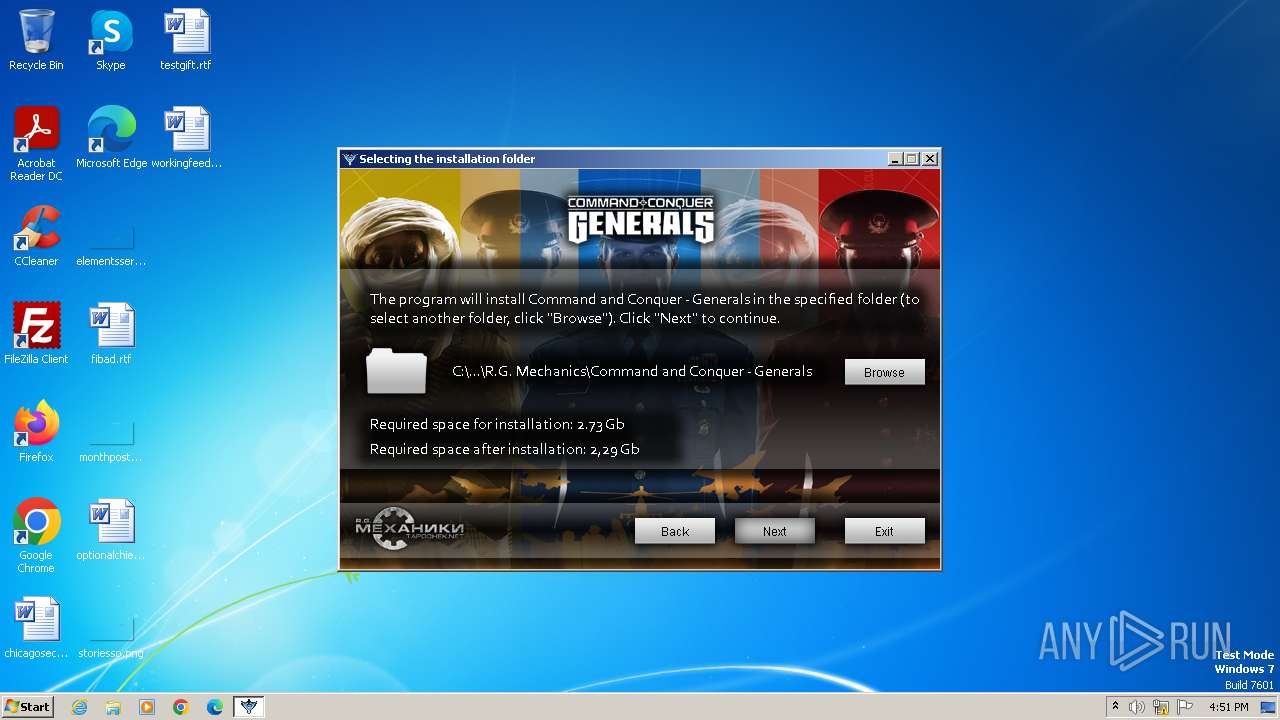
Creates files in the program directory
- setup.tmp (PID: 2072)
Creates a software uninstall entry
- setup.tmp (PID: 2072)
Reads the machine GUID from the registry
- setup.tmp (PID: 2072)
Creates files or folders in the user directory
- setup.tmp (PID: 2072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37888 |
| InitializedDataSize: | 20480 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9c14 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
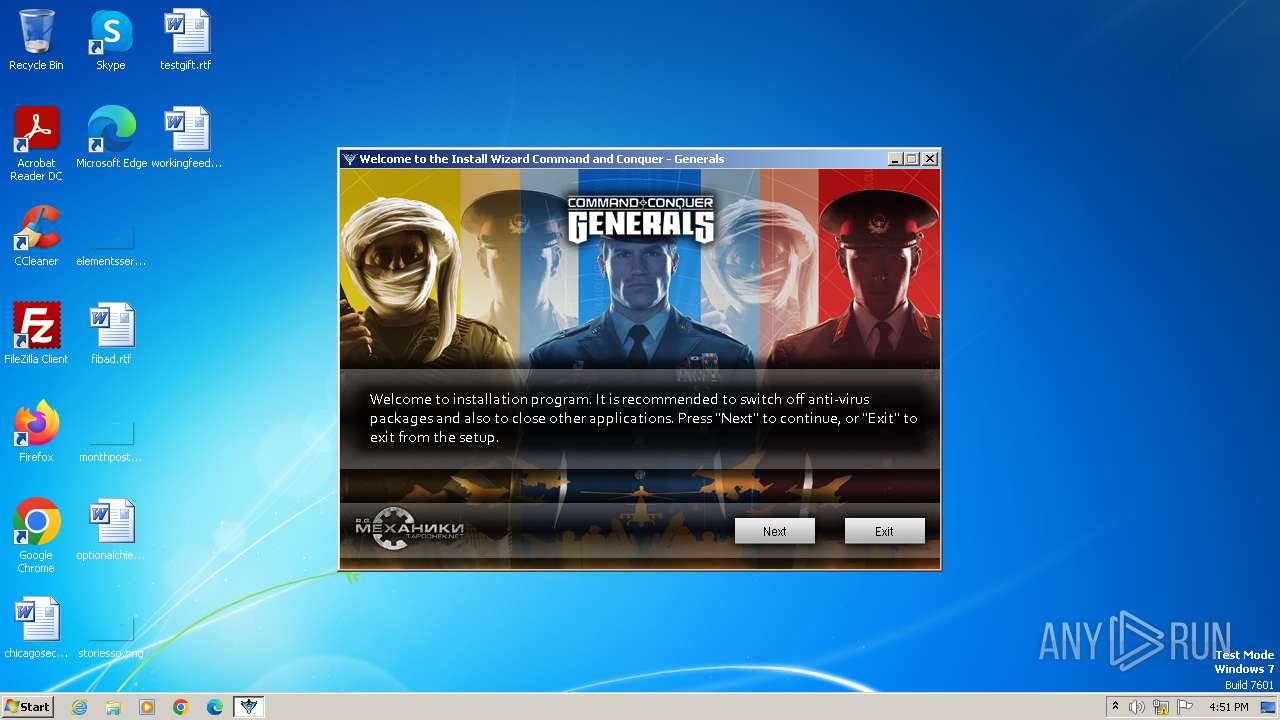
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | tapochek.net |
| FileDescription: | Command and Conquer - Generals |
| FileVersion: | 1.0.0.0 |
| LegalCopyright: | R.G. Mechanics, Panky |
| ProductName: | Command and Conquer - Generals |
| ProductVersion: | 1.0.0.0 |
Total processes
40
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp" /SECONDPHASE="C:\Users\admin\AppData\Roaming\Command and Conquer - Generals\Uninstall\unins000.exe" /FIRSTPHASEWND=$30178 /VERYSILENT | C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp | unins000.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 1580 | "C:\Users\admin\AppData\Roaming\Command and Conquer - Generals\Uninstall\unins000.exe" /VERYSILENT | C:\Users\admin\AppData\Roaming\Command and Conquer - Generals\Uninstall\unins000.exe | setup.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2072 | "C:\Users\admin\AppData\Local\Temp\is-V55QC.tmp\setup.tmp" /SL5="$30138,1693106,59392,C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\is-V55QC.tmp\setup.tmp | setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 3976 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | — | explorer.exe | |||||||||||
User: admin Company: tapochek.net Integrity Level: MEDIUM Description: Command and Conquer - Generals Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4080 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | explorer.exe | ||||||||||||
User: admin Company: tapochek.net Integrity Level: HIGH Description: Command and Conquer - Generals Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
11 557
Read events
11 325
Write events
207
Delete events
25
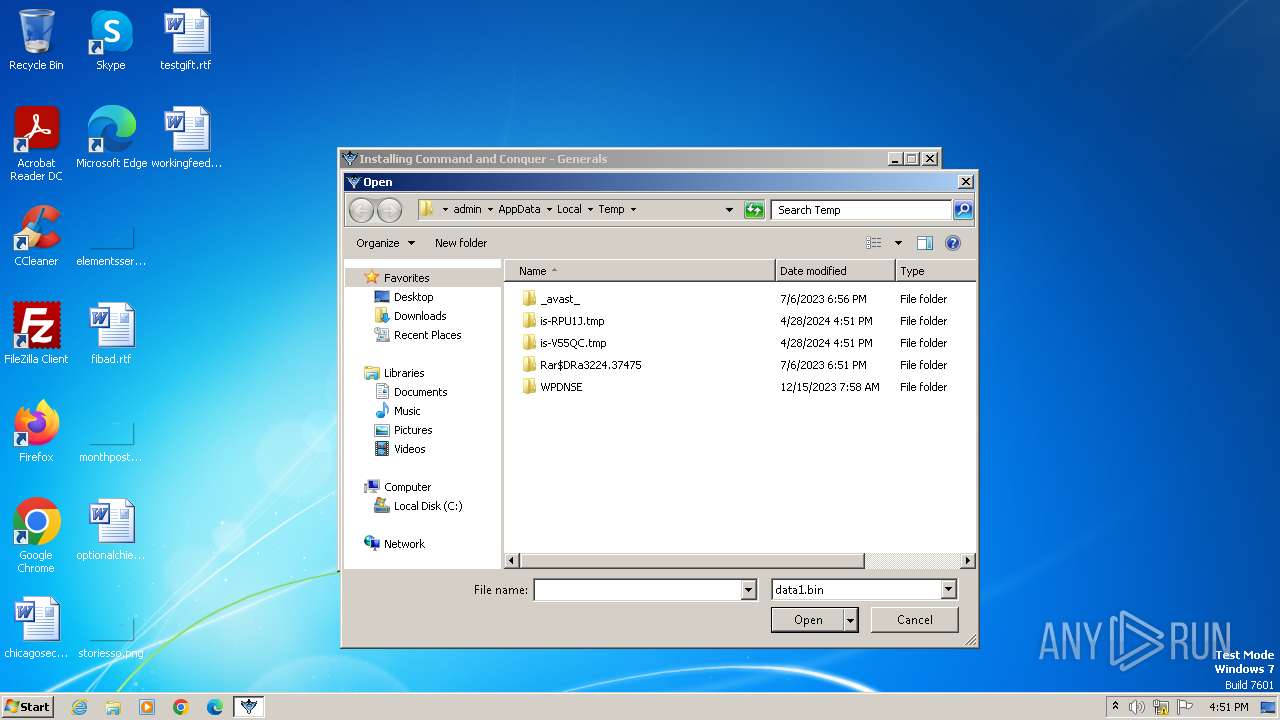
Modification events
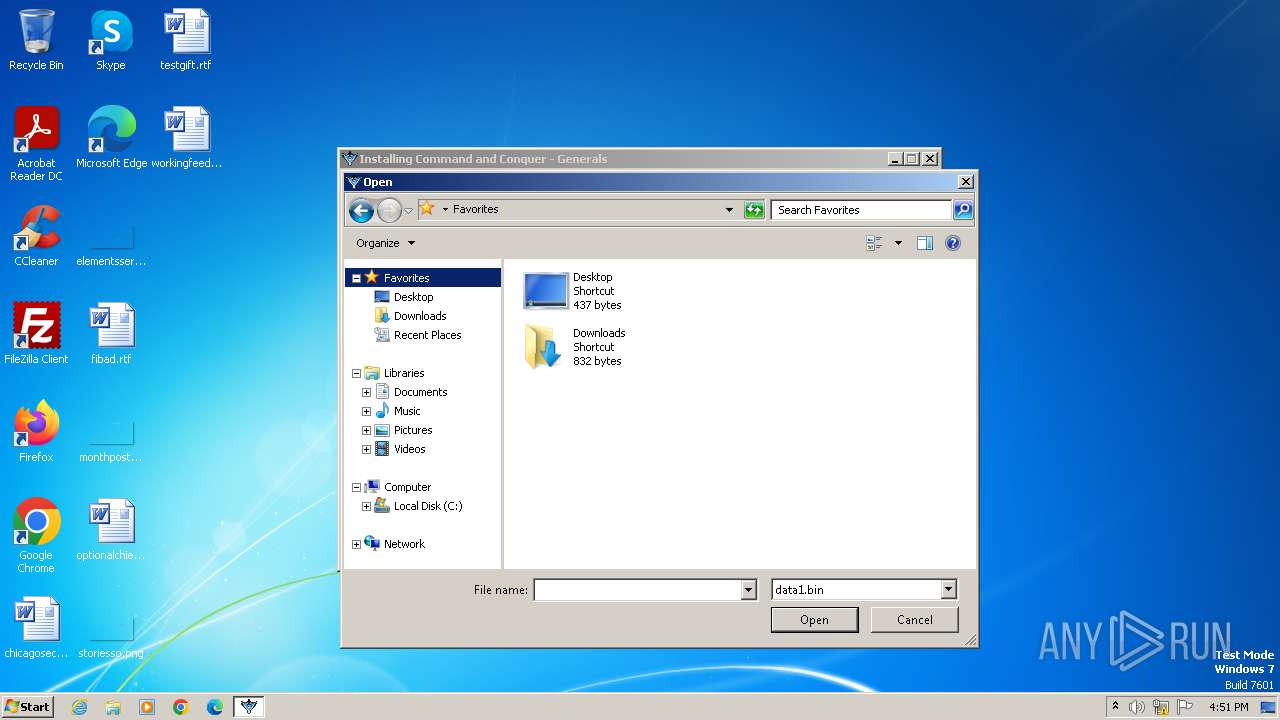
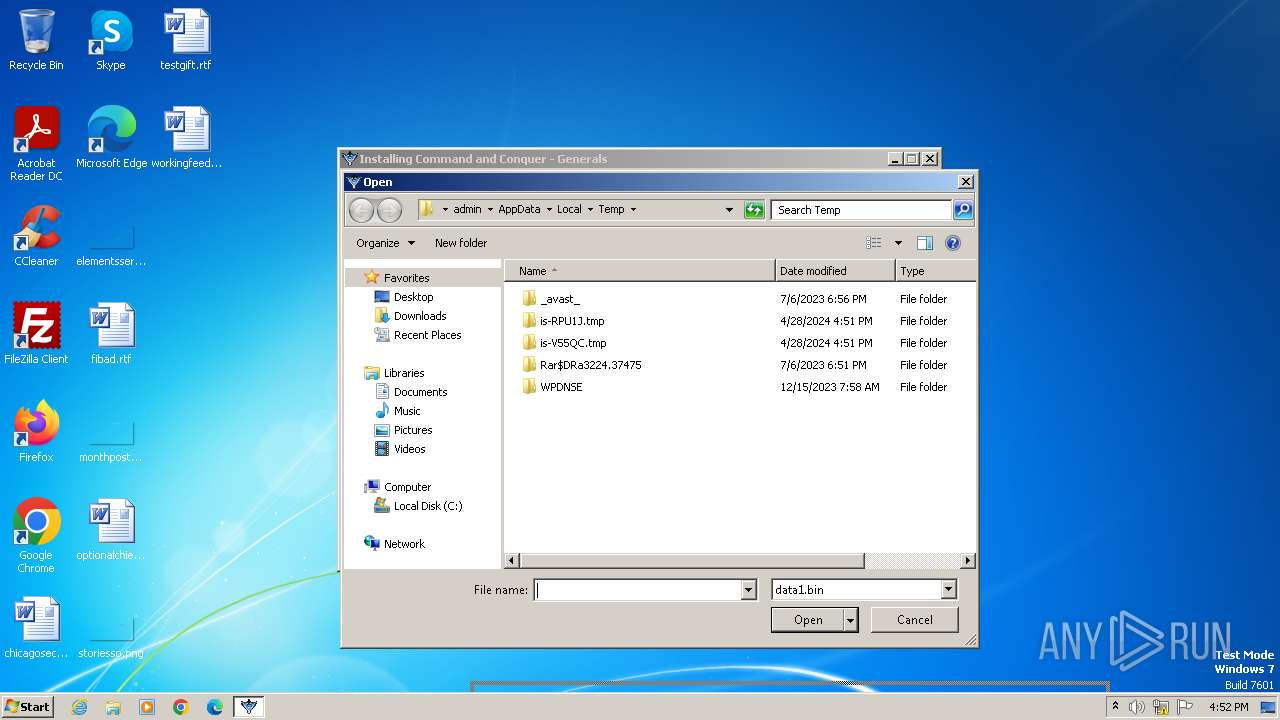
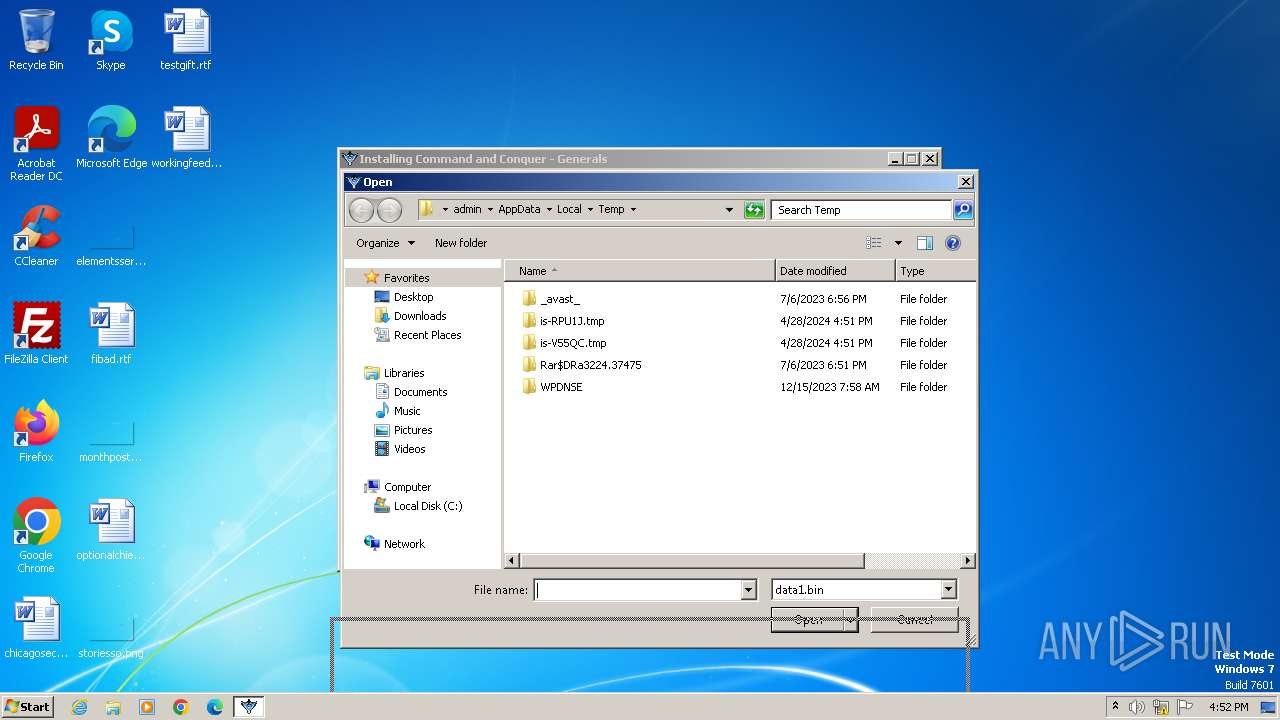
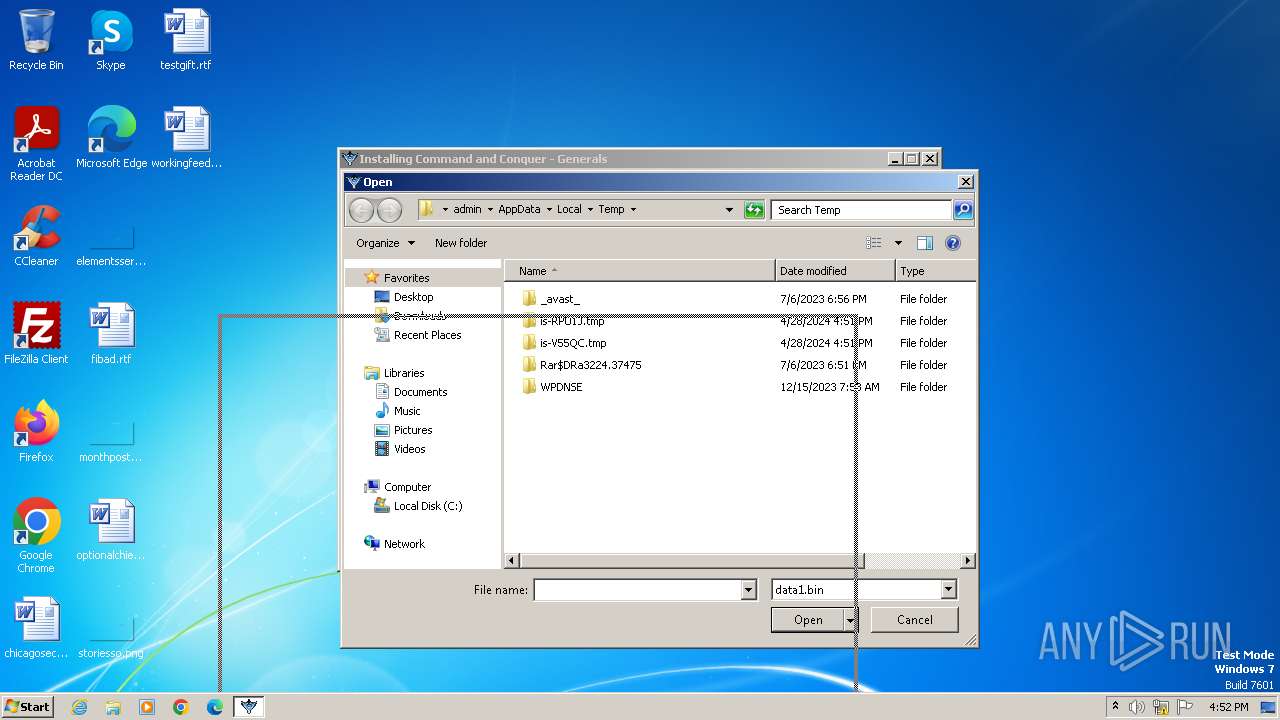
| (PID) Process: | (2072) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | delete value | Name: | MRUList |
Value: | |||
| (PID) Process: | (2072) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | 0 |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C00690073002D00560035003500510043002E0074006D0070005C00730065007400750070002E0074006D007000000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C000000 | |||
| (PID) Process: | (2072) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (2072) setup.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2072) setup.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 07000000010000000200000006000000000000000B0000000C0000000D0000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2072) setup.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\103\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
| (PID) Process: | (2072) setup.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2072) setup.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0900000007000000010000000200000006000000000000000B0000000C0000000D0000000A00000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2072) setup.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0700000009000000010000000200000006000000000000000B0000000C0000000D0000000A00000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2072) setup.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\103\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
Executable files
14
Suspicious files
1
Text files
27
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2072 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-RPU1J.tmp\_isetup\_RegDLL.tmp | executable | |
MD5:0EE914C6F0BB93996C75941E1AD629C6 | SHA256:4DC09BAC0613590F1FAC8771D18AF5BE25A1E1CB8FDBF4031AA364F3057E74A2 | |||
| 2072 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-RPU1J.tmp\SDWImage7.png | image | |
MD5:3450F2BBF8A2953ACE85F0DAC3168AEA | SHA256:D723EF4A90413558C35C9D862FBA1FEEBFB30DA9D575DBC3DBD8B8FE63D46907 | |||
| 2072 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-RPU1J.tmp\SDWImage11.png | image | |
MD5:149635BE32B1900FB9B9733D61CFE70E | SHA256:7713D4446D7326B0C751EB7E662AE9057C923EFE72814448A80EFA5E471ACFC1 | |||
| 2072 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-RPU1J.tmp\SDWImage9.png | image | |
MD5:DE5659D4A338EA9454DA0D15A166E737 | SHA256:1C1BB4546E59E2953BBD831B16746D24AAEF607B4167E173D03B46DF3C94BD63 | |||
| 2072 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-RPU1J.tmp\SDWImage10.png | image | |
MD5:AAB377E3EF751DC212F70C12DC577512 | SHA256:4512AAC6CBA173F582A7351E21AAFE8216135303191709FB264822407168041C | |||
| 2072 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-RPU1J.tmp\SDWImage8.png | image | |
MD5:72914E7EBB71916EFE3E63D4E70FFAFB | SHA256:0A7B552BE8D1341B73F45DD49FD81912623504A355EE7848EC2EEED2D607EBD7 | |||
| 2072 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-RPU1J.tmp\BGImage1.png | image | |
MD5:7E7BABA0A45675FB3BB23E80A21DA627 | SHA256:3DED6E1FF32DDC1A078A6F5132AF98ECBE0D50BA24BA82E92402308D268FD6B6 | |||
| 2072 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-RPU1J.tmp\botva2.dll | executable | |
MD5:67965A5957A61867D661F05AE1F4773E | SHA256:450B9B0BA25BF068AFBC2B23D252585A19E282939BF38326384EA9112DFD0105 | |||
| 4080 | setup.exe | C:\Users\admin\AppData\Local\Temp\is-V55QC.tmp\setup.tmp | executable | |
MD5:B35695A9E38A0B20DE3F9596524FE555 | SHA256:47A3B4DA5326BDBED2AE1C67B38780B578C0123AB07C92904412DF120EF494B7 | |||
| 2072 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-RPU1J.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |