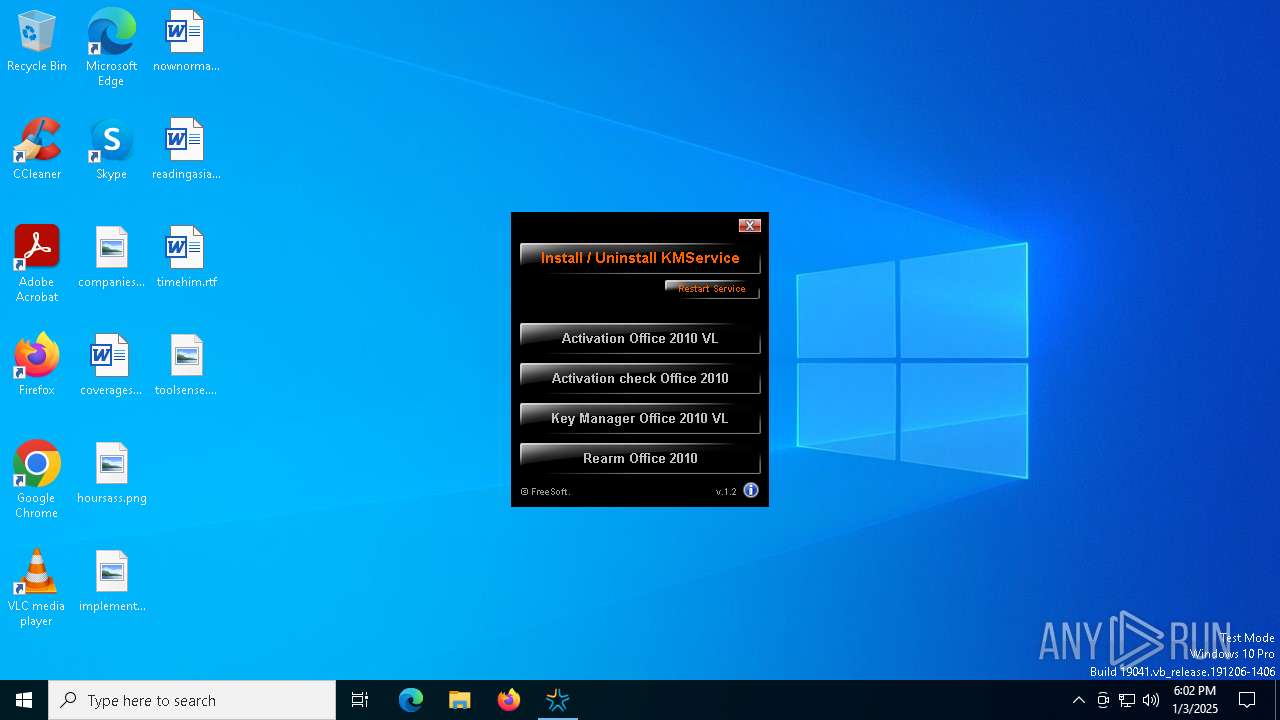
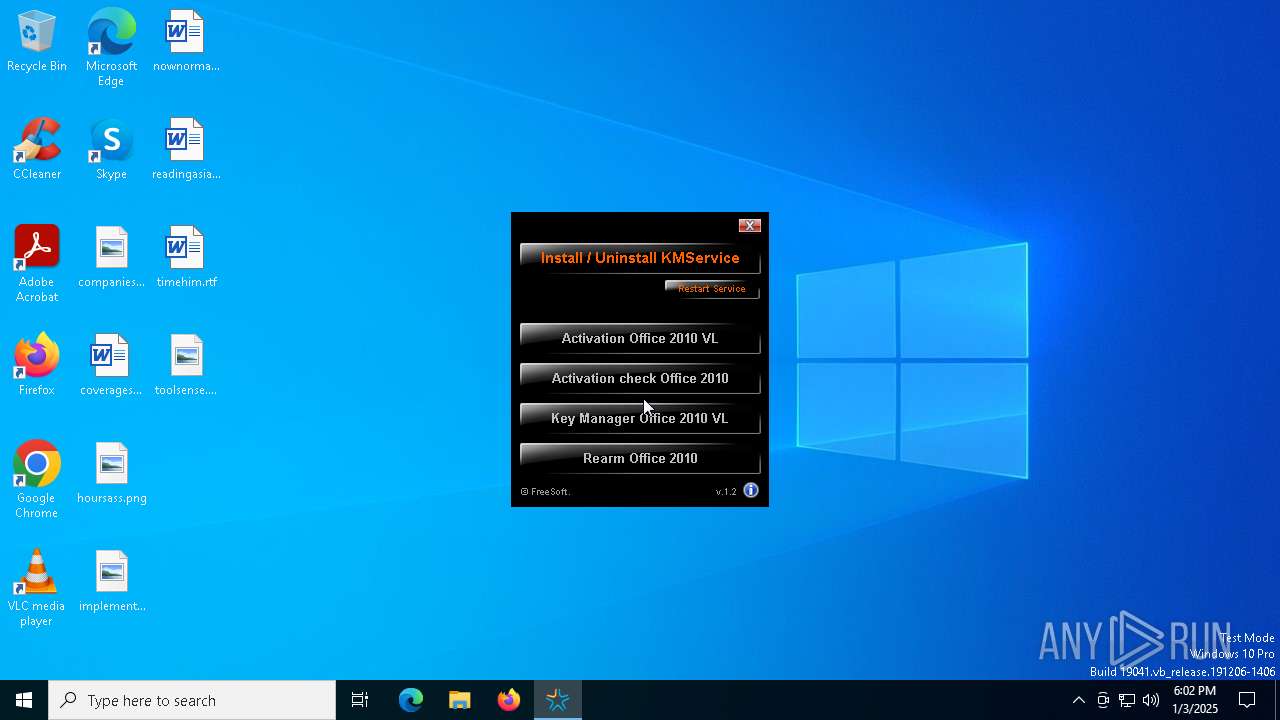
| File name: | mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe |
| Full analysis: | https://app.any.run/tasks/2d890ec0-1a91-4080-bcb4-26d699b2a7ca |
| Verdict: | Malicious activity |
| Analysis date: | January 03, 2025, 18:02:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, 3 sections |
| MD5: | 5F4091B76C20EBB609730620D05B70CD |
| SHA1: | 493C3B008780B48413E435AE04AD39DDE1BF567B |
| SHA256: | FD47386E7CEBFF127DA53526768DB1E6861E0A8FC9AC18E21FB727549DC33283 |
| SSDEEP: | 49152:q3OR19ad2MkGzUkusEapl9LLZU6hVKmf0G4EPHwxE/oYKQipJTg9XokGX+1+rdQ+:QOR1IkmIkbEkltFhVBj4EvwuQYKQi4ox |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe (PID: 6232)
- autorun.exe (PID: 6816)
The process creates files with name similar to system file names
- mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe (PID: 6232)
Reads security settings of Internet Explorer
- mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe (PID: 6232)
- autorun.exe (PID: 6816)
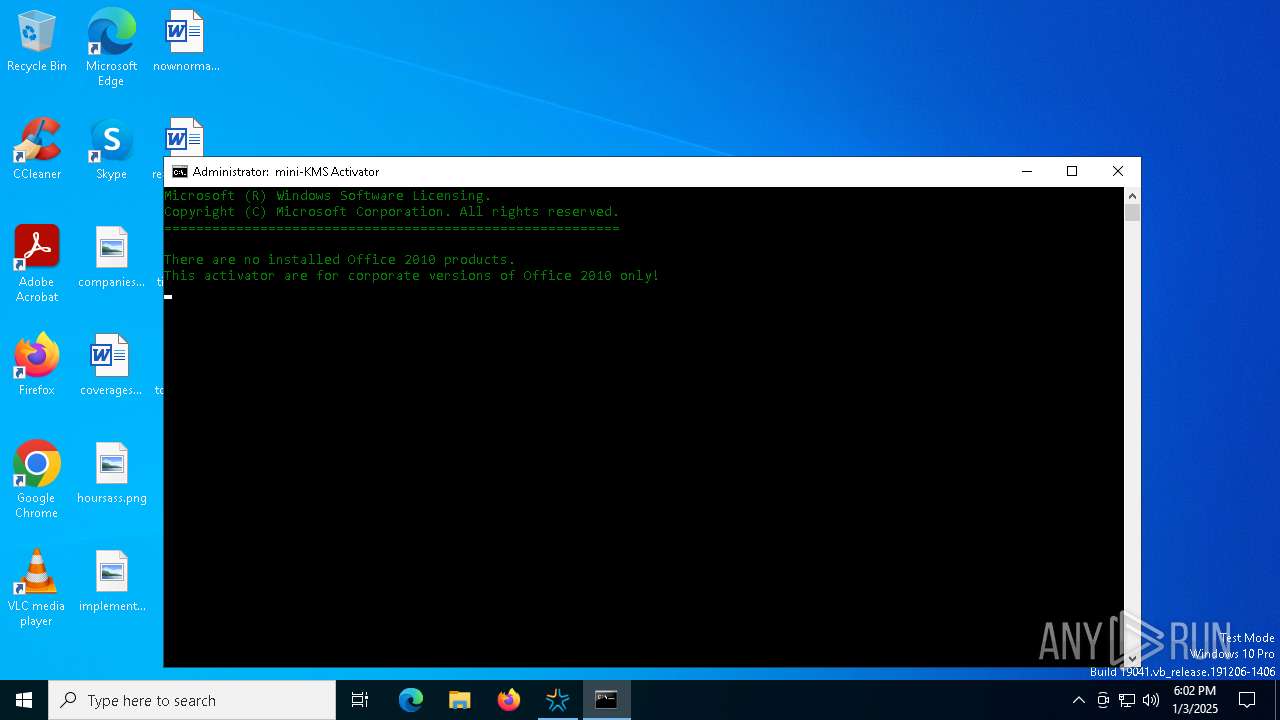
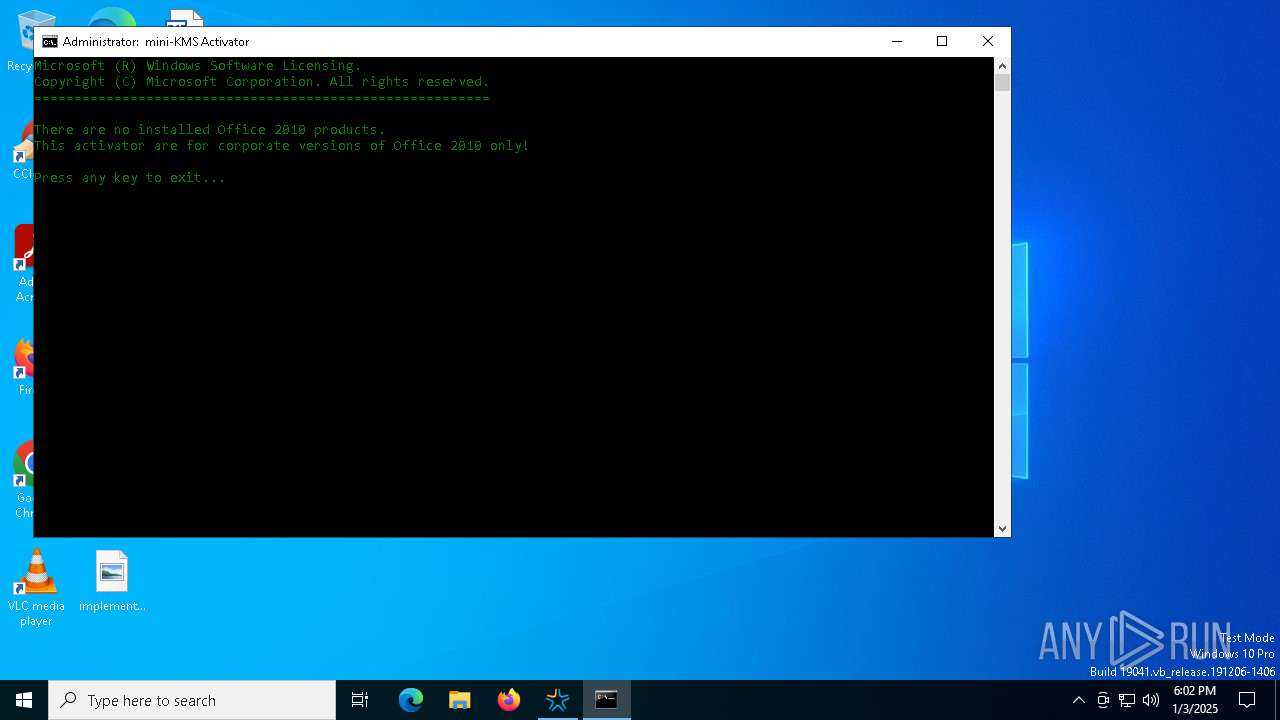
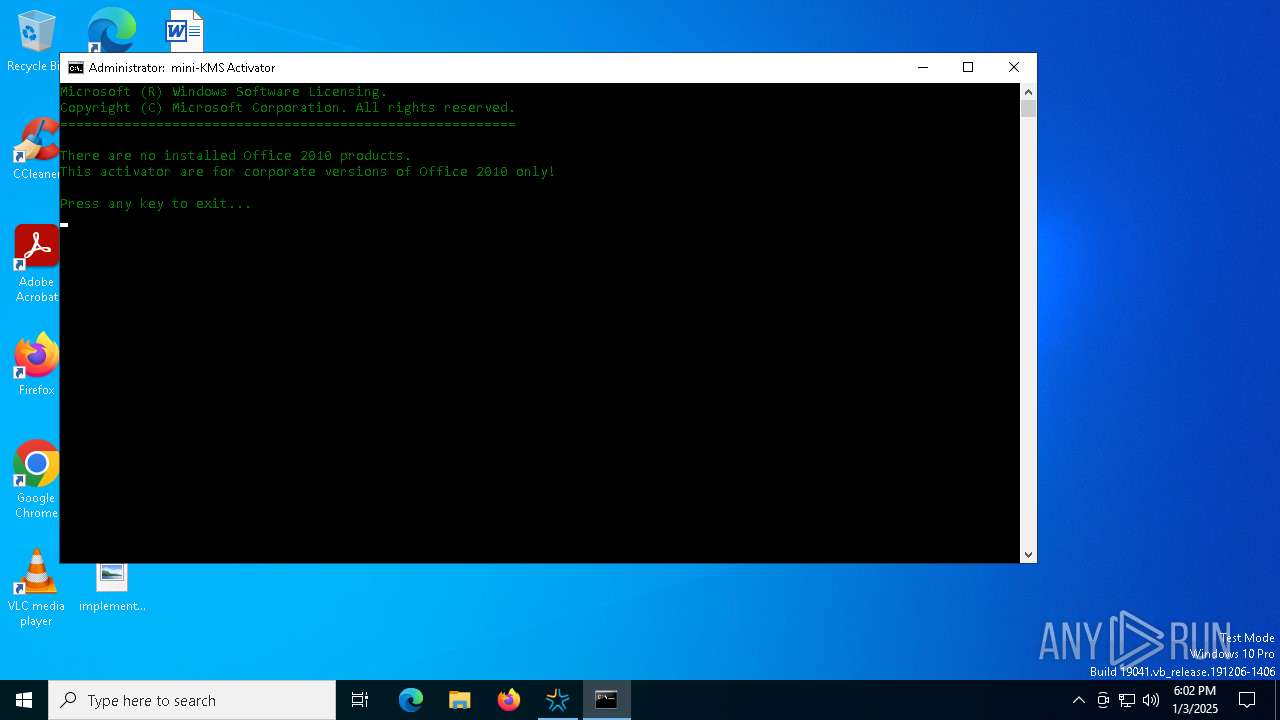
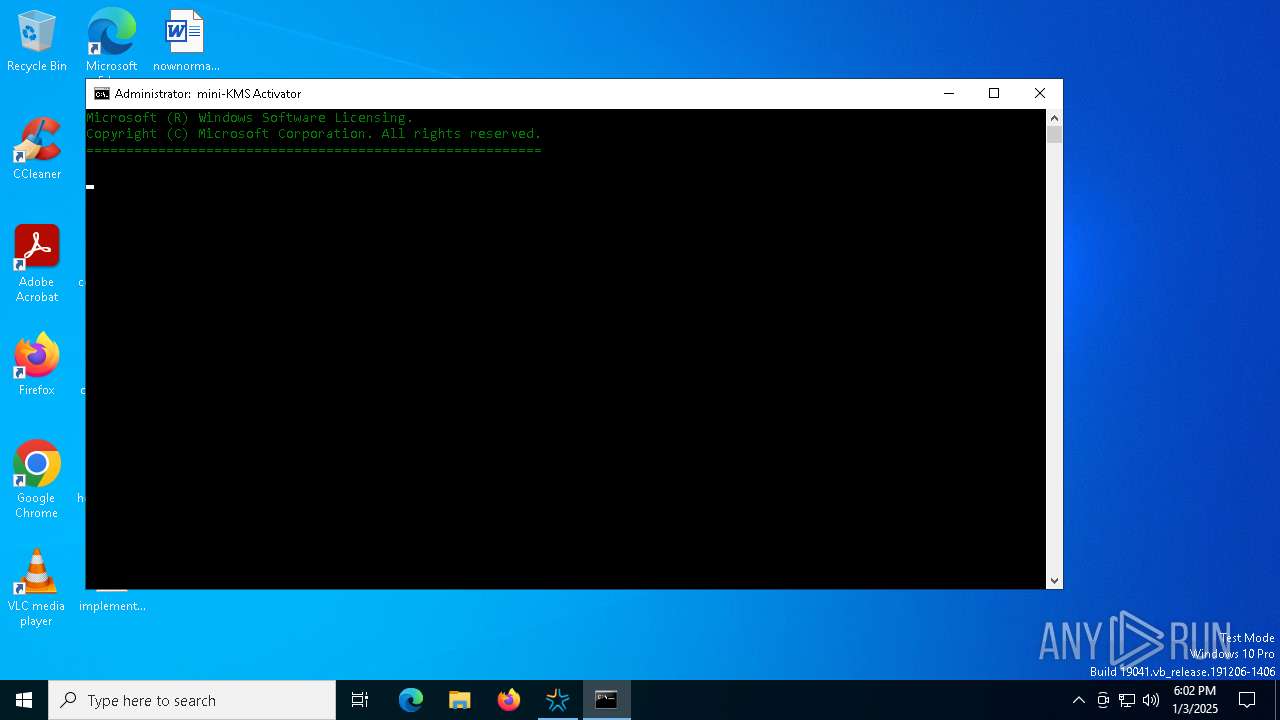
Starts CMD.EXE for commands execution
- mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe (PID: 6232)
- autorun.exe (PID: 6816)
Process drops legitimate windows executable
- mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe (PID: 6232)
The executable file from the user directory is run by the CMD process
- autorun.exe (PID: 6816)
Executing commands from ".cmd" file
- autorun.exe (PID: 6816)
- mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe (PID: 6232)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7000)
Get information on the list of running processes
- cmd.exe (PID: 7000)
INFO
Checks supported languages
- mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe (PID: 6232)
- autorun.exe (PID: 6816)
The sample compiled with english language support
- mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe (PID: 6232)
- autorun.exe (PID: 6816)
The sample compiled with russian language support
- mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe (PID: 6232)
Create files in a temporary directory
- mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe (PID: 6232)
- autorun.exe (PID: 6816)
Reads the computer name
- mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe (PID: 6232)
- autorun.exe (PID: 6816)
Process checks computer location settings
- mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe (PID: 6232)
- autorun.exe (PID: 6816)
UPX packer has been detected
- mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe (PID: 6232)
The process uses the downloaded file
- autorun.exe (PID: 6816)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:02:07 06:33:08+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 1024000 |
| InitializedDataSize: | 32768 |
| UninitializedDataSize: | 1552384 |
| EntryPoint: | 0x2749b0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.2.0.0 |
| ProductVersionNumber: | 1.2.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release, Private build |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
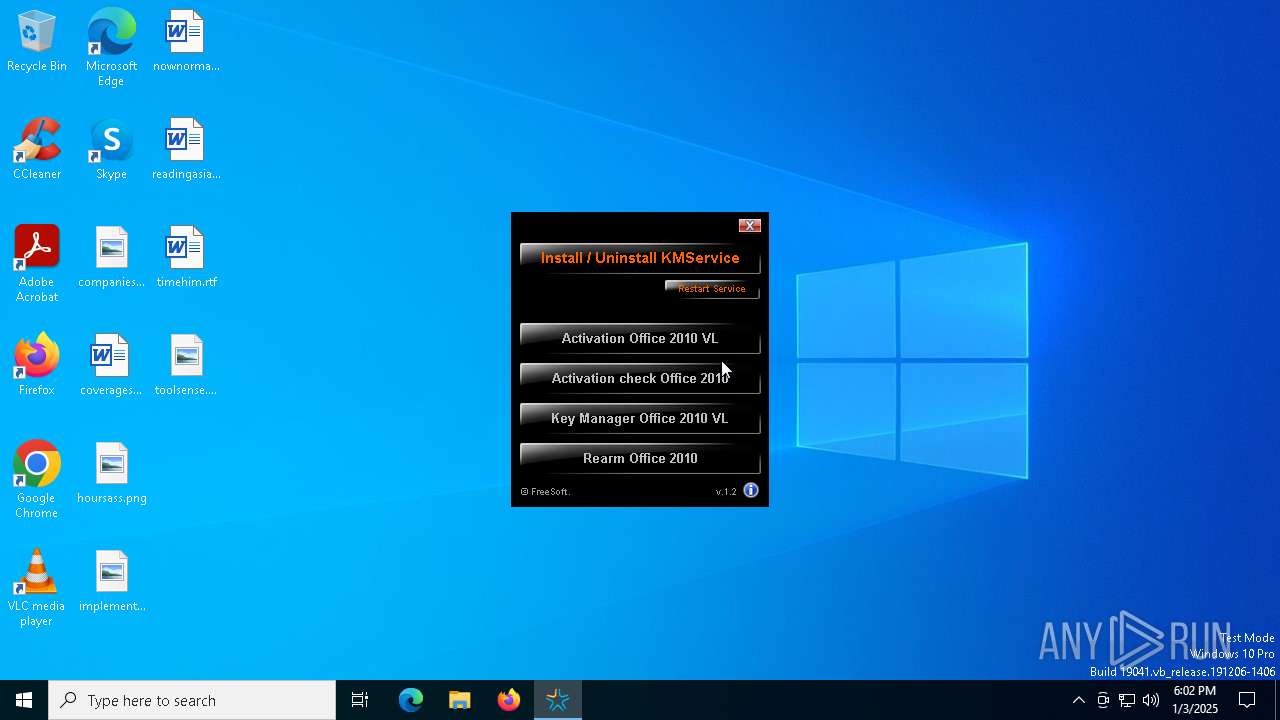
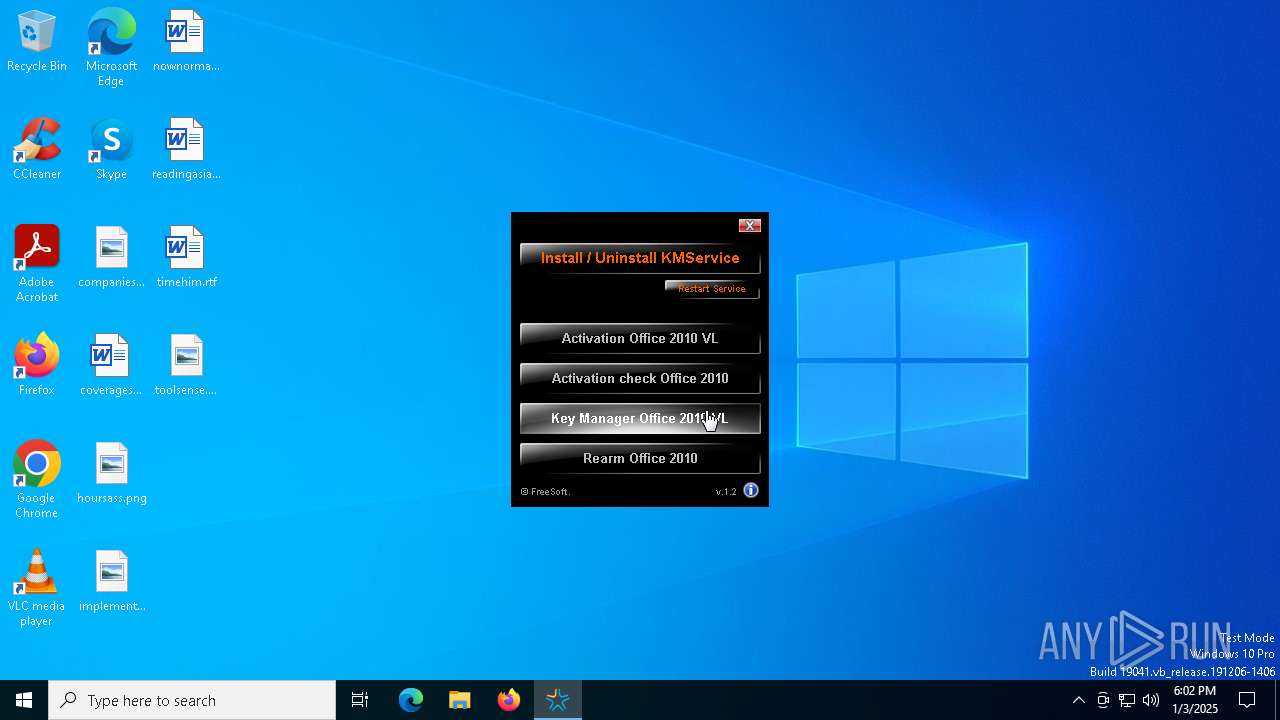
| CompanyName: | FreeSoft |
| FileDescription: | mini-KMS Activator |
| FileVersion: | 1,2,0,0 |
| ProductName: | mini-KMS Activator v1.2 Office2010 VL ENG |
| InternalName: | mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe |
| ProductVersion: | 1,2,0,0 |
| LegalCopyright: | © 2010, FreeSoft |
Total processes
154
Monitored processes
25
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1064 | REG QUERY HKLM\SOFTWARE\Microsoft\Office | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2624 | find /i "14.0" | C:\Windows\SysWOW64\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3544 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\5509.tmp\Chk.cmd" " | C:\Windows\SysWOW64\cmd.exe | — | autorun.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5208 | REG QUERY HKLM\SOFTWARE\Microsoft\Office | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5532 | "C:\Users\admin\AppData\Local\Temp\mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe" | C:\Users\admin\AppData\Local\Temp\mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 5604 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5696 | find /i "14.0" | C:\Windows\SysWOW64\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6232 | "C:\Users\admin\AppData\Local\Temp\mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe" | C:\Users\admin\AppData\Local\Temp\mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 6452 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\5509.tmp\Start.cmd" " | C:\Windows\SysWOW64\cmd.exe | — | mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) | |||||||||||||||
| 6460 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
Total events
1 016
Read events
1 016
Write events
0
Delete events
0
Modification events
Executable files
12
Suspicious files
3
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6232 | mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe | C:\Users\admin\AppData\Local\Temp\5509.tmp\srvany.exe | executable | |
MD5:4635935FC972C582632BF45C26BFCB0E | SHA256:ABD4AFD71B3C2BD3F741BBE3CEC52C4FA63AC78D353101D2E7DC4DE2725D1CA1 | |||
| 6232 | mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe | C:\Users\admin\AppData\Local\Temp\5509.tmp\KMService.exe | executable | |
MD5:BCA43E19E7013331D99FF788EA6B42A0 | SHA256:B075602CF6BCB3284C44A640DAFFA49CC5AA8F469A20E4B242F2DDE85FCB4DBE | |||
| 6232 | mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe | C:\Users\admin\AppData\Local\Temp\5509.tmp\cscript.exe | executable | |
MD5:34098403F9D8F71CE2EC749122168E89 | SHA256:12DF0B06A9B56DCE3EFDB85984F84B387B1A5B61C9EBBF5A3BD61A5FBB996F60 | |||
| 6232 | mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe | C:\Users\admin\AppData\Local\Temp\5509.tmp\Chk.cmd | text | |
MD5:446E36B030E961F4738F7C2CBBDC2E45 | SHA256:0FFBA112E282785C7310F267D4673303046ADED0786BDC37BB9A9A627740EF6C | |||
| 6232 | mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe | C:\Users\admin\AppData\Local\Temp\5509.tmp\hidcon.exe | executable | |
MD5:B2DADAB18C318443301D0087CD7200BA | SHA256:B88A4D442BCD94457FC75DC5A541DC3437FD01091A2B6500569C699260E65238 | |||
| 6232 | mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe | C:\Users\admin\AppData\Local\Temp\5509.tmp\Act.cmd | text | |
MD5:5B4C58D71EE0D2B6A568B0BE49F22109 | SHA256:C3D3CE5F098D661499CD72A7728762452E09D2929888B4CF1BA4A367AC0EF8C6 | |||
| 6232 | mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe | C:\Users\admin\AppData\Local\Temp\5509.tmp\service.inf | text | |
MD5:9EE35B92CE83972E9D38F57B6B885057 | SHA256:AEFB41EB7A52009D9490A4C09C2DD4B6BEED3B3614CD2A7BAA36384DFE395D0C | |||
| 6232 | mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe | C:\Users\admin\AppData\Local\Temp\5509.tmp\Rest.cmd | text | |
MD5:36CE3FA1E31C33133B13437DAAD5866F | SHA256:A4C0F40806A2D28393208FA25AFFE5F108DBB0B65EED750F613E0E4884DEE71C | |||
| 6232 | mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe | C:\Users\admin\AppData\Local\Temp\5509.tmp\KeyMng.cmd | text | |
MD5:EF937694A5D582E803A3CB3529C4408C | SHA256:E975348F9C0D1DCEE3D4B747895635E83B8AAB98D09B8E259A27590C862F1F0B | |||
| 6232 | mini-KMS_Activator_v1.2_Office2010_VL_ENG_FIXED.exe | C:\Users\admin\AppData\Local\Temp\5509.tmp\Rearm.cmd | text | |
MD5:226035E36361A016DFD6A1D601A03C01 | SHA256:BF14A1C88ED5427A29BE11C29742AC8B55D473D04446FF63E31075BC55BD6AC0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
31
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6320 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4628 | SIHClient.exe | GET | 200 | 184.30.230.103:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.230.103:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4628 | SIHClient.exe | GET | 200 | 184.30.230.103:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 184.30.230.103:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.23.227.215:443 | www.bing.com | Ooredoo Q.S.C. | QA | unknown |
— | — | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1076 | svchost.exe | 23.56.254.14:443 | go.microsoft.com | Mobile Telecommunications Company | KW | whitelisted |
1176 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |