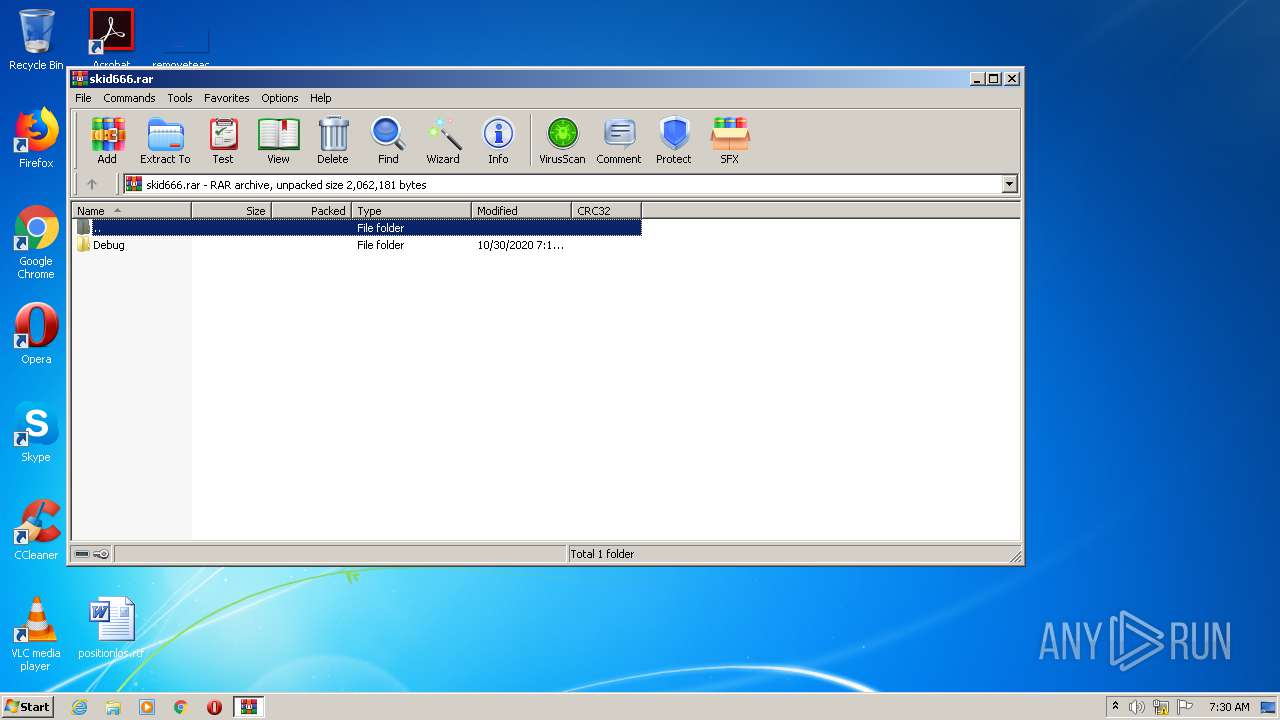
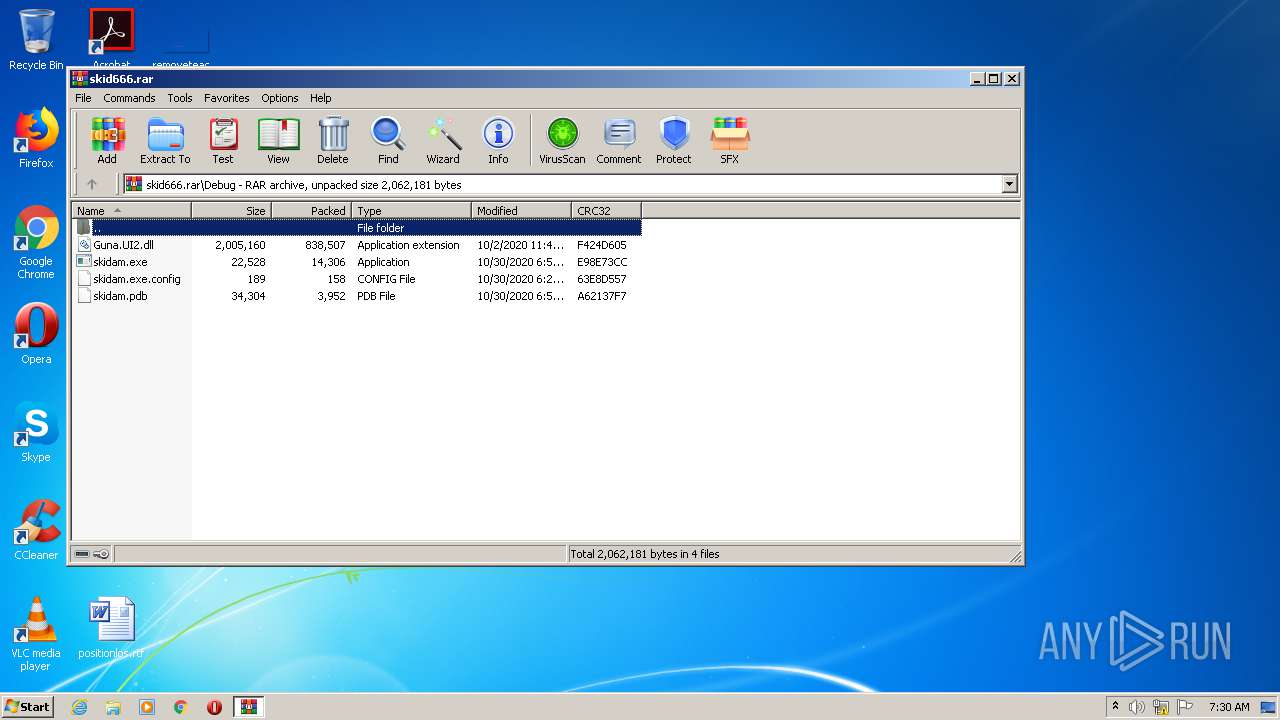
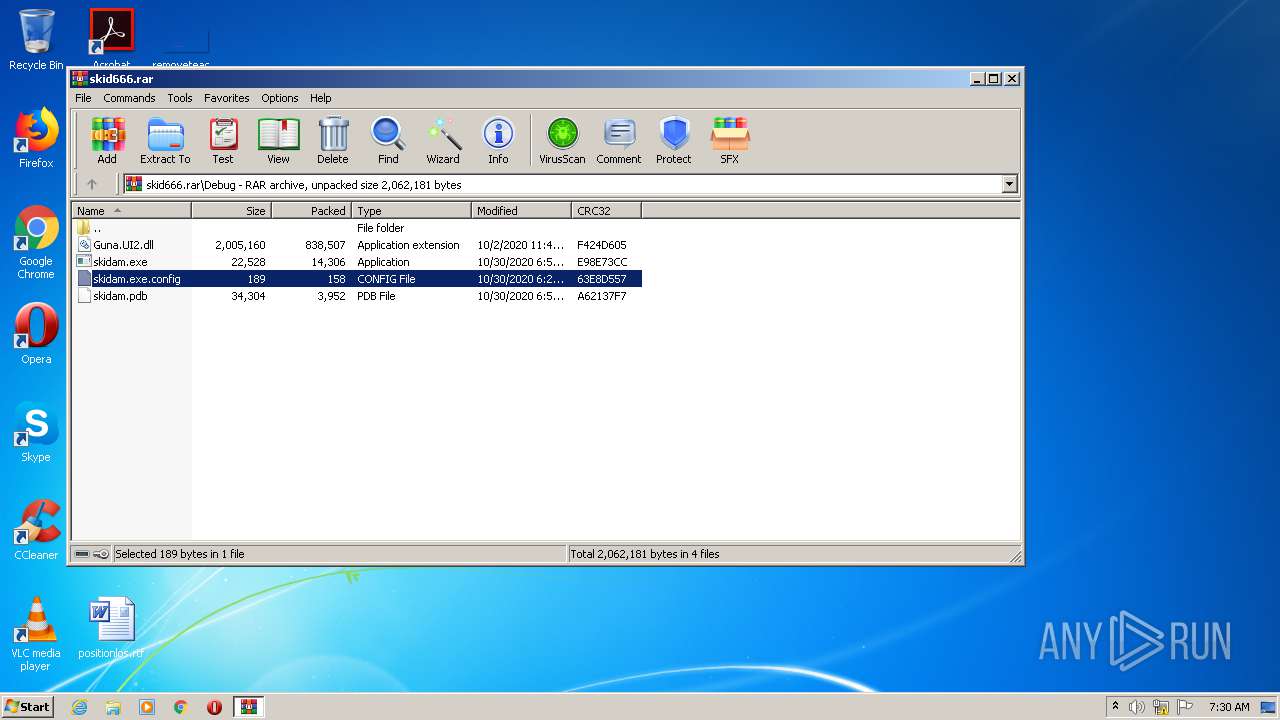
| File name: | skid666.rar |
| Full analysis: | https://app.any.run/tasks/b48d980f-2524-431d-93d8-4ea3705dc8ff |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 07:29:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | C3032D9FE0BC43B3185FD7957828ABB2 |
| SHA1: | 85EE026D85147C4B2FED7DD4C7E2C0E2E4BB9318 |
| SHA256: | FD31F961E3D61102153D248B9466F7FD8237EAD2C0118892895637F49777870E |
| SSDEEP: | 24576:zINL/VsCYOTEBQmIZT7AX51l/1DQxQOxqbh:oCC/T1ZTEXFC6O0h |
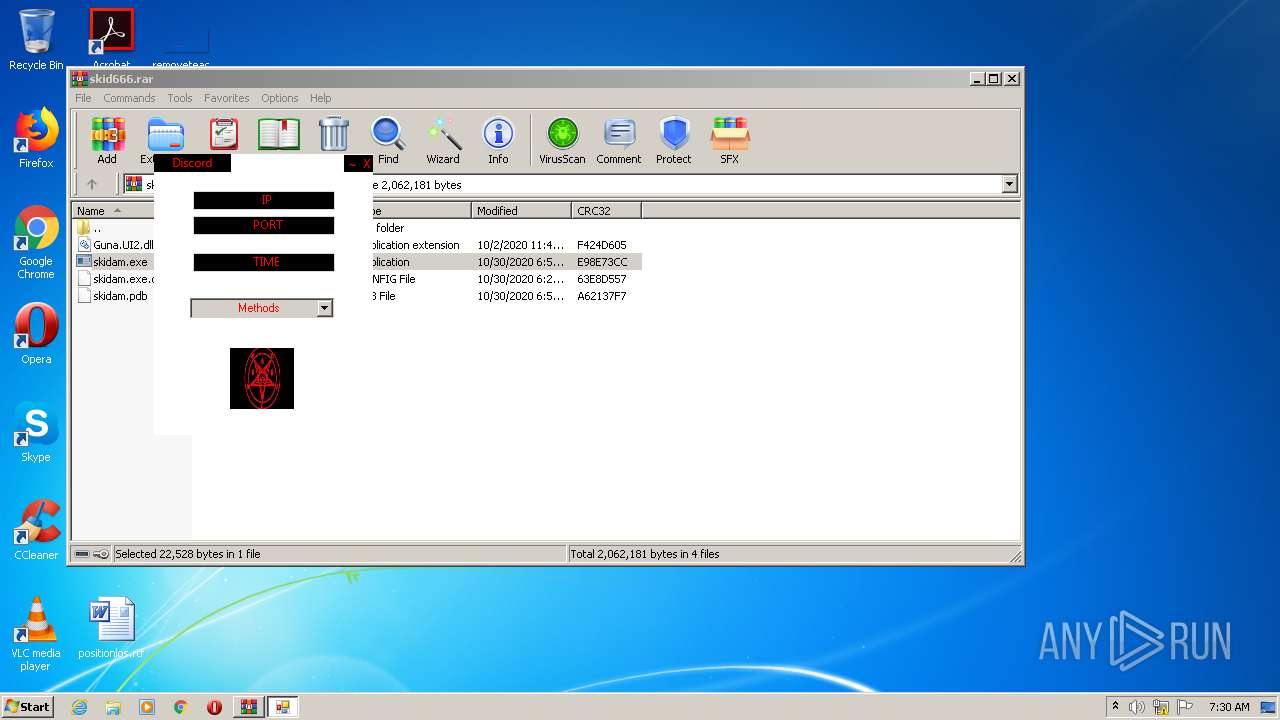
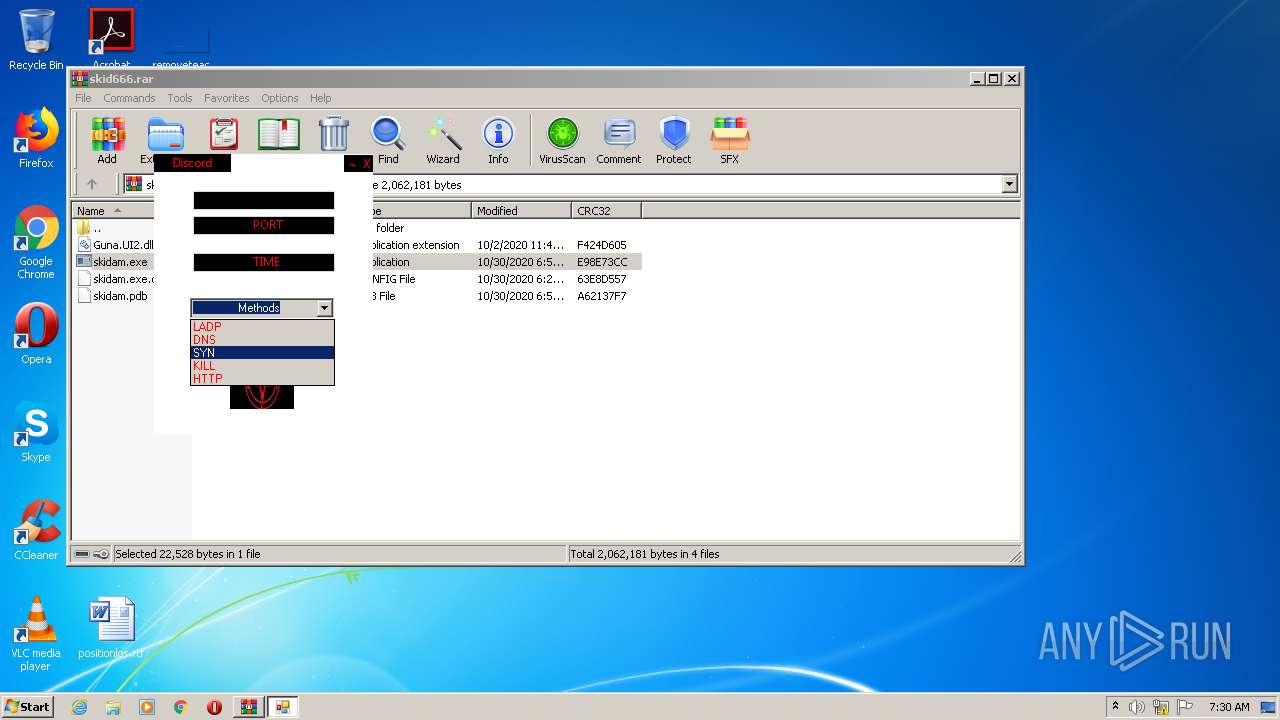
MALICIOUS
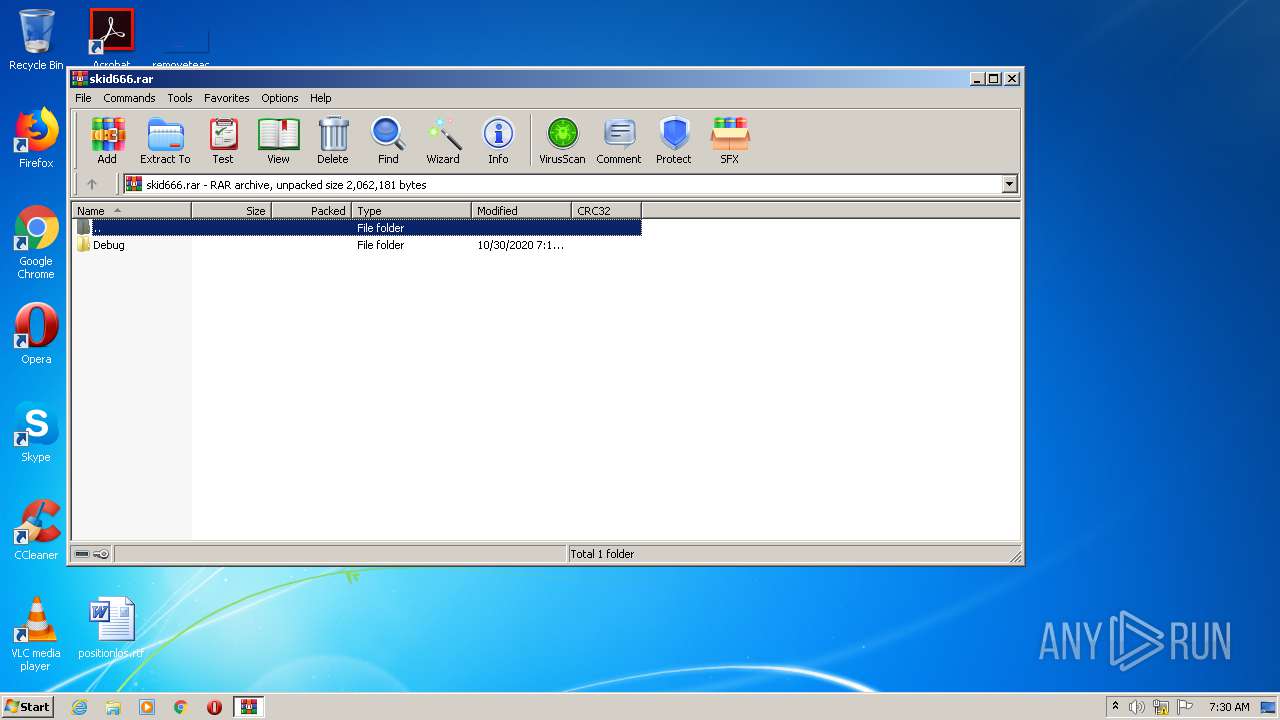
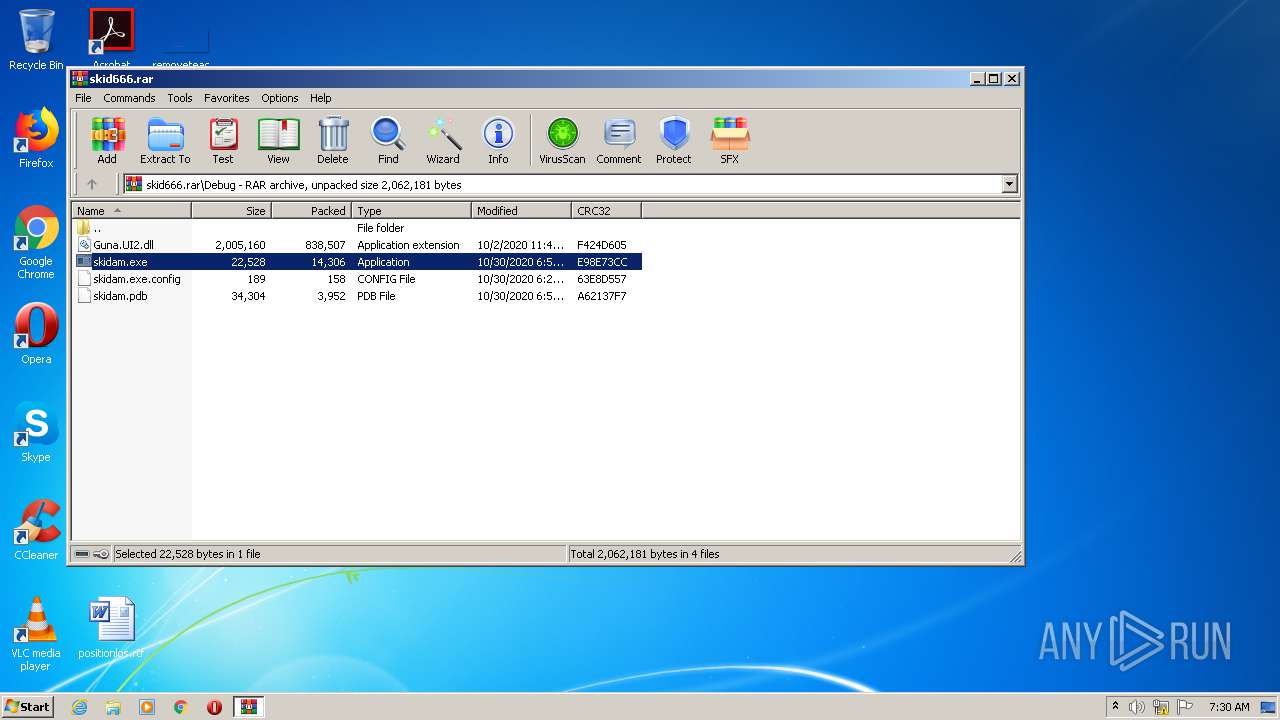
Drops executable file immediately after starts
- skidam.exe (PID: 2704)
Application was dropped or rewritten from another process
- skidam.exe (PID: 2704)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2172)
- skidam.exe (PID: 2704)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2172)
- skidam.exe (PID: 2704)
Drops a file with too old compile date
- WinRAR.exe (PID: 2172)
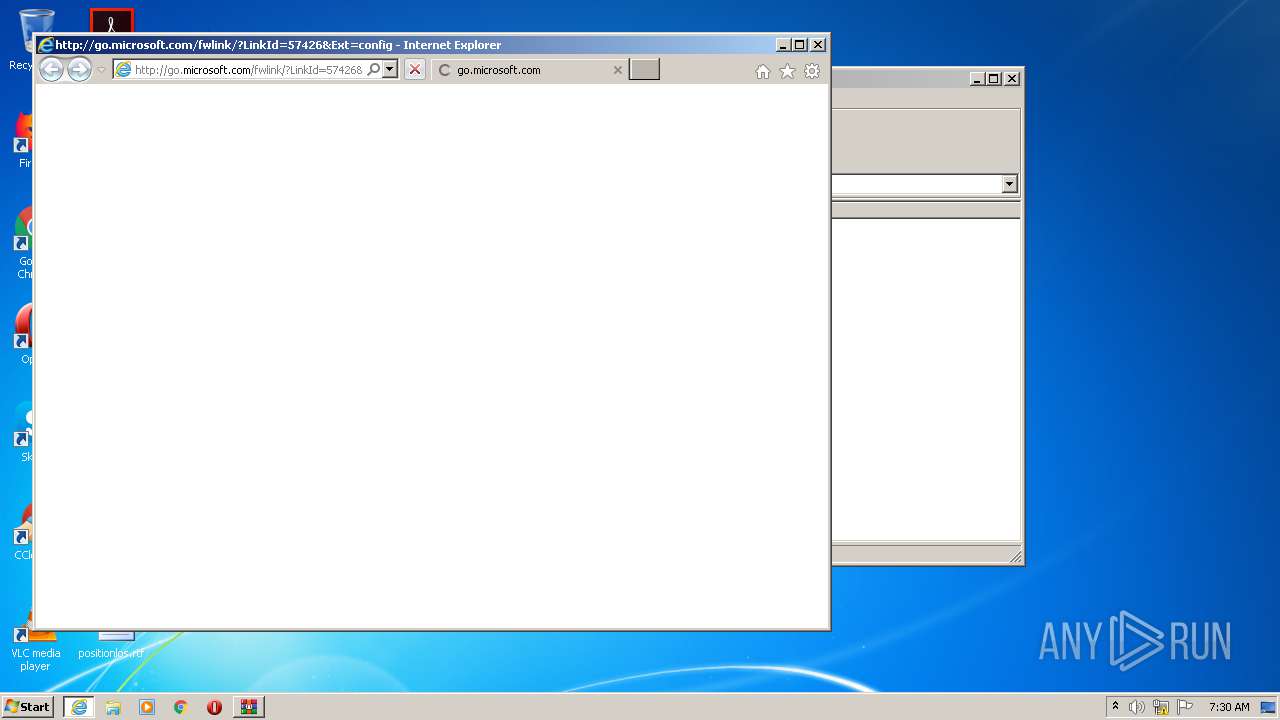
Starts Internet Explorer
- rundll32.exe (PID: 3180)
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 2172)
INFO
Reads settings of System Certificates
- iexplore.exe (PID: 2500)
- iexplore.exe (PID: 1028)
Application launched itself
- iexplore.exe (PID: 1028)
Changes internet zones settings
- iexplore.exe (PID: 1028)
Reads internet explorer settings
- iexplore.exe (PID: 2500)
Creates files in the user directory
- iexplore.exe (PID: 2500)
Changes settings of System certificates
- iexplore.exe (PID: 1028)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
39
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1028 | "C:\Program Files\Internet Explorer\iexplore.exe" http://go.microsoft.com/fwlink/?LinkId=57426&Ext=config | C:\Program Files\Internet Explorer\iexplore.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
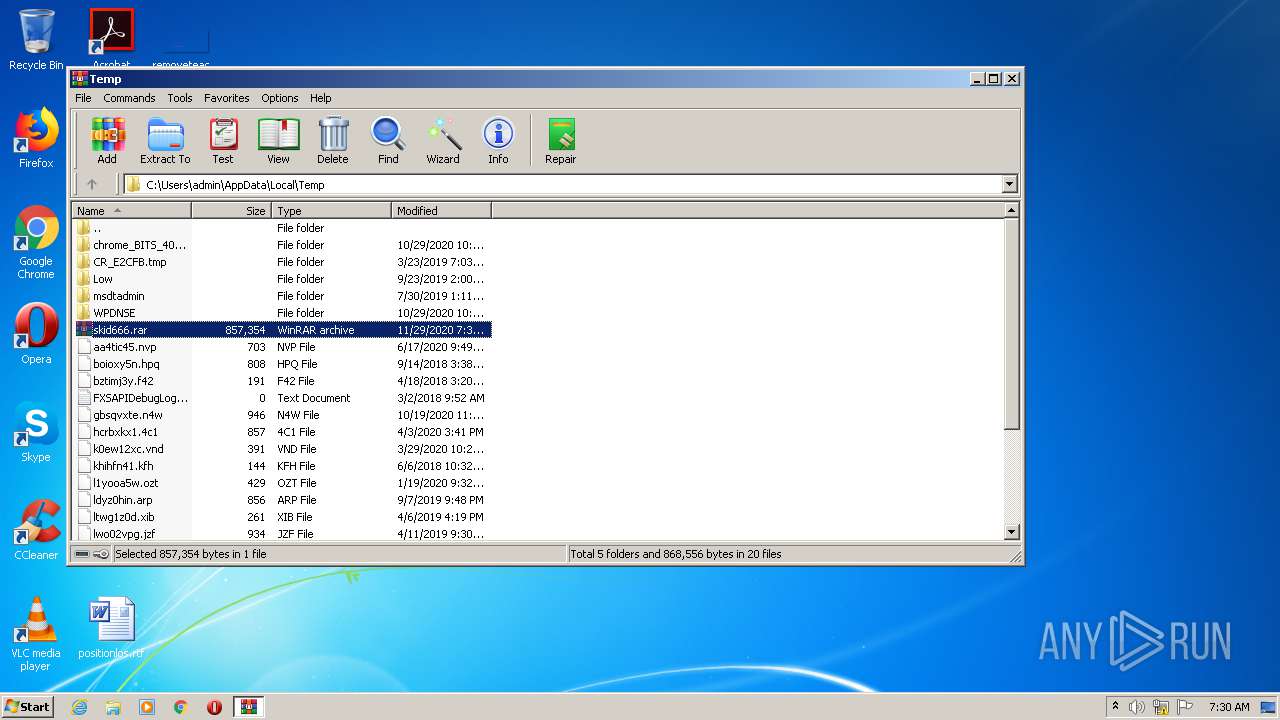
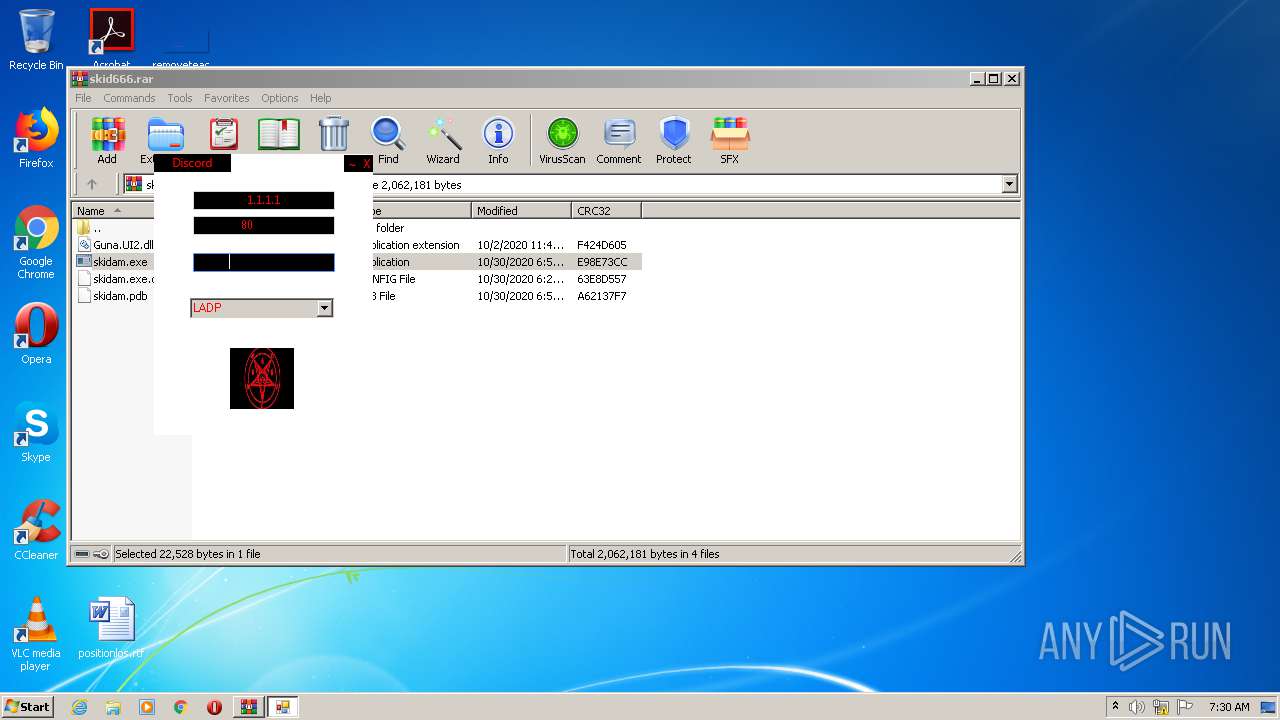
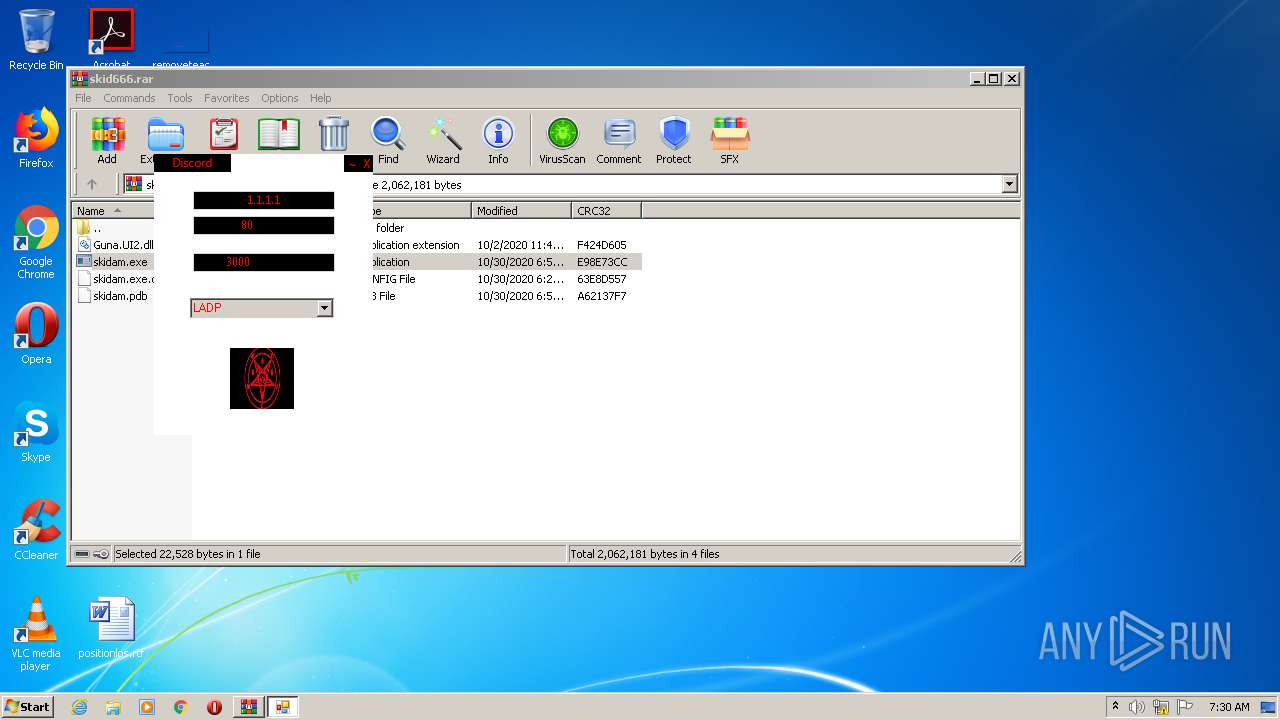
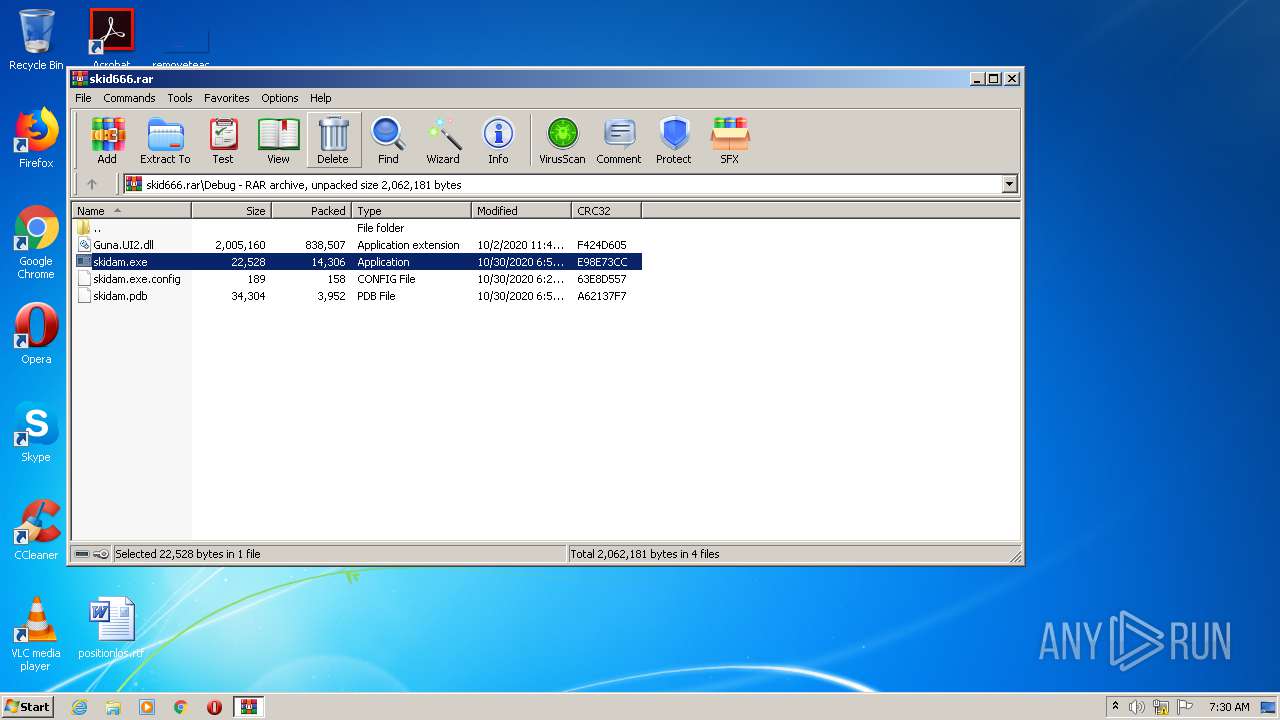
| 2172 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\skid666.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2500 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1028 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2704 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2172.34401\Debug\skidam.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2172.34401\Debug\skidam.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: skidam Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
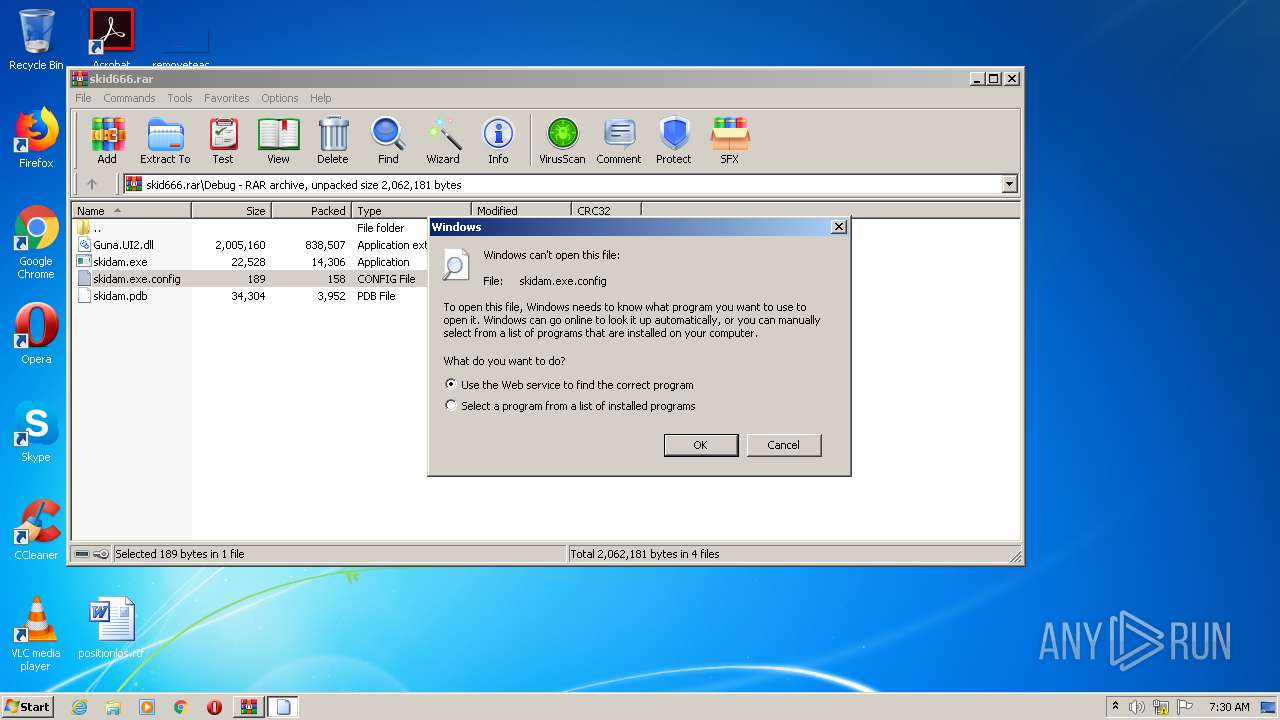
| 3180 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIa2172.38036\skidam.exe.config | C:\Windows\system32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 089
Read events
1 014
Write events
74
Delete events
1
Modification events
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\skid666.rar | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
3
Suspicious files
4
Text files
9
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2500 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab1FA2.tmp | — | |
MD5:— | SHA256:— | |||
| 2500 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar1FA3.tmp | — | |
MD5:— | SHA256:— | |||
| 2500 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\U4EL2K09.txt | — | |
MD5:— | SHA256:— | |||
| 2500 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\A47Q8MRL.txt | — | |
MD5:— | SHA256:— | |||
| 2500 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\A2E0CGRL.txt | — | |
MD5:— | SHA256:— | |||
| 2500 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\6VHM1J2X.txt | — | |
MD5:— | SHA256:— | |||
| 2172 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2172.34401\Debug\skidam.exe | executable | |
MD5:— | SHA256:— | |||
| 2172 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2172.34401\Debug\skidam.pdb | pdb | |
MD5:— | SHA256:— | |||
| 2500 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 2500 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\5K1DBU0U.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
14
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2500 | iexplore.exe | GET | 302 | 23.43.214.226:80 | http://go.microsoft.com/fwlink/?LinkId=57426&Ext=config | US | — | — | whitelisted |
2500 | iexplore.exe | GET | 301 | 92.122.188.58:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=config | unknown | — | — | whitelisted |
2500 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 471 b | whitelisted |
2500 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 92.122.188.58:80 | shell.windows.com | NTT America, Inc. | — | unknown |
— | — | 23.43.214.226:80 | go.microsoft.com | Akamai International B.V. | US | malicious |
2500 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2500 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1028 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
shell.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |