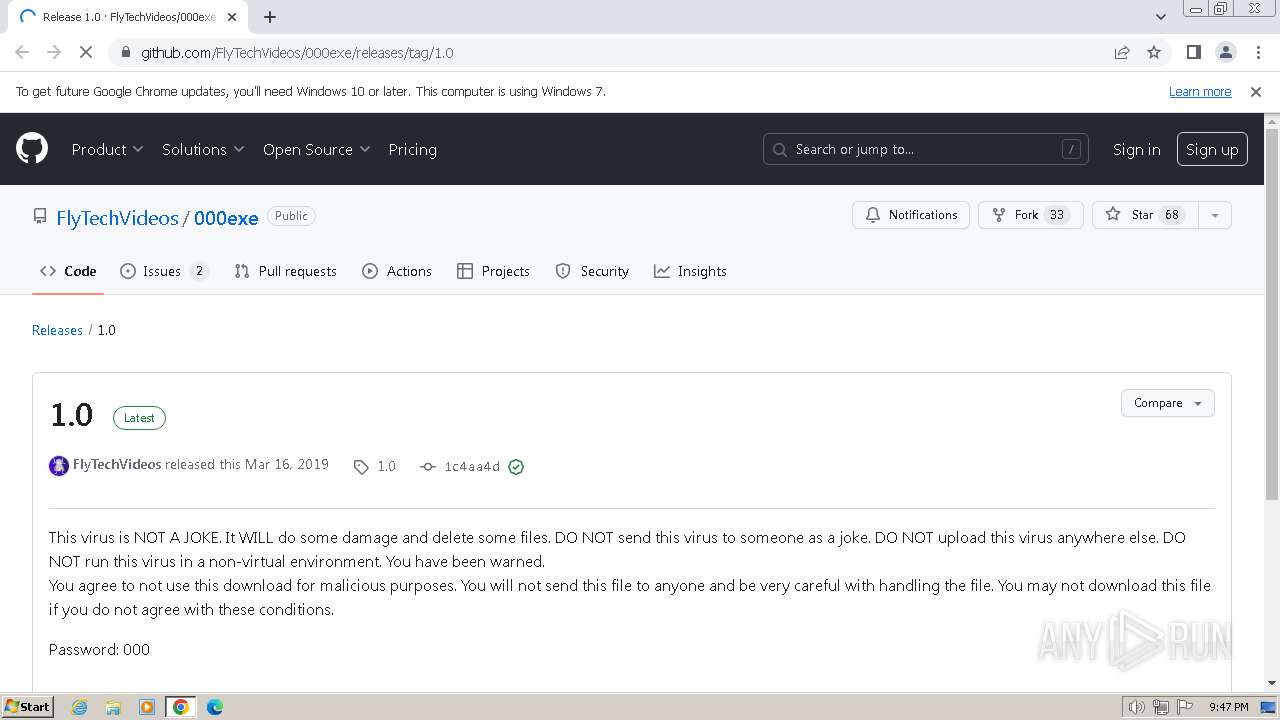
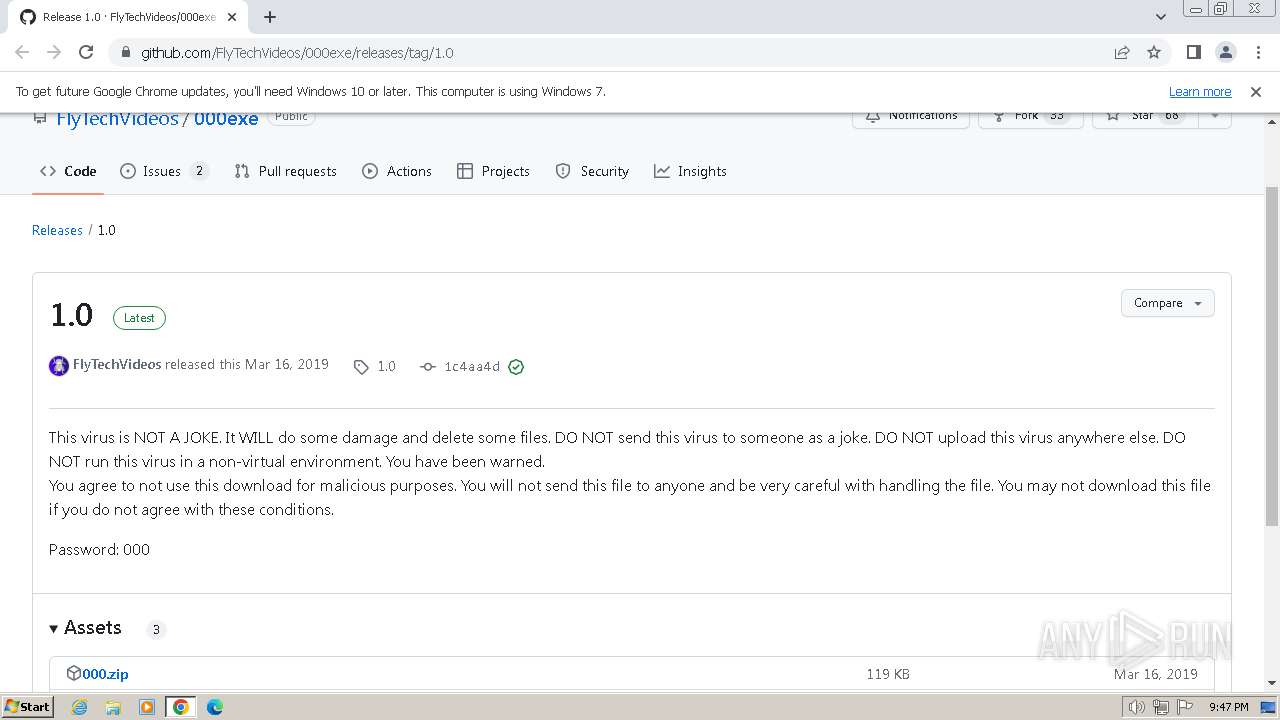
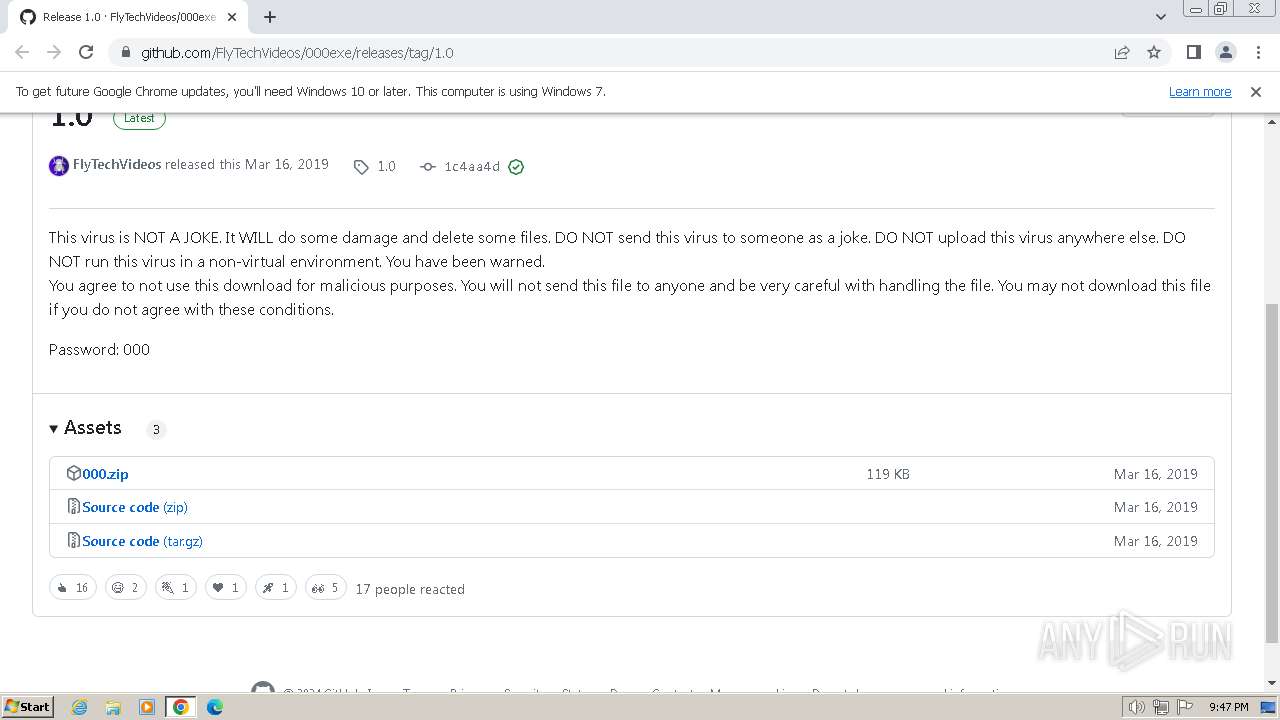
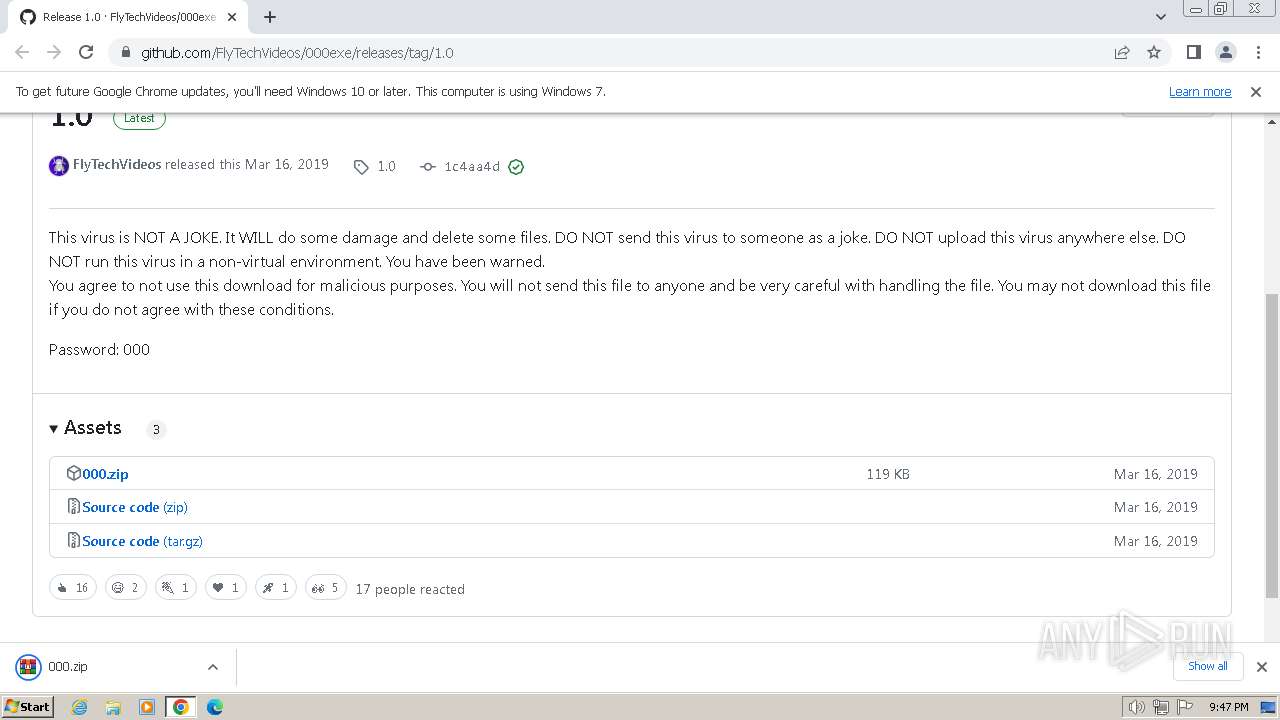
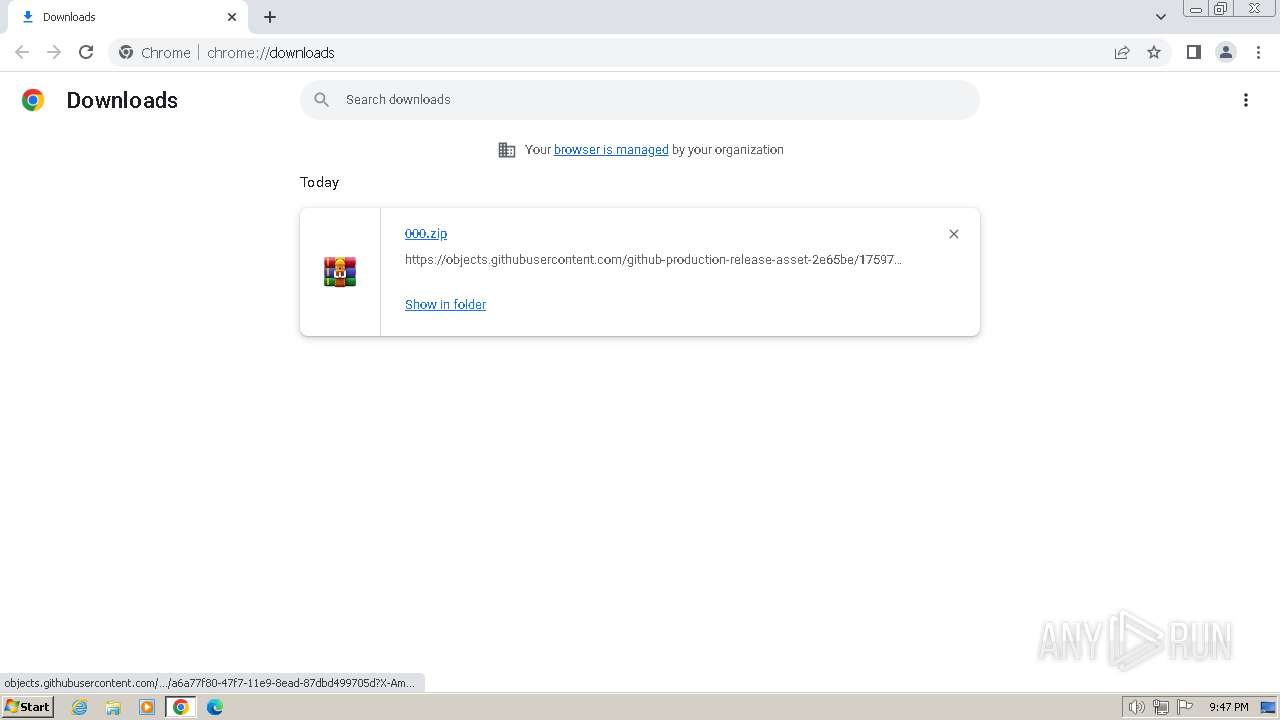
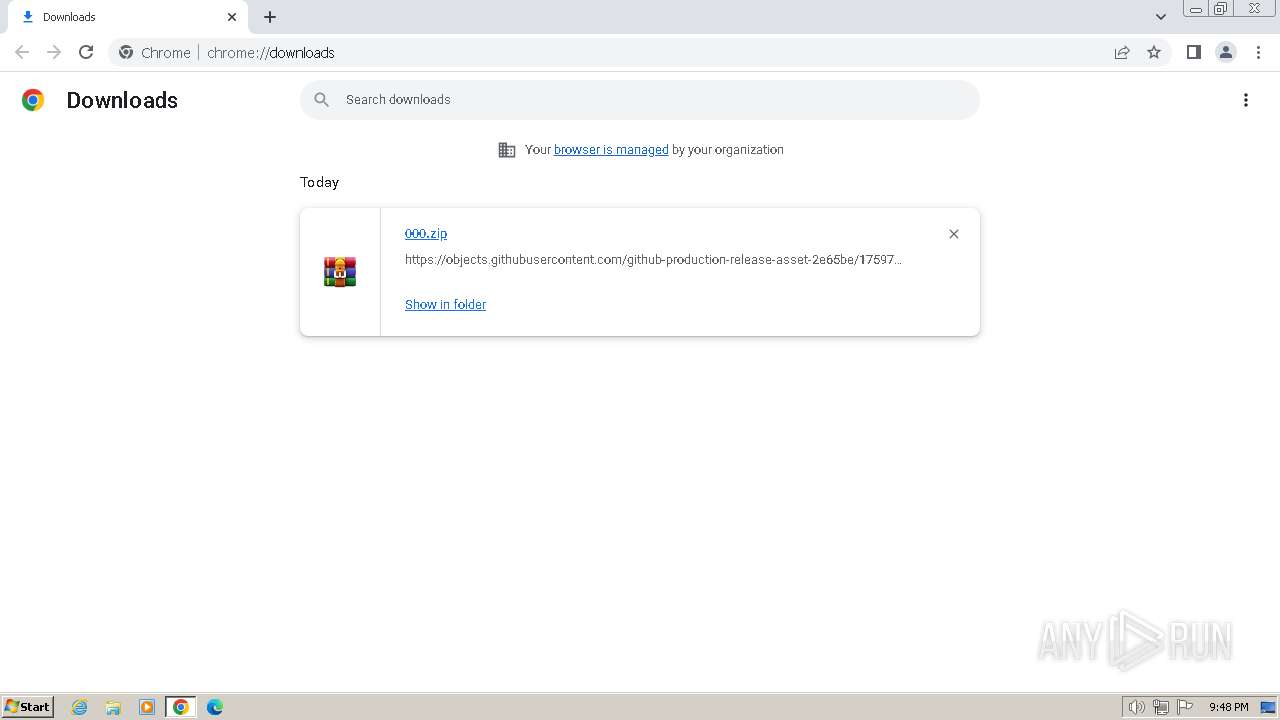
| URL: | https://github.com/FlyTechVideos/000exe/releases/tag/1.0 |
| Full analysis: | https://app.any.run/tasks/c157d8bd-b614-4d21-8385-0a8bd575cc42 |
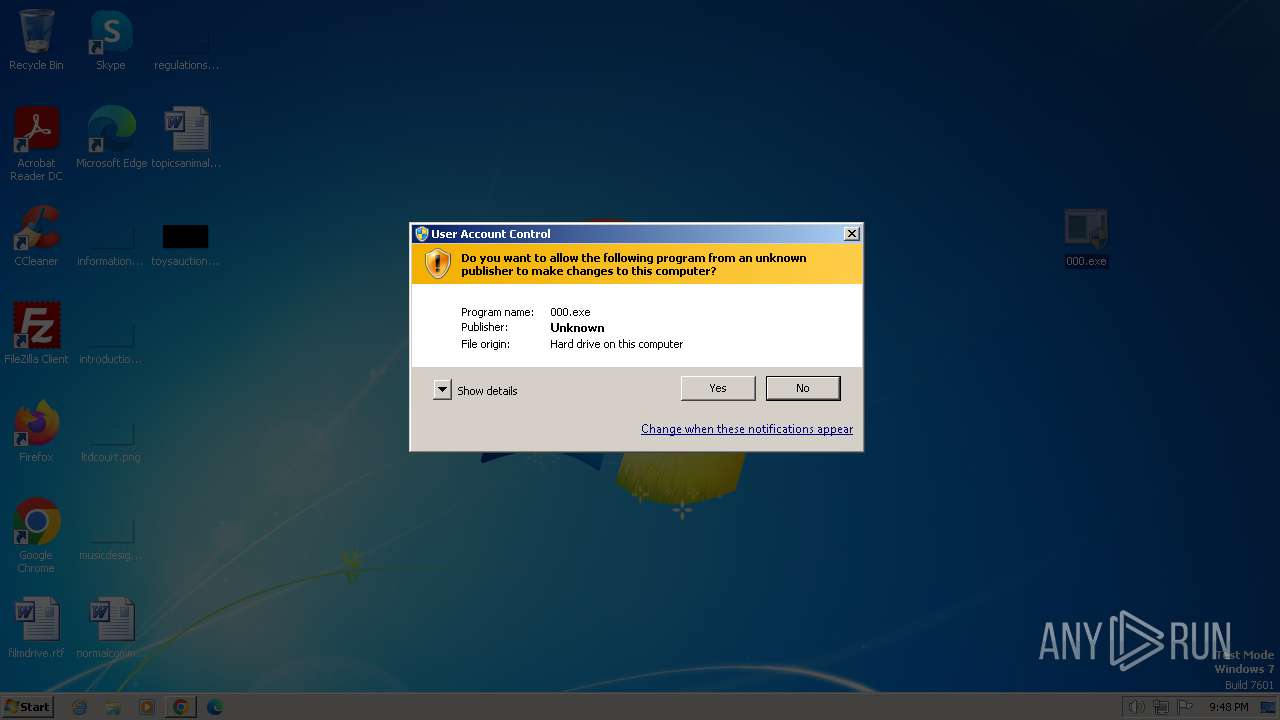
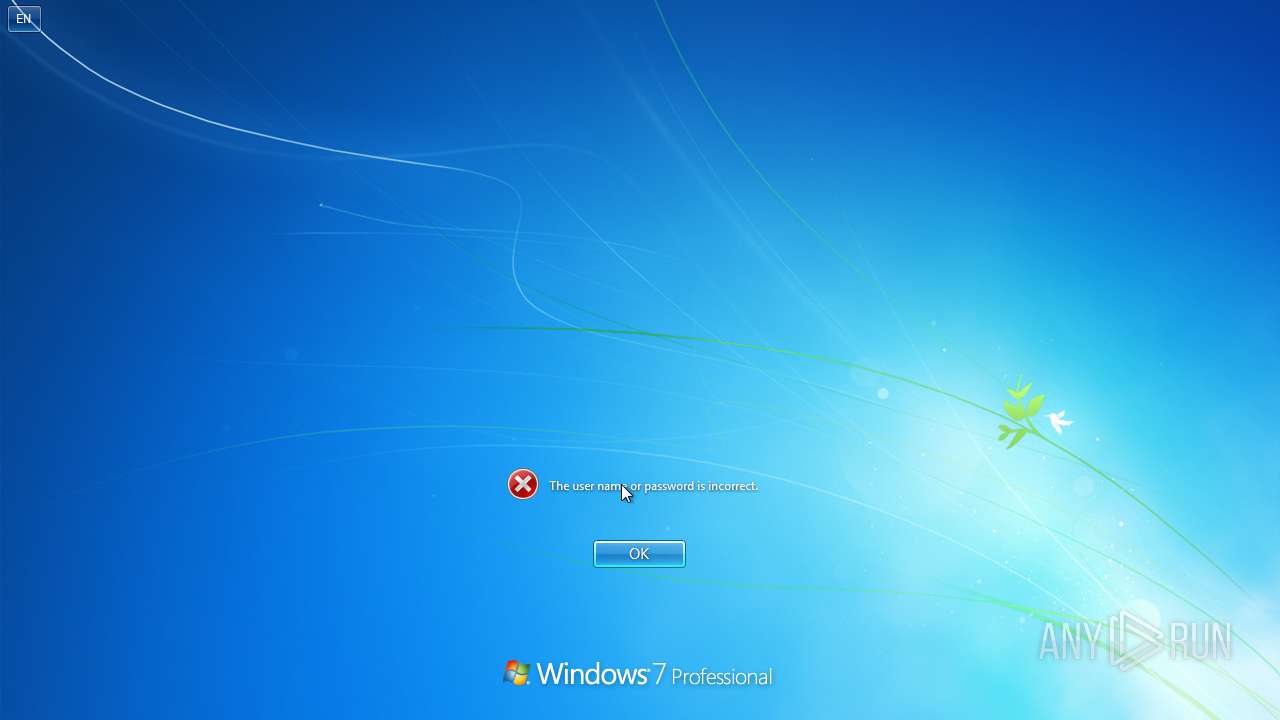
| Verdict: | Malicious activity |
| Analysis date: | February 15, 2024, 21:47:21 |
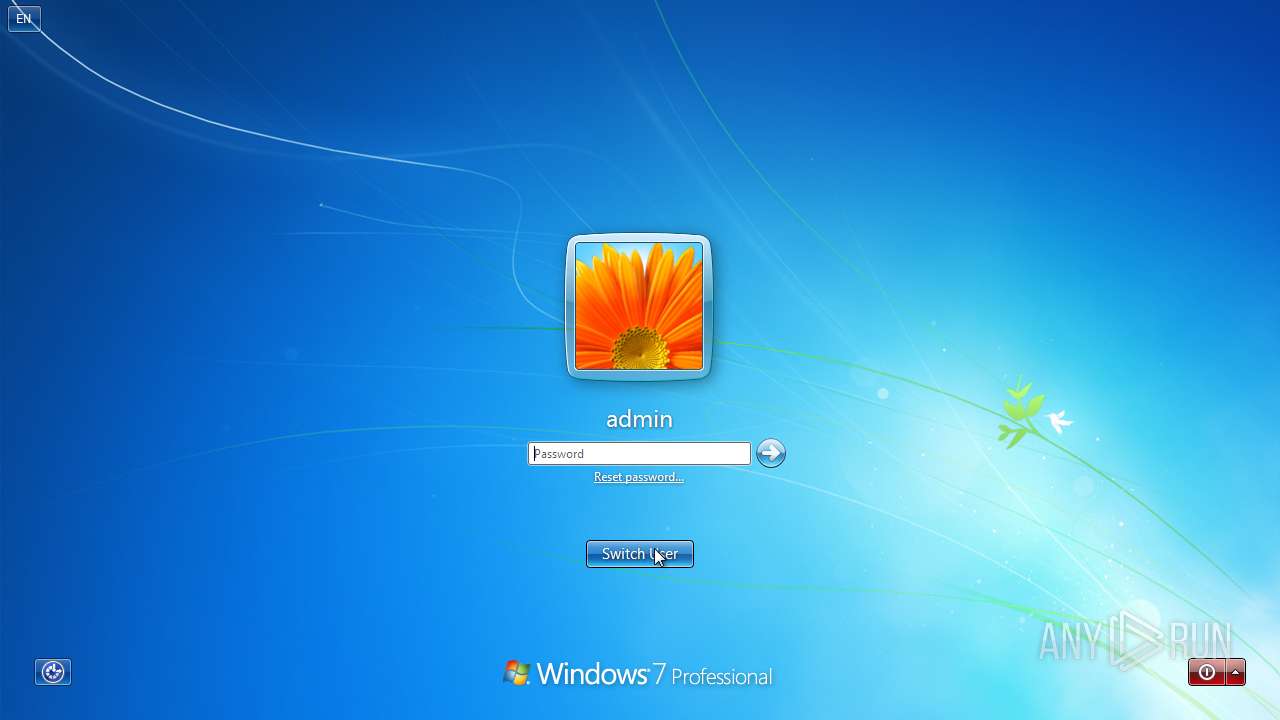
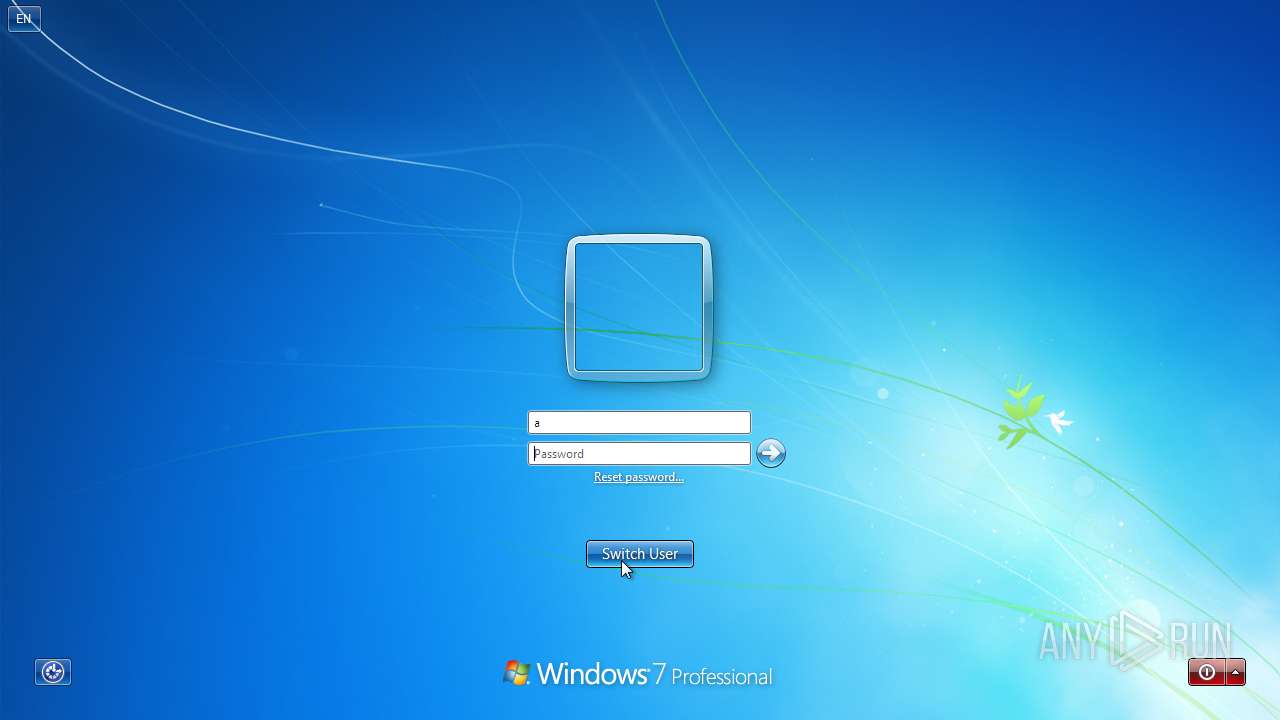
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 784AC523A497E4431CE5117BF79D20FA |
| SHA1: | 99A36FC063C67FE11B4214317CD4FF97C7E34F9D |
| SHA256: | FD2D8D3ECCCC4B363FE42E966D0DC3865E2C5818F77830C520353ACAEA518928 |
| SSDEEP: | 3:N8tEdFlagBAN6mAMsArqKmn:2uQSMdxm |
MALICIOUS
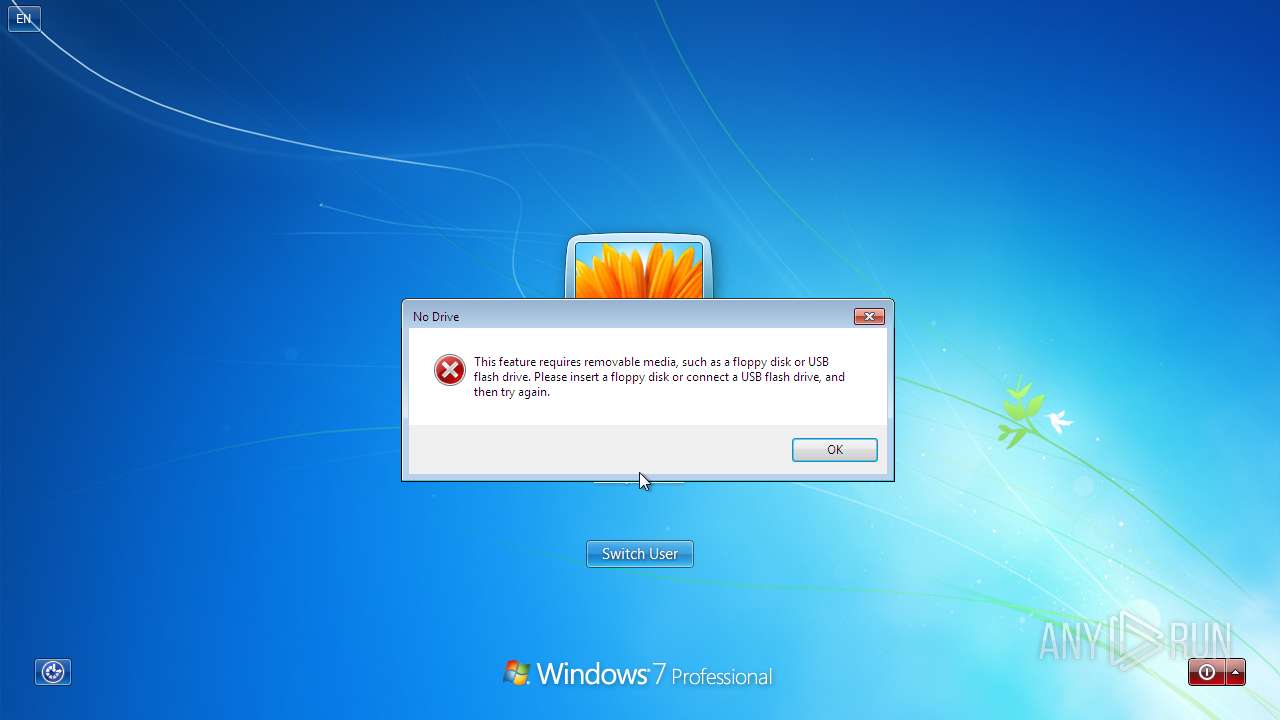
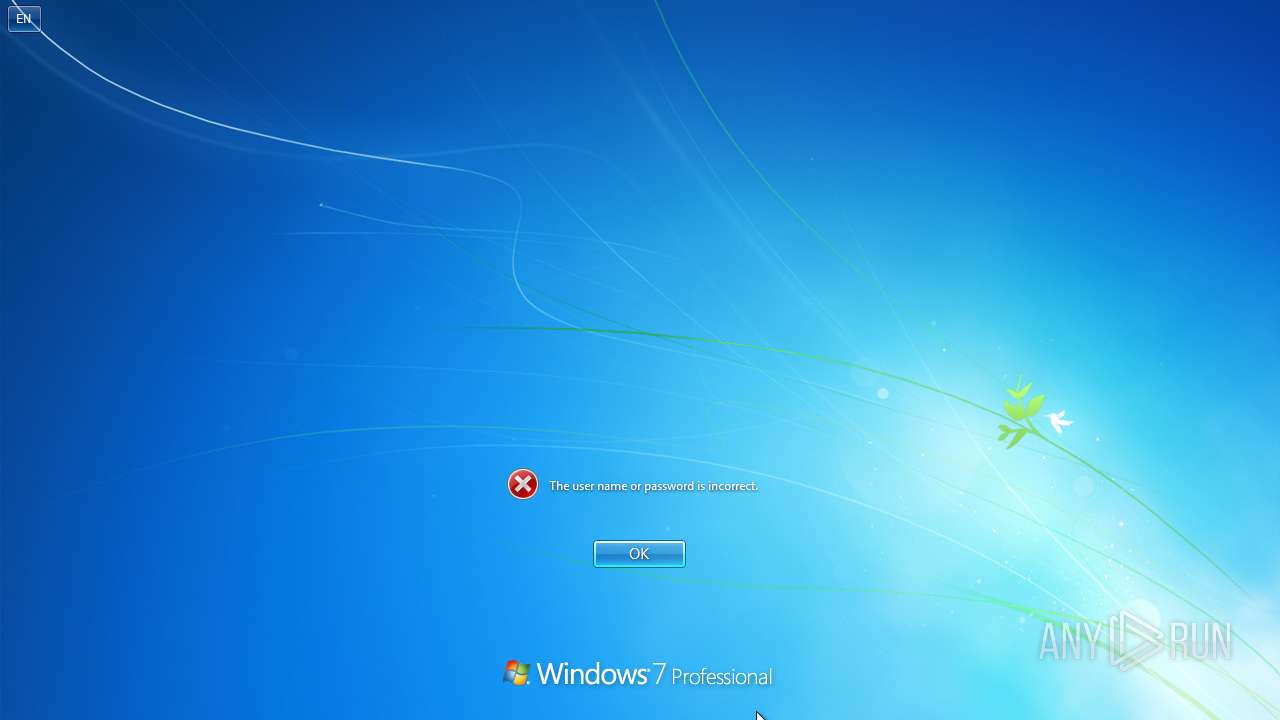
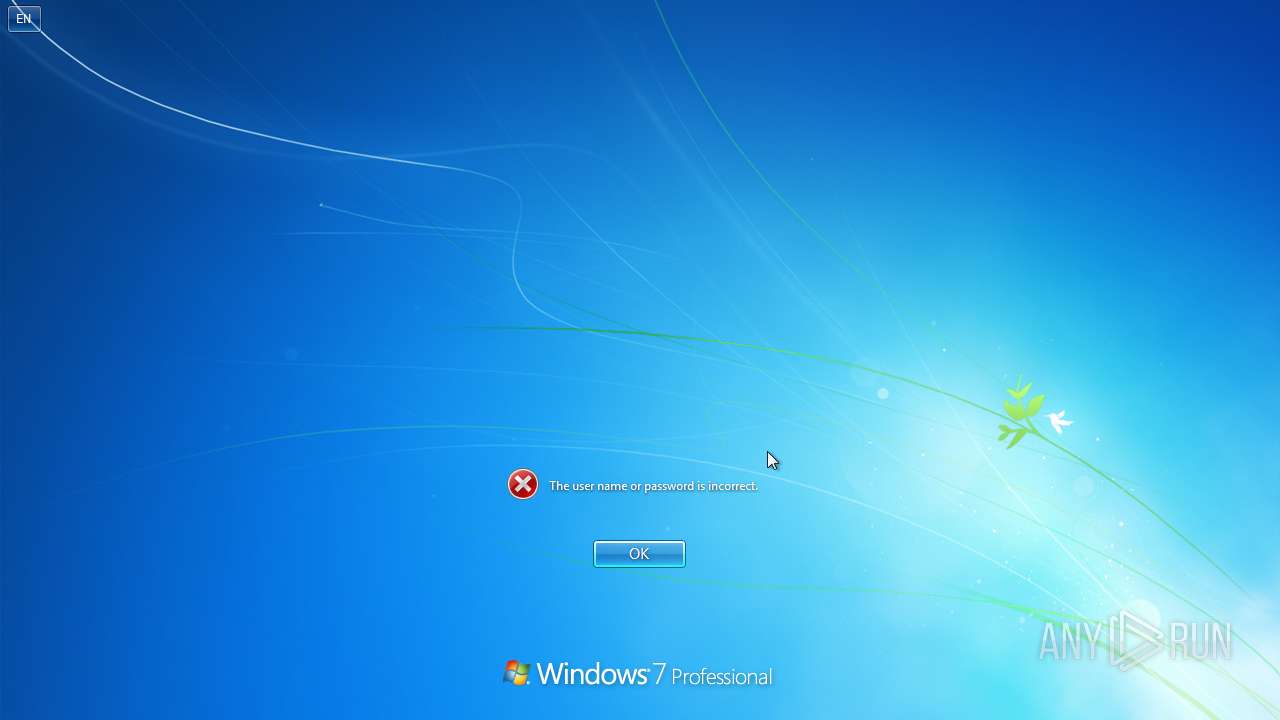
Changes the login/logoff helper path in the registry
- 000.exe (PID: 1380)
Drops the executable file immediately after the start
- 000.exe (PID: 1380)
- cmd.exe (PID: 2736)
Create files in the Startup directory
- cmd.exe (PID: 2736)
SUSPICIOUS
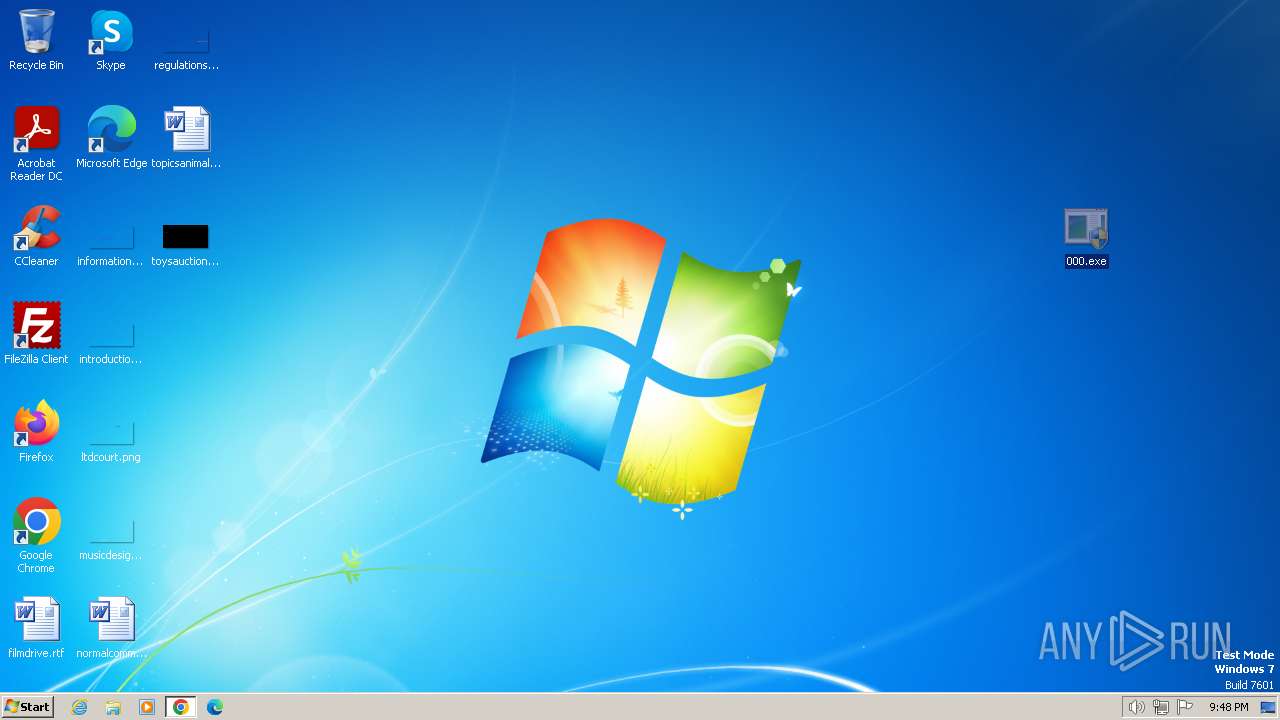
Changes the desktop background image
- 000.exe (PID: 1380)
Starts CMD.EXE for commands execution
- 000.exe (PID: 1380)
Executing commands from a ".bat" file
- 000.exe (PID: 1380)
Executable content was dropped or overwritten
- 000.exe (PID: 1380)
- cmd.exe (PID: 2736)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2736)
Reads security settings of Internet Explorer
- 000.exe (PID: 1380)
Reads the Internet Settings
- 000.exe (PID: 1380)
- WMIC.exe (PID: 3380)
- WMIC.exe (PID: 2524)
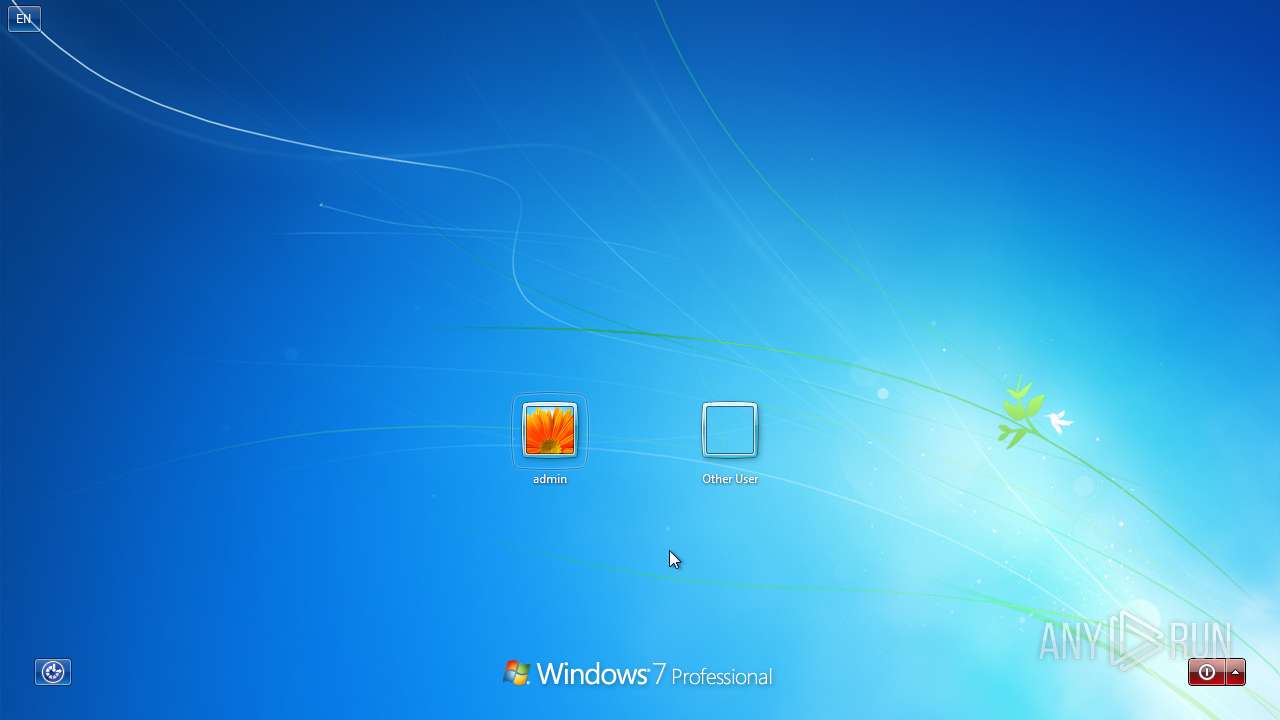
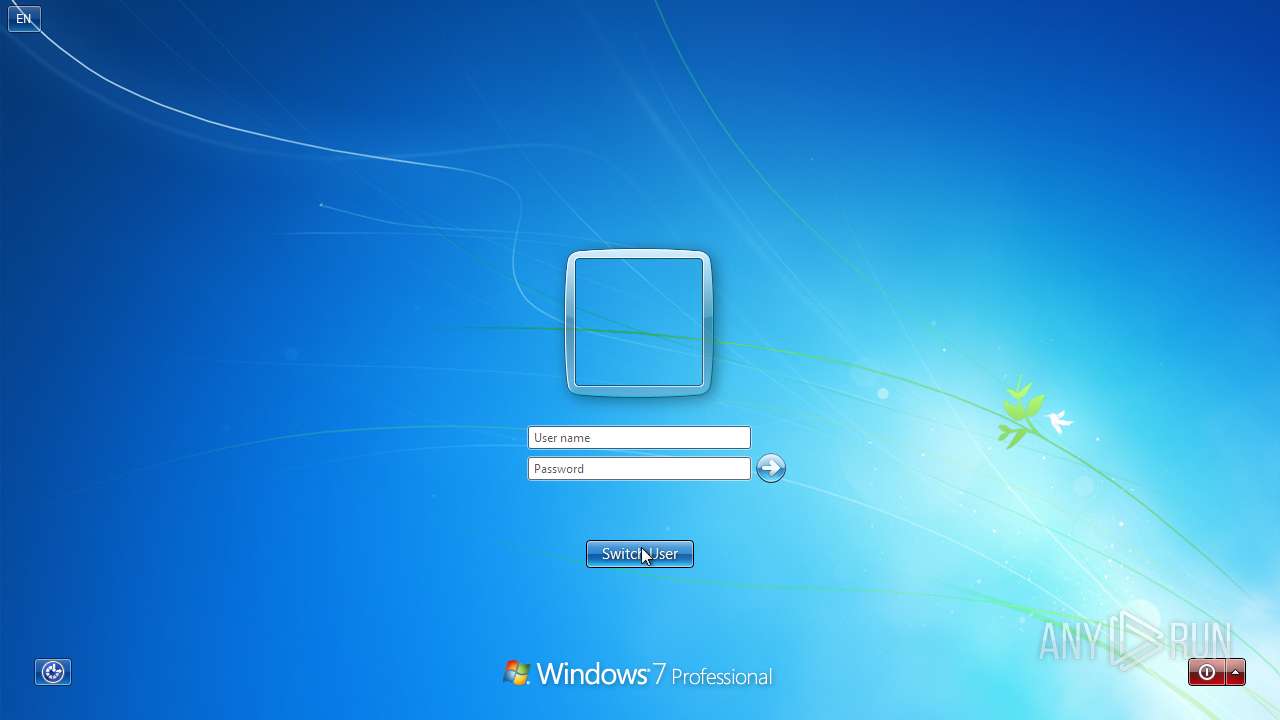
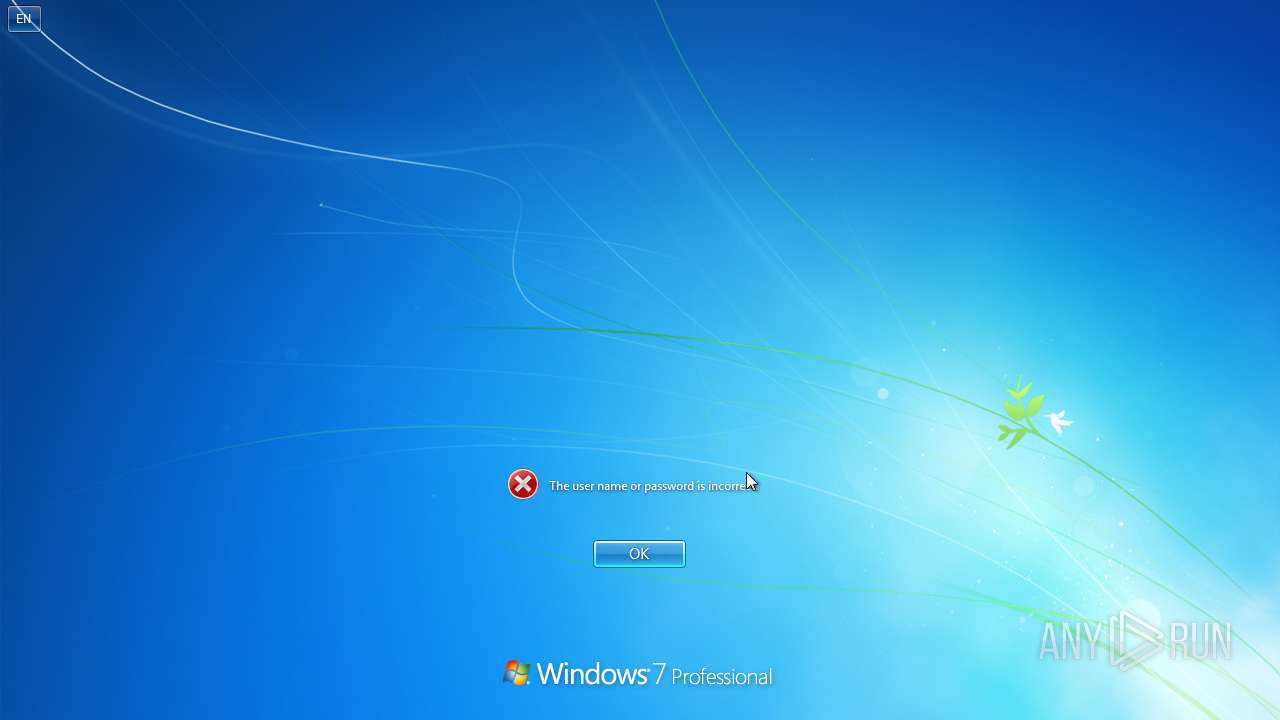
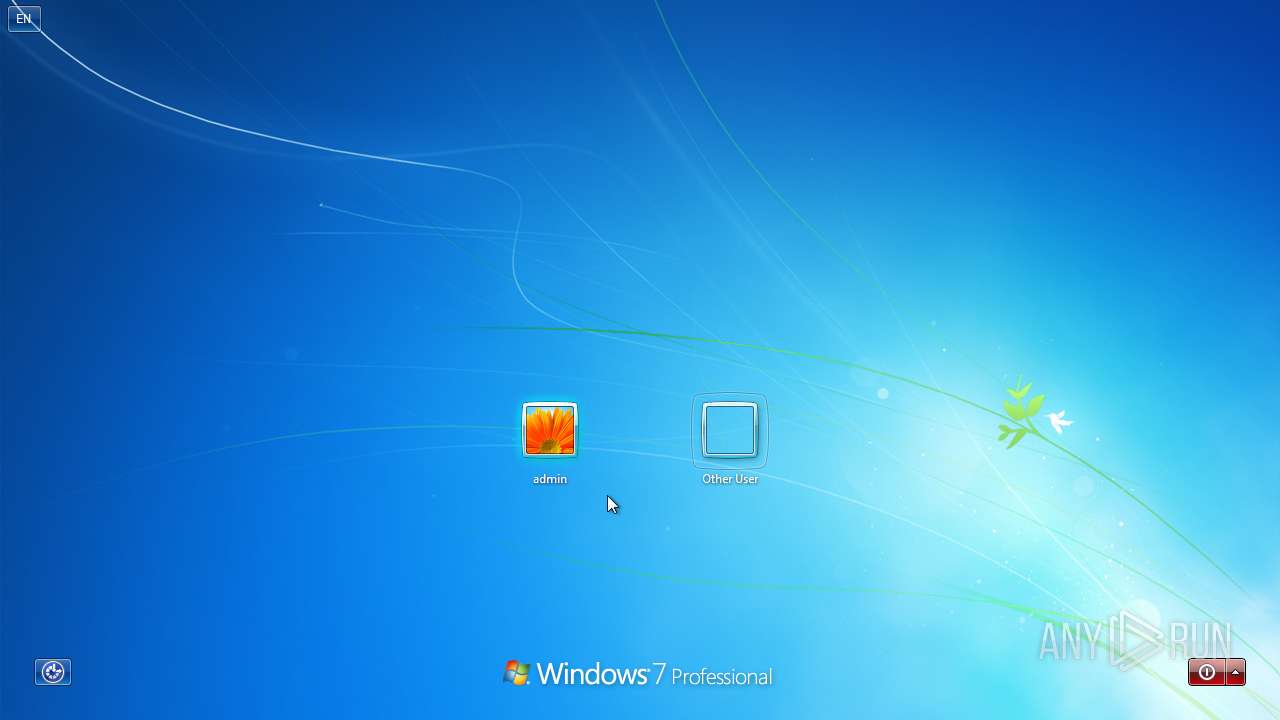
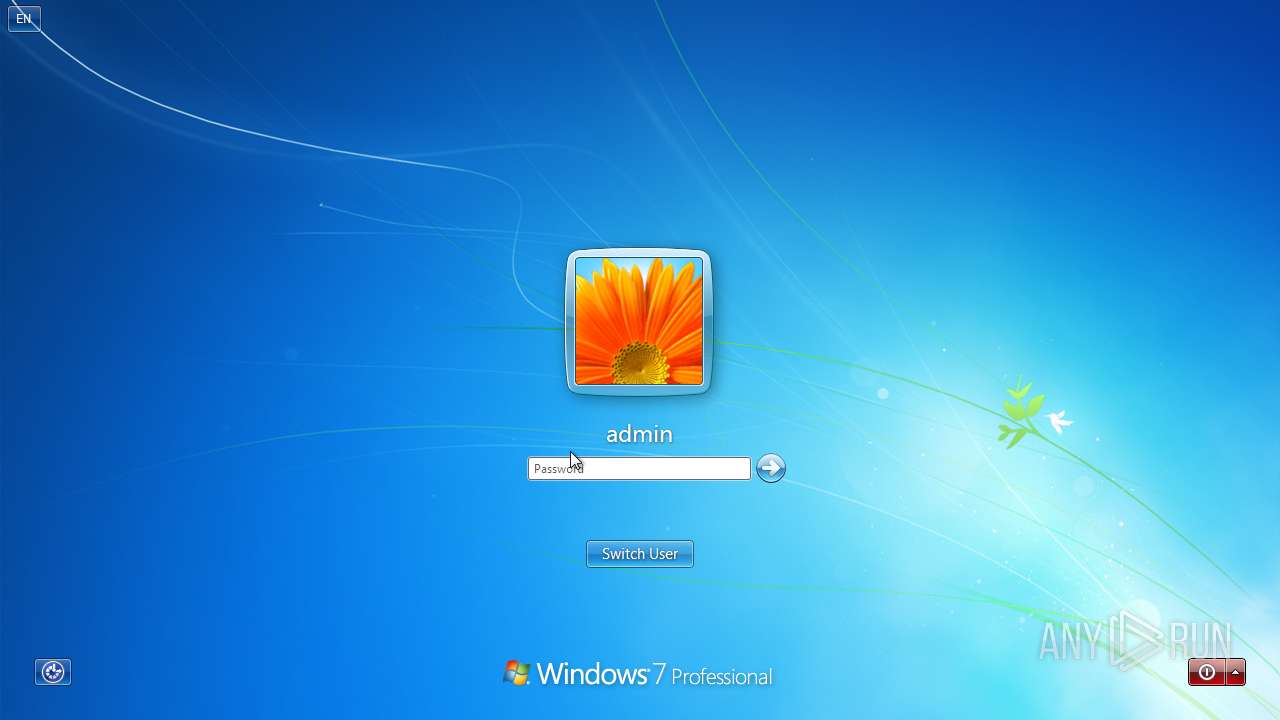
Uses WMIC.EXE to obtain user accounts information
- cmd.exe (PID: 2736)
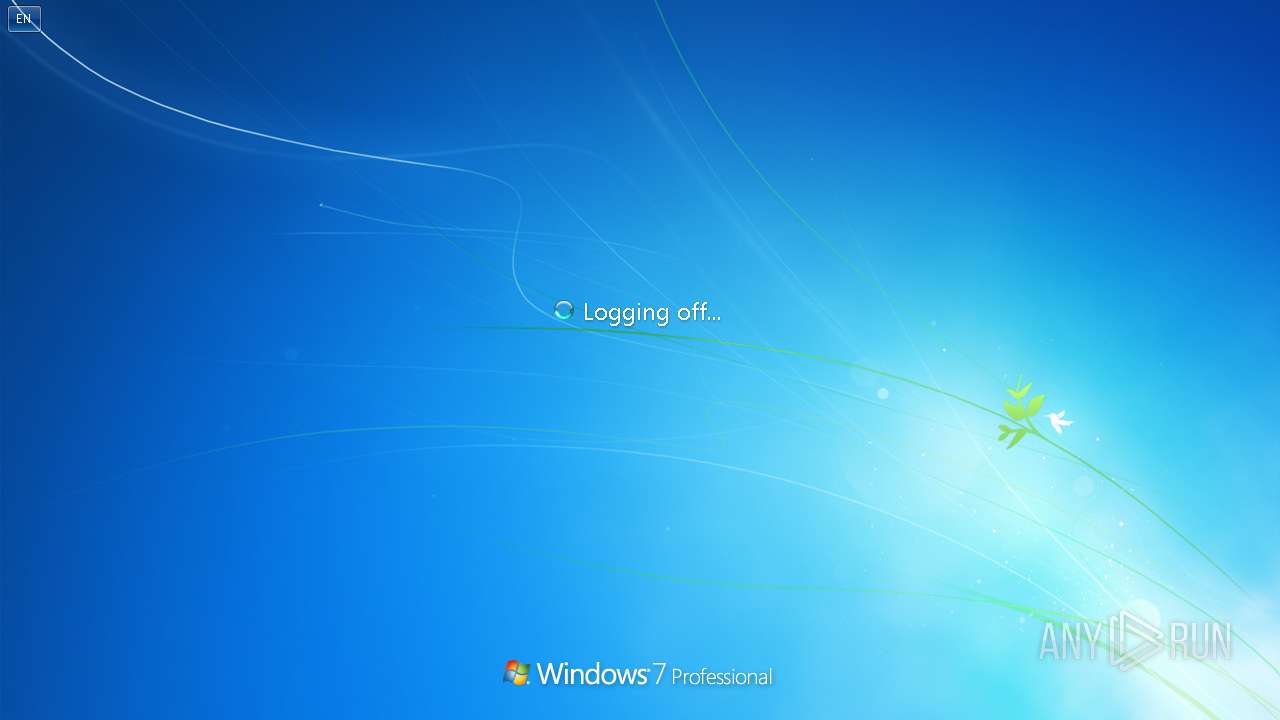
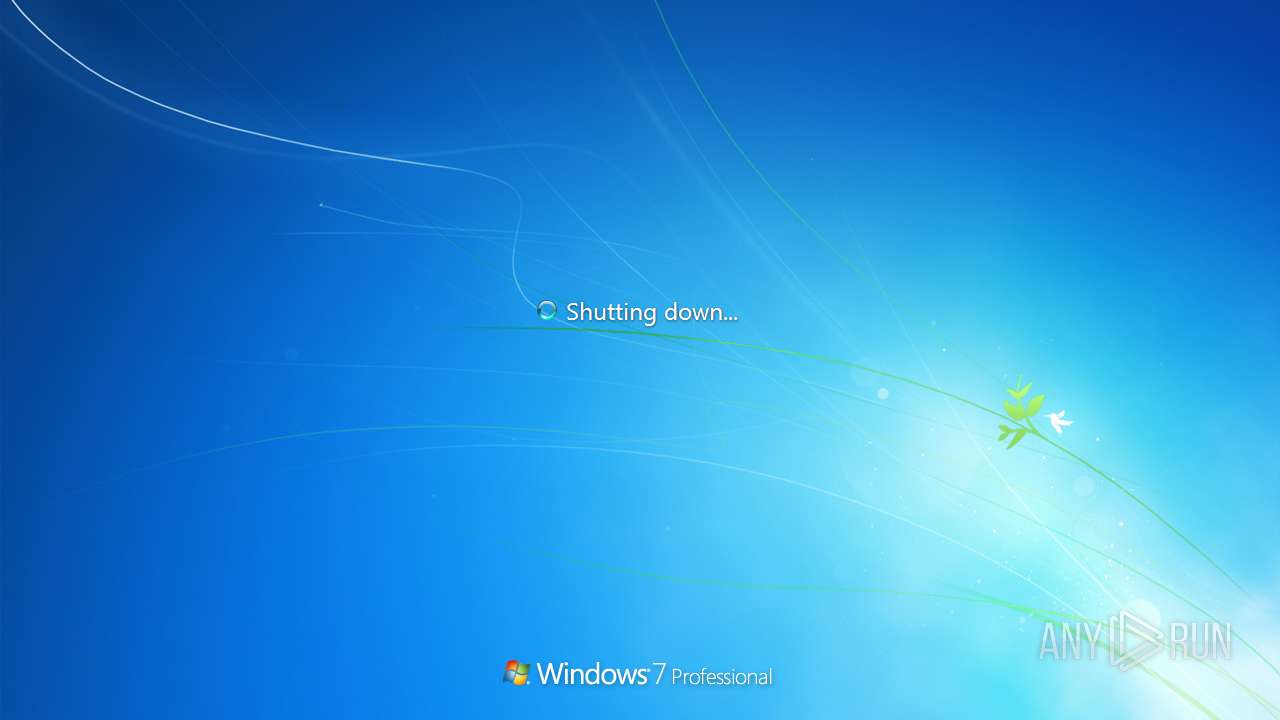
The system shut down or reboot
- cmd.exe (PID: 2736)
INFO
Application launched itself
- chrome.exe (PID: 3240)
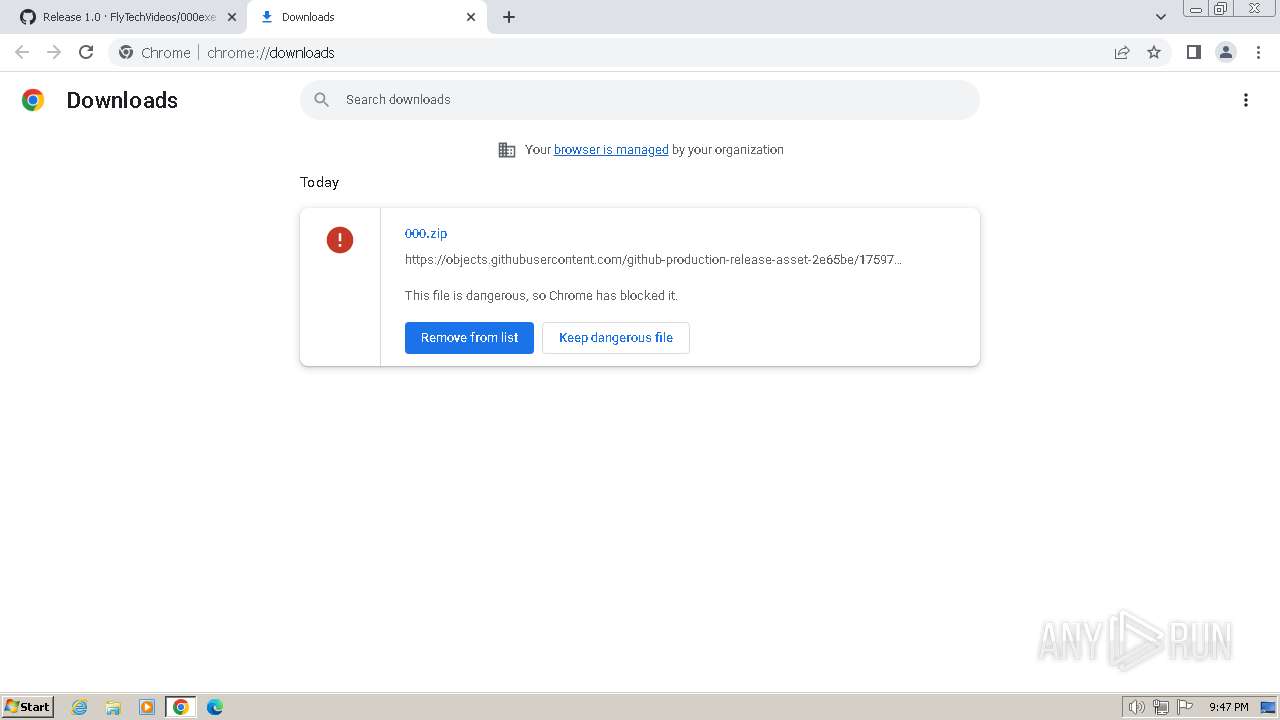
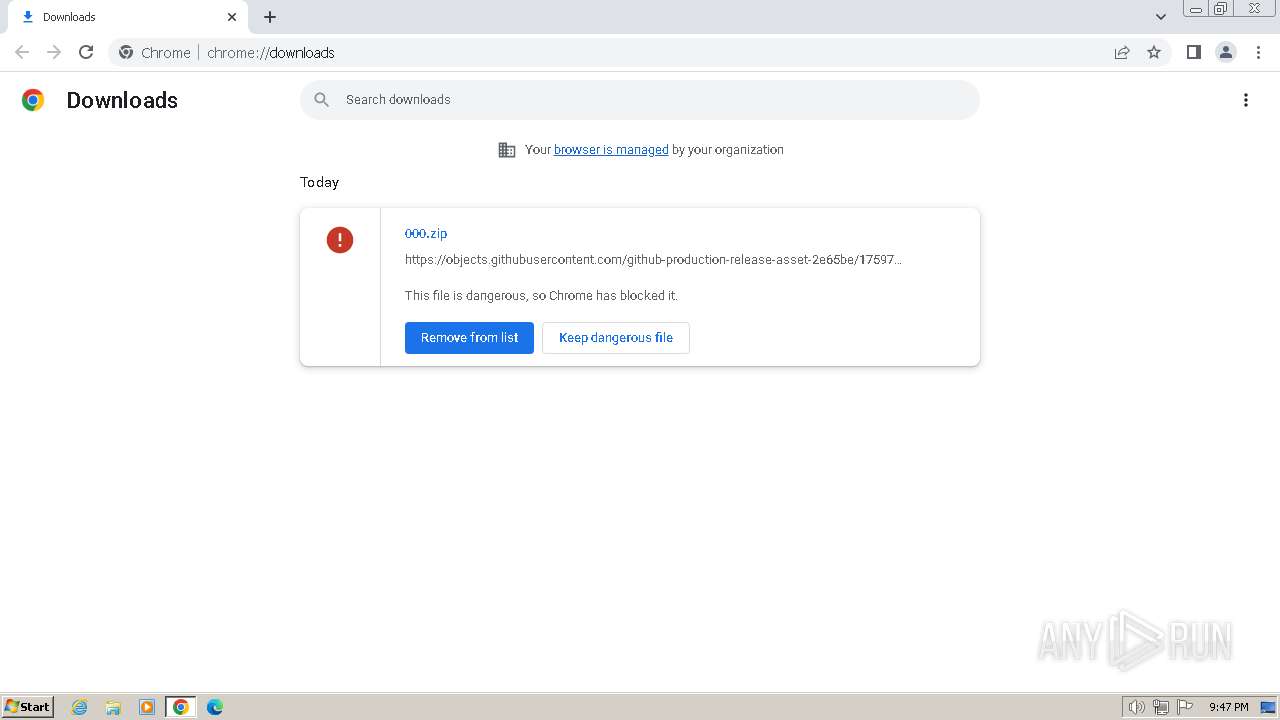
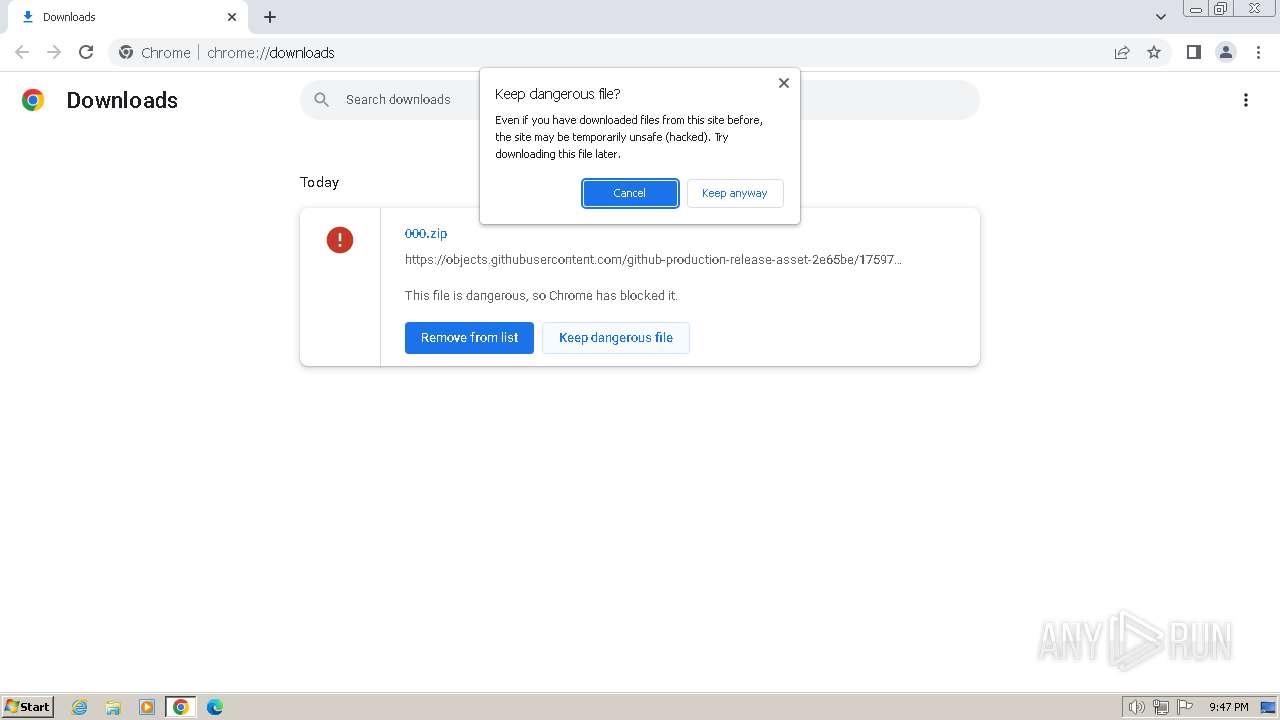
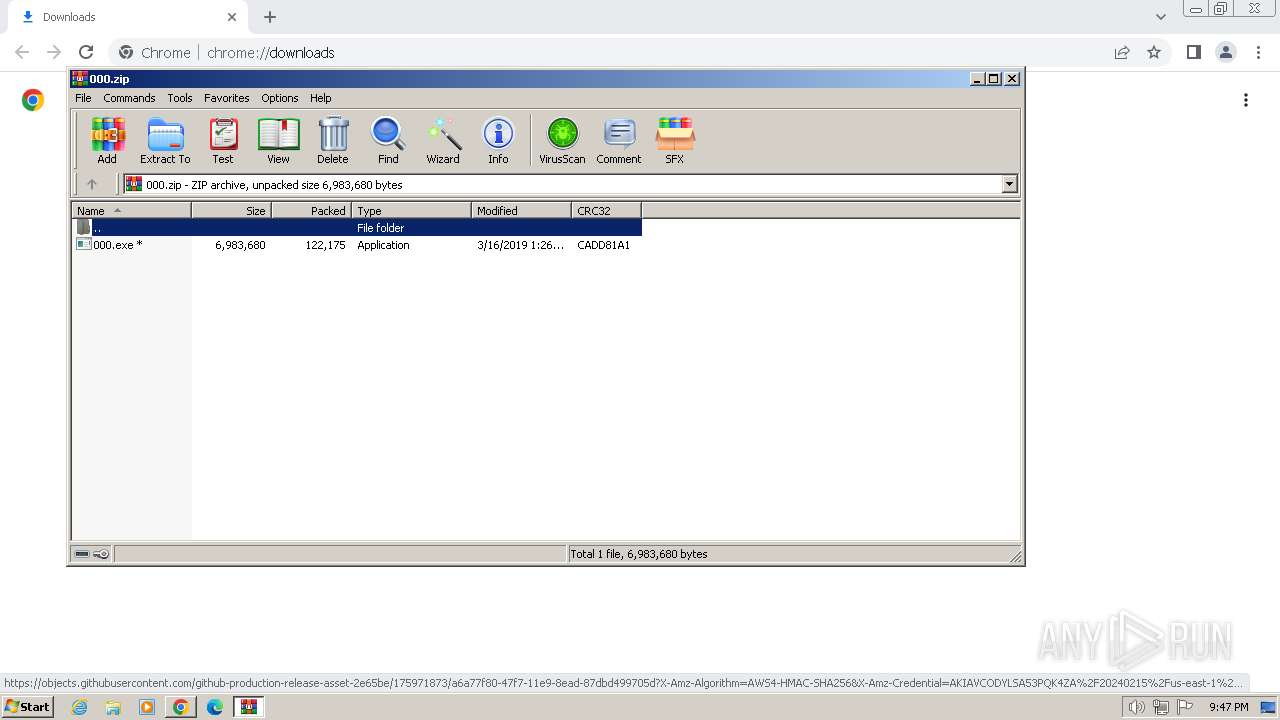
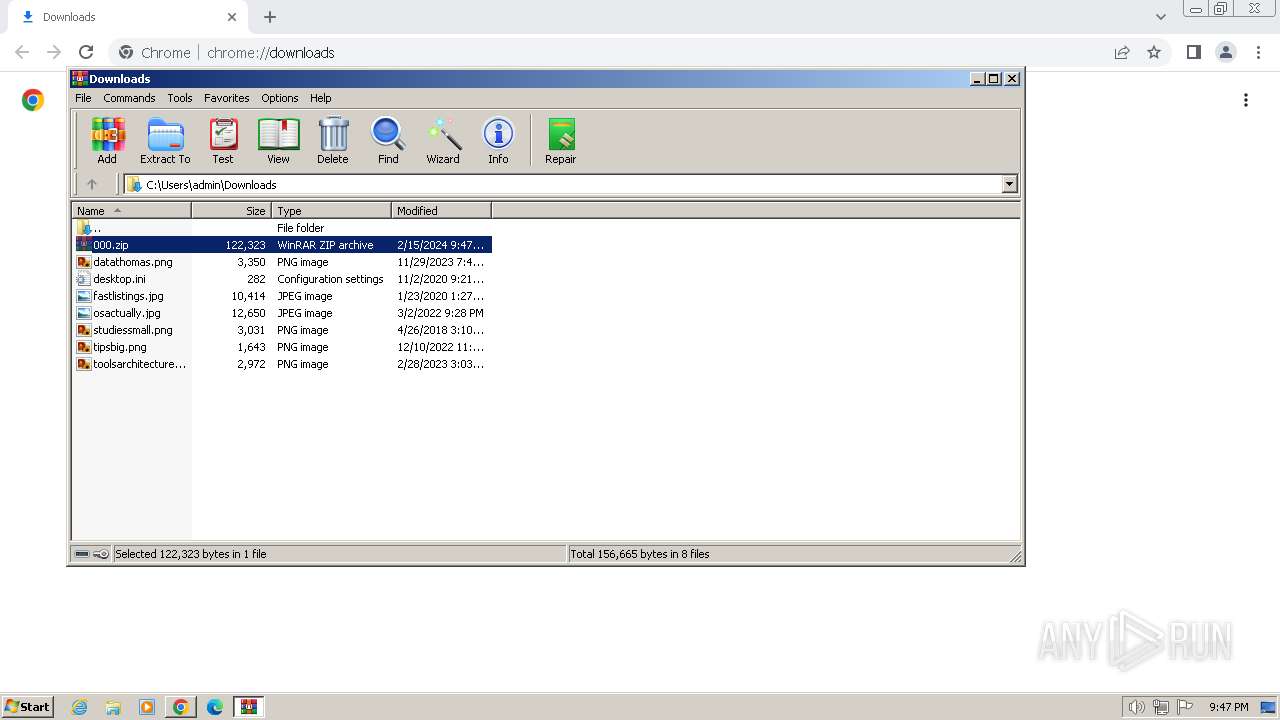
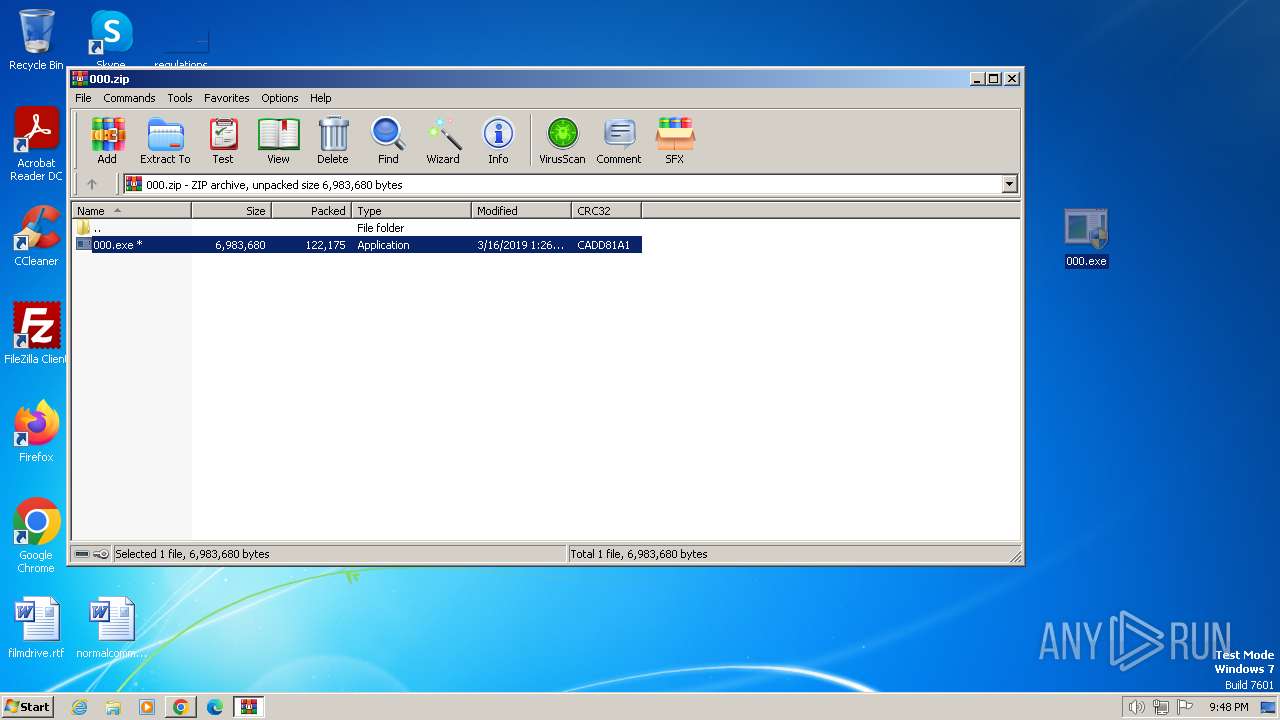
The process uses the downloaded file
- chrome.exe (PID: 2576)
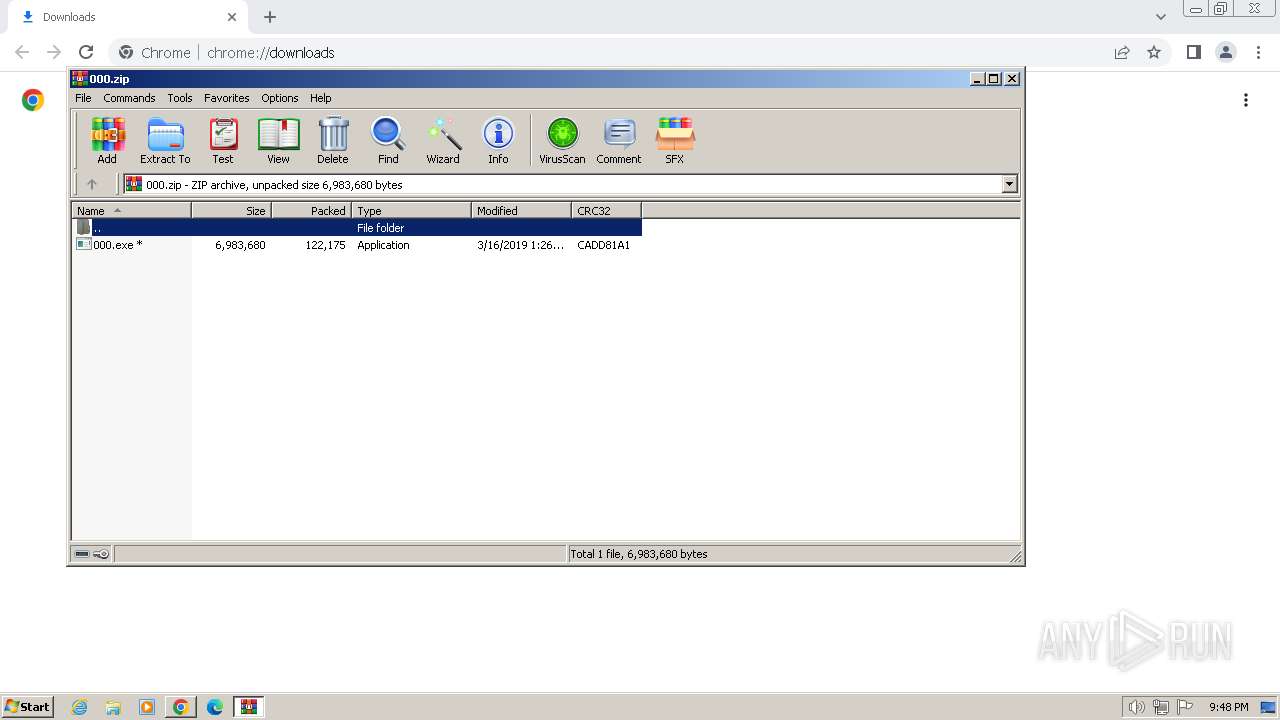
- WinRAR.exe (PID: 992)
Checks supported languages
- 000.exe (PID: 1380)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 992)
Reads the computer name
- 000.exe (PID: 1380)
Reads the machine GUID from the registry
- 000.exe (PID: 1380)
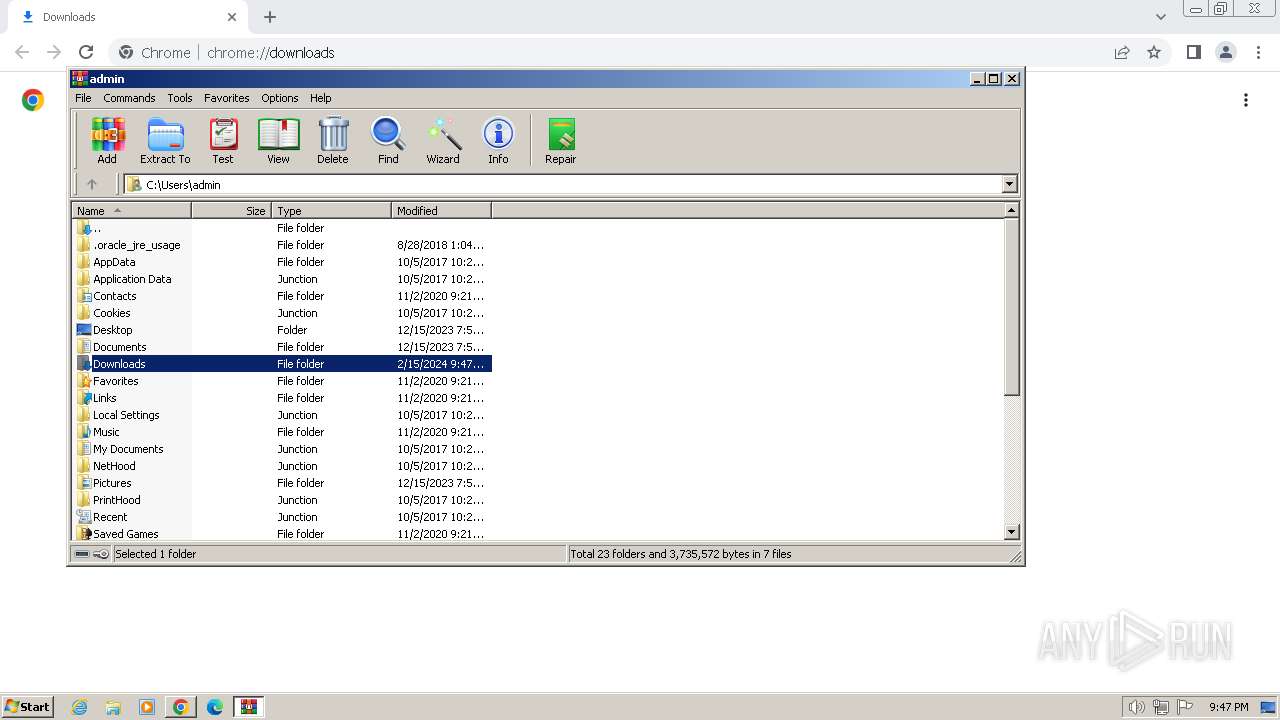
Manual execution by a user
- 000.exe (PID: 1216)
- 000.exe (PID: 1380)
Create files in a temporary directory
- 000.exe (PID: 1380)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 992)
Creates files in the program directory
- cmd.exe (PID: 2736)
Checks proxy server information
- 000.exe (PID: 1380)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
128
Monitored processes
23
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | taskkill /f /im taskmgr.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1248 --field-trial-handle=1168,i,17974188765009550863,9203217514069226008,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
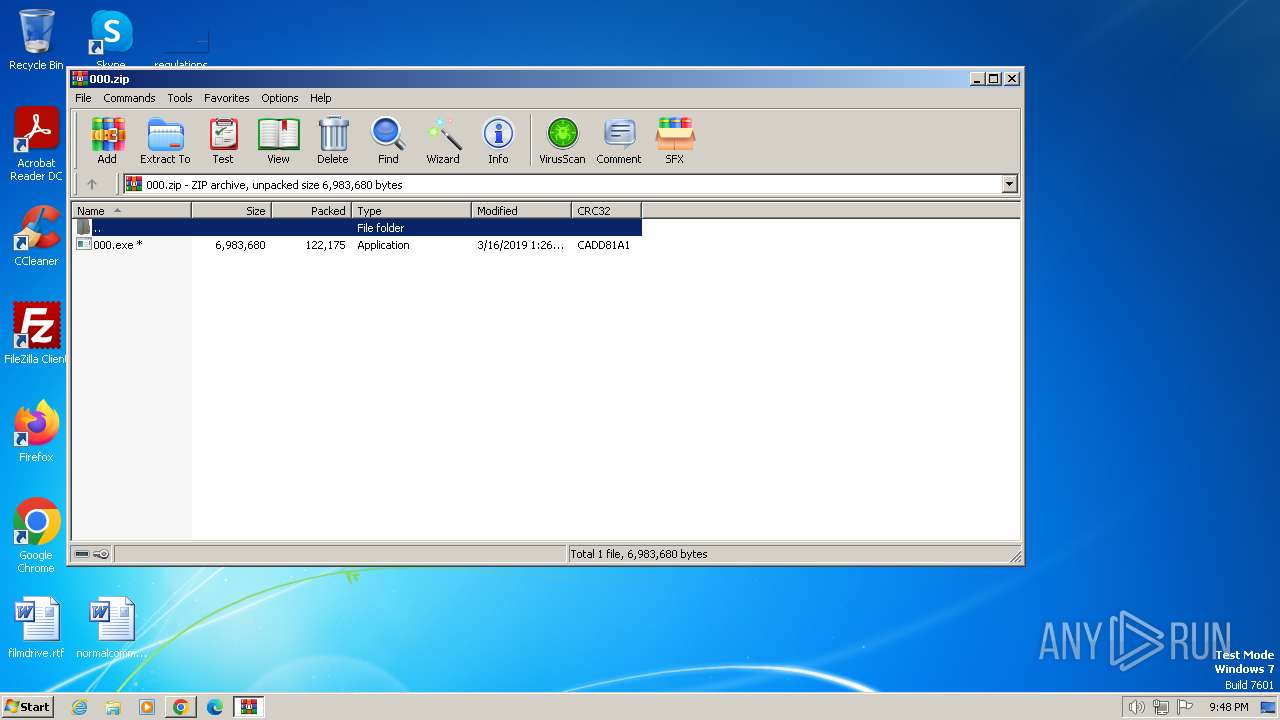
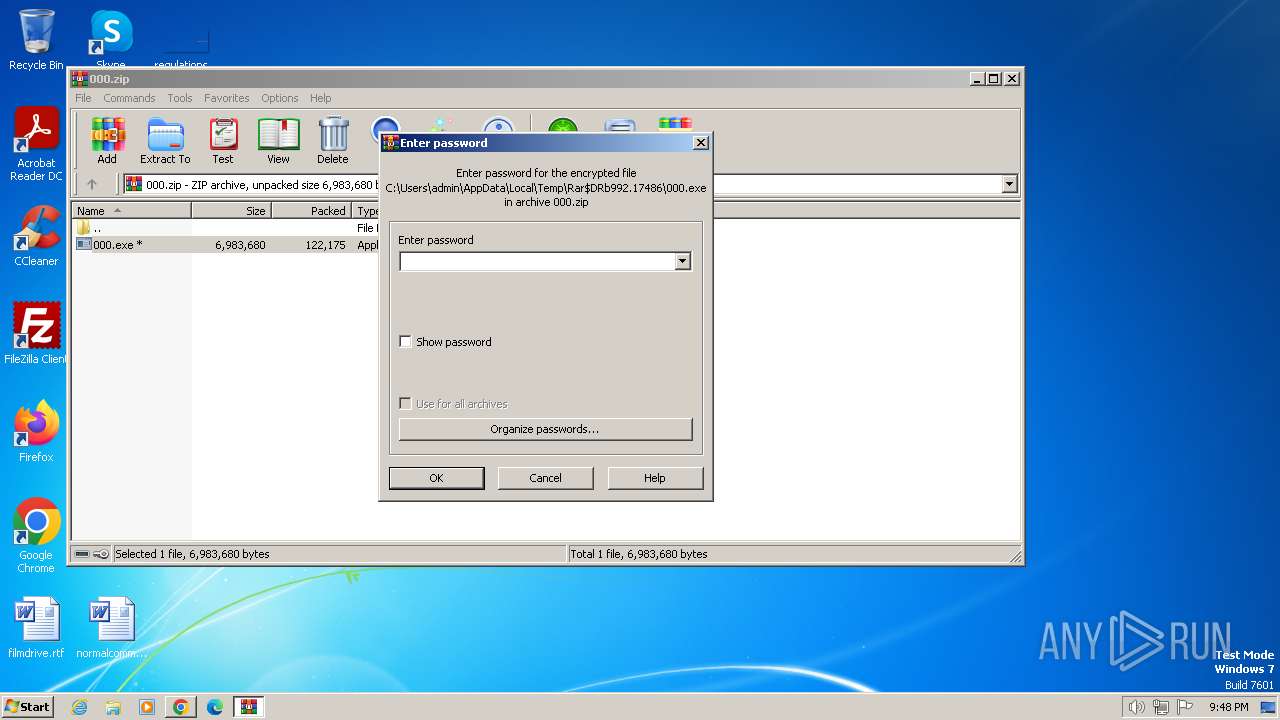
| 992 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\000.zip" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1216 | "C:\Users\admin\Desktop\000.exe" | C:\Users\admin\Desktop\000.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: 000 Exit code: 3221226540 Version: 0.0.0.0 Modules
| |||||||||||||||
| 1380 | "C:\Users\admin\Desktop\000.exe" | C:\Users\admin\Desktop\000.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 000 Exit code: 1073807364 Version: 0.0.0.0 Modules
| |||||||||||||||
| 1792 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\000.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2028 | taskkill /f /im explorer.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
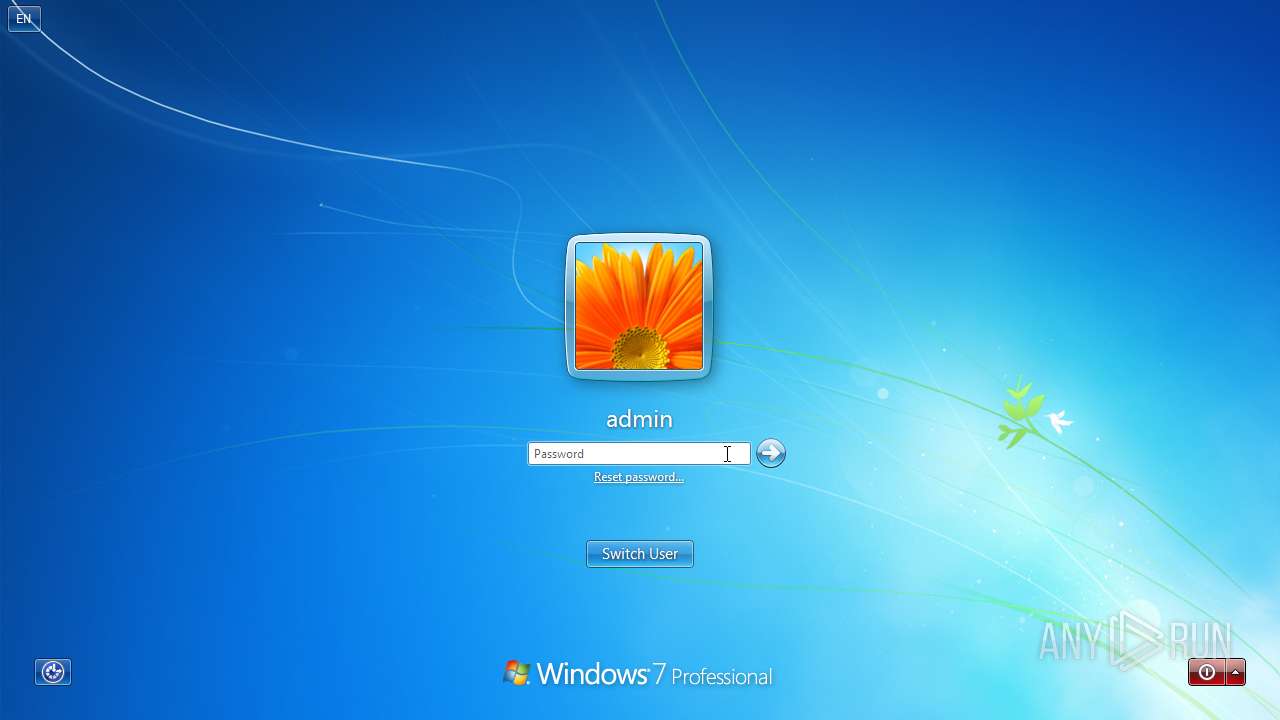
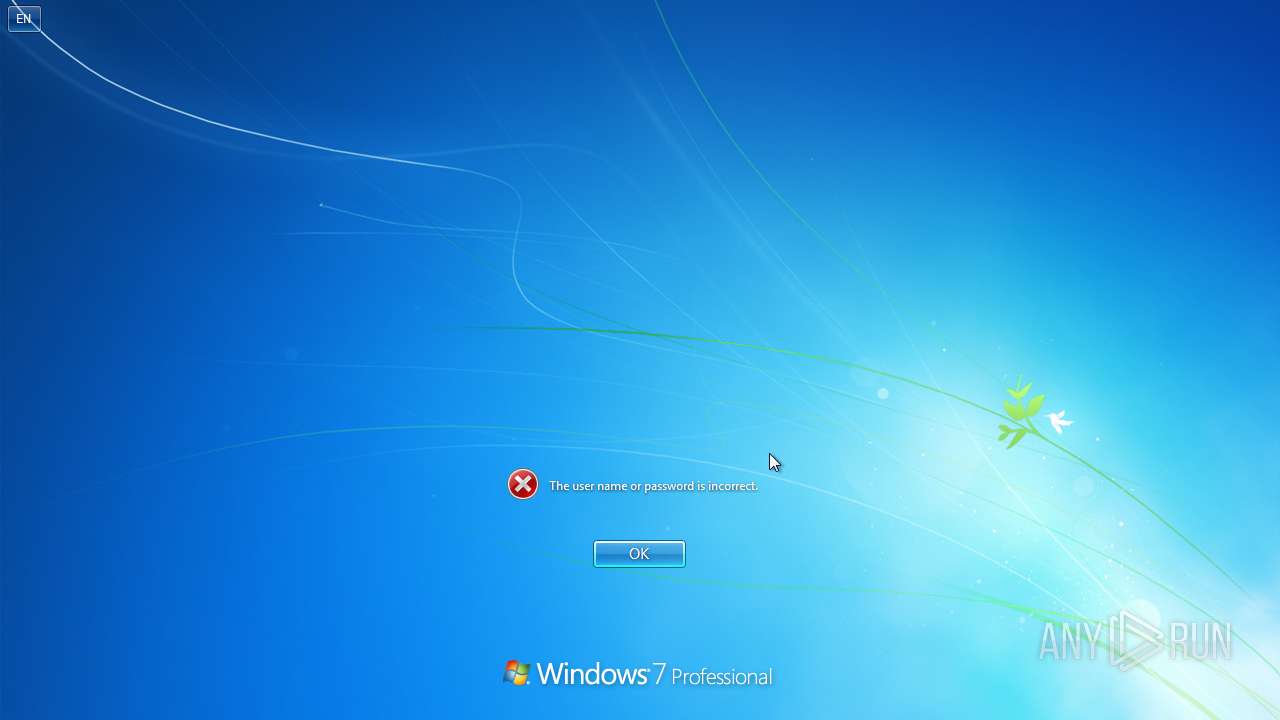
| 2524 | wmic useraccount where name='admin' rename 'UR NEXT' | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2012 --field-trial-handle=1168,i,17974188765009550863,9203217514069226008,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3328 --field-trial-handle=1168,i,17974188765009550863,9203217514069226008,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
18 229
Read events
18 077
Write events
142
Delete events
10
Modification events
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
3
Suspicious files
30
Text files
451
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17f193.TMP | — | |
MD5:— | SHA256:— | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a88f7aac-2e6b-45e4-b7f2-e62a093d83d3.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF17f387.TMP | text | |
MD5:F5B58F0B08202C8D6DE12514994A84BF | SHA256:F5BA8809B6A3920A11CF31E7F6A1DEC46EF4F4339D6158967CCB1405409D1241 | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:65239F35CB63C76EA1F59EF64F7AAFF4 | SHA256:252EF82CC03FDE4BEF13CF81CD1AC5CE45854212D1A7359035E7A5D6BEDBE229 | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF17f85a.TMP | — | |
MD5:— | SHA256:— | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF17f1b3.TMP | text | |
MD5:ADB669AB4CD1C63883C64FB0DBA2C7DA | SHA256:18BFF89047EC5B122573D089B3DC7A7DD14A5A7A515B2D8141584B41E723253F | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF180886.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
33
DNS requests
28
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
3240 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2752 | chrome.exe | 140.82.121.4:443 | github.com | GITHUB | US | unknown |
2752 | chrome.exe | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | unknown |
2752 | chrome.exe | 185.199.109.154:443 | github.githubassets.com | FASTLY | US | unknown |
2752 | chrome.exe | 142.250.186.170:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
2752 | chrome.exe | 185.199.111.133:443 | avatars.githubusercontent.com | FASTLY | US | unknown |
2752 | chrome.exe | 142.250.185.106:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| shared |
accounts.google.com |
| shared |
github.githubassets.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
collector.github.com |
| whitelisted |
api.github.com |
| whitelisted |
objects.githubusercontent.com |
| shared |
sb-ssl.google.com |
| whitelisted |